Identification method of an entity
Bringer , et al.
U.S. patent number 10,230,724 [Application Number 15/353,633] was granted by the patent office on 2019-03-12 for identification method of an entity. This patent grant is currently assigned to IDEMIA IDENTITY & SECURITY. The grantee listed for this patent is Safran Identity & Security. Invention is credited to Julien Bringer, Herve Chabanne, Roch Olivier Lescuyer De Chaptal-Lamure, Eduardo Soria-Vazquez.












View All Diagrams
| United States Patent | 10,230,724 |
| Bringer , et al. | March 12, 2019 |
Identification method of an entity
Abstract
A biometric identification method of an entity including computation of a matching value between biometric data of an entity u and reference biometric data u', by application of a function F to the biometric data. A non-interactive, publicly verifiable computation method is performed wherein representation of the function is obtained by converting an arithmetic circuit into a polynomial representation. A matching value is obtained by evaluating the arithmetic circuit and the reference biometric data as inputs. Proof of correction of the computation execution of the matching values is obtained. Verification of said received proof. The function is encoded with an integer k>1 of a vector of a biometric datum on at least one input wire of the circuit. The function includes at least m scalar products. Evaluation of the circuit is iteratively computed depending on the value of m.
| Inventors: | Bringer; Julien (Issy les Moulineaux, FR), Lescuyer De Chaptal-Lamure; Roch Olivier (Issy les Moulineaux, FR), Chabanne; Herve (Issy les Moulineaux, FR), Soria-Vazquez; Eduardo (Issy les Moulineaux, FR) | ||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|
| Applicant: |
|
||||||||||
| Assignee: | IDEMIA IDENTITY & SECURITY
(Issy les Moulineaux, FR) |
||||||||||
| Family ID: | 55646697 | ||||||||||
| Appl. No.: | 15/353,633 | ||||||||||
| Filed: | November 16, 2016 |
Prior Publication Data
| Document Identifier | Publication Date | |
|---|---|---|
| US 20170142103 A1 | May 18, 2017 | |
Foreign Application Priority Data
| Nov 16, 2015 [FR] | 15 60942 | |||
| Current U.S. Class: | 1/1 |
| Current CPC Class: | H04L 9/3231 (20130101); G06F 17/10 (20130101); H04L 9/3218 (20130101); H04L 63/0861 (20130101); H04L 63/0442 (20130101); G06F 21/32 (20130101); H04L 63/061 (20130101); H04L 9/0869 (20130101); H04L 2209/76 (20130101); H04L 2209/46 (20130101) |
| Current International Class: | H04L 29/06 (20060101); G06F 17/10 (20060101); G06F 21/32 (20130101); H04L 9/32 (20060101); H04L 9/08 (20060101) |
| Field of Search: | ;713/171 |
References Cited [Referenced By]
U.S. Patent Documents
| 2009/0022374 | January 2009 | Boult |
| 2010/0317420 | December 2010 | Hoffberg |
| 2016/0381003 | December 2016 | Caceres |
| 2017/0185761 | June 2017 | Stanwood |
Other References
|
Ben-Sasson et al. "Secure Sampling of Public Parameters for Succinct Zero Knowledge Proofs" Sep. 25, 2015; 2015 IEEE Symposium on Security and Privacy, pp. 287-304 (Year: 2015). cited by examiner . French Search Report with English Language Translation Cover Sheet dated Jul. 27, 2016, FR Application No. 1560942. cited by applicant . Anonymous, "Efficient Way to Multiply a Large Set of Small Numbers", Stack Overflow Site, Apr. 2014, pp. 5-8. cited by applicant . Barni, Mauro, et al., "Privacy Protection in Biometric-Based Recognition Systems: A Marriage between Cryptography and Signal Processing", IEEE Signal Processing Magazine, vol. 32, No. 5, Sep. 2015, pp. 70-76. cited by applicant . Bringer, Julien, et al., "Gshade: Faster Privacy-Preserving Distance Computation and Biometric Identification", Proceedings of the 2nd ACM Workshop on Information Hiding and Multimedia Security, IH&MMSEC '14, Jun. 2014, pp. 191-198. cited by applicant . Bringer, Julien, et al., "Privacy-Preserving Biometric Identification Using Secure Multiparty Computation: An Overview and Recent Trends", IEEE Signal Processing Magazine, IEEE Service Center, Piscataway, NJ, US, vol. 30, No. 2, Mar. 2013, pp. 46-52. cited by applicant . Bringer, Julien, et al., "Some Applications of Verifiable Computation to Biometric Verification", 2015 IEEE International Workshop on Information Forensics and Security (WIFS), IEEE, Nov. 2015, pp. 5-6. cited by applicant . Costello, Craig, et al., "Geppetto: Versatile Verifiable Computation", International Association for Cryptologic Research, vol. 20141201:093827, Nov. 2014, pp. 5-21. cited by applicant . Parno, Bryan, et al., "Pinnocchio: Nearly Practical Verifiable Computation", Security and Privacy (SP), 2013 IEEE Symposium on, IEEE, May 2013, pp. 238-252. cited by applicant . Upmanyu, Maneesh, et al., "Efficient Biometric Verification in Encrypted Domain", Advances in Biometrics, Springer Berlin Heidelberg, Berlin, Heidelberg, Jun. 2009, pp. 903-908. cited by applicant . Walfish, Michael, et al., "Verifying Computations without Reexecuting Them", Communications of the ACM, Association for Computing Machinery, Inc, United States, vol. 58, No. 2, Jan. 2015, pp. 78-84. cited by applicant. |
Primary Examiner: Naghdali; Khalil
Attorney, Agent or Firm: Womble Bond Dickinson (US) LLP
Claims
The invention claimed is:
1. A biometric identification method of an entity, by a biometric identification system comprising a client device and a remote computation device, comprising: computation of at least one matching value between at least one biometric datum of the entity u and at least one reference biometric datum u', by application of a function F to said biometric data, each of said data being a vector of N binary integers u.sub.i or u'.sub.i with 1.ltoreq.i.ltoreq.N, each integer being coded on n bits, said function F comprising a scalar product between a biometric datum of the entity and a reference biometric datum, said computation performing a non-interactive, publicly verifiable computation method comprising steps of: representation of said function F in form of an arithmetic circuit comprising wires transporting values of finite prime field .sub.q, with q a prime number, and connecting addition and multiplication operators, conversion of said arithmetic circuit into a polynomial representation, QAP (Quadratic Arithmetic Program) or multi-QAP, generation of a public evaluation key and of a public verification key as a function of said polynomial representation, obtaining by the remote computation device of the arithmetic circuit and of the public evaluation key, for each biometric datum of the entity, determination of at least one matching value between said biometric datum and at least one reference biometric datum by the remote computation device by evaluating the arithmetic circuit having as inputs the biometric datum of the entity and the reference biometric datum, for each determined matching value, generation by the remote computation device of a proof of correction of computation execution of matching value, so-called generated proof, from said polynomial representation, the public evaluation key and result of the evaluation of the arithmetic circuit, transmission by the remote computation device of matching values and generated proofs to the client device, verification of said generated proofs received by the client device by means of the public verification key, identification of the entity by the client device as the function of the matching values and result of said verification of the generated proofs, wherein: representation of said function F comprises encoding an integer k>1 of binary integers of a vector of a biometric datum on at least one input wire of the arithmetic circuit, and the function F comprising at least m scalar products, m being a divider of length N of biometric data vectors, if the divider m is equal to 2 or 3, the arithmetic circuit comprises at least N/(k*m) multiplication operators connected to input wires of the arithmetic circuit, a storage memory, and at least one addition operator, and evaluation of the arithmetic circuit iteratively comprises computation of each of the m scalar products by means of said N/(k*m) multiplication operators, storage of m results of computations of said scalar products in said storage memory and summation of said results by means of said addition operator, if the divider m is greater than or equal to 4, the arithmetic circuit comprises at least one first computation sub-circuit of the scalar product comprising N/(k*m) first multiplication operators connected to input wires of the arithmetic circuit and a first storage memory, and a second computation sub-circuit of the scalar product comprising N/(k*m) second multiplication operators connected to the input wires of the arithmetic circuit and a second storage memory, each one of said first and second computation sub-circuits being also connected to an output of the storage memory of the other one of said first and second computation sub-circuits, and evaluation of the arithmetic circuit iteratively comprises computation of each of the m scalar products by using alternatively one of said first and second computation sub-circuit to compute sum of the scalar product of values of the input wires of the used one of said first and second computation sub-circuits and value stored in the storage memory of the other one of said first and second computation sub-circuits, wherein said biometric identification method delegates to a remote entity a comparison of biometric datum in terms of a protocol of verifiable computations suitable for a real-time execution.
2. The identification method according to claim 1, wherein the verification of said received proofs comprises batch verification of pairings.
3. The identification method according to claim 1, wherein: if the divider m of the length N of the biometric data vectors is equal to 1, given an asymmetric bilinear environment (q, G.sub.1, G.sub.2, G.sub.T, g.sub.1, g.sub.2, e) where q is a prime number G.sub.1, G.sub.2 and G.sub.T three groups of order q, g.sub.1 a generator of G.sub.1, g.sub.2 a generator of G.sub.2, and e a non-degenerate bilinear pairing e: G.sub.1.times.G.sub.2.fwdarw.G.sub.T and the arithmetic circuit being represented in form of a QAP of the circuit Q=(t, V, W, Y) of size .rho. and degree .delta., with V={vi}, W={wi}, Y={yi}, 0.ltoreq.i.ltoreq..rho., and given I.sub.io={1, . . . , .theta.} set of indices corresponding to input/output wires of the arithmetic circuit and I.sub.mid={.theta.+1, . . . , .rho.} set of indices of intermediate wires of the arithmetic circuit not being input wires of the arithmetic circuit, the generation of the public evaluation key and of the public verification key comprises: generation of random variables r.sub.v, r.sub.w, s, .alpha..sub.v, .alpha..sub.w, .alpha..sub.y, .beta., .gamma. in .sub.q, definition of coefficients r.sub.y=r.sub.vr.sub.w, g.sub.v1=g.sub.1.sup.r.sup.v, g.sub.w1=g.sub.1.sup.r.sup.w, g.sub.w2=g.sub.2.sup.r.sup.w, g.sub.y1=g.sub.1.sup.r.sup.y and g.sub.y2=g.sub.2.sup.r.sup.y, generation of public evaluation key EK.sub.F equal to (EK.sub.F1, EK.sub.F2) where .times..times..times..times..function..di-elect cons..times..times..function..di-elect cons..times..times..function..di-elect cons..times..times..alpha..function..di-elect cons..times..times..alpha..function..di-elect cons..times..times..alpha..function..di-elect cons..di-elect cons..delta..times..times..beta..function..times..times..beta..function..- times..times..beta..function..di-elect cons. ##EQU00035## .times..times..times..times..function..di-elect cons. ##EQU00035.2## generation of public verification key VK.sub.F equal to (VK.sub.F1, VK.sub.F2) where: VK.sub.F1=(g.sub.1,{g.sub.v1.sup.v.sup.i.sup.(s)}.sub.i.di-elect cons.[1,.theta.],{g.sub.y1.sup.y.sup.i.sup.(s)}.sub.i.di-elect cons.[1,.theta.]) VK.sub.F2=(g.sub.2,g.sub.2.sup..alpha..sup.v,g.sub.2.sup..alpha..sup.w,g.- sub.2.sup..alpha..sup.y,g.sub.2.sup..gamma.,g.sub.2.sup..beta..gamma.,g.su- b.y2.sup.t(s),{g.sub.w2.sup.w.sup.i.sup.(s)}.sub.i.di-elect cons.[1,.theta.]) generation by the remote computation device of the proof of correction of the computation execution of a matching value comprises, {c.sub.i}.sub.i.di-elect cons.[1,.rho.] being set of values of the arithmetic circuit determined during determination of the determined matching value: determination of a polynomial h(x) such that p(x)=h(x)t(x) with p(x)=(v.sub.0(x)+.SIGMA..sub.i=1.sup..rho.c.sub.iv.sub.i (x))(w.sub.0(x)+.SIGMA..sub.i=1.sup..rho.c.sub.iw.sub.i(x))-(y.sub.0(x)+.- SIGMA..sub.i=1.sup..rho.c.sub.iy.sub.i(x)), computation of generated proof .pi.=(.pi..sub.1, .pi..sub.2) with: .pi..times..times..function..times..times..function..times..times..functi- on..function..times..times..alpha..function..times..times..alpha..function- ..times..times..alpha..function..times..times..beta..function..times..time- s..beta..function..times..times..beta..function..times..pi..times..times..- function. ##EQU00036## where: v.sub.mid(x)=.SIGMA..sub.i.di-elect cons.I.sub.midc.sub.iv.sub.i(x),w.sub.mid(x)=.SIGMA..sub.i.di-elect cons.I.sub.midc.sub.iw.sub.i(x) and y.sub.mid(x)=.SIGMA..sub.i.di-elect cons.I.sub.midc.sub.iy.sub.i(x), and, wherein said proofs received by the client device being equal to (.pi..sub.r1, .pi..sub.r2) with .pi..sub.r1 in form of: (g.sub.v1.sup.V.sup.mid, g.sub.w1.sup.W.sup.mid, g.sub.y1.sup.Y.sup.mid, g.sub.1.sup.H, g.sub.v1.sup.V'.sup.mid, g.sub.w1.sup.W'.sup.mid, g.sub.y1.sup.Y'.sup.mid, g.sub.1.sup.Z) and .pi..sub.r2 in the form g.sub.w2.sup.w.sup.mid, the verification of a received proof comprises performing following equality tests: e(g.sub.v1.sup.v.sup.o.sup.(s)g.sub.v1.sup.v.sup.io.sup.(s)g.sub.v1.sup.V- .sup.mid,g.sub.w2.sup.w.sup.o.sup.(s)g.sub.w2.sup.w.sup.io.sup.(s)g.sub.w2- .sup.W.sup.mid)=e(g.sub.1.sup.H,g.sub.y2.sup.t(s))e(g.sub.y1.sup.y.sup.o.s- up.(s)g.sub.y1.sup.y.sup.io.sup.(s)g.sub.y1.sup.Y.sup.mid,g.sub.2), e((g.sub.v1.sup.V'.sup.mid).sup.d.sup.1(g.sub.w1.sup.W'.sup.mid).sup.d.su- p.2(g.sub.y1.sup.Y'.sup.mid).sup.d.sup.3,g.sub.2)=e((g.sub.v1.sup.V.sup.mi- d).sup.d.sup.1,g.sub.2.sup..alpha..sup.v)e((g.sub.w1.sup.W.sup.mid).sup.d.- sup.2,g.sub.2.sup..alpha..sup.w)e((g.sub.y1.sup.Y.sup.mid).sup.d.sup.3,g.s- ub.2.sup..alpha..sup.y),e((g.sub.1.sup.Z,g.sub.2.sup..gamma.)=e(g.sub.v1.s- up.V.sup.midg.sub.w1.sup.W.sup.midg.sub.y1.sup.Y.sup.mid,g.sub.2.sup..beta- ..gamma.) where g.sub.v1.sup.v.sup.io.sup.(s)=.PI..sub.i=1.sup..theta.(g.sub.v1.sup.v.sup- .i.sup.(s)).sup.c.sup.i, g.sub.w1.sup.w.sup.io.sup.(s)=.PI..sub.i=1.sup..theta.(g.sub.w1.sup.w.sup- .i.sup.(s)).sup.c.sup.i, and g.sub.y1.sup.y.sup.io.sup.(s)=.PI..sub.i=1.sup..theta.(g.sub.y1.sup.y.sup- .i.sup.(s)).sup.c.sup.i and (d.sub.1, d.sub.2, d.sub.3) elements of .sub.q on .lamda. bits with .lamda. a security parameter.
