System and Method for Security Activation with Session Granularity
Tenny; Nathan Edward ; et al.
U.S. patent application number 15/990156 was filed with the patent office on 2019-03-28 for system and method for security activation with session granularity. The applicant listed for this patent is Futurewei Technologies, Inc.. Invention is credited to Yi Guo, Nathan Edward Tenny.
| Application Number | 20190098495 15/990156 |
| Document ID | / |
| Family ID | 65808529 |
| Filed Date | 2019-03-28 |





| United States Patent Application | 20190098495 |
| Kind Code | A1 |
| Tenny; Nathan Edward ; et al. | March 28, 2019 |
System and Method for Security Activation with Session Granularity
Abstract
A method for operating a user equipment (UE) includes deriving security keys for a signaling radio bearer (SRB) in accordance with a first message received from an access node, initiating security for the SRB in accordance with the first message, receiving, from the access node, a second message including at least one security parameter for at least one data radio bearer (DRB), wherein the at least one security parameter is associated with a session that includes the at least one DRB, and wherein the second message is secured with the security keys for the SRB, and initiating security for the at least one DRB in accordance with the at least one security parameter.
| Inventors: | Tenny; Nathan Edward; (Poway, CA) ; Guo; Yi; (Shanghai, CN) | ||||||||||
| Applicant: |
|
||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|
| Family ID: | 65808529 | ||||||||||
| Appl. No.: | 15/990156 | ||||||||||
| Filed: | May 25, 2018 |
Related U.S. Patent Documents
| Application Number | Filing Date | Patent Number | ||
|---|---|---|---|---|
| 62564435 | Sep 28, 2017 | |||
| Current U.S. Class: | 1/1 |
| Current CPC Class: | H04W 12/0401 20190101; H04W 12/04 20130101; H04W 88/08 20130101; H04W 76/10 20180201; H04W 76/20 20180201 |
| International Class: | H04W 12/04 20060101 H04W012/04; H04W 76/10 20060101 H04W076/10 |
Claims
1. A computer implemented method for operating a user equipment (UE), the method comprising: deriving, by the UE, security keys for a signaling radio bearer (SRB) in accordance with a first message received from an access node; initiating, by the UE, security for the SRB in accordance with the first message; receiving, by the UE from the access node, a second message including at least one security parameter for at least one data radio bearer (DRB), wherein the at least one security parameter is associated with a session that includes the at least one DRB, and wherein the second message is secured with the security keys for the SRB; and initiating, by the UE, security for the at least one DRB in accordance with the at least one security parameter.
2. The method of claim 1, further comprising: receiving, by the UE from the access node, a third message associated with at least one additional DRB, the third message including the at least one security parameter, and wherein the third message is secured with the security keys for the SRB; and initiating, by the UE, security for the at least one additional DRB in accordance with the at least one security parameter.
3. The method of claim 2, wherein a first key used for securing the at least one DRB and a second key used for securing the at least one additional DRB are the same.
4. The method of claim 2, wherein a first key used for securing the at least one DRB and a second key used for securing the at least one additional DRB are different.
5. The method of claim 2, wherein the at least one security parameter comprises a session identifier.
6. The method of claim 1, wherein the at least one security parameter comprises one or more of an integrity indicator, a ciphering indicator, one or more radio bearer specific algorithms, or radio bearer specific key information.
7. The method of claim 1, wherein the first message comprises a SecurityModeCommand message.
8. The method of claim 1, wherein the second message comprises a radio resource control (RRC) reconfiguration message.
9. The method of claim 8, wherein the RRC reconfiguration message comprises a RRCConnectionReconfiguration message.
10. A computer implemented method for operating an access node, the method comprising: receiving, by the access node from an access and mobility management function (AMF), a first message to initiate a session at a user equipment (UE), the first message including at least one security parameter for at least one data radio bearer (DRB) associated with the session; sending, by the access node to the UE, a second message including the at least one security parameter for the at least one DRB associated with the session; and initiating, by the access node, security for the at least one DRB in accordance with the at least one security parameter.
11. The method of claim 10, further comprising: sending, by the access node to the UE, a third message including the at least one security parameter for at least one additional DRB; and initiating, by the access node, security for the at least one additional DRB in accordance with the at least one security parameter.
12. The method of claim 10, further comprising: receiving, by the access node from the AMF, a fourth message initiating a context setup; and sending, by the access node to the UE, a fifth message initiating security on the UE.
13. The method of claim 12, wherein the fifth message comprises a SecurityModeCommand message.
14. The method of claim 12, wherein the fourth message comprises an initial context setup request message.
15. The method of claim 10, wherein the first message comprises a protocol data unit (PDU) session setup message.
16. The method of claim 10, wherein the second message comprises a radio resource control (RRC) reconfiguration message.
17. The method of claim 16, wherein the RRC reconfiguration message comprises a RRCConnectionReconfiguration message.
18. A user equipment (UE) comprising: a memory storage comprising instructions; and one or more processors in communication with the memory storage, wherein the one or more processors execute the instructions to: derive security keys for a signaling radio bearer (SRB) in accordance with a first message received from an access node, initiate security for the SRB in accordance with the first message, receive, from the access node, a second message including at least one security parameter for at least one data radio bearer (DRB), wherein the at least one security parameter is associated with a session that includes the at least one DRB, and wherein the second message is secured with the security keys for the SRB, and initiate security for the at least one DRB in accordance with the at least one security parameter.
19. The UE of claim 18, wherein the one or more processors further execute the instructions to receive, from the access node, a third message associated with at least one additional DRB, the third message including the at least one security parameter, and wherein the third message is secured with the security keys for the SRB, and initiate security for the at least one additional DRB in accordance with the at least one security parameter.
20. The UE of claim 19, wherein a first key used for securing the at least one DRB and a second key used for securing the at least one additional DRB are the same.
21. The UE of claim 19, wherein a first key used for securing the at least one DRB and a second key used for securing the at least one additional DRB are different.
22. An access node comprising: a memory storage comprising instructions; and one or more processors in communication with the memory storage, wherein the one or more processors execute the instructions to: receive, from an access and mobility management function (AMF), a first message to initiate a session at a user equipment (UE), the first message including at least one security parameter for at least one data radio bearer (DRB) associated with the session, send, to the UE, a second message including the at least one security parameter for the at least one DRB associated with the session, and initiate security for the at least one DRB in accordance with the at least one security parameter.
23. The access node of claim 22, wherein the one or more processors further execute the instructions to send, to the UE, a third message including the at least one security parameter for at least one additional DRB, and initiate security for the at least one additional DRB in accordance with the at least one security parameter.
24. The access node of claim 22, wherein the one or more processors further execute the instructions to receive, from the AMF, a fourth message initiating a context setup, and send, to the UE, a fifth message initiating security on the UE.
Description
[0001] This application claims the benefit of U.S. Provisional Application No. 62/564,435, filed on Sep. 28, 2017, entitled "System and Method for Security Activation with Session Granularity," which application is hereby incorporated herein by reference in its entirety.
TECHNICAL FIELD
[0002] The present disclosure relates generally to a system and method for digital communications, and, in particular embodiments, to a system and method for security activation with session granularity.
BACKGROUND
[0003] Security in wireless communications systems is an important consideration. End-to-end security provides protection for information exchanged between communications devices, as well as protection for the users of these communications devices. Security in wireless communications systems may involve user or device authentication, data integrity, user or data confidentiality, access control, billing, and so on. Heretofore, security has been provided in a one-shot basis, with all sessions associated with a single device having the same security settings.
