Alarm Routing Optimization Strategies In Targeted Alarm System
BROUSE; Christopher J.
U.S. patent application number 17/132570 was filed with the patent office on 2021-04-22 for alarm routing optimization strategies in targeted alarm system. The applicant listed for this patent is DRAGERWERK AG & CO. KGAA. Invention is credited to Christopher J. BROUSE.
| Application Number | 20210120366 17/132570 |
| Document ID | / |
| Family ID | 1000005303709 |
| Filed Date | 2021-04-22 |



| United States Patent Application | 20210120366 |
| Kind Code | A1 |
| BROUSE; Christopher J. | April 22, 2021 |
ALARM ROUTING OPTIMIZATION STRATEGIES IN TARGETED ALARM SYSTEM
Abstract
A targeted alarm system is described that includes a network probe for sending test data to terminal devices connected to a network and deriving reliability data of the terminal devices and the network. When a targeted alarm message needs to be sent, the system identifies a targeted terminal device based on the reliability data for sending the targeted alarm message. Related methods, apparatus, and non-transitory computer readable media are also disclosed.
| Inventors: | BROUSE; Christopher J.; (Cupertino, CA) | ||||||||||
| Applicant: |
|
||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|
| Family ID: | 1000005303709 | ||||||||||
| Appl. No.: | 17/132570 | ||||||||||
| Filed: | December 23, 2020 |
Related U.S. Patent Documents
| Application Number | Filing Date | Patent Number | ||
|---|---|---|---|---|
| 14896659 | Dec 7, 2015 | 10911891 | ||
| PCT/US2014/071294 | Dec 18, 2014 | |||
| 17132570 | ||||
| Current U.S. Class: | 1/1 |
| Current CPC Class: | G16H 40/60 20180101; G08B 25/001 20130101; H04L 67/12 20130101; G08B 26/007 20130101; G08B 25/003 20130101; H04W 4/023 20130101; G06Q 10/1091 20130101; G16H 40/20 20180101; G08B 26/006 20130101; H04M 2242/04 20130101; G08B 25/004 20130101; G08B 29/185 20130101; A61B 5/746 20130101; A61B 5/1113 20130101; G16H 40/63 20180101; H04W 4/90 20180201 |
| International Class: | H04W 4/02 20060101 H04W004/02; G08B 25/00 20060101 G08B025/00; G08B 29/18 20060101 G08B029/18; G16H 40/63 20060101 G16H040/63; H04W 4/90 20060101 H04W004/90; G16H 40/20 20060101 G16H040/20 |
Claims
1-41. (canceled)
42. A targeted medical alarm system for sending data to terminal devices, the system comprising: one or more network adapters configured to communicate with a plurality of terminal devices over one or more networks, each of the terminal devices being associated with a respective caregiver; one or more processors configured to: periodically transmit data to each of the terminal devices, receive acknowledgment data from each of the terminal devices indicating when the data was received by the respective terminal device, and store the received acknowledgment data indicating when the data was received by the respective terminal device in one or more storage mediums; track real-time locations the terminal devices, and store the real-time locations of the terminal devices in the one or more storage mediums; determine a predicted alarm message latency based on at least one of (i) the real-time locations of the terminal devices and (ii) historical acknowledgment data for at least one of the terminal devices, the historical acknowledgment data being measured when the at least one of the terminal devices was previously in the real-time location of the at least one of the terminal devices; identify a targeted terminal device to which a targeted message is to be sent based at least in part on the predicted alarm message latency; and send the targeted message to the targeted terminal device.
43. The system according to claim 42, wherein the one or more processors are further configured to track a scheduled location of the respective caregiver to enable the one or more processors to be able to predict locations of caregiver based on a time and day.
44. The system according to claim 43, wherein the one or more processors predict locations of the respective caregiver when real-time tracking is not available based at least in part on the scheduled locations the caregiver.
45. The system according to claim 42, wherein the data comprises one or more data packets sent to the terminal devices via the one or more networks.
46. The system according to claim 42, wherein the one or more processors identify the targeted terminal device using a reliability map of the network that is comprised of data sets representing reliability of at least one of sub-networks, links, and components of the network.
47. The system according to claim 42, wherein the one or more processors identify the targeted terminal device using current workload data for the respective caregiver associated with the at least one of the terminal devices.
48. The system according to claim 42, wherein the one or more processors identify the targeted terminal device using proximity data for the respective caregiver associated with the at least one of the terminal devices.
49. The system according to claim 42, wherein the one or more processors identify the targeted terminal device using energy level data of the respective caregiver associated with the at least one of the terminal devices.
50. The system according to claim 42, wherein the one or more processors identify the targeted terminal device using a physical distribution of the respective caregiver associated with the at least one of the terminal devices.
51. The system according to claim 42, wherein the one or more processors are further configured to automatically measure network conditions of the one or more networks by determining, for the at least one of the terminal devices, one or more latency-related values associated with each of the data and the acknowledgment data, the latency-related values including a message latency.
52. The system according to claim 51, wherein the one or more processors are further configured to weigh and combine each of the latency-related values to generate an overall reliability and latency for the at least one of the terminal devices.
53. The system according to claim 51, wherein the one or more latency-related values include one or more of: round-trip message latency, and a message routing path, and a physical location.
54. The system according to claim 42, wherein the one or more processors are further configured to: receive a response message from a responsive terminal device; and generate one or more statistics of the responsive terminal device based on the response message.
55. The system according to claim 42, wherein the one or more processors are further configured to: identify a secondary terminal device based at least in part on the predicted alarm message latency; and send the targeted message to the secondary terminal device.
56. The system according to claim 42, wherein the one or more processors are further configured to generate a report of the predicted alarm message latency.
57. The system according to claim 42, wherein the targeted terminal device is determined based at least in part on a location distribution of the terminal devices.
58. The system according to claim 42, wherein each of the terminal devices automatically generates the acknowledgment data upon receipt of the data.
59. A method for a targeted medical alarm system including one or more network adapters configured to communicate with a plurality of terminal devices over one or more networks, each of the terminal devices being associated with a respective caregiver, the method comprising: periodically transmitting data to each of the terminal devices, receiving acknowledgment data from each of the terminal devices indicating when the data was received by the respective terminal device, and storing the received acknowledgment data indicating when the data was received by the respective terminal device in one or more storage mediums; tracking real-time locations the terminal devices, and storing the real-time locations of the terminal devices in the one or more storage mediums; determining a predicted alarm message latency based on at least one of (i) the real-time locations of the terminal devices and (ii) historical acknowledgment data for at least one of the terminal devices, the historical acknowledgment data being measured when the at least one of the terminal devices was previously in the real-time location of the at least one of the terminal devices; identifying a targeted terminal device to which a targeted message is to be sent based at least in part on the predicted alarm message latency; and sending the targeted message to the targeted terminal device.
Description
TECHNICAL FIELD
[0001] The subject matter described herein relates to alarm routing monitoring and optimization strategies in a targeted medical alarm system.
BACKGROUND
[0002] In a distributed targeted alarm system, there is risk of alarm message delivery failure or delay, which could be harmful to the patient. Deliver y failure or delay can emerge at the level of systems integration. Even if individual monitoring hardware and software are perfect, timely deliveries of alarm messages will depend (at least partly) on, for example, the hospital's network infrastructure. Another factor that could cause delivery failure or delay is the terminal devices carried by caregivers that will receive the alarm messages (e.g., iPhones, Android phones, pagers). Different network devices and even caregivers may have different reliability characteristics. For example, a central station hard-wired over Ethernet will likely have a very reliable network connection, while a mobile wireless device may be less reliable. Furthermore, a mobile device connected over a wide area cellular network will have much greater latency than one connected directly to the hospital's internet network. These different possible conditions can create uncertainty in alarm message delivery.