4. The identification method according to claim 1 wherein: if the divider m of the length N of the biometric data vectors is greater than or equal to 2, given an asymmetric bilinear environment (q, G.sub.1, G.sub.2, G.sub.T, g.sub.1, g.sub.2, e) where q is a prime number G.sub.1, G.sub.2 and G.sub.T three groups of order q, g.sub.1 a generator of G.sub.1, g.sub.2 a generator of G.sub.2, and e a non-degenerate bilinear pairing e: G.sub.1.times.G.sub.2.fwdarw.G.sub.T, the arithmetic circuit being represented in form of a multi-QAP Q=({B.sub.b}.sub.b.di-elect cons.[1,l],t,V,W, of size .rho. and degree .delta., with {B.sub.b}.sub.b.di-elect cons.[1,l] a set of l banks B.sub.b of Q used in the computation of the function F, and V={vi}, W={wi}, Y={yi} with 0.ltoreq.i.ltoreq..rho., the generation of the public evaluation key and of the public verification key comprises: generation of random variables s, {(.alpha..sub.bv, .alpha..sub.bw, .alpha..sub.by, .beta..sub.b,.gamma..sub.b)}.sub.b.di-elect cons.[1,l], r.sub.v, r.sub.w in .sub.q, definition of following coefficients: r.sub.y=r.sub.yr.sub.w, g.sub.v1=g.sub.1.sup.r.sup.v, g.sub.v2=g.sub.2.sup.r.sup.v, g.sub.w1=g.sub.1.sup.r.sup.w, g.sub.w2=g.sub.2.sup.r.sup.w, g.sub.y1=g.sub.1.sup.r.sup.y and g.sub.y2=g.sub.2.sup.r.sup.y, generation of public evaluation key EK.sub.F equal to: ({EK.sub.Fb}.sub.b.di-elect cons.[1,l],{g.sub.1.sup.s.sup.i}.sub.i.di-elect cons.[1,.delta.],g.sub.v1.sup.t(s),g.sub.w1.sup.t(s),g.sub.y1.sup.t(s),g.- sub.v2.sup.t(s),g.sub.w2.sup.t(s),g.sub.y2.sup.t(s)) where each public bank key EK.sub.Fb is equal to (EK.sub.Fb1, EK.sub.Fb2) with: .times..times..times..times..function..times..times..function..times..tim- es..function..times..times..alpha..function..times..times..alpha..function- ..times..times..alpha..function..times..times..beta..function..times..time- s..beta..function..times..times..beta..function..di-elect cons..times..times..alpha..function..times..times..alpha..function..times- ..times..alpha..function..times..times..beta..function..times..times..beta- ..function..times..times..beta..function. ##EQU00037## EK.sub.Fb2=({g.sub.w2.sup.w.sup.i.sup.(s)}.sub.i.di-elect cons.B.sub.b,g.sub.w2.sup..alpha..sup.bw.sup.,t(s)) generation of the public verification key VK.sub.F equal to: ({VK.sub.Fb}.sub.b.di-elect cons.[1,l], g.sub.1, g.sub.2, g.sub.y2.sup.t(s)) where each public bank key VK.sub.Fb is equal to (g.sub.2.sup..alpha..sup.bv, g.sub.2.sup..alpha..sup.bw, g.sub.2.sup..alpha..sup.by, g.sub.2.sup..gamma..sup.b, g.sub.2.sup..beta..sup.b.sup..gamma..sup.b), determination of a matching value comprises, function F being divided into .omega. sub-functions F.sub.1, . . . , F.sub..omega. and .sigma.=((f.sub.l, (T.sub.l1, . . . , T.sub.ll))).sub.l.di-elect cons.[1,L] being a scheduling of length L with f.sub.l .di-elect cons.{1, . . . , .omega.}, evaluation of each sub-function F.sub..omega. from the biometric data of the entity and the reference biometric data and determination of the values of the arithmetic circuit, generation by the remote computation device of the proof of correction of the computation execution of a matching value comprises, for each l={1, . . . , L}: for each bank B.sub.b such that b.di-elect cons..LAMBDA., with .LAMBDA.[1,l] set of indices b.di-elect cons.[1,l] such that T.sub.lb.noteq.0,.GAMMA.=U.sub.b.di-elect cons..LAMBDA.B.sub.b, {c.sub.j}.sub.j.di-elect cons.B.sub.b an instance of bank B.sub.b, .DELTA.={c.sub.i}.sub.i.di-elect cons..GAMMA. set of values of .GAMMA.: generation of pledging random variables in .sub.q: o.sub.b=(o.sub.bv, o.sub.bw, o.sub.by), computation of a digest D.sub.b equal to (D.sub.b1,D.sub.b2) from the instance of the bank B.sub.b: B.sub.b.sup.(T.sup.lb.sup.)={c.sub.i.di-elect cons..DELTA.}.sub.i.di-elect cons.B.sub.b and pledging random variables o.sub.b and such that: if the bank B.sub.b is an input/output bank: D.sub.b1=(g.sub.v1.sup.v.sup.(b).sup.(s),g.sub.y1.sup.y.sup.(b).sup.(s)) and D.sub.b2=(g.sub.w2.sup.w.sup.(b).sup.(s)), if the bank B.sub.b is not input/output bank: .times..times..times..times..function..times..times..function..times..tim- es..function..times..times..alpha..function..times..times..alpha..function- ..times..times..alpha..function..times..times..beta..function..times..time- s..beta..function..times..times..beta..function. ##EQU00038## .times..times..times..times..function. ##EQU00038.2## with: v.sup.(b)(s)=.SIGMA..sub.i.di-elect cons.B.sub.bc.sub.iv.sub.i(s)+o.sub.bvt(s), w.sup.(b)(s)=.SIGMA..sub.i.di-elect cons.B.sub.bc.sub.iw.sub.i(s)+o.sub.bwt(s), y.sup.(b)(s)=.SIGMA..sub.i.di-elect cons.B.sub.bc.sub.iy.sub.i(s)+o.sub.byt(s), determination of a polynomial h.sup.(l)(x) such that p.sup.(l)(x)=h.sup.(l)(x)t(x) with p.sup.(l)(x)=(v.sub.0(x)+.SIGMA..sub.i.di-elect cons..GAMMA.c.sub.iv.sub.j(x)+.SIGMA..sub.b.di-elect cons..LAMBDA.o.sub.bvt(x))(w.sub.0(x)+.SIGMA..sub.i.di-elect cons..GAMMA.c.sub.iw.sub.j(x)+.SIGMA..sub.b.di-elect cons..LAMBDA.o.sub.bwt(x))-(y.sub.0(x)+.SIGMA..sub.i.di-elect cons..GAMMA.c.sub.iy.sub.j(x)+.SIGMA..sub.b.di-elect cons..LAMBDA.o.sub.byt(x)) computation of a proof element .pi..sup.(l) equal to g.sub.1.sup.h.sup.(l).sup.(s), and, wherein said proofs received by the client device being of the form D.sub.1.sup.(1), . . . , D.sub.l.sup.(1), .pi..sup.(1), . . . , D.sub.1.sup.(L), . . . , D.sub.l.sup.(L), .pi..sup.(L) where for all l.di-elect cons.{1, . . . , L} and b.di-elect cons.{1, . . . ,l}: .times..times..times..times..times..times..times..times.'.times..times..t- imes..times.'.times..times..times..times.'.times..times..times..times. ##EQU00039## and .pi..sup.(l)=g.sub.1.sup.H.sup.(l), verification of the received proof comprises: verification of Ll digests, for l.di-elect cons.{1, . . . , L} and b.di-elect cons.{1, . . . , l} comprising performing following equality tests: .function..times..times.'.times..times..alpha..function..times..times. ##EQU00040## .function..times..times.'.function..alpha..function..times..times. ##EQU00040.2## .function..times..times.'.times..times..alpha..function..times..times. ##EQU00040.3## .function..gamma..function..times..times..times..times..times..times..bet- a..gamma. ##EQU00040.4## verification of L proofs comprising for l.di-elect cons.{1, . . . , L} performing following equality test: .function. .times..times..times. .times..times..times..times..function..times..times..function..function. .times..times..times. ##EQU00041##
5. The identification method according to claim 1 wherein: if the divider m of the length N of the biometric data vectors is greater than or equal to 2, given an asymmetric bilinear environment (q, G.sub.1, G.sub.2, G.sub.T, g.sub.1, g.sub.2, e) where q is a prime number G.sub.1, G.sub.2 and G.sub.T three groups of order q, g.sub.1 a generator of G.sub.1, g.sub.2 a generator of G.sub.2, and e a non-degenerate bilinear pairing e: G.sub.1.times.G.sub.2.fwdarw.G.sub.T, the arithmetic circuit being represented in form of a multi-QAP Q=({B.sub.b}.sub.b.di-elect cons.[1,l], t, V, W, of size .rho. and degree .delta., with {B.sub.b}.sub.b.di-elect cons.[1,l] a set of l banks B.sub.b of Q used in computation of the function F, and V={vi}, W={wi}, Y={yi} with 0.ltoreq.i.ltoreq..rho., the generation of the public evaluation key and the public verification key comprises: generation of random variables s,{(.alpha..sub.bv,.alpha..sub.bw,.alpha..sub.by, .beta..sub.b, .gamma..sub.b)}.sub.b.di-elect cons.[1,l], r.sub.v, r.sub.w in .sub.q, generation of random variables s,{(.alpha..sub.bv, .alpha..sub.bw, .alpha..sub.by, .beta..sub.b, .gamma..sub.b)}.sub.b.di-elect cons.[1,l], r.sub.v, r.sub.w in .sub.q, definition of the following coefficients: r.sub.y=r.sub.br.sub.w, g.sub.v1=g.sub.1.sup.r.sup.v, g.sub.v2=g.sub.2.sup.r.sup.v, g.sub.w1=g.sub.1.sup.r.sup.w, g.sub.w2.sup.r.sup.w=g.sub.2.sup.r.sup.w, g.sub.y1=g.sub.1.sup.r.sup.y and g.sub.y2=g.sub.2.sup.r.sup.y, generation of the public evaluation key EK.sub.F equal to: ({EK.sub.Fb}.sub.b.di-elect cons.[1,l],{g.sub.1.sup.s.sup.i}.sub.i.di-elect cons.[1,.delta.],g.sub.v1.sup.t(s),g.sub.w1.sup.t(s),g.sub.y1.sup.t(s),g.- sub.v2.sup.t(s),g.sub.w2.sup.t(s),g.sub.y2.sup.t(s)) where each public bank key EK.sub.Fb is equal to (EK.sub.Fb1, EK.sub.Fb2) with: .times..times..times..times..function..times..times..function..times..tim- es..function..times..times..alpha..function..times..times..alpha..function- ..times..times..alpha..function..times..times..beta..function..times..time- s..beta..function..times..times..beta..function..di-elect cons..times..times..alpha..function..times..times..alpha..function..times- ..times..alpha..function..times..times..beta..function..times..times..beta- ..function..times..times..beta..function. ##EQU00042## .times..times..times..times..times..function..di-elect cons..times..times..alpha..function. ##EQU00042.2## generation of the public verification key VK.sub.F is equal to: ({VK.sub.Fb}.sub.b.di-elect cons.[1,l], g.sub.1, g.sub.2, g.sub.y2.sup.t(s)) where each public bank key VK.sub.Fb is equal to (g.sub.2.sup..alpha..sup.bv, g.sub.2.sup..alpha..sup.bw, g.sub.2.sup..alpha..sup.by, g.sub.2.sup..gamma..sup.b, g.sub.2.sup..beta..sup.b.sup..gamma..sup.b), determination of the matching value comprises, function F being divided into .omega. sub-functions F.sub.1, . . . , F.sub..omega. and .sigma.=((f.sub.l, (T.sub.l1, . . . , T.sub.ll))).sub.l.di-elect cons.[1,L] being a scheduling of length L with f.sub.l .di-elect cons.{1, . . . , .omega.}, evaluation of each sub-function F.sub..omega. from the biometric data of the entity and the reference biometric data and determination of the determined values of the arithmetic circuit, generation by the remote computation device of the proof of correction of the computation execution of the matching value comprises, for each l={1, . . . , L}: for each bank B.sub.b such that b.di-elect cons..LAMBDA., with .LAMBDA.[1,l] the set of indices b.di-elect cons.[1,l] such that T.sub.lb.noteq.0,.GAMMA.=U.sub.b.di-elect cons..LAMBDA.B.sub.b, {c.sub.j}.sub.j.di-elect cons.B.sub.b an instance of the bank B.sub.b, .DELTA.={c.sub.i}.sub.i.di-elect cons..GAMMA. the set of values of .GAMMA.: generation of pledging random variables in .sub.q: o.sub.b=(o.sub.bv, o.sub.bw, o.sub.by), computation of a digest D.sub.b equal to (D.sub.b1,D.sub.b2) from the instance of the bank B.sub.b: B.sub.b.sup.(T.sup.lb.sup.)={c.sub.i.di-elect cons..DELTA.}.sub.i.di-elect cons.B.sub.b and pledging random variables o.sub.b and such that: if the bank B.sub.b is input/output bank: D.sub.b1=(g.sub.v1.sup.v.sup.(b).sup.(s),g.sub.y1.sup.y.sup.(b).sup.(s)) and D.sub.b2=(g.sub.w2.sup.w.sup.(b).sup.(s)), if the bank B.sub.b is not the input/output bank: .times..times..times..times..function..times..times..function..times..tim- es..function..times..times..alpha..function..times..times..alpha..function- ..times..times..alpha..function..times..times..beta..function..times..time- s..beta..function..times..times..beta..function. ##EQU00043## .times..times..times..times..function. ##EQU00043.2## with: v.sup.(b)(s)=.SIGMA..sub.i.di-elect cons.B.sub.bc.sub.iv.sub.i(s)+o.sub.bvt(s), w.sup.(b)(s)=.SIGMA..sub.i.di-elect cons.B.sub.bc.sub.iw.sub.i(s)+o.sub.bwt(s), y.sup.(b)(s)=.SIGMA..sub.i.di-elect cons.B.sub.bc.sub.iy.sub.i(s)+o.sub.byt(s), determination of a polynomial h.sup.(l)(x) such that p.sup.(l)(x)=h.sup.(l)(x)t(x) with p.sup.(l)(x)=(v.sub.0(x)+.SIGMA..sub.i.di-elect cons..GAMMA.c.sub.iv.sub.j(x)+.SIGMA..sub.b.di-elect cons..LAMBDA.o.sub.bvt(x))(w.sub.0(x)+.SIGMA..sub.i.di-elect cons..GAMMA.c.sub.iw.sub.j(x)+.SIGMA..sub.b.di-elect cons..LAMBDA.o.sub.bwt(x))-(y.sub.0(x)+.SIGMA..sub.i.di-elect cons..GAMMA.c.sub.iy.sub.j(x)+.SIGMA..sub.b.di-elect cons..LAMBDA.o.sub.byt(x)) computation of the proof element .pi..sup.(l) equal to g.sub.1.sup.h.sup.(l).sup.(s), and, wherein said proofs received by the client device being of form D.sub.1.sup.(1), . . . , D.sub.l.sup.(1), .pi..sup.(1), . . . , D.sub.1.sup.(L), . . . , D.sub.l.sup.(L), .pi..sup.(L) where for all l.di-elect cons.{1, . . . , L} and b.di-elect cons.{1, . . . ,l}: .times..times..times..times..times..times..times..times.'.times..times..t- imes..times.'.times..times..times..times.'.times..times..times..times. ##EQU00044## and .pi..sup.(l)=g.sub.1.sup.H.sup.(l), verification of the received proof comprises, given a correction parameter .lamda.: selection of a random vector (d.sub.1, . . . , d.sub.3l) of elements of size .lamda., batch verification of Ll digests comprising performing l times the following equality tests, for b.di-elect cons.{1, . . . , l}: .function..times..times..times.'.times..times..alpha..function..times..ti- mes..times.'.times..times..alpha..function..times..times..times.'.times..t- imes..alpha..function..times..times..times..times..times..times..times..ti- mes..times. ##EQU00045## .times..function..times..gamma..function..times..times..times..times..tim- es..times..times..beta..gamma. ##EQU00045.2## batch verification of the L proofs comprising performing the following equality test: .times..function. .times..times..times..times. .times..times..times..function..times..times..times..function..function..- times. .times..times..times. ##EQU00046##
6. The identification method according to claim 1, wherein the identification of the entity comprises comparison of the matching values with a predetermined threshold.
7. The identification method according to claim 1, wherein the function F comprises comparison of result of the scalar product between said biometric data of the entity and said reference biometric data with a predetermined threshold.
8. The identification method according to claim 1, wherein the encoding of k binary integers u.sub.i or u'.sub.i on an input wire of an j.sup.th multiplication operator, 1.ltoreq.j.ltoreq.N/k, is equal to .times..times..function..times..times..times..times..times..times..functi- on.' ##EQU00047## with 1.ltoreq.z.ltoreq.m, and is given by the formula: .times..function..times..times..times..times. ##EQU00048## with .epsilon..sub.1, . . . , .epsilon..sub.k predetermined integers.
9. A computer program product comprising code instructions for execution of a method according to a biometric identification method of an entity, by a biometric identification system comprising a client device and a remote computation device, comprising: computation of at least one matching value between at least one biometric datum of the entity u and at least one reference biometric datum u', by application of a function F to said biometric data, each of said data being a vector of N binary integers u.sub.i or u'.sub.i with 1.ltoreq.i.ltoreq.N, each integer being coded on n bits, said function F comprising a scalar product between a biometric datum of the entity and a reference biometric datum, said computation performing a non-interactive, publicly verifiable computation method comprising steps of: representation of said function F in form of an arithmetic circuit comprising wires transporting values of finite prime field .sub.q, with q a prime number, and connecting addition and multiplication operators, conversion of said arithmetic circuit into a polynomial representation, QAP (Quadratic Arithmetic Program) or multi-QAP, generation of a public evaluation key and of a public verification key as a function of said polynomial representation, obtaining by the remote computation device of the arithmetic circuit and of the public evaluation key, for each biometric datum of the entity, determination of at least one matching value between said biometric datum and at least one reference biometric datum by the remote computation device by evaluating the arithmetic circuit having as inputs the biometric datum of the entity and the reference biometric datum, for each determined matching value, generation by the remote computation device of a proof of correction of computation execution of matching value, so-called generated proof, from said polynomial representation, the public evaluation key and result of the evaluation of the arithmetic circuit, transmission by the remote computation device of matching values and generated proofs to the client device, verification of said generated proofs received by the client device by means of the public verification key, identification of the entity by the client device as the function of the matching values and result of said verification of the generated proofs, wherein: representation of said function F comprises encoding an integer k>1 of binary integers of a vector of a biometric datum on at least one input wire of the arithmetic circuit, and the function F comprising at least m scalar products, m being a divider of length N of biometric data vectors, if the divider m is equal to 2 or 3, the arithmetic circuit comprises at least N/(k*m) multiplication operators connected to the input wires of the arithmetic circuit, a storage memory, and at least one addition operator, and evaluation of the arithmetic circuit iteratively comprises computation of each of the m scalar products by means of said N/(k*m) multiplication operators, storage of m results of computations of said scalar products in said storage memory and summation of said results by means of said addition operator, if the divider m is greater than or equal to 4, the arithmetic circuit comprises at least one first computation sub-circuit of the scalar product comprising N/(k*m) first multiplication operators connected to input wires of the arithmetic circuit and a first storage memory, and a second computation sub-circuit of the scalar product comprising N/(k*m) second multiplication operators connected to the input wires of the arithmetic circuit and a second storage memory, each one of said first and second computation sub-circuits being also connected to an output of the storage memory of the other one of said first and second computation sub-circuits, and evaluation of the arithmetic circuit iteratively comprises computation of each of the m scalar products by using alternatively one of said first and second computation sub-circuit to compute sum of the scalar product of values of the input wires of the used one of said first and second computation sub-circuits and value stored in the storage memory of the other one of said first and second computation sub-circuits, wherein said biometric identification method delegates to a remote entity a comparison of biometric datum in terms of a protocol of verifiable computations suitable for a real-time execution, when said computer program product is executed by a processor.