[0004] However, at a single device, some sessions may not require the highest levels of security, while other sessions may find that the security settings associated with the device are insufficient. Therefore, there is a need for session granularity security activations.
SUMMARY
[0005] Example embodiments provide a system and method for security activation with session granularity.
[0006] In accordance with an example embodiment, a computer implemented method for operating a user equipment (UE) is provided. The method includes deriving, by the UE, security keys for a signaling radio bearer (SRB) in accordance with a first message received from an access node, initiating, by the UE, security for the SRB in accordance with the first message, receiving, by the UE from the access node, a second message including at least one security parameter for at least one data radio bearer (DRB), wherein the at least one security parameter is associated with a session that includes the at least one DRB, and wherein the second message is secured with the security keys for the SRB, and initiating, by the UE, security for the at least one DRB in accordance with the at least one security parameter.
[0007] Optionally, in any of the preceding embodiments, an embodiment further includes receiving, by the UE from the access node, a third message associated with at least one additional DRB, the third message including the at least one security parameter, and wherein the third message is secured with the security keys for the SRB, and initiating, by the UE, security for the at least one additional DRB in accordance with the at least one security parameter.
[0008] Optionally, in any of the preceding embodiments, an embodiment wherein a first key used for securing the at least one DRB and a second key used for securing the at least one additional DRB are the same.
[0009] Optionally, in any of the preceding embodiments, an embodiment wherein a first key used for securing the at least one DRB and a second key used for securing the at least one additional DRB are different.
[0010] Optionally, in any of the preceding embodiments, an embodiment wherein the at least one security parameter comprises a session identifier.
[0011] Optionally, in any of the preceding embodiments, an embodiment wherein the at least one security parameter comprises one or more of an integrity indicator, a ciphering indicator, one or more radio bearer specific algorithms, or radio bearer specific key information.
[0012] Optionally, in any of the preceding embodiments, an embodiment wherein the first message comprises a SecurityModeCommand message.
[0013] Optionally, in any of the preceding embodiments, an embodiment wherein the second message comprises a radio resource control (RRC) reconfiguration message.
[0014] Optionally, in any of the preceding embodiments, an embodiment wherein the RRC reconfiguration message comprises a RRCConnectionReconfiguration message.
[0015] In accordance with an example embodiment, a computer implemented method for operating an access node is provided. The method includes receiving, by the access node from an access and mobility management function (AMF), a first message to initiate a session at a UE, the first message including at least one security parameter for at least one DRB associated with the session, sending, by the access node to the UE, a second message including the at least one security parameter for the at least one DRB associated with the session, and initiating, by the access node, security for the at least one DRB in accordance with the at least one security parameter.
[0016] Optionally, in any of the preceding embodiments, an embodiment further includes sending, by the access node to the UE, a third message including the at least one security parameter for at least one additional DRB, and initiating, by the access node, security for the at least one additional DRB in accordance with the at least one security parameter.
[0017] Optionally, in any of the preceding embodiments, an embodiment further includes receiving, by the access node from the AMF, a fourth message initiating a context setup, and sending, by the access node to the UE, a fifth message initiating security on the UE.
[0018] Optionally, in any of the preceding embodiments, an embodiment wherein the fifth message comprises a SecurityModeCommand message.
[0019] Optionally, in any of the preceding embodiments, an embodiment wherein the fourth message comprises an initial context setup request message.
[0020] Optionally, in any of the preceding embodiments, an embodiment wherein the first message comprises a PDU session setup message.
[0021] Optionally, in any of the preceding embodiments, an embodiment wherein the second message comprises a RRC reconfiguration message.
[0022] Optionally, in any of the preceding embodiments, an embodiment wherein the RRC reconfiguration message comprises a RRCConnectionReconfiguration message.
[0023] In accordance with an example embodiment, a UE is provided. The UE includes a memory storage comprising instructions, and one or more processors in communication with the memory storage. The one or more processors execute the instructions to derive security keys for a SRB in accordance with a first message received from an access node, initiate security for the SRB in accordance with the first message, receive, from the access node, a second message including at least one security parameter for at least one DRB, wherein the at least one security parameter is associated with a session that includes the at least one DRB, and wherein the second message is secured with the security keys for the SRB, and initiate security for the at least one DRB in accordance with the at least one security parameter.
[0024] Optionally, in any of the preceding embodiments, an embodiment wherein the one or more processors further execute the instructions to receive, from the access node, a third message associated with at least one additional DRB, the third message including the at least one security parameter, and wherein the third message is secured with the security keys for the SRB, and initiate security for the at least one additional DRB in accordance with the at least one security parameter.
[0025] Optionally, in any of the preceding embodiments, an embodiment wherein a first key used for securing the at least one DRB and a second key used for securing the at least one additional DRB are the same.
[0026] Optionally, in any of the preceding embodiments, an embodiment wherein a first key used for securing the at least one DRB and a second key used for securing the at least one additional DRB are different.
[0027] In accordance with an example embodiment, an access node is provided. The access node includes a memory storage comprising instructions, and one or more processors in communication with the memory storage. The one or more processors execute the instructions to receive, from an AMF, a first message to initiate a session at a UE, the first message including at least one security parameter for at least one DRB associated with the session, send, to the UE, a second message including the at least one security parameter for the at least one DRB associated with the session, and initiate security for the at least one DRB in accordance with the at least one security parameter.
[0028] Optionally, in any of the preceding embodiments, an embodiment wherein the one or more processors further execute the instructions to send, to the UE, a third message including the at least one security parameter for at least one additional DRB, and initiate security for the at least one additional DRB in accordance with the at least one security parameter.
[0029] Optionally, in any of the preceding embodiments, an embodiment wherein the one or more processors further execute the instructions to receive, from the AMF, a fourth message initiating a context setup, and send, to the UE, a fifth message initiating security on the UE.
[0030] Practice of the foregoing embodiments enables the security settings to be configured on a session basis, thereby allowing for the tailoring of the security settings to meet the security requirements of a particular session. Not only does the configuration of the security settings based on the security requirements of the different sessions enables the meeting of each sessions' security requirements, the use of less stringent security settings for sessions that do not require high security levels helps to improve overall communications system performance by reducing processing time and overhead.
BRIEF DESCRIPTION OF THE DRAWINGS
[0031] For a more complete understanding of the present disclosure, and the advantages thereof, reference is now made to the following descriptions taken in conjunction with the accompanying drawings, in which:
[0032] FIG. 1 illustrates an example wireless communications system that includes both a core network (CN) and a radio access network (RAN) according to example embodiments described herein;
[0033] FIG. 2 illustrates a diagram of an interaction between communications devices in a communications system setting up security;
[0034] FIG. 3 illustrates a diagram of an interaction between communications devices in a communications system setting up security with session granularity according to example embodiments described herein;
[0035] FIG. 4 illustrates a flow diagram of example operations occurring in a UE participating in security activation with session granularity according to example embodiments described herein;
[0036] FIG. 5 illustrates a flow diagram of example operations occurring in an access node participating in security activation with session granularity according to example embodiments described herein;
[0037] FIG. 6 illustrates an example communication system according to example embodiments described herein;
[0038] FIGS. 7A and 7B illustrate example devices that may implement the methods and teachings according to this disclosure; and
[0039] FIG. 8 is a block diagram of a computing system that may be used for implementing the devices and methods disclosed herein.
