Near-Capacity Iterative Detection of Co-Channel Interference for A High-Efficiency Multibeam Satellite System
BEIDAS; Bassel F. ; et al.
U.S. patent application number 16/784207 was filed with the patent office on 2021-05-27 for near-capacity iterative detection of co-channel interference for a high-efficiency multibeam satellite system. This patent application is currently assigned to Hughes Network Systems, LLC. The applicant listed for this patent is Bassel F. BEIDAS, Rohit Iyer SESHADRI. Invention is credited to Bassel F. BEIDAS, Rohit Iyer SESHADRI.
| Application Number | 20210159923 16/784207 |
| Document ID | / |
| Family ID | 1000004651551 |
| Filed Date | 2021-05-27 |


View All Diagrams
| United States Patent Application | 20210159923 |
| Kind Code | A1 |
| BEIDAS; Bassel F. ; et al. | May 27, 2021 |
Near-Capacity Iterative Detection of Co-Channel Interference for A High-Efficiency Multibeam Satellite System
Abstract
A communications apparatus to receive a composite signal including a desired signal and interferer signals, where the desired signal may include desired symbols and the interferer signals may include interferer symbols. The system may include N frameworks, each framework may include a detector to partition the desired symbols and the interferer symbols based on an interference severity into a dominant group and a non-dominant group, and to generate A Posteriori Probabilities (APP) of the desired symbols and the interferer symbols. The detector of each of the N frameworks generates the APP based on a feedback of a priori probabilities from each of the N frameworks.
| Inventors: | BEIDAS; Bassel F.; (Germantown, MD) ; SESHADRI; Rohit Iyer; (Germantown, MD) | ||||||||||
| Applicant: |
|
||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|
| Assignee: | Hughes Network Systems, LLC Germantown MD |
||||||||||
| Family ID: | 1000004651551 | ||||||||||
| Appl. No.: | 16/784207 | ||||||||||
| Filed: | February 6, 2020 |
Related U.S. Patent Documents
| Application Number | Filing Date | Patent Number | ||
|---|---|---|---|---|
| 62939928 | Nov 25, 2019 | |||
| Current U.S. Class: | 1/1 |
| Current CPC Class: | H04B 17/345 20150115; H03M 13/3933 20130101; H03M 13/3927 20130101; H03M 13/3911 20130101; H04B 7/18513 20130101 |
| International Class: | H03M 13/39 20060101 H03M013/39; H04B 7/185 20060101 H04B007/185; H04B 17/345 20060101 H04B017/345 |
Claims
1. A communications apparatus comprising: a composite signal comprising a desired signal and interferer signals, wherein the desired signal comprises desired symbols and the interferer signals comprise interferer symbols; and N frameworks, each framework comprising a detector to partition the desired symbols and the interferer symbols based on an interference severity into a dominant group and a non-dominant group, and to generate A Posteriori Probabilities (APP) of the desired symbols and the interferer symbols, wherein the detector of each of the N frameworks generates the APP based on a feedback of a priori probabilities from each of the N frameworks.
2. The communications apparatus of claim 1, wherein the detector of each of the N frameworks transforms the APP to a first Log-Likelihood Ratios (LLRs) using a bit-to-symbol mapping rule, and each of N frameworks further comprises a deinterleaver to deinterleave the first LLRs into a decoder input, a Forward Error Correcting (FEC) Decoder to decode the decoder input and to generate a second LLRs from a decoded decoder input, and an interleaver to interleave the second LLRs, wherein the second LLRs are treated as a priori probabilities for a respective N framework after the interleaver of the respective N framework, and the second LLRs of each of the N frameworks represent either the desired symbols or the interferer symbols.
3. The communications apparatus of claim 2, wherein the desired signal is more robust than each of the interferer signals, and the second LLRs from the FEC decoder of a first framework of the N frameworks represent the desired symbols.
4. The communications apparatus of claim 2, wherein at least one of the interferer signals is more robust than the desired signal, and the second LLRs from the FEC decoder of a framework other than a first framework of the N frameworks represent the desired symbols.
5. The communications apparatus of claim 4, wherein the desired symbols are recovered by Simultaneous Decoding (SD) or by Simultaneous Non-unique Decoding (SND).
6. The communications apparatus of claim 1, wherein the detector is selected from a Soft-In Soft-Out (SISO) detector, a Divide-And-Conquer (DAC) detector or a SISO DAC detector.
7. The communications apparatus of claim 1, wherein the communications apparatus is disposed in an SISO Iterative Divide and Conquer (IDAC) receiver and the detector is a SISO DAC detector.
8. The communications apparatus of claim 1, wherein the dominant group comprises an Optimal-Bayesian (OB) group via a probability mass function (pmf).
9. The communications apparatus of claim 1, wherein the non-dominant group comprises a Noise-Floor (NF) group incorporated via a power of each member and a Subtractive-Cancellation (SC) group incorporated via first- and second-order moments derived from the a priori probabilities, and the dominant group comprises an Optimal-Bayesian (OB) group incorporated via a probability mass function (pmf).
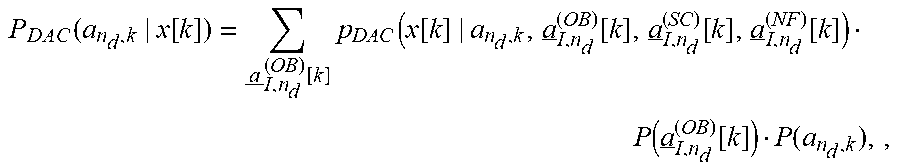
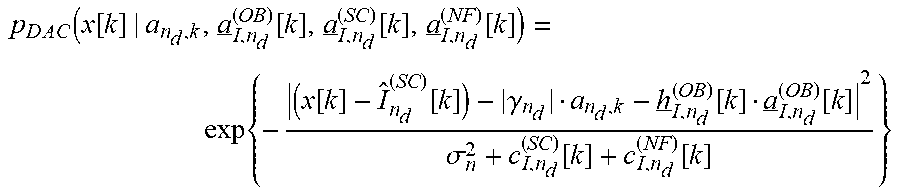
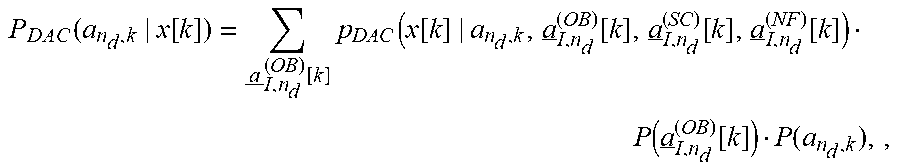
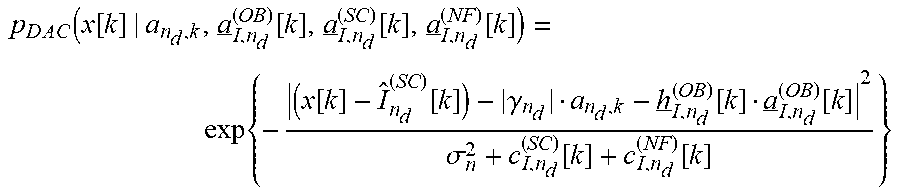
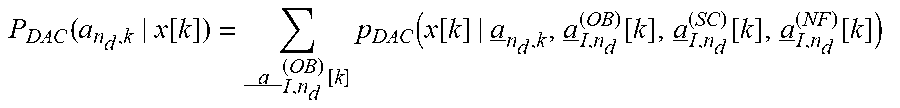
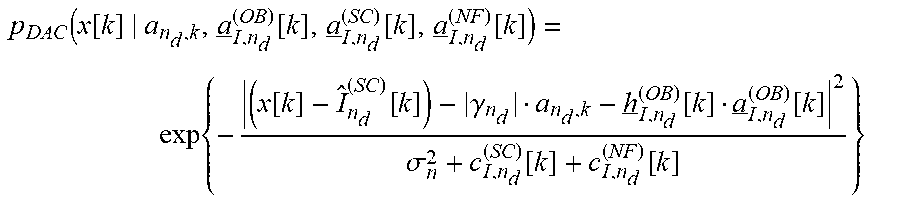
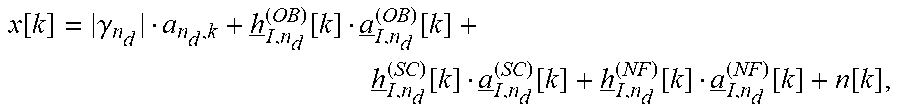
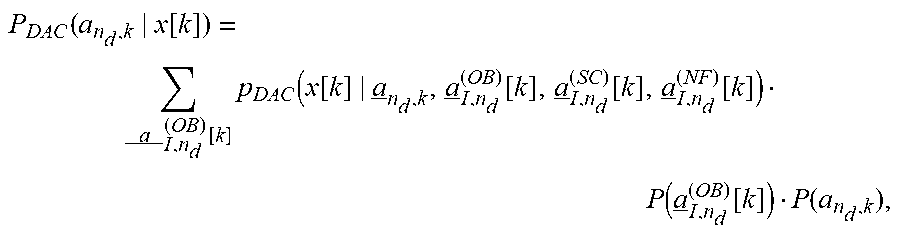
10. The communications apparatus of claim 9, wherein an output x [ k ] = .gamma. n d a n d , k + h _ I , n d ( OB ) [ k ] a _ I , n d ( OB ) [ k ] + h _ I , n d ( SC ) [ k ] a _ I , n d ( SC ) [ k ] + h _ I , n d ( NF ) [ k ] a _ I , n d ( NF ) [ k ] + n [ k ] , ##EQU00016## where a.sub.i,nd [k] partitioned into three groups, a.sub.I,n.sub.d.sup.(NF)[k], a.sub.I,n.sub.d.sup.(SC)[k], a.sub.I,n.sub.d.sup.(OB)[k], and h.sub.I,n.sub.d.sup.(NF)[k], h.sub.I,n.sub.d.sup.(SC)[k], h.sub.I,n.sub.d.sup.(OB)[k] represents spatial and temporal CCI channel coefficients corresponding to the NF group, the SC group and the OB group, respectively.
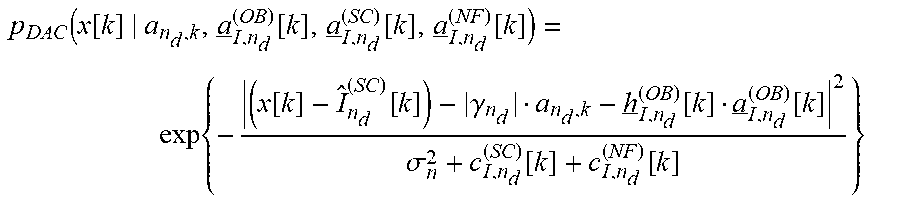
11. The communications apparatus of claim 10, wherein the detector is P DAC ( a n d , k | x [ k ] ) = a _ I , n d ( OB ) [ k ] p DAC ( x [ k ] | a _ n d , k , a _ I , n d ( OB ) [ k ] , a _ I , n d ( SC ) [ k ] , a _ I , n d ( NF ) [ k ] ) ##EQU00017## mathematically expressed as P(a.sub.I,n.sub.d.sup.(OB)[k])P(a.sub.n.sub.d.sub.,k), where p.sub.DAC( ) is p DAC ( x [ k ] | a n d , k , a _ I , n d ( OB ) [ k ] , a _ I , n d ( SC ) [ k ] , a _ I , n d ( NF ) [ k ] ) = exp { - ( x [ k ] - I ^ n d ( SC ) [ k ] ) - .gamma. n d a n d , k - h _ I , n d ( OB ) [ k ] a _ I , n d ( OB ) [ k ] 2 .sigma. n 2 + c I , n d ( SC ) [ k ] + c I , n d ( NF ) [ k ] } ##EQU00018## a likelihood function associated with observing x[k], P( ) is the a priori probabilities corresponding to the second LLRs representing the desired symbols, I.sub.n.sub.d.sup.(SC)[k]=h.sub.I,n.sub.d.sup.(SC)[k]{a.sub.I,n.sub.d.sup- .(SC)[k]}, c.sub.I,n.sub.d.sup.(SC)[k]=h.sub.I,n.sub.d.sup.(SC)[k]Cov{a.su- b.I,n.sub.d.sup.(SC)[k]}(h.sub.I,n.sub.d.sup.(SC)[k]).sup.H, and c.sub.I,n.sub.d.sup.(NF)[k]=h.sub.I,n.sub.d.sup.(NF)[k](h.sub.I,n.sub.d.s- up.(NF)[k]).sup.H.
12. The communications apparatus of claim 1, wherein a count of the N frameworks is selected from one (1), two (2) or three (3).
13. The communications apparatus of claim 1, wherein the desired signal and the interferer signals comprise DVB-S2X standard compliant signals.
14. A computer implemented method comprising: providing a composite signal comprising a desired signal and interferer signals, wherein the desired signal comprises desired symbols and the interferer signals comprise interferer symbols; and iteratively computing, N frameworks, each framework comprising partitioning the desired symbols and the interferer symbols based on an interference severity into a dominant group and a non-dominant group, and generating A Posteriori Probabilities (APP) of the desired symbols and the interferer symbols, wherein the detector of each of the N frameworks generates the APP based on a feedback of a priori probabilities from each of the N frameworks.
