Smartphone Based Reminding System For Forgotten Objects
Lenchner; Jonathan ; et al.
U.S. patent application number 16/584836 was filed with the patent office on 2021-04-01 for smartphone based reminding system for forgotten objects. The applicant listed for this patent is International Business Machines Corporation. Invention is credited to Jonathan Lenchner, Komminist Weldemariam, Reha Yurdakul.
| Application Number | 20210097843 16/584836 |
| Document ID | / |
| Family ID | 1000004398463 |
| Filed Date | 2021-04-01 |

| United States Patent Application | 20210097843 |
| Kind Code | A1 |
| Lenchner; Jonathan ; et al. | April 1, 2021 |
SMARTPHONE BASED REMINDING SYSTEM FOR FORGOTTEN OBJECTS
Abstract
A peripheral device, e.g. a smart phone, receives information defining a secured area perimeter of a secure area and a global positioning system (GPS) about the location of a user. The process compares the security perimeter to the position information to determine whether a user is within the secured area. If the user is outside the secured area and has not returned an access device, e.g. a badge, a temporary pass, etc., the peripheral device posts an alert to the user, e.g. a warning the user may have forgotten to return the access device/badge. Alerts can be posted or sent for other conditions as well.
| Inventors: | Lenchner; Jonathan; (North Salem, NY) ; Yurdakul; Reha; (Istanbul, TR) ; Weldemariam; Komminist; (Ottawa, CA) | ||||||||||
| Applicant: |
|
||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|
| Family ID: | 1000004398463 | ||||||||||
| Appl. No.: | 16/584836 | ||||||||||
| Filed: | September 26, 2019 |
| Current U.S. Class: | 1/1 |
| Current CPC Class: | H04B 5/0062 20130101; H04W 4/021 20130101; H04B 5/0025 20130101; H04W 4/80 20180201; G08B 21/24 20130101; H04W 4/023 20130101 |
| International Class: | G08B 21/24 20060101 G08B021/24; H04W 4/02 20060101 H04W004/02; H04W 4/021 20060101 H04W004/021; H04W 4/80 20060101 H04W004/80; H04B 5/00 20060101 H04B005/00 |
Claims
1: A peripheral device comprising: one or more memories, one or more central processing units (CPUs), and one or more user interfaces, the user interfaces capable of sending and receiving information; and a process executed by the one or more CPUs that i. receives geometric information defining a secured area perimeter of a secure area from the one or more user interfaces; ii. receives user position information from a global positioning system (GPS) through the one or more interfaces, iii. compares the security perimeter to the position information to determine whether or not a user is within the secured area and takes some action when the user is deemed to be outside the secure area and an access device to the secure area is not returned, wherein the process is removed from the peripheral device or stops executing on the one or more CPUs when a user returns the access device.
2: The peripheral device, as in claim 1, where the process posts an alert to the user on the one or more user interfaces when the user is deemed to be outside the secure area.
3: The peripheral device, as in claim 2, where the process is enabled when the user has possession of the access device and the alert is only sent when the user has not returned the access device.
4: The peripheral device, as in claim 3, where the access device is one or more of the following: a badge, a temporary identification, and a radio frequency identification (RFID) device.
5: The peripheral device, as in claim 1, that is a smart phone.
6: The peripheral device, as in claim 1, where the geometric information is received by the peripheral device by the one or more user interfaces when an access device is given to the user.
7: The peripheral device, as in claim 1, where the geometric information further comprises a tolerance perimeter information.
8: The peripheral device, as in claim 7, where the tolerance perimeter information describes a tolerance perimeter a tolerance distance outside of the secured area perimeter.
9: The peripheral device, as in claim 1, where the secured area perimeter is in the shape of a polygon and the geometric information are GPS coordinates of one or more vertices of the polygon.
10: The peripheral device, as in claim 1, where the process further receives information from the one or more user interfaces about a final time the user is to leave the secured area.
11: The peripheral device, as in claim 10, where the process sends the final alert to the user through the one or more user interfaces after the final time if an access device is not returned, the final alert indicating the user has left the secured area without returning the access device.
12: The peripheral device, as in claim 1, where the process further receives other information through the one or more user interfaces about one or more conditions, the conditions including one or more of the following: a security level for the secured area, a classification of the user, a time of allowed access to the secured area, and a date of allowed access to the secured area.
13: The peripheral device, as in claim 12, where if one or more of the conditions is not met and an access device is not returned, an alert is sent to the user.
14: The peripheral device, as in claim 1, where the geometric information is received by the peripheral device by one or more of the following: a radio frequency signal, a hard wire connection, a one time reading of a visual code, a one time scan, a one time reading of a bar code, and a one time reading of a quick response (QR) code, and a text.
15: A method of alerting a user comprising the steps of: receiving geometric information defining a secured area perimeter of a secure area; receiving user position information from a global positioning system (GPS); determining whether the user returned an access device; comparing the position information to the geometric information to determine whether the user is outside the secured area; and alerting the user with an alert when the user is deemed to be outside the secured area and has not returned the access device.
16: The method, as in claim 15, where the alert is a final alert if the time is passed a final time the user is expected to be in the secured area.
17: The method, as in claim 15, where the alert is a final alert when the user has failed to meet a condition and has not returned the access device.
18: The method, as in claim 17, where the condition is one or more of the following: having an inappropriate user classification, being in the secured area within a time period, being within the secured area on a date in time, time passing a final time, and an incompatibility between a security level of the secured area and the user classification.
19: A system for alerting a user to return an access device comprising: a base station having one or more memories, one or more central processing units, and one or more user interfaces; geometric information stored in the one or more memories, the geometric information defining one or more secured area perimeters, each of the one or more secured area perimeters defining a secured area; a process that creates a scannable input containing the geometric information; and one or more displays being one or more of the user interfaces, the displays displaying the scannable input so a peripheral device can read the geometric information.
20: The system, as in claim 19, where other information is stored in the one or more memories, included in the scannable input, and displayed on the one or more of the displays.
Description
BACKGROUND
[0001] The present invention relates to a system and method using a smartphone for reminding a user about forgotten objects, and more specifically, to remind users to return forgotten visitor's badges.
[0002] When visiting a secured area, a visitor is often given an access device, e.g. a security or visitor's badge, that needs returning later. Sometimes the visitor is required to give some sort of identification or other surety to ensure the access device/badge is returned.
[0003] However, it is not uncommon to forget to return the visitor's badge. The problem is compounded when the surety is not returned to the visitor in exchange for returning the badge. For example, if the surety is a form of identification, possibly a passport, that is not returned to the visitor, the visitor potentially risks great inconvenience, e.g. arriving at an airport with no passport.
[0004] There is a need for a system that reminds users to return objects like security badges and re-acquire any surety that was given in exchange.
SUMMARY
[0005] According to one embodiment, the present invention is a peripheral device, e.g. a smartphone, with one or more memories, one or more central processing units (CPUs), and one or more user interfaces. The user interfaces can send and receive information. A process executes on the peripheral device. The process receives geometric information defining a secured area perimeter of a secure area through one or more of the user interfaces of the peripheral device. Typically, the geometric information is received one time. The peripheral device (process) also receives user position information from a global positioning system (GPS) through one of the peripheral device interfaces. The process compares the security perimeter to the position information to determine whether a user is within the secured area.
[0006] Using this information, the peripheral device can perform various functions. As an example, the device process provides/posts an alert to the user when the user is outside the secure area. Generally, the alert is posted only when the user still possesses (has not returned) an access device (e.g. a temporary pass, temporary identification, badge, radio frequency device, etc.) and the user is outside of the secured area, i.e. the user may have forgotten to return the access device/badge.
[0007] Various alert types are described. Conditions can also be provided to the device. For example, conditions might include one or more of the following: a security level for the secured area, a classification of the user, a time of allowed access to the secured area, and a date of allowed access to the secured area, etc. If one or more conditions is not met and the access device/badge is not returned, an alert can be sent or posted to the user.
[0008] A base station, systems, and methods are also disclosed.
BRIEF DESCRIPTION OF THE DRAWINGS
[0009] Various embodiments of the present invention will be described below in more detail, with reference to the accompanying drawings, now briefly described. The Figures show various apparatus, structures, and related method steps of the present invention.