DETAILED DESCRIPTION OF ILLUSTRATIVE EMBODIMENTS
[0040] The making and using of the presently example embodiments are discussed in detail below. It should be appreciated, however, that the present disclosure provides many applicable inventive concepts that can be embodied in a wide variety of specific contexts. The specific embodiments discussed are merely illustrative of specific ways to make and use the embodiments, and do not limit the scope of the disclosure.
[0041] FIG. 1 illustrates an example wireless communications system 100 that includes both a core network (CN) 101 and a radio access network (RAN) 102. RAN 102 includes an access node 105 serving a plurality of UEs, such as UE 110, UE 112, and UE 114. In a cellular operating mode, communications to and from the plurality of UEs go through access node 105, while in device to device communications mode, such as proximity services (ProSe) operating mode, for example, direct communication between UEs is possible. Access nodes may also be commonly referred to as Node Bs, evolved Node Bs (eNBs), next generation (NG) Node Bs (gNBs), master eNBs (MeNBs), secondary eNBs (SeNBs), master gNBs (MgNBs), secondary gNBs (SgNBs), network controllers, control nodes, base stations, access points, and so on, while UEs may also be commonly referred to as mobile stations, mobiles, terminals, users, subscribers, stations, and the like. Examples of UEs include cellular phones, wireless tablets, laptop computers, etc. A separate radio network controller (RNC) that does not have base station functionality is another example of a control node or network controller, but the access node may incorporate RNC functionality to reduce response times. Communications from an access node to a UE are commonly referred to as downlink communications, while communications from a UE to an access node are commonly referred to as uplink communications.
[0042] Core network 101 includes network entities such as a user plane function (UPF) 115 that provides entry and egress points for packets intended for users and an access and mobility management function (AMF) 125 that performs mobility management functions such as, for example, choosing the UPF for a UE, authenticating the UE, and checking its access permissions. Core network 101 also includes a session management function (SMF) 120, which performs session management functions such as, for example, establishing and releasing protocol data unit (PDU) sessions, enforcing policy on PDU sessions, and terminating session management signaling with the UE. It is noted that the definitions and terminology used in the discussion of FIG. 1 are from the Third Generation Partnership Project (3GPP) New Radio (NR) series of technical standards and they may differ for other types of communications systems. 3GPP NR is also commonly referred to as Fifth Generation (5G) NR. The names of the entities shown in core network 101 are exemplary and may vary in particular embodiments. For example, the network entities may be nodes that support a set of virtualized network functions. As another example, the network entities in a 3GPP Long Term Evolution (LTE) system may comprise a packet gateway (P-GW), a serving gateway (S-GW), a mobility management entity (MME), and the like. Therefore, the use of 3GPP NR terminology and definitions should not be construed as being limiting to the scope or the spirit of the example embodiments.
[0043] Wireless communications system 100 also includes a plurality of remote devices (RDs) within RAN 102, such as RD 127 and RD 129. The plurality of RDs includes a cellular handset functioning as a Remote UE 125, while the remaining RDs may include sensor devices, wearable devices, smart appliances, and so on. The term remote device (RD) may be used to refer to remote UEs, including remote devices that function as UEs but do not have the form factor or function of a conventional cellular handset (such as sensor devices, wearable devices, smart appliances, and so on). While it is understood that communications systems may employ multiple access nodes capable of communicating with a number of UEs, remote UEs, and other RDs, only one access node, one remote UE, a number of other UEs, and a number of other RDs are illustrated for simplicity.
[0044] As discussed previously, security in wireless communications systems provides protection for information exchanged between communications devices, as well as user or device authentication, data integrity, user or data confidentiality, access control, billing, and so forth. Therefore, security is an important consideration. However, existing security techniques have provided security on a one-shot basis (such as when the UE context is set up, for example), where all sessions associated with a single device have the same security settings. For example, a single procedure may activate security for all sessions or all bearers associated with the device, using a common set of security settings.
[0045] FIG. 2 illustrates a diagram 200 of an interaction between communications devices in a communications system setting up security. As shown in FIG. 2, the interaction occurs between a UE 205, an eNB 207, and a MME 209, while the communications devices participate in setting up security for UE 205. The communications made and the processing performed by the communications device shown in FIG. 2, as well as the terminology used in the description thereof, are compliant with the 3GPP LTE series of technical standards. Security set up procedures for other communications systems are similar.
[0046] UE 205, upon entering a coverage area of eNB 207 or powering on in the coverage area of eNB 207, initiates a random access procedure (by transmitting a preamble on a random access channel (RACH), for example) with eNB 207 (event 215). If eNB 207 does not already have a context for UE 205 (i.e., a UE context for UE 205), eNB 207 sends an initial UE message to MME 209 (event 217) and receives an initial context setup request from MME 209, which includes information needed to set up the UE context for UE 205 (event 219). UE 205 is now in a connected state, e.g., a radio resource control (RRC) connected state (RRC_CONNECTED), with eNB 207 (block 221). eNB 207 sends a SecurityModeCommand message to UE 205 (event 223) to activate security at UE 205. The SecurityModeCommand message activates security, e.g., ciphering or integrity checking, for UE 205 on a per UE basis, meaning that the same security settings is applied to all sessions of UE 205, independent of actual security needs of individual sessions. UE 205 derives security keys and starts security operations (block 225).
[0047] As discussed previously, the use of a single set of security settings may not adequately meet the needs of all sessions of a UE. As an illustrative example, watching a publicly accessible video typically does not require the same level of security as participating in on-line banking, on-line tax filing, or accessing medical records. Applying maximum security (as usually needed for on-line banking, on-line tax filing, or medical record access) to video consumption may lead to inefficient use of network resources (due to network resources being dedicated to providing the higher level of security), thereby leading to decreased communications system performance. A decision as to the required level of security may be made on a per-session basis, taking into account operator policy regarding the service(s) supported by each session, for example. Therefore, there is a need for systems and methods for security activation with at least session granularity.
[0048] Additionally, an objective for the 5G NR system architecture is to have security be on a per PDU session basis, with some security parameters, such as security keys, still potentially being on a per UE basis. Data integrity, at least, will be enabled or disabled on a per PDU session basis, and it is also considered to have data encryption enabled or disabled on a per PDU session basis. In general, when a PDU session is enabled, one or more radio bearers are configured. Furthermore, packet data convergence protocol (PDCP) entities for these radio bearers should reflect the PDU session security configuration.
[0049] The 3GPP LTE security procedure, as shown in FIG. 2, for example, does not manage security on a per session basis. The PDU session is not exposed to the UE Access Stratum (AS), which implies that it may not be possible to simply activate security for a specific PDU session because the UE AS layers have no concept of a particular PDU session. The introduction of the PDU session concept to the UE AS would be a violation of the layering concept. However, a signaling procedure that can achieve the security granularity is needed.
[0050] According to an example embodiment, systems and methods for security activations on a session basis are provided. According to an example embodiment, the network individually configures the security configuration of each radio bearer of a PDU session. The network may be responsible for ensuring that the radio bearers of the PDU session share a common security configuration by consistently configuring the security configuration of the radio bearers of the PDU session. As an illustrative example, a SecurityModeCommand message is sent during an initial UE context setup. The SecurityModeCommand message establishes security parameters on a per UE basis and starts security on signaling radio bearers (SRBs). Then, when a PDU session is set up, the network establishes new data radio bearers (DRBs) of the PDU session with RRCConnectionReconfiguration messages. The network specifies the security configuration of each new radio bearer of the PDU session in a corresponding PDCP configuration of each new radio bearer. Additional radio bearers may be added to the PDU session and the network specifies the security configuration of each additional radio bearer in its corresponding PDCP configuration. Therefore, the network ensures that each radio bearer of the PDU session has the same security settings by consistently configuring the individual security configurations of each of the radio bearers of the PDU session. In other words, the network applies the same security settings to each radio bearer of the PDU session when the individual radio bearers are set up, therefore, the radio bearers of the PDU session have the same security configuration.