10. A biometric identification system comprising a client device and a remote computation device wherein: said client device and said remote computation device each comprise a processor, an interface and a memory for performing steps of an identification method according to a biometric identification method of an entity, by a biometric identification system comprising a client device and a remote computation device, comprising: computation of at least one matching value between at least one biometric datum of the entity u and at least one reference biometric datum u', by application of a function F to said biometric data, each of said data being a vector of N binary integers u.sub.i or u'.sub.i with 1.ltoreq.i.ltoreq.N, each integer being coded on n bits, said function F comprising a scalar product between a biometric datum of the entity and a reference biometric datum, said computation performing a non-interactive, publicly verifiable computation method comprising steps of: representation of said function F in form of an arithmetic circuit comprising wires transporting values of the finite prime field .sub.q, with q a prime number, and connecting addition and multiplication operators, conversion of said arithmetic circuit into a polynomial representation, QAP (Quadratic Arithmetic Program) or multi-QAP, generation of a public evaluation key and of a public verification key as a function of said polynomial representation, obtaining by the remote computation device of the arithmetic circuit and of the public evaluation key, for each biometric datum of the entity, determination of at least one matching value between said biometric datum and at least one reference biometric datum by the remote computation device by evaluating the arithmetic circuit having as inputs the biometric datum of the entity and the reference biometric datum, for each determined matching value, generation by the remote computation device of a proof of correction of computation execution of matching value, so-called generated proof, from said polynomial representation, the public evaluation key and result of the evaluation of the arithmetic circuit, transmission by the remote computation device of matching values and generated proofs to the client device, verification of said generated proofs received by the client device by means of the public verification key, identification of the entity by the client device as the function of the matching values and result of said verification of the generated proofs, wherein: representation of said function F comprises encoding an integer k>1 of binary integers of a vector of a biometric datum on at least one input wire of the arithmetic circuit, and the function F comprising at least m scalar products, m being a divider of length N of biometric data vectors, if the divider m is equal to 2 or 3, the arithmetic circuit comprises at least N/(k*m) multiplication operators connected to input wires of the arithmetic circuit, a storage memory, and at least one addition operator, and evaluation of the arithmetic circuit iteratively comprises computation of each of the m scalar products by means of said N/(k*m) multiplication operators, storage of m results of computations of said scalar products in said storage memory and summation of said results by means of said addition operator, if the divider m is greater than or equal to 4, the arithmetic circuit comprises at least one first computation sub-circuit of the scalar product comprising N/(k*m) first multiplication operators connected to input wires of the arithmetic circuit and a first storage memory, and a second computation sub-circuit of the scalar product comprising N/(k*m) second multiplication operators connected to the input wires of the arithmetic circuit and a second storage memory, each one of said first and second computation sub-circuits being also connected to an output of the storage memory of the other one of said first and second computation sub-circuits, and evaluation of the arithmetic circuit iteratively comprises computation of each of the m scalar products by using alternatively one of said first and second computation sub-circuit to compute sum of the scalar product of values of the input wires of the used one of said first and second computation sub-circuits and value stored in the storage memory of the other one of said first and second computation sub-circuits, wherein said biometric identification method delegates to a remote entity a comparison of biometric datum in terms of a protocol of verifiable computations suitable for a real-time execution.
Description
GENERAL TECHNICAL FIELD
The present invention relates to the field of identification of an entity, individual or object. More precisely, it relates to a biometric identification method in which comparison to reference biometric data is delegated to a remote device in terms of a publicly verifiable computation protocol.
STATE OF THE ART
Due to increasing miniaturization of digital computation systems, from now on there is a wide range of digital devices fitted with variable computational power, including the smart card, the supercomputer, the smartphone and the personal computer. In such a scope it can be interesting for a device fitted with limited computational power to delegate costly computations to a remote device fitted with greater computational power. Such delegation in particular has been made easier recently by the development of high-speed communications networks and an offer to outsourced computations to the cloud.
But such delegation of computations raises the problem of the confidence which can be accorded to computation results transmitted by a remote executing party. Computation errors can in fact occur, also due to technical problems independent of the will of the executing party, due to the fact of voluntary and malicious action.
In this way, considerable efforts have been made to develop a computation protocol, called verifiable computation, letting a remote executing party prove to the device having ordered computation that the latter was executed correctly. For a long time however, developed protocols have remained applicable to specific functions only, or else remained unusable in practice due to the substantial number of computations necessary for the ordering party to verify proof supplied by the executing party.
The Pinocchio protocol presented in the publication "Bryan Parno, Craig Gentry, Jon Howell, and Mariana Raykova, Pinocchio: Nearly Practical Verifiable Computation, in Proceedings of the IEEE Symposium on Security and Privacy, IEEE, 21 May 2013" was one of the first verifiable computation protocols for the executing party to verifiably compute the application of any function and for the ordering party to verify the associated proof in a computation time less than that necessary for making the computation itself, allowing the ordering party to effectively take advantage of delegation of computation despite excess costs linked to verification of the proof.
The Pinocchio protocol has the major disadvantage of needing substantial computational power on the part of the executing party. The production cost of computation proof by this protocol is in fact greater by several orders of magnitude than that of the computation itself.
The Pinocchio protocol is based on transcription of the function to be evaluated in the form of an arithmetic circuit and construction of the corresponding quadratic arithmetic program (QAP). The computation cost rises with the number of multipliers in this arithmetic circuit. Such a number can rapidly become large, for example in the case where the function comprises a loop whereof each iteration must be represented explicitly by its own operators in the circuit. This limits the practical use of such a protocol to evaluation of very simple functions.
This protocol was then improved via the Geppetto protocol, presented in the publication "Craig Costello, Cedric Fournet, Jon Howell, Markulf Kohlweiss, Benjamin Kreuter, Michael Naehrig, Bryan Parno, and Samee Zahur, Geppetto: Versatile Verifiable Computation, in Proceedings of the IEEE Symposium on Security and Privacy, IEEE, 18 May 2015". This novel protocol of verifiable computation proposes cutting out the function to be evaluated into several sub-functions, optionally used several times for evaluation of the overall function, for example at each iteration of a loop. The proof of evaluation of this function can then be constructed from the less expensive proofs relative to evaluation of such sub-functions. The total arithmetic circuit can be substantially simplified relative to that of the Pinocchio protocol, considerably limiting the number of multipliers to be employed. The total production cost of the proof for the executing party is reduced relative to that of the Pinocchio protocol. The computation cost of a proof in terms of the Geppetto protocol continues to grow however with the number of multipliers necessary for representation of the function to be evaluated in the form of an arithmetic circuit. A bootstrapping technique has been introduced to improve the situation, but implementing this method degrades performance.
Many other derivatives of the Pinocchio protocol have been proposed, and there are varied applications in multiple technical fields. For example, the Cendrillon protocol presented in the publication "Antoine Delignat-Lavaud, Cedric Fournet, Markulf Kohlweiss and Bryan Parno, Cinderella: Turning Shabby X.509 Certificates into Elegant Anonymous Credentials with the Magic of Verifiable Computation, in 2016 IEEE Symposium on Security and Privacy", relates to the electronic signing of documents, and the PhotoProof protocol, presented in the publication "Assa Naveh, Eran Tromer, PhotoProof: cryptographic image authentication for any set of permissible transformations, proc. IEEE Symposium on Security & Privacy (Oakland) 2016, 255-271, IEEE, 2016" ensures that a photograph has been modified only according to a set of admissible transformations and has not been falsified.
Within the scope of biometric identification it is necessary to compare a biometric fingerprint to a multitude of reference biometric fingerprints, in a sufficiently short period to be supported by the individual to be identified. Such comparison between two biometric fingerprints each represented in the form of a vector u, respectively u', of N binary integers u.sub.i or u'.sub.i, can be made by computing the scalar product uu' between these two vectors. The arithmetic circuit corresponding to such a scalar product is represented in FIG. 1. It then comprises at least N multipliers each taking on input an integer u.sub.i and the corresponding integer u'.sub.i. Such a number of multipliers implies a number of computations by the protocols described hereinabove too great to be realized in real time, making such protocols inadequate to use in terms of a biometric identification method.
There is therefore a need for a biometric identification method for delegating to a remote entity comparison of biometrics fingerprints in terms of a protocol of verifiable computation, for a cost of computation, production and verification of proof comprised, for execution in real time.
PRESENTATION OF THE INVENTION
The present invention proposes according to a first aspect a biometric identification method of an entity, by a biometric identification system comprising a client device and a remote computation device, comprising: computation of at least one matching value between at least one biometric datum of the entity u and at least one reference biometric datum u', by application of a function F to said biometric data, each of said data being a vector of N binary integers u.sub.i or u'.sub.i with 1.ltoreq.i.ltoreq.N, each integer being coded on n bits, said function comprising a scalar product between a biometric datum of the entity and a reference biometric datum, said computation performing a non-interactive, publicly verifiable computation method comprising steps of: representation of said function in the form of an arithmetic circuit comprising wires transporting values of the finite prime field .sub.q, with q a prime number, and connecting addition and multiplication operators, conversion of said arithmetic circuit into a polynomial representation, QAP (Quadratic Arithmetic Program) or multi-QAP, generation of a public evaluation key and of a public verification key as a function of said polynomial representation, obtaining by the remote computation device of the arithmetic circuit and of the public evaluation key, for each biometric datum of the entity, determination of at least one matching value between said biometric datum and at least one reference biometric datum by the remote computation device by evaluating the arithmetic circuit having as inputs the biometric datum of the entity and the reference biometric datum, for each determined matching value, generation by the remote computation device of a proof of correction of the computation execution of the matching value, so-called generated proof, from said polynomial representation, the public evaluation key and the result of the evaluation of the arithmetic circuit, transmission by the remote computation device of said matching values and of said generated proofs to the client device, verification of said proofs received by the client device by means of the public verification key, identification of the entity by the client device as a function of the matching values and of the result of said verification of proofs, characterized in that: representation of said function comprises encoding an integer k>1 of binary integers of a vector of a biometric datum on at least one input wire of the circuit, and the function F comprising at least m scalar products, m being a divider of the length N of the biometric data vectors, if the divider m is equal to 2 or 3, the circuit comprises at least N/km multiplication operators connected to the input wires of the circuit, a storage memory, and at least one addition operator, and evaluation of the circuit iteratively comprises computation of each of the m scalar products by means of said N/km multiplication operators, storage of m results of computations of said scalar products in said storage memory and summation of said results by means of said addition operator, if the divider m is greater than or equal to 4, the circuit comprises at least one first computation sub-circuit of scalar product comprising N/km first multiplication operators connected to the input wires of the circuit and a first storage memory, and a second computation sub-circuit of scalar product comprising N/km second multiplication operators connected to the input wires of the circuit and a second storage memory, each of said sub-circuit being also connected to an output of the storage memory of the other sub-circuit, and evaluation of the circuit iteratively comprises computation of each of the m scalar products by using alternatively the first or the second sub-circuit to compute the sum of the scalar product of the values of the input wires of this sub-circuit and of the value stored in the storage memory of the other sub-circuit.