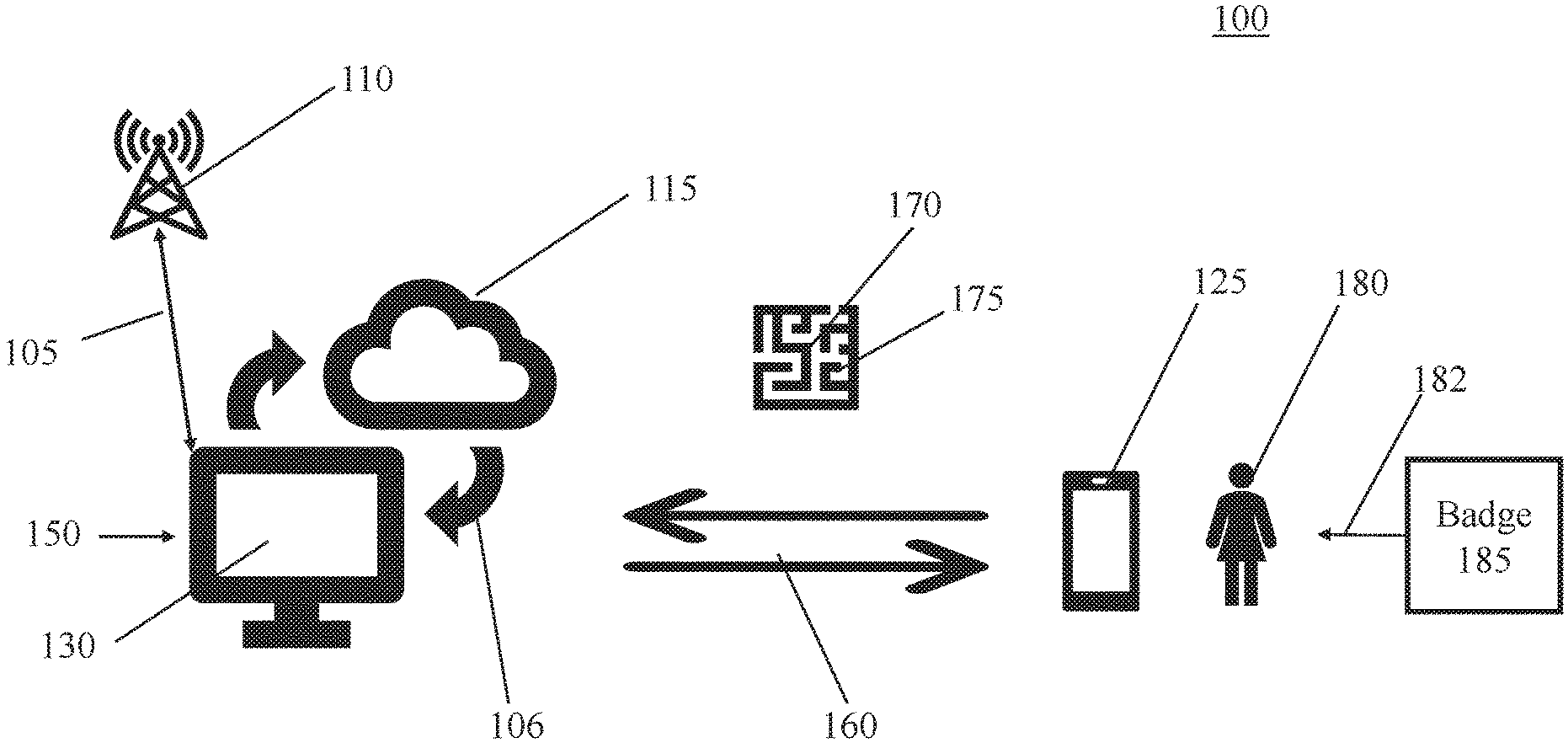
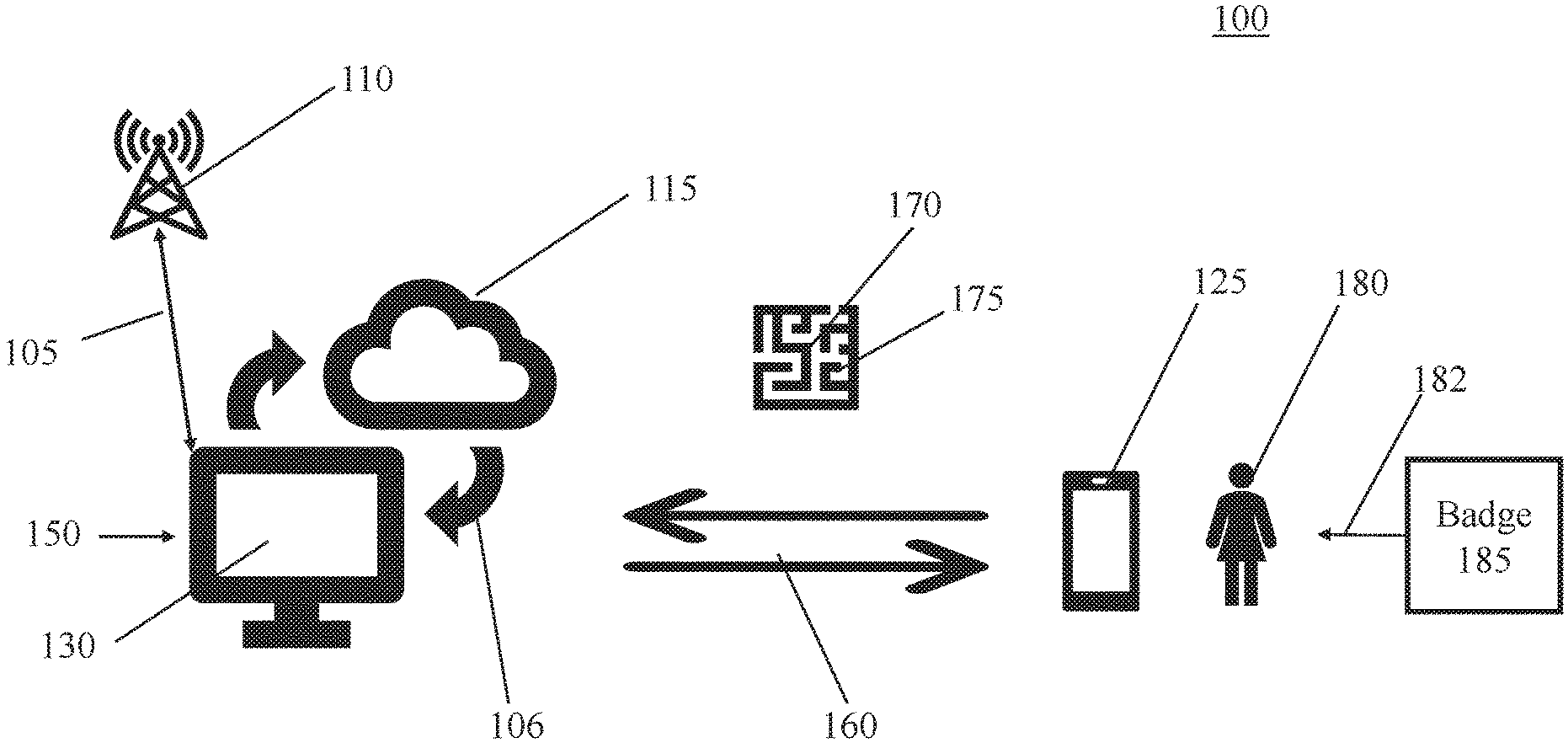
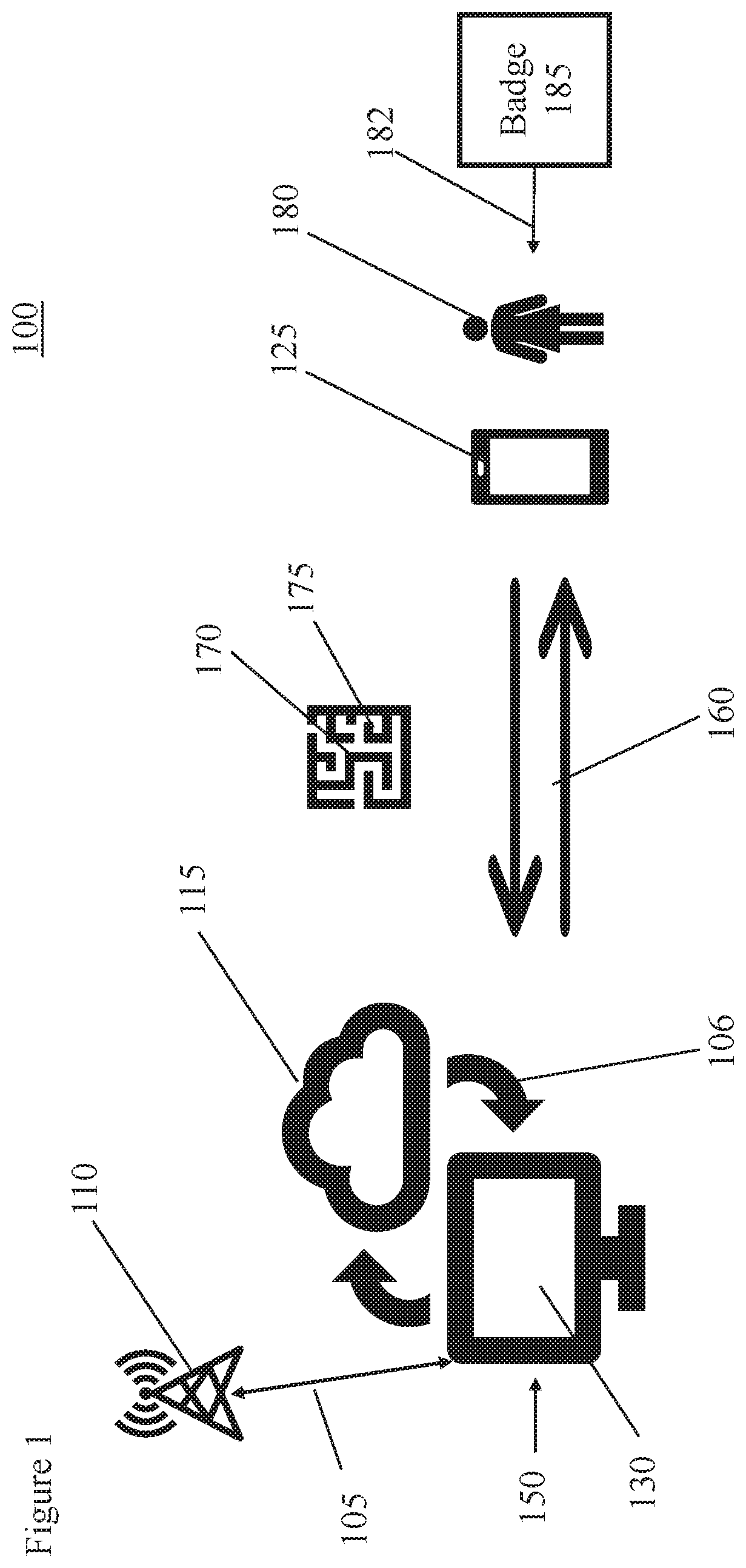
[0010] FIG. 1 is an illustration of one embodiment of the present invention showing a base station, a user, and a peripheral device like a smart phone.