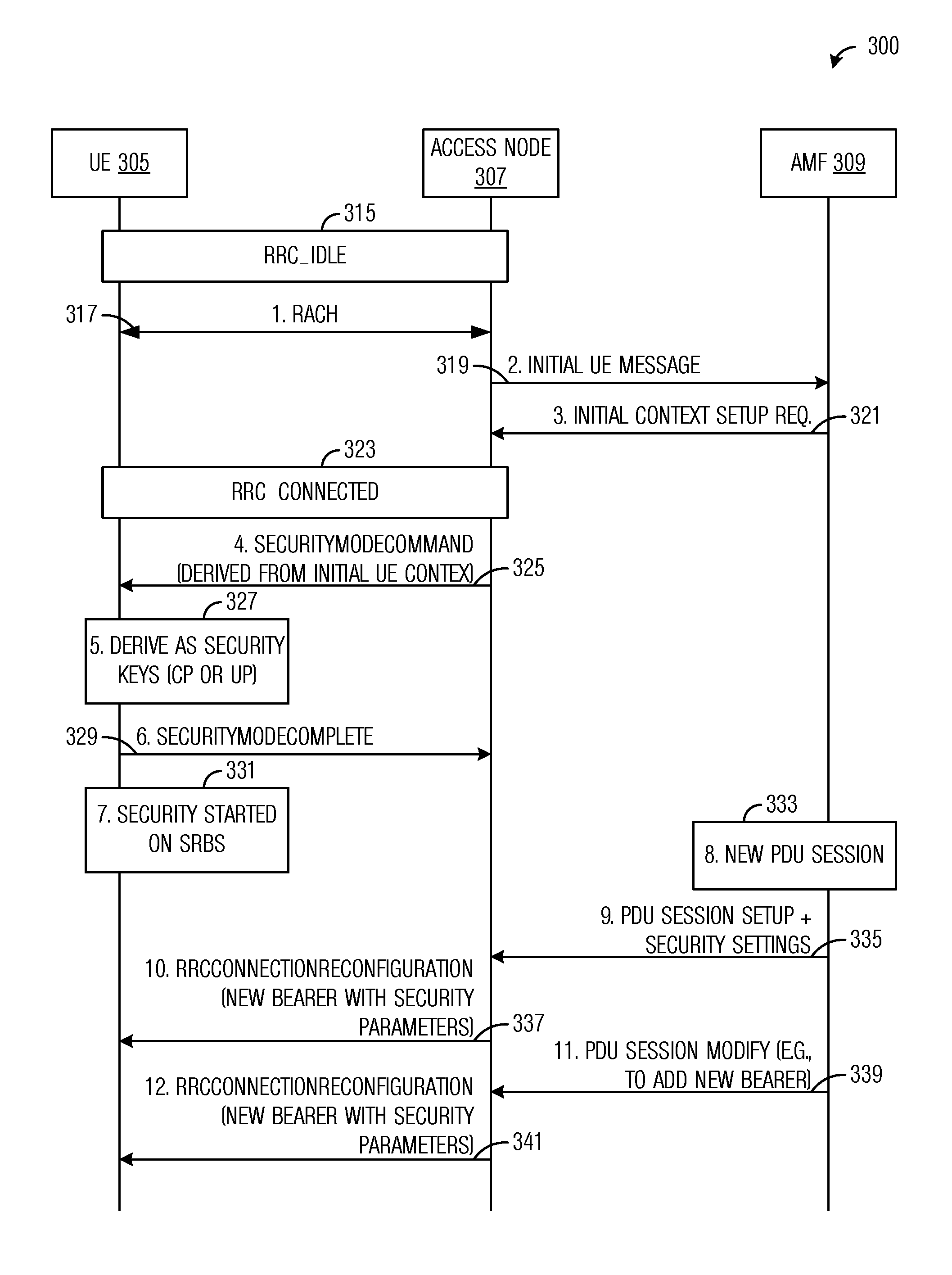
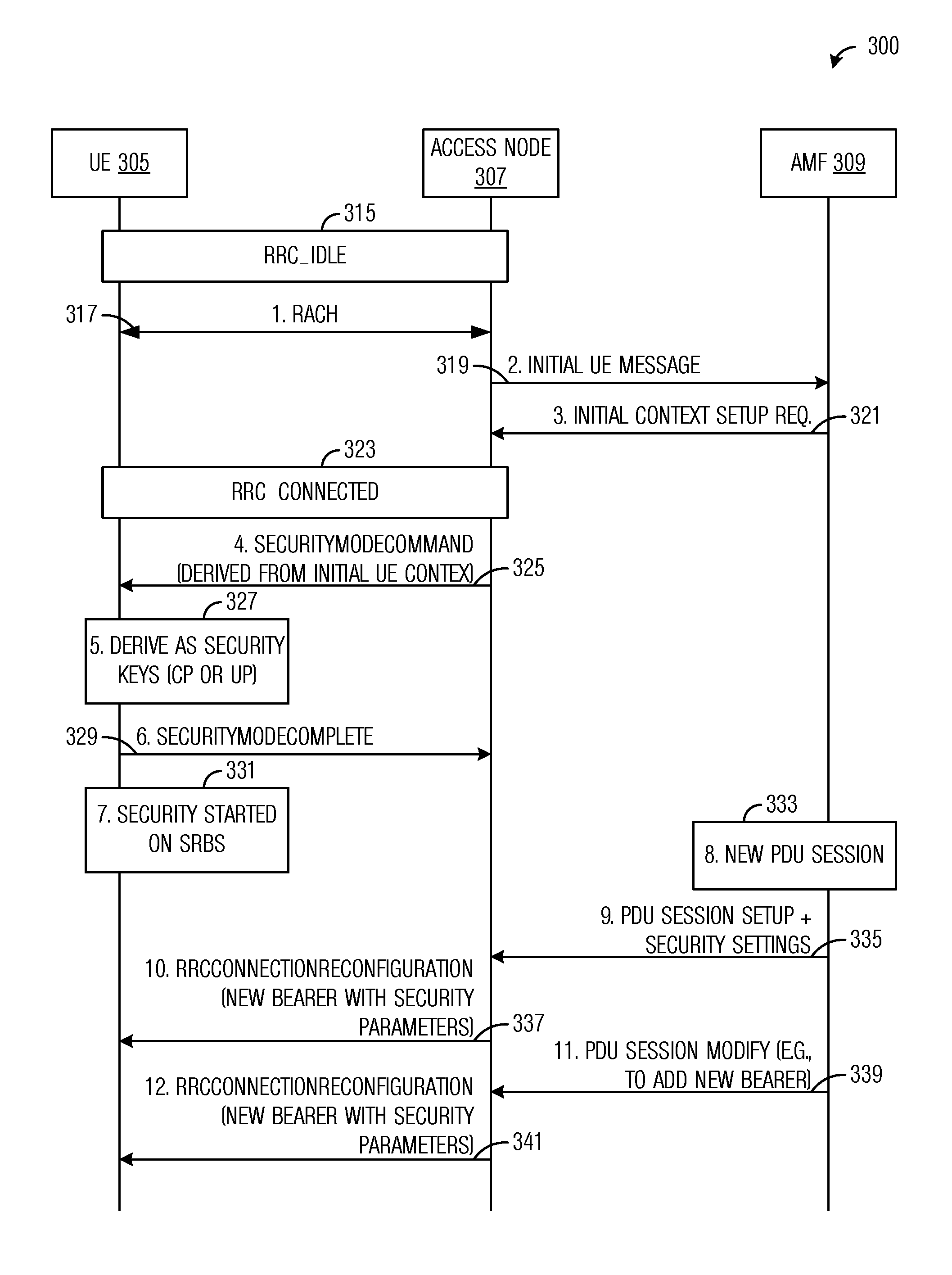
[0051] FIG. 3 illustrates a diagram 300 of an interaction between communications devices in a communications system setting up security with session granularity. As shown in FIG. 3, interactions between a UE 305, an access node 307, and an access and mobility management function (AMF) 309, while the communications devices participate in setting up security for UE 305 with session granularity. The communications made and the processing performed by the communications devices shown in FIG. 3, as well as the terminology used in the description thereof, are compliant with 5G NR system architecture documents. However, the example embodiments presented herein are operable with other standards compliant and non-standards compliant communications systems. Therefore, the use of 5G NR terminology should not be construed as being limiting to either the scope or the spirit of the example embodiments.