SUMMARY
[0003] Variations of the present subject matter are directed to methods, systems, devices, and other articles of manufacture that are provided to alarm routing monitoring and optimization strategies in a targeted medical alarm system.
[0004] The present subject matter provides a targeted medical alarm system that includes a network adapter configured to communicate with a plurality of terminal devices over one or more networks. Each of the terminal devices is associated with a respective caregiver. The system also includes one or more data processors and a computer-readable medium storing instructions that when executed by the one or more data processors, performs operations that include sending test data to each of the terminal devices. The operations also include receiving acknowledgment data indicating when the test data was received by the respective terminal device, and determining one or more latency-related values associated with each of the test data and the acknowledgment data; updating reliability data based at least in part on the latency-related values. Based at least in part on the reliability data, a targeted terminal device to which a targeted message is to be sent is identified.
[0005] One or more of the following features can be included in any feasible combination. For example, in some variations, the test data comprise one or more test packets. In some variations, the test data is sent periodically. In some variations, the reliability data comprise a reliability map.
[0006] In some variations, the operations can also include one or more of: sending the targeted message to the targeted terminal device; receiving one or more response messages generated by each of the terminal devices, and generating one or more statistics for each of the terminal devices based on the one or more response messages; and identifying a secondary terminal device based at least in part on the reliability data and sending the targeted message to the secondary terminal device.
[0007] In some variations, the one or more latency-related values include one or more of: a success or failure of acknowledgment, round-trip message latency, a message routing path, and a physical location.
[0008] In some variations, the reliability data include one or more of: a current workload data for at least some of the caregivers and the associated terminal devices; a proximity data for at least some of the caregivers and the associated terminal devices; an energy level data for at least some of the caregivers and the associated terminal devices; a historical response data for at least some of the caregivers; and a physical distribution of the caregivers and the associated terminal devices.
[0009] In some variations, the one or more statistics include one or more of: a response time, a current location, a typical location, a scheduled activity, and a scheduled location.
[0010] In some variations, the targeted terminal device is determined based at least in part on the one or more statistics of each of the terminal devices.
[0011] In some variations, the secondary terminal device is identified for each critical message.
[0012] In some variations, the server is further configured to generate a report of the reliability data.
[0013] In some variations, the targeted device is determined based at least in part on a location distribution of the terminal devices.
[0014] In some variations, each of the latency-related values are weighed and combined to generate an overall reliability and latency of each of the terminal devices.
[0015] In some variations, the system further includes one or more of the plurality of terminal devices. Each of the terminal devices is configured to generate the acknowledgment data upon receipt of the test data.
[0016] The present subject matter also provides a method of targeted medical alarm for implementation by one or more data processors forming part of a least one computing device. The method includes transmitting, by at least one data processor, test data to each of a plurality of terminal devices, and receiving, by at least one data processor, an automatic acknowledgment from each of the terminal devices indicating when the test data were received. Based on the automatic acknowledgment, one or more latency-related values associated with the test data are determined (by at least one data processor), and reliability data based at least in part on the latency-related values are updated. The method also includes identifying, by at least one data processor and based on the reliability data, a terminal device to which a targeted message is to be sent.
[0017] One or more of the following features can be included in any feasible combination. For example, in some variations, the test data comprises one or more test packets.
[0018] In some variations, the test data is transmitted periodically.
[0019] In some variations, the reliability data includes one or more of: a reliability map; a current workload data for at least some of the caregivers and the associated terminal devices; a proximity data for at least some of the caregivers and the associated terminal devices; an energy level data for at least some of the caregivers and the associated terminal devices; a historical response data for at least some of the caregivers; and a physical distribution of the caregivers and the associated terminal devices.
[0020] In some variations, the method further includes sending the targeted message to the targeted terminal device.
[0021] In some variations, the one or more latency-related values include one or more of: a success or failure of acknowledgment, round-trip message latency, a message routing path, and a physical location.
[0022] In some variations, the method further includes receiving, by at least one data processor, a response message from a responsive terminal device; and generating, by at least one data processor, one or more statistics of the responsive terminal device based on the response message.
[0023] In some variations, the one or more statistics include one or more of: a response time, a current location, a typical location, a scheduled activity, and a scheduled location.
[0024] In some variations, the targeted device is determined based at least in part on the one or more statistics of each of the terminal devices.
[0025] In some variations, the method further includes identifying, by at least one data processor, a secondary terminal device based at least in part on the reliability data; and sending, by at least one data processor, the targeted message to the secondary terminal device.
[0026] In some variations, the secondary terminal device is identified for each critical message.
[0027] In some variations, the method further includes generating, by at least one processor, a report of the reliability data.
[0028] In some variations, the targeted device is determined based at least in part on a location distribution of the terminal devices.
[0029] In some variations, the method further includes weighing and combining, by one or more data processor, each of the latency-related values to generate an overall reliability and latency of each of the terminal devices.
[0030] In some variations, the method further includes generating the automatic acknowledgment from each of the terminal devices upon receipt of the test data.
[0031] Non-transitory computer program products (i.e., physically embodied computer program products) are also described that store instructions, which when executed by one or more data processors of one or more computing systems, causes at least one data processor to perform operations herein. Similarly, computer systems are also described that may include one or more data processors and memory coupled to the one or more data processors. The memory may temporarily or permanently store instructions that cause at least one processor to perform one or more of the operations described herein. In addition, methods can be implemented by one or more data processors either within a single computing system or distributed among two or more computing systems. Such computing systems can be connected and can exchange data and/or commands or other instructions or the like via one or more connections, including but not limited to a connection over a network (e.g. the Internet, a wireless wide area network, a local area network, a wide area network, a wired network, or the like), via a direct connection between one or more of the multiple computing systems, etc.
[0032] The subject matter described herein provides many advantages. For example, by providing a system and method that can determine (a) how long it will take for an alarm message to reach a caregiver, and how long will it take that caregiver to respond, (b) the uncertainty in the message latency and caregiver response time, and (c) how a targeted alarm system can mitigate this uncertainty when transmitting life-critical and/or time-critical alarm messages, alarm message delivery failures and delays can be reduced.