This lets the client device delegate computation of scalar products necessary for biometric identification of the entity, and verifies the exactitude of computations made by the remote device, all of this for moderate cost due to the reduced complexity of the circuits used to represent the function of scalar product. Such circuits in fact comprise around the order of k*m fewer multipliers than the circuit according to the state of the art.
The verification step of said received proofs can comprise batch verification of pairings.
In a first mode of operation, if the divider m of the length N of the biometric data vectors is equal to 1, given an asymmetric bilinear environment (q, G.sub.1, G.sub.2, G.sub.T, g.sub.1, g.sub.2, e) where q is a prime number, G.sub.1, G.sub.2 and G.sub.T three groups of order q, g.sub.1 a generator of G.sub.1, g.sub.2 a generator of G.sub.2, and e a non-degenerate bilinear pairing e: G.sub.1.times.G.sub.2.fwdarw.G.sub.T and the arithmetic circuit being represented in the form of a QAP of the circuit Q=(t, V, W, Y) of size .rho. and degree .delta., with V={vi}, W={wi}, Y={yi}, 0.ltoreq.i.ltoreq..rho.,
and given I.sub.io={1, . . . , .theta.} the set of indices corresponding to the input/output wires of the circuit and I.sub.mid={.theta.+1, . . . , .rho.} the set of indices of intermediate wires of the circuit not being input wires of the circuit,
the generation step of a public evaluation key and a public verification key comprises: generation of random variables r.sub.v, r.sub.w, s, .alpha..sub.v, .alpha..sub.w, .alpha..sub.y, .beta., .gamma. in .sub.q, definition of coefficients r.sub.y=r.sub.vr.sub.w, g.sub.v1=g.sub.1.sup.r.sup.v, g.sub.w1=g.sub.1.sup.r.sup.w, g.sub.w2=g.sub.2.sup.r.sup.w, g.sub.y1=g.sub.1.sup.r.sup.y and g.sub.y2=g.sub.2.sup.r.sup.y, generation of the public evaluation key EK.sub.F equal to (EK.sub.F1, EK.sub.F2) where
.times..times..times..times..function..di-elect cons..times..times..function..di-elect cons..times..times..function..di-elect cons..times..times..alpha..function..di-elect cons..times..times..alpha..function..di-elect cons..times..times..function..di-elect cons..di-elect cons..delta..times..times..beta..function..times..times..beta..function..- times..times..beta..function..di-elect cons. ##EQU00001## .times..times..times..times..function..di-elect cons. ##EQU00001.2## generation of the public verification key VK.sub.F equal to (VK.sub.F1, VK.sub.F2) where: VK.sub.F1=(g.sub.1,{g.sub.v1.sup.v.sup.i.sup.(s)}.sub.i.di-elect cons.[1,.theta.],{g.sub.y1.sup.y.sup.i.sup.(s)}.sub.i.di-elect cons.[1,.theta.]) VK.sub.F2=(g.sub.2,g.sub.2.sup..alpha..sup.v,g.sub.2.sup..alpha..sup.w,g.- sub.2.sup..alpha..sup.y,g.sub.2.sup..gamma.,g.sub.2.sup..beta..gamma.,g.su- b.y2.sup.t(s),{g.sub.w2.sup.w.sup.i.sup.(s)}.sub.i.di-elect cons.[1,.theta.]) generation by the remote computation device of proof of correction of the computation execution of a matching value comprises, {c.sub.i}.sub.i.di-elect cons.[1,.rho.] being the set of values of the circuit determined during the determination step of the matching value: determination of a polynomial h(x) such that p(x)=h(x)t(x) with p(x)=(v.sub.0(x)+.SIGMA..sub.i=1.sup..rho.c.sub.iv.sub.i(x))(w.sub.0(x)+.- SIGMA..sub.i=1.sup..rho.c.sub.iw.sub.i(x))-(y.sub.0(x)+.SIGMA..sub.i=1.sup- ..rho.c.sub.iy.sub.i(x)), computation of the generated proof .pi.=(.pi..sub.1, .pi..sub.2) with:
.pi..times..times..function..times..times..function..times..times..functi- on..function..times..times..alpha..function..times..times..alpha..function- ..times..times..alpha..function..times..times..beta..function..times..time- s..beta..function..times..times..beta..function..times..pi..times..times..- function. ##EQU00002## where: v.sub.mid(x)=.SIGMA..sub.i.di-elect cons.I.sub.midc.sub.iv.sub.i(x),w.sub.mid(x)=.SIGMA..sub.i.di-elect cons.I.sub.midc.sub.iw.sub.i(x) and y.sub.mid(x)=.SIGMA..sub.i.di-elect cons.I.sub.midc.sub.iy.sub.i(x), and, wherein said proofs received by the client device being equal to (.pi..sub.r1, .pi..sub.r2) with .pi..sub.r1 in the form of: (g.sub.v1.sup.V.sup.mid, g.sub.w1.sup.W.sup.mid, g.sub.y1.sup.Y.sup.mid, g.sub.1.sup.H, g.sub.v1.sup.V'.sup.mid, g.sub.w1.sup.W'.sup.mid, g.sub.y1.sup.Y'.sup.mid, g.sub.1.sup.Z) and .pi..sub.r2 in the form g.sub.w2.sup.w.sup.mid, verification of a received proof comprises performing the following equality tests: e(g.sub.v1.sup.v.sup.o.sup.(s)g.sub.v1.sup.v.sup.io.sup.(s)g.sub.v1.sup.V- .sup.mid,g.sub.w2.sup.w.sup.o.sup.(s)g.sub.w2.sup.w.sup.io.sup.(s)g.sub.w2- .sup.W.sup.mid)=e(g.sub.1.sup.H,g.sub.y2.sup.t(s))e(g.sub.y1.sup.y.sup.o.s- up.(s)g.sub.y1.sup.y.sup.io.sup.(s)g.sub.y1.sup.Y.sup.mid,g.sub.2), e((g.sub.v1.sup.V'.sup.mid).sup.d.sup.1(g.sub.w1.sup.W'.sup.mid).sup.d.su- p.2(g.sub.y1.sup.Y'.sup.mid).sup.d.sup.3,g.sub.2)=e((g.sub.v1.sup.V.sup.mi- d).sup.d.sup.1,g.sub.2.sup..alpha..sup.v)e((g.sub.w1.sup.W.sup.mid).sup.d.- sup.2,g.sub.2.sup..alpha..sup.w)e((g.sub.y1.sup.Y.sup.mid).sup.d.sup.3,g.s- ub.2.sup..alpha..sup.y), e((g.sub.1.sup.Z,g.sub.2.sup..gamma.)=e(g.sub.v1.sup.V.sup.midg.sub.w1.su- p.W.sup.midg.sub.y1.sup.Y.sup.mid,g.sub.2.sup..beta..gamma.) where g.sub.v1.sup.v.sup.io.sup.(s)=.PI..sub.i=1.sup..theta.(g.sub.v1.sup.v.sup- .i.sup.(s)).sup.c.sup.i, g.sub.w1.sup.w.sup.io.sup.(s)=.PI..sub.i=1.sup..theta.(g.sub.w1.sup.w.sup- .i.sup.(s)).sup.c.sup.i, and g.sub.y1.sup.y.sup.io.sup.(s)=.PI..sub.i=1.sup..theta.(g.sub.y1.sup.y.sup- .i.sup.(s)).sup.c.sup.i and (d.sub.1, d.sub.2, d.sub.3) elements of .sub.q on .lamda. bits with .lamda. a security parameter.
Verification of the proof of computation is accelerated relative to the Pinocchio protocol, by way of simultaneous verification of several pairings.
In a second mode of operation, if the divider m of the length N of the biometric data vectors is greater than or equal to 2, given an asymmetric bilinear environment (q, G.sub.1, G.sub.2, G.sub.T, g.sub.1, g.sub.2, e) where q is a prime number, G.sub.1, G.sub.2 and G.sub.T three groups of order q, g.sub.1 a generator of G.sub.1, g.sub.2 a generator of G.sub.2, and e a non-degenerate bilinear pairing e: G.sub.1.times.G.sub.2.fwdarw.G.sub.T, the arithmetic circuit being represented in the form of a multi-QAP Q=({B.sub.b}.sub.b.di-elect cons.[1,l],t,V,W,Y) of size .rho. and degree .delta., with {B.sub.b}.sub.b.di-elect cons.[1,l] a set of l banks B.sub.b of Q used in computation of the function F, and V={vi}, W={wi}, Y={yi} with 0.ltoreq.i.ltoreq..rho., the generation step of a public evaluation key and a public verification key comprises: generation of random variables s,{(.alpha..sub.bv, .alpha..sub.bw, .alpha..sub.by, .beta..sub.b, .gamma..sub.b)}.sub.b.di-elect cons.[1,l], r.sub.v, r.sub.w in .sub.q, definition of the following coefficients: r.sub.y=r.sub.br.sub.w, g.sub.v1=g.sub.1.sup.r.sup.v, g.sub.v2=g.sub.2.sup.r.sup.v, g.sub.w1=g.sub.1.sup.r.sup.w, g.sub.w2.sup.r.sup.w=g.sub.2.sup.r.sup.w, g.sub.y1=g.sub.1.sup.r.sup.y and g.sub.y2=g.sub.2.sup.r.sup.y, generation of the public evaluation key EK.sub.F equal to: ({EK.sub.Fb}.sub.b.di-elect cons.[1,l],{g.sub.1.sup.s.sup.i}.sub.i.di-elect cons.[1,.delta.],g.sub.v1.sup.t(s),g.sub.w1.sup.t(s),g.sub.y1.sup.t(s),g.- sub.v2.sup.t(s),g.sub.w2.sup.t(s),g.sub.y2.sup.t(s))
where each public bank key EK.sub.Fb is equal to (EK.sub.Fb1, EK.sub.Fb2) with:
.times..times..times..times..function..times..times..function..times..tim- es..function..times..times..alpha..function..times..times..alpha..function- ..times..times..alpha..function..times..times..beta..function..times..time- s..beta..function..times..times..beta..function..di-elect cons..times..times..alpha..function..times..times..alpha..function..times- ..times..alpha..function..times..times..beta..function..times..times..beta- ..function..times..times..beta..function. ##EQU00003## .times..times..times..times..times..function..di-elect cons..beta..times..times..alpha..function. ##EQU00003.2## generation of the public verification key VK.sub.F equal to: ({VK.sub.Fb}.sub.b.di-elect cons.[1,l], g.sub.1, g.sub.2, g.sub.y2.sup.t(s)) where each public bank key VK.sub.Fb is equal to (g.sub.2.sup..alpha..sup.bv, g.sub.2.sup..alpha..sup.bw, g.sub.2.sup..alpha..sup.by, g.sub.2.sup..gamma..sup.b, g.sub.2.sup..beta..sup.b.sup..gamma..sup.b) determination of a matching value comprises, function F being divided into .omega. sub-functions F.sub.1, . . . , F.sub..omega. and .sigma.=((f.sub.l, (T.sub.l1, . . . , T.sub.ll))).sub.l.di-elect cons.[1,L] being a scheduling of length L with f.sub.l .di-elect cons.{1, . . . , .omega.}, evaluation of each sub-function F.sub..omega. from the biometric data of the entity and the reference biometric data and determination of the values i of the circuit, generation by the remote computation device of proof of correction of the computation execution of a matching value comprises, for each l={1, . . . , L}: for each bank B.sub.b such that b.di-elect cons..LAMBDA., with .LAMBDA.[1,l] the set of indices b.di-elect cons.[1,l] such that T.sub.lb.noteq.0,.GAMMA.=U.sub.b.di-elect cons..LAMBDA.B.sub.b, {c.sub.j}.sub.j.di-elect cons.B.sub.b an instance of the bank B.sub.b, .DELTA.={c.sub.i}.sub.i.di-elect cons..GAMMA. the set of values of .GAMMA.: generation of pledging random variables in .sub.q: o.sub.b=(o.sub.bv, o.sub.bw, o.sub.by), computation of a digest D.sub.b equal to (D.sub.b1,D.sub.b2) from the instance of the bank of variables B.sub.b: B.sub.b.sup.(T.sup.lb.sup.)={c.sub.i.di-elect cons..DELTA.}.sub.i.di-elect cons.B.sub.b and pledging random variables o.sub.b and such that: if the bank B.sub.b is an input/output bank: D.sub.b1=(g.sub.v1.sup.v.sup.(b).sup.(s),g.sub.y1.sup.y.sup.(b).sup.(s)) and D.sub.b2=(g.sub.w2.sup.w.sup.(b).sup.(s)), if the bank B.sub.b is not an input/output bank:
.times..times..times..times..function..times..times..function..times..tim- es..function..times..times..alpha..function..times..times..alpha..function- ..times..times..alpha..function..times..times..beta..function..times..time- s..beta..function..times..times..beta..function. ##EQU00004## .times..times..times..times..function. ##EQU00004.2## with: v.sup.(b)(s)=.SIGMA..sub.i.di-elect cons.B.sub.bc.sub.iv.sub.i(s)+o.sub.bvt(s), w.sup.(b)(s)=.SIGMA..sub.i.di-elect cons.B.sub.bc.sub.iw.sub.i(s)+o.sub.bwt(s), y.sup.(b)(s)=.SIGMA..sub.i.di-elect cons.B.sub.bc.sub.iy.sub.i(s)+o.sub.byt(s), determination of a polynomial h.sup.(l)(x) such that p.sup.(l)(x)=h.sup.(l)(x)t(x) with p.sup.(l)(x)=(v.sub.0(x)+.SIGMA..sub.i.di-elect cons..GAMMA.c.sub.iv.sub.j(x)+.SIGMA..sub.b.di-elect cons..LAMBDA.o.sub.bvt(x))(w.sub.0(x)+.SIGMA..sub.i.di-elect cons..GAMMA.c.sub.iw.sub.j(x)+.SIGMA..sub.b.di-elect cons..LAMBDA.o.sub.bwt(x))-(y.sub.0(x)+.SIGMA..sub.i.di-elect cons..GAMMA.c.sub.iy.sub.j(x)+.SIGMA..sub.b.di-elect cons..LAMBDA.o.sub.byt(x)) computation of a proof element .pi..sup.(l) equal to g.sub.1.sup.h.sup.(l).sup.(s), and, wherein said proofs received by the client device being of the form D.sub.1.sup.(1), . . . , D.sub.l.sup.(1), .pi..sup.(1), . . . , D.sub.1.sup.(L), . . . , D.sub.l.sup.(L), .pi..sup.(L) where for all l.di-elect cons.{1, . . . , L} and b.di-elect cons.{1, . . . ,l}:
.times..times..times..times..times..times..times..times.'.times..times..t- imes..times.'.times..times..times..times.'.times..times..times..times. ##EQU00005## and .pi..sup.(l)=g.sub.1.sup.H.sup.(l), verification of a received proof (E8) comprises: verification of Ll digests, for l.di-elect cons.{1, . . . , L} and b.di-elect cons.{1, . . . , l} comprising performing the following equality tests:
.function..times..times.'.times..times..alpha..function..times..times. ##EQU00006## .function..times..times.'.function..alpha..function..times..times. ##EQU00006.2## .function..times..times.'.times..times..alpha..function..times..times. ##EQU00006.3## .function..gamma..function..times..times..times..times..times..times..bet- a..gamma. ##EQU00006.4## verification of L proofs comprising for l.di-elect cons.{1, . . . , L} performing the following equality test:
.function. .times..times..times. .times..times..times..function..times..times..function..function. .times..times..times. ##EQU00007##
Verification of the proof of computation is accelerated relative to the Geppetto protocol, by way of simultaneous verification of several pairings.
In a third mode of operation, if the divider m of the length N of the biometric data vectors is greater than or equal to 2, given an asymmetric bilinear environment (q, G.sub.1, G.sub.2, G.sub.T, g.sub.1, g.sub.2, e) where q is a prime number G.sub.1, G.sub.2 and G.sub.T three groups of order q, g.sub.1 a generator of G.sub.1, g.sub.2 a generator of G.sub.2, and e a non-degenerate bilinear pairing e: G.sub.1.times.G.sub.2.fwdarw.G.sub.T, the arithmetic circuit being represented in the form of a multi-QAP Q=({B.sub.b}.sub.b.di-elect cons.[1,l], t,V,W,Y) of size .rho. and degree .delta., with {B.sub.b}.sub.b.di-elect cons.[1,l] a set of l banks B.sub.b of Q used in computation of the function F, and V={vi}, W={wi}, Y={yi} with 0.ltoreq.i.ltoreq..rho., generation step of a public evaluation key and a public verification key comprises: generation of random variables s, {(.alpha..sub.bv, .alpha..sub.bw, .alpha..sub.by, .beta..sub.b, .gamma..sub.b)}.sub.b.di-elect cons.[1,l], r.sub.v, r.sub.w in .sub.q, definition of the following coefficients: r.sub.y=r.sub.vr.sub.w, g.sub.v1=g.sub.1.sup.r.sup.v, g.sub.v2=g.sub.2.sup.r.sup.v, g.sub.w1=g.sub.1.sup.r.sup.w, g.sub.w2=g.sub.2.sup.r.sup.w, g.sub.y1=g.sub.1.sup.r.sup.y and g.sub.y2=g.sub.2.sup.r.sup.y, generation of the public evaluation key EK.sub.F equal to: ({EK.sub.Fb}.sub.b.di-elect cons.[1,l],{g.sub.1.sup.s.sup.i}.sub.i.di-elect cons.[1,.delta.],g.sub.v1.sup.t(s),g.sub.w1.sup.t(s),g.sub.y1.sup.t(s),g.- sub.v2.sup.t(s),g.sub.w2.sup.t(s),g.sub.y2.sup.t(s)) where each public bank key EK.sub.Fb is equal to (EK.sub.Fb1, EK.sub.Fb2) with:
.times..times..times..times..function..times..times..function..times..tim- es..function..times..times..alpha..function..times..times..alpha..times..f- unction..times..times..alpha..function..times..times..beta..function..time- s..times..beta..function..times..times..beta..function..di-elect cons..times..times..alpha..function..times..times..alpha. .function..times..times..alpha..function..times..times..beta..function..t- imes..times..beta..function..times..times..beta..function. ##EQU00008## .times..times..times..times..times..function..di-elect cons..times..times..alpha..function. ##EQU00008.2## generation of the public verification key VK.sub.F equal to: ({VK.sub.Fb}.sub.b.di-elect cons.[1,l], g.sub.1, g.sub.2, g.sub.y2.sup.t(s)) where each public bank key VK.sub.Fb is equal to (g.sub.2.sup..alpha..sup.bv, g.sub.2.sup..alpha..sup.bw, g.sub.2.sup..alpha..sup.by, g.sub.2.sup..gamma..sup.b, g.sub.2.sup..beta..sup.b.sup..gamma..sup.b), determination of a matching value comprises, function F being divided into .omega. sub-functions F.sub.1, . . . , F.sub..omega. and .sigma.=((f.sub.l, (T.sub.l1, . . . , T.sub.ll))).sub.l.di-elect cons.[1,L] being a scheduling of length L with f.sub.l.di-elect cons.{1, . . . , .omega.}, evaluation of each sub-function F.sub..omega. from the biometric data of the entity and the reference biometric data and determination of the values of the circuit, generation by the remote computation device of proof of correction of the computation execution of a matching value comprises, for each l={1, . . . , L}: for each bank B.sub.b such that b.di-elect cons..LAMBDA., with .LAMBDA.[1,l] the set of indices b.di-elect cons.[1,l] such that T.sub.lb.noteq.0, .GAMMA.=U.sub.b.di-elect cons..LAMBDA.B.sub.b, {c.sub.j}.sub.j.di-elect cons..sub.B an instance of the bank B.sub.b, .DELTA.={c.sub.i}.sub.i.di-elect cons..GAMMA. the set of values of r: generation of pledging random variables in .sub.q: o.sub.b=(o.sub.bv, o.sub.bw, o.sub.by), computation of a digest D.sub.b equal to (D.sub.b1,D.sub.b2) from the instance of the bank of variables B.sub.b: B.sub.b.sup.(T.sup.lb.sup.)={c.sub.i.di-elect cons..DELTA.}.sub.i.di-elect cons.B.sub.b and pledging random variables o.sub.b and such that: if the bank B.sub.b is an input/output bank: D.sub.b1=(g.sub.v1.sup.v.sup.(b).sup.(s), g.sub.y1.sup.v.sup.(b).sup.(s)) and D.sub.b2=(g.sub.w2.sup.w.sup.(b).sup.(s)). if the bank B.sub.b is not an input/output bank:
.times..times..times..times..function..times..times..function..times..tim- es..function..times..times..alpha..function..times..times..alpha..function- ..times..times..alpha..function..times..times..beta..function..times..time- s..beta..function..times..times..beta..function. ##EQU00009## .times..times..times..times..function. ##EQU00009.2## with: v.sup.(b)(s)=.SIGMA..sub.i.di-elect cons.B.sub.bc.sub.iv.sub.i(s)+o.sub.bvt(s), w.sup.(b)(s)=.SIGMA..sub.i.di-elect cons.B.sub.bc.sub.iw.sub.i(s)+o.sub.bwt(s), y.sup.(b)(s)=.SIGMA..sub.i.di-elect cons.B.sub.bc.sub.iy.sub.i(s)+o.sub.byt(s), determination of a polynomial h.sup.(l)(x) such that p.sup.(l)(x)=h.sup.(l)(x)t(x) with p.sup.(l)(x)=(v.sub.0(x)+.SIGMA..sub.i.di-elect cons..GAMMA.c.sub.iv.sub.j(x)+.SIGMA..sub.b.di-elect cons..LAMBDA.o.sub.bvt(x))(w.sub.0(x)+.SIGMA..sub.i.di-elect cons..GAMMA.c.sub.iw.sub.j(x)+.SIGMA..sub.b.di-elect cons..LAMBDA.o.sub.bwt(x))-(y.sub.0(x)+.SIGMA..sub.i.di-elect cons..GAMMA.c.sub.iy.sub.j(x)+.SIGMA..sub.b.di-elect cons..LAMBDA.o.sub.byt(x)) computation of a proof element .pi..sup.(l) equal to g.sub.1.sup.h.sup.(l).sup.(s), and, wherein said proofs received by the client device being of the form D.sub.1.sup.(1), . . . , D.sub.l.sup.(1), .pi..sup.(1), . . . , D.sub.1.sup.(L), . . . , D.sub.l.sup.(L), .pi..sup.(L) where for all l.di-elect cons.{1, . . . , L} and b.di-elect cons.{1, . . . ,l}:
.times..times..times..times..times..times..times..times.'.times..times..t- imes..times.'.times..times..times..times.'.times..times..times..times. ##EQU00010## and .pi..sup.(l)=g.sub.1.sup.H.sup.(l), verification of a received proof comprises, given a correction parameter .lamda.: selection of a random vector (d.sub.1, . . . , d.sub.3l) of elements of size .lamda., batch verification of Ll digests comprising performing l times the following equality tests, for b.di-elect cons.{1, . . . , l}:
.function..times..times..times.'.times..times..alpha..function..times..ti- mes..times.'.times..times..alpha..function..times..times..times.'.times..t- imes..alpha..function..times..times..times..times..times..times..times..ti- mes..times. ##EQU00011## .times..function..times..gamma..function..times..times..times..times..tim- es..times..times..beta..gamma. ##EQU00011.2## batch verification of L proofs comprising performing the following equality test:
.times..times..function. .times..times..times..times..function. .times..times..times..times..function..function..times..times..times..tim- es..function..function..times..times. .times..times..times..times. ##EQU00012##
This makes verification of a proof even faster due to batch verification of digests of the proof.
Identification of the entity can comprise comparison of the matching values with a predetermined threshold.
Function F can comprise comparison of the result of the scalar product between said biometric data of the entity and said reference biometric data with a predetermined threshold.
Such comparison to a threshold decides if the compared biometric data are sufficiently close to conclude successful identification of the entity to be identified.
Encoding of k binary integers u.sub.i or u'.sub.i on an input wire of an j.sup.th multiplication operator, 1.ltoreq.j.ltoreq.N/k, is equal to
.times..times..function. ##EQU00013## ##EQU00013.2## .times..times..function.' ##EQU00013.3## with 1.ltoreq.z.ltoreq.m, and is given by the formula:
.times..function..times..times..times..times. ##EQU00014##
with .di-elect cons..sub.1, . . . , .di-elect cons..sub.k predetermined integers.
Several integers of the biometric data can be encoded on each input wire, reducing the number of multipliers necessary for computation of the scalar product between a biometric datum of the entity and a reference biometric datum.
According to a second aspect, the invention relates to a computer program product comprising code instructions for execution of a method according to the first aspect when this program is executed by a processor.
According to a third aspect, the invention relates to a biometric identification system comprising a client device and a remote computation device characterized in that said client device and said remote computation device each comprise a processor, an interface and a memory for performing the steps of the identification method according to the first aspect.
Such computer program product and system have the same advantages as those mentioned for the method according to the first aspect.
PRESENTATION OF THE FIGURES
Other characteristics and advantages of the present invention will emerge from the following description of a preferred embodiment. This description will be given in reference to the appended drawings, in which:
FIG. 1 illustrates an arithmetic circuit corresponding to naive implementation of a scalar product for biometric identification of an entity;
FIG. 2 illustrates an identification system according to an embodiment of the invention;
FIG. 3 is a diagram showing an implementation of an identification method according to the invention;
FIGS. 4a and 4b illustrate an arithmetic circuit for biometric identification of an entity according to a first mode of operation of the invention;
FIGS. 5a and 5b illustrate an example implementation of the circuit of FIG. 4 for N=3000, n=8, q=256, k=3;
FIGS. 6a to 6c illustrate a arithmetic circuit for biometric identification of an entity according to a second mode of operation of the invention;
FIGS. 7a and 7b illustrate an arithmetic circuit for biometric identification of an entity according to a third mode of operation of the invention;
DETAILED DESCRIPTION
The present invention relates to implementing a biometric identification method of an entity 1 by an identification system 2 comprising a client device 3 and a remote computation device 4 capable of being connected together by a communications network 5, as represented in FIG. 2. Such an entity can be an individual or else an object having biometric data such as a biometric passport.
The client device and the remote computation device can each comprise a random access memory and internal storage means such as rewritable non-volatile memory (flash memory or EEPROM memory) and processing means comprising a processor. They can also comprise an interface for dialoguing with each other, of wired type such as an Ethernet link, or wireless such as a Wifi or Bluetooth connection.
The aim of this method carried out is to allow the device to delegate to the remote computation device the computations necessary for biometric identification of the entity to be identified, so that the computations made by the remote computation device are publicly verifiable, all this happening over a sufficiently short period to be acceptable in terms of an identification method.
For conducting such biometric identification the client device acquires at least one biometric datum of the entity to be identified u. To identify the entity, this at least one biometric datum u must be compared to one or more reference biometric data u', stored in advance.
By way of example, such biometric data can be fingerprints, DNA, voice or even iris images or venous networks. Each of these biometric data is a vector of N binary integers u.sub.i or u'.sub.i with 1.ltoreq.i.ltoreq.N. Each integer u.sub.i or u'.sub.i is coded on n bits. For example in the case of a face biometric datum, there can typically be N=3000 and n=8.
The client device can comprise or be connected to a device for capturing such biometric data, such as a fingerprint reader, a microphone, or an iris-imaging device. This capture device can be employed to acquire the biometric datum u acquired for the entity 1. The reference biometric data u' can be stored in the storage means of the client device or of the remote computation device.
The identification method can comprise the steps described hereinbelow in reference to FIG. 3.
First of all at least one matching value can be computed F1 between at least one biometric datum of the entity u and at least one reference biometric datum u', by application of a function F, so-called correlation function, to said biometric data. Function F comprises a scalar product between a biometric datum of the entity and a reference biometric datum. Such a scalar product in fact computes a score S=.SIGMA..sub.j=1.sup.N(u.sub.ju.sub.j') which is all the higher since the data compared are similar. Such a score can be used as matching value. To determine if an attempt at identification has succeeded, the matching values can be compared to a predetermined threshold T. Alternatively, function F can comprise the comparison of the result of the scalar product between the biometric data of the entity u and the reference biometric data u', i.e. of the score S, to this predetermined threshold T. Computation of the matching value can comprise computation of the value (S-T) and the matching value coming from such computation can be a sign bit for example taking the value 1 if S-T>0, the value 0 if not.
To ensure the quality of the result obtained, computation of such a matching value F1 employs a non-interactive, publicly verifiable computation method. Such a method generally being divided into three phases: representation of the function F to be evaluated in the form of a system constraints represented in the form of an arithmetic circuit. transformation of this arithmetic circuit into polynomial representation called "Quadratic Arithmetic Programs" (abbreviated to QAP below). generation of a proof of correction of the computation execution from the QAP.
The non-interactive, publicly verifiable computation method carried out more precisely first comprises a representation step E1 of said function F in the form of an arithmetic circuit. Such an arithmetic circuit comprises wires transporting values of the finite prime field Zq, with q a prime number, and connecting addition and multiplication operators. Typically the size q of the values of the circuit wires can be equal to 256 bits.
The arithmetic circuit is then converted E2 into a polynomial representation, QAP ("Quadratic Arithmetic Program") or multi-QAP. Such representations and the way to attain them from an arithmetic circuit are described in more detail in the publications cited hereinabove on the existing Pinocchio and Geppetto protocols.
Next a public evaluation key and a public verification key are generated E3 as a function of said polynomial representation. The remote computation device then obtains E4 the arithmetic circuit and the public evaluation key.
The representation steps in the form of an arithmetic circuit E1, conversion into a polynomial representation E2 and generation of keys E3 can be conducted by the client device itself. Alternatively these steps can be delegated to a trusted third party. Since such steps are independent of the value of the biometric data to be compared, they can be conducted once only, prior to comparisons of biometric data described hereinbelow, and do not need to be repeated as long as the format of the biometric data to be compared does not change.
For each biometric datum of the entity at least one matching value between said biometric datum and at least one reference biometric datum is then determined E5 by the remote computation device by evaluating the arithmetic circuit with the biometric data of the entity and the reference biometric datum as inputs.
For each determined matching value the remote computation device generates E6 a proof of correction of the computation execution of the matching value, so-called generated proof, from said polynomial representation, the public evaluation key and the result of evaluation of the arithmetic circuit. It then transmits E7 the matching values and said generated proofs to the client device.
The latter verifies E8 the received proof by means of the public verification key. The verification step of said received proofs E8 can comprise or not batch verification of pairings.
Finally the entity is identified F2 by the client device as a function of the matching values and the result of said verification of proofs.
The integers u.sub.i and u.sub.i' constituting the data of the entity and the reference data are usually encoded on a number of bits n far less than the size q of the values of wires of the circuit. By way of example the number of bits n can be equal to 8 bits and the size q can be equal to 256 bits. To limit the number of multipliers necessary for representation of the function F in the form of an arithmetic circuit, several integers u respectively u.sub.i' are encoded on each input wire of the arithmetic circuit. Representation of said function E1 comprises encoding an integer k>1 of binary integers of a vector of a biometric datum on at least one input wire of the circuit. In practice, encoding E.sub.k.sup.((j-1)k+1)(u) or E.sub.k.sup.((j-1)k+1)(u') of k binary integers u.sub.i or u'.sub.i on an input wire of a j.sup.th multiplication operator, 1.ltoreq.j.ltoreq.N/k, can be defined by the formula:
.times..function..times..times..times..times. ##EQU00015## with .di-elect cons..sub.1, . . . , .di-elect cons..sub.k predetermined integers.)
A multiplier having on input E.sub.k.sup.((j-1)k+1)(u) and E.sub.k.sup.((j-1)k+1)(u') has on its output wire the product of encodings of successive k binary integers u.sub.i or u'.sub.i coded on its input wires. This product is noted E.sub.uu',k.sup.((j-1)k+1)=E.sub.k.sup.((j-1)k+1)(u). E.sub.k.sup.((j-1)k+1)(u'). By way of example, for j=1, there is: E.sub.uu',k.sup.(1)=2.sup.2.di-elect cons..sup.1u.sub.1u.sub.1'+2.sup..di-elect cons..sup.2(u.sub.1u.sub.2'+u.sub.2u.sub.1')+2.sup.2.di-elect cons..sup.2u.sub.2u.sub.2'+ . . . +2.sup.2.di-elect cons..sup.ku.sub.ku.sub.k'
To further reduce the number of multipliers of the arithmetic circuit, the method as carried out also proposes splitting computation of the scalar product of the biometric datum of the entity u and of the reference biometric datum u' of lengths N into several computations of scalar products of vectors of lesser size coming from splitting of the vectors u and u'. The combination of the results of these scalar products produces the score S corresponding to the result of the scalar product of u and u'.