[0052] UE 305, upon entering a coverage area of access node 307 or powering on in the coverage area of access node 307, is initially in an idle state, such as RRC_IDLE (block 315). UE 305 initiates a random access procedure (by transmitting a preamble on a RACH, for example) with access node 307 (event 317). If access node 307 does not already have a context for UE 305 (i.e., a UE context for UE 305), access node 307 sends an initial UE message to AMF 309 (event 319) and receives an initial context setup request from AMF 309, which includes information needed to set up the UE context for UE 305 (event 321). UE 305 is now in a connected state, e.g., RRC_CONNECTED, with access node 307 (block 323).
[0053] At this stage, UE 305 only has a first SRB (i.e., SRB1) setup with no security activated. Security activation occurs with the SecurityModeCommand message. With UE 305 in the connected state, access node 307 sends a SecurityModeCommand message to trigger key derivation and starts security at SRBs associated with UE 305 (event 325). The SecurityModeCommand message includes information derived from the UE context. The information derived from the UE context includes at least security algorithms to be used on the SRBs. The SecurityModeCommand message may also comprise an instruction to derive the keys. According to an embodiment, the SecurityModeCommand message does not start security for DRBs. UE 307 derives security keys, such as control plane (CP) or user plane (UP) protection keys (block 327). UE 305 sends a SecurityModeComplete message to access node 307 to convey that security keys have been derived and security has been started on SRBs (event 329). With the sending of SecurityModeComplete message, UE 305 has started security on SRBs (block 331).
[0054] When a PDU session starts (block 333), one or more DRBs are started. The one or more DRBs have their own security parameters. However, AMF 309 ensures that security parameter consistency is maintained so that at least some of the security parameters of the DRBs of the PDU session are maintained consistently across all of the DRBs of the PDU session. AMF 309 sends a PDU session setup command with security parameters to access node 307 (event 335). The PDU session setup command may include security parameters for the one or more DRBs. The security parameters for the one or more DRBs are forwarded to UE 305 in a RRC message. Access node 307 sends a connection configuration message, such as a RRCConnectionReconfiguration message, to UE 305 (event 337). The connection configuration message may include security parameters for the one or more DRBs. The security parameters may include integrity on or off (e.g., an integrity indicator, information, or flag), ciphering on or off (e.g., a ciphering indicator, information, or flag), PDU session specific or radio bearer specific algorithms, PDU session specific or radio bearer specific key information, and so forth. In some embodiments, certain security parameters may vary between DRBs of the same PDU session, while other security parameters are maintained consistently across all of the DRBs of the PDU session. For example, all DRBs of the PDU session may use the same algorithms and have the same settings for integrity on or off and ciphering on or off, but different DRBs of the PDU session may be configured to use different (e.g., bearer specific) keys.
[0055] If one or more DRBs are to be added to the PDU session, the one or more additional DRBs have their own security parameters, however, AMF 309 ensures that security parameter consistency is maintained so that at least some of the security parameters of the DRBs of the PDU session are maintained consistently across all of the DRBs of the PDU session. For example, all DRBs of the PDU session may use the same algorithms and have the same settings for integrity on or off and ciphering on or off. AMF 309 sends a PDU session modify command with security parameters to access node 307 (event 339). The PDU session setup command may include security parameters for the one or more additional DRBs. The security parameters for the one or more additional DRBs are forwarded to UE 305 in a RRC message. Access node 307 sends a connection configuration message, such as a RRCConnectionReconfiguration message, to UE 305 (event 341). The connection configuration message may include security parameters for the one or more DRBs. The security parameters may include integrity on or off (e.g., an integrity indicator, information, or flag), ciphering on or off (e.g., a ciphering indicator, information, or flag), radio bearer specific algorithms, bearer specific key information, and so forth. In some embodiments, certain security parameters may vary between DRBs of the same PDU session, while other security parameters are maintained consistently across all of the DRBs of the PDU session. For example, all DRBs of the PDU session may use the same algorithms and have the same settings for integrity on or off and ciphering on or off, but different DRBs of the PDU session may be configured to use different (e.g., bearer specific) keys.
[0056] It is noted that many security parameters, if they are configured on a per PDU session basis, remain the same for each radio bearer of the PDU session. However, some security parameters, such as security keys, should not be shared over the air for security reasons. Such parameters would not be expected to be configured explicitly in the over-the-air signaling, e.g., they would typically not be enumerated in the configuration fields describing a DRB. According to an example embodiment, information, such as a PDU session identifier, is provided to the UE in order to protect secure information. The information may be included in the bearer configuration sent to the UE. It is noted that it is not necessary to have a new PDU session start instruction to send to the UE. Only the information, which is associated with the radio bearer needs to be sent to the UE. As an illustrative example, when the UE sees a bearer configuration with new information (such as a new PDU session identifier), for which it hasn't already generated a security key, the UE generates a new security key and starts using the new security key for that particular radio bearer (the bearer associated with the new PDU session identifier). In other words, the PDU session-specific information, such as the PDU session identifier, is used as a key index by the UE.
[0057] FIG. 4 illustrates a flow diagram of example operations 400 occurring in a UE participating in security activation with session granularity. Operations 400 may be indicative of operations occurring in a UE as the UE participates in security activation with session granularity.
[0058] Operations 400 begin with the UE in a connected state (such as RRC_CONNECTED) and having a first SRB (i.e., SRB1) setup, but with no security activation. The UE receives a SecurityModeCommand message from an access node (block 405). The UE derives security keys and initiates security on SRBs (block 407). The SecurityModeCommand message triggers key derivation and initiates security on SRBs associated with the UE, for example. The SecurityModeCommand message includes information derived from the UE context of the UE. The information derived from the UE context includes at least security algorithms to be used on the SRBs. The SecurityModeCommand message may also comprise an instruction to derive the keys. The UE receives a configuration command, such as a connection configuration message (e.g., a RRCConnectionReconfiguration message) from the access node (block 409). The connection configuration message starts one or more DRBs associated with a PDU session at the UE. The connection configuration message may include security parameters for the one or more DRBs associated with the PDU session. The connection configuration message may be secured by a key associated with one or more SRBs. The UE initiates security on the one or more DRBs in accordance with the security parameters (block 411). In a situation where one or more additional DRBs are added to the PDU session, the UE may receive an additional connection configuration message (such as a RRCConnectionReconfiguration message) from the access node (block 413). The additional connection configuration message starts one or more additional DRBs associated with the PDU session at the UE. The additional connection configuration message may include security parameters for the one or more additional DRBs, where at least some of the security parameters included with the additional connection configuration message are the same as the corresponding security parameters included with the connection configuration message received in block 409. The UE may initiate security on the one or more additional DRBs in accordance with the security parameters (block 415).