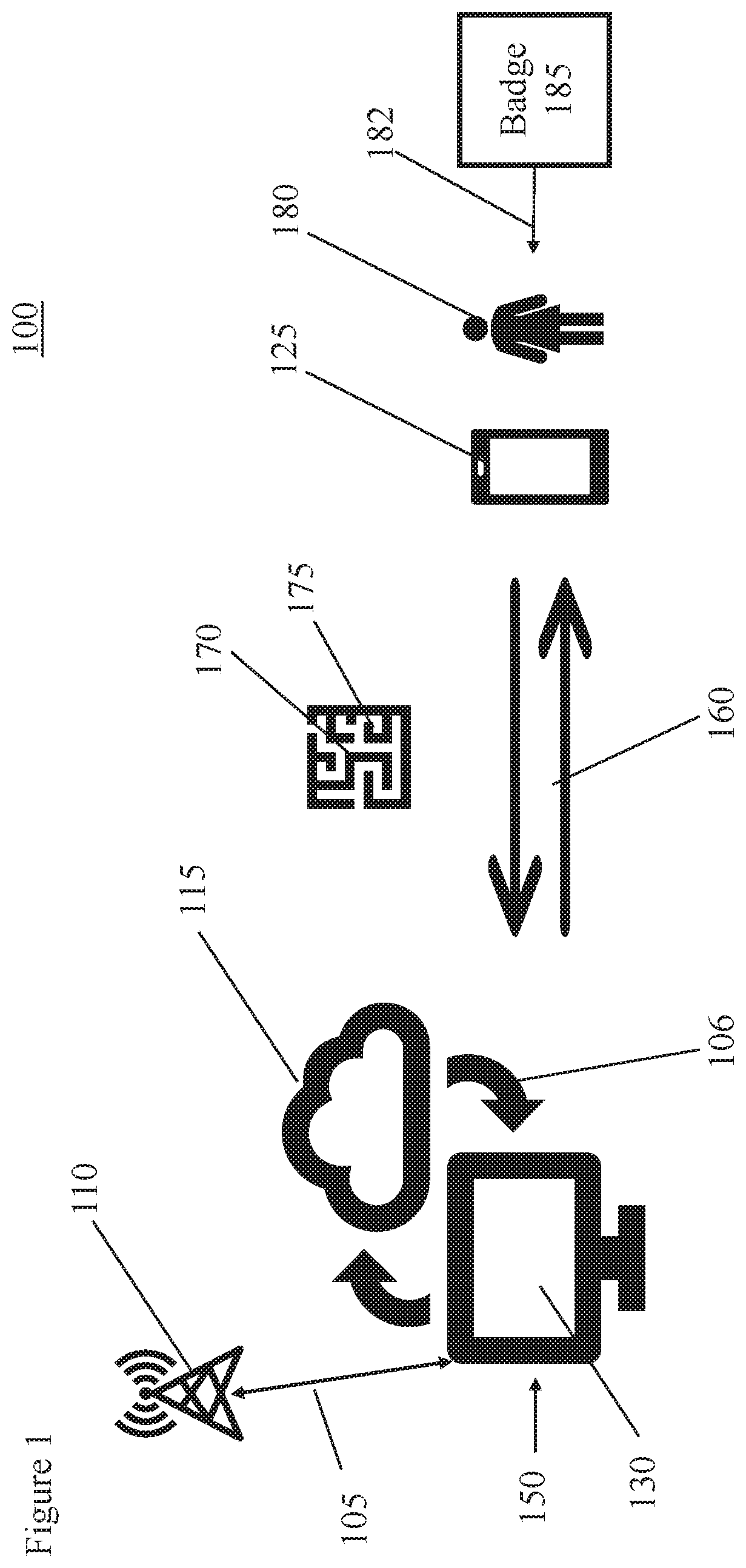
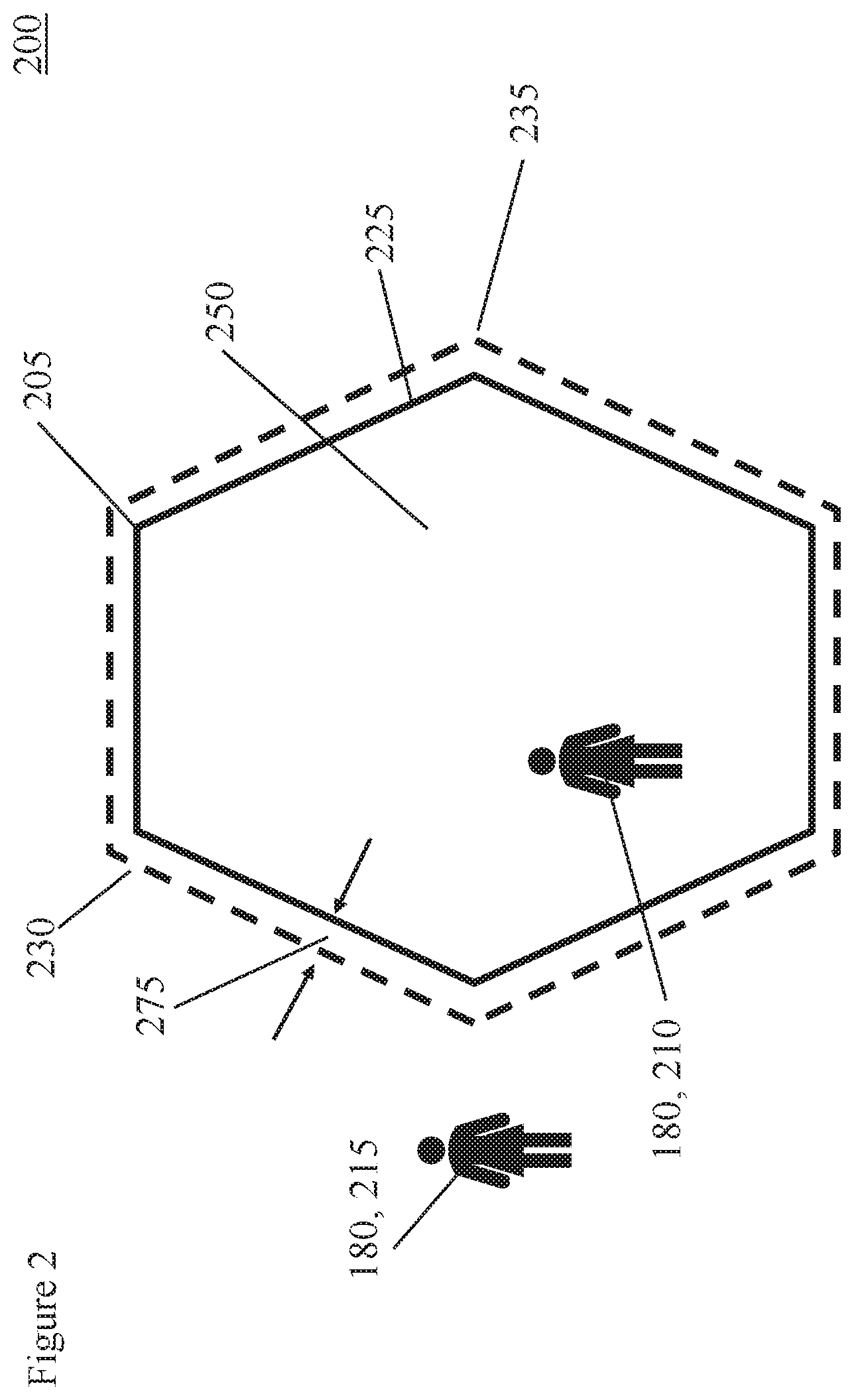
[0011] FIG. 2 is an illustration showing a secured area, a secured area perimeter, and a tolerance distance.