15. The method of claim 14, wherein the detector of each of the N frameworks transforms the APP to a first Log-Likelihood Ratios (LLRs) using a bit-to-symbol mapping rule, and the iteratively computing further comprises: deinterleaving the first LLRs into a decoder input, decoding the decoder input, generating a second LLRs from a decoded decoder input and interleaving the second LLRs, wherein the second LLRs are treated as a priori probabilities for a respective N framework after the interleaver of the respective N framework, and the second LLRs of each of the N frameworks represent either the desired symbols or the interferer symbols.
16. The method of claim 15, wherein the desired signal is more robust than each of the interferer signals, and the second LLRs from the decoding of a first framework of the N frameworks represent the desired symbols.
17. The method of claim 15, wherein at least one of the interferer signals is more robust than the desired signal, and the second LLRs from the decoding of a framework other than a first framework of the N frameworks represent the desired symbols.
18. The method of claim 14, wherein the non-dominant group comprises a Noise-Floor (NF) group incorporated via a power of each member and a Subtractive-Cancellation (SC) group incorporated via first- and second-order moments derived from the a priori probabilities, and the dominant group comprises an Optimal-Bayesian (OB) group incorporated via a probability mass function (pmf).
19. The method of claim 18, wherein an output x[k] is, x [ k ] = .gamma. n d a n d , k + h _ I , n d ( OB ) [ k ] a _ I , n d ( OB ) [ k ] + h _ I , n d ( SC ) [ k ] a _ I , n d ( SC ) [ k ] + h _ I , n d ( NF ) [ k ] a _ I , n d ( NF ) [ k ] + n [ k ] , ##EQU00019## where a.sub.i,nd [k] is partitioned into three groups, a.sub.I,n.sub.d.sup.(NF)[k], a.sub.I,n.sub.d.sup.(SC)[k], a.sub.I,n.sub.d.sup.(OB)[k], and h.sub.I,n.sub.d.sup.(NF)[k], h.sub.I,n.sub.d.sup.(SC)[k], h.sub.I,n.sub.d.sup.(OB)[k], represents spatial and temporal CCI channel coefficients corresponding to the NF group, the SC group and the OB group, respectively.
20. The method of claim 19, wherein the detector is mathematically expressed as P DAC ( a n d , k | x [ k ] ) = a _ I , n d ( OB ) [ k ] p DAC ( x [ k ] | a _ n d , k , a _ I , n d ( OB ) [ k ] , a _ I , n d ( SC ) [ k ] , a _ I , n d ( NF ) [ k ] ) P ( a _ I , n d ( OB ) [ k ] ) P ( a n d , k ) , ##EQU00020## where pDAC( ) is p DAC ( x [ k ] | a n d , k , a _ I , n d ( OB ) [ k ] , a _ I , n d ( SC ) [ k ] , a _ I , n d ( NF ) [ k ] ) = exp { - ( x [ k ] - I ^ n d ( SC ) [ k ] ) - .gamma. n d a n d , k - h _ I , n d ( OB ) [ k ] a _ I , n d ( OB ) [ k ] 2 .sigma. n 2 + c I , n d ( SC ) [ k ] + c I , n d ( NF ) [ k ] } ##EQU00021## a likelihood function associated with observing x[k], P( ) is the a priori probabilities corresponding to the second LLRs representing the desired symbols, I.sub.n.sub.d.sup.(SC)[k]=h.sub.I,n.sub.d.sup.(SC)[k]{a.sub.I,n.- sub.d.sup.(SC)[k]}, c.sub.I,n.sub.d.sup.(SC)[k]=h.sub.I,n.sub.d.sup.(SC)[k]Cov{a.sub.I,n.sub.- d.sup.(SC)[k]}(h.sub.I,n.sub.d.sup.(SC)[k]).sup.H, and c.sub.I,n.sub.d.sup.(NF)[k]=h.sub.I,n.sub.d.sup.(NF)[k](h.sub.I,n.sub.d.s- up.(NF)[k]).sup.H.
Description
CROSS-REFERENCE TO RELATED APPLICATIONS AND INCORPORATION BY REFERENCE
[0001] The present application claims the benefit under 35 U.S.C. 119(e) of U.S. Provisional Application Ser. No. 62/939,928, filed Nov. 25, 2019, which is incorporated herein by reference in its entirety.
FIELD
[0002] A receiver to improve spectral efficiency in a multibeam satellite system with Co Channel Interference (CCI), in particular, systems that employ aggressive frequency reuse. The receiver successfully mitigates CCI by compensating for memory effects compounding the CCI which are unavoidable in a multibeam satellite system. The receiver may be deployed at a user terminal. In the present teachings, an exemplary receiver is presented for satellite applications; however, the receiver of the present teachings may be applied in other radio communications systems, such as cellular (e.g., 4G, LTE, or 5G) and WiFi.
BACKGROUND
[0003] In the prior art, precoding and beamforming techniques are limited by the accuracy of Channel State Information (CSI) information available at the gateway. Additionally, precoding techniques are also limited by the lack of feeder-link bandwidth. Compensating for CCI at a receiver, for example, a user terminal, overcomes the above limitations.
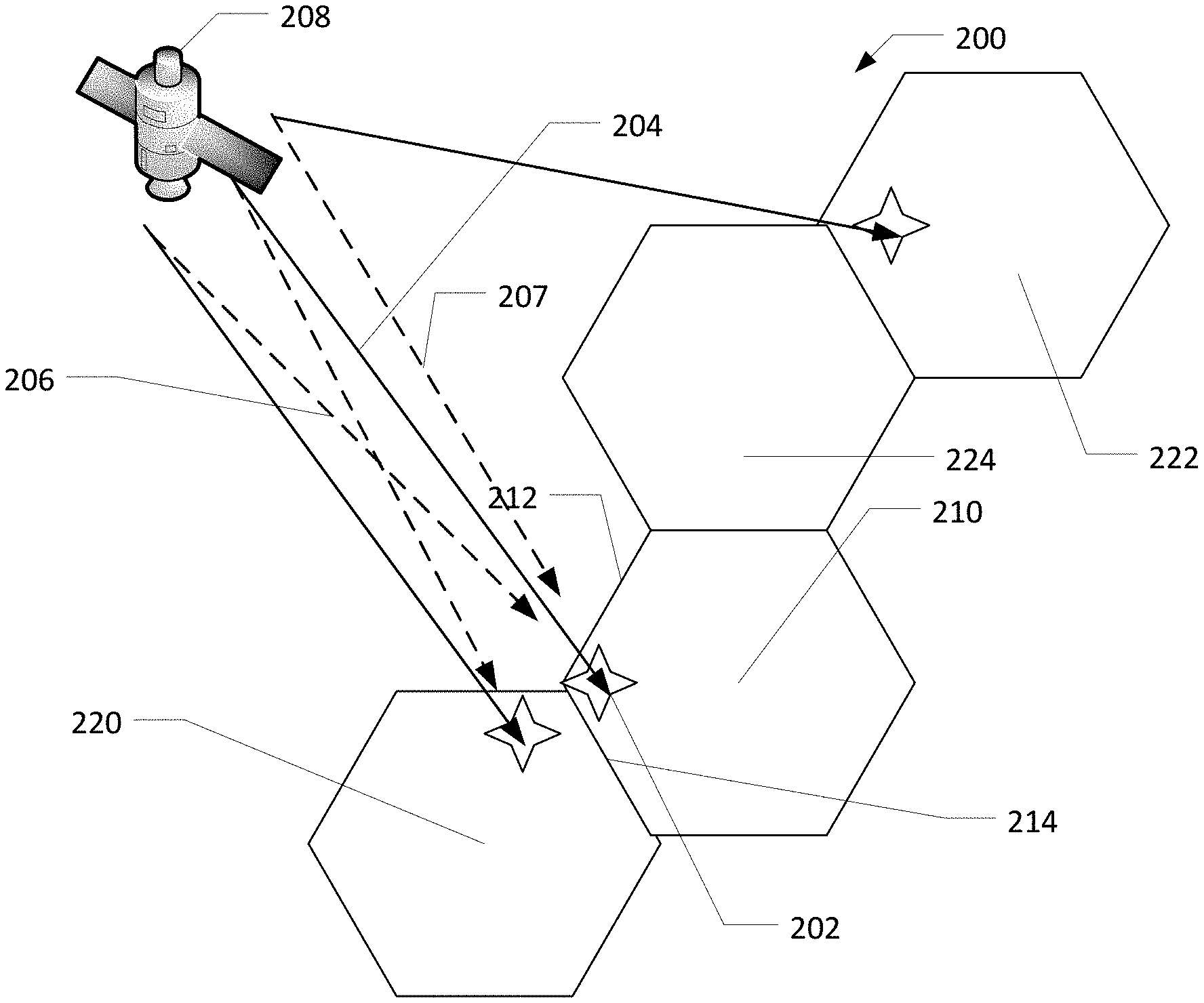
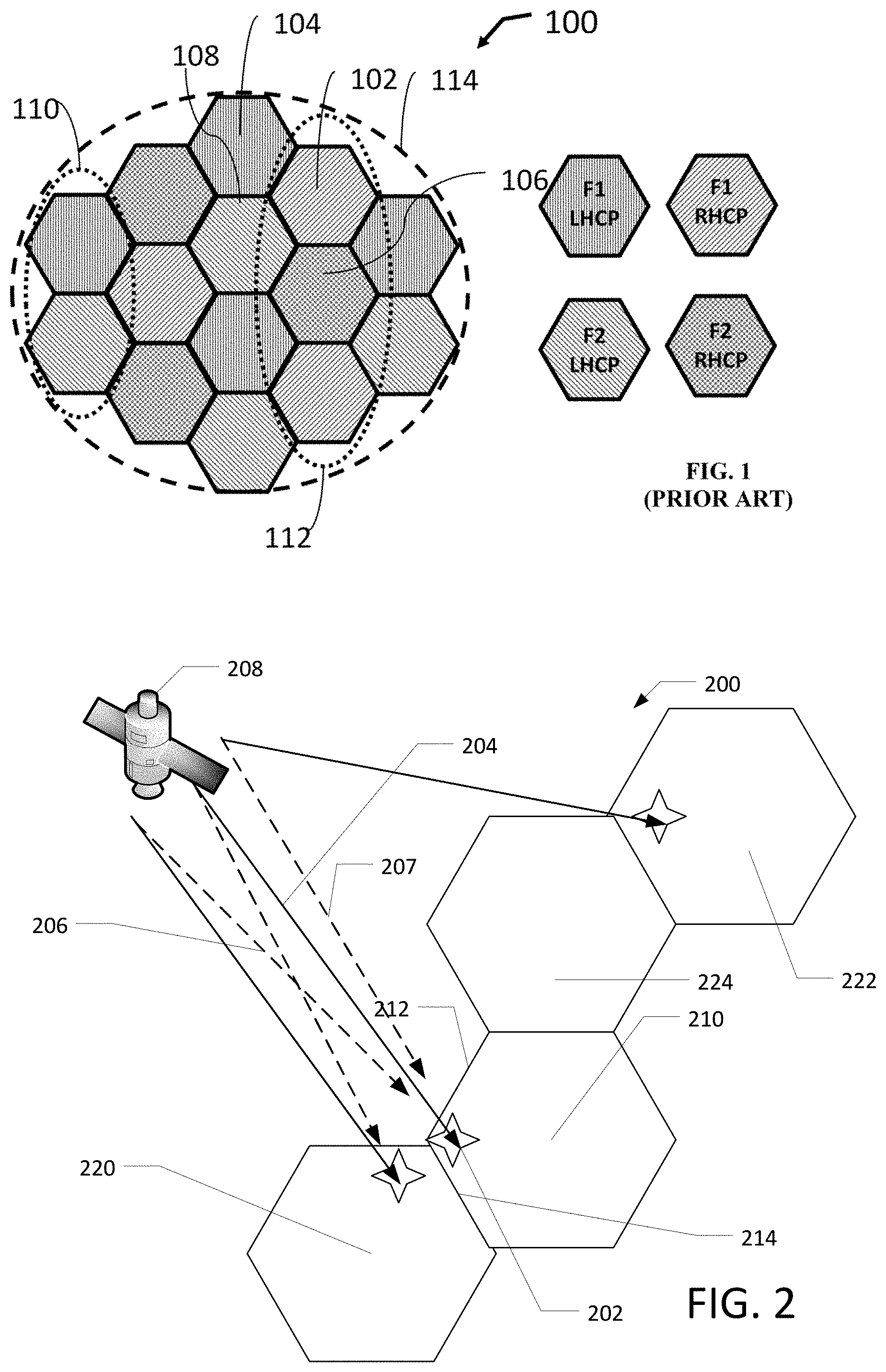
[0004] A multibeam satellite system employs frequency reuse in which different beams share the same frequency resource or bandwidth. Beams sharing bandwidth are known as co-channel beams. The closer the two co-channel beams are located geographically, the greater is the co-channel interference (CCI). CCI can have devastating impact on the performance, hence prior art systems maintain CCI at acceptable levels by typically employing a reuse factor of 4, illustrated in FIG. 1, where the total system bandwidth B is divided into two parts on each antenna polarization, such that each beam has bandwidth of B/2.
[0005] FIG. 1 illustrates a prior art beam laydown pattern with a 4-reuse plan for a multi-beam satellite, according to various embodiments.
[0006] FIG. 1 illustrates a reuse plan combining signal polarization and non-overlapping frequency spectrums to create a 4-reuse plan 100. In the example, the four colors (hashing in FIG. 1) correspond to four different frequency/polarization allocations. An available frequency spectrum is divided into two frequency sub-bands F1 and F2 and each sub-band is assigned/mapped to a different color, and two orthogonal polarizations are assigned/mapped colors to provide the two other colors in the 4-color reuse plan. A service or coverage area 114 may be divided into cells. Multi-beam satellites typically illuminate multiple hexagonal cells within a service area 114. In exemplary embodiments, a cell 102 may be illuminated by a far field beam pattern in band F1 using a right hand circular polarization (RHCP), a cell 104 in band F1 may be illuminated by a far field beam pattern in band F1 using a left hand circular polarization (LHCP), a cell 106 may be illuminated by a far field beam pattern in F2 using a RHCP and a cell 108 which may be illuminated by a far field beam pattern in F2 using a LHCP A multi-beam satellite implementing a reuse plan may arrange the two polarizations in separate alternate rows, for example, a LHCP row 110 and a RHCP row 112. It is possible to tessellate a desired coverage area, such as, earth's surface, using an Nc color reuse tessellate where Nc is any positive natural number. A one-color and two-color is also known. Moreover, a 3 or 7-color reuse plan, each of which use both polarizations, is also known.
[0007] The very high capacity required by the next generation of broadband satellites makes it necessary to adopt more aggressive reuse factors such as reuse 2 and reuse 1 in which each beam can make use of the entire bandwidth B. Under such deployments, users at the edge of the co-channel cells experience severe CCI which adversely affects their data rate and quality of service.
[0008] The CCI mitigation techniques applied at the satellite gateway such as precoding and beamforming are well known. The effectiveness of precoding and beamforming depends on the accuracy of the Channel State Information (CSI) (for example, magnitude, phase, and delay) available at the gateway. CSI depends on effective estimation and frequent reporting from user terminals to the gateway. Furthermore, transmitter-based techniques used, for example, at the gateway, are also limited by the feeder-link bandwidth since effective precoding requires that signals transmitted to co-frequency beams come from the same gateway.
[0009] The multiuser detection framework of prior art receivers assumes that CCI is memoryless, namely, that the current receive filter sampled output depends only on the current symbol from CCI. However, memory effects in CCI are inevitable since the desired signal and interfering signals arrive asynchronously at the user terminal. Even though the co-channel beams may be formed and emitted by the satellite simultaneously, they propagate through different paths causing unavoidable differential delays. Further, the beams could be conveying signals originating from multiple gateways, interconnected via terrestrial links. Other sources that generate memory effects include different symbol rates required by co-channel beams and/or using pulse shaping with different rolloff values. Prior art receivers based on optimal realizations handle memory effects with a complexity that is exponential with the number of interferers and the memory span of each CCI source, making such a receiver severely unaffordable. Other receivers suffer from 2 dB of degradation with only moderate timing offset of 15% of the symbol period. Additionally, the memory effects can be made worse due to different symbol rates and/or different roll-off factors employed by the different co-channel beams. These critical limitations motivate the development of low-complexity, innovative solutions that can compensate for CCI with memory at the user terminal and are described in detail in this disclosure.
SUMMARY
[0010] This Summary is provided to introduce a selection of concepts in a simplified form that is further described below in the Detailed Description. This Summary is not intended to identify key features or essential features of the claimed subject matter, nor is it intended to be used to limit the scope of the claimed subject matter.
[0011] In the present teachings, receiver based CCI mitigation alleviates the need for frequent reporting of CSI by the user terminal to the different gateways. Additionally, the receiver-based mitigation overcomes feeder-link bandwidth limitation since it does not require the interfering signals being processed at the user terminal to be generated by the same gateway.
[0012] The present teachings disclose several signal processing innovations absent in the prior art multiuser detection techniques. An innovation is the ability to mitigate memory effects in CCI at a user terminal receiver, having a modular structure, without an exponential increase in the receiver complexity. The receiver mitigates interference terms with computational power commensurate with the intensity level of interference experienced at the user terminal. Extensive performance evaluation of the receiver using state-of-the art MODCODs selected from the DVB-S2X standard demonstrates effectiveness under severe CCI with memory. The performance associated with the receiver is near capacity approaching the limits predicted by information theory.
[0013] A system of one or more computers can be configured to perform particular operations or actions by virtue of having software, firmware, hardware, or a combination of them installed on the system that in operation causes or cause the system to perform the actions. One or more computer programs can be configured to perform operations or actions by virtue of including instructions that, when executed by data processing apparatus, cause the apparatus to perform the actions. One general aspect of a communications apparatus includes processing a composite signal may include a desired signal and interferer signals, where the desired signal may include desired symbols and the interferer signals may include interferer symbols; and N frameworks, each framework may include a detector to partition the desired symbols and the interferer symbols based on an interference severity into a dominant group and a non-dominant group, and to generate A Posteriori Probabilities (APP) of the desired symbols and the interferer symbols. The detector of each of the N frameworks generates the APP based on a feedback of a priori probabilities from each of the N frameworks. Other embodiments of this aspect include corresponding computer systems, apparatus, and computer programs recorded on one or more computer storage devices, each configured to perform the actions of the methods.
[0014] Implementations may include one or more of the following features. The communications apparatus where the detector of each of the N frameworks transforms the APP to a First Log-Likelihood Ratios (LLRs) using a bit-to-symbol mapping rule, and each of N frameworks further may include a deinterleaver to deinterleave the first LLRs into a decoder input, a Forward Error Correcting (FEC) decoder to decode the decoder input and to generate a second LLRs from a decoded decoder input, and an interleaver to interleave the second LLRs, where the second LLR are treated as a priori probabilities for a respective N framework after the interleaver of the respective N framework, and the second LLRs of each of the N frameworks represent either the desired symbols or the interferer symbols.
[0015] In some embodiments, the desired signal is more robust than each of the interferer signals, and the second LLRs from the FEC decoder of a first framework of the N frameworks represent the desired symbols. In some embodiments, at least one of the interferer signals is more robust than the desired signal, and the second LLRs from the FEC decoder of a framework other than a first framework of the N frameworks represent the desired symbols. In some embodiments, the desired symbols are recovered by Simultaneous Decoding (SD) or by Simultaneous Non-Unique Decoding (SND). In some embodiments, the detector is selected from a Soft-In Soft-Out (SISO) detector, a Divide-And-Conquer (DAC) detector or a SISO DAC detector. In some embodiments, the communications apparatus is disposed in an SISO Iterative Divide and Conquer (IDAC) receiver and the detector is a SISO DAC detector. In some embodiments, the dominant group may include an Optimal-Bayesian (OB) group via a probability mass function (pmf). The non-dominant group may include a Noise-Floor (NF) group incorporated via a power of each member and a Subtractive-Cancellation (SC) group incorporated via first- and second-order moments derived from the a priori probabilities, and the dominant group may include an Optimal-Bayesian (OB) group incorporated via a probability mass function (pmf).
[0016] In some embodiments, an output
x [ k ] = .gamma. n d a n d , k + h _ I , n d ( OB ) [ k ] a _ I , n d ( OB ) [ k ] + h _ I , n d ( SC ) [ k ] a _ I , n d ( SC ) [ k ] + h _ I , n d ( NF ) [ k ] a _ I , n d ( NF ) [ k ] + n [ k ] , ##EQU00001##
[0017] where a.sub.i,nd [k] is partitioned into three groups, a.sub.I,n.sub.d.sup.(NF)[k], a.sub.I,n.sub.d.sup.(SC)[k], a.sub.I,n.sub.d.sup.(OB)[k], and h.sub.I,n.sub.d.sup.(NF)[k], h.sub.I,n.sub.d.sup.(SC)[k], h.sub.I,n.sub.d.sup.(OB)[k], represents spatial and temporal CCI channel coefficients corresponding to the NF group, the SC group and the OB group, respectively. In some embodiments, the detector is mathematically expressed as
P D A C ( a n d , k | x [ k ] ) = a _ I , n d ( OB ) [ k ] p DAC ( x [ k ] | a n d , k , a I , n d ( OB ) [ k ] , a I , n d ( SC ) [ k ] , a I , n d ( NF ) [ k ] ) P ( a I , n d ( OB ) [ k ] ) P ( a n d , k ) , , ##EQU00002##
[0018] where p.sub.DAC( ) is
p D A C ( x [ k ] | a n d , k , a I , n d ( OB ) [ k ] , a I , n d ( SC ) [ k ] , a I , n d ( NF ) [ k ] ) = exp { - ( x [ k ] - I ^ n d ( SC ) [ k ] ) - .gamma. n d a n d , k - h _ I , n d ( OB ) [ k ] a _ I , n d ( OB ) [ k ] 2 .sigma. n 2 + c I , n d ( SC ) [ k ] + c I , n d ( NF ) [ k ] } ##EQU00003##
[0019] a likelihood function associated with observing x[k], P( ) is the a priori probabilities corresponding to the second LLRs representing the desired symbols, I.sub.n.sub.d.sup.(SC)[k]=h.sub.I,n.sub.d.sup.(SC)[k]{a.sub.I,n.sub.d.sup- .(SC)[k]}, c.sub.I,n.sub.d.sup.(SC)[k]=h.sub.I,n.sub.d.sup.(SC)[k]ov{a.sub- .I,n.sub.d.sup.(SC)[k]}(h.sub.I,n.sub.d.sup.(SC)[k]).sup.H, and c.sub.I,n.sub.d.sup.(NF)[k]=h.sub.I,n.sub.d.sup.(NF)[k](h.sub.I,n.sub.d.s- up.(NF)[k]).sup.H. In some embodiments, a count of the N frameworks is selected from one (1), two (2) or three (3). In some embodiments, the desired signal and the interferer signals may include DVB-S2X standard compliant signals. Implementations of the described techniques may include hardware, a method or process, or computer software on a computer-accessible medium.
[0020] One general aspect includes a computer implemented method. The method includes providing a composite signal may include a desired signal and interferer signals, where the desired signal may include desired symbols and the interferer signals may include interferer symbols; and iteratively computing, N frameworks, each framework may include partitioning the desired symbols and the interferer symbols based on an interference severity into a dominant group and a non-dominant group, and generating a posteriori probabilities (APP) of the desired symbols and the interferer symbols. The method also includes where the detector of each of the N frameworks generates the APP based on a feedback of a priori probabilities from each of the N frameworks. Other embodiments of this aspect include corresponding computer systems, apparatus, and computer programs recorded on one or more computer storage devices, each configured to perform the actions of the methods.
[0021] Additional features will be set forth in the description that follows, and in part will be apparent from the description, or may be learned by practice of what is described.
DRAWINGS
[0022] In order to describe the manner in which the above-recited and other advantages and features may be obtained, a more particular description is provided below and will be rendered by reference to specific embodiments thereof which are illustrated in the appended drawings. Understanding that these drawings depict only typical embodiments and are not, therefore, to be limiting of its scope, implementations will be described and explained with additional specificity and detail with the accompanying drawings.
[0023] FIG. 1 illustrates a prior art beam laydown pattern with a 4-color reuse plan for a multi-beam satellite, according to various embodiments.
[0024] FIG. 2 illustrates two users serviced by two co-channel beams showing CCI between beams according to various embodiments.
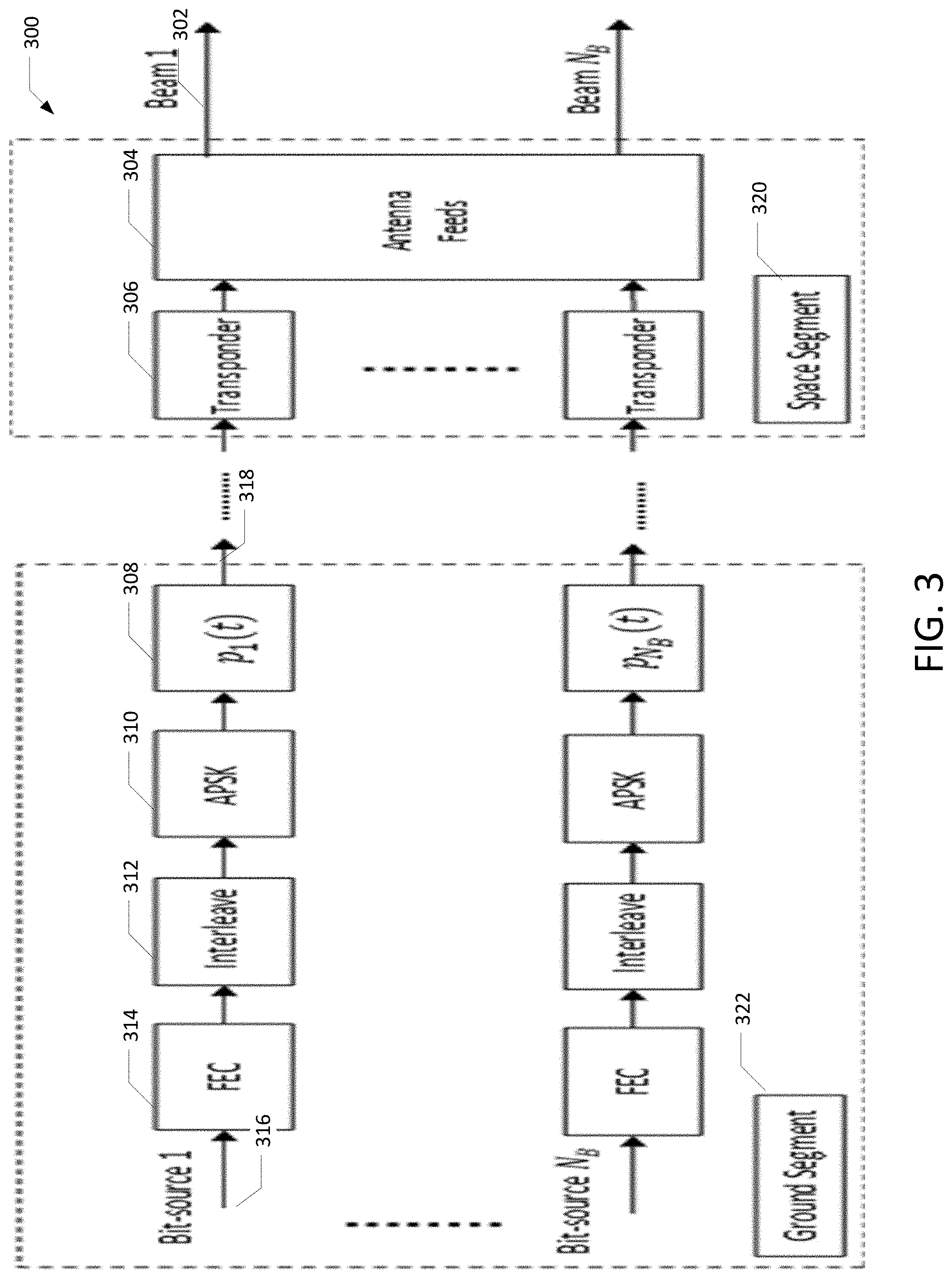
[0025] FIG. 3 illustrates a multi-spot beam satellite system model according to various embodiments.
[0026] FIG. 4 illustrates a block diagram of a soft-in-soft-out (SISO) IDAC receiver according to various embodiments, shown here for two dominant interferers.
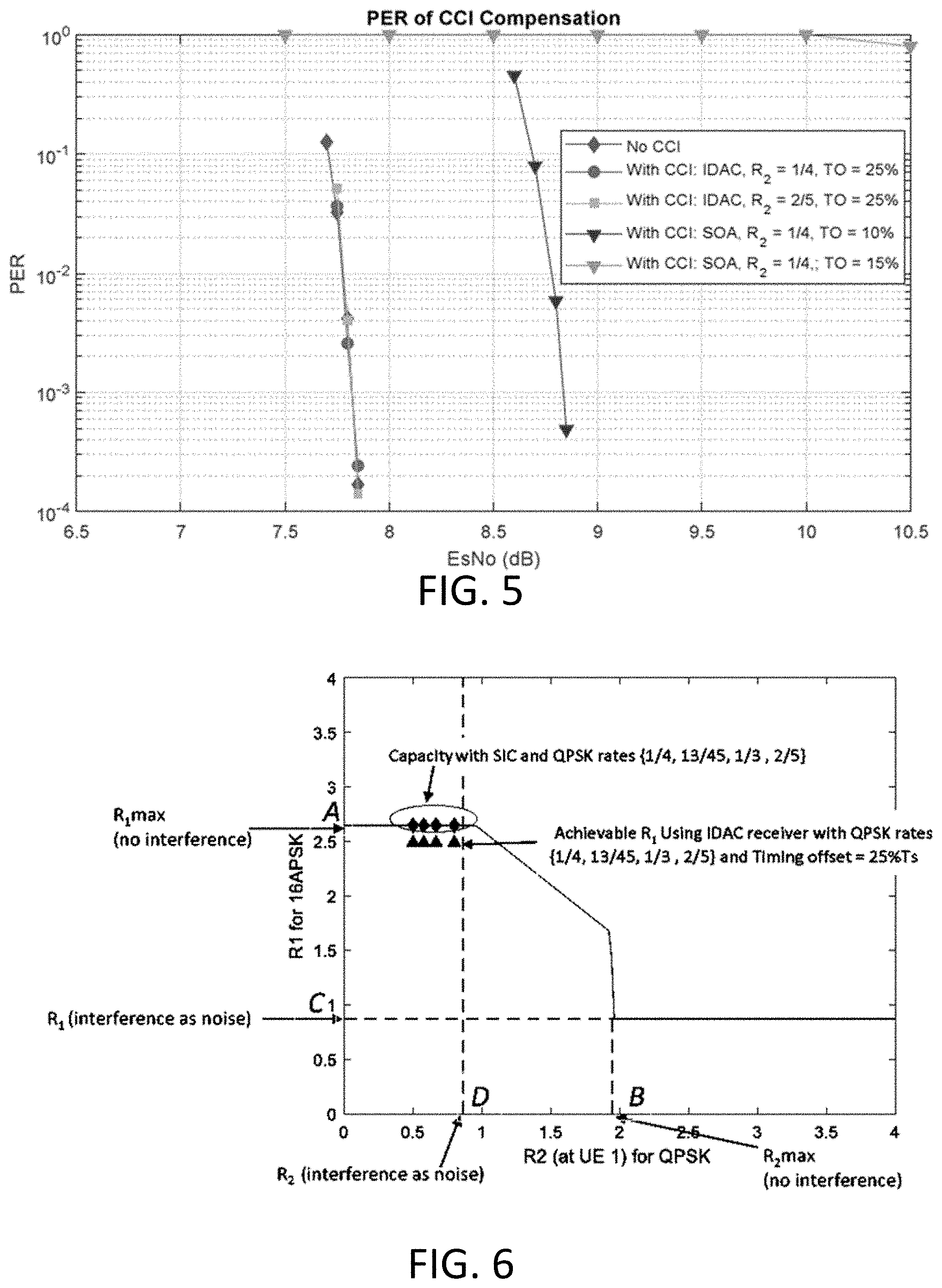
[0027] FIG. 5 illustrates a coded PER of DVB-S2X 16APSK with code rate 28/45 when interfered by QPSK with rate R.sub.2 at different levels of timing offset (TO), according to various embodiments.
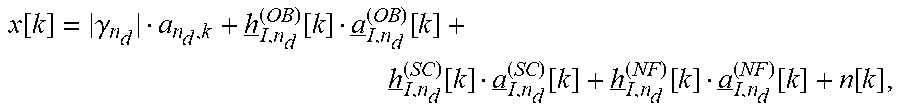
[0028] FIG. 6 illustrates an information-theoretic achievable-rate region for 16APSK when interfered by QPSK at C/I=0 dB and E.sub.s/N.sub.0=7.83 dB), according to various embodiments.
[0029] Throughout the drawings and the detailed description, unless otherwise described, the same drawing reference numerals will be understood to refer to the same elements, features, and structures. The relative size and depiction of these elements may be exaggerated for clarity, illustration, and convenience.
DETAILED DESCRIPTION
[0030] The present teachings may be a system, a method, and/or a computer program product at any possible technical detail level of integration. The computer program product may include a computer readable storage medium (or media) having computer readable program instructions thereon for causing a processor to carry out aspects of the present invention.
[0031] The computer readable storage medium can be a tangible device that can retain and store instructions for use by an instruction execution device. The computer readable storage medium may be, for example, but is not limited to, an electronic storage device, a magnetic storage device, an optical storage device, an electromagnetic storage device, a semiconductor storage device, or any suitable combination of the foregoing. A non-exhaustive list of more specific examples of the computer readable storage medium includes the following: a portable computer diskette, a hard disk, a random access memory (RAM), a read-only memory (ROM), an erasable programmable read-only memory (EPROM or Flash memory), a static random access memory (SRAM), a portable compact disc read-only memory (CD-ROM), a digital versatile disk (DVD), a memory stick, a floppy disk, a mechanically encoded device such as punch-cards or raised structures in a groove having instructions recorded thereon, and any suitable combination of the foregoing. A computer readable storage medium, as used herein, is not to be construed as being transitory signals per se, such as radio waves or other freely propagating electromagnetic waves, electromagnetic waves propagating through a waveguide or other transmission media (e.g., light pulses passing through a fiber-optic cable), or electrical signals transmitted through a wire.
[0032] Computer readable program instructions described herein can be downloaded to respective computing/processing devices from a computer readable storage medium or to an external computer or external storage device via a network, for example, the Internet, a local area network, a wide area network and/or a wireless network. The network may comprise copper transmission cables, optical transmission fibers, wireless transmission, routers, firewalls, switches, gateway computers and/or edge servers. A network adapter card or network interface in each computing/processing device receives computer readable program instructions from the network and forwards the computer readable program instructions for storage in a computer readable storage medium within the respective computing/processing device.
[0033] Computer readable program instructions for carrying out operations of the present invention may be assembler instructions, instruction-set-architecture (ISA) instructions, machine instructions, machine dependent instructions, microcode, firmware instructions, state-setting data, or either source code or object code written in any combination of one or more programming languages, including an object oriented programming language such as SMALLTALK, C++ or the like, and conventional procedural programming languages, such as the "C" programming language or similar programming languages. The computer readable program instructions may execute entirely on the user's computer, partly on the user's computer, as a stand-alone software package, partly on the user's computer and partly on a remote computer or entirely on the remote computer or server. In the latter scenario, the remote computer may be connected to the user's computer through any type of network, including a local area network (LAN) or a wide area network (WAN), or the connection may be made to an external computer (for example, through the Internet using an Internet Service Provider). In some embodiments, electronic circuitry including, for example, programmable logic circuitry, field-programmable gate arrays (FPGA), or programmable logic arrays (PLA) may execute the computer readable program instructions by utilizing state information of the computer readable program instructions to personalize the electronic circuitry, in order to perform aspects of the present invention.
[0034] Aspects of the present invention are described herein with reference to flowchart illustrations and/or block diagrams of methods, apparatus (systems), and computer program products according to embodiments of the invention. It will be understood that each block of the flowchart illustrations and/or block diagrams, and combinations of blocks in the flowchart illustrations and/or block diagrams, can be implemented by computer readable program instructions.
[0035] These computer readable program instructions may be provided to a processor of a general purpose computer, special purpose computer, or other programmable data processing apparatus to produce a machine, such that the instructions, which execute via the processor of the computer or other programmable data processing apparatus, create means for implementing the functions/acts specified in the flowchart and/or block diagram block or blocks. These computer readable program instructions may also be stored in a computer readable storage medium that can direct a computer, a programmable data processing apparatus, and/or other devices to function in a particular manner, such that the computer readable storage medium having instructions stored therein comprises an article of manufacture including instructions which implement aspects of the function/act specified in the flowchart and/or block diagram block or blocks.
[0036] The computer readable program instructions may also be loaded onto a computer, other programmable data processing apparatus, or other device to cause a series of operational steps to be performed on the computer, other programmable apparatus or other device to produce a computer implemented process, such that the instructions which execute on the computer, other programmable apparatus, or other device implement the functions/acts specified in the flowchart and/or block diagram block or blocks.
[0037] The flowchart and block diagrams in the Figures illustrate the architecture, functionality, and operation of possible implementations of systems, methods, and computer program products according to various embodiments of the present invention. In this regard, each block in the flowchart or block diagrams may represent a module, segment, or portion of instructions, which comprises one or more executable instructions for implementing the specified logical function(s). In some alternative implementations, the functions noted in the block may occur out of the order noted in the figures. For example, two blocks shown in succession may, in fact, be executed substantially concurrently, or the blocks may sometimes be executed in the reverse order, depending upon the functionality involved. It will also be noted that each block of the block diagrams and/or flowchart illustration, and combinations of blocks in the block diagrams and/or flowchart illustration, can be implemented by special purpose hardware-based systems that perform the specified functions or acts or carry out combinations of special purpose hardware and computer instructions.
[0038] Reference in the specification to "one embodiment" or "an embodiment" of the present invention, as well as other variations thereof, means that a feature, structure, characteristic, and so forth described in connection with the embodiment is included in at least one embodiment of the present invention. Thus, the appearances of the phrase "in one embodiment" or "in an embodiment", as well any other variations, appearing in various places throughout the specification are not necessarily all referring to the same embodiment.
[0039] The ever-increasing demand for higher throughput and ubiquitous connectivity implies extracting higher spectral efficiencies and improved energy efficiencies from modern satellite broadband systems. Spectrum scarcity imposes fundamental limitations on the data rates and necessitates the most efficient use of available frequency resources.
[0040] In the prior art, precoding and beamforming techniques are limited by the accuracy of Channel State Information (CSI) available at the gateway. Additionally, precoding techniques are also limited by the lack of feeder-link bandwidth. Compensating for CCI at a receiver, for example, a user terminal, overcomes the above limitations. In the present teachings, a user terminal mitigates CCI in a multiuser detection framework by jointly processing a desired signal together with a dominant source. In some embodiments, the dominant source can comprise one, two or more interferers.
[0041] Extensive computer simulations, along with accompanying information-theoretic results, demonstrate the superlative performance of the present teachings when tackling severe cases of CCI in multibeam satellite systems employing aggressive frequency reuse, even without imposing the restrictive requirement of synchronous reception.
System Model
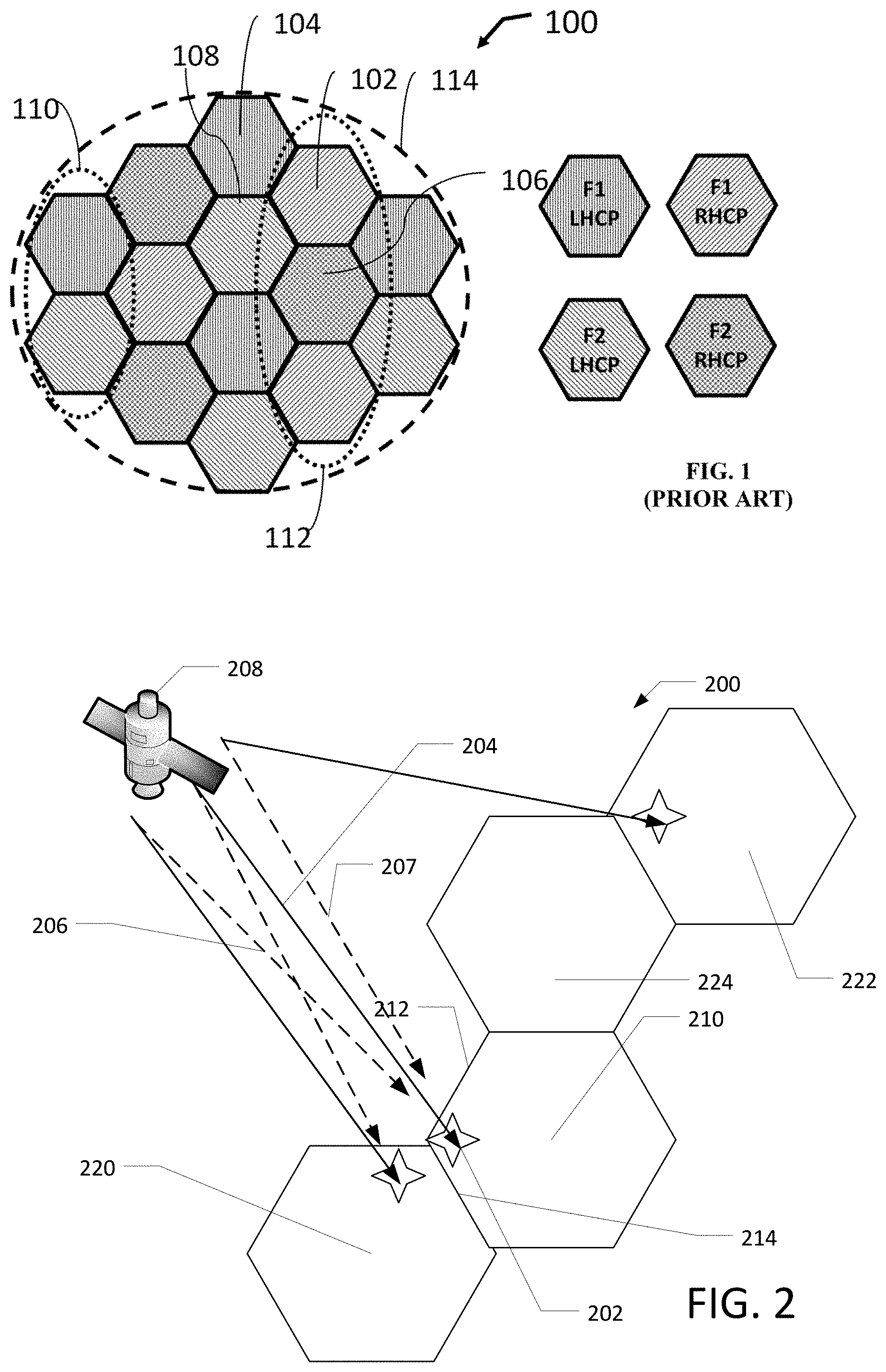
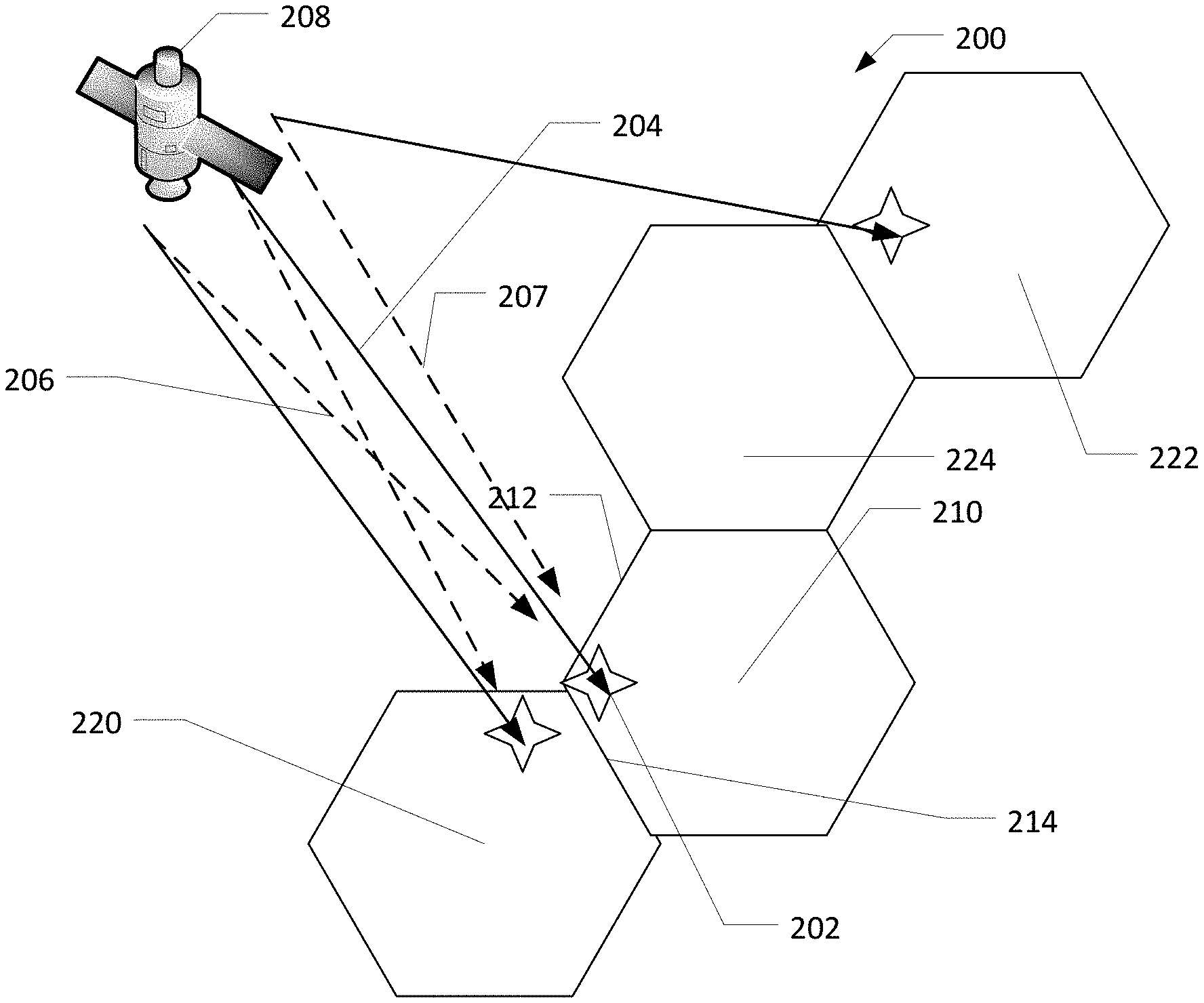
[0042] FIG. 2 illustrates two users serviced by two co-channel beams showing CCI between beams according to various embodiments.
[0043] FIG. 2 illustrates a satellite communications system 200 including a user terminal (UT) 202 communicating with a satellite 208 via a beam 204. When the UT 202 is located near an edge 212 or 214 of their coverage area 210, a co-channel beam 206 (here intended for coverage area 220), in a reuse 2 deployment will interfere with the beam 204. In this case, the UT 202 will receive its desired/intended signal (beam 204) in the presence of interference arising from interferer signals/co-channel beams 206, 207 intended for a UT disposed in the coverage areas 220, 222 respectively. The ratio of the beam 204 at UT 202 (C) to the interfering signal/co-channel beams 206, 207 (I) is known as the carrier-to-interference ratio (C/I) and can be as high as 0 dB, or of equal strength. In some deployments, one or more of the interferer signals 206, 207 may be more robust than the desired signal 204. An interference severity may be based on the C/I ratio.
[0044] It is quite likely that the desired signal and the interferer signals can come from different gateways (not shown), employ different coded-modulation (MODCOD) formats, have different symbol rates and pulse shaping filters with different roll-off factors. The desired and interfering signals can arrive at the user terminal in an asynchronous manner. Even though the co-channel beams may be formed and emitted by the satellite simultaneously, they propagate through different paths causing unavoidable differential delays. Further, the beams could be conveying signals originating from multiple gateways, interconnected via terrestrial links. Other sources that generate memory effects include different symbol rates required by co-channel beams and/or using pulse shaping with different rolloff values. CCI mitigation techniques are required to maintain reasonable performance for such users.
[0045] Here co-channel beam 206 may also be known as a dominant source. When a UT, such as UT 202, is disposed near two edges of its coverage area (i.e., coverage area 210), the UT 202 may receive two co-channel beams (second co-channel beam not shown) and portions of both may qualify as dominant sources with respect to the desired signal. For example, a current sample of the co-channel beam may be considered a dominant source, while a previous sample of the co-channel beam may be considered a non-dominant source. In some embodiments, an intended signal of a UT may be interfered with by one or more dominant sources.
[0046] The interfering signal/co-channel beams 206, 207 may include interfering symbols. Interfering symbols of the beam 206 targeting the coverage area 220 immediately adjacent to the coverage area 210 where the UT 202 is disposed may be partitioned into a dominant group of interfering symbols. Interfering symbols of the beam 207 targeting the coverage area 222 not immediately adjacent to the coverage area 210 may be partitioned into a non-dominant group of interfering symbols. Interfering symbols of a beam (not shown) targeting the coverage area 224 that is immediately adjacent to the coverage area 210 may also be partitioned into the non-dominant group of interfering symbols as the UT 202 is not disposed adjacent to a common edge of the coverage areas 210, 225.
System Model
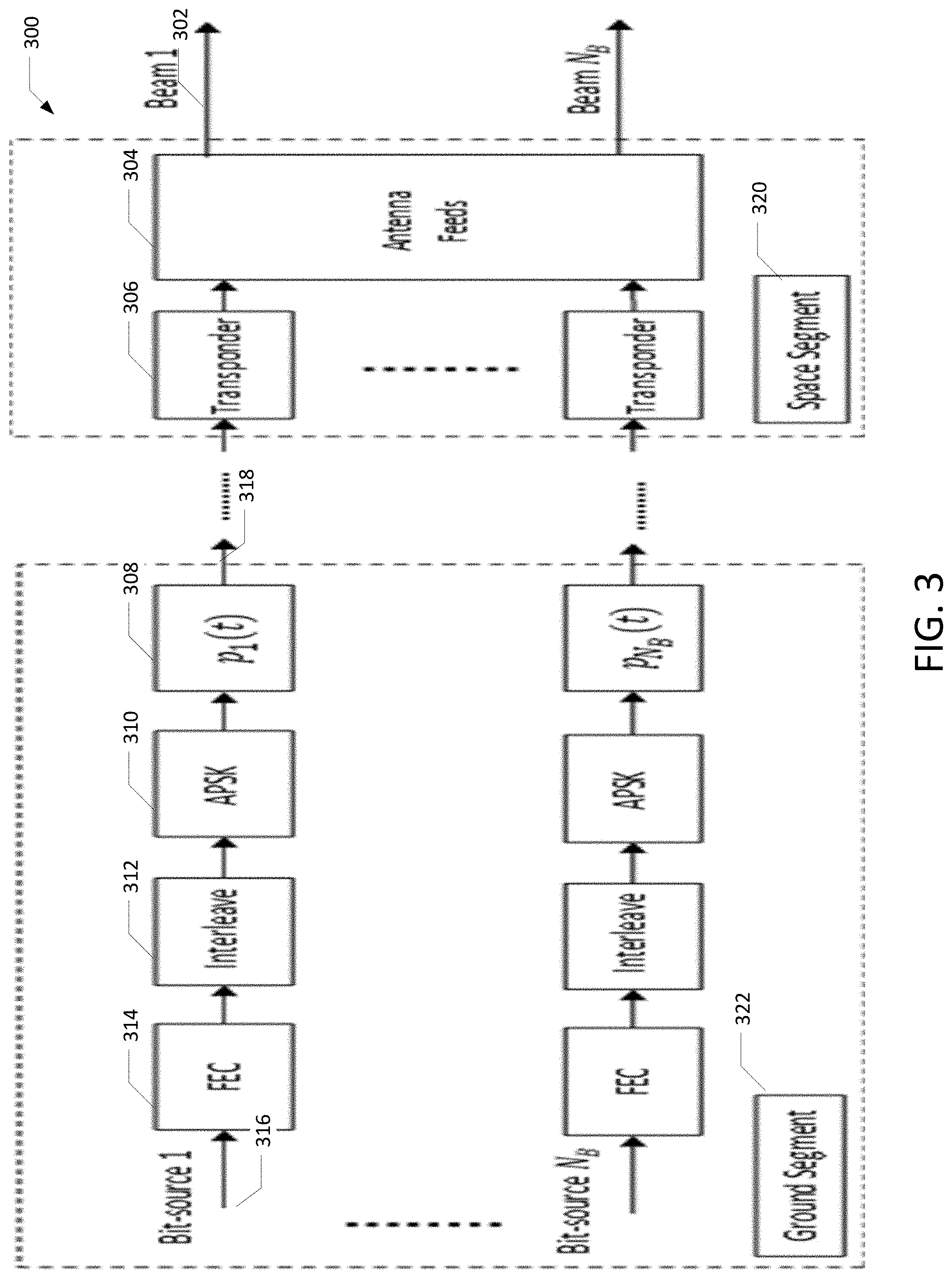
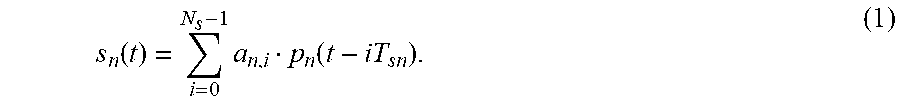
[0047] FIG. 3 illustrates a multi-spot beam satellite system model according to various embodiments.
[0048] A multi-spot beam satellite system 300 is illustrated in FIG. 3. FIG. 3 focuses on a forward link from a satellite gateway to a user terminal. Information bits 316 intended for a particular user located in a specific beam n, are FEC-encoded 314, bit-interleaved 312 and mapped onto an M-ary complex constellation 310 at a gateway 322 to form a symbol sequence of length Ns and symbol rate T.sub.s,n.sup.-1 such that, {a.sub.n,i; i=0, 1, . . . , Ns-1}. The uplink signal after pulse shaping has a baseband representation given by
s n ( t ) = i = 0 N s - 1 a n , i p n ( t - iT sn ) . ( 1 ) ##EQU00004##
Uplink signals 318 intended for the different spot beams are processed by their respective transponders 306 and transmitted to intended beams 302 by the satellite feed and antenna mechanism 320.
[0049] When aggressive frequency reuse factors, such as reuse 1 and reuse 2 are employed to boost a system's capacity, user terminals, especially those at the beam edge, experience a high level of CCI due to the sharing of common time-frequency resources. In such cases, the terminal receives the intended transmission and transmissions from N.sub.B-1 co-channel beams such that the received signal at a user terminal can be modelled using (1) as
r ( t ) = n = 1 N B i .gamma. n a n , i p n ( t - ( i + n ) T s , n ) e j ( 2 .pi. b jn t + .theta. n ) + n ( t ) ( 2 ) ##EQU00005##
In (2), .gamma..sub.n is a complex-valued channel gain that is a function of the antenna gain from the nth beam's feed in the direction of the user terminal under consideration. Here, { .sub.n,.delta..sub.j.sub.n,.theta..sub.n} represents the normalized differences in arrival times, carrier frequencies and carrier phases between the N.sub.B co-frequency beams at the receiver. In this example, downlink noise n(t) is assumed as an Additive White Gaussian Noise (AWGN) with a single-sided Power Spectral Density (PSD) level of N.sub.0 (Watt/Hz). The uplink noise may be assumed to be negligible relative to the downlink noise, a situation achieved through proper satellite link parameters including the size of the transmit antenna. Finally, it is assumed that any on-board High-Power Amplifiers (HPAs) have small nonlinear impact at the user terminals.
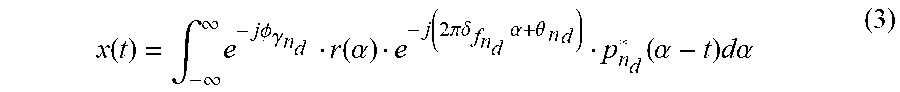
Analytical Characterization of CCI
[0050] Without limitation, per statistical decision theory, a set of sufficient statistics can be generated at the output of a filter matched to the desired signal, labelled as n.sub.d, then sampled at the symbol rate T.sub.s,nd, or x((k+.epsilon..sub.nd) T.sub.s,nd), where
x ( t ) = .intg. - .infin. .infin. e - j.phi. .gamma. n d r ( .alpha. ) e - j ( 2 .pi..delta. f n d .alpha. + .theta. n d ) p n d * ( .alpha. - t ) d.alpha. ( 3 ) ##EQU00006##
and .PHI..sub..gamma.n.sub.d is the phase associated with the complex-valued channel gain .gamma..sub.n.sub.d. To characterize the effective CCI channel response, substitute (2) into (3) to yield
x ( t ) = n = 1 N B i = - .infin. .infin. e - j .phi. .gamma. n d .gamma. n a n , i .eta. n , n d ( ( i + n ) T s , n , t ) + n ( t ) where e - j .phi. .gamma. n d . ( 4 ) ##EQU00007##
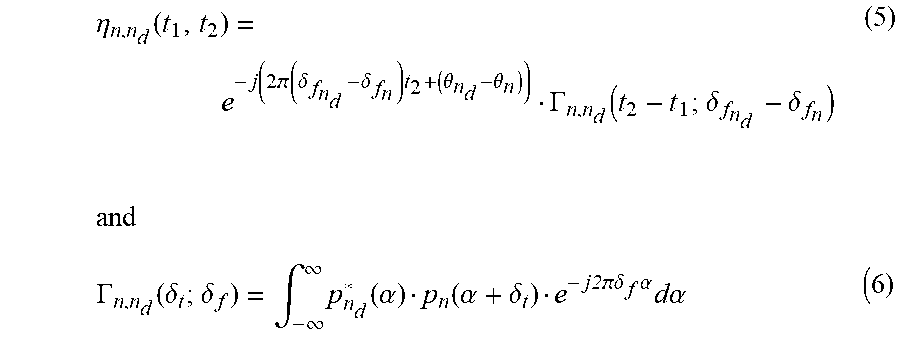
is the spatial contribution, while .eta..sub.n,n.sub.d(t.sub.1,t.sub.2) represents the time-varying impulse response due to the temporal contribution of CCI. In (4),
.eta. n , n d ( t 1 , t 2 ) = e - j ( 2 ( .delta. f n d - .delta. f n ) t 2 + ( .theta. n d - .theta. n ) ) .GAMMA. n , n d ( t 2 - t 1 ; .delta. f n d - .delta. f n ) ( 5 ) and .GAMMA. n , n d ( .delta. t ; .delta. f ) = .intg. - .infin. .infin. p n d * ( .alpha. ) p n ( .alpha. + .delta. t ) e - j2 .delta. f .alpha. d.alpha. ( 6 ) ##EQU00008## and
.GAMMA..sub.n,n.sub.d(.delta..sub.t;.delta..sub.f)=.intg..sub.-.infin..s- up..infin.p.sub.n.sub.d*(.alpha.)p.sub.n(.alpha.+.delta..sub.t)e.sup.-j2.p- i..delta..sup.f.sup..alpha.d.alpha. (6)
[0051] Focusing on the pulse shaping that satisfies the Nyquist criterion of zero Inter-Symbol Interference (ISI), such as bandwidth-efficient Root-Raised Cosine (RRC) pulses, used in the widely adopted DVB-S2X satellite standard. Thus, sampling the matched filter output in (4) at the correct sampling instant yields
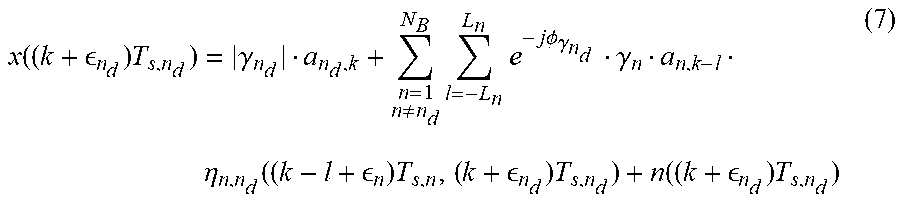
x ( ( k + n d ) T s , n d ) = .gamma. n d a n d , k + n = 1 n .noteq. n d N B l = - L n L n e - j .phi. .gamma. n d .gamma. n a n , k - l .eta. n , n d ( ( k - l + n ) T s , n , ( k + n d ) T s , n d ) + n ( ( k + n d ) T s , n d ) ( 7 ) ##EQU00009##
[0052] where L.sub.n denotes the memory-span associated with CCI. From (7), it can be inferred that the desired symbols at the matched filter output are affected by CCI coming from N.sub.B-1 beams, in addition to Gaussian noise. It can also be inferred that CCI has memory due to the interfering signals combining asynchronously. The memory effects can be made worse due to different symbol rates and/or different roll-off factors employed by the different co-channel beams.
Iterative Divide-and-Conquer Detection
Iterative Soft-In-Soft-Out Receiver
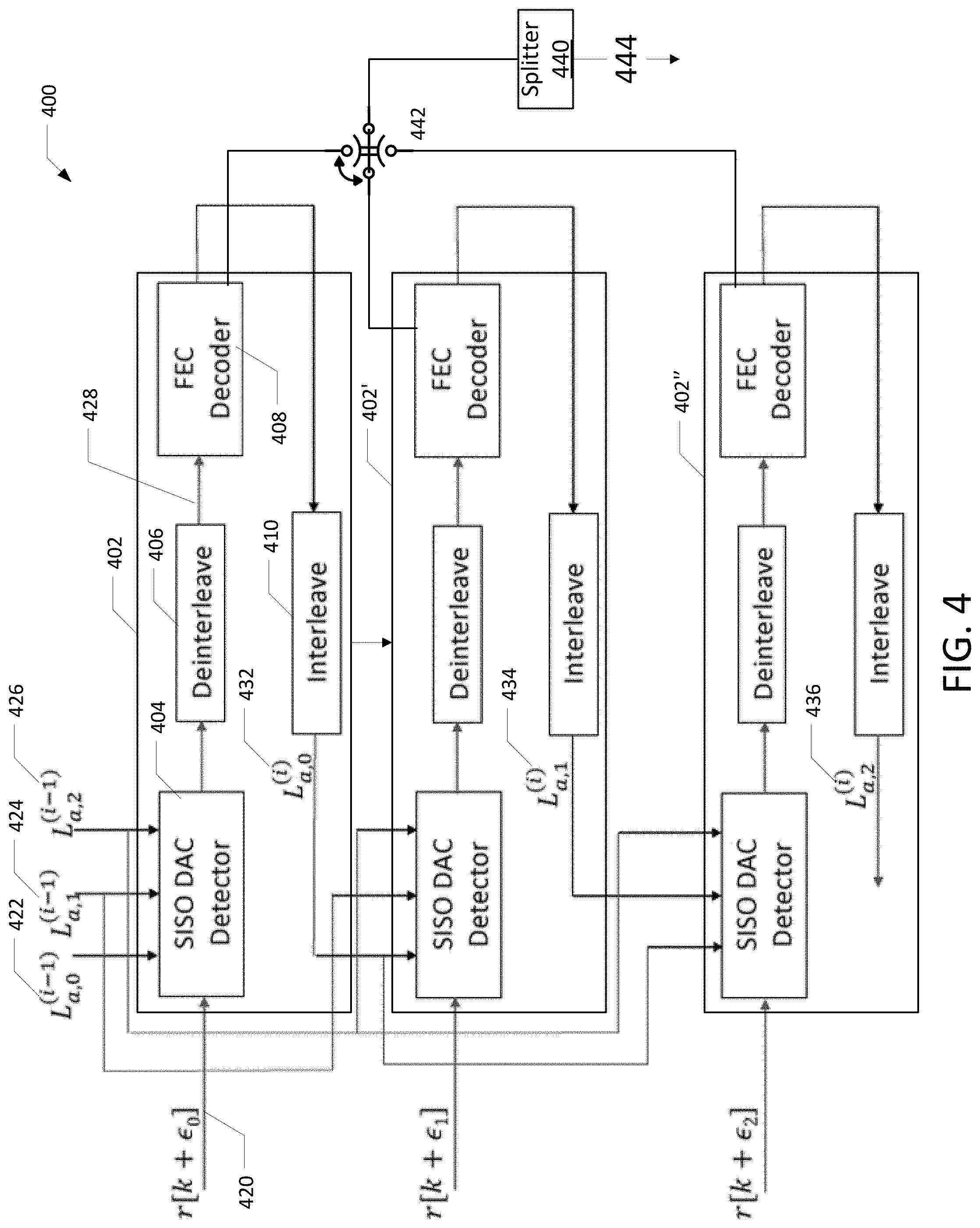
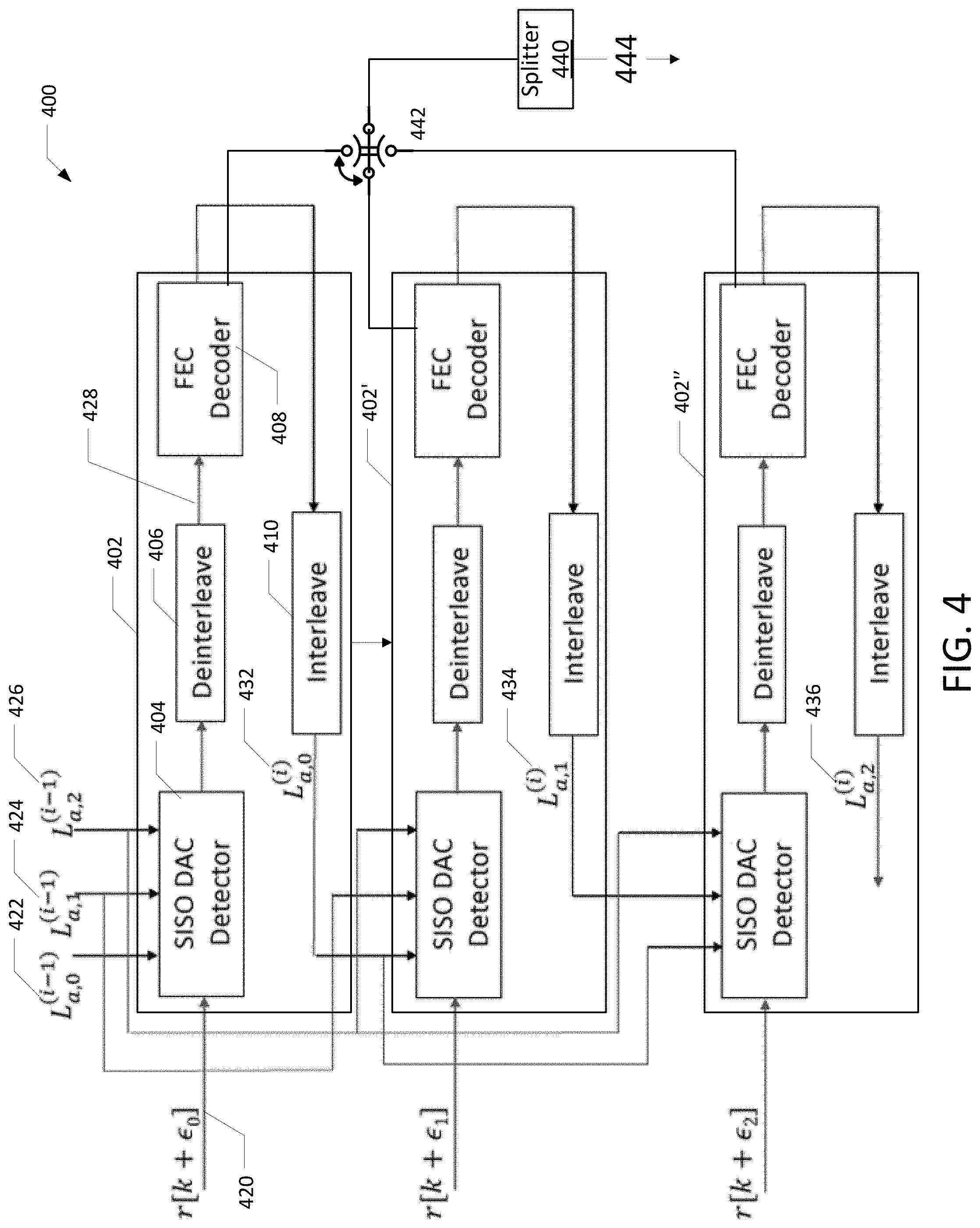
[0053] FIG. 4 illustrates a block diagram of a Soft-In-Soft-Out (SISO) Iterative Soft-In-Soft-Out (IDAC) receiver according to various embodiments.
[0054] A Soft-In-Soft-Out (SISO) Iterative Soft-In-Soft-Out (IDAC) receiver 400 implements a plurality of Soft-In-Soft-Out (SISO) frameworks 402, 402' and 402''. The count of SISO frameworks may vary. For brevity, the framework 402 is further elaborated below. However, each of the frameworks 402', 402'' function in a manner similar to the framework 402.
[0055] The framework 402 performs joint detection with a SISO DAC detector 404 along with decoding with a FEC decoder 408 (after deinterleaving with a deinterleaver 406) is applied in an iterative fashion to recover the information bits intended for a user terminal. An outer or global iteration begins by processing a composite signal 420 including a desired signal and interfering signal. The outer or global iteration processes the interfering signal by employing the most robust signal in the joint CCI SISO DAC detector 404, while assuming equally likely a priori information 422, 424, 426 for the interferer signal, the desired signal and any additional interfering signal being processed jointly. The Iterative Divide-And-Conquer Detection (IDAC), detailed above, provides soft-information about CCI in the form of the symbol A Posteriori Probabilities (APPS) 432, 434, 436 which are transformed to bit Log-Likelihood Ratios (LLRs) using the bit-to-symbol mapping rule employed at the transmitter.
[0056] These bit LLRs are in turn deinterleaved by the deinterleaver 406 and input to the FEC decoder 408 as a decoding input 428. The FEC decoder 408 subsequently generates LLR soft-estimates of the interfering signal's information bits. These are converted to extrinsic information by subtracting the LLRs at the input to the FEC decoder 408. The receiver 400 immediately uses this extrinsic information as a posteriori probability 432, 434, 436 for processing the composite signal 420 employing the next most robust signal, thereby incorporating the latest information from the previous signal's FEC decoder, during the same outer iteration, leading to faster convergence.
[0057] At the completion of an outer iteration, the receiver has the APP 432, 434, 436 estimates for all the signals being jointly processed and can use them during the next outer iteration as a priori information 422, 424, 426. As such the APP of a first iteration is the a priori information for the next iteration. Each framework may use the APP in succession or in parallel. For example, the receiver 400 uses the APP generated by the framework 402 in succession for the framework 402', and the APP generated by the framework 402' is used in succession for the framework 402''. In a parallel implementation (not shown) of the receiver, the APP of an iteration is not used by the plurality of frameworks within the iteration.
[0058] The above framework can be applied to systems employing either Simultaneous Decoding (SD) or Simultaneous Non-unique Decoding (SND) methods. In SD, after a certain maximum number of global iterations, the hard decisions provided by two or more decoders is multiplexed by multiplexor 442 to form an estimate of the desired symbols 444 that may be converted to the user's information bits, for example, in a splitter 440. In SND, after a certain maximum number of global iterations, the hard decisions provided by only a single FEC decoder provides an estimate of the desired symbols 444 that may be converted to the user's information bits, for example, in the splitter 440. In SND, the multiplexor 442 may be eliminated.
[0059] Stacked Construction of CCI With Memory
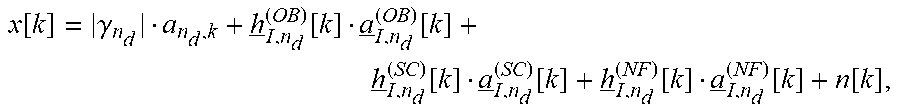
[0060] Using the analysis above, a useful formulation is disclosed for IDAC detection. It is based on a stacked construction that models the spatial and temporal contributions of the CCI in multibeam satellite systems on the forward link, namely from the gateway to the user terminals. The kth time-instant of the MF output x[k] of (7), received in the n.sub.dth beam, is described as
x[k]=|.gamma..sub.n.sub.d|a.sub.n.sub.d.sub.,k+h.sub.I,n.sub.d[k]a.sub.I- ,n.sub.d[k]+n[k] (8)
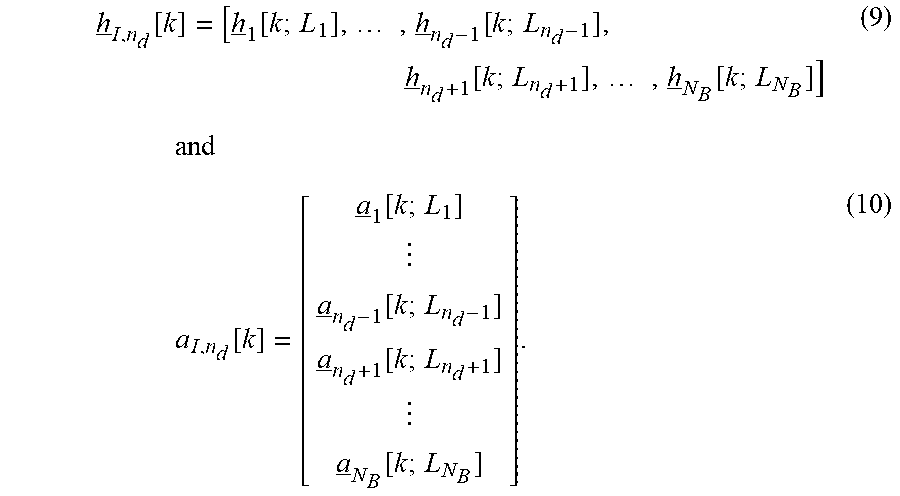
where h.sub.I,n.sub.d[k] is a stacked row-vector containing the channel coefficients associated with each of the neighboring co-channel interfering beams and a.sub.i,nd [k] is a stacked column-vector that models the corresponding symbols serviced by the interfering beams, defined as
h _ I , n d [ k ] = [ h _ 1 [ k ; L 1 ] , , h _ n d - 1 [ k ; L n d - 1 ] , h _ n d + 1 [ k ; L n d + 1 ] , , h _ N B [ k ; L N B ] ] ( 9 ) and a I , n d [ k ] = [ a _ 1 [ k ; L 1 ] a _ n d - 1 [ k ; L n d - 1 ] a _ n d + 1 [ k ; L n d + 1 ] a _ N B [ k ; L N B ] ] . ( 10 ) ##EQU00010##
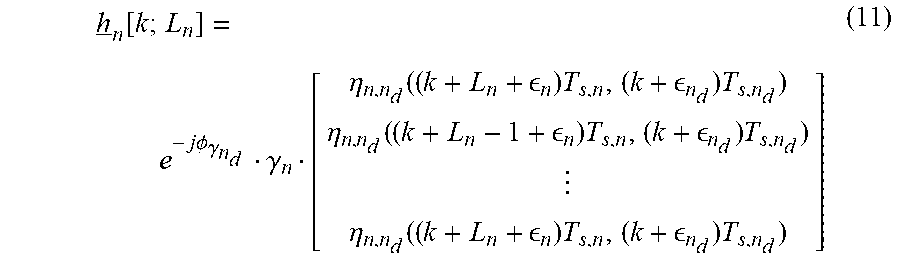
[0061] respectively. The individual row-vector h.sub.i,n [k] in (9) is in turn composed of a vector containing the spatial and temporal coefficients belonging to the nth beam with single-sided memory of L.sub.n (see for example, 432, 434, 436 in FIG. 4) symbols, outlined in (7), and expressed as
h _ n [ k ; L n ] = e - j .phi. .gamma. n d .gamma. n [ .eta. n , n d ( ( k + L n + n ) T s , n , ( k + n d ) T s , n d ) .eta. n , n d ( ( k + L n - 1 + n ) T s , n , ( k + n d ) T s , n d ) .eta. n , n d ( ( k + L n + n ) T s , n , ( k + n d ) T s , n d ) ] ( 11 ) ##EQU00011##
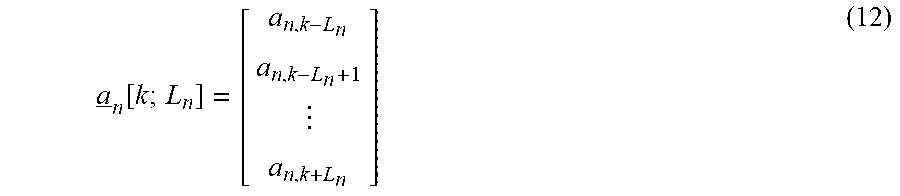
In (10), a.sub.n[k, L.sub.n] is a column-vector containing the individual interfering symbols from the nth beam or
a _ n [ k ; L n ] = [ a n , k - L n a n , k - L n + 1 a n , k + L n ] ( 12 ) ##EQU00012##
SISO Divide-and-Conquer Detector
[0062] The receiver implements a SISO Divide-And-Conquer (DAC) detector of CCI which partitions the interfering symbols into three smaller groups depending on the intensity of their interference levels. These smaller groups use different methods of contributing to the APP computation. The first is the Noise-Floor (NF) group whose elements are incorporated only through their powers. The second is the Subtractive-Cancellation (SC) group which is incorporated in the SISO DAC APP module via first- and second-order moments, derived from a priori probabilities.
[0063] The third group is based on the Optimal-Bayesian (OB) method contributing to the SISO DAC APP module using the a priori probability mass function (pmf) of the interfering symbols from within the OB group only. To start the kth time-instant of the MF output x[k] of (8) is equivalently expressed as
x k = .gamma. n d a n d , k + h _ I , n d ( OB ) [ k ] a _ I , n d ( OB ) [ k ] + h _ I , n d ( SC ) [ k ] a _ I , n d ( SC ) [ k ] + h _ I , n d ( NF ) [ k ] a _ I , n d ( NF ) [ k ] + n [ k ] ( 13 ) ##EQU00013##
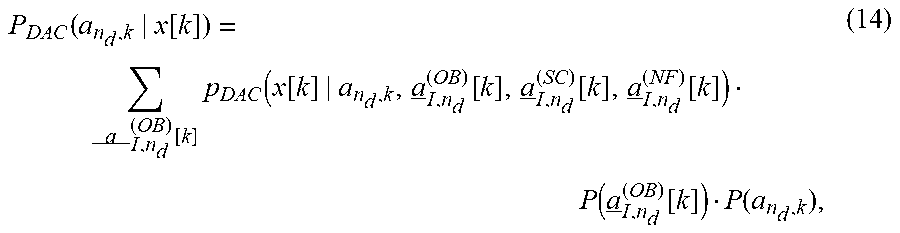
where the elements of a.sub.i,nd [k] is partitioned into three groups, a.sub.I,n.sub.d.sup.(NF)[k], a.sub.I,n.sub.d.sup.(SC)[k], a.sub.I,n.sub.d.sup.(OB)[k], and h.sub.I,n.sub.d.sup.(NF)[k], h.sub.I,n.sub.d.sup.(SC)[k], h.sub.I,n.sub.d.sup.(OB)[k] are the corresponding spatial and temporal CCI channel coefficients extracted from h.sub.i,nd[k]. Based on the partitioned expression (13), the proposed SISO DAC APP module, P.sub.DAC(a.sub.n.sub.d.sub.,k|x[k]), is mathematically expressed as
P DAC ( a n d , k | x [ k ] ) = a _ I , n d ( OB ) [ k ] p DAC ( x [ k ] | a n d , k , a _ I , n d ( OB ) [ k ] , a _ I , n d ( SC ) [ k ] , a _ I , n d ( NF ) [ k ] ) P ( a _ I , n d ( OB ) [ k ] ) P ( a n d , k ) , ( 14 ) ##EQU00014##
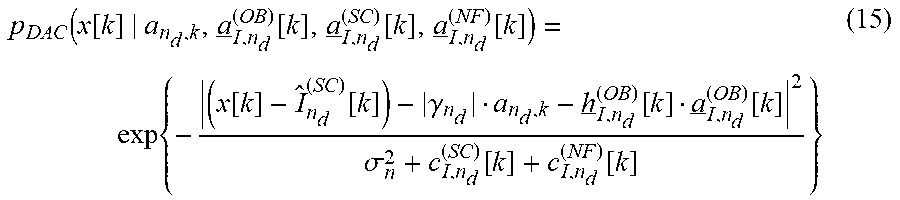
where p.sub.DAC( ) is the likelihood function associated with observing x[k] given the desired and interfering symbols and P( ) is the a priori pmf corresponding to the symbols computed based on the individual FEC decoders. In (14), the likelihood function p.sub.DAC( ) assumes that x[k] is a random variable that retains a Gaussian density expression or
p DAC ( x [ k ] | a n d , k , a _ I , n d ( OB ) [ k ] , a _ I , n d ( SC ) [ k ] , a _ I , n d ( NF ) [ k ] ) = exp { - ( x [ k ] - I ^ n d ( SC ) [ k ] ) - .gamma. n d a n d , k - h _ I , n d ( OB ) [ k ] a _ I , n d ( OB ) [ k ] 2 .sigma. n 2 + c I , n d ( SC ) [ k ] + c I , n d ( NF ) [ k ] } ( 15 ) ##EQU00015##
where I.sub.n.sub.d.sup.(SC)[k] is the soft CCI estimate arising from the SC group that is subtracted and is computed as
I.sub.n.sub.d.sup.(SC)[k]=h.sub.I,n.sub.d.sup.(SC)[k]{a.sub.I,n.sub.d.su- p.(SC)[k]} (16)
Also, the likelihood expression in (15) contains the variances from the SC and NF interfering groups, c.sub.I,n.sub.d.sup.(SC)[k] and c.sub.I,n.sub.d.sup.(NF)[k], respectively, obtained by
c.sub.I,n.sub.d.sup.(SC)[k]=h.sub.I,n.sub.d.sup.(SC)[k]Cov{a.sub.I,n.sub- .d.sup.(SC)[k]}(h.sub.I,n.sub.d.sup.(SC)[k]).sup.H (17)
and
c.sub.I,n.sub.d.sup.(NF)[k]=h.sub.I,n.sub.d.sup.(NF)[k](h.sub.I,n.sub.d.- sup.(NF)[k]).sup.H (18)
Performance Evaluation
[0064] Extensive performance evaluations demonstrate the effectiveness of the IDAC receiver. The simulation setup implements the system model described previously and employs Low-Density Parity Check (LDPC) codes for FEC as well as the modulation formats defined in the DVB-S2X standard. RRC filters with a rolloff of 0.05 are considered at the transmitters for pulse-shaping and at their corresponding receivers for matched filtering. It is assumed that the satellite transponders are operated in a single-carrier per-HPA mode with the operating point causing small nonlinear distortion at the user terminals. It is also assumed that a multibeam system is employing aggressive frequency reuse, and as such the channel gains from a particular beam in the direction of a user terminal located in a neighboring co-channel beam are severe. This results in CCI at the user terminal which can be as high as C/I=0 dB, i.e., of equal strength, as considered in the performance evaluations. In a multibeam system, a user's receiver may experience a substantial amount of CCI with memory due to the desired signal and interference arriving at the user terminal asynchronously with some relative delay.
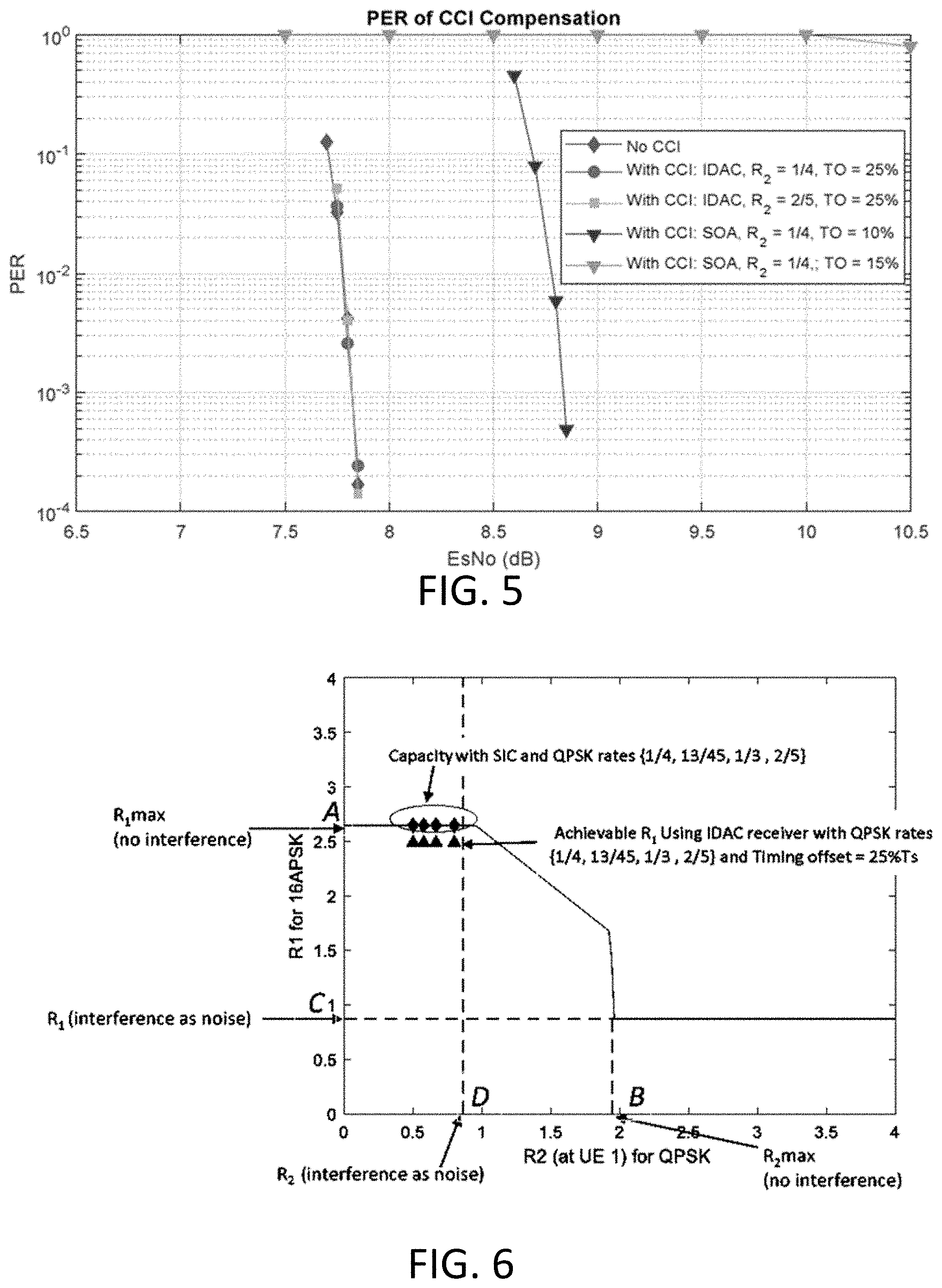
[0065] FIG. 5 illustrates a coded PER of DVB-S2X 16APSK with code rate 28/45 when interfered by QPSK with rate R.sub.2 at different levels of timing offset (TO) according to various embodiments.
[0066] FIG. 5 starts with an examination of the Packet Error Rate (PER) performance in the presence of CCI and AWGN. FIG. 5 documents PER versus E.sub.s/N.sub.0 for a desired user employing 16APSK with the rate 28/45 LDPC code. In this scenario, 16APSK symbols intended for the desired user arrive at the user terminal in the presence of a strong co-channel interferer at C/I=0 dB that employs QPSK MODCOD with rates of 1/4 or 2/5. A significant amount of distortion experienced at the decoder input will cause the LDPC decoding to fail without CCI mitigation. FIG. 5 also illustrates the inability of state-of-the-art (SOA) memoryless CCI mitigation techniques popular in the literature to handle asynchronous reception. As an example, when the offset between the desired signal and the interferer is 10% of T.sub.s, performance with the memoryless solution degrades by more than 1 dB and a delay of 15% relative to T.sub.s causes the receiver to become ineffective. These limitations motivate the need for the innovative, low-complexity and modular IDAC framework disclosed in the present teachings.
[0067] As is evident in FIG. 5, the receiver of the present teachings does not suffer from performance degradation even at delays as high as 25% of Ts and approaches no-CCI performance. Further, the present teachings are just as effective when the interfering beam carries QPSK with the weaker code rate of 2/5. The low-complexity of the present teachings is particularly noteworthy in light of the significant CCI memory span and APSK modulation cardinality. The impressive performance offered by the present teachings allows user terminals located at the edges of co-frequency beams to benefit from high spectral efficiencies offered by APSK MODCODs.
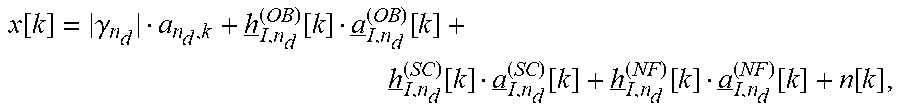
[0068] FIG. 6 illustrates an information-theoretic achievable-rate region for 16APSK when interfered by QPSK at C/I=0 dB and E.sub.s/N.sub.0=7.83 dB), according to various embodiments.
[0069] FIG. 6 illustrates a map out of the information-theoretic rate regions supported at a user terminal when 16APSK and QPSK symbols are transmitted on co-channel beams. These report mutual information between the transmitted modulated symbols and the received symbols at E.sub.s/N.sub.0=7.83 dB. By adopting that with the SND method, only 16APSK symbols carry information for the targeted user which the user terminal can recover by jointly processing the desired signal and the interfering signal. The rate region has several points of interest that are discussed here; the point labelled A denotes the maximum rate R.sub.1 at which 16APSK symbols can be reliably received at the user terminal when there is no CCI and is approximately 2.65 bits-per-symbol.
[0070] Conversely, the point B denotes the maximum rate R.sub.2 at which QPSK symbols can be reliably received at the same user terminal, without any CCI and is 1.95 bits-per-symbol. Points C and D are the maximum rates possible when CCI is unmitigated and treated as noise at the receiver, these rates are R.sub.1=0.87 bits-per-symbol for 16APSK and R.sub.2=0.86 bits-per-symbol for QPSK, respectively. It is clear from these results that CCI, if left unmitigated can impose a significant penalty on the spectral efficiency. Information theory also indicates that as long as 0<R.sub.2<0.86, it is possible to receive 16APSK at its maximum rate at the user terminal in the presence of CCI by jointly processing both signals. In particular, QPSK can be recovered first and can subsequently assist in recovering the 16APSK symbols. As an example, the curve marked in green diamond indicates that 16APSK can be signaled at its maximum rate of 2.65 bits-per-symbol when the interfering QPSK signal has rates R.sub.2=2.times.{1/4, 13/45, 1/3, 2/5} by jointly processing both signals at the user terminal.
[0071] It is also interesting to visualize how the rates promised by information-theory compare with performance achievable with the IDAC receiver employing finite-length DVB-S2X LDPC codes and operating under the realistic assumption of CCI with memory. Towards this end, extensive PER performance simulations were conducted by transmitting progressively more spectrally efficient QPSK MODCODs on the interfering signal by increasing its code rate to 13/45, 1/3 and 2/5. As done previously, C/I=0 dB and timing offset of 25% of Ts were assumed. Results indicate that. similar to FIG. 5, there is no noticeable performance loss relative to a no-CCI scenario. This implies that the IDAC receiver does not penalize the interfering user to employ its most spectrally efficient MODCOD. Furthermore, the achievable rate for 16APSK of 2.5 bits-per-symbol, when using 28/45 code, is quite close to the information-theoretic maximum of 2.65 bits-per-symbol. This is also illustrated in FIG. 6, where the E.sub.s/N.sub.0 for the coded simulations corresponds to a PER of 10.sup.-3. Hence, it is easy to infer from these results that the IDAC receiver offers a capacity-approaching solution to handling severe CCI at the user terminal, even when confronted with symbol asynchronism.
[0072] Having described preferred embodiments of a system and method (which are intended to be illustrative and not limiting), it is noted that modifications and variations can be made by persons skilled in the art considering the above teachings. It is therefore to be understood that changes may be made in the embodiments disclosed which are within the scope of the invention as outlined by the appended claims. Having thus described aspects of the invention, with the details and particularity required by the patent laws, what is claimed and desired protected by Letters Patent is set forth in the appended claims.
* * * * *
D00000
D00001
D00002
D00003
D00004



P00001

P00002

XML
uspto.report is an independent third-party trademark research tool that is not affiliated, endorsed, or sponsored by the United States Patent and Trademark Office (USPTO) or any other governmental organization. The information provided by uspto.report is based on publicly available data at the time of writing and is intended for informational purposes only.
While we strive to provide accurate and up-to-date information, we do not guarantee the accuracy, completeness, reliability, or suitability of the information displayed on this site. The use of this site is at your own risk. Any reliance you place on such information is therefore strictly at your own risk.
All official trademark data, including owner information, should be verified by visiting the official USPTO website at www.uspto.gov. This site is not intended to replace professional legal advice and should not be used as a substitute for consulting with a legal professional who is knowledgeable about trademark law.