Maintaining an Authenticated State
Prag; Johan ; et al.
U.S. patent application number 16/872055 was filed with the patent office on 2021-01-28 for maintaining an authenticated state. This patent application is currently assigned to Google LLC. The applicant listed for this patent is Google LLC. Invention is credited to Brandon Barbello, Alok Chandel, Selim Flavio Cinek, Leonardo Giusti, Tyler Reed Kugler, Lucas Dupin Moreira Costa, Johan Prag, Vignesh Sachidanandam, Artur Tsurkan.
| Application Number | 20210029542 16/872055 |
| Document ID | / |
| Family ID | 1000004825804 |
| Filed Date | 2021-01-28 |








View All Diagrams
| United States Patent Application | 20210029542 |
| Kind Code | A1 |
| Prag; Johan ; et al. | January 28, 2021 |
Maintaining an Authenticated State
Abstract
This document describes techniques and systems for maintaining an authenticated state based radar data from a radar system, and in some cases, on sensor data from an Inertial Measurement Unit (IMU). The techniques and systems use radar data to determine, after an indication that the user has potentially disengaged with the user equipment, to determine whether or not the user is passively engaged with the user equipment. Responsive to determining that the user is passively engaged, the techniques and systems maintain the authenticated state. By maintaining this authenticated state, the techniques manage the user equipment's state to correspond to a user's engagement with the user equipment, which can save power and improve a user's experience.
| Inventors: | Prag; Johan; (Mountain View, CA) ; Kugler; Tyler Reed; (Palo Alto, CA) ; Tsurkan; Artur; (San Francisco, CA) ; Giusti; Leonardo; (San Francisco, CA) ; Chandel; Alok; (Mountain View, CA) ; Moreira Costa; Lucas Dupin; (Mountain View, CA) ; Cinek; Selim Flavio; (Los Angeles, CA) ; Sachidanandam; Vignesh; (Redwood City, CA) ; Barbello; Brandon; (Mountain View, CA) | ||||||||||
| Applicant: |
|
||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|
| Assignee: | Google LLC Mountain View CA |
||||||||||
| Family ID: | 1000004825804 | ||||||||||
| Appl. No.: | 16/872055 | ||||||||||
| Filed: | May 11, 2020 |
Related U.S. Patent Documents
| Application Number | Filing Date | Patent Number | ||
|---|---|---|---|---|
| PCT/US2019/049208 | Aug 30, 2019 | |||
| 16872055 | ||||
| 62879361 | Jul 26, 2019 | |||
| Current U.S. Class: | 1/1 |
| Current CPC Class: | H04L 63/0861 20130101; G01S 13/867 20130101; H04W 12/08 20130101; H04W 12/06 20130101 |
| International Class: | H04W 12/06 20060101 H04W012/06; G01S 13/86 20060101 G01S013/86; H04W 12/08 20060101 H04W012/08; H04L 29/06 20060101 H04L029/06 |
Claims
1. A method comprising: determining, during an authenticated state of a user equipment, a potential disengagement by the user of the user equipment, the authenticated state permitting access by the user of data, applications, functions, accounts, or components of the user equipment; determining, based on radar data and by the user equipment, a passive engagement by the user with the user equipment; and responsive to the determination of the passive engagement by the user with the user equipment, maintaining the authenticated state.
2. The method of claim 1, wherein the authenticated state permits access by the user to the data, the applications, the functions, at least one of the accounts, and at least one of the components of the user equipment.
3. The method of claim 1, further comprising determining that an inactivity time period has expired and wherein determining the potential disengagement is based on the determination that the inactivity time period has expired.
4. The method of claim 3, wherein the inactivity timer period begins at a last user action with the user equipment, a last active engagement with the user equipment, or a last-determined intent to engage with the user equipment.
5. The method of claim 1, further comprising determining, based on inertial data of an inertial measurement unit (IMU) integral with the user equipment, a movement of the user equipment, and wherein determining the potential disengagement is based on the determined movement.
6. The method of claim 1, wherein determining the passive engagement by the user with the user equipment is responsive to the determination of the potential disengagement and further comprising, prior to determining the passive engagement by the user, increasing a power state of a component of a radar system from which the radar data is received.
7. The method of claim 1, wherein determining passive engagement by the user determines, based on the radar data, that a hand of the user is holding the user equipment at an orientation at which a display of the user equipment is maintained.
8. The method of claim 1, wherein determining passive engagement by the user of the user equipment determines, based on the radar data, that the user is oriented toward or looking toward the user equipment.
9. The method of claim 1, wherein determining passive engagement by the user of the user equipment determines, based on the radar data, that the user is within two meters of the user equipment.
10. The method of claim 1, further comprising reducing an information state of the user equipment from a high-information state to an intermediate-information state or a low-information state.
11. The method of claim 10, wherein reducing the information state is responsive to determining that the user is oriented or looking away from the user equipment.
12. The method of claim 1, further comprising determining, based on the radar data or later-received radar data, an intent to engage of a non-user or a presence of the non-user and, responsive to the determination of the intent to engage of the non-user or the presence of the non-user, ceasing to maintain the authenticated state.
13. The method of claim 12, further comprising returning to the authenticated state responsive to determining that the non-user is no longer present.
14. The method of claim 13, further comprising, responsive to the determination of the intent to engage of the non-user or the presence of the non-user, reducing an information state of the user equipment and, responsive to returning to the authenticated state, increasing the information state of the user equipment.
15. The method of claim 14, wherein increasing the information state of the user equipment presents information as presented prior to the reduction of the information state.
16. An apparatus configured to: determine, during an authenticated state of the apparatus and by at least one of a radar manager, a movement manager, and a state manager, a potential disengagement by the user of the apparatus, the authenticated state permitting access by the user of data, applications, functions, accounts, or components of the apparatus; determine, based on radar data and by the radar manager, a passive engagement by the user with the apparatus; and responsive to the determination of the passive engagement by the user with the apparatus, maintain the authenticated state.
17. The apparatus of claim 16, wherein the determination of the passive engagement by the user with the apparatus is responsive to the determination of the potential disengagement; and the apparatus further configured to, prior to the determination of the passive engagement by the user, increase a power state of a component of a radar system from which the radar data is received.
18. The apparatus of claim 16, wherein the apparatus is configured to, in determining passive engagement by the user with the apparatus, determine, based on the radar data, that the user is within two meters of the apparatus.
19. The apparatus of claim 16, wherein the apparatus is further configured to reduce, responsive to a determination that the user is oriented or looking away from the apparatus, an information state of the apparatus from a high-information state to an intermediate-information state or a low-information state.
20. The apparatus of claim 16, further configured to determine, based on the radar data or later-received radar data, an intent to engage of a non-user or a presence of the non-user and, responsive to the determination of the intent to engage of the non-user or the presence of the non-user, ceasing to maintain the authenticated state.
Description
RELATED APPLICATIONS
[0001] This application is a continuation of and claims priority to PCT Patent Application Serial No. PCT/US2019/049208 filed Aug. 30, 2019 entitled "Maintaining an Authenticated State", which, in turn, claims priority under 35 U.S.C. .sctn. 119(e) to U.S. Provisional Patent Application No. 62/879,361, entitled "Authentication Management Using IMU and Radar" and filed on Jul. 26, 2019, the disclosures of which are incorporated in their entireties by reference herein.
BACKGROUND
[0002] User equipment, such as smartphones, wearable computers, and tablets, often require authentication of a user prior to permitting access to the device. Once the user equipment has authenticated the user, the user equipment enters an authenticated state in which the user enjoys access to various data, applications, and functions of the user equipment.
[0003] As users interact with their devices more and more often, with some users authenticating themselves to their devices tens or even hundreds of times a day, the importance of managing this authenticated state continues to rise. Any error in managing this authenticated state, such as failing to remain authenticated when a user wishes to maintain access or failing to de-authenticate when appropriate, is increasingly problematic.
SUMMARY
[0004] This document describes techniques and systems for maintaining an authenticated state. The techniques and systems use radar data, and in some cases inertial sensor data from an inertial measurement unit (IMU), to determine when to maintain an authenticated state, thereby permitting a user to maintain access to their user equipment when some current techniques would de-authenticate the user. These techniques and systems conserve power, improve a user's experience, or better protect a user's privacy.
[0005] For example, a method is described that determines, during an authenticated state of a user equipment, a potential disengagement by the user of the user equipment. This authenticated state permits access by the user of data, applications, functions, accounts, or components of the user equipment. The method also determines, based on radar data and by the user equipment, a passive engagement by the user with the user equipment. Responsive to the determination of the passive engagement by the user with the user equipment, the method maintains the authenticated state.
[0006] This document also describes computer-readable media having instructions for performing the above-summarized method and other methods set forth herein, as well as systems and means for performing these methods.
[0007] This summary is provided to introduce simplified concepts for maintaining an authenticated state, which is further described below in the Detailed Description and Drawings. This summary is not intended to identify essential features of the claimed subject matter, nor is it intended for use in determining the scope of the claimed subject matter.
BRIEF DESCRIPTION OF THE DRAWINGS
[0008] The details of one or more aspects of maintaining an authenticated state are described in this document with reference to the following drawings. The same numbers are used throughout the drawings to reference like features and components:
[0009] FIG. 1 illustrates an example environment in which techniques for maintaining an authenticated state can be implemented.