[0059] Additionally, the UE may receive a further configuration command, such as a connection configuration message (e.g., a RRCConnectionReconfiguration message) from the access node, with the further connection configuration message starts one or more DRBs associated with a further PDU session at the UE. The further connection configuration message may include further security parameters for the one or more DRBs associated with the further PDU session. The further connection configuration message may be secured by a key associated with one or more SRBs. The UE initiates security on the one or more DRBs associated with the further PDU session in accordance with the security parameters provided in the further connection configuration message. In other words, the UE initiates separate security for different PDU sessions.
[0060] FIG. 5 illustrates a flow diagram of example operations 500 occurring in an access node participating in security activation with session granularity. Operations 500 may be indicative of operations occurring in an access node as the access node participates in security activation with session granularity.
[0061] Operations 500 begin with the access node sending a SecurityModeCommand message to a UE (block 505). The SecurityModeCommand message triggers key derivation and initiates security on SRBs associated with the UE. The SecurityModeCommand message includes information derived from the UE context of the UE. The information derived from the UE context includes at least security algorithms to be used on the SRBs. The SecurityModeCommand message may also comprise an instruction to derive the keys. The access node receives a PDU session setup command from the network (block 507). The PDU session setup command may be received from an AMF, for example. The PDU session setup command includes security parameters for one or more DRBs associated with the PDU session. The access node sends a connection configuration message (such as a RRCConnectionReconfiguration message) to the UE (block 509). The connection configuration message starts one or more DRBs associated with a PDU session at the UE. The connection configuration message may include security parameters for the one or more DRBs. The access node participates in initiating security on the one or more DRBs (block 511). In a situation where one or more additional DRBs are added to the PDU session, the access node may send an additional connection configuration message (such as a RRCConnectionReconfiguration message) to the UE (block 513). The additional connection configuration message starts one or more additional DRBs associated with the PDU session at the UE. The additional connection configuration message may include security parameters for the one or more additional DRBs, where at least some of the security parameters included with the additional connection configuration message are the same as the corresponding security parameters included with the connection configuration message sent in block 509. The access node participates in initiating security on the one or more additional DRBs (block 515).
[0062] Additionally, the access node may receive a further PDU session setup command from the network, where the further PDU session setup command includes security parameters for one or more DRBs associated with the further PDU session. The access node may send a further connection configuration message (such as a RRCConnectionReconfiguration message) to the UE. The further connection configuration message starts one or more DRBs associated with a further PDU session at the UE. The connection configuration message may include security parameters for the one or more DRBs.
[0063] FIG. 6 illustrates an example communication system 600. In general, the system 600 enables multiple wireless or wired users to transmit and receive data and other content. The system 600 may implement one or more channel access methods, such as code division multiple access (CDMA), time division multiple access (TDMA), frequency division multiple access (FDMA), orthogonal FDMA (OFDMA), single-carrier FDMA (SC-FDMA), or non-orthogonal multiple access (NOMA).
[0064] In this example, the communication system 600 includes electronic devices (ED) 610a-610c, radio access networks (RANs) 620a-620b, a core network 630, a public switched telephone network (PSTN) 640, the Internet 650, and other networks 660. While certain numbers of these components or elements are shown in FIG. 6, any number of these components or elements may be included in the system 600.
[0065] The EDs 610a-610c are configured to operate or communicate in the system 600. For example, the EDs 610a-610c are configured to transmit or receive via wireless or wired communication channels. Each ED 610a-610c represents any suitable end user device and may include such devices (or may be referred to) as a user equipment or device (UE), wireless transmit or receive unit (WTRU), mobile station, fixed or mobile subscriber unit, cellular telephone, personal digital assistant (PDA), smartphone, laptop, computer, touchpad, wireless sensor, or consumer electronics device.
[0066] The RANs 620a-620b here include base stations 670a-670b, respectively. Each base station 670a-670b is configured to wirelessly interface with one or more of the EDs 610a-610c to enable access by the EDs to the core network 630, the PSTN 640, the Internet 650, or the other networks 660. For example, the base stations 670a-670b may include (or be) one or more of several well-known devices, such as a base transceiver station (BTS), a Node-B (NodeB), an evolved NodeB (eNodeB), a Home NodeB, a Home eNodeB, a site controller, an access point (AP), or a wireless router. The EDs 610a-610c are configured to interface and communicate with the Internet 650 and may access the core network 630, the PSTN 640, or the other networks 660.
[0067] In the embodiment shown in FIG. 6, the base station 670a forms part of the RAN 620a, which may include other base stations, elements, or devices. Also, the base station 670b forms part of the RAN 620b, which may include other base stations, elements, or devices. Each base station 670a-670b operates to transmit or receive wireless signals within a particular geographic region or area, sometimes referred to as a "cell." In some embodiments, multiple-input multiple-output (MIMO) technology may be employed having multiple transceivers for each cell.
[0068] The base stations 670a-670b communicate with one or more of the EDs 610a-610c over one or more air interfaces 690 using wireless communication links. The air interfaces 690 may utilize any suitable radio access technology.
[0069] It is contemplated that the system 600 may use multiple channel access functionality, including such schemes as described above. In particular embodiments, the base stations and EDs implement NR, LTE, LTE-A, or LTE-B. Of course, other multiple access schemes and wireless protocols may be utilized.
[0070] The RANs 620a-620b are in communication with the core network 630 to provide the EDs 610a-610c with voice, data, application, Voice over Internet Protocol (VoIP), or other services. Understandably, the RANs 620a-620b or the core network 630 may be in direct or indirect communication with one or more other RANs (not shown). The core network 630 may also serve as a gateway access for other networks (such as the PSTN 640, the Internet 650, and the other networks 660). In addition, some or all of the EDs 610a-610c may include functionality for communicating with different wireless networks over different wireless links using different wireless technologies or protocols. Instead of wireless communication (or in addition thereto), the EDs may communicate via wired communication channels to a service provider or switch (not shown), and to the Internet 650.
[0071] Although FIG. 6 illustrates one example of a communication system, various changes may be made to FIG. 6. For example, the communication system 600 could include any number of EDs, base stations, networks, or other components in any suitable configuration.