For this, function F comprising at least m scalar products, function F can be decomposed into at least m occurrences of sub-functions, m being a divider m of the length N of the biometric data vectors. Only the split sub-functions are represented by their own sub-circuit in the arithmetic circuit, reducing the number of multipliers of the circuit. To combine decomposition of the scalar product of u and u' into m scalar sub-products, and coding of k integers on each input wire of the circuit, it is possible to select k such that k divides m. The scalar product of u and u' can be decomposed into m scalar sub-products of vectors of length N/km. The sum of the results of these m scalar products produces an encoded score {tilde over (S)} defined by the following formula:
.times..times.'.times..times..times. .times..times.'' ##EQU00016## and of the following form if the expression hereinabove is deployed and if the terms are gathered by power of 2: {tilde over (S)}=2.sup.2.di-elect cons..sup.1a.sub.1+2.sup.2.di-elect cons..sup.2a.sub.2'+2.sup.2.di-elect cons..sup.2a.sub.2+2.sup.2.di-elect cons..sup.3a.sub.3'+ . . . +2.sup.2.di-elect cons..sup.ka.sub.k with a.sub.i the terms at 2.sup.2.di-elect cons..sup.i gathering the products of integers u.sub.i and u'.sub.i of the same indices useful for computing the scalar product and u and u', and with a.sub.i' the terms at 2.sup..di-elect cons..sup.2, . . . , 2.sup..di-elect cons..sup.k gathering the remaining products, cross products of integers u.sub.i and u'.sub.j of different indices not useful for computation of the scalar product of u and u'.
To extract the score S from its encoded version {tilde over (S)}, it is possible to extract the k sub-terms corresponding to the coefficients 2.sup.2.di-elect cons..sup.1, . . . , 2.sup.2.di-elect cons..sup.k (i.e., the elements a.sub.1, a.sub.2, . . . , a.sub.k), then add them.
The paragraphs hereinbelow present the specific features of the method for different ranges of value of the divider m. m can be determined by making a compromise between the computational powers of the client device and the remote computation device as well especially as memories.
In a first mode of operation in which the divider m is equal to 1, function F can be put in the form of the circuit represented in FIGS. 4a and 4b. Such a circuit comprises N/k input multipliers each taking on input E.sub.k.sup.((j-1)k+1)(u) and E.sub.k.sup.((j-1)k+1)(u') with 1.ltoreq.j.ltoreq.N/k. In FIGS. 4a and 4b these multipliers are noted r.sub.j and the input wires are numbered from 1 to 2N/k. The N/k output wires of the multipliers carry the values E.sub.uu',k.sup.((j-1)k+i) whereof the sum is equal to the encoded score {tilde over (S)} described hereinabove. The circuit comprises an additional output multiplier, numbered r.sub.N/k+1, necessary for conversion of the circuit in the form of QAP. This multiplier multiplies the output of the scalar product by 1 so as not to modify the encoded score {tilde over (S)}. Finally, a split gate is employed to extract the coefficients a.sub.i with 1.ltoreq.i.ltoreq.k corresponding to the terms of the scalar product uu'. The summation of these terms first split from the encoded score then reconstituted by multiplication by powers of two and added produces the score S. FIGS. 4a and 4b correspond to an execution in which the score is compared to the predetermined threshold T. The value (S-T) is computed and provided on input with a second split gate to extract the sign bit indicating the result of the comparison. More precisely, hereinbelow split gate means an arithmetic gate which splits an integer bit by bit. Given an integer a.di-elect cons..sub.q, as is known to keep on .tau. bits, the split gate contains an input wire (containing the integer a) and .tau. output wires. In terms of elementary arithmetic constraints, its definition is given for example in the cited article Pinocchio, paragraph 3.2. It is recalled here by way of indication. It is clear that c.sub.0 is the input wire and c.sub.1, . . . , c.sub..tau. the output wires. The arithmetic circuit of the gate so-called "split gate" is defined as follows: concatenation of the bits on output is equal to the input
.tau..times. ##EQU00017## each output wire contains a Boolean value (0 or 1): .A-inverted.i.di-elect cons.{1, . . . ,.tau.}:c.sub.j(1-c.sub.j)=0 When a "split gate" gate is used within a circuit, the integer .tau. is determined as an achieved upper limit given the size of the circuit inputs and all the arithmetic gates located between the inputs and the split gate.
An example of implementation is represented in FIGS. 5a and 5b for N=3000, n=8, q=256, k=3. In such an mode of operation, the following values can be used for the parameters .epsilon..sub.i:.epsilon..sub.1=0, .epsilon..sub.2=26, .epsilon..sub.3=78.
In a second mode of operation in which the divider m is equal to 2 or 3, function F can be decomposed into a function F1 computing a scalar sub-product between two vectors of size N/km, to be used m times, and a function F2 computing the sum of m values, corresponding to a coded score, and performing extraction of the corresponding score equal to the preferred scalar product.
As represented in FIGS. 6a to 6c, the corresponding circuit comprises at least N/km multiplication operators connected to the input wires of the circuit, a storage memory, and at least one addition operator, and evaluation of the circuit iteratively comprises computation of each of the m scalar products by means of said N/km multiplication operators, storage of the m results of computations of said scalar products in said storage memory and summation of said results by means of said addition operator.
With F.sub.1 and F.sub.2 defined as such, evaluation of function F corresponds to m applications of function F.sub.1 followed by application of function F.sub.2. The circuit represented in FIGS. 6a to 6c comprises N/km input multipliers each taking on input, during the iteration z of the function F1,
.times..times..function. ##EQU00018## ##EQU00018.2## .times..times..function.' ##EQU00018.3## with 1.ltoreq.j.ltoreq.N/km. In FIGS. 6a to 6c these multipliers are noted r.sub.j and the input wires are numbered from 1 to 2 N/km.
The m applications of function F.sub.1 compute the coded sub-scores {tilde over (S)}.sub.z, for z.di-elect cons.{1, . . . , m}:
.times.' ##EQU00019##
By way of example, for z=1, there is:
.times..times.'.times..times..times. .times..times.'' ##EQU00020##
During the iteration z the N/km output wires of the multipliers thus carry the values
'.times..times. ##EQU00021## whereof the sum is equal to the encoded score {tilde over (S)}.sub.z described hereinabove. The circuit comprises an additional output multiplier, numbered r.sub.N/km+1, necessary for conversion of the circuit into the form of QAP. The m coded sub-scores {tilde over (S)}.sub.z noted {tilde over (S)}.sub.z.sup.(out) in FIGS. 6a to 6c are stored in the storage memory corresponding to the m bus ("Bus Bank") of the verifiable computation method. Evaluation of function F2, with on input the m values coming from the buses, noted {tilde over (S)}.sub.z.sup.(in) in FIGS. 6a to 6c, produces the coded score S described hereinabove.
As in the case of the circuit in FIGS. 4a and 4b, a first split gate recovers the terms a.sub.i with 1.ltoreq.i.ltoreq.k corresponding to the terms of the scalar product uu'. The summation of these terms produces the score S which is then compared to the predetermined threshold T.
According to a variant not represented, function F1 can comprise decoding of the coded sub-score {tilde over (S)}.sub.z obtained during its evaluation into a sub-score S.sub.z. Such decoding can be done similarly to the decoding of the coded score {tilde over (S)} presented hereinabove. Function F2 comprises only the summation of the sub-scores S.sub.z to obtain the score S corresponding to the scalar product uu', according to the formula:
.times..times..times..times..times.'.times..times.'.times.'.times. ##EQU00022##
In a third mode of operation in which the divider m is greater than or equal to 4, it is possible to decompose function F into a function F.sub.1 and a function F.sub.2, alternatively use and m times the total, which each take on input two vectors of size N/km and a sub-score, and on output return an updated sub-score defined as the sum of the sub-score given on input with the result of the scalar product of the vectors provided on input; and a function F.sub.3 which decodes a coded score {tilde over (S)} into a score S.
As represented in FIGS. 7a and 7b, the circuit comprises at least one first computation sub-circuit of scalar product comprising N/km first multiplication operators connected to the input wires of the circuit, for evaluation of function F1 for z odd, and a first storage memory, and a second computation sub-circuit of scalar product comprising N/km second multiplication operators connected to the input wires of the circuit, for evaluation of function F2 for z even, and a second storage memory, each of said sub-circuit being also connected to an output of the storage memory of the other sub-circuit, and evaluation of the circuit iteratively comprises computation of each of the m scalar products by using alternatively the first or the second sub-circuit to compute the sum of the scalar product of the values of the input wires of this sub-circuit and of the value stored in the storage memory of the other sub-circuit.
With F.sub.1, F.sub.2 and F.sub.3 defined as such, evaluation of the function F then corresponds to m applications alternatively of function F.sub.1 and function F.sub.2 followed by application of function F.sub.3.
The circuit represented in FIGS. 7a and 7b comprises two sets of N/km input multipliers. During the iteration z of the function F1 or F2, the N/km multipliers of the relevant sub-circuit each take on input,
.times..times..function. ##EQU00023## ##EQU00023.2## .times..times..function.' ##EQU00023.3## with 1.ltoreq.j.ltoreq.N/km. In FIGS. 7a and 7b these multipliers are noted r.sub.j with respectively 1.ltoreq.j.ltoreq.N/km and N/km+2.ltoreq.j.ltoreq.2N/km+1. The input wires are numbered respectively from 1 to 2N/km and from 3N/km+3 to 5N/km+2.
The m applications of functions F.sub.1 and F.sub.2 compute the coded sub-scores {tilde over (S)}.sub.z, for z.di-elect cons.{1, . . . , m}:
.zeta..times..times.'.zeta. ##EQU00024##
The N/km output wires of the multipliers of a sub-circuit during the iteration z carry the values
'.times..times. ##EQU00025## whereof the sum, added to the coded sub-score of the preceding iteration {tilde over (S)}.sub.z-1, is equal to the encoded score {tilde over (S)}.sub.z described hereinabove. The sub-score {tilde over (S)}.sub.0 can be also initialized at 0 during the first iteration. The coded score {tilde over (S)} is constructed iteratively, each iteration adding to the sub-score coming from the preceding iteration the result of the current scalar sub-product .SIGMA..sub.j=1.sup.N/kmE.sub.uu',k.sup.((z-1)(N/m)+(j-1)k+1).
The circuit comprises an additional output multiplier for each sub-circuit, numbered r.sub.N/km+1, r.sub.2N/km+2 necessary for conversion of the circuit in the form of QAP. On completion of its evaluation each sub-circuit stores the coded sub-scores {tilde over (S)}.sub.z computed in the storage memory corresponding to its bus (Bus Bank) r2.sub.N/km+3, r.sub.2N/km+219 in terms of the verifiable computation method.
On completion of m iterations of functions F1 and F2, the coded score g is thus stored in one of the two storage memories. In the example of FIGS. 7a and 7b, it is supposed that m is odd. The coded score {tilde over (S)} is stored in the first storage memory. During evaluation of the function F3, with the coded score {tilde over (S)} on input a first split gate recovers the terms a.sub.i with 1.ltoreq.i.ltoreq.k corresponding to the terms of the scalar product uu'. The summation of these terms produces the score S which is then compared to the predetermined threshold T.
Within the scope of the method described hereinabove the operations to be carried out for generation of the evaluation and verification public keys, and for generation and verification of computation proof can be derived from existing verifiable computation protocols such as Pinocchio, when m=1, and Geppetto, when m>1. The paragraphs hereinbelow describe these operations in more detail as a function of the value of the divider m.
It is to be understood that the embodiment to be described is a particularly advantageous embodiment which is not limiting. The skilled person can use other ways to perform generation of the evaluation and verification public keys, generation and verification of computation proof, and derive said operations from other verifiable existing computation protocols.
Case m=1: In the first mode of operation where m=1, an asymmetric bilinear environment (q, G.sub.1, G.sub.2, G.sub.T, g.sub.1, g.sub.2, e) is defined with q a prime number, G.sub.1, G.sub.2 and G.sub.T three groups of order q, g.sub.1 a generator of G.sub.1, g.sub.2 a generator of G.sub.2, and e a non-degenerate bilinear pairing e: G.sub.1.times.G.sub.2.fwdarw.G.sub.T.
The arithmetic circuit can be represented in the form of a polynomial representation of the circuit Q=(t,V,W,Y) of size .rho. and degree .delta., with V={vi}, W={wi}, Y={yi}, 0.ltoreq.i.ltoreq..rho..
The following are noted hereinbelow:
I.sub.io={1, . . . , .theta.} the set of indices corresponding to the input/output wires of the circuit,
I.sub.mid={.theta.+1, . . . , .rho.} the set of indices of the intermediate wires of the circuit not being input wires of the circuit.
During generation step E3 of a public evaluation key and a public verification key, random variables r.sub.v, r.sub.w, s, .alpha..sub.v, .alpha..sub.w, .alpha..sub.y, .beta., .gamma. are first generated in .sub.q.
Then the following coefficients are defined: r.sub.y=r.sub.vr.sub.w, g.sub.v1=g.sub.1.sup.r.sup.v, g.sub.w1=g.sub.1.sup.r.sup.w, g.sub.w2=g.sub.2.sup.r.sup.w, g.sub.y1=g.sub.1.sup.r.sup.y and g.sub.y2=g.sub.2.sup.r.sup.y.
The public evaluation key EK.sub.F is then generated as equal to (EK.sub.F1, EK.sub.F2) where
.times..times..times..times..function..di-elect cons..times..times..function..di-elect cons..times..times..function..di-elect cons..times..times..alpha..function..di-elect cons..times..times..alpha..function..di-elect cons..times..times..alpha..function..di-elect cons..di-elect cons..delta..times..times..beta..function..times..times..beta..function..- times..times..beta..function..di-elect cons. ##EQU00026## .times..times..times..times..function..di-elect cons. ##EQU00026.2##
The public verification key VK.sub.F is also generated as equal to (VK.sub.F1, VK.sub.F2) where: VK.sub.F1=(g.sub.1,{g.sub.v1.sup.v.sup.i.sup.(s)}.sub.i.di-elect cons.[1,.theta.],{g.sub.y1.sup.y.sup.i.sup.(s)}.sub.i.di-elect cons.[1,.theta.]) VK.sub.F2=(g.sub.2,g.sub.2.sup..alpha..sup.v;g.sub.2.sup..alpha..sup.w,g.- sub.2.sup..alpha..sup.y,g.sub.2.sup..beta..gamma.,g.sub.y2.sup.t(s),{g.sub- .w2.sup.w.sup.i.sup.(s)}.sub.i.di-elect cons.[1,.theta.]).
The remote computation device then obtains E4 the arithmetic circuit and the public evaluation key.
For each biometric datum of the entity, at least one matching value between the biometric datum of the entity and at least one reference biometric datum can then be determined E5 by the remote computation device by evaluating the arithmetic circuit received from the biometric data of the entity and the reference biometric data. The set of values of the circuit {c.sub.i}.sub.i.di-elect cons.[1,.rho.] can then be obtained.