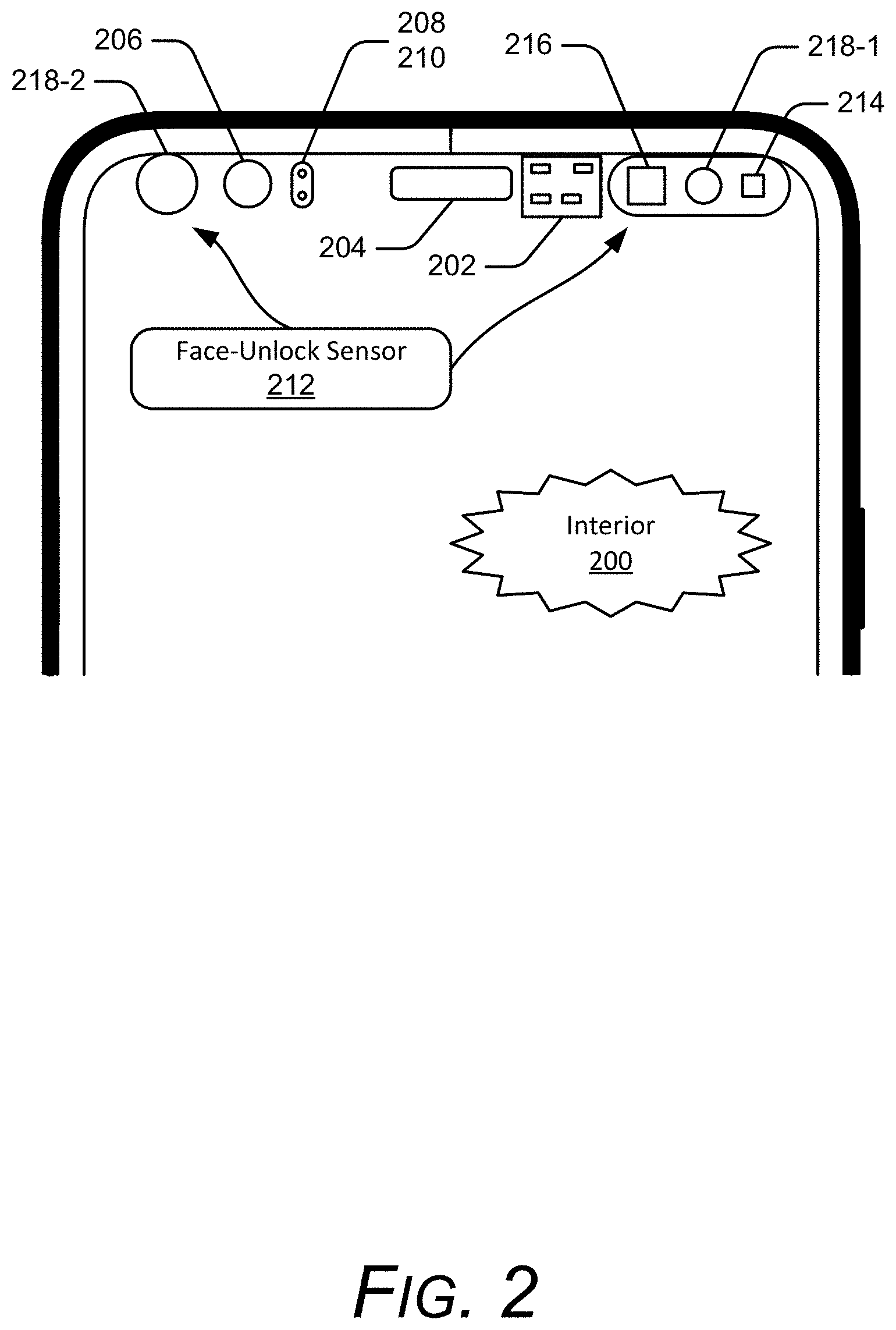
[0010] FIG. 2 illustrates an example of the authentication system set forth in FIG. 1.
[0011] FIG. 3 illustrates an example user authenticated by the authentication system of FIG. 2.
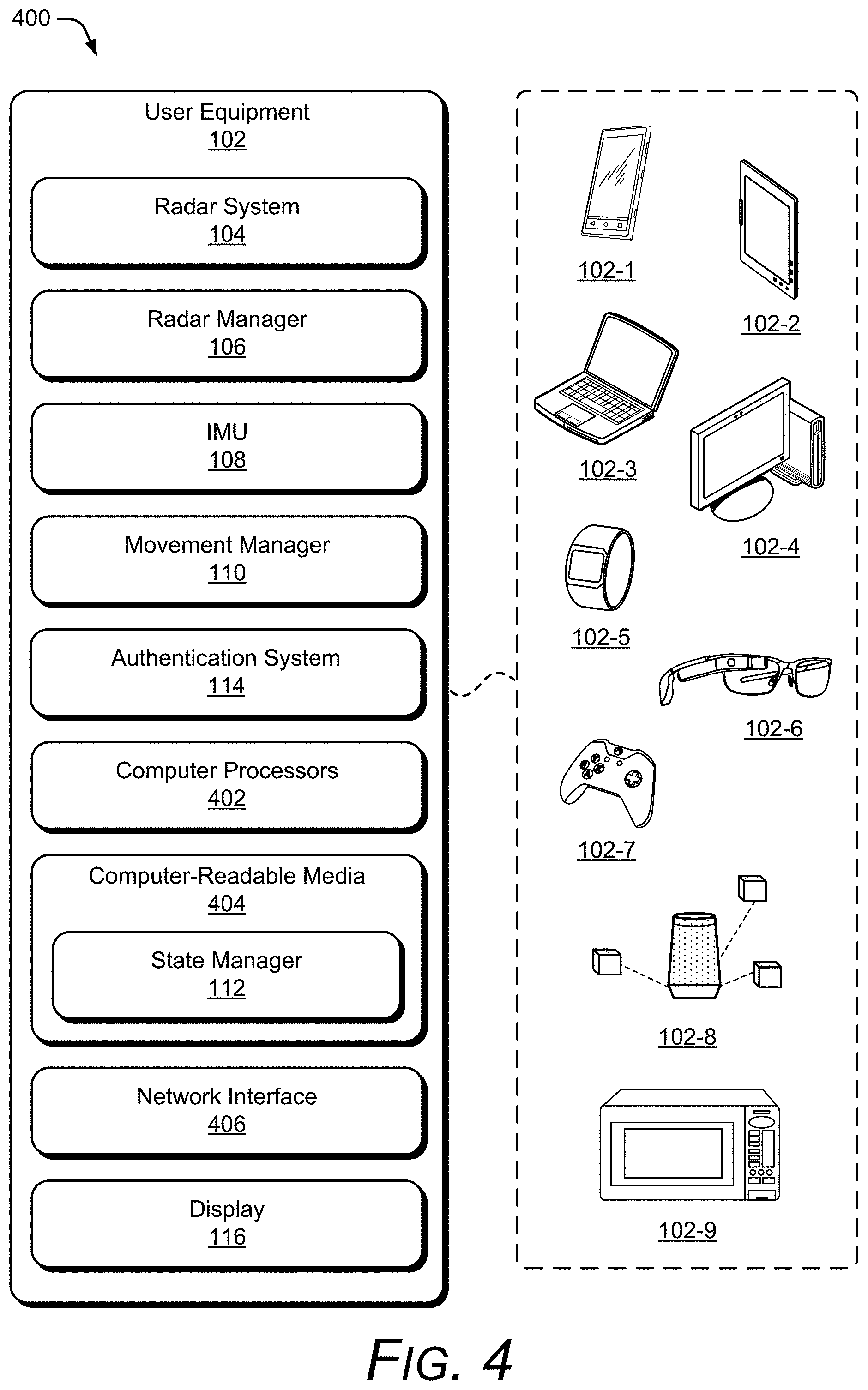
[0012] FIG. 4 illustrates an implementation of the user equipment of FIG. 1 that can alter states, including a power state of an authentication system responsive to determination of a user's intent to engage with a user equipment.
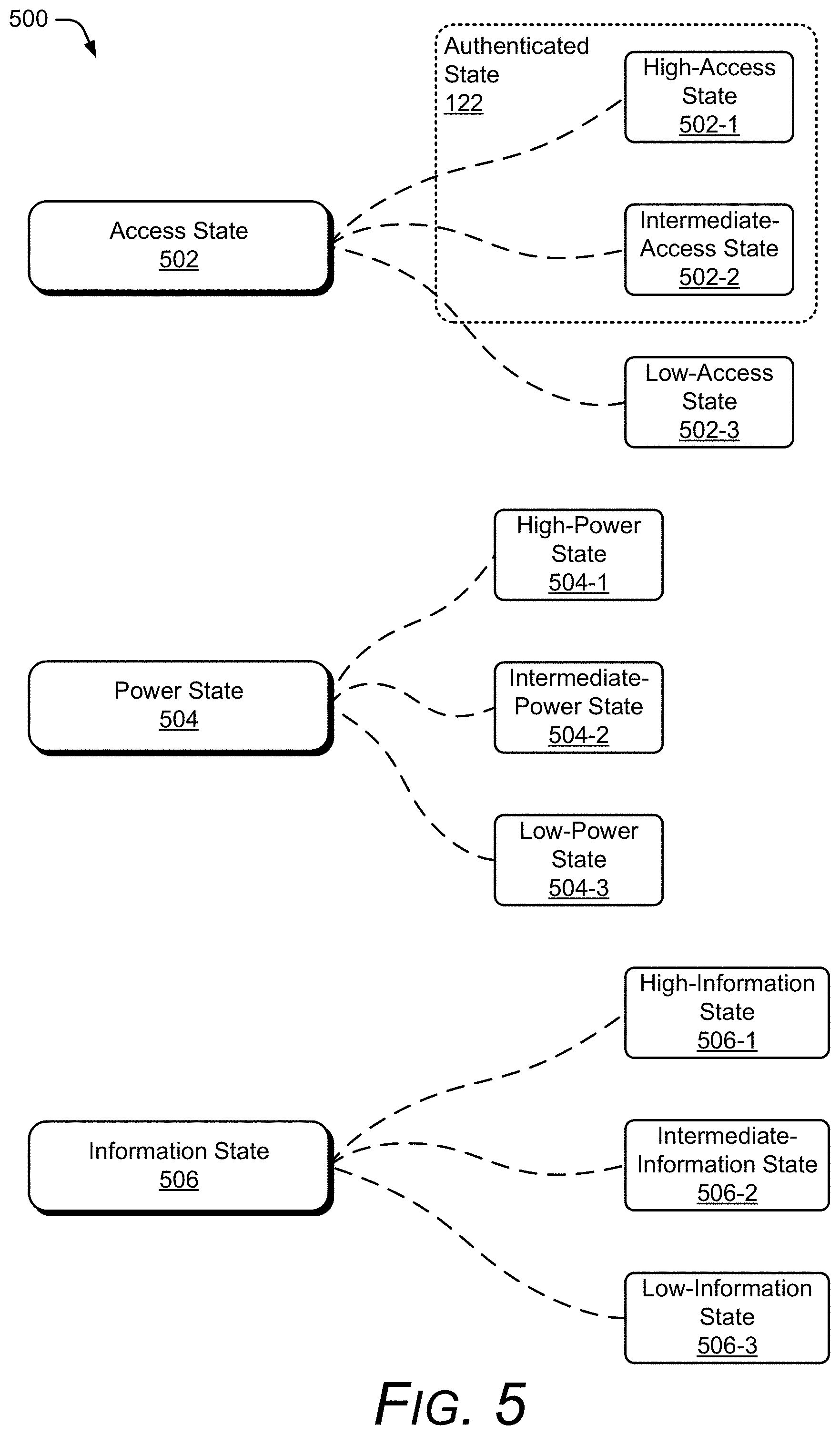
[0013] FIG. 5 illustrates example information, power, and access states of a user equipment.