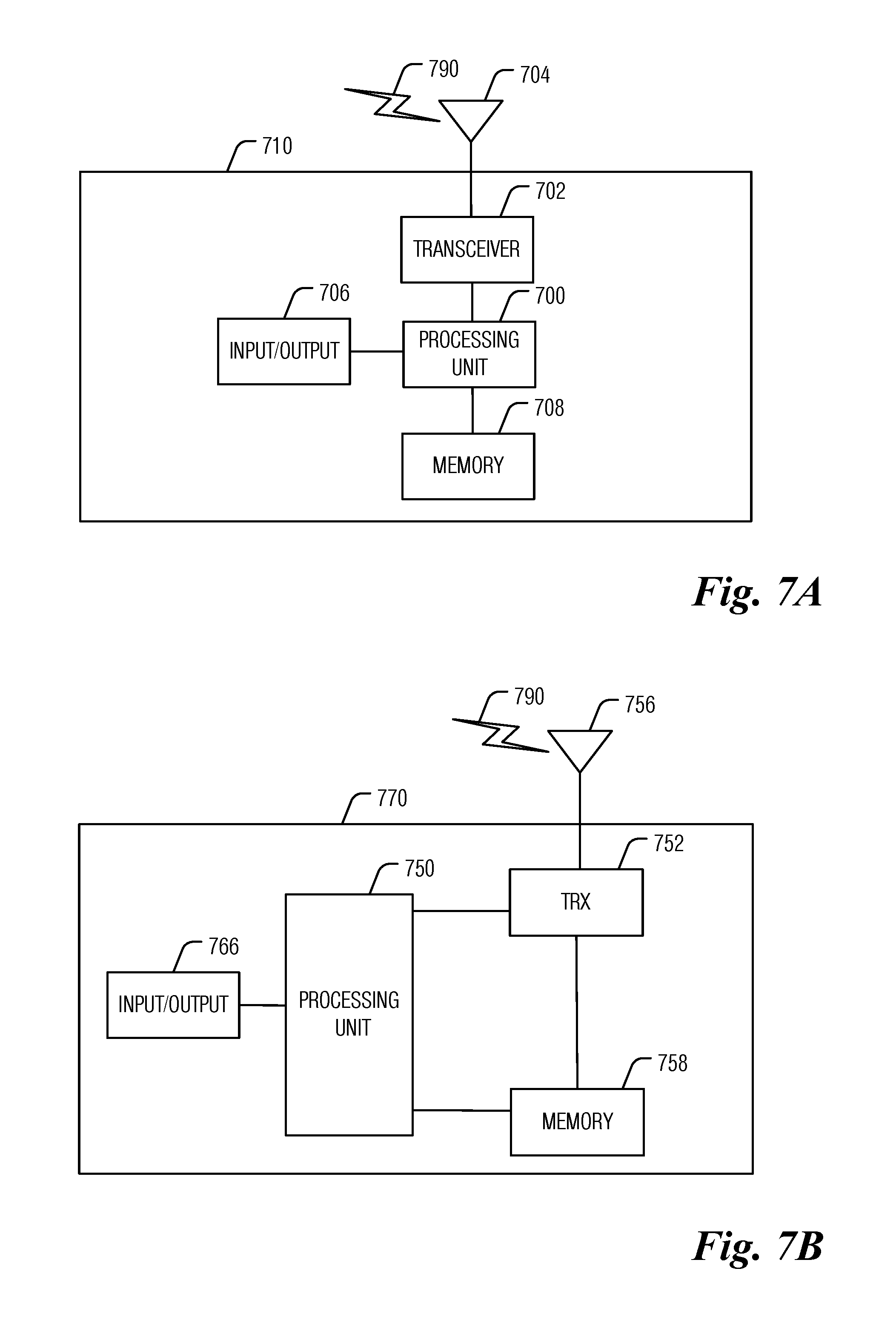
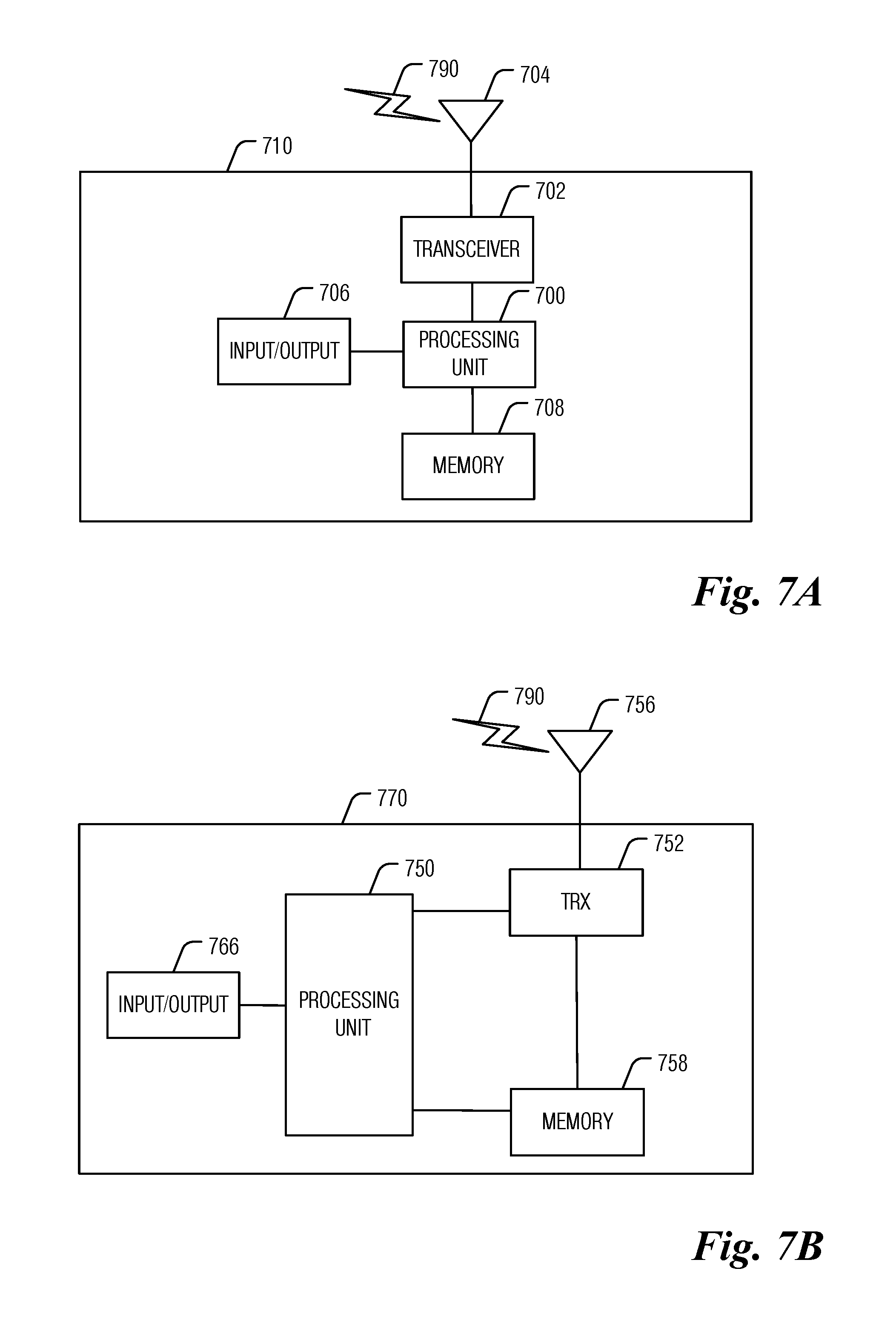
[0072] FIGS. 7A and 7B illustrate example devices that may implement the methods and teachings according to this disclosure. In particular, FIG. 7A illustrates an example ED 710, and FIG. 7B illustrates an example base station 770. These components could be used in the system 600 or in any other suitable system.
[0073] As shown in FIG. 7A, the ED 710 includes at least one processing unit 700. The processing unit 700 implements various processing operations of the ED 710. For example, the processing unit 700 could perform signal coding, data processing, power control, input or output processing, or any other functionality enabling the ED 710 to operate in the system 600. The processing unit 700 also supports the methods and teachings described in more detail above. Each processing unit 700 includes any suitable processing or computing device configured to perform one or more operations. Each processing unit 700 could, for example, include a microprocessor, microcontroller, digital signal processor, field programmable gate array, or application specific integrated circuit.