BRIEF DESCRIPTION OF THE FIGURES
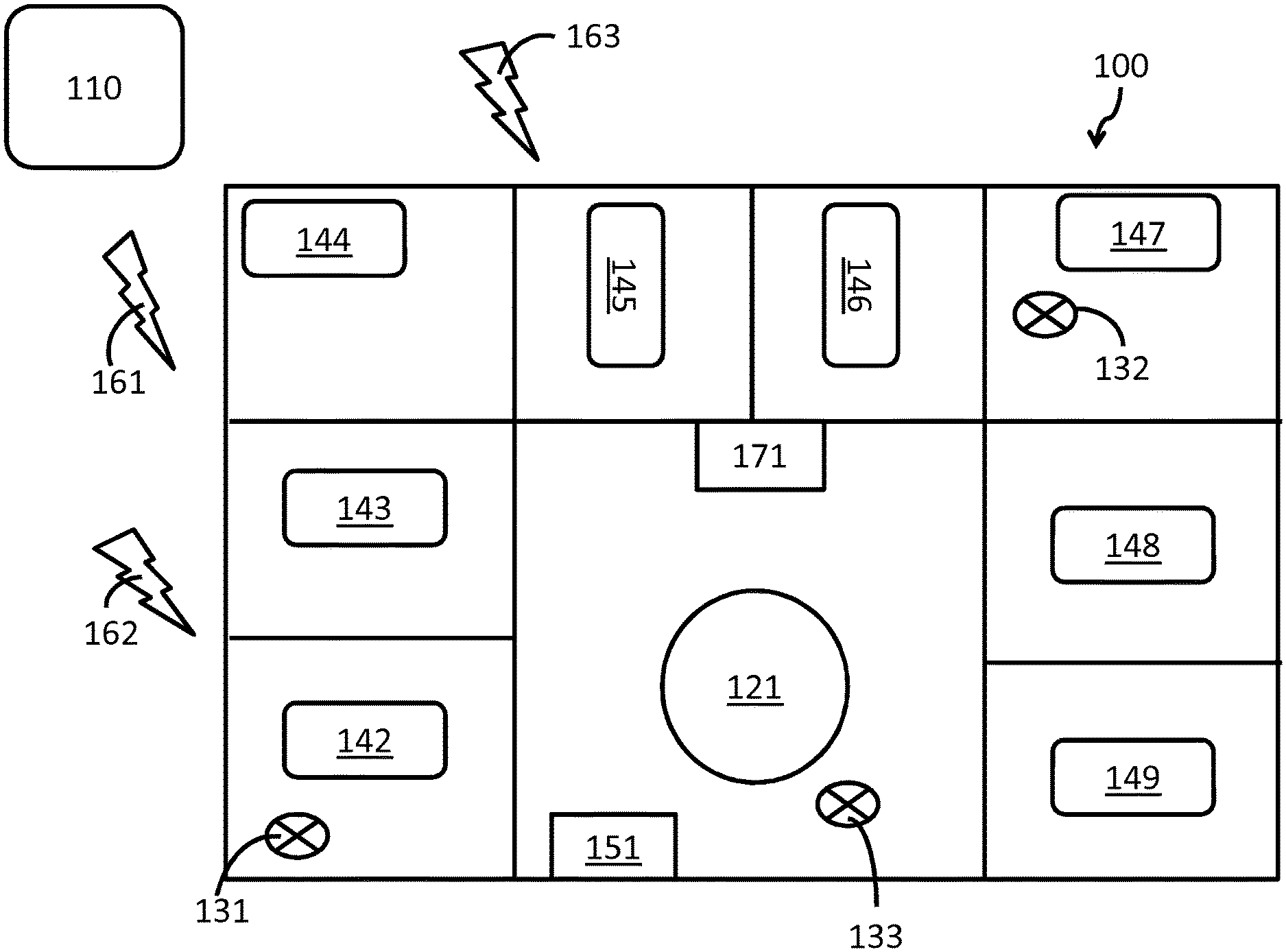
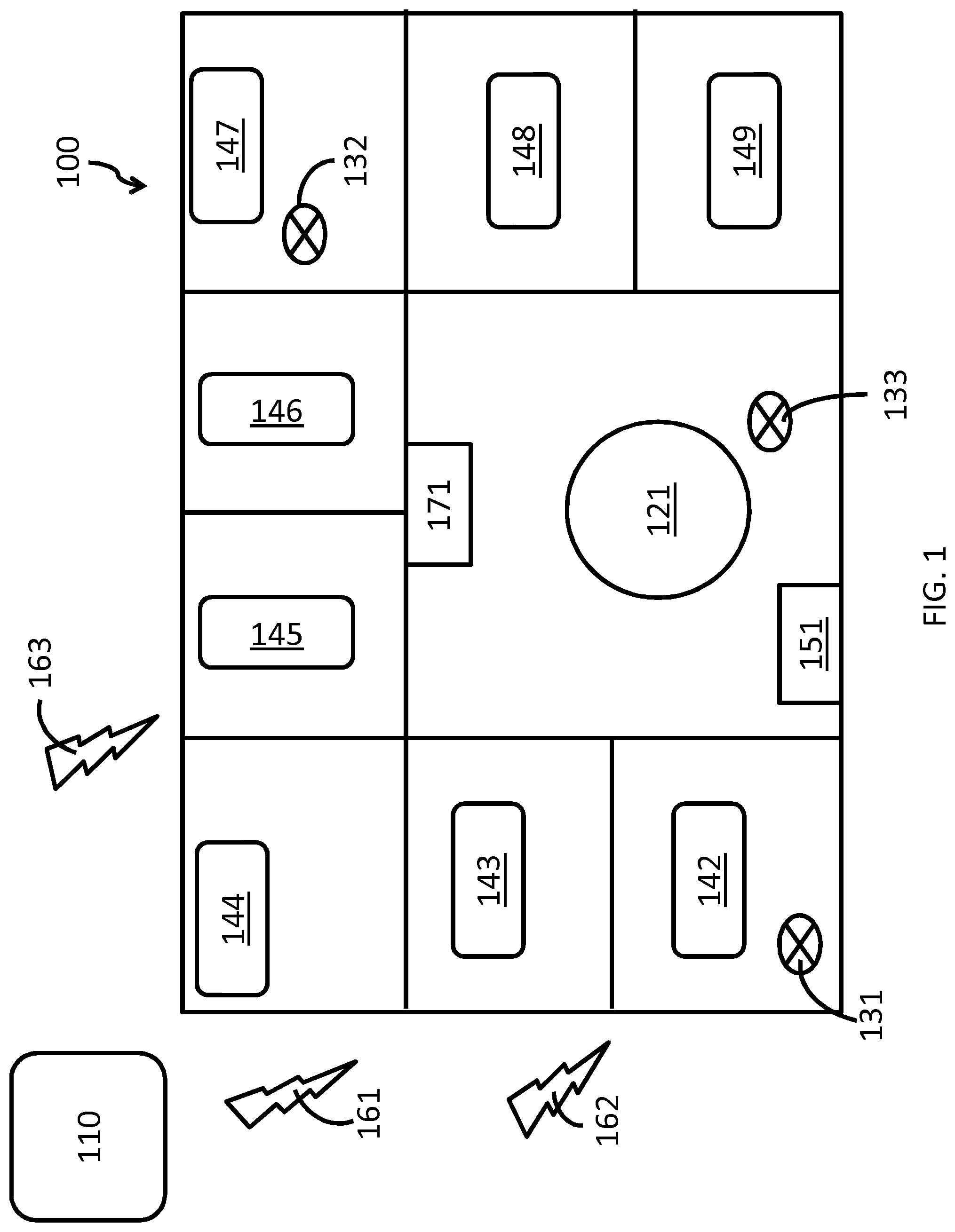
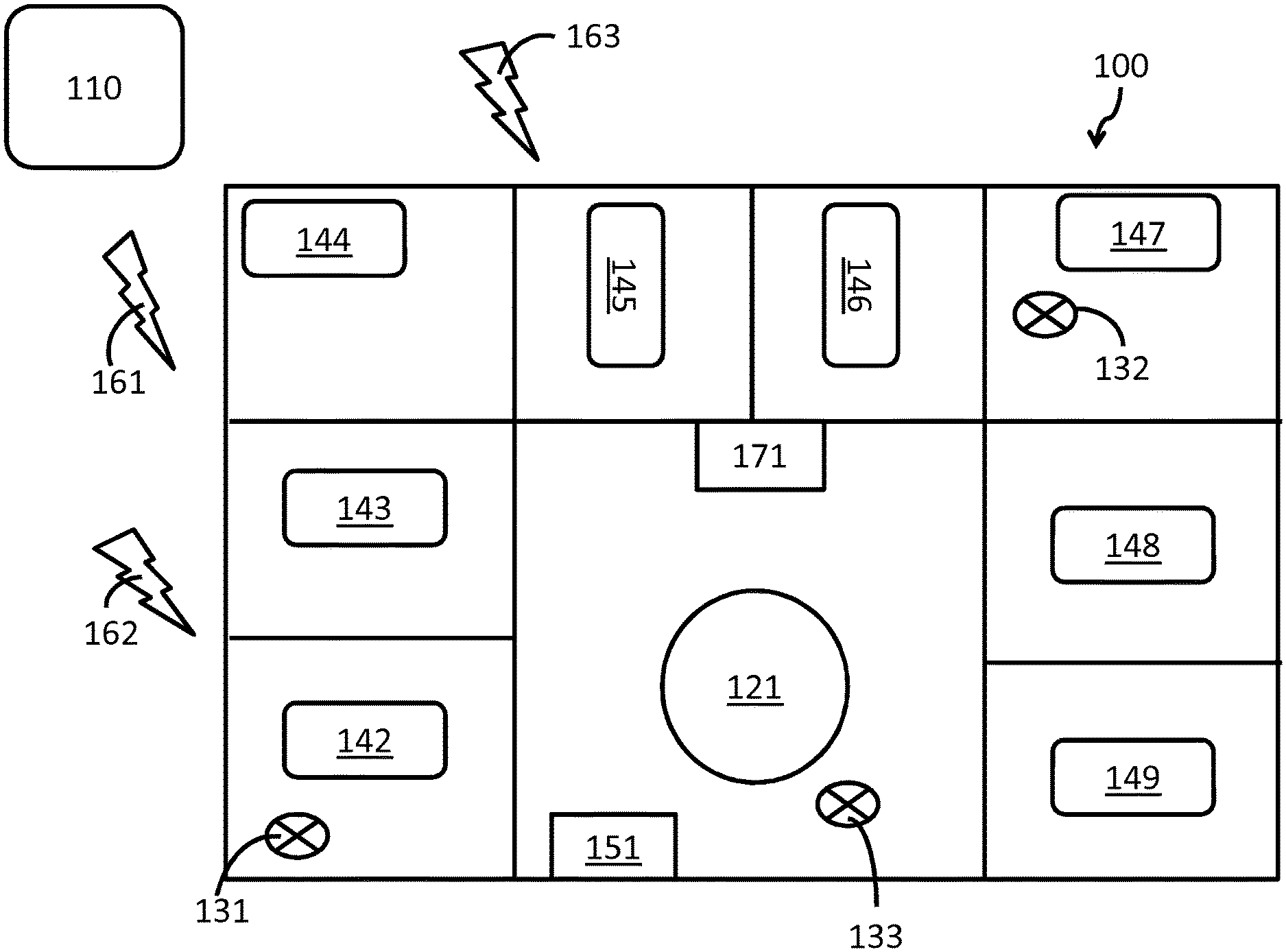
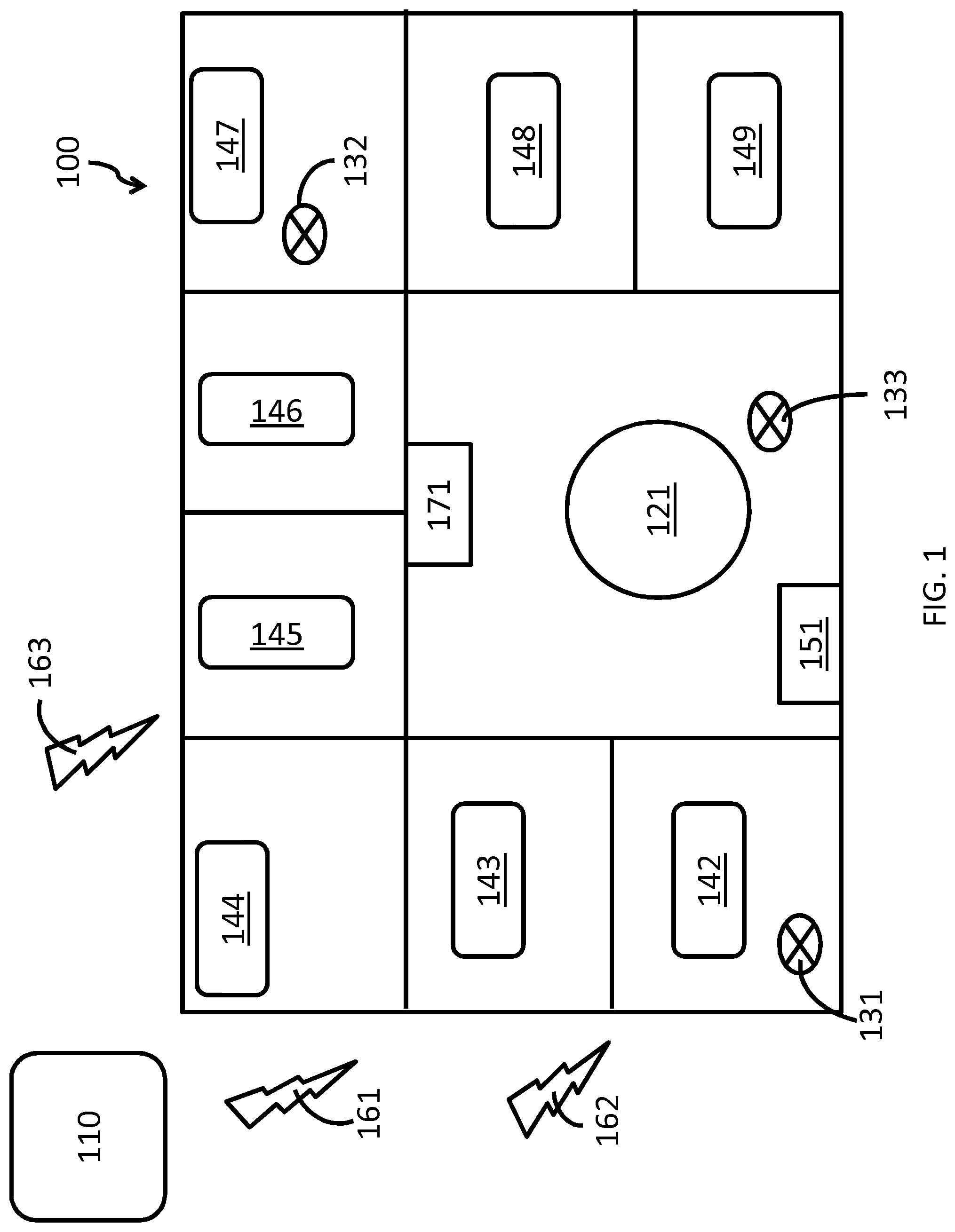
[0033] FIG. 1 is a diagrammatic illustration of an example of an