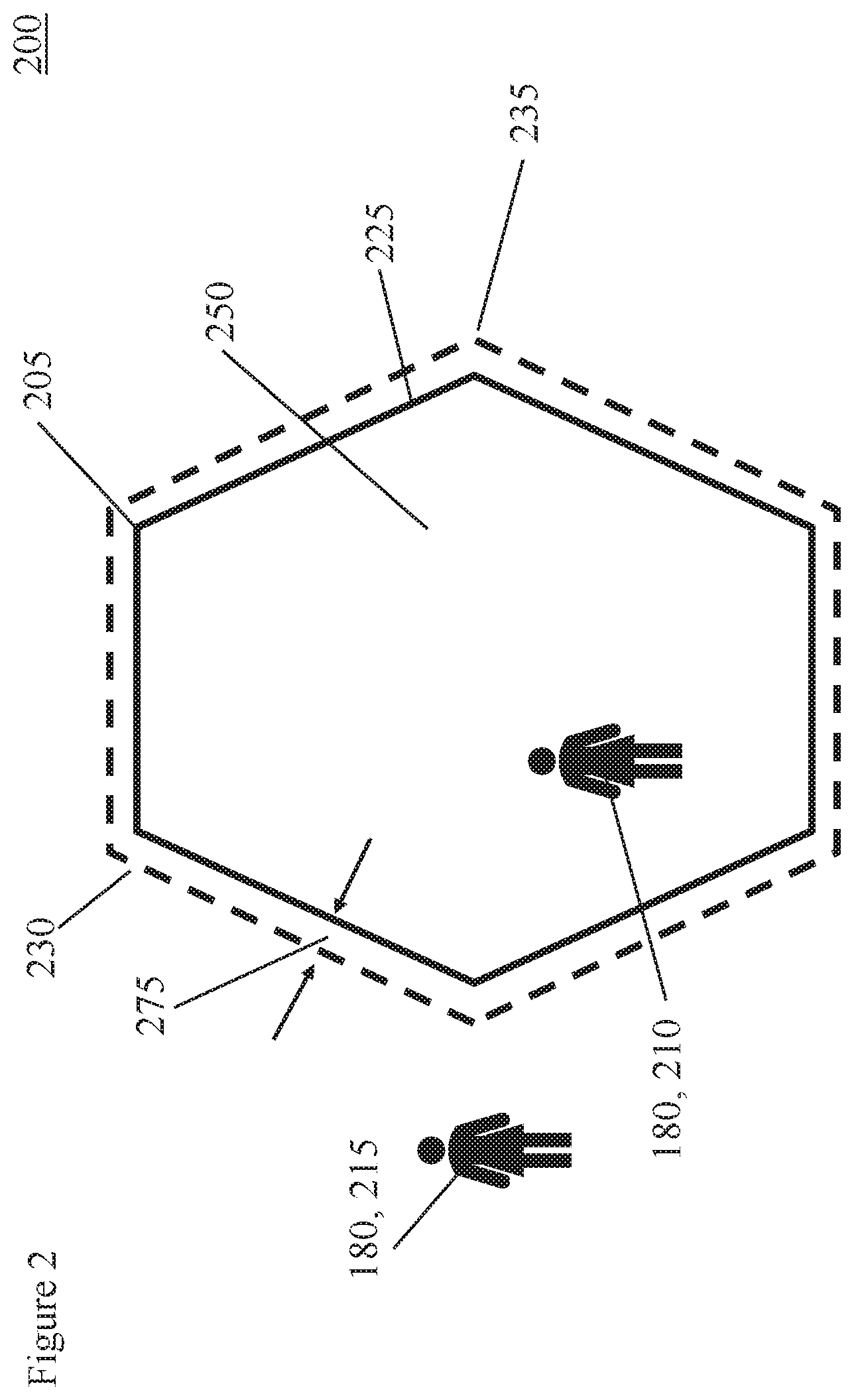
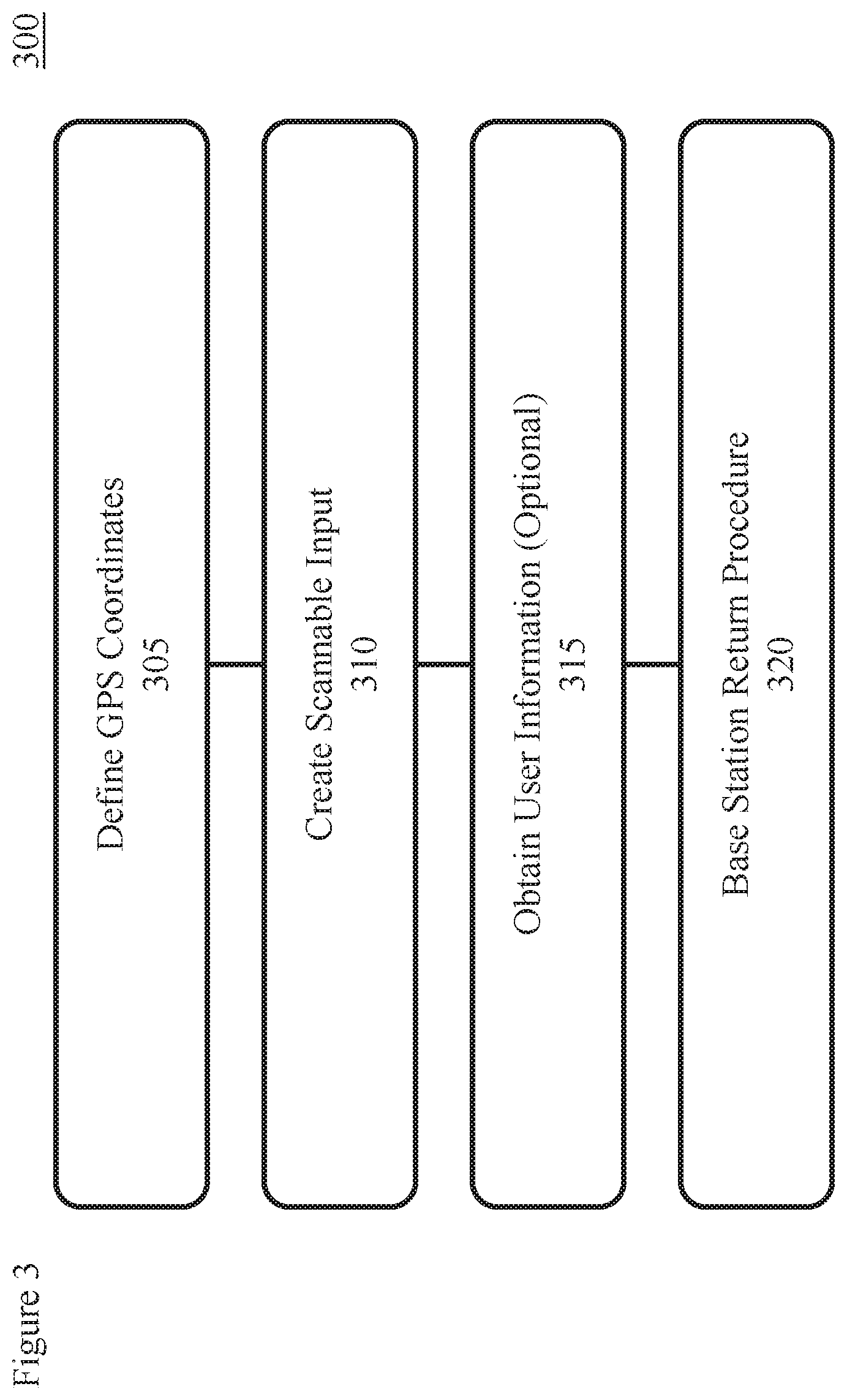
[0012] FIG. 3 is a flow chart showing the steps of a user registration/deregistration and operation process, typically performed by the base station and/or related system.
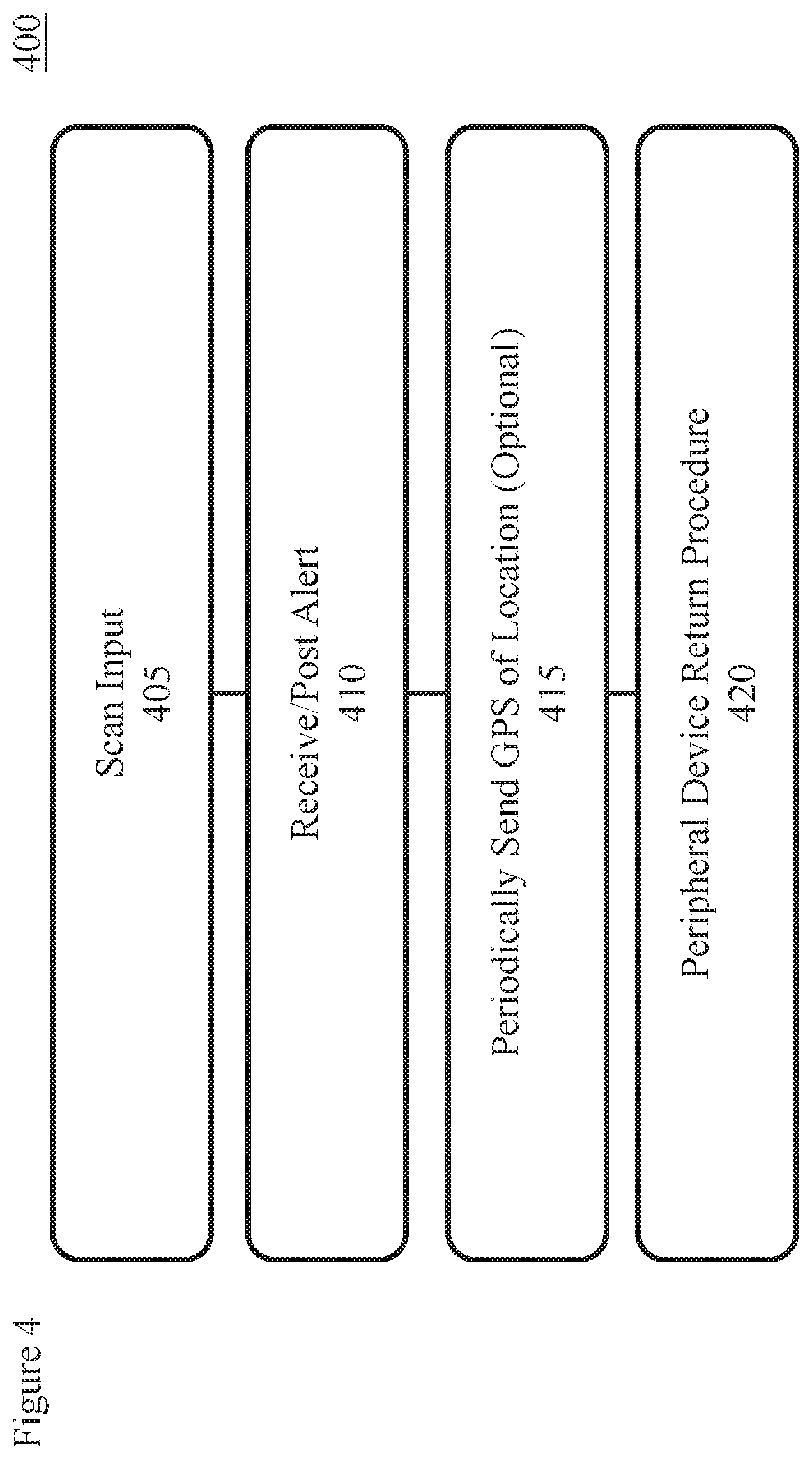
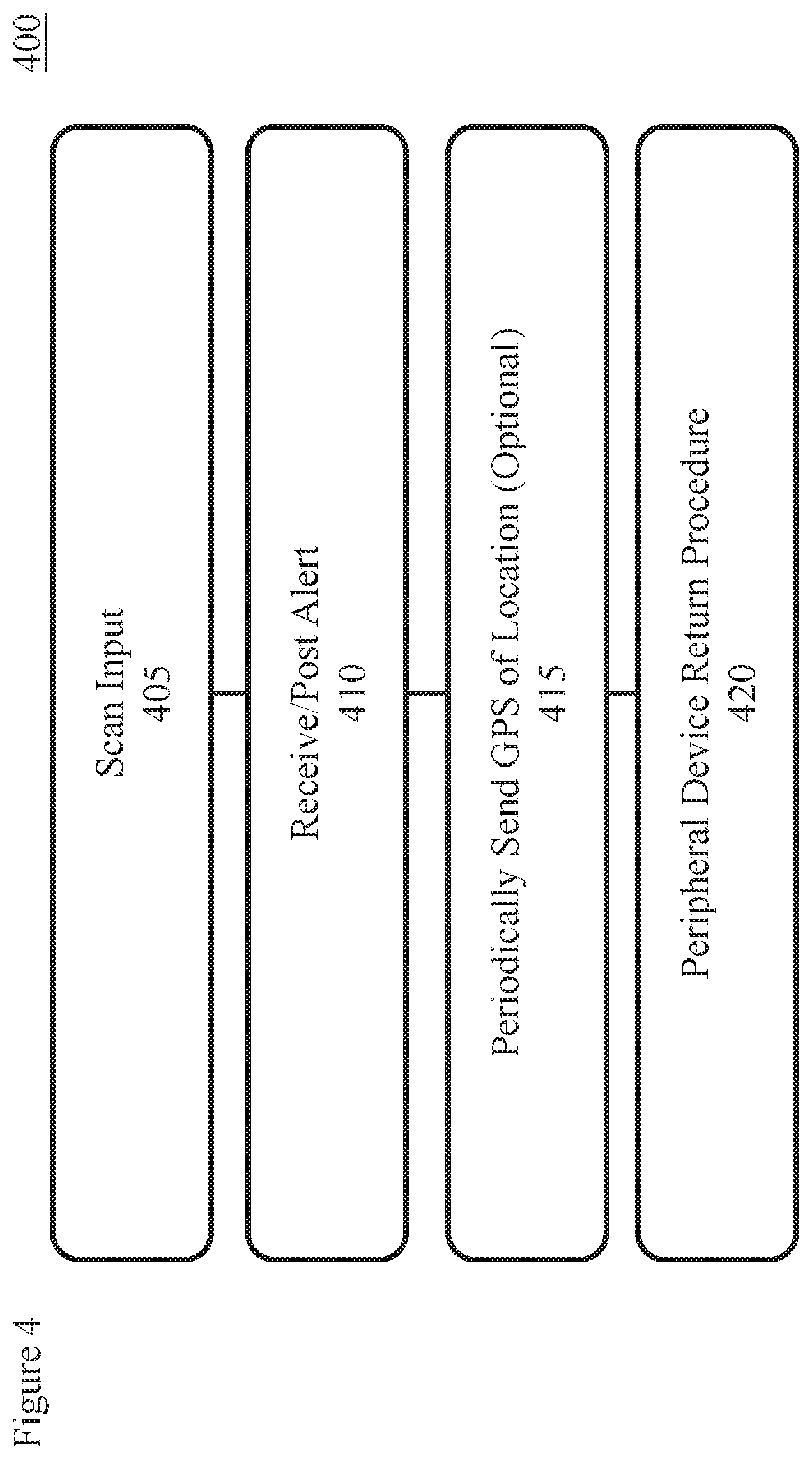
[0013] FIG. 4 is a flow chart showing the steps of a user registration/deregistration and operation process performed by the peripheral device.
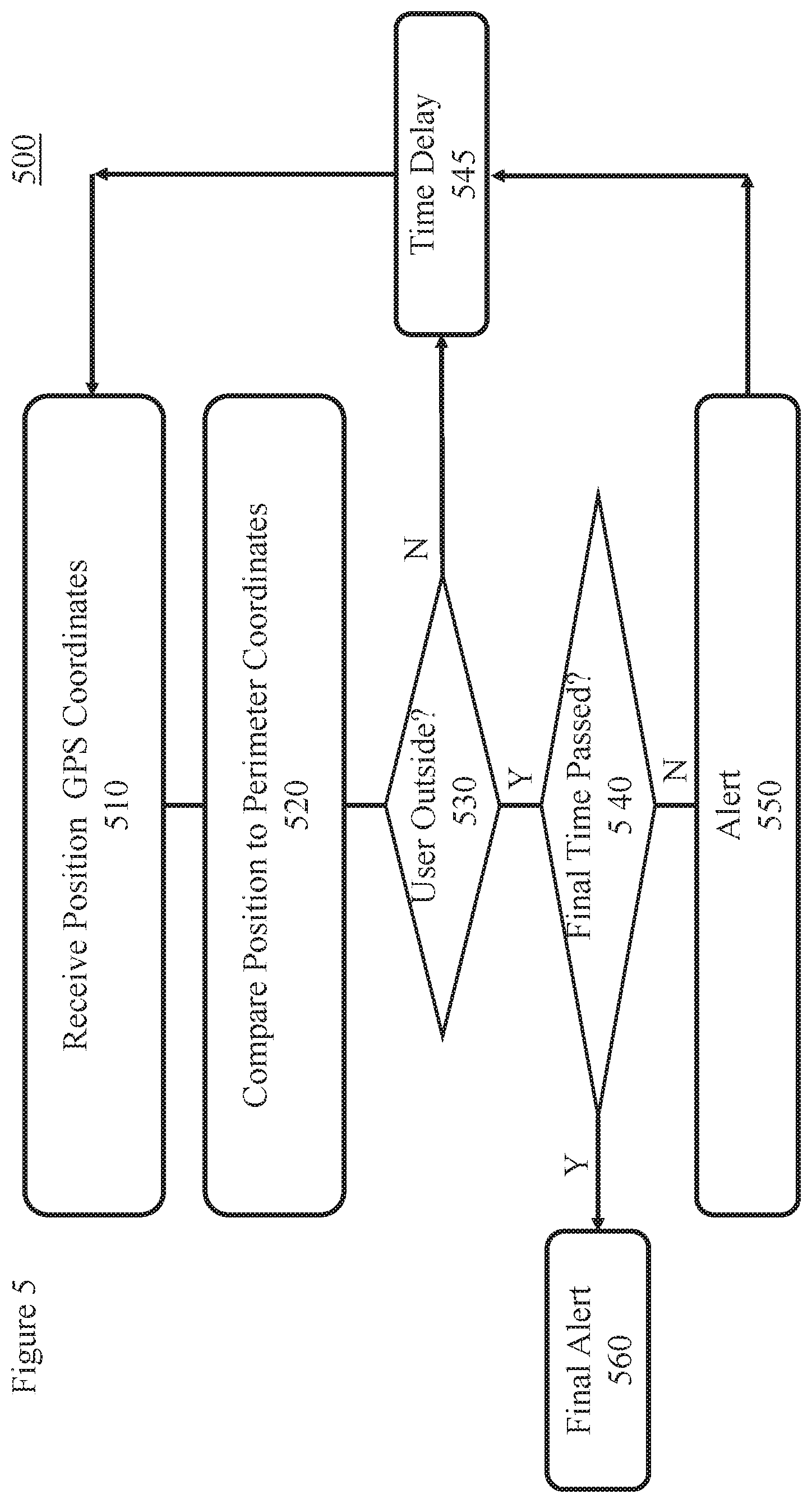
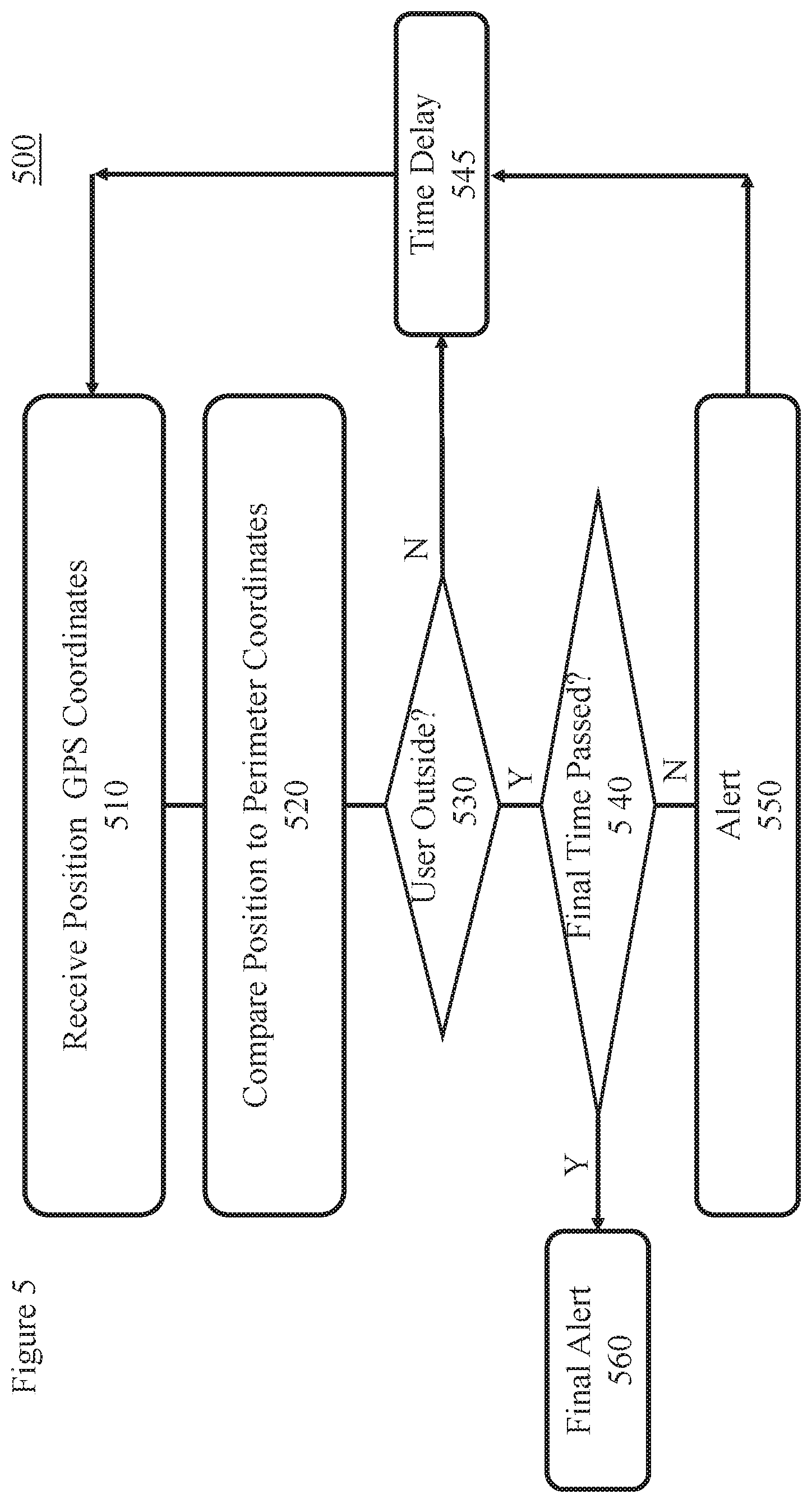
[0014] FIG. 5 is a flow chart showing the steps of one embodiment of an alert process performed by the peripheral device, e.g. a smartphone.
[0015] FIG. 6 is a flow chart showing the steps of one embodiment of an alert process performed by the base station.
DETAILED DESCRIPTION
[0016] It is to be understood that embodiments of the present invention are not limited to the illustrative methods, apparatus, structures, systems and devices disclosed herein but instead are more broadly applicable to other alternative and broader methods, apparatus, structures, systems and devices that become evident to those skilled in the art given this disclosure.
[0017] In addition, it is to be understood that the various features shown in the accompanying drawings are not drawn to scale, and that one or more features of a type commonly used may not be explicitly shown in any given drawing. This does not imply that the features not explicitly shown are omitted from the actual methods, apparatus, structures, systems, methods, and/or devices.
[0018] In addition, certain elements may be left out of a figure for the sake of clarity and/or simplicity when explanations are not necessarily focused on such omitted elements. Moreover, the same or similar reference numbers used throughout the drawings are used to denote the same or similar features, elements, method steps, or structures, and thus, a detailed explanation of the same or similar features, elements, method steps, or structures may not be repeated for each of the drawings.
[0019] The methods, features, apparatus, structures, systems, methods, and/or devices disclosed in accordance with embodiments of the present invention can be employed in applications, hardware, and/or electronic systems. Suitable hardware and systems for implementing embodiments of the invention may include, but are not limited to, personal computers, communication networks, electronic commerce systems, portable communications devices (e.g., feature phones or cell and smart phones), solid-state media storage devices, expert and artificial intelligence systems, functional circuitry, neural networks, etc. Systems and hardware incorporating the invention are contemplated embodiments of the invention.
[0020] It is understood that the meaning of terms might be affected by the orientation of the device described. For example, while the meaning of these descriptions might change if the device was rotated upside down, the descriptions remain valid because they describe relative relationships between features of the invention.
[0021] Many secured areas have temporary or permanent facility access devices like cards or badges 185 to enable access to the secured area 250. (These access devices 185 will be referred to as badges 185 without loss of generality). Some of these badges use radio frequency identification (RFID) chips embedded in the badge. Readers installed near a door or entry into the secured area read the RFID chips and in turn trigger an unlocking device to grant entry, e.g. open the door, for a time period to allowed access to the secured area. After the time period expires the entrance (e.g. door) is relocked.
[0022] One embodiment of the present invention is enabled by a one-time download of a smartphone application/process. The smartphone application/process can be used for all RFID enabled badges (or other access devices given to a user). No pairing of devices is required. In some embodiments, the smartphone application/process has a companion application or base station application that is enabled when dispensing of the badges at each secured area. See description below.
[0023] In some embodiments, the base station application/process identifies the Global Positioning System (GPS) coordinates defining a perimeter of the secured area (e.g. a polygon shaped perimeter) for which the badge given to a visitor/user allows access.
[0024] In some embodiments, when the visitor/user signs out a badge, the user's smartphone application/process reads/scans a code 170. Embodiments of the code include any code 170 physically or optically readable or readable from an electromagnetic signal like a quick response (QR) code, a bar code, or radio frequency signal. The code provides coordinates 175 to the smartphone application defining a secured area perimeter 225 within which the badge 185 provides access. For example, GPS coordinates of vertices of a polygon defining the secured area accessible by the badge are provided to the user's smartphone application/process. Other information 175 can be provide as described below.
[0025] In alternative embodiments, the user provides identifying information to the base station. In these embodiments, a tracking capability, e.g. embedded in the badge, provides a user position of the user/visitor to the base station system. The base station system executes a process that determines when the user position is outside of the secured area perimeter. When the user is outside the secured area perimeter and the badge has not been returned, the base station system sends an alert message to the user. The alert can be sent to the user's smartphone and/or to an alarm indication on the badge. The alert can be sent to the user alone and/or to the manager of the secured area. In alternative embodiments, the manager of the secured area is notified that the user is outside of the secured area perimeter without having returned the badge but the exact location of the user is not provided to the manager of the secured area. In some instantiations, if the user consents to having their exact location tracked, the manager of the secured area can optionally receive the user's location, e.g. the GPS coordinates of the user.
[0026] In alternative embodiments, the alert is sent out only if the distance outside the secured area perimeter exceeds a tolerance distance. The alert can take various forms that inform the user that the secured area was left without returning the badge. For example, the alert can be a text message, a smartphone vibration signal, a phone call, a notification, a display, and an e-mail.
[0027] Note that a given user/visitor may be stepping outside of the grounds with the intent to return, e.g., to go to lunch or a meeting outside the secured area. In such event the system warning can be ignored. Some embodiments provide an alert after the user is expected to leave the secured area, either temporarily or finally, if the badge is not returned. The time at which the visitor expects finally to leave the facility can be noted 175 upon signing the badge out. In these embodiments, the process executing on the base station system has logic to provide an alarm on each excursion of the user beyond the secured area perimeter and/or a final alarm when the user is beyond the secured area perimeter after the final departure time without the badge being returned. Logic for other conditions are described below.
[0028] Once the user turns in their badge, the GPS-outside-of-polygon tracker can be removed. This removal can happen in multiple ways. Scanning of the same QR code 170 that enabled the system a second time can disable the user monitoring by the base station system. In one embodiment, the smartphone application provides an indicator upon enabling the monitoring that the monitoring is enabled. Upon disabling the monitoring, the smartphone application/process can provide an indicator that the monitor is removed. Software embodiments of the system can be removed from the peripheral device as well.
[0029] Referring now to FIG. 1, an illustration is provided of one embodiment of the present invention 100 showing a base station 150. In some embodiments the base station 150 is connected (105, 106) to one or more networks, for example, a telecommunications network 110 and one or more computer networks 115, like the cloud.
[0030] The base station can include one or more general purpose computers. The base station 150 has one or more user interfaces 130, e.g. a graphical user interface (GUI) 130. Other user interfaces 130 include but are not limited to a keyboard, mouse, pointing device, voice recognition, etc. Radio frequency interfaces 130 also can be enabled to communicate 160 with peripheral devices 125 including like cell phones 125, smart phones 125, laptops 125, notebooks 125, etc.
[0031] Information 175 is exchanged 160 between the base station 150 and the peripheral devices 125 by one or more known methods. For example, information 175 can be provided to a peripheral device 125 like a smartphone 125 by the smart phone scanning a visual code 170 on a GUI. Alternatively, the information 175 can be presented in a visual code 170 like a visual image including text, bar codes, QR code, etc. In some embodiments the information 175 can be exchanged through radio frequency communication. In other embodiments, the peripheral device 125 can be connected 160 by hard wire to the base station 150.
[0032] In some embodiments, the base station 150 communicates a plurality of geographical points defining a secured area perimeter 225. (Reference FIG. 2 as well.) Typically, the geographical points are global positioning system (GPS) points, where each GPS point represents a point 205 on the secured area perimeter 225, e.g. a vertex of a geometric shape of a secured area 250 enclosed by the secured area perimeter 225. In some embodiments, a level of authorization 175 is also provided for each of two or more secured areas 250 defined by its own secured area perimeter 225. A time period of authorized access and other information 175 may also be provided to the peripheral device 125.
[0033] For example, a visitor/user 180 is visiting a building with multiple floors. The visitor/user 180 is permitted to visit the second floor of the building on Wednesday between the hours of 3 to 5 PM. The base station 150 can provide the user's 180 smartphone 125 four GPS points 205, each GPS point corresponding the position of one corner 205 of the rectangular 225 building. In addition, the base station 150 will provide the restrictive information 175 about access only permitted on the second floor between 3 to 5 PM on Wednesday.
[0034] Information 175 may be provided from the user 180 to the base station 150 as well. In some embodiments, the user 180 provides permissions for the system 100 to track/monitor the position of the user 180 if the user is outside of the secured area perimeter. In some embodiments, the user 180 might be required to grant this permission in order to gain access to the secured area 250. The user 180 might also provide information 175 like times the user 180 will not be in the secured area, e.g. lunch time, and/or the final time that user 180 expects to leave the secured area.
[0035] The peripheral device 125, e.g. a smartphone 125, has one or more memories, one or more central processing units (CPUs), one or more user interfaces. The user interfaces can receive and send information 175. For example, an image recognition system, like a camera, can receive information 175 encoded in a visual code 170. The peripheral device 125 also has an interface to receive positional data, e.g. GPS position of the user 180.
[0036] FIG. 2 is an illustration 200 showing a secured area 250, a secured area perimeter 225, and a tolerance distance 275 between the secured area perimeter 225 and a tolerance perimeter 230.
[0037] One user 180 is a user 210 within the tolerance perimeter 230. Another user 180 is a user 215 outside of the tolerance perimeter 230.
[0038] In some embodiments, the secured area perimeter 225 and the tolerance perimeter 230 are defined as polygonal shapes with three or more vertices (205, 235). Secured areas 250 that are not polygonal in shape can be defined approximately as a polygonal shape 225 in which the secured area 250 is inscribed. This this case the tolerance distance 275 will not be constant.
[0039] FIG. 3 is a flow chart showing the steps of a user registration/deregistration and operation process 300. Typically, most of this process 300 is performed by the base station 150.
[0040] In step 305, the GPS coordinates of the secured area perimeter 225 are defined. In some embodiments, the GPS coordinates 305 are the GPS position of each of the vertices (205, 235) of the polygonal shape defining the secured area perimeter (225, 230).
[0041] Additional information 175 can be defined in this step. For example, the tolerance perimeter 230 is also defined. The entity controlling access to the secured area 250 can determine a policy defining how far away a user 180 is permitted to be outside of the secured area perimeter 225. Values can be added to the GPS coordinates 305 of the secured area perimeter 225 to define the vertices 235 (tolerance perimeter vertices 235) of the tolerance perimeter 230. The tolerance distance 275 can be dependent on user 180 classification, date, time of day, weather conditions, or other conditions 175. For example, a tolerance distance 275 for a co-worker from a different location might be larger than a tolerance distance 275 given to an outside vendor.
[0042] Other information 175 can be defined in step 305. For example, one or more security levels or permission levels can be established for each of the secured areas 250. Times and other conditions of access can also be established for each of the secured areas 250. Classification of user 180 can be determined and if this classification affects the security or permission levels, tolerance perimeter 230, secured area perimeter 225, etc.
[0043] In step 310, the information 175 defined in step 305, e.g. the GPS coordinates etc., is coded into a scannable input 170 that can be read by one or more peripheral devices 125.
[0044] Step 315 is an optional step where the base station gathers information from the user 180. Information gathered in step 315 includes but is not limited to times the user 180 will be in the secured area(s) 250, final departing time, dates the user will be in the secured area(s) 250, classification information about the user 180, whether or not the user will permit being tracked outside of the secured area(s) 250, times the user 180 will leave one of the secure areas 250 with the intent to return, etc.
[0045] At this point in some embodiments, the user 180 is given 182 a badge 185. See FIG. 1. In some embodiments, the badge 185 has the capability of receiving GPS information about the position of the user 180, performing logical functions as described below, and, in some cases, communicating information with the base station 150.
[0046] In step 320, the process 300 verifies the user 180 has left all secured areas 250 and does not intend to return under this registration, e.g. a final access time has passed. In addition, the user 180 has turned in their badge 185. Upon completion of all these conditions, in some embodiments, step 320 de-registers the user 180 and optionally stores information about the user 180 access to the secured area(s) 250. In some embodiments, a signal is sent to the user's 180 peripheral device 125 to deactivate the any associated processes, e.g. process 500 below.
[0047] FIG. 4 is a flow chart showing the steps of a user registration/deregistration and operation process 400 performed by the peripheral device 125.
[0048] In step 405, the peripheral device 125, e.g. a smartphone 125, scans the code 170 that contains the information 175 the peripheral device 125 will need to perform the logic (e.g. described in FIG. 5) to determine whether the user 180 (device 125) is outside 215 of the secured area perimeter 225. In some embodiments, other information 175 is provided, as described above. For example, the code 170 can provide information 175 including but not limited to the tolerance perimeter 230, times and/or dates of access, levels of permission, classification of user 180 access for a given secured area 250, etc.
[0049] As described above, the peripheral device 125 access the information by a variety of ways including scanning a visual code 170, receiving a radio frequency or infrared signal, hard wire connection, etc.
[0050] In step 410, the peripheral device 125 receives and/or posts alerts 410 to the user 180. The peripheral device 125 can post alerts by performing logic as describe in one embodiment presented in process 500 below. Alternatively, the base station 150 or another computer system 100 can perform logic, as the example embodiment shown in process 600 below, and send the alert for the peripheral device to receive 410.
[0051] As an option, and sometimes if the user 180 grants permission, the peripheral device 125 sends GPS location information of the user 415 to the base station 150.
[0052] Step 420 is a procedure that deletes and/or disables information and processes on the peripheral device after the user 180 leaves the secured area(s) 250 and returns the badge 285.
[0053] FIG. 5 is a flow chart showing the steps of one embodiment of an alert process 500 performed by the peripheral device 125, e.g. a smartphone 125.
[0054] Step 510 begins with the peripheral device 125 receiving information like GPS coordinates defining the secured area(s) 250 and/or the tolerance perimeter 230 as described above, e.g. in step 305.
[0055] In step 520, the peripheral device determines the user location. In some embodiments, the user location is the GPS coordinates of the position/location at a given time as determined by the peripheral device 125.
[0056] The GPS coordinates of the user location are compared with the GPS coordinates in the secured area(s) 250, i.e. within the secured area perimeter 225 and/or the tolerance perimeter 230.
[0057] The determination of whether the user's GPS coordinates are within the polygon defined by the GPS coordinates of the vertices of the tolerance perimeter can be based on standard Point-in-Polygon algorithms [see K. Hormann and A. Agathos, "The point in polygon problem for arbitrary polygons", Computational Geometry 20: 131-144, 2001].
[0058] In step 530, based on the comparison in step 520, the process 500 determines whether the user 180 is inside the secured area 250 or outside the secured area 250 (or outside the tolerance perimeter 230).
[0059] If the user 180 is inside, the process 500 delays for a time delay 545 and steps 510, 520, and 530 are repeated. In some embodiments the time delay is between 1 and 60 seconds or any time thought to be short enough to account for changes in the user 180 location.
[0060] In alternative embodiments, steps 520 and 530 can perform other or additional comparisons. For example, these steps can determine whether certain conditions are met. Conditions include whether the user 180 has the appropriate security classification, and/or if the user is in the secured area 250 on the correct date and/or at the correct time. If these conditions are not met, the user 180 might be required to return the existing badge 185 and re-register for a new badge 185.
[0061] If the user 180 is outside the secured area 250, step 540 determines whether the final departure time for the user 180 has passed and/or another condition has not satisfied. If the final departure time has not passed (and/or all conditions are satisfied), an alert is posted 550 by the peripheral device 125 alerting 550 the user 180 that they are outside of the secure area 250 without returning their badge 185.
[0062] The process 500 then delays for a time delay 545 and repeats the process 500 from step 510. In this case, the time delay can is longer than the one used after step 530. For example, the time delay after step 550 might be from 30 to 90 minutes, e.g. to allow for a lunch break away from the secured area 250.
[0063] If the final departure time has passed 540 (and/or some condition is not satisfied), a final alert 560 can be sent. This final alert 560 indicates access to the secure area 250 is terminated, the badge 185 has not been returned, and the user 180 should return the badge 185 (and/or re-register is a condition is not satisfied).
[0064] In some embodiments, once the badge 185 is returned, process 500 is deleted or turned off 420.
[0065] FIG. 6 is a flow chart showing the steps of one embodiment of an alert process 600 performed by the base station 150.
[0066] In step 605, the process 600 issues the badge 185 to the user 180.
[0067] In step 610, the process 600 exchanges information 175 with the user 180 as defined above, e.g. in steps 310 and 315. Note that step 605 can be performed after step 610.
[0068] Step 615 determines if the badge 185 is returned. If the badge 185 is returned, the process ends. At this point the base station returns to procedure 320 and/or the peripheral device return procedure 420 can be performed.
[0069] If the badge 185 is not returned, step 620 determines if the user 180 is outside the secured area(s) 250. If the user 180 is not outside the secured area(s), the process delays for a time delay 645 and begins again at step 615. In some embodiments, this time delay is between 1 and 60 seconds or any time short enough to account for changes in the user 180 location.
[0070] If the user 180 is outside the secured area(s) 620, step 625 determines if the final departure time has passed for the user 180 (and/or if another condition is not met).
[0071] If the final departure time has not passed (and all conditions are met) 625, an alert 640 is sent to the peripheral device 125 informing the user 180 that they are out of the secured area(s) 250 and have not turned in the badge 185. The alert 640 can be a text message, a recorded phone call, an alarm, etc.
[0072] The process then delays for a time delay 645 and returns to step 615. In this case the time delay 645 might be between 30 to 90 minutes, e.g. to allow for a lunch break away from the secured area 250.
[0073] If the final departure time has passed (or another condition is not met) 625, a final alert 630 is sent. This final alert 640 informs the user that access to the secure area 250 is terminated and the badge 185 has not been returned. (If a condition is not met, the user 180 may have to return the badge 185 and re-register.)
[0074] In some embodiments, once the badge 185 is returned, process 600 is deleted or turned off 420 for the user 180 in question.
[0075] The descriptions of the various embodiments of the present invention have been presented for purposes of illustration but are not intended to be exhaustive or limited to the embodiments disclosed. Many modifications and variations will be apparent to those of ordinary skill in the art without departing from the scope and spirit of the described embodiments. The terminology used herein was chosen to best explain the principles of the embodiments, the practical application or technical improvement over technologies found in the marketplace, or to enable others of ordinary skill in the art to understand the embodiments disclosed herein.
[0076] The terminology used herein was chosen to explain the principles of the embodiments and the practical application or technical improvement over technologies found in the marketplace or to otherwise enable others of ordinary skill in the art to understand the embodiments disclosed herein. Devices, components, elements, features, apparatus, systems, structures, techniques, and methods described with different terminology that perform substantially the same function, work in the substantial the same way, have substantially the same use, and/or perform the similar steps are contemplated as embodiments of this invention.
* * * * *
D00000
D00001
D00002
D00003
D00004
D00005
D00006

XML
uspto.report is an independent third-party trademark research tool that is not affiliated, endorsed, or sponsored by the United States Patent and Trademark Office (USPTO) or any other governmental organization. The information provided by uspto.report is based on publicly available data at the time of writing and is intended for informational purposes only.
While we strive to provide accurate and up-to-date information, we do not guarantee the accuracy, completeness, reliability, or suitability of the information displayed on this site. The use of this site is at your own risk. Any reliance you place on such information is therefore strictly at your own risk.
All official trademark data, including owner information, should be verified by visiting the official USPTO website at www.uspto.gov. This site is not intended to replace professional legal advice and should not be used as a substitute for consulting with a legal professional who is knowledgeable about trademark law.