[0074] The ED 710 also includes at least one transceiver 702. The transceiver 702 is configured to modulate data or other content for transmission by at least one antenna or NIC (Network Interface Controller) 704. The transceiver 702 is also configured to demodulate data or other content received by the at least one antenna 704. Each transceiver 702 includes any suitable structure for generating signals for wireless or wired transmission or processing signals received wirelessly or by wire. Each antenna 704 includes any suitable structure for transmitting or receiving wireless or wired signals. One or multiple transceivers 702 could be used in the ED 710, and one or multiple antennas 704 could be used in the ED 710. Although shown as a single functional unit, a transceiver 702 could also be implemented using at least one transmitter and at least one separate receiver.
[0075] The ED 710 further includes one or more input or output devices 706 or interfaces (such as a wired interface to the Internet 650). The input or output devices 706 facilitate interaction with a user or other devices (network communications) in the network. Each input or output device 706 includes any suitable structure for providing information to or receiving or providing information from a user, such as a speaker, microphone, keypad, keyboard, display, or touch screen, including network interface communications.
[0076] In addition, the ED 710 includes at least one memory 708. The memory 708 stores instructions and data used, generated, or collected by the ED 710. For example, the memory 708 could store software or firmware instructions executed by the processing unit(s) 700 and data used to reduce or eliminate interference in incoming signals. Each memory 708 includes any suitable volatile or non-volatile storage and retrieval device(s). Any suitable type of memory may be used, such as random access memory (RAM), read only memory (ROM), hard disk, optical disc, subscriber identity module (SIM) card, memory stick, secure digital (SD) memory card, and the like.
[0077] As shown in FIG. 7B, the base station 770 includes at least one processing unit 750, at least one transceiver 752, which includes functionality for a transmitter and a receiver, one or more antennas 756, at least one memory 758, and one or more input or output devices or interfaces 766. A scheduler, which would be understood by one skilled in the art, is coupled to the processing unit 750. The scheduler could be included within or operated separately from the base station 770. The processing unit 750 implements various processing operations of the base station 770, such as signal coding, data processing, power control, input or output processing, or any other functionality. The processing unit 750 can also support the methods and teachings described in more detail above. Each processing unit 750 includes any suitable processing or computing device configured to perform one or more operations. Each processing unit 750 could, for example, include a microprocessor, microcontroller, digital signal processor, field programmable gate array, or application specific integrated circuit.
[0078] Each transceiver 752 includes any suitable structure for generating signals for wireless or wired transmission to one or more EDs or other devices. Each transceiver 752 further includes any suitable structure for processing signals received wirelessly or by wire from one or more EDs or other devices. Although shown combined as a transceiver 752, a transmitter and a receiver could be separate components. Each antenna 756 includes any suitable structure for transmitting or receiving wireless or wired signals. While a common antenna 756 is shown here as being coupled to the transceiver 752, one or more antennas 756 could be coupled to the transceiver(s) 752, allowing separate antennas 756 to be coupled to the transmitter and the receiver if equipped as separate components. Each memory 758 includes any suitable volatile or non-volatile storage and retrieval device(s). Each input or output device 766 facilitates interaction with a user or other devices (network communications) in the network. Each input or output device 766 includes any suitable structure for providing information to or receiving or providing information from a user, including network interface communications.
[0079] FIG. 8 is a block diagram of a computing system 800 that may be used for implementing the devices and methods disclosed herein. For example, the computing system can be any entity of UE, access network (AN), mobility management (MM), session management (SM), user plane gateway (UPGW), or access stratum (AS). Specific devices may utilize all of the components shown or only a subset of the components, and levels of integration may vary from device to device. Furthermore, a device may contain multiple instances of a component, such as multiple processing units, processors, memories, transmitters, receivers, etc. The computing system 800 includes a processing unit 802. The processing unit includes a central processing unit (CPU) 814, memory 808, and may further include a mass storage device 804, a video adapter 810, and an I/O interface 812 connected to a bus 820.
[0080] The bus 820 may be one or more of any type of several bus architectures including a memory bus or memory controller, a peripheral bus, or a video bus. The CPU 814 may comprise any type of electronic data processor. The memory 808 may comprise any type of non-transitory system memory such as static random access memory (SRAM), dynamic random access memory (DRAM), synchronous DRAM (SDRAM), read-only memory (ROM), or a combination thereof. In an embodiment, the memory 808 may include ROM for use at boot-up, and DRAM for program and data storage for use while executing programs.
[0081] The mass storage 804 may comprise any type of non-transitory storage device configured to store data, programs, and other information and to make the data, programs, and other information accessible via the bus 820. The mass storage 804 may comprise, for example, one or more of a solid state drive, hard disk drive, a magnetic disk drive, or an optical disk drive.
[0082] The video adapter 810 and the I/O interface 812 provide interfaces to couple external input and output devices to the processing unit 802. As illustrated, examples of input and output devices include a display 818 coupled to the video adapter 810 and a mouse, keyboard, or printer 816 coupled to the I/O interface 812. Other devices may be coupled to the processing unit 802, and additional or fewer interface cards may be utilized. For example, a serial interface such as Universal Serial Bus (USB) (not shown) may be used to provide an interface for an external device.
[0083] The processing unit 802 also includes one or more network interfaces 806, which may comprise wired links, such as an Ethernet cable, or wireless links to access nodes or different networks. The network interfaces 806 allow the processing unit 802 to communicate with remote units via the networks. For example, the network interfaces 806 may provide wireless communication via one or more transmitters or transmit antennas and one or more receivers or receive antennas. In an embodiment, the processing unit 802 is coupled to a local-area network 822 or a wide-area network for data processing and communications with remote devices, such as other processing units, the Internet, or remote storage facilities.
[0084] It should be appreciated that one or more steps of the embodiment methods provided herein may be performed by corresponding units or modules. For example, a signal may be transmitted by a transmitting unit or a transmitting module. A signal may be received by a receiving unit or a receiving module. A signal may be processed by a processing unit or a processing module. Other steps may be performed by a deriving unit or module, or an initiating unit or module. The respective units or modules may be hardware, software, or a combination thereof. For instance, one or more of the units or modules may be an integrated circuit, such as field programmable gate arrays (FPGAs) or application-specific integrated circuits (ASICs).
[0085] Although the present disclosure and its advantages have been described in detail, it should be understood that various changes, substitutions and alterations can be made herein without departing from the spirit and scope of the disclosure as defined by the appended claims.
* * * * *
D00000
D00001

D00002

D00003

D00004

D00005

D00006
XML
uspto.report is an independent third-party trademark research tool that is not affiliated, endorsed, or sponsored by the United States Patent and Trademark Office (USPTO) or any other governmental organization. The information provided by uspto.report is based on publicly available data at the time of writing and is intended for informational purposes only.
While we strive to provide accurate and up-to-date information, we do not guarantee the accuracy, completeness, reliability, or suitability of the information displayed on this site. The use of this site is at your own risk. Any reliance you place on such information is therefore strictly at your own risk.
All official trademark data, including owner information, should be verified by visiting the official USPTO website at www.uspto.gov. This site is not intended to replace professional legal advice and should not be used as a substitute for consulting with a legal professional who is knowledgeable about trademark law.