environment in accordance with the current subject matter;
[0034] FIG. 2 is a diagrammatic illustration of a system in accordance with some variations of the current subject matter;
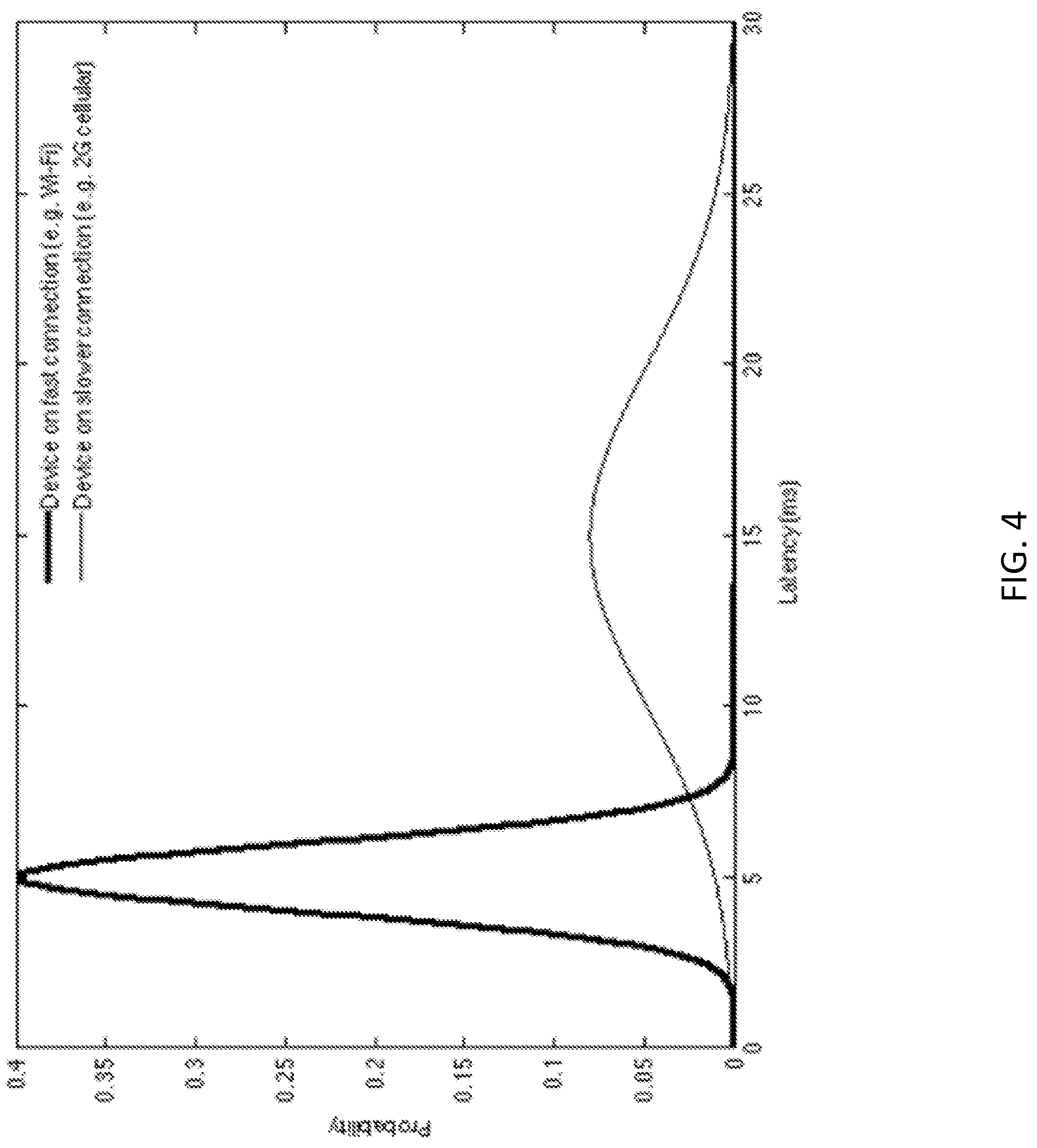
[0035] FIGS. 3-5 are graphs showing examples