Generation E6 by the remote computation device, for each determined matching value, of a proof of correction of the computation execution of the matching value, so-called generated proof .pi.=(.pi..sub.1,.pi..sub.2) can then comprise:
determination of a polynomial h(x) such that p(x)=h(x)t(x) with p(x)=(v.sub.0(x)+.SIGMA..sub.i=1.sup..rho.c.sub.iv.sub.i(x))(w.sub.0(x)+.- SIGMA..sub.i=1.sup..rho.c.sub.iw.sub.i(x))-(x)+.SIGMA..sub.i=1.sup..rho.c.- sub.iy.sub.i(x)),
computation of:
.pi..times..times..function..times..times..function..times..times..functi- on..function..times..times..alpha..function..times..times..alpha..function- ..times..times..alpha..function..times..times..beta..function..times..time- s..beta..function..times..times..beta..function. ##EQU00027## and .pi..sub.2=(g.sub.w2.sup.W.sup.mid.sup.(s)) where: v.sub.mid(x)=.SIGMA..sub.i.di-elect cons.I.sub.mid c.sub.iv.sub.i(x), w.sub.mid(x)=.SIGMA..sub.i.di-elect cons.I.sub.mid c.sub.iw.sub.i(x) and y.sub.mid=.SIGMA..sub.i.di-elect cons.I.sub.mid c.sub.iy.sub.i(x). The remote computation device then transmits E7 the matching values and said generated proofs to the client device.
The proofs received by the client device are of the form (.pi..sub.r1, .pi..sub.r12) with: .pi..sub.r1 in the form of: (g.sub.v1.sup.V.sup.mid, g.sub.w1.sup.W.sup.mid, g.sub.y1.sup.Y.sup.mid, g.sub.1.sup.H, g.sub.v1.sup.V'.sup.mid, g.sub.w1.sup.W'.sup.mid, g.sub.y1.sup.Y'.sup.mid, g.sub.1.sup.Z) and .pi..sub.r2 in the form g.sub.w2.sup.w.sup.mid.
The client device then verifies E8 each received proof (.pi..sub.r1, .pi..sub.r2) by performing the following equality tests: e(g.sub.v1.sup.v.sup.o.sup.(s)g.sub.v1.sup.v.sup.io.sup.(s)g.sub.v1.sup.V- .sup.mid,g.sub.w2.sup.w.sup.o.sup.(s)g.sub.w2.sup.w.sup.io.sup.(s)g.sub.w2- .sup.W.sup.mid)=e(g.sub.1.sup.H,g.sub.y2.sup.t(s))e(g.sub.y1.sup.y.sup.o.s- up.(s)g.sub.y1.sup.y.sup.io.sup.(s)g.sub.y1.sup.Y.sup.mid,g.sub.2), e((g.sub.v1.sup.V'.sup.mid).sup.d.sup.1(g.sub.w1.sup.W'.sup.mid).sup.d.su- p.2(g.sub.y1.sup.Y'.sup.mid).sup.d.sup.3,g.sub.2)=e((g.sub.v1.sup.V.sup.mi- d).sup.d.sup.1,g.sub.2.sup..alpha..sup.v)e((g.sub.w1.sup.W.sup.mid).sup.d.- sup.2,g.sub.2.sup..alpha..sup.w)e((g.sub.y1.sup.Y.sup.mid).sup.d.sup.3,g.s- ub.2.sup..alpha..sup.y), e((g.sub.1.sup.Z,g.sub.2.sup..gamma.)=e(g.sub.v1.sup.V.sup.midg.sub.w1.su- p.W.sup.midg.sub.y1.sup.Y.sup.mid,g.sub.2.sup..beta..gamma.) where g.sub.v1.sup.v.sup.io.sup.(s)=.PI..sub.i=1.sup..theta.(g.sub.v1.sup.v.sup- .i.sup.(s)).sup.c.sup.i, g.sub.w1.sup.w.sup.io.sup.(s)=.PI..sub.i=1.sup..theta.(g.sub.w1.sup.w.sup- .i.sup.(s)).sup.c.sup.i, and g.sub.y1.sup.y.sup.io.sup.(s)=.PI..sub.i=1.sup..theta.(g.sub.y1.sup.y.sup- .i.sup.(s)).sup.c.sup.i and (d.sub.1, d.sub.2, d.sub.3) elements of .sub.q on .lamda. bits with .lamda. a security parameter. In this mode of operation the verification step of said received proofs therefore comprises batch verification of pairings.
Case m>1:
Bank B is called a sub-set of indices [1, .rho.] (in other words a sub-set of the circuit wires) and an instance of a bank B is a set of values for these indices (for example noted {c.sub.j}.sub.j.di-elect cons.B).
The function F is divided into .omega. sub-functions F.sub.1, . . . , F.sub..omega.. For example in the case of FIGS. 6 and 7 selection can be made respectively .omega.=2 and .omega.=3 as described hereinabove.
.sigma.=((f.sub.l, (T.sub.l1, . . . , T.sub.ll))).sub.l.di-elect cons.[1,L] is defined as a scheduling of length L with f.sub.l.di-elect cons.{1, . . . , .omega.} the index of the function to be computed.
By way of example, in the case m=2 or m=3 described hereinabove in reference to FIGS. 6a to 6c, L=m+1 and the function F is split into two functions F.sub.1, F.sub.2.
The banks used are: (B.sub.io, B.sub.L.sub.1, B.sub.L.sub.2, B.sub.B.sub.1, . . . , B.sub.B.sub.m) where:
B.sub.io: banks of input/output type. Number of instances: m+1 B.sub.L.sub.1: bank of local type for F1. Number of instances: m B.sub.L.sub.2: bank of local type for F2. Number of instances: 1 B.sub.B.sub.1, . . . , B.sub.B.sub.m: banks of bus type. An instance of each. The scheduling of proofs, of length m+1, is: .sigma.=((1,(1,1,0,1,0, . . . 0)), . . . ,(1,(m,m,0, . . . ,1)),(2,(m+1,0,1, . . . ,1))) In other words, the scheduling of proofs is: For l.di-elect cons.{1, . . . , m}: digest of B.sub.L.sub.1.sup.(l), pledging of B.sub.B.sub.l, proof with B.sub.L.sub.1.sup.(l), inputs B.sub.io.sup.(l), and bus B.sub.B.sub.l. For l=m+1: digest of B.sub.L.sub.2, proof with B.sub.L.sub.2, inputs B.sub.io.sup.(l), and all buses B.sub.B.sub.1, . . . , B.sub.B.sub.m. By way of example, in the case m.gtoreq.4 described hereinabove in reference to FIGS. 7a and 7b, the function F is split into three functions F.sub.1, F.sub.2, F.sub.3. The banks used are: (B.sub.io, B.sub.L1, B.sub.L2, B.sub.L2, B.sub.B1, B.sub.B2) where: B.sub.io: banks of input/output type. Number of instances: m+1 B.sub.L.sub.1: bank of local type for F.sub.1. Number of instances: .left brkt-top.m/2.right brkt-bot. B.sub.L.sub.2: bank of local type for F.sub.2. Number of instances: .left brkt-top.m/2.right brkt-bot. B.sub.L.sub.3: bank of local type for F.sub.3. Number of instances: 1 B.sub.B.sub.1, B.sub.B.sub.2: banks of bus type. .left brkt-top.m/2.right brkt-bot. instances of the first .left brkt-top.m/2.right brkt-bot. instances of the second. The scheduling of proofs, of length m+1, is: .sigma.=(.sigma..sub.1,.sigma..sub.2, . . . .sigma..sub.m,.sigma..sub.m+1) where: For l .di-elect cons.{1, . . . , m}: If l odd: digest of B.sub.L.sub.1.sup.(.left brkt-top.l/2.right brkt-bot.), pledging of B.sub.B.sub.1, proof with B.sub.L.sub.1.sup.(.left brkt-top.l/2.right brkt-bot.), inputs B.sub.io.sup.(l), and bus B.sub.B.sub.1. .sigma..sub.l=(1,(l,.left brkt-top.l/2.right brkt-bot.,0,0,.left brkt-top.l/2.right brkt-bot.,.left brkt-top.l/2.right brkt-bot.-1)) If l even: digest of B.sub.L.sub.2.sup.(.left brkt-top.l/2.right brkt-bot.), pledging of B.sub.B.sub.2, proof with B.sub.L.sub.2.sup.(.left brkt-top.l/2.right brkt-bot.), inputs B.sub.io.sup.(l), and bus B.sub.B.sub.2 . . . .sigma..sub.l=(2,(l,0,.left brkt-top.l/2.right brkt-bot.,0,.left brkt-top.l/2.right brkt-bot.-1,.left brkt-top.l/2.right brkt-bot.)) For l=m+1: digest of B.sub.L.sub.3, proof with B.sub.L.sub.3, inputs B.sub.io.sup.(l), and the bus bank B.sub.B.sub.1 (if m is odd) or B.sub.B.sub.2 (if not). .sigma..sub.l=(3,(m+1,0,0,1,.left brkt-top.l-1/2.right brkt-bot.,0)) or .sigma..sub.l=(3,+1,0,0,1,0,.left brkt-top.l-1/2.right brkt-bot.)). For a number x the notation .left brkt-top.x/2.right brkt-bot. (respectively .left brkt-bot.x/2.right brkt-bot.) designates the natural integer greater than or equal (respectively less then or equal) to the rational value x/2. For more information on the use of banks and such scheduling, the paragraphs hereinbelow can be viewed in the light of the publication referenced hereinabove describing the Geppetto protocol from which the protocol presented hereinbelow is derived.
In these second and third modes of operation, an asymmetric bilinear environment (q, G.sub.1, G.sub.2, G.sub.T, g.sub.1, g.sub.2, e) is defined with q a prime number, G.sub.1, G.sub.2 and G.sub.T three groups of order q, g.sub.1 a generator of G.sub.1, g.sub.2 a generator of G.sub.2, and e a non-degenerate bilinear pairing e: G.sub.1.times.G.sub.2.fwdarw.G.sub.T.
The arithmetic circuit can be represented in the form of a multi-QAP Q=({B.sub.b}.sub.b.di-elect cons.[1,l], t, V, W, Y) of size .rho. and degree .delta., with {B.sub.b}.sub.b.di-elect cons.[1,l] a set of l banks B.sub.b of Q used in computing the function F, and V={vi}, W={wi}, Y={yi} with 0.ltoreq.i.ltoreq..rho..
During the generation step E3 by the client device of a public evaluation key and a public verification key, random variables s,{(.alpha..sub.bv, .alpha..sub.bw, .alpha..sub.by, .beta..sub.b, .gamma..sub.b)}.sub.b.di-elect cons.[1,l], r.sub.v, r.sub.w are generated in .sub.q.
Next, the following coefficients are defined: r.sub.y=r.sub.vr.sub.w, g.sub.v1=g.sub.1.sup.r.sup.v, g.sub.v2=g.sub.2.sup.r.sup.v, g.sub.w1=g.sub.1.sup.r.sup.w, g.sub.w2=g.sub.2.sup.r.sup.w, g.sub.y1=g.sub.1.sup.r.sup.y and g.sub.y2=g.sub.2.sup.r.sup.y.
The public evaluation key EK.sub.F is generated as equal to: ({EK.sub.Fb}.sub.b.di-elect cons.[1,l],{g.sub.1.sup.s.sup.i}.sub.i.di-elect cons.[1,.delta.],g.sub.v1.sup.t(s),g.sub.w1.sup.t(s),g.sub.y1.sup.t(s),g.- sub.v2.sup.t(s),g.sub.w2.sup.t(s),g.sub.y2.sup.t(s)) Each public bank key EK.sub.Fb is equal to (EK.sub.Fb1, EK.sub.Fb2) and generated by computing:
.times..times..times..times..function..times..times..function..times..tim- es..function..times..times..alpha..function..times..times..alpha..function- ..times..times..alpha..function..times..times..beta..function..times..time- s..beta..function..times..times..beta..function..di-elect cons..times..times..alpha..function..times..times..alpha..function..times- ..times..alpha..function..times..times..beta..function..times..times..beta- ..function..times..times..beta..function. ##EQU00028## .times..times..times..times..times..function..di-elect cons..times..times..alpha..function. ##EQU00028.2##
The public verification key VK.sub.F is also generated as equal to: ({VK.sub.Fb}.sub.b.di-elect cons.[1,l], g.sub.1, g.sub.2, g.sub.y2.sup.t(s)). Each public bank key VK.sub.Fb is equal to (g.sub.2.sup..alpha..sup.bv, g.sub.2.sup..alpha..sup.bw, g.sub.2.sup..alpha..sup.by, g.sub.2.sup..gamma..sup.b, g.sub.2.sup..beta..sup.b.sup..gamma..sup.b).
The remote computation device obtains E4 the arithmetic circuit and the public evaluation key.
For each biometric datum of the entity, at least one matching value between said biometric datum and at least one reference biometric datum can then be determined E5 by the remote computation device by evaluating the arithmetic circuit received from the biometric data of the entity and the reference biometric data. The remote computation device evaluates each sub-function F.sub..omega. from the biometric data of the entity and the reference biometric data for obtaining the matching value and the values of the circuit.
Generation E6 by the remote computation device, for each determined matching value, of a proof of correction of the computation execution of the matching value can comprise for each l={1, . . . , L} a list of digests and proofs obtained as described hereinbelow.
Let .LAMBDA.[1,l] be the set of indices b.di-elect cons.[1,l] such that T.sub.lb.noteq.0 in the scheduling .sigma.=((f.sub.l, (T.sub.l1, . . . , T.sub.ll))).sub.l.di-elect cons.[1,L].
Hereinbelow the following: .GAMMA.=U.sub.b.SIGMA..LAMBDA.B.sub.b, {c.sub.j}.sub.j.di-elect cons.B.sub.b an instance of the bank B.sub.b and .DELTA.={c.sub.i}.sub.i.di-elect cons..GAMMA. the set of values of .GAMMA..
For each bank B.sub.b such as b.di-elect cons..LAMBDA.,
the remote computation device generates pledging random variables o.sub.b=(o.sub.bv, o.sub.bw, o.sub.by) in .sub.q.
it then computes the digest D.sub.b equal to (D.sub.b1, D.sub.b2) from the instance of the bank of variables B.sub.b: B.sub.b.sup.(T.sup.lb.sup.)={c.sub.i.di-elect cons..DELTA.}.sub.i.di-elect cons.B.sub.b and pledging random variables o.sub.b. Such digests are such that: if the bank B.sub.b is an input/output bank: D.sub.b1=(g.sub.v1.sup.v.sup.(b).sup.(s), g.sub.y1.sup.y.sup.(b).sup.(s)) and D.sub.b2=(g.sub.w1.sup.w.sup.(b).sup.(s)), if the bank B.sub.b is not an input/output bank:
.times..times..times..times..function..times..times..function..times..tim- es..function..times..times..alpha..function..times..times..alpha..function- ..times..times..alpha..function..times..times..beta..function..times..time- s..beta..function..times..times..beta..function. ##EQU00029## .times..times..times..times..function. ##EQU00029.2## with: v.sup.(b)(s)=.SIGMA..sub.i.di-elect cons.B.sub.bc.sub.iv.sub.i(s)+o.sub.bvt(s), w.sup.(b)(s)=.SIGMA..sub.i.di-elect cons.B.sub.bc.sub.iw.sub.i(s)+o.sub.bwt(s), y.sup.(b)(s)=.SIGMA..sub.i.di-elect cons.B.sub.bc.sub.iy.sub.i(s)+o.sub.byt(s), The remote computation device then determines a polynomial h.sup.(l)(x) such that p.sup.(l)(x)=h.sup.(l)(x)t(x) with p.sup.(l)(x)=(v.sub.0(x)+.SIGMA..sub.i.di-elect cons..GAMMA.c.sub.iv.sub.j(x)+.SIGMA..sub.b.di-elect cons..LAMBDA.o.sub.bvt(x))(w.sub.0(x)+.SIGMA..sub.i.di-elect cons..GAMMA.c.sub.iw.sub.j(x)+.SIGMA..sub.b.di-elect cons..LAMBDA.o.sub.bwt(x))-(y.sub.0(x)+.SIGMA..sub.i.di-elect cons..GAMMA.c.sub.iy.sub.j(x)+.SIGMA..sub.b.di-elect cons..LAMBDA.o.sub.byt(x)) Finally, it computes a proof element .pi..sup.(l) equal to g.sub.1.sup.h.sup.(l).sup.(s).
The remote computation device then transmits E7 the matching values and said generated proofs comprising the list of computed digests and proof elements to the client device.
The proofs received by the client device are of the form of: D.sub.1.sup.(1), . . . , D.sub.l.sup.(1), .pi..sup.(1), . . . , D.sub.1.sup.(L), . . . , D.sub.l.sup.(L), .pi..sup.(L) where for all l.di-elect cons.{1, . . . , L} and .di-elect cons.{1, . . . ,l}:
.times..times..times..times..times..times..times..times.'.times..times..t- imes..times.'.times..times..times..times.'.times..times..times..times. ##EQU00030## and .pi..sup.(l)=g.sub.1.sup.H.sup.(l).
Two verification implementation variants of the received proof E8 are specified hereinbelow.
In a first implementation variant, the client device then verifies each received proof by performing: verification of Le digests, for l.di-elect cons.{1, . . . , L} and b.di-elect cons.{1, . . . , l} comprising the following equality tests:
.function..times..times.'.times..times..alpha..function..times..times. ##EQU00031## .function..times..times.'.function..alpha..function..times..times. ##EQU00031.2## .function..times..times.'.times..times..alpha..function..times..times. ##EQU00031.3## .function..gamma..function..times..times..times..times..times..times..bet- a..gamma. ##EQU00031.4## verification of L proofs comprising for l.di-elect cons.{1, . . . , L} the following equality test:
.function. .times..times..times. .times..times..times..times..function..times..times..function..function. .times..times..times. ##EQU00032##
In a second implementation variant, the client device then verifies each received proof by executing batch verification comprising, given a correction parameter .lamda.: selection of a random vector (d.sub.1, . . . , d.sub.3l) of elements of size .lamda., batch verification of the Ll digests, in l times by executing the following equality tests, for b.di-elect cons.{1, . . . , l}:
.function..times..times..times..times.'.function..alpha..function..times.- .times..times.'.function..alpha..function..times..times..times..times.'.fu- nction..alpha..function..times..times..times..times..times..times..times..- times..times..times..times..times. ##EQU00033## .times..function..times..times..gamma..function..times..times..times..tim- es..times..times..times..times..beta..gamma. ##EQU00033.2## batch verification the L proofs by executing the following equality test:
.times..function. .times..times..times..times. .times..times..times..function..times..times..times..function..function..- times. .times..times..times. ##EQU00034## and as a verification option of the belonging of elements on which the pairings is applied to their respective groups.
The method performed carries out biometric identification by comparing biometric data in terms of the scope of a publicly verifiable computation protocol and minimizing the time necessary for production and verification of proofs relative to proper execution of this computation, by way of minimization of the number of multipliers employed to represent this computation in the form of an arithmetic circuit.
* * * * *
D00000