[0014] FIG. 6-1 illustrates an example radar system as part of a computing device.
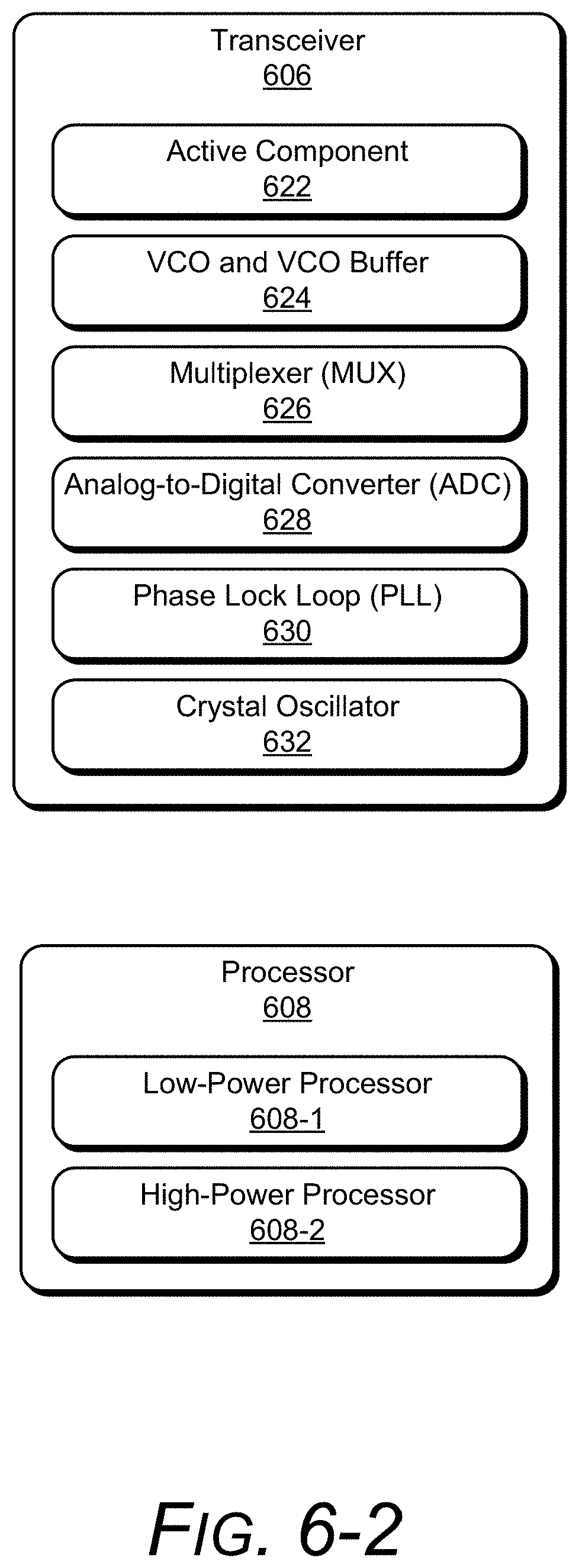
[0015] FIG. 6-2 illustrates an example transceiver and processor.
[0016] FIG. 6-3 illustrates an example relationship between power consumption, a gesture-frame update rate, and a response delay.
[0017] FIG. 6-4 illustrates an example framing structure.
[0018] FIG. 7 illustrates example arrangements of receiving antenna elements for the radar system of FIG. 6-1.
[0019] FIG. 8 illustrates additional details of an example implementation of the radar system of FIG. 6-1.
[0020] FIG. 9 illustrates an example scheme that can be implemented by the radar system of FIG. 6-1.
[0021] FIG. 10 illustrates an example method for authentication management through IMU and/or radar.
[0022] FIG. 11 illustrates an example scenario for authentication management.
[0023] FIG. 12 illustrates an example method for reducing a state of a user equipment.
[0024] FIG. 13 illustrates an example scenario for reducing a state of a user equipment.
[0025] FIG. 14 illustrates an example method for maintaining an authenticated state.
[0026] FIG. 15 illustrates an example scenario for maintaining an authenticated state.
[0027] FIG. 16 illustrates another example scenario for maintaining an authenticated state.
DETAILED DESCRIPTION
[0028] Overview
[0029] This document describes techniques and systems for maintaining an authenticated state based radar data from a radar system, and in some cases, on sensor data from an Inertial Measurement Unit (IMU). The techniques and systems use radar data to determine, after an indication that the user has potentially disengaged with the user equipment, to determine whether or not the user is passively engaged with the user equipment. Responsive to determining that the user is passively engaged, the techniques and systems maintain the authenticated state. By maintaining this authenticated state, the techniques manage the user equipment's state to correspond to a user's engagement with the user equipment, which can save power and improve a user's experience.
[0030] Furthermore, alternative techniques are disclosed that de-authenticate the user equipment responsive to a non-user's presence or intent to engage with the user equipment, thereby reducing unwarranted access, reducing an amount of information provided to a non-user, both of which can help protect the user's privacy.
[0031] In contrast to the disclosed techniques, conventional user equipment are often unable to accurately determine a user's engagement with the user equipment (UE). Because these UE are unable to do so, but still need to de-authenticate the UE to keep it secure, current techniques lock the UE when a time period expires. This time period, for many conventional techniques, is a period during which the user has not pressed any buttons or touched a sensor on the mobile device, such as touching a touch-sensitive display. Thus, conventional techniques often start a timer when no obvious input from a user is received, and then de-authenticate the UE when the timer expires without any obvious input. But this solution can de-authenticate a user when that user still desires to maintain engagement with, or at least maintain the authenticated state of, the user equipment. Because current solutions de-authenticate when undesired by the user, the user's experience is reduced by having to re-authenticate and power is wasted in performing the re-authentication.
[0032] By way of one example, assume that a user, while their tablet computer is in an authenticated state, sets their tablet against a book on their desk, selects a movie to watch, and then sits back to watch the movie. Conventional techniques often start a timer, and then, after the timer expires without any obvious input from the user, de-authenticates the user equipment. If, as is common, the time period is five minutes, the user's device then de-authenticates (e.g., "locks"). If the user wishes to access the user device, they must re-authenticate. This provides a poor user experience and wastes power, often resulting in reduced battery life, further reducing the user's experience with their user equipment.
[0033] In contrast to these conventional techniques, the described techniques determine, based on radar data, that a user is passively engaged with the user equipment, such as by determining that they are continuing to look toward the tablet computer. Based on this passive engagement, the techniques maintain the authenticated state, thereby permitting the user to access the user equipment without re-authenticating.
[0034] This is but one example of how the described techniques and devices may be used to maintain an authenticated state. Other examples and implementations are described throughout this document. The document now turns to an example operating environment, after which example devices, methods, and systems are described.
[0035] Operating Environment
[0036] FIG. 1 illustrates an example environment 100 in which techniques for maintaining an authenticated state can be implemented. The example environment 100 includes a user equipment (UE) 102 (e.g., a smartphone), which includes, or is associated with, a radar system 104, a radar manager 106, an inertial measurement unit (IMU) 108, a movement manager 110, a state manager 112, an authentication system 114, and a display 116.
[0037] In the example environment 100, the radar system 104 provides a radar field 118 by transmitting one or more radar signals or waveforms as described below with reference to FIGS. 7-9. The radar field 118 is a volume of space from which the radar system 104 can detect reflections of the radar signals and waveforms (e.g., radar signals and waveforms reflected from objects in the volume of space, also referred to generally herein as radar data). The radar system 104 also enables the UE 102, or another electronic device, to sense and analyze this radar data from reflections within the radar field 118. The radar field 118 may take any of a variety of shapes and forms. For example, the radar field 118 may have a shape as described with reference to FIGS. 1 and 7. In other cases, the radar field 118 may take a shape of a radius extending from the radar system 104, a volume around the radar system 104 (e.g., a sphere, a hemisphere, a partial sphere, a beam, or a cone), or a non-uniform shape (e.g., to accommodate interference from obstructions in the radar field 118). The radar field 118 may extend any of a variety of distances from the radar system 104 such as inches to twelve feet (less than a third of a meter to four meters). The radar field 118 may be predefined, user-selectable, or determined via another method (e.g., based on power requirements, remaining battery life, or another factor).
[0038] The reflection from the user 120 in the radar field 118 enables the radar system 104 to determine various information about the user 120, such as the body position and posture of the user 120, which may indicate a variety of different nonverbal body language cues, body positions, or body postures. The cues, positions, and postures may include an absolute position or distance of the user 120 with reference to the UE 102, a change in the position or distance of the user 120 with reference to the UE 102 (e.g., whether the user 120 or the user's hand or object held by the user 120 is moving closer to or farther from the UE 102), the velocity of the user 120 (e.g., a hand or a non-user object) when moving toward or away from the UE 102, whether the user 120 turns toward or away from the UE 102, whether the user 120 leans toward, waves toward, reaches for, or points at the UE 102, and so forth. These reflections can also be analyzed to determine, or to add confidence to, authentication, such as an identity of a human through analysis of the radar data (e.g., scattering centers of a user's face).
[0039] The radar manager 106 is configured to determine, based on radar data from the radar system 104, a user's intent to engage, disengage, or maintain engagement with the UE 102. A user's intent can be deduced from the various cues, positions, postures, and distances/velocities noted above, such as based on a hand or arm reach toward, a movement of eyes to look at, or movement of a head or face oriented toward the UE 102. For a hand or arm reach, the radar manager 106 determines that the user is reaching their hand or orienting their arm in such a way as to indicate a likely intent to touch or pick up the UE 102. Examples include a user reaching toward a volume button on a wirelessly attached speaker, a reach toward a wireless or wired mouse associated with a tablet computer, or a reach toward the UE 102 itself This reach toward can be determined based on a hand movement alone, an arm and hand movement, or an arm bending or straightening in a manner that permits a hand of the arm to touch or grab the UE 102. As noted in FIGS. 14-16 below, this intent to engage determination can be for non-users or users, authenticated or not.
[0040] A user's intent to engage can also be deduced based on a user's movement of their head or eyes to look at, or orient their face toward, the UE 102 or, in some cases, an associated peripheral of the UE 102. For movement of a user's eyes to look toward the UE 102, the radar manager 106 determines that the user's eyes are looking in the direction of the UE 102, such as through tracking of the user's eyes. For movement of the user's head to orient their face toward the UE 102 (e.g., a facial orientation), the radar manager 106 determines that various points (e.g., scattering centers as noted below) are now oriented such that the user's face is pointing toward the UE 102. Thus, a user need not perform an action designed to control or activate the UE 102, such as activating (pressing) on a button on the UE 102, or a touch-dependent gesture (e.g., on a touch pad or screen) or touch-independent gesture (e.g., using the radar system 104) in order for the radar manager 106 to determine that the user intends to engage (or disengage or maintain engagement) with the UE 102.
[0041] As noted above, the radar manager 106 is also configured to determine a user's intent to disengage with the UE 102. The radar manager 106 determines a user's intent to disengage similarly to a user's intent to engage, though deduced from radar data indicating that the user's hand or arm is moving away from the UE 102 (e.g., retracting), movement of eyes to look away from, or movement of the head or face away from the UE 102 (e.g., a facial orientation change away from looking at the UE 102). Additional manners through which to determine a user's intent to disengage are not only the opposite or cessation of engagement noted above, but also radar data indicating that the user has walked away, moved their body away from, or has engaged with a different, unassociated object or device. Thus, the radar manager 106 may determine an intent to disengage with the UE 102 based on determining an intent to engage, by the user, with some other object, device, or user equipment. Assume, for example, that a user is looking at and interacting with a smartphone. Example intents to engage that indicate an intent to disengage with that smartphone include the user looking, instead of at the smartphone, at a television screen, beginning to talk to a nearby physically-present person, or reaching toward another device with which engagement is likely to replace the engagement with the smartphone, such as an e-book or media player.
[0042] The radar manager 106 is also configured to determine a user's intent to maintain engagement with the UE 102. This maintaining of engagement can be active or passive. For active engagement, the radar manager 106 may determine, based on radar data, that the user is interacting through touch-independent gestures, and so forth. The radar manager 106 may also or instead determine active engagement through non-radar data (e.g., performed with assistance from other components of the UE 102). These non-radar data include indications that the user is inputting data to or controlling the UE 102 or a peripheral. Thus, through touch, typing, or audio data, the user is determined to be touching (e.g., tapping on a soft keyboard or performing a gesture) through a touch-screen input of the display 116, typing on a peripheral keyboard, or is determined to be dictating an audio input. For maintaining passive engagement, the radar manager 106 determines, independently or through assistance of other components of the UE 102, that the user is consuming content or providing the UE 102 to others to consume content, such as pointing their face toward the UE 102, looking at the display 116, or is holding the UE 102 in such a way as to orient the UE 102's display to be visible by the user or a third party. Other examples of maintaining passive engagement include a user's presence, such as through the radar manager 106 determining that the user 120 is within reach of (e.g., two, 1.5, one, or one-half of one meter from) the UE 102. Details of example ways in which the radar manager 106 determines a user's intent to engage, disengage, or maintain engagement, both passively and actively, are described below.
[0043] Further still, the radar manager 106, using radar data from the radar system 104, may also determine gestures performed by a user. These gestures can involve the user touching some surface, such as a table, the display 116, or their shirt sleeve, or touch-independent gestures. Touch-independent gestures can be performed in the air, in three dimensions, and/or without necessitating a hand or fingers touch an input device, but are not precluded from touching some object. These gestures can be determined based on the radar data and then used as input to, or to indicate engagement with, the UE 102. Example gestures include those similar to sign language (e.g., ASL or American Sign Language), which are varied, complex single hand or multi-hand gestures, or simple multi-hand or single hand gestures, such as to swipe left, right, up, or down, flat-hand-raise or lower (e.g., to raise or lower music volume of the UE 102 or a television or stereo controlled through the UE 102), or to swipe forward or backward (e.g., left-to-right or right-to-left) to change music and video tracks, snooze alarms, dismiss phone calls, or even play games. These are but a few of the many example gestures and functions controllable by these gestures and which are enabled through the radar system 104 and the radar manager 106. Thus, while this document is directed to engagement and state management, nothing in this document should be misconstrued to indicate that the radar system 104 and the radar manager 106 cannot also be configured for gesture recognition.
[0044] The IMU 108 can be any of a variety of devices configured to measure movement, which is here defined to include specific force, angular rate, orientation, vibrations, acceleration, velocity, and position, including pitch, roll, and yaw for each of three axes (e.g., X, Y, and Z). The IMU 108 can be one or multiple devices within the UE 102, such as an accelerometer, gyroscope, and/or magnetometer.
[0045] The movement manager 110 is configured to determine, based on inertial data from the IMU 108, movements of the UE 102. Example movements include the UE 102 being lifted (e.g., picked up), oriented toward or away from the user 120, and vibrations. Example movements can indicate cessation of physical contact by the user 120 of the UE 102, placement of the UE 102 on a non-living object (e.g., a table, car console, couch arm, pillow, floor, docking station), and placement of the UE 102 within an enclosed container, e.g., a pocket, bag, or purse.
[0046] These movements can indicate a user's potential engagement, disengagement, or maintained engagement with the UE 102. For example, the movement of the UE 102 may indicate that the user equipment is moving or orienting toward or is being moved/oriented away from the user 120, is moving too rapidly or changing movement too rapidly to be interacted with for many likely types of user engagement, is being held by the user 120 (via natural human movements, respiration, heartbeat), or is vibrating due to a mechanical or non-user source (e.g., a vehicle's vibration, ambient sounds shaking the UE 102, music causing the UE 102 to vibrate). Thus, orienting away, which would indicate a potential disengagement with the UE 102, may include an orientation change of the UE 102 such that a prior orientation where the user 120 was likely to have been looking at the display 116, is now unlikely to be doing so. The user 120 typing or reading at one orientation, and then turning the phone over, or sideways, or placing in a pocket, etc., is but one example of a movement indicating an orienting away and thus a potential disengagement. Example movements that may indicate maintained engagement include vibrations indicating that a user is maintaining a hold or placement of the UE 102 or is maintaining their orientation relative to the UE 102 where that orientation previously indicated, or was coincident with, engagement with the UE 102.
[0047] The display 116 can include any suitable display device, such as a touchscreen, a liquid crystal display (LCD), thin film transistor (TFT) LCD, an in-place switching (IPS) LCD, a capacitive touchscreen display, an organic light emitting diode (OLED) display, an active-matrix organic light-emitting diode (AMOLED) display, super AMOLED display, and so forth. As noted, the display 116 can be powered at various levels, such as at full saturation with touch-input powered, reduced saturation without touch-input powered, and with low-saturation and low power (e.g., a gray clock) or no power.
[0048] The state manager 112 manages states of the UE 102, such as power, access, and information states. This management of the UE 102 and its components is performed based on determinations made by the radar manager 106 and the movement manager 110. For example, the state manager 112 can manage powering a component of the authentication system 114, such as by altering the UE 102's display 116 to increase power in anticipation of receiving touch input from the user 120 to input a password, a computer processor to perform calculations used in authentication, or an imaging system to perform image-based facial authentication, radar (e.g., the radar system 104), or other components.
[0049] As noted, this managing of the UE 102 is based on determinations by the radar manager 106 and the movement manager 110, which determine an intent to engage, disengage, or maintain engagement and movement of the UE 102, respectively. The state manager 112 can do so based on these determinations alone or also based on other information, such as a current state, current engagement, applications running and the content shown by these applications, and so forth. Furthermore, while the radar manager 106 may determine a user's intent and the movement manager 110 can determine movement, some of which are determined to indicate a user's intent to engage with the UE 102, the state manager 112, by using both of their determinations, can improve the accuracy, robustness, and/or speed of an overall determination that the user's intent is to engage, disengage, or maintain engagement with the UE 102.
[0050] This use of both determinations, that of the radar manager 106 and the movement manager 110, can be performed together or in stages as part of managing the states of the UE 102, or one of these may alone be used. For example, assume that the UE 102 is at a low-power state for components used to authenticate. The radar manager 106 may determine that the user 120 is intending to authenticate with the UE 102 based on a movement toward or a reach toward the UE 102. In some cases this alone is considered by the state manager 112 to be insufficient for the state manager 112 to cause the UE 102 to be altered to a high-power state. Thus, the state manager 112 can cause some of the authentication components to be powered up to an intermediate state, rather than a high-power state (e.g., the high-power state 504-1 of FIG. 5). For example, in cases where the authentication system 114 uses infrared sensors to perform facial recognition, the state manager 112 can power these sensors and the display 116 to a higher power, in anticipation of authenticating the user, and in the case of the display 116, indicating to the user that the UE 102 is "waking up" and therefore is increasingly responsive. As an additional step, the state manager 112 can wait until the movement manager 110 determines that the user has moved, picked up, lifted, and so forth the UE 102 before fully powering on the authentication components, here the infrared sensors. While not required, the state manager 112 may cause the authentication to be attempted by the components without further input from the user, thereby making authentication seamless for the user 120.
[0051] In some cases, however, the state manager 112 determines to increase power or otherwise prepare the state of the UE 102 responsive to both inertial data and radar data, e.g., the radar manager 106 determining that the user is intending to engage and the movement manager 110 determining that the user is picking up the UE 102.
[0052] Thus, the state manager 112 can wait until a higher level of confidence that the user's intent is to engage by picking up the UE 102, such as an indication by the movement manager 110 that the user has just started to touch the UE 102. In such a case, the state manager 112 may increase power based on just the radar manager 106's determination but may do so to an intermediate-power level of a display or the authentication system 114 or component thereof, instead waiting until the movement manager 110 indicates a touch by the user to fully power these components. As noted, however, the state manager 112 may alter states to higher power levels solely on determination of an intent to engage based on radar data or lower those levels solely on determination of an intent do disengage based on radar data.
[0053] One of many example ways in which the state manager 112 can manage states (e.g., to maintain an authenticated state) of the UE 102 is shown in FIG. 1 at example environments 100-1, 100-2, and 100-3.
[0054] In the environment 100-1, assume that the user 120, while their smartphone is in an authenticated state 122, sits down at a desk, and places their smartphone down on desk. They then, as shown in 100-2, sit back to read a book. Conventional techniques often start a timer, an example of which is shown at 124, and then, after the timer 124 expires without any obvious input from the user, de-authenticates and otherwise alters the states of the device. If, as is common, the time period is five minutes, the UE 102 de-authenticates (e.g., "locks") after five minutes. If the user 120 wishes to access the UE 102, they must re-authenticate. This provides a poor user experience and wastes power, often resulting in reduced battery life, further reducing the user's experience with their user equipment.
[0055] In contrast to the conventional techniques, on expiration of the timer 124, as is shown at 100-3, the UE 102 remains in the authenticated state 122. To maintain the authenticated state 122, the radar system 104 provides the radar field 118, from which radar data is received indicating that the user 120 is either present (which is the case, within arm's reach) or that the user 120 is otherwise passively engaged (such as holding or looking toward the UE 102, which is not the case). The radar manager 106 determines, based on this radar data, that the user 120 is within arm's reach in this case. The radar manager 106 passes this determination to the state manager 112, which in turns maintains the authenticated state 122 even though a potential disengagement (the timer 124 expiring) was previously determined.
[0056] This is but one example of how the techniques and systems enable a seamless user experience for users, which can not only save users time but power and battery life as well.
[0057] Note that in this example the authenticated state 122 is maintained by the state manager 112, and that the power and information states are not shown to be reduced. The power and information states can be maintained or reduced, examples of which are described in detail below.
[0058] Furthermore, in this example the potential disengagement is determined by the state manager 112 based on the timer 124 expiring. Another potential disengagement can instead (or also) be determined based on the placing of the UE 102 on the table. This placing results in the IMU 108 sensing, and then providing inertial data, to the movement manager 110. The movement manager 110 determines, based on this inertial data, that the UE 102 has moved. At this point the movement manager 110 may pass this movement determination to the radar manager 106 (to determine passive engagement) or the state manager 112. After the timer 124 expiring or the movement data indicating movement, the radar manager 106 determines that the user is passively engaged, as noted above.
[0059] Not only can the state manager 112 maintain an authenticated state, the state manager 112 may increase or decrease states of the UE 102. By way of a detailed example of increasing a power state, consider the authentication system 114, shown in FIG. 2. This is but one example, as other authentication systems controllable by the state manager 112 are considered, such as password-entry through a touch-sensitive display, radar authentication using the radar system 104, or a finger-print reader, to name just a few.
[0060] This example of the authentication system 114 is illustrated showing an interior 200 of the UE 102 (shown as a smartphone). In the depicted configuration, the UE 102 includes a radar integrated circuit 202 of the radar system 104, a speaker 204, a front-facing camera 206, a proximity sensor 208, and an ambient light sensor 210. The UE 102 also includes a face-unlock sensor 212, which includes a near-infrared (NIR) flood illuminator 214 and a near-infrared (NIR) dot projector 216, both of which project infrared or near-infrared light on a user. The face-unlock sensor 212 also includes two NIR cameras 218-1 and 218-2, which are positioned on opposite sides of the UE 102. The NIR cameras 218-1 and 218-2 sense the infrared and near-infrared light that is reflected by the user. This reflected near-infrared light can be used to determine facial features and, with these features, determine if the user is authentic based on comparison with previously-stored facial-feature information. The NIR flood illuminator 214, for example, "floods" an environment with NIR light, which provides, on receiving the reflection from the user (and other objects), an image. This image includes, even in low or no ambient light, the face of a user, and thus can be used to determine facial features. The NIR dot projector 216 provides NIR light reflections that can be analyzed to determine depth of objects, including features of a user's face. Thus, a depth map (e.g., a spectrum depth map) for the user can be created (e.g., previously when setting up facial authentication) and a current depth map can be determined and compared to the stored, previously-created depth map. This depth map aids in preventing authentication of a picture or other two-dimensional rendering of a user's face (rather than the person's actual face).
[0061] This mapping of a user's facial features can be stored securely on the UE 102 and, based on a user's preferences, be both secure on the UE 102 and prevented from being made available to external entities.
[0062] The authentication system 114 includes the face-unlock sensor 212, but can also include other components, such as the front-facing camera 206, the proximity sensor 208 and the ambient light sensor 210, as well as processors to analyze the data, memory (which may have multiple power states as well) to store, cache, or buffer the sensor data, and so forth.
[0063] The face-unlock sensor 212 senses IR (infrared) and NIR (near-infrared) data to perform facial recognition, which is one way in which the techniques may authenticate the user and therefore alter an access state (e.g., to unlock the UE 102) as noted in the methods described below. To conserve power, the face-unlock sensor 212 operates in a low-power state (which can also be simply off) when not in use. In particular, the NIR flood illuminator 214 and the NIR dot projector 216 do not radiate in the off-state. However, a warm-up sequence associated with transitioning from a low or no-power state to an intermediate-power state and/or a high-power state can be used for the NIR flood illuminator 214 and the NIR dot projector 216. By increasing a power level of one or both of these components, the latency in authenticating the user can be reduced, sometimes by a half-second or more. Given the tens or even hundreds of times many users authenticate their devices each day, this can save the users time and improve their experience. As noted herein, this time delay is reduced by the radar manager 106 determining that the user is intending to engage with their device based on radar data provided by the radar system 104. This is managed by the state manager 112. In effect, the techniques proactively detect the user's intent to engage and initiate the warm-up sequence. The techniques may do so even prior to the user touching the UE 102, though this is not required. Thus, the techniques enable the NIR flood illuminator 214 and the NIR dot projector 216 to be sufficiently powered to be used in authenticating the user, which reduces time spent by the user waiting for facial recognition to complete.
[0064] Before moving on to other components in the UE 102, consider an aspect of the face-unlock sensor 212. This example component of the authentication system 114 can authenticate a user using facial recognition in as little as ten degrees relative to the plane of the display 116. Thus, the user need not pick up the phone and turn the sensors to their face, such as at an angle of 70 to 110 or 80 to 100 degrees, instead, the authentication system 114, using the face-unlock sensor 212, is configured to authenticate the user before they even pick up the UE 102. This is illustrated in FIG. 3, which shows the user 120, with portions of their face that are used in facial recognition (e.g., their chin, nose, or cheekbones) at an angle 302, which can be as little as ten degrees relative to plane 304 of the display 116. Also shown, the user 120 is authenticated while having their face more than one meter away from the face-unlock sensor 212, shown at facial distance 306. By so doing, the techniques permit nearly seamless and immediate authentication, even with the UE 102 oriented upside-down or at odd angles.
[0065] In more detail, consider FIG. 4, which illustrates an example implementation 400 of the UE 102 (including the radar manager 106, the movement manager 110, and the state manager 112) that can implement techniques for maintaining an authenticated state and other techniques. The UE 102 of FIG. 4 is illustrated with a variety of example devices, including a UE 102-1, a tablet 102-2, a laptop 102-3, a desktop computer 102-4, a computing watch 102-5, computing spectacles 102-6, a gaming system 102-7, a home-automation and control system 102-8, and a microwave 102-9. The UE 102 can also include other devices, such as televisions, entertainment systems, audio systems, automobiles, drones, track pads, drawing pads, netbooks, e-readers, home security systems, and other home appliances. Note that the UE 102 can be wearable, non-wearable but mobile, or relatively immobile (e.g., desktops and appliances).
[0066] Exemplary overall lateral dimensions of the UE 102 can be, for example, approximately eight centimeters by approximately fifteen centimeters. Exemplary footprints of the radar system 104 can be even more limited, such as approximately four millimeters by six millimeters with antennas included. The requirement of such a limited footprint for the radar system 104, which is needed to accommodate the many other desirable features of the UE 102 in such a space-limited package combined with power and processing limitations, can lead to compromises in the accuracy and efficacy of radar gesture detection, at least some of which can be overcome in view of the teachings herein.
[0067] The UE 102 also includes one or more computer processors 402 and one or more computer-readable media 404, which includes memory media and storage media. Applications and/or an operating system (not shown) implemented as computer-readable instructions on the computer-readable media 404 can be executed by the computer processors 402 to provide some or all of the functionalities described herein, such as some or all of the functions of the radar manager 106, the movement manager 110, and the state manager 112 (shown within the computer-readable media 404, though this is not required).
[0068] The UE 102 may also include a network interface 406. The UE 102 can use the network interface 406 for communicating data over wired, wireless, or optical networks. By way of example and not limitation, the network interface 406 may communicate data over a local-area-network (LAN), a wireless local-area-network (WLAN), a personal-area-network (PAN), a wide-area-network (WAN), an intranet, the Internet, a peer-to-peer network, point-to-point network, or a mesh network.
[0069] In aspects, the radar system 104 is implemented at least partially in hardware. Various implementations of the radar system 104 can include a System-on-Chip (SoC), one or more Integrated Circuits (ICs), a processor with embedded processor instructions or configured to access processor instructions stored in memory, hardware with embedded firmware, a printed circuit board with various hardware components, or any combination thereof The radar system 104 operates as a monostatic radar by transmitting and receiving its own radar signals. In some implementations, the radar system 104 may also cooperate with other radar systems 104 that are within an external environment to implement a bistatic radar, a multistatic radar, or a network radar. Constraints or limitations of the UE 102, however, may impact a design of the radar system 104. The UE 102, for example, may have limited power available to operate the radar, limited computational capability, size constraints, layout restrictions, an exterior housing that attenuates or distorts radar signals, and so forth. The radar system 104 includes several features that enable advanced radar functionality and high performance to be realized in the presence of these constraints, as further described below.
[0070] Prior to setting out additional example ways in which the state manager 112 may act, consider FIG. 5, which illustrates the many information, power, and access states in which the UE 102 may operate and which can be managed by the state manager 112.
[0071] FIG. 5 illustrates access, information, and power states in which the UE 102 may operate, each of which can be managed by the described techniques. These example levels and types of device states 500 are shown in three levels of granularity for visual brevity, though many levels of each are contemplated for access state 502, power state 504, and information state 506. The access state 502 is shown with three examples levels of granularity, high-access state 502-1, intermediate-access state 502-2, and low-access state 502-3. Similarly, the power state 504 is shown three examples levels of granularity, high-power state 504-1, intermediate-power state 504-2, and low-power state 504-3. Likewise, the information state 506 is shown three examples levels of granularity, high-information state 506-1, intermediate-information state 506-2, and low-information state 506-3.
[0072] In more detail, the access state 502 is concerned with the access rights available to a user of the device to the data, applications, functions, accounts, or components of the UE 102. This access can be high, sometimes referred to as an "unlocked" state for the UE 102. This high-access level can include simply the applications and functions of the device, or may also include access to various accounts, such as bank accounts, social-media accounts, and so forth that are accessible through the UE 102. Many computing devices, such as the UE 102, require authentication to provide high access, such as the high-access state 502-1.
[0073] Various intermediate levels of access (e.g., 502-2) can be permitted with or without authentication by the UE 102 (e.g., depending on a user preference or an operating system default setting). This intermediate-access state 502-2 permits a user to access some but not all accounts, services, or components of the UE 102. Examples include allowing a user to take pictures but not to access previously-captured pictures. Other examples include allowing the user to answer a telephone call but not access a contact list when making a telephone call. These are but a few of the many intermediate rights that the UE 102 can permit, shown with the intermediate-access state 502-2.
[0074] The authenticated state 122, as noted above, is concerned with access permitted by the UE 102. Thus, a user is authenticated and then access is granted. As noted throughout this document, the techniques and systems described enable greater security, where access to the UE 102 is both easier for a user and more likely that the access granted is to the authenticated user rather than a third party. This authentication state 122 can permit a high or intermediate level of access, such as the high-access state 502-1 or the intermediate-access state 502-2, as noted above, and illustrated in FIG. 5 with a dashed-line box including the high-access state 502-1 and the intermediate-access state 502-2.
[0075] Lastly, the access state 502 can refrain from permitting access, shown as the low-access state 502-3. In this case the device may be on, send notifications like an alarm to wake up a user, and so forth, but not permit access to functions of the UE 102 (or the UE 102 may simply be off, and thus permit no access).
[0076] The power state 504 is shown with three examples levels of granularity, the high-power state 504-1, the intermediate-power state 504-2, and the low-power state 504-3. The power state 504 is concerned with an amount of power to one or more components of the UE 102, such as the radar system 104, the display 116, or other power-consuming components, such as processors, cameras, microphone, voice assistant, touchscreen, sensors, radar, and components that are part of the authentication system 114 (which may include the previous components listed as well). In the context of powering up a component, as well as the power states 504 generally, the terms power, powering up, increasing power, reducing power, and so forth can include, control of a power-management integrated circuit (PMIC); managing power rails extending from the PMIC; opening and closing switches between a power rail, the PMIC, and one or more circuit components (e.g., the mentioned NIR components, cameras, displays, and radar); and providing a supply voltage to accurately and safely operate a component, which may include ramping or distributing an applied voltage or managing current in-rush.
[0077] Regarding the radar system 104, the power state 504 can be reduced by collecting radar data at different duty cycles (e.g., lower frequencies may use less power and higher frequencies may use more power), turning various components off when the components are not active, or adjusting a power amplification level. By so doing, the radar system 104 may use approximately 90 mW of power at the high-power state 504-1, 30 to 60 mW at the intermediate-power state 504-2, or less than 30 mW at the low-power state 504-3 (e.g., the radar system 104 can operate from 2 to 20 mW while still providing some usable radar data, such as user presence). Each of these levels of power usage permit different resolutions and distance. Additional details regarding power management of the radar system 104 (and the UE 102) are described with reference to FIG. 6-1.
[0078] In the context of altering states noted above, the state manager 112, based on the determinations by the radar manager 106 and the movement manager 110, may increase or decrease power to various components of the UE 102.
[0079] For example, the state manager 112 can alter the power of the authentication system 114 or the display 116 from a lower-power state (e.g., the low-power state 504-3 to the intermediate-power state 504-2 or either of these to the high-power state 504-1). By so doing, the UE 102 may more-quickly or more-easily engage with a user or authenticate the user. Thus, the state manager 112 may alter the power-state 504 to be a higher or lower power than is currently the case for that system of the UE 102 or for particular power-consuming entities associated with the UE 102. Example components are described further as part of FIG. 2 above, including powering up or down the face-unlock sensor 212 and its components, the NIR flood illuminator 214 and the NIR dot projector 216, as well as the NIR cameras 218-1 and 218-2, reducing power to these components, a display, microphone, touch-input sensor, and so forth.
[0080] The third example state of the UE 102 is the information state 506, which is illustrated with the high-information state 506-1, the intermediate-information state 506-2, and the low-information state 506-3. In more detail, the information state 506 is concerned with an amount of information provided to a user, e.g., the user 120 of FIG. 1. In the context of notifications, the high-information state 506-1 provides a highest level of information, and generally assumes that the UE 102 is unlocked or otherwise authenticated, or has a user preference for providing high levels of information even without authentication. Examples include, for the high-information state 506-1, showing a caller's name, number, and even associated image when a call is received. Similarly, when a text or email is received, or other type of message, the content is automatically presented through the display 116 or audio speakers, a peripheral, and so forth. This assumes a high-level of engagement, though a user's preferences can determine what engagement is required. Here it is assumed that there is some correlation between the user's engagement and the amount of information provided, and therefore, the techniques, by determining engagement, can tailor the information presented to that determination. Examples of reduced information, e.g., the intermediate-information state 506-2, include presenting a ring tone when a call is received but not the caller's name/identification, indicating that text message or email has been received but only the subject line, or only the address, or part of the content in the body but not all of it, and so forth. The low-information state 506-3 presents little to no information that is personally associated with the user 120, but can include information that is generic or widely considered common knowledge or non-sensitive, such as the display 116 showing a current date, time, weather condition, battery-power status, or that the UE 102 is on. Other examples of the low-information state 506-3 include a blank or black screen when a text message is received with an audible "ping" indicating only that a message has been received, or a ring tone for a call, but not the name, number, or other information about the caller.
[0081] FIG. 6-1 illustrates an example implementation 600 of the radar system 104. In the example 600, the radar system 104 includes at least one of each of the following components: a communication interface 602, an antenna array 604, a transceiver 606, a processor 608, and a system media 610 (e.g., one or more computer-readable storage media). The processor 608 can be implemented as a digital signal processor, a controller, an application processor, another processor (e.g., the computer processors 402 of the UE 102) or some combination thereof. The system media 610, which may be included within, or be separate from, the computer-readable media 404 of the UE 102, includes one or more of the following modules: an attenuation mitigator 614, a digital beamformer 616, an angle estimator 618, or a power-management module 620. These modules can compensate for, or mitigate the effects of, integrating the radar system 104 within the UE 102, thereby enabling the radar system 104 to recognize small or complex gestures, distinguish between different orientations of the user (e.g., "reach"), continuously monitor an external environment, or realize a target false-alarm rate. With these features, the radar system 104 can be implemented within a variety of different devices, such as the devices illustrated in FIG. 4.
[0082] Using the communication interface 602, the radar system 104 can provide radar data to the radar manager 106. The communication interface 602 may be a wireless or wired interface based on the radar system 104 being implemented separate from, or integrated within, the UE 102. Depending on the application, the radar data may include raw or minimally processed data, in-phase and quadrature (I/Q) data, range-Doppler data, processed data including target location information (e.g., range, azimuth, elevation), clutter map data, and so forth. Generally, the radar data contains information that is usable by the radar manager 106 for providing a user's intent to engage, disengage, or maintain engagement to the state manager 112.
[0083] The antenna array 604 includes at least one transmitting antenna element (not shown) and at least two receiving antenna elements (as shown in FIG. 7). In some cases, the antenna array 604 may include multiple transmitting antenna elements to implement a multiple-input multiple-output (MIMO) radar capable of transmitting multiple distinct waveforms at a time (e.g., a different waveform per transmitting antenna element). The use of multiple waveforms can increase a measurement accuracy of the radar system 104. The receiving antenna elements can be positioned in a one-dimensional shape (e.g., a line) or a two-dimensional shape for implementations that include three or more receiving antenna elements. The one-dimensional shape enables the radar system 104 to measure one angular dimension (e.g., an azimuth or an elevation) while the two-dimensional shape enables two angular dimensions to be measured (e.g., both azimuth and elevation). Example two-dimensional arrangements of the receiving antenna elements are further described with respect to FIG. 7.
[0084] FIG. 6-2 illustrates an example transceiver 606 and processor 608. The transceiver 606 includes multiple components that can be individually turned on or off via the power-management module 620 in accordance with an operational state of the radar system 104. Note that the power-management module 620 can be separate, integrated with, or under the control of the state manager 112, such as in cases where the state manager 112 is powering up or down components (e.g., the authentication system 114) used to authenticate a user. The transceiver 606 is shown to include at least one of each of the following components: an active component 622, a voltage-controlled oscillator (VCO) and voltage-controlled buffer 624, a multiplexer 626, an analog-to-digital converter (ADC) 628, a phase lock loop (PLL) 630, and a crystal oscillator 632. If turned on, each of these components consume power, even if the radar system 104 is not actively using these components to transmit or receive radar signals. The active component 622, for example, can include an amplifier or filter that is coupled to a supply voltage. The VCO 624 generates a frequency-modulated radar signal based on a control voltage that is provided by the PLL 630. The crystal oscillator 632 generates a reference signal for signal generation, frequency conversion (e.g., upconversion or downconversion), or timing operations within the radar system 104. By turning these components on or off, the power-management module 620 enables the radar system 104 to quickly switch between active and inactive operational states and conserve power during various inactive time periods. These inactive time periods may be on the order of microseconds (.mu.s), milliseconds (ms), or seconds (s).
[0085] The processor 608 is shown to include multiple processors that consume different amounts of power, such as a low-power processor 608-1 and a high-power processor 608-2. As an example, the low-power processor 608-1 can include a processor that is embedded within the radar system 104 and the high-power processor can include the computer processors 402 or some other processor that is external to the radar system 104. The differences in power consumption can result from different amounts of available memory or computational ability. For instance, the low-power processor 608-1 may utilize less memory, perform fewer computations, or utilize simpler algorithms relative to the high-power processor 608-2. Despite these limitations, the low-power processor 608-1 can process data for less-complex radar-based applications, such as proximity detection or motion detection (based on radar data rather than inertial data). The high-power processor 608-2, in contrast, may utilize a large amount of memory, perform a large amount of computations, or execute complex signal processing, tracking, or machine-learning algorithms. The high-power processor 608-2 may process data for high-profile radar-based applications, such as gesture recognition, facial recognition (for the authentication system 114), and provide accurate, high-resolution data through the resolution of angular ambiguities or distinguishing of multiple users and features thereof.
[0086] To conserve power, the power-management module 620 can control whether the low-power processor 608-1 or the high-power processor 608-2 are used to process the radar data. In some cases, the low-power processor 608-1 can perform a portion of the analysis and pass data onto the high-power processor 608-2. Example data may include a clutter map, raw or minimally processed radar data (e.g., in-phase and quadrature data or range-Doppler data), or digital beamforming data. The low-power processor 608-1 may also perform some low-level analysis to determine whether there is anything of interest in the environment for the high-power processor 608-2 to analyze. In this way, power can be conserved by limiting operation of the high-power processor 608-2 while utilizing the high-power processor 608-2 for situations in which high-fidelity or accurate radar data is requested by the radar-based application. Other factors that can impact power consumption within the radar system 104 are further described with respect to FIG. 6-1.
[0087] These and other capabilities and configurations, as well as ways in which entities of FIGS. 1, 2, 4, and 6-9 act and interact, are set forth in greater detail below. These entities may be further divided, combined, and so on. The environment 100 of FIG. 1 and the detailed illustrations of FIG. 2 through FIG. 9 illustrate some of many possible environments and devices capable of employing the described techniques. FIGS. 6-9 describe additional details and features of the radar system 104. In FIGS. 6-9, the radar system 104 is described in the context of the UE 102, but as noted above, the applicability of the features and advantages of the described systems and techniques are not necessarily so limited, and other embodiments involving other types of electronic devices may also be within the scope of the present teachings.
[0088] FIG. 7 illustrates example arrangements 700 of receiving antenna elements 702. If the antenna array 604 includes at least four receiving antenna elements 702, for example, the receiving antenna elements 702 can be arranged in a rectangular arrangement 704-1 as depicted in the middle of FIG. 7. Alternatively, a triangular arrangement 704-2 or an L-shape arrangement 704-3 may be used if the antenna array 604 includes at least three receiving antenna elements 702.
[0089] Due to a size or layout constraint of the UE 102, an element spacing between the receiving antenna elements 702 or a quantity of the receiving antenna elements 702 may not be ideal for the angles at which the radar system 104 is to monitor. In particular, the element spacing may cause angular ambiguities to be present that make it challenging for conventional radars to estimate an angular position of a target. Conventional radars may therefore limit a field of view (e.g., angles that are to be monitored) to avoid an ambiguous zone, which has the angular ambiguities, and thereby reduce false detections. For example, conventional radars may limit the field of view to angles between approximately -45 degrees to 45 degrees to avoid angular ambiguities that occur using a wavelength of 8 millimeters (mm) and an element spacing of 6.5 mm (e.g., the element spacing being 90% of the wavelength). Consequently, the conventional radar may be unable to detect targets that are beyond the 45-degree limits of the field of view. In contrast, the radar system 104 includes the digital beamformer 616 and the angle estimator 618, which resolve the angular ambiguities and enable the radar system 104 to monitor angles beyond the 45-degree limit, such as angles between approximately -90 degrees to 90 degrees, or up to approximately -180 degrees and 180 degrees. These angular ranges can be applied across one or more directions (e g., azimuth and/or elevation). Accordingly, the radar system 104 can realize low false-alarm rates for a variety of different antenna array designs, including element spacings that are less than, greater than, or equal to half a center wavelength of the radar signal.
[0090] Using the antenna array 604, the radar system 104 can form beams that are steered or un-steered, wide or narrow, or shaped (e.g., as a hemisphere, cube, fan, cone, or cylinder). As an example, the one or more transmitting antenna elements (not shown) may have an un-steered omnidirectional radiation pattern or may be able to produce a wide beam, such as the wide transmit beam 706. Either of these techniques enable the radar system 104 to illuminate a large volume of space. To achieve target angular accuracies and angular resolutions, however, the receiving antenna elements 702 and the digital beamformer 616 can be used to generate thousands of narrow and steered beams (e.g., 3000 beams, 7000 beams, or 9000 beams), such as the narrow receive beam 708. In this way, the radar system 104 can efficiently monitor the external environment and accurately determine arrival angles of reflections within the external environment.
[0091] Returning to FIG. 6-1, the transceiver 606 includes circuitry and logic for transmitting and receiving radar signals via the antenna array 604. Components of the transceiver 606 can include amplifiers, mixers, switches, analog-to-digital converters, filters, and so forth for conditioning the radar signals. The transceiver 606 can also include logic to perform in-phase/quadrature (I/Q) operations, such as modulation or demodulation. The transceiver 606 can be configured for continuous wave radar operations or pulsed radar operations. A variety of modulations can be used to produce the radar signals, including linear frequency modulations, triangular frequency modulations, stepped frequency modulations, or phase modulations.
[0092] The transceiver 606 can generate radar signals within a range of frequencies (e.g., a frequency spectrum), such as between 1 gigahertz (GHz) and 400 GHz, between 4 GHz and 100 GHz, or between 57 GHz and 63 GHz. The frequency spectrum can be divided into multiple sub-spectra that have a similar bandwidth or different bandwidths. The bandwidths can be on the order of 500 megahertz (MHz), 1 GHz, 2 GHz, and so forth. As an example, different frequency sub-spectra may include frequencies between approximately 57 GHz and 59 GHz, 59 GHz and 61 GHz, or 61 GHz and 63 GHz. Multiple frequency sub-spectra that have a same bandwidth and may be contiguous or non-contiguous may also be chosen for coherence. The multiple frequency sub-spectra can be transmitted simultaneously or separated in time using a single radar signal or multiple radar signals. The contiguous frequency sub-spectra enable the radar signal to have a wider bandwidth while the non-contiguous frequency sub-spectra can further emphasize amplitude and phase differences that enable the angle estimator 618 to resolve angular ambiguities. The attenuation mitigator 614 or the angle estimator 618 may cause the transceiver 606 to utilize one or more frequency sub-spectra to improve performance of the radar system 104, as further described with respect to FIGS. 8 and 9. Some embodiments of the techniques are particularly advantageous, such as when the UE 102 is a handheld smartphone, the radar signals are in the 57 Ghz-64 Ghz band, a peak effective isotropic radiated power (EIRP) is in the range of 10 dBm-20 dBm (10 mW-100 mW), and an average power-spectral density is about 13 dBm/MHz, which has been found to suitably address radiation health and co-existence issues while also providing a nicely-sized "bubble" of radar detection (e.g., at least one meter and often up to or exceeding two meters in extent) near-around the smartphone and the user within which the described methods for authentication management through IMU and radar provided particularly good time-saving convenience while conserving power.
[0093] A power-management module 620 manages power usage to balance performance and power consumption. For example, the power-management module 620 communicates with the radar manager 106 to cause the radar system 104 to collect data using a predefined radar-power state. Each predefined radar-power state can be associated with a particular framing structure, a particular transmit power level, or particular hardware (e.g., the low-power processor 608-1 or the high-power processor 608-2 of FIG. 6-2). Adjusting one or more of these affects the radar system's 104 power consumption. Reducing power consumption, however, affects performance, such as a gesture-frame update rate and response delay, which are described below.
[0094] FIG. 6-3 illustrates an example relationship between power consumption, a gesture-frame update rate 634, and a response delay. In graph 636, radar-power states 638-1, 638-2, and 638-3 are associated with different levels of power consumption and different gesture-frame update rates 634. The gesture-frame update rate 634 represents how often the radar system 104 actively monitors the external environment by transmitting and receiving one or more radar signals. Generally speaking, the power consumption is proportional to the gesture-frame update rate 634. As such, higher gesture-frame update rates 634 result in larger amounts of power being consumed by the radar system 104.
[0095] In graph 636, the radar-power state 638-1 utilizes a smallest amount of power whereas the radar-power state 638-3 consumes a largest amount of power. As an example, the radar-power state 638-1 consumes power on the order of a few milliwatts (mW) (e.g., between approximately 2 mW and 4 mW) whereas the radar-power state 638-3 consumes power on the order of several milliwatts (e.g., between approximately 6 mW and 20 mW). In terms of the gesture-frame update rate 634, the radar-power state 638-1 uses an update rate that is on the order of a few hertz (e.g., approximately 1 Hz or less than 5 Hz) while the radar-power state 638-3 uses a gesture-frame update rate 634 that is on the order of tens of hertz (e.g., approximately 20 Hz or greater than 10 Hz).
[0096] Graph 640 depicts a relationship between the response delay and the gesture-frame update rate 634 for the different radar-power states 638-1 to 638-3. Generally speaking, the response delay is inversely-proportional to both the gesture-frame update rate 634 and the power consumption. In particular, the response delay exponentially decreases while the gesture-frame update rate 634 increases. The response delay associated with the radar-power state 638-1 may be on the order of hundreds of milliseconds (ms) (e.g., 1000 ms or more than 200 ms) while the response delay associated with the radar-power state 638-3 may be on the order of several milliseconds (e.g., 50 ms or less than 100 ms). For the radar-power state 638-2, the power consumption, gesture-frame update rate 634, and response delay are between that of the radar-power state 638-1 and the radar-power state 638-3. For instance, the radar-power state's 638-2 power consumption is approximately 5 mW, the gesture-frame update rate is approximately 8 Hz, and the response delay is between approximately 100 ms and 200 ms.
[0097] Instead of operating at either the radar-power state 638-1 or the radar-power state 638-3, the power-management module 620 dynamically switches between the radar-power states 638-1, 638-2, and 638-3 (and sub-states between each of these radar-power states 638) such that the response delay and the power consumption are managed together based on the activity within the environment. As an example, the power-management module 620 activates the radar-power state 638-1 to monitor the external environment or detect an approaching user. Later in time, the power-management module 620 activates the radar-power state 638-3 if the radar system 104 determines the user is showing an intent to engage or may be starting to do so, or starting to perform a gesture. Different triggers may cause the power-management module 620 to switch between the different radar-power states 638-1 through 638-3. Example triggers include motion or the lack of motion, appearance or disappearance of the user, the user moving into or out of a designated region (e.g., a region defined by range, azimuth, or elevation), a change in velocity of a motion associated with the user, an intent to engage determined by the radar manager 106 (e.g., a "reach" though some intents to engage require additional power, such as facial feature tracking), or a change in reflected signal strength (e.g., due to changes in radar cross section). In general, the triggers that indicate a lower probability of the user interacting with the UE 102 or a preference to collect data using a longer response delay may cause the radar-power state 638-1 to be activated to conserve power.
[0098] In general, the power-management module 620 determines when and how power can be conserved, and incrementally adjusts power consumption to enable the radar system 104 to operate within power limitations of the UE 102. In some cases, the power-management module 620 may monitor an amount of available power remaining and adjust operations of the radar system 104 accordingly (e.g., due to a low battery). For example, if the remaining amount of power is low, the power-management module 620 may continue operating in the radar-power state 638-1 instead of switching to either of the radar-power states 638-2 or 638-3.
[0099] Each power state 638-1 to 638-3 can be associated with a particular framing structure. The framing structure specifies a configuration, scheduling, and signal characteristics associated with the transmission and reception of the radar signals. In general, the framing structure is set up such that the appropriate radar data can be collected based on the external environment. The framing structure can be customized to facilitate collection of different types of radar data for different applications (e.g., proximity detection, feature recognition, or gesture recognition). During inactive times throughout each level of the framing structure, the power-management module 620 can turn off the components within the transceiver 606 in FIG. 6-2 to conserve power. An example framing structure is further described with respect to FIG. 6-4.
[0100] FIG. 6-4 illustrates an example framing structure 642. In the depicted configuration, the framing structure 642 includes three different types of frames. At a top level, the framing structure 642 includes a sequence of gesture frames 644, which can be in the active state or the inactive state. Generally speaking, the active state consumes a larger amount of power relative to the inactive state. At an intermediate level, the framing structure 642 includes a sequence of feature frames (FF) 646, which can similarly be in the active state or the inactive state. Different types of feature frames include a pulse-mode feature frame 648 (shown at the bottom-left of FIG. 6-4) and a burst-mode feature frame 650 (shown at the bottom-right of FIG. 6-4). At a low level, the framing structure 642 includes a sequence of radar frames (RF) 652, which can also be in the active state or the inactive state.
[0101] The radar system 104 transmits and receives a radar signal during an active radar frame (RF) 652. In some situations, the radar frames 652 are individually analyzed for basic radar operations, such as search and track, clutter-map generation, user location determination, and so forth. Radar data collected during each active radar frame 652 can be saved to a buffer after completion of the radar frame 652 or provided directly to the processor 608 of FIG. 6-1.
[0102] 100801 The radar system 104 analyzes the radar data across multiple radar frames 652 (e.g., across a group of radar frames 652 associated with an active feature frame 646) to identify a particular feature associated with one or more gestures. Example types of features include a particular type of motion, a motion associated with a particular appendage (e.g., a hand or individual fingers), and a feature associated with different portions of the gesture. To recognize a gesture performed by the user 120 during an active gesture frame 644, the radar system 104 analyzes the radar data associated with one or more active feature frames 646.
[0103] Depending upon the type of gesture, a duration of the gesture frame 644 may be on the order of milliseconds or seconds (e.g., between approximately 10 ms and 10 s). After the active gesture frames 644 occur, the radar system 104 is inactive, as shown by inactive gesture frames 644-3 and 644-4. A duration of the inactive gesture frames 644 is characterized by a deep sleep time 654, which may be on the order of tens of milliseconds or more (e.g., greater than 50 ms). In an example implementation, the radar system 104 can turn off all of the components within the transceiver 606 to conserve power during the deep sleep time 654.
[0104] In the depicted framing structure 642, each gesture frame 644 includes K feature frames 646, where K is a positive integer. If the gesture frame 644 is in the inactive state, all of the feature frames 646 associated with that gesture frame 644 are also in the inactive state. In contrast, an active gesture frame 644 includes J active feature frames 646 and K-J inactive feature frames 646, where J is a positive integer that is less than or equal to K. A quantity of feature frames 646 can be based on a complexity of the gesture and may include a few to a hundred feature frames 646 (e.g., K may equal 2, 10, 30, 60, or 100). A duration of each feature frame 646 may be on the order of milliseconds (e.g., between approximately 1 ms and 50 ms).
[0105] To conserve power, the active feature frames 646-1 to 646-J occur prior to the inactive feature frames 646-(J+1) to 646-K. A duration of the inactive feature frames 646-(J+1) to 646-K is characterized by a sleep time 656. In this way, the inactive feature frames 646-(J+1) to 646-K are consecutively executed such that the radar system 104 can be in a powered-down state for a longer duration relative to other techniques that interleave the inactive feature frames 646-(J+1) to 646-K with the active feature frames 646-1 to 646-J. Generally speaking, increasing a duration of the sleep time 656 enables the radar system 104 to turn off components within the transceiver 606 that require longer start-up times.
[0106] Each feature frame 646 includes L radar frames 652, where L is a positive integer that may or may not be equal to J or K. In some implementations, a quantity of radar frames 652 may vary across different feature frames 646 and may comprise a few frames or hundreds of frames (e.g., L may equal 5, 15, 30, 100, or 500). A duration of a radar frame 652 may be on the order of tens or thousands of microseconds (e.g., between approximately 30 .mu.s and 5 ms). The radar frames 652 within a particular feature frame 646 can be customized for a predetermined detection range, range resolution, or Doppler sensitivity, which facilitates detection of a particular feature and gesture. For example, the radar frames 652 may utilize a particular type of modulation, bandwidth, frequency, transmit power, or timing. If the feature frame 646 is in the inactive state, all of the radar frames 652 associated with that feature frame 646 are also in the inactive state.
[0107] The pulse-mode feature frame 648 and the burst-mode feature frame 650 include different sequences of radar frames 652. Generally speaking, the radar frames 652 within an active pulse-mode feature frame 648 transmit pulses that are separated in time by a predetermined amount. In contrast, the radar frames 652 within an active burst-mode feature frame 650 transmit pulses continuously across a portion of the burst-mode feature frame 650 (e.g., the pulses are not separated by a predetermined amount of time).
[0108] Within each active pulse-mode feature frame 648, the sequence of radar frames 652 alternates between the active state and the inactive state. Each active radar frame 652 transmits a radar signal (e.g., chirp), which is illustrated by a triangle. A duration of the radar signal is characterized by an active time 658. During the active time 658, the components within the transceiver 606 are powered-on. During a short-idle time 660, which includes the remaining time within the active radar frame 652 and a duration of the following inactive radar frame 652, the radar system 104 conserves power by turning off components within the transceiver 606 that have a start-up time within a duration of the short-idle time 660.
[0109] An active burst-mode feature frame 650 includes M active radar frames 652 and L-M inactive radar frames 652, where M is a positive integer that is less than or equal to L. To conserve power, the active radar frames 652-1 to 652-M occur prior to the inactive radar frames 652-(M+1) to 652-L. A duration of the inactive radar frames 652-(M+1) to 652-L is characterized by a long-idle time 662. By grouping the inactive radar frames 652-(M+1) to 652-L together, the radar system 104 can be in a powered-down state for a longer duration relative to the short-idle time 660 that occurs during the pulse-mode feature frame 648. Additionally, the power management module 620 can turn off additional components within the transceiver 606 that have start-up times that are longer than the short-idle time 660 and shorter that the long-idle time 662.
[0110] Each active radar frame 652 within an active burst-mode feature frame 650 transmits a portion of a radar signal. In this example, the active radar frames 652-1 to 652-M alternate between transmitting a portion of the radar signal that increases in frequency and a portion of the radar signal that decreases in frequency.
[0111] The framing structure 642 enables power to be conserved through adjustable duty cycles within each frame type. A first duty cycle 664 is based on a quantity of active feature frames 646 (J) relative to a total quantity of feature frames 646 (K). A second duty cycle 665 is based on a quantity of active radar frames 652 (e.g., L/2 or M) relative to a total quantity of radar frames 652 (L). A third duty cycle 668 is based on a duration of the radar signal relative to a duration of a radar frame 652.
[0112] Consider an example framing structure 642 for the power state 638-1 that consumes approximately 2 mW of power and has a gesture-frame update rate 634 between approximately 1 Hz and 4 Hz. In this example, the framing structure 642 includes a gesture frame 644 with a duration between approximately 250 ms and 1 second. The gesture frame 644 includes thirty-one pulse-mode feature frames 648 (e.g., L is equal to 31). One of the thirty-one pulse-mode feature frames 648 is in the active state. This results in the duty cycle 664 being approximately equal to 3.2%. A duration of each pulse