Configuring Logging In Non-emulated Environment Using Commands And Configuration In Emulated Environment
Heit; James R. ; et al.
U.S. patent application number 17/100050 was filed with the patent office on 2021-03-11 for configuring logging in non-emulated environment using commands and configuration in emulated environment. The applicant listed for this patent is Unisys Corporation. Invention is credited to Robert L. Bergerson, James R. Heit, John A. Peters, Jason C. Schultz.
| Application Number | 20210073104 17/100050 |
| Document ID | / |
| Family ID | 1000005234842 |
| Filed Date | 2021-03-11 |








| United States Patent Application | 20210073104 |
| Kind Code | A1 |
| Heit; James R. ; et al. | March 11, 2021 |
CONFIGURING LOGGING IN NON-EMULATED ENVIRONMENT USING COMMANDS AND CONFIGURATION IN EMULATED ENVIRONMENT
Abstract
Methods and systems for logging data in a computing system are disclosed. The methods and systems include receiving a first request to create log data of an activity of the computing system. The methods and systems further include acquiring information about the activity of the computing system. The methods and systems further include creating the log data of the activity of the computing system. The methods and systems further include retrieving stored log data.
| Inventors: | Heit; James R.; (Eagan, MN) ; Bergerson; Robert L.; (Eagan, MN) ; Schultz; Jason C.; (Eagan, MN) ; Peters; John A.; (Eagan, MN) | ||||||||||
| Applicant: |
|
||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|
| Family ID: | 1000005234842 | ||||||||||
| Appl. No.: | 17/100050 | ||||||||||
| Filed: | November 20, 2020 |
Related U.S. Patent Documents
| Application Number | Filing Date | Patent Number | ||
|---|---|---|---|---|
| 14874642 | Oct 5, 2015 | 10846195 | ||
| 17100050 | ||||
| Current U.S. Class: | 1/1 |
| Current CPC Class: | G06F 11/3476 20130101 |
| International Class: | G06F 11/34 20060101 G06F011/34 |
Claims
1. A method for logging data in a computing system, comprising: receiving, at a processor executing an operating system, a first request from an emulated environment to create log data of an activity of the computing system; acquiring, at the processor executing the operating system, information about the activity of the computing system; and creating, with the processor executing the operating system, the log data of the activity of the computing system.
2. The method of claim 1, further comprising: setting, with the processor executing the operating system, a log level of the log data of the activity of the computing system.
3. The method of claim I, further comprising: receiving, at the processor executing the operating system, a second request from the emulated environment to set a log level of the log data of the activity of the computing system; and setting, with the processor executing the operating system, the log level of the log data of the activity of the computing system.
4. The method of claim 3, wherein the first request and the second request are received at the processor executing the operating system simultaneously.
5. The method of claim 1, wherein the activity of the computing system is an activity of a networking component of the computing system.
6. The method of claim 1, further comprising: receiving, at the processor executing the operating system, a third request from the emulated environment to retrieve stored log data; and transmitting, from the operating system, the stored log data.
7. The method of claim 6, wherein the first request, the second request, and the third request are received at the processor executing the operating system simultaneously.
8. A computer program product, comprising: a non-transitory computer-readable medium comprising instructions which, when executed by a processor of a computing system, cause the processor to perform the steps of: receiving a first request from an emulated environment to create log data of an activity of the computing system; acquiring information about the activity of the computing system; and creating the log data of the activity of the computing system.
9. The computer program product of claim 8, wherein the medium further comprises instructions to cause the processor to perform the steps of: setting a log level of the log data of the activity of the computing system.
10. The computer program product of claim 8, wherein the medium further comprises instructions to cause the processor to perform the steps of: receiving a second request from the emulated environment to set a log level of the log data of the activity of the computing system; and setting the log level of the log data of the activity of the computing system.
11. The computer program product of claim 10, wherein the first request and the second request are received simultaneously.
12. The computer program product of claim 8, wherein the activity of the computing system is an activity of a networking component of the computing system.
13. The computer program product of claim 8, wherein the medium further comprises instructions to cause the processor to perform the steps of: receiving a third request from the emulated environment to retrieve stored log data; and transmitting the stored log data.
14. The computer program product of claim 13, wherein the first request, the second request, and the third request are received simultaneously.
15. An apparatus, comprising: a memory; and a processor coupled to the memory, the processor being configured to execute the steps of: receiving a first request from an emulated environment to create log data of an activity of the computing system; acquiring information about the activity of the computing system; and creating the log data of the activity of the computing system.
16. The apparatus of claim 15, wherein the processor is further configured to perform the steps of: setting a log level of the log data of the activity of the computing system.
17. The apparatus of claim 15, wherein the processor is further configured to perform the steps of: receiving a second request from the emulated environment to set a log level of the log data of the activity of the computing system; and setting the log level of the log data of the activity of the computing system.
18. The apparatus of claim 17, wherein the first request and the second request are received simultaneously.
19. The apparatus of claim 15, wherein the activity of the computing system is an activity of a networking component of the computing system.
20. The apparatus of claim 15, wherein the processor is further configured to perform the steps of: receiving a third request from the emulated environment to retrieve stored log data; and transmitting the stored log data.
Description
CROSS-REFERENCE TO RELATED APPLICATIONS
[0001] This application is a continuation of U.S. patent application Ser. No. 14/874, 642, filed Oct. 5, 2015, now U.S. Pat. No. 10,846,195 issued on Nov. 24, 2020, which is hereby incorporated herein by reference.
FIELD OF THE DISCLOSURE
[0002] The instant disclosure relates generally to computer loggings. More specifically, this disclosure relates to embodiments enabling a non-emulated environment, e.g., operating system or the like, to share log data with an emulated environment, e.g., emulated operating system, emulated computer program, emulated virtual machine, or the like.
BACKGROUND
[0003] An emulated environment is separate from a non-emulated environment. Therefore, log data of the emulated environment and log data of the non-emulated environment are also separate. This separation of log data makes debugging of applications, e.g., networking applications, difficult.
SUMMARY
[0004] The log data of a non-emulated environment, e.g., a System Architecture Interface Layer (SAIL) based operating system, may be shared with an emulated environment, e.g., OS 2200 and/or CPCommOS, by using commands and configurations of the emulated environment. According to one embodiment, a method for logging data in a computing system may include receiving, at a processor executing an operating system, a first request from an emulated environment to create log data of an activity of the computing system. The method may further include acquiring, at the processor executing the operating system, information about the activity of the computing system. The method may further include creating, with the processor executing the operating system, the log data of the activity of the computing system.
[0005] According to anther embodiment, computer program product may include a non-transitory computer-readable medium comprising instructions which, when executed by a processor of a computing system, cause the processor to perform the steps of receiving a first request from an emulated environment to create log data of an activity of the computing system. The medium may also include instructions which cause the processor to perform the step of acquiring information about the activity of the computing system. The medium may also include instructions which cause the processor to perform the step of creating the log data of the activity of the computing system.
[0006] According to yet another embodiment, an apparatus may include a memory and a processor coupled to the memory. The processor may be configured to execute the steps of receiving a first request from an emulated environment to create log data of an activity of the computing system. The processor may also be configured to execute the step of acquiring information about the activity of the computing system. The processor may further be configured to execute the step of creating the log data of the activity of the computing system.
[0007] It is expressly noted that the term "emulated environment" used herein in the disclosure includes any software, hardware environment, virtual machine, or the like, that is emulated, including, but not limited to, an emulated operating system, e.g., Linux, Windows, Java, Unix, OS 2200, or the like, and any computer program running within the emulated operating system, e.g., CPCommOS. For example, the request of "a request from an emulated environment" may be made by a processor executing an emulated operating system, e.g. OS 2200, and/or any computer program running within an emulated operating system, e.g., CPCommOS.
[0008] The foregoing has outlined rather broadly the features and technical advantages of the present invention in order that the detailed description of the invention that follows may be better understood. Additional features and advantages of the invention will be described hereinafter that form the subject of the claims of the invention. It should be appreciated by those skilled in the art that the concepts and specific embodiments disclosed may be readily utilized as a basis for modifying or designing other structures for carrying out the same purposes of the present invention. It should also be realized by those skilled in the art that such equivalent constructions do not depart from the spirit and scope of the invention as set forth in the appended claims. The novel features that are believed to be characteristic of the invention, both as to its organization and method of operation, together with further objects and advantages will be better understood from the following description when considered in connection with the accompanying figures. It is to be expressly understood, however, that each of the figures is provided for the purpose of illustration and description only and is not intended as a definition of the limits of the present invention.
BRIEF DESCRIPTION OF THE DRAWINGS
[0009] For a more complete understanding of the disclosed systems and methods, reference is now made to the following descriptions taken in conjunction with the accompanying drawings.
[0010] FIG. 1 is a schematic block diagram illustrating a computing system including an operating system and an emulated environment according to one embodiment of the disclosure.
[0011] FIG. 2 is a flow chart illustrating a method for logging data in a computing system according to one embodiment of the disclosure.
[0012] FIG. 3 is a flow chart illustrating a method for logging data and setting log levels in a computing system according to one embodiment of the disclosure.
[0013] FIG. 4 is a flow chart illustrating a method for logging data and setting log levels in a computer system according to one embodiment of the disclosure.
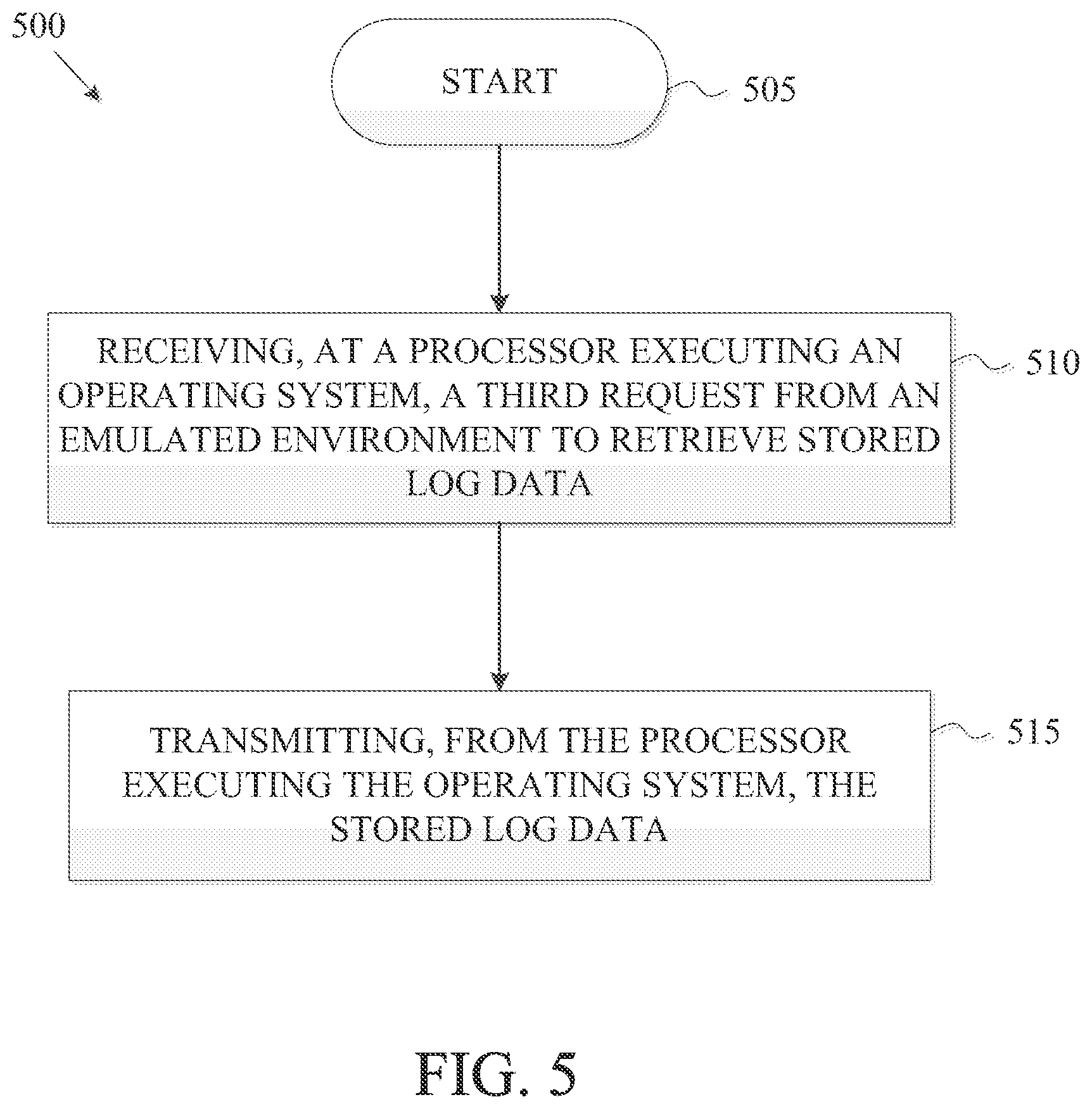
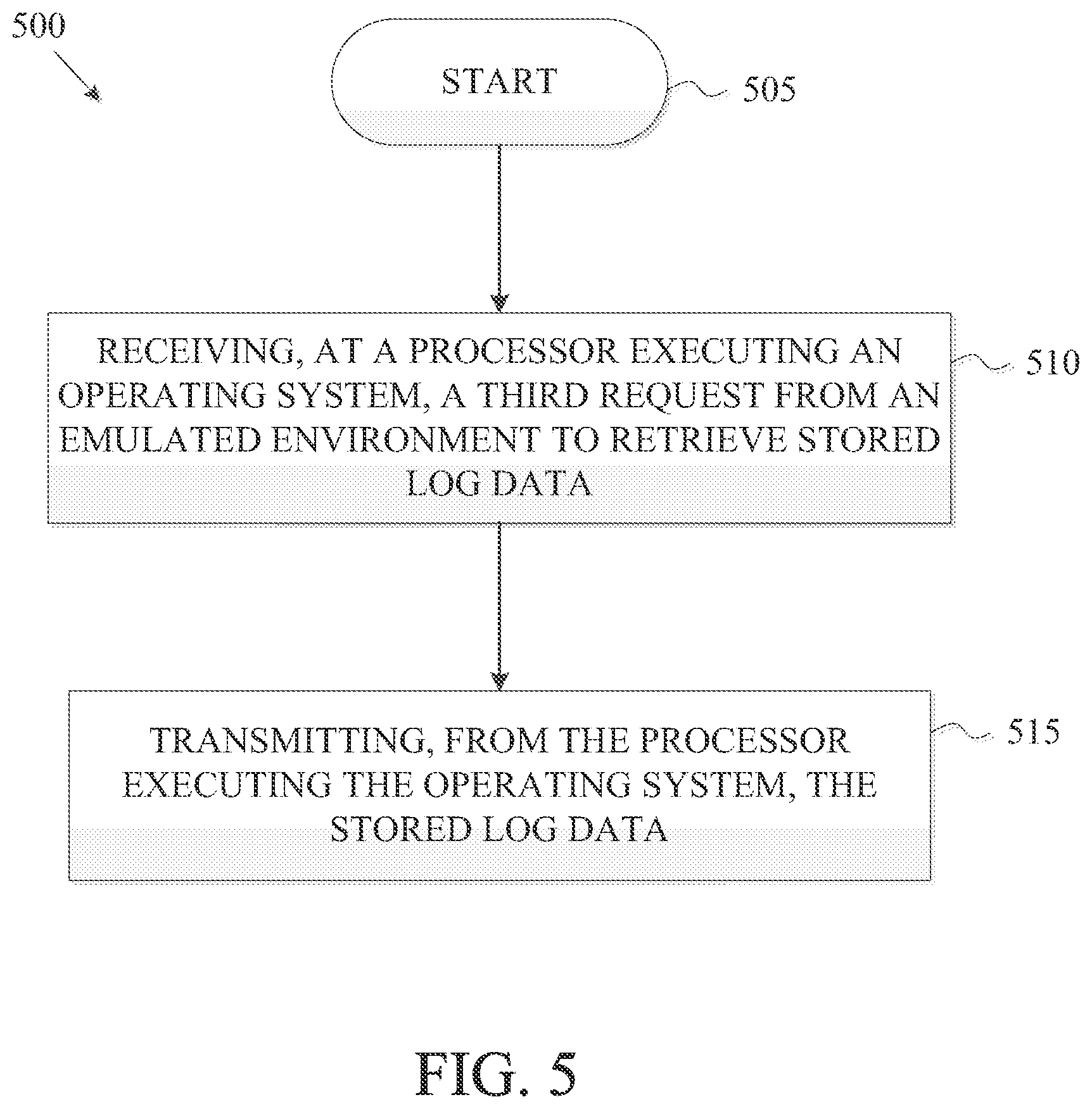
[0014] FIG. 5 is a flow chart illustrating a method for retrieving stored log data according to one embodiment of the disclosure.
[0015] FIG. 6 is a block diagram illustrating a computer network according to one embodiment of the disclosure.
[0016] FIG. 7 is a block diagram illustrating a computer system according to one embodiment of the disclosure.
[0017] FIG. 8A is a block diagram illustrating a server hosting an emulated software environment for virtualization according to one embodiment of the disclosure.
[0018] FIG, 8B is a block diagram illustrating a server hosting an emulated hardware environment according to one embodiment of the disclosure.
DETAILED DESCRIPTION
[0019] FIG. 1 is a schematic block diagram illustrating a computing system 100 including an operating system 120 and an emulated environment 105 according to one embodiment of the disclosure. In the computing system 100, the operating system 120 is a non-emulated environment. The emulated environment 105 may include instruction sets that are emulated or translated, via software, executing on an underlying instruction set of the operating system 120, such as from a commodity instruction processor, such as the x86 processor, and Linux. Examples of computing devices useable to execute computing instructions constituting the computing system 100 are discussed below in connection with FIGS. 6-8. The computing system 100 shown in FIG. 1 may be used to perform the embodiments of systems and methods disclosed herein, such as the methods shown in FIGS. 2-5.
[0020] In the embodiment shown in FIG. 1, the computing system 100 includes an operating system 120 and an emulated environment 105. In one embodiment, the computing system 100 may be a server that includes networking components and other hardware components. The emulated environment 105 may be an emulated operating system, e.g., Linux, Windows, Java, Unix, OS 2200, or the like. In one embodiment, the emulated environment 105 may execute instruction sets on a server, controlled by an operating system 120, e.g. System Architecture Interface Layer (SAIL), Unix, Linux, or the like. The operating system 120 may include drivers for accessing networking components and other hardware components of the computing system 100.
[0021] As shown in FIG. 1, the emulated environment 105 includes a computer program 110. In one embodiment, the computer program 110 can be a communication platform, such as CPCommOS, that is able to connect application programs on one or more network connected servers that have terminals, workstations, and other applications in a data communication network. As shown in FIG. 1, a communication 115 is established between the computer program 110 and a non-emulated networking interface 125. The computer program 110 may access a networking function of the operating system 120 through the non-emulated networking interface 125, such as Extended Network Input Output Processor (XNIOP). The non-emulated networking interface 125 may translate requests from the computer program 110 for accessing the networking functions of the operating system 120.
[0022] In some embodiments, the operating system 120, e.g., SAIL, Unix Linux, or the like, may be responsible for loading and initializing the emulated environment 105 and/or the computer program 110. According to another embodiment, operating system 120 may also be responsible for initializing the non-emulated interface 125 to establish networking functions during a regular operation or a computer system startup.
[0023] In some embodiments, the operating system 120 may include instruction sets and drivers for the non-emulated networking interface 125 (e.g., XNIOP) that includes various networking components, e.g., transmission control protocol/internet protocol (TCP/IP), transport layer security (TLS), secure sockets layer (SSL), user datagram protocol (UDP), routing information, etc. Logging capability may exist in each and every component of the non-emulated networking interface 125.
[0024] In other embodiments, the computer program 110, e.g., CPCommOS, in the emulated environment 105 may initiate a request to the non-emulated networking interface 125, e.g., XNIOP, at the processor executing the operating system 120 to create log data. In one embodiment, the request may be made by a user through a console command. The log data may log various information, e.g., number of fields, type of logged activity, sub-type of logged activity, data input size, upload request, upload byte count, log showing request, number of log showing fields, etc. In one embodiment, the log data may be defined using the following instructions:
TABLE-US-00001 Struct cadbug_cmd_struct { Struct translator_header trans_hdr; WORD2200 number_of_fields; WORD2200 type; WORD2200 sub_type; WORD2200 max_input_size; WORD2200 upload_command; WORD2200 upload_byte_count; WORD2200 log_show_command; WORD2200 nbr_log_show_fields; #ifndef XNIOP char param1 [MAX_CADBUG_FIELD_SIZE]; char param2[MAX_CADBUG_FIELD_SIZE]; char command_result[MAX_CADBUG_RESULT_SIZE]; #else WORD2200 param1[MAX_CADBUG_FIELD_SIZE / 4]; WORD2200 param2[MAX_CADBUG_FIELD_SIZE / 4]; WORD2200 command_result[MAX_CADBUG_RESULT_SIZE / 4]; #endif WORD2200 console_routing_id; }
[0025] The log data may log any type of activity performed by the non-emulated networking interface (XNIOP) 125. In one embodiment, the log data may log networking activities. The networking activities to be logged may include activities done through, without limitation e.g., transmission control protocol/internet protocol (TCP/IP), transport layer security (TLS), secure sockets layer (SSL), user datagram protocol (UDP), routing, or the like. In other embodiments, the log data may log non-networking activities.
[0026] In some other embodiments, the computer program 110, e.g., CPCommOS, in the emulated environment 105 may initiate a request to the non-emulated networking interface 125, e.g., XNIOP, at the processor executing the operating system 120 to set a log level for log data. The log level may be defined in different degrees, without limitation for example, LOW, MEDIUM, HIGH, etc. In some embodiments, log levels may be set for log data that are already stored in computer-readable mediums. In some other embodiments, log levels may be set for log data that will be created for future activities.
[0027] In one embodiment, the request for setting a log level can be made by the computer program 110 simultaneously at the same time when making a request for creating log data. In another embodiment, the request for setting a log level can be made by the computer program 110 before or after making a request for creating log data.
[0028] In one embodiment, the computer program 110 may set the log level of all log data without specifying any component and/or activity. In one embodiment, the computer program 110 may set log level without specifying any component and/or activity by using the following instruction: [0029] CPCOMM CADBUG COMMAND LOG <LOGLEVEL> [0030] In another embodiment, the computer program 110 may set log level for a specific activity and/or component. In one embodiment, the computer program 110 may set log levels for a specific activity and/or component using the following instruction: [0031] CPCOMM CADBUG COMMAND LOG <COMPONENT> <LOGLEVEL> [0032] Log levels may be set for any XNIOP component and/or activity, e.g., TPC/IP, TIL, SSL, UDP, routing, or the like.
[0033] Requests for creating log data and setting log levels may be made through console commands entered by the user. In some other embodiments, the requests for creating log data and setting log levels may be made without a console command entered by the user. In one embodiment, the requests may be made automatically by the configuration file of the computer program 110, e.g,, configuration file of CPCommOS. A configuration file of the computer program 110 may be immediately processed during an initiation process of the computer program 110. In such a manner, the requests for creating log data and setting up log levels may be made automatically during an initiation process without a console command entered by the user. Making the requests for creating log data and setting log levels through a configuration file of the computer program 110 may provide the ability to create log data when console commands are not available and avoid repetitive entries of console commands.
[0034] In one embodiment, the configuration file of CPCommOS may set the log level as "HIGH" for all XNIOP component using the following exemplary instruction: XTRACE , HIGH. In another embodiment, the configuration file of CPCommOS may set the log level for specific components of XNIOP, for example, setting TCP as "HIGH" and "SSL" as "LOW," using the following exemplary instructions: XTRACE, TOP, HIGH XTRACE, SSL, LOW.
[0035] In some embodiments, the computer program 110 may make a request to the non-emulated networking interface (XNIOP) 125 to retrieve stored log data. For example, in one embodiment, CPCommOS may make a request to the non-emulated networking interface (XNIOP) 125 to retrieve stored log data. Upon receiving the request, the operating system 120 may send the stored log data back to CPCommOS.
[0036] The retrieved information of stored log data may include the same information as the log data that was created. In some embodiments, the retrieved log data may include number of fields, type of logged activity, sub-type of logged activity, data input size, upload request, upload byte count, log showing request, number of log showing fields, etc. In one embodiment, the stored log data can be retrieved using the following instructions: CPCOMM CADBUG COMMAND LOG UPLOAD. In one embodiment, when the computer program 110 receives the stored log data, the computer program 100 may store the log data in a log file, e.g., a CPCommOS log file.
[0037] FIG. 2 is a flow chart illustrating a method 200 for logging data in a computing system according to one embodiment of the disclosure. The method 200 shown in FIG. 2 may be part of or combined with other methods disclosed herein, such as the methods shown in FIGS. 3-5. The method 200 shown in FIG. 2 may be implemented in the systems and apparatuses disclosed herein, such as the systems and apparatuses shown in FIGS. 1 and 6-8.
[0038] As shown in FIG. 2, the method 200 starts at block 205. The method 200 proceeds to block 210. At block 210, method 200 includes receiving, at a processor executing an operating system, a request from an emulated environment to create log data of an activity of the computing system. The method 200 proceeds to block 215 which includes acquiring, at the processor executing the operating system, information about the activity of the computing system. The method proceeds to block 220 which includes creating, with the processor executing the operating system, the log data of the activity of the computing system.
[0039] In one embodiment of the method 200, the operating system of blocks 210, 215, and 220 may be the operating system 120 shown in FIG, 1. In another embodiment, the operating system of blocks 210, 215, and 220 may be System Architecture Interface Layer (SAIL), Unix, Linux, or the like. In another embodiment, the operating system of blocks 210, 215, and 220 may include a non-emulated networking interface, such as the non-emulated networking interface 125 shown in FIG. 1. In another embodiment, the operating system of blocks 210, 215, and 220 may include XNIOP.
[0040] In one embodiment of the method 200, the emulated environment of block 210 may be the emulated environment 105 shown in FIG. 1. In another embodiment, the emulated environment of block 210 may be Linux, Windows, Java, Unix, OS 2200, or the like. In another embodiment, the emulated environment of block 210 may include the computer program 110 shown in FIG. 1. In another embodiment, the emulated environment of block 210 may include CPCommOS or the like communication platforms.
[0041] In one embodiment of the method 200, the log data of blocks 210 and 220 may include any information existing in any data structure. In another embodiment of the method 200, the log data of blocks 210 and 220 may include information, such as, for example, number of fields, type of logged activity, sub-type of logged activity, data input size, upload request, upload byte count, log showing request, number of log showing fields, etc.
[0042] In one embodiment of method 200, the activity of the computing system of blocks 210, 215, and 220 may be networking activities done through a transmission control protocol/internet protocol (TCP/IP), transport layer security (TLS), secure sockets layer (SSL), user datagram protocol (UDP), routing, or the like. In one embodiment of method 200, the activity of the computing system of blocks 210, 215, and 220 may be non-networking activities.
[0043] FIG. 3 is a flow chart illustrating a method 300 for logging data and setting log levels in a computing system according to one embodiment of the disclosure. The method 300 shown in FIG. 3 may be part of or combined with other methods disclosed herein, such as, for example, the methods shown in FIGS. 2 and 4-5. The method 300 shown in FIG. 3 may be implemented in the systems and apparatuses disclosed herein, such as the systems and apparatuses shown in FIGS. 1 and 6-8.
[0044] As shown in FIG. 3, the method 300 starts at block 305. The method 300 proceeds to block 310 which includes receiving, at a processor executing an operating system, a first request from an emulated environment to create log data of an activity of a computing system. The method 300 proceeds to block 315 which includes acquiring, at the processor executing the operating system, information about the activity of the computing system. The method 300 proceeds to block 320 which includes creating, with the processor executing the operating system, the log data of the activity of the computing system. The method 300 proceeds to block 325 which includes receiving, at the processor executing the operating system, a second request from the emulated environment to set a log level of the log data of the activity of the computing system. The method 300 proceeds to block 330 which includes setting, with the processor executing the operating system, the log level of the log data of the activity of the computing system.
[0045] In one embodiment of the method 300, the operating system of blocks 310, 315, 320, 325, and 330 may be a computing system configured with the operating system 120 shown in FIG. 1. In another embodiment, the operating system of blocks 310, 315. 320, 325, and 330 may be a computing system configured with System Architecture Interface Layer (SAIL), Unix, Linux, or the like. In another embodiment, the operating system of blocks 310, 315, 320, 325, and 330 may include a non-emulated networking interface, such as the non-emulated networking interface 125 shown in FIG. 1. In another embodiment, the operating system of blocks 310, 315, 320, 325, and 330 may include XNIOP.
[0046] In one embodiment of the method 300, the emulated environment of blocks 310 and 325 may be the emulated environment 105 shown in FIG. 1. In another embodiment, the emulated environment of blocks 310 and 325 may be Linux, Windows, Java, Unix, OS 2200, or the like. In another embodiment, the emulated environment of blocks 310 and 325 may include the computer program 110 shown in FIG. 1. In another embodiment, the emulated environment of blocks 310 and 325 may include CPCommOS or the like communication platforms.
[0047] In one embodiment of the method 300, the log data of blocks 310, 320, 325, and 330 may include any information existing in any data structure. In another embodiment of the method 300, the log data of blocks 310, 320, 325, and 330 may include information, such as number of fields, type of logged activity, sub-type of logged activity, data input size, upload request, upload byte count, log showing request, number of log showing fields, etc.
[0048] In one embodiment of method 300, the activity of the computing system of blocks 310, 315, 320, 325, and 330 may be networking activities done through a transmission control protocol/internet protocol (TCP/IP), transport layer security (TLS), secure sockets layer (SSL), user datagram protocol (UDP), routing, or the like. In one embodiment of method 300, the activity of the computing system of blocks 310, 315, 320, 325, and 330 may be non-networking activities.
[0049] In one embodiment of method 300, the log level of blocks 325 and 330 may be defined in different degrees without limitation, for example, LOW, MEDIUM, HIGH, etc. In another embodiment of method 300, the log levels of blocks 325 and 330 may be set for log data that is already stored in computer-readable mediums. In another embodiment of method 300, the log levels of blocks 325 and 330 may be set for log data that will be created for future activities.
[0050] FIG. 4 is a flow chart illustrating a method 400 for logging data and setting log levels in a computer system according to one embodiment of the disclosure. The method 400 shown in FIG. 4 may be part of or combined with other methods disclosed herein, such as the methods shown in FIGS. 2-3 and 5. The method 400 shown in FIG. 4 may be implemented in the systems and apparatuses disclosed herein, such as the systems and apparatuses shown in FIGS. 1 and 6-8.
[0051] As shown in FIG. 4, the method 400 starts at block 405. The method 400 proceeds to block 410 which includes receiving, at a processor executing an operating system, a first request from an emulated environment to create log data of an activity of a networking component of the computing system. The method 400 proceeds to block 415 which includes acquiring, at the processor executing the operating system, information about the activity of the networking component of the computing system. The method 400 proceeds to block 420 which includes creating, with the processor executing the operating system, the log data of the activity of the networking component of the computing system. The method 400 proceeds to block 425 which includes receiving, at the processor executing the operating system, a second request from the emulated environment to set a log level of the log data of the activity of the networking component of the computing system. The method 400 proceeds to block 430 which includes setting, with the processor executing the operating system, the log level of the log data of the activity of the networking component of the computing system.
[0052] In one embodiment of the method 400, the blocks 410, 415, 420, 425, and 430 may be a computing system configured with operating system 120 shown in FIG. 1. In another embodiment, the operating system of blocks 410, 415, 420, 425, and 430 may be a computing system configured with System Architecture Interface Layer (SAIL), Unix, Linux, or the like. In another embodiment, the operating system of blocks 410, 415, 420, 425, and 430 may include a non-emulated networking interface, such as the non-emulated networking interface 125 shown in FIG. 1. In another embodiment, the operating system of blocks 410, 415, 420, 425, and 430 may include XNIOP.
[0053] In one embodiment of the method 400, the emulated environment of blocks 410 and 425 may be the emulated environment 105 shown in FIG. 1. In another embodiment, the emulated environment of blocks 410 and 425 may be Linux, Windows, Java, Unix, OS 2200, or the like. In another embodiment, the emulated environment of blocks 410 and 425 may include the computer program 110 shown in FIG. 1. In another embodiment, the emulated environment of blocks 410 and 425 may include CPCommOS or the like communication platforms.
[0054] In one embodiment of the method 400, the log data of blocks 410, 420, 425, and 430 may include any information existing in any data structure. In another embodiment of the method 400, the log data of blocks 410, 420, 425, and 430 may include information, such as number of fields, type of logged activity, sub-type of logged activity, data input size, upload request, upload byte count, log showing request, number of log showing fields, etc.
[0055] In one embodiment of method 400, the networking component of the computing system of blocks 410, 415, 420, 425, and 430 may employ transmission control protocol/internet protocol (TCP/IP), transport layer security (TLS), secure sockets layer (SSL) protocols, user datagram protocol (UDP), routing, or the like.
[0056] In one embodiment of method 400, the log levels of blocks 425 and 430 may be defined in different degrees without limitation, for example, LOW, MEDIUM, HIGH, etc. In another embodiment of method 400, the log levels of blocks 425 and 430 may be set for log data that are already stored in computer-readable mediums. In another embodiment of method 400, the log levels of blocks 425 and 430 may be set for log data that will be created for future activities.
[0057] FIG. 5 is a flow chart illustrating a method 500 for retrieving stored log data according to one embodiment of the disclosure. The method 500 shown in FIG. 5 may be part of or combined with other methods disclosed herein, such as the methods shown in FIGS. 2-4. The method 500 shown in FIG. 5 may be implemented in the systems and apparatuses disclosed herein, such as the systems and apparatuses shown in FIGS. 1 and 6-8.
[0058] As shown in FIG. 5, the method 500 starts at block 505. The method 500 proceeds to block 510 which includes receiving, at a processor executing an operating system, a third request from an emulated environment to retrieve stored log data. The method 500 proceeds to block 515 which includes transmitting, from the processor executing the operating system the stored log data.
[0059] In one embodiment of the method 500, the operating system of blocks 510 and 515 may be the operating system 120 shown in FIG. 1. In another embodiment, the operating system of blocks 510 and 515 may be System Architecture Interface Layer (SAIL), Unix, Linux, or the like. In another embodiment, the operating system of blocks 510 and 515 may include a non-emulated networking interface, such as the non-emulated networking interface 125 shown in FIG. 1. In another embodiment, the operating system of blocks 510 and 515 may include XNIOP.
[0060] In one embodiment of the method 500, the emulated environment of block 510 may be the emulated environment 105 shown in FIG. 1. In another embodiment, the emulated environment of block 510 may be Linux, Windows, Java, Unix, OS 2200, or the like. In another embodiment, the emulated environment of block 510 may include the computer program 110 shown in FIG. 1. In another embodiment, the emulated environment of block 510 may include CPCommOS or the like communication platforms.
[0061] In one embodiment of the method 500, the stored log data of blocks 510 and 515 may include any information existing in any data structure. In another embodiment of the method 500, the stored log data of blocks 510 and 515 may include information, such as number of fields, type of logged activity, sub-type of logged activity, data input size, upload request, upload byte count, log showing request, number of log showing fields, etc. In another embodiment of the method 500, the stored log data of blocks 510 and 515 may be stored in computer-readable mediums.
[0062] FIG. 6 illustrates a computer network 600 for obtaining access to database files in a computing system according to one embodiment of the disclosure. The system 600 may include a server 602, a data storage device 606, a network 608, and a user interface device 610. The server 602 may also be a hypervisor-based system executing one or more guest partitions hosting operating systems with modules having server configuration information. In a further embodiment, the system 600 may include a storage controller 604, or a storage server configured to manage data communications between the data storage device 606 and the server 602 or other components in communication with the network 608. In an alternative embodiment, the storage controller 604 may be coupled to the network 608.
[0063] In one embodiment, the user interface device 610 is referred to broadly and is intended to encompass a suitable processor-based device such as a desktop computer, a laptop computer, a personal digital assistant (PDA) or tablet computer, a smartphone or other mobile communication device having access to the network 608. In a further embodiment, the user interface device 610 may access the Internet or other wide area or local area network to access a web application or web service hosted by the server 602 and may provide a user interface for enabling a user to enter or receive information.
[0064] The network 608 may facilitate communications of data between the server 602 and the user interface device 610. The network 608 may include any type of communications network including, but not limited to, a direct PC-to-PC connection, a local area network (LAN), a wide area network (WAN), a modem-to-modem connection, the Internet, a combination of the above, or any other communications network now known or later developed within the networking arts which permits two or more computers to communicate.
[0065] FIG. 7 illustrates a computer system 700 adapted according to certain embodiments of the server 602 and/or the user interface device 610. The central processing unit ("CPU") 702 is coupled to the system bus 704. The CPU 702 may be a general purpose CPU or microprocessor, graphics processing unit ("GPU"), and/or microcontroller. The present embodiments are not restricted by the architecture of the CPU 702 so long as the CPU 702, whether directly or indirectly, supports the operations as described herein. The CPU 702 may execute the various logical instructions according to the present embodiments.
[0066] The computer system 700 may also include random access memory (RAM) 708, which may be synchronous RAM (SRAM), dynamic RAM (DRAM), synchronous dynamic RAM (DRAM), or the like. The computer system 700 may utilize RAM 708 to store the various data structures used by a software application. The computer system 700 may also include read only memory (ROM) 706 which may be PROM, EPROM, EEPROM, optical storage, or the like. The ROM may store configuration information for booting the computer system 700. The RAM 708 and the ROM 706 hold user and system data, and both the RAM 708 and the ROM 706 may be randomly accessed.
[0067] The computer system 700 may also include an I/O adapter 710, a communications adapter 714, a user interface adapter 716, and a display adapter 722. The I/O adapter 710 and/or the user interface adapter 716 may, in certain embodiments, enable a user to interact with the computer system 700. In a further embodiment, the display adapter 722 may display a graphical user interface (GUI) associated with a software or web-based application on a display device 724, such as a monitor or touch screen.
[0068] The I/O adapter 710 may couple one or more storage devices 712, such as one or more of a hard drive, a solid state storage device, a flash drive, a compact disc (CD) drive, a floppy disk drive, and a tape drive, to the computer system 700. According to one embodiment, the data storage 712 may be a separate server coupled to the computer system 700 through a network connection to the I/O adapter 710. The communications adapter 714 may be adapted to couple the computer system 700 to the network 608, which may be one or more of a LAN, WAN, and/or the Internet. The user interface adapter 716 couples user input devices, such as a keyboard 720, a pointing device 718, and/or a touch screen (not shown) to the computer system 700. The display adapter 722 may be driven by the CPU 702 to control the display on the display device 724. Any of the devices 702-722 may be physical and/or logical.
[0069] The applications of the present disclosure are not limited to the architecture of computer system 700. Rather the computer system 700 is provided as an example of one type of computing device that may be adapted to perform the functions of the server 602 and/or the user interface device 710. For example, any suitable processor-based device may be utilized including, without limitation, personal data assistants (PDAs), tablet computers, smartphones, computer game consoles, and multi-processor servers. Moreover, the systems and methods of the present disclosure may be implemented on application specific integrated circuits (ASIC), very large scale integrated (VLSI) circuits, or other circuitry. In fact, persons of ordinary skill in the art may utilize any number of suitable structures capable of executing logical operations according to the described embodiments. For example, the computer system 700 may be virtualized for access by multiple users and/or applications.
[0070] FIG. 8A is a block diagram illustrating a server hosting an emulated software environment for virtualization according to one embodiment of the disclosure. An operating system 802 executing on a server includes drivers for accessing hardware components, such as a networking layer 804 for accessing the communications adapter 814. The operating system 802 may be, for example, Linux or Windows. An emulated environment 808 in the operating system 802 executes a program 810, such as Communications Platform for Open Systems (CPCommOS). The program 810 accesses the networking layer 804 of the operating system 802 through a non-emulated interface 806, such as extended network input output processor (XNIOP). The non-emulated interface 806 translates requests from the program 810 executing in the emulated environment 808 for the networking layer 804 of the operating system 802.
[0071] In another example, hardware in a computer system may be virtualized through a hypervisor. FIG. 8B is a block diagram illustrating a server hosting an emulated hardware environment according to one embodiment of the disclosure. Users 852, 854, 856 may access the hardware 860 through a hypervisor 858. The hypervisor 858 may be integrated with the hardware 860 to provide virtualization of the hardware 860 without an operating system, such as in the configuration illustrated in FIG. 8A. The hypervisor 858 may provide access to the hardware 860, including the CPU 802 and the communications adaptor 814.
[0072] If implemented in firmware and/or software, the functions described above may be stored as one or more instructions or code on a computer-readable medium. Examples include non-transitory computer-readable media encoded with a data structure and computer-readable media encoded with a computer program. Computer-readable media includes physical computer storage media. A storage medium may be any available medium that can be accessed by a computer. By way of example, and not limitation, such computer-readable media can comprise RAM, ROM, EEPROM, CD-ROM or other optical disk storage, magnetic disk storage or other magnetic storage devices, or any other medium that can be used to store desired program code in the form of instructions or data structures and that can be accessed by a computer. Disk and disc includes compact discs (CD), laser discs, optical discs, digital versatile discs (DVD), floppy disks and blu-ray discs. Generally, disks reproduce data magnetically, and discs reproduce data optically. Combinations of the above should also be included within the scope of computer-readable media.
[0073] In addition to storage on computer-readable medium, instructions and/or data may be provided as signals on transmission media included in a communication apparatus. For example, a communication apparatus may include a transceiver having signals indicative of instructions and data. The instructions and data are configured to cause one or more processors to implement the functions outlined in the claims.
[0074] Although the present disclosure and its advantages have been described in detail, it should be understood that various changes, substitutions and alterations can be made herein without departing from the spirit and scope of the disclosure as defined by the appended claims. Moreover, the scope of the present application is not intended to be limited to the particular embodiments of the process, machine, manufacture, composition of matter, means, methods and steps described in the specification. As one of ordinary skill in the art will readily appreciate from the present invention, disclosure, machines, manufacture, compositions of matter, means, methods, or steps, presently existing or later to be developed that perform substantially the same function or achieve substantially the same result as the corresponding embodiments described herein may be utilized according to the present disclosure. Accordingly, the appended claims are intended to include within their scope such processes, machines, manufacture, compositions of matter, means, methods, or steps.
* * * * *
D00000

D00001

D00002

D00003

D00004

D00005
D00006

D00007

D00008

XML
uspto.report is an independent third-party trademark research tool that is not affiliated, endorsed, or sponsored by the United States Patent and Trademark Office (USPTO) or any other governmental organization. The information provided by uspto.report is based on publicly available data at the time of writing and is intended for informational purposes only.
While we strive to provide accurate and up-to-date information, we do not guarantee the accuracy, completeness, reliability, or suitability of the information displayed on this site. The use of this site is at your own risk. Any reliance you place on such information is therefore strictly at your own risk.
All official trademark data, including owner information, should be verified by visiting the official USPTO website at www.uspto.gov. This site is not intended to replace professional legal advice and should not be used as a substitute for consulting with a legal professional who is knowledgeable about trademark law.