D00001

D00002

D00003

D00004

D00005

D00006

D00007

D00008

D00009

D00010

D00011

D00012

M00001

M00002

M00003

M00004
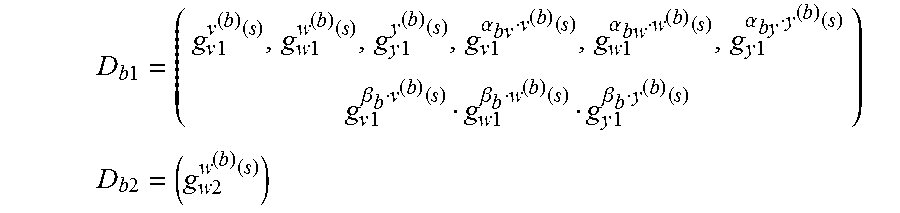
M00005

M00006

M00007

M00008

M00009

M00010

M00011

M00012

M00013

M00014
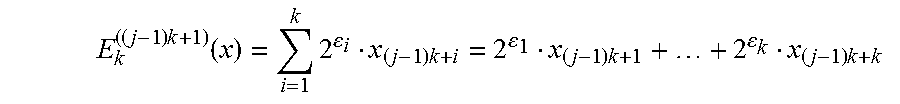
M00015

M00016

M00017

M00018

M00019

M00020

M00021

M00022

M00023

M00024

M00025

M00026

M00027

M00028

M00029

M00030

M00031

M00032

M00033

M00034

M00035

M00036

M00037

M00038

M00039

M00040

M00041
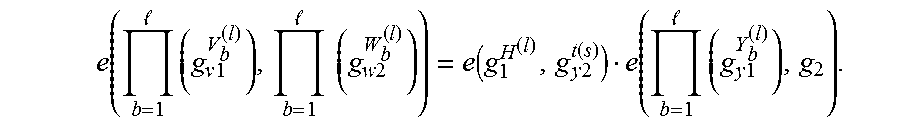
M00042

M00043
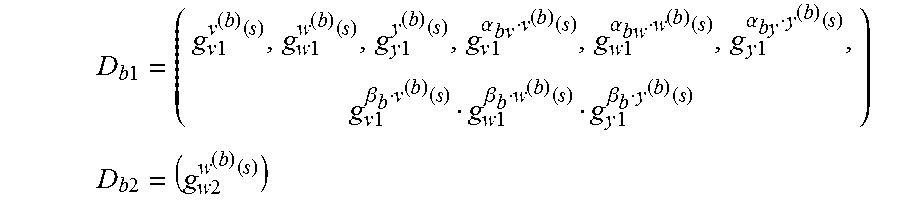
M00044

M00045

M00046

M00047

M00048

P00001

P00002

XML
uspto.report is an independent third-party trademark research tool that is not affiliated, endorsed, or sponsored by the United States Patent and Trademark Office (USPTO) or any other governmental organization. The information provided by uspto.report is based on publicly available data at the time of writing and is intended for informational purposes only.
While we strive to provide accurate and up-to-date information, we do not guarantee the accuracy, completeness, reliability, or suitability of the information displayed on this site. The use of this site is at your own risk. Any reliance you place on such information is therefore strictly at your own risk.
All official trademark data, including owner information, should be verified by visiting the official USPTO website at www.uspto.gov. This site is not intended to replace professional legal advice and should not be used as a substitute for consulting with a legal professional who is knowledgeable about trademark law.