of the latency distribution, and probability distributions; and
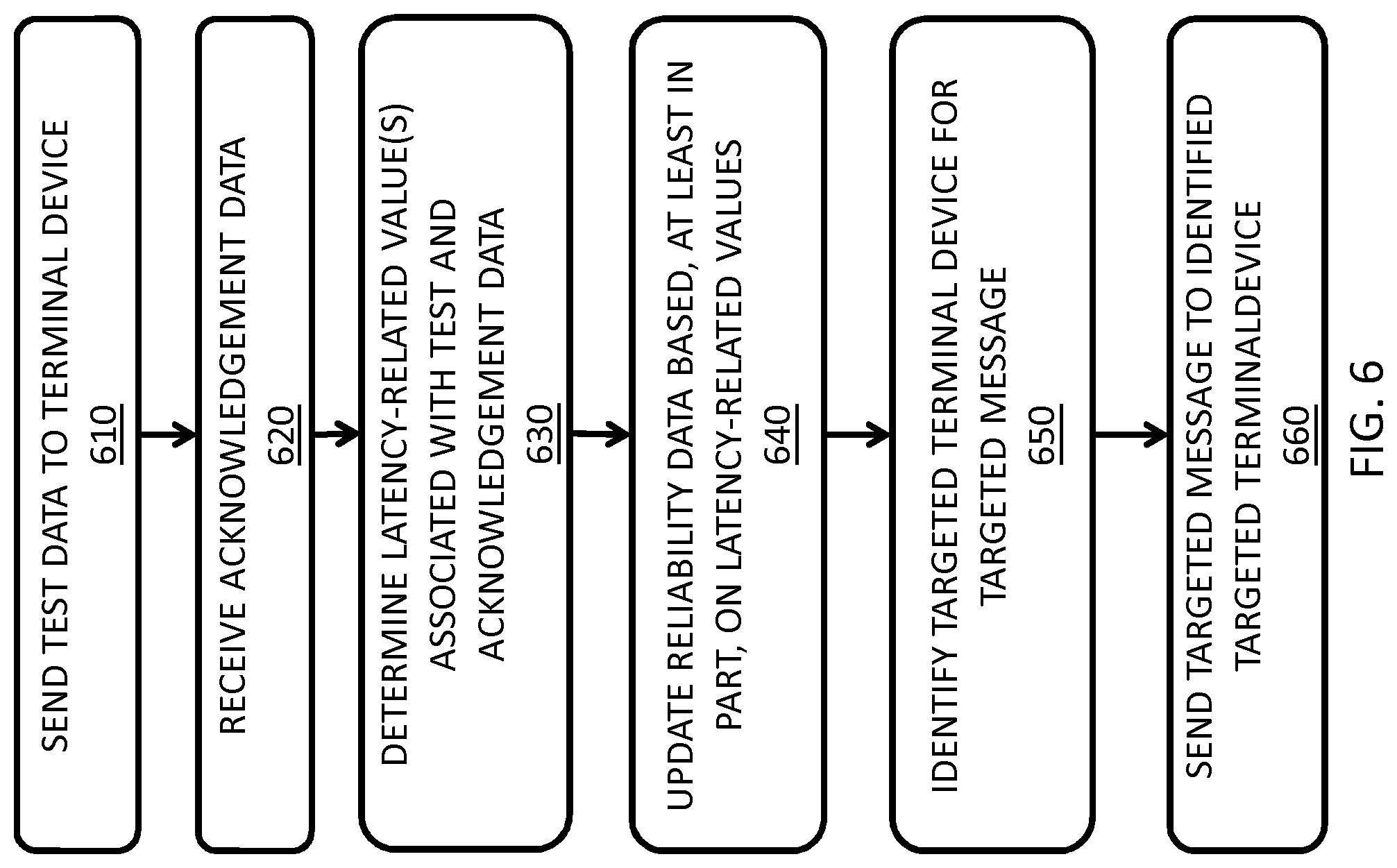
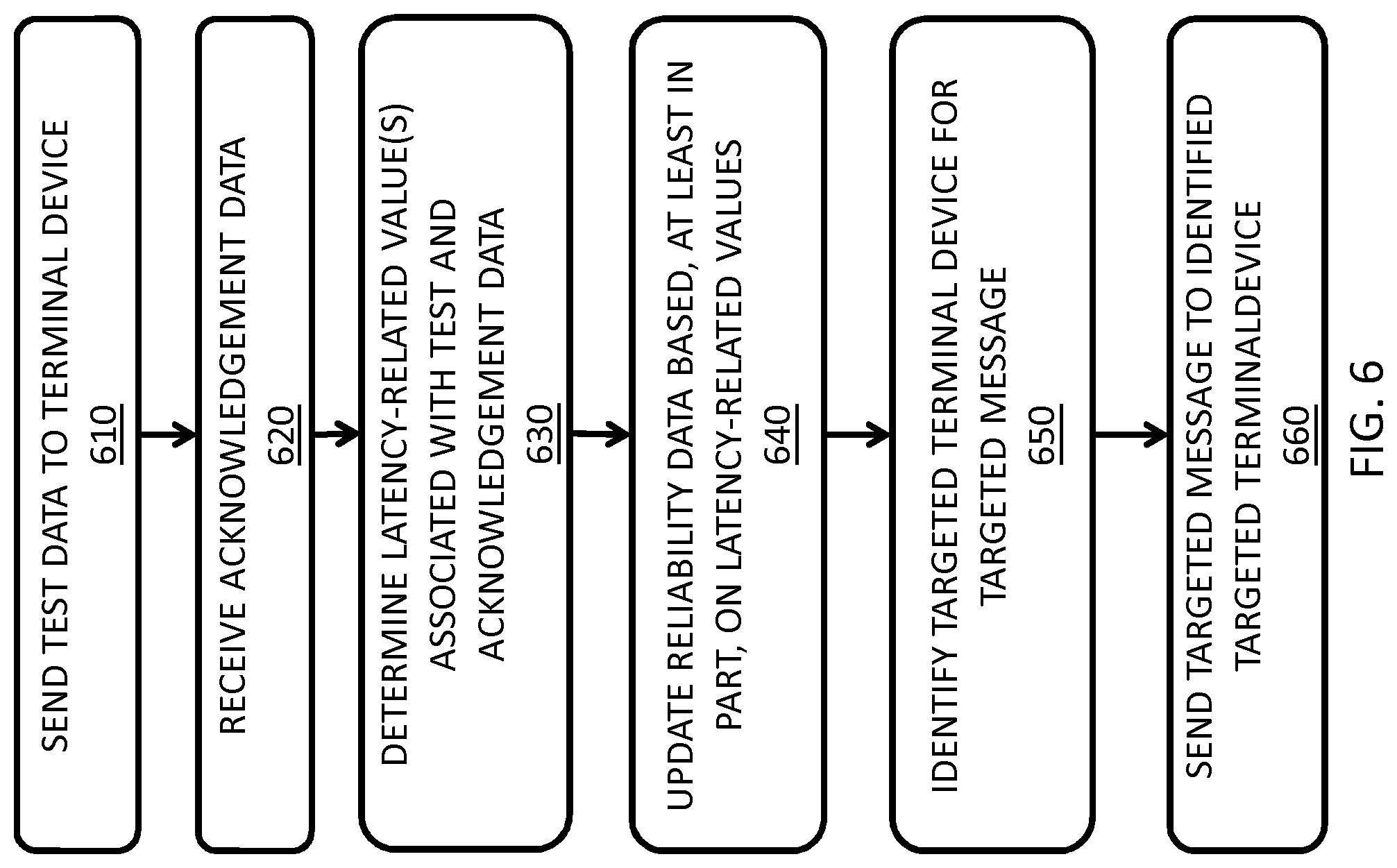
[0036] FIG. 6 shows an example of process flow in accordance with some variations of the current subject matter.
DESCRIPTION
[0037] FIG. 1 is a diagrammatic illustration of an example of an environment for implementing alarm routing monitoring, and optimization. Here, a targeted medical alarm system 110 is in data communication with terminal devices 131, 132, and 133 via one or more of cellular networks 161, 162, 163, and WiFi network 151. The terminal devices are each associated with a respective caregiver, who are caring for one or more patients in room/bed 142-149. The caregiver associated with terminal device 131 is attending to the patient in room/bed 142 while the caregiver associated with terminal device 132 is attending to the patient in room/bed 147. The caregiver associated with terminal device 133 is at the caregiver central station 121, which can be provided with an alarm display system (e.g., connected to a local computer network through a hard-wired data connection like Ethernet). Another alarm display system 171 is also provided in a common area (e.g., in a hallway). The alarm display system 171 can also be connected to the local computer network through a hard-wired data connection like Ethernet, or a wireless data communication (e.g., over WiFi network 151).
[0038] FIG. 2 is a diagrammatic illustration of system 110 in accordance with some variations of the current subject matter. In this example, system 110 includes one or more processors 111, memory 112, and network adapter 113. Network adapter 113 is configured to communicate with a plurality of terminal devices (e.g., 131-133). System 110 is in data communication with data storage 210 (e.g., for storing one or more databases containing various data relating to the terminal devices, networks, etc.) via data connection 201. System 110 can also include, for example, input devices such as a keyboard, mouse, and the like, and output devices such as speakers, display, printer, and the like. In some variations, data storage 210 can be implemented as part of the system. Memory 112 and/or storage 210 can include instructions that perform one or more features discussed in this application when executed by one or more processors 111.
[0039] In some variations, system 110 can be configured to continuously (automatically) measure network conditions to estimate the reliability of different terminal devices on different branches of the network. For example, terminal device 131 can be connected to cellular network 161, (e.g., a 2G cellular network, through a first provider), terminal device 132 is connected to cellular network 162 (e.g., a 3G cellular network, through a second provider) and WiFi network 151, and terminal device 133 is connected to cellular network 163 (e.g., a 4G cellular network, through a third provider), and system 110 can be configured to monitor and measure network conditions over each cellular network 161-163 and WiFi network 151.
[0040] In some variations, system 110 can include a network probe configured to send test data to each of the various terminal devices connected to the networks. In some variations, the test data can include test packets, which can be sent, for example, periodically.
[0041] In some variations, the terminal devices can be configured to automatically acknowledge receipt of the test data just as they would for an actual alarm message (this can be done, for example, without disturbing the caregiver). The network probe can be configured to log one or more result data including, for example: success or failure of acknowledgment, round-trip message latency, message routing path, and possibility physical location of the terminal device in space.
[0042] In some variations, the selection of the target terminal device and/or the time of message could be randomized and/or staggered so as not to overload the network. In some variations, samples are taken frequently enough to gather information with sufficient resolution over time and space. In some variations, after enough samples have been collected, the probe can derive a reliability map of the network. In some variations, the reliability map can be a data set that includes (for example) data representing the reliability of sub-networks, links, and other network components of which the network is comprised. In such a map, some sub-networks and links can be highly reliable and have low latency, while others will be less reliable and have higher latency. Reliability conditions can change over time as network channel and loading conditions change, so in some variations, the map can be (and should be) continuously dynamically updated.
[0043] The current subject matter also provides, in some variations, a system configured to predict alarm message latency based on network reliability measurements. In some variations, network reliability can be represented as a graph of probability distributions. In some variations, graph nodes can, for example, represent the terminal devices, and links between nodes can, for example, represent the network infrastructure. The network probe can be configured to find nodes and links to have certain probability distributions of latency (in the event of failure, infinite latency). In some variations, the targeted alarm system can be configured to estimate the total latency, for example, by combining the latency distributions through the graph. The result would be probabilistic, represented, for example, by a random variable with a probability distribution. Statistics could be calculated from the random variable, including, for example, one or more of: mean, median, mode, variance, skew, kurtosis, and higher order measures of uncertainty.
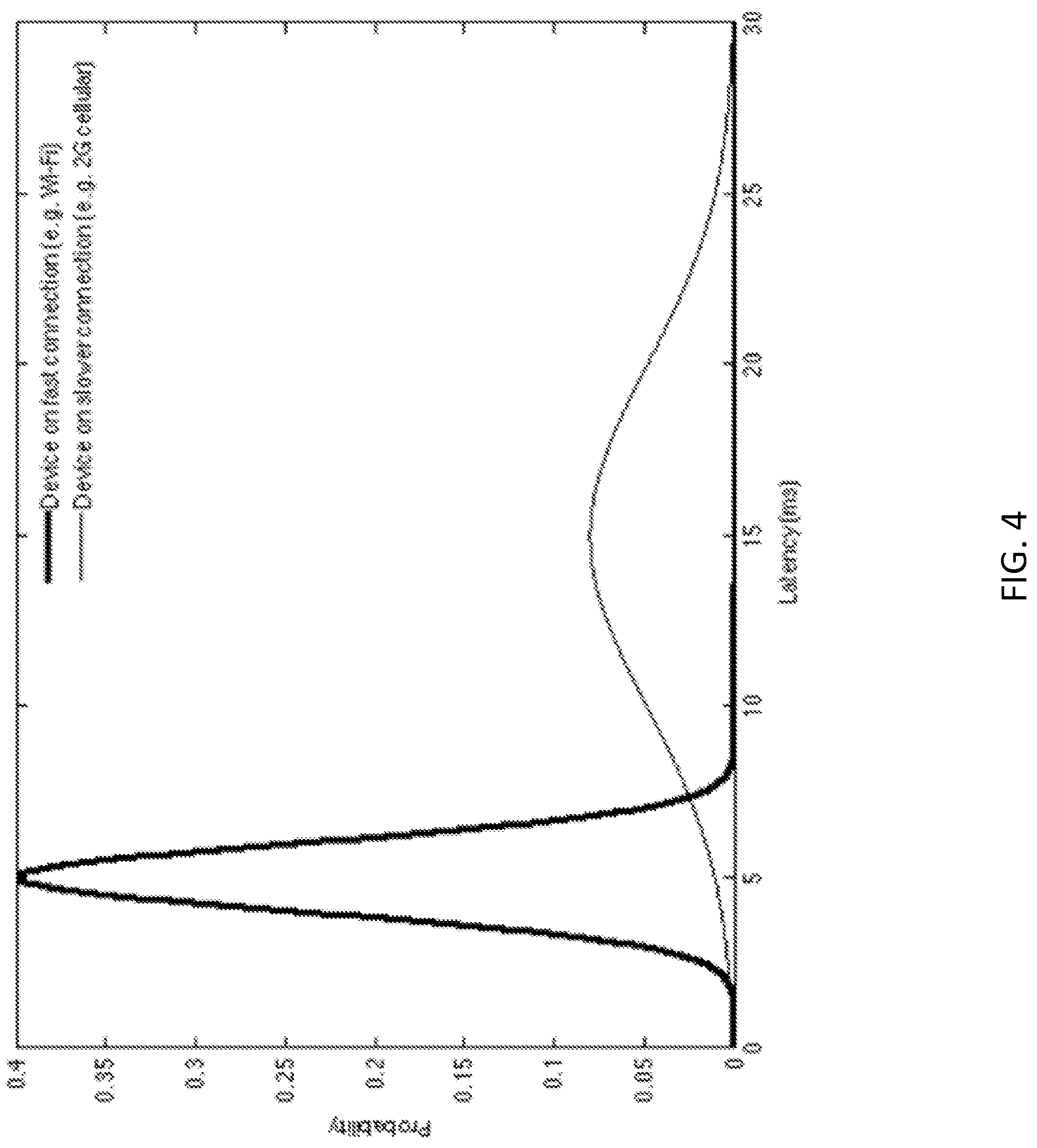
[0044] References will be made now to FIGS. 3-5, which show examples of the latency distribution, and probability distributions. These figures are provided for illustrative purposes only, and do not limit the current subject matter.
[0045] FIG. 3 shows an example of how a large collection of latency samples can be used to estimate a probability distribution. The system can be configured to sample a device's latency periodically and records the value. As the values are collected, they can be represented in a histogram (the histogram shown in FIG. 3 is normalized; that is, the frequency values are divided by the total number of samples). As the number of samples becomes very large, the histogram tends to an underlying probability distribution, probability density function (PDF). The PDF can then be used by the system to estimate the statistics of the device's latency.
[0046] FIG. 4 shows an example of the probability distributions of latency for two different devices. One device is connected to the hospital's internal Wi-Fi network, and the other on a legacy 2G cellular network. These data have been collected from historical latencies measured during automatic sampling. The Wi-Fi connected device has a lower mean latency (5 ms vs. 15 ms), which means that on average it will receive the message more quickly. It also has a smaller variance (1 ms{circumflex over ( )}2 vs. 25 ms{circumflex over ( )}2), which means that its latency is more stable and predictable. The Wi-Fi connected device is expected to have a shorter latency and is thus a better target for a time-sensitive message (all else being equal).
[0047] FIG. 5 shows the probability distributions of response time for two different nurses. These data have been collected from historical response times to previous targeted alarms. Nurse A has a lower mean latency (150 s vs. 200 s), which means that on average s/he will respond to a message more quickly. However, Nurse A has a larger variance (1600 s{circumflex over ( )}2 vs. 100 s{circumflex over ( )}2), which means his/her response time is less predictable. Nurse A is expected to respond more quickly to the message, but there is a chance s/he may take much longer to respond. In certain situations this may be acceptable. In other situations, a more stable/predictable response time may be more desirable than a quicker average response time. The system may choose Nurse A or B based on its requirements for the given message.
[0048] The probability distributions can be combined together to arrive at a total response time distribution. Individual parameters may include the device latency given its current location and network connection, the individual caregiver's innate response time, the caregiver's time since the start of his/her shift, the caregiver's current workload, and the travel time from the caregiver's current location. Probability density functions (PDFs) as shown in FIGS. 4, 5, and 6 can be combined by convolving them. The convolution operator is a standard mathematical technique known to those skilled in the art, and can easily be implemented on a computer. For a full treatment of the combinations of probability distributions, see e.g. Springer M. D. 1979, "The Algebra of Random Variables," John Wiley & Sons, New York (the contents of which are incorporated herein by reference).
[0049] In some variations, the targeted medical alarm system can be further configured to track one or more statistics on the individual caregivers, including, for example one or more of:
[0050] A. Response times: historical response times to alarm messages can be used to estimate the caregiver latency. This latency can be estimated, for example, as a factor independent of the network infrastructure and messaging device used.
[0051] B. Current location: If real-time location tracking is available, the system can be configured to track it.
[0052] C. Typical locations: If real-time location tracking is unavailable, the system can be configured to use typical assignment locations from the caregiver's schedule as approximations for expected latency calculations.
[0053] D. Scheduled activities and locations: If a caregiver is assigned to different care areas at different times or days, the system can be configured to track this information to predict caregiver location.
[0054] In some variations, the targeted medical alarm system can be configured to use feedback from the probe's estimated statistics of the network, devices, and caregivers to intelligently identify one or more recipients for each alarm message. For example, when a monitor detects a critical condition in a patient that requires an immediate response (e.g., asystole or ventricular fibrillation), the targeted alarm system can be configured to employ, for example, a routing table that can include an escalation path (having, for example, one or more of primary, secondary, tertiary, etc.) of caregivers responsible for responding to the alarm to route the critical message in an efficient way that minimizes delivery failure and/or delay. In some variations, the system can be configured to minimize its routing path to elicit the most rapid response possible.
[0055] In some variations, the targeted medical alarm system can he configured to select (identify) or reject a terminal device/caregiver based on estimated network latency and reliability. For example, the reliability map may indicate that the primary caregiver is in an unreliable branch of the network. The probe map may have this information from, for example, real-time location tracking, scheduled caregiver activities, or statistics of historical locations for this particular caregiver. In response, the targeted alarm system can be configured, for example, to re-route the alarm to a secondary caregiver who is more likely to receive the high priority alarm quickly. This can be repeated, in some variations, to be re-routed to a tertiary, or additional layers of caregivers depending on estimated network latency and reliability. In some variations, the system can include a threshold value (e.g., maximum latency permitted) in identifying or rejecting a terminal device/caregiver.
[0056] FIG. 6 shows an example of process flow in accordance with some variations of the current subject matter. At 310, the system sends test data to a terminal device 310. The terminal device is configured to generate acknowledgment data, including when the test data was received, and send the acknowledgment data to the system (received by the system at 320). The system determines one or more latency-related values associated with the test and acknowledgment data at 330, and updates (e.g., generates and stores) reliability data that are based, at least in part, on the one or more latency-related values at 340. When the system needs to send a targeted alarm message (e.g., a critical care message), the system identifies a targeted terminal device (with an associated caregiver) for the targeted message at 350, which is based, at least in part, on the reliability data. At 360, the system sends the targeted message to the identified targeted device.
[0057] In some variations, the alarm system can be configured to select (identify) or reject a terminal device/caregiver based on estimated device latency and/or reliability. For example, the probe map may indicate that the primary caregiver's device has a high latency (e.g., connected to a 2G cellular network). In response, the targeted alarm system can be configured to re-route the alarm to a secondary (or a tertiary, etc.) caregiver who is more likely to receive the high priority alarm quickly.
[0058] In some variations, the alarm system can be configured to select (identify) the optimum terminal device/caregiver based on the caregiver's current workload. The scheduling statistics may indicate that the primary caregiver is currently occupied on another alarm or assigned to a different high priority action, and may be too busy to react quickly. In response, the targeted alarm system can be configured to re-route the alarm to the secondary (or tertiary, etc.) caregiver who is currently unoccupied, or less busy, and thus able to respond more quickly. In some variations, the system can be configured to send the alarm message to an already-occupied caregiver only if the alarm is of higher priority than the caregiver's current task.
[0059] In some variations, the alarm system can be configured to select (identify) the optimum caregiver based on, for example, proximity to the patient needing care. Using the real-time location tracking of all caregivers, the system can be configured to determine that, for example, the tertiary caregiver is in closest proximity to the patient. Proximity measures can be, for example, simple linear distances, or can take into account a map of the care area and the travel path required to reach the patient. In response, the targeted alarm system can be configured to re-route the alarm to the tertiary caregiver (for example) who is able to respond more quickly.
[0060] In some variations, the alarm system can be configured to select (identify) an optimum caregiver based on energy level, estimated from the time since the start of the caregiver's shift. For example, the system can be configured to record, for example, the number and/or the type of tasks the caregiver has performed during a particular shift. Based on this information, the system can be configured to route the alarm message to a fresh caregiver at the start of his/her shift (or who has performed fewer and/or lesser tiring tasks), who is more likely to have higher energy levels and is more likely to respond quickly to the alarm.
[0061] In some variations, the alarm system can be configured to select (identify) an optimum caregiver based on historical response rates and/or times. For example, the system can be configured to reject a primary caregiver who often fails to response to alarm messages in the past (e.g., does not notice his/her phone vibrating), in favor of a more responsive secondary caregiver.
[0062] In some variations, the system can be configured to maintain a physical distribution of caregivers to prepare for unexpected future alarms. For example, the system can be configured to keep track of the physical locations of individual caregivers, and the larger distribution of the caregiver population. The system can be configured to target the alarms in such a way as to help ensure the caregivers remain physically distributed across care areas. If most caregivers were to become concentrated all in one care area, it would leave some patients more at risk of a longer response to a critical event.
[0063] In some variations, the system can be configured to employ one or more (including all) factors and variations described above, for example, weighing them to identify a target caregiver for sending the alarm message. For example, the reliability and/or latency of one or more (including all) elements in the system (e.g., network, device, caregiver) can be combined to estimate the overall reliability and latency of each caregiver at a given point in time. The system can be configured to select (identify) the caregiver with the highest reliability and/or lowest latency at the particular time required for the particular alarm condition, and routes the alarm message to him/her.
[0064] In some variations, the system can be configured to generate a report including one or more of, for example, reliability, latency, and other statistics to help identify one or more weak points in the targeted alarming system. Such reports could allow, for example, the hospital administration, or technicians, to improve unreliable parts of the network, upgrade terminal devices that do not perform well as alarm recipients, and device caregiver management strategies to improve schedule, physical distribution, workflow, and more.
[0065] One or more aspects or features of the subject matter described herein can be realized in digital electronic circuitry, integrated circuitry, specially designed application specific integrated circuits (ASICs), field programmable gate arrays (FPGAs) computer hardware, firmware, software, and/or combinations thereof. These various aspects or features can include implementation in one or more computer programs that are executable and/or interpretable on a programmable system including at least one programmable processor, which can be special or general purpose, coupled to receive data and instructions from, and to transmit data and instructions to, a storage system, at least one input device, and at least one output device. The programmable system or computing system may include clients and servers. A client and server are generally remote from each other and typically interact through a communication network. The relationship of client and server arises by virtue of computer programs running on the respective computers and having a client-server relationship to each other.
[0066] These computer programs, which can also be referred to as programs, software, software applications, applications, components, or code, include machine instructions for a programmable processor, and can be implemented in a high-level procedural language, an object-oriented programming language, a functional programming language, a logical programming language, and/or in assembly/machine language. As used herein, the term "machine-readable medium" refers to any computer program product, apparatus and/or device, such as for example magnetic discs, optical disks, memory, and Programmable Logic Devices (PLDs), used to provide machine instructions and/or data to a programmable processor, including a machine-readable medium that receives machine instructions as a machine-readable signal. The term "machine-readable signal" refers to any signal used to provide machine instructions and/or data to a programmable processor. The machine-readable medium can store such machine instructions non-transitorily, such as for example as would a non-transient solid-state memory or a magnetic hard drive or any equivalent storage medium. The machine-readable medium can alternatively or additionally store such machine instructions in a transient manner, such as for example as would a processor cache or other random access memory associated with one or more physical processor cores.
[0067] To provide for interaction with a user, one or more aspects or features of the subject matter described herein can be implemented on a computer having a display device, such as for example a cathode ray tube (CRT) or a liquid crystal display (LCD) or a light emitting diode (LED) monitor for displaying information to the user and a keyboard and a pointing device, such as for example a mouse or a trackball, by which the user may provide input to the computer. Other kinds of devices can be used to provide for interaction with a user as well. For example, feedback provided to the user can be any form of sensory feedback, such as for example visual feedback, auditory feedback, or tactile feedback; and input from the user may be received in any form, including, but not limited to, acoustic, speech, or tactile input. Other possible input devices include, but are not limited to, touch screens or other touch-sensitive devices such as single or multi-point resistive or capacitive trackpads, voice recognition hardware and software, optical scanners, optical pointers, digital image capture devices and associated interpretation software, and the like.
[0068] In the descriptions above and in the claims, phrases such as "at least one of" or "one or more of" may occur followed by a conjunctive list of elements or features. The term "and/or" may also occur in a list of two or more elements or features. Unless otherwise implicitly or explicitly contradicted by the context in which it is used, such a phrase is intended to mean any of the listed elements or features individually or any of the recited elements or features in combination with any of the other recited elements or features. For example, the phrases "at least one of A and B;" "one or more of A and B;" and "A and/or B" are each intended to mean "A alone, B alone, or A and B together." A similar interpretation is also intended for lists including three or more items. For example, the phrases "at least one of A, B, and C;" "one or more of A, B, and C;" and "A, B, and/or C" are each intended to mean "A alone, B alone, C alone, A and B together, A and C together, B and C together, or A and B and C together." In addition, use of the term "based on," above and in the claims is intended to mean, "based at least in part on," such that an unrecited feature or element is also permissible.
[0069] The subject matter described herein can be embodied in systems, apparatus, methods, and/or articles depending on the desired configuration. The implementations set forth in the foregoing description do not represent all implementations consistent with the subject matter described herein. Instead, they are merely some examples consistent with aspects related to the described subject matter. Although a few variations have been described in detail above, other modifications or additions are possible. In particular, further features and/or variations can be provided in addition to those set forth herein. For example, the implementations described above can be directed to various combinations and subcombinations of the disclosed features and/or combinations and subcombinations of several further features disclosed above. In addition, the logic flows depicted in the accompanying figures and/or described herein do not necessarily require the particular order shown, or sequential order, to achieve desirable results. Other implementations may be within the scope of the following claims.
* * * * *
D00000
D00001
D00002

D00003

D00004
D00005

D00006
XML
uspto.report is an independent third-party trademark research tool that is not affiliated, endorsed, or sponsored by the United States Patent and Trademark Office (USPTO) or any other governmental organization. The information provided by uspto.report is based on publicly available data at the time of writing and is intended for informational purposes only.
While we strive to provide accurate and up-to-date information, we do not guarantee the accuracy, completeness, reliability, or suitability of the information displayed on this site. The use of this site is at your own risk. Any reliance you place on such information is therefore strictly at your own risk.
All official trademark data, including owner information, should be verified by visiting the official USPTO website at www.uspto.gov. This site is not intended to replace professional legal advice and should not be used as a substitute for consulting with a legal professional who is knowledgeable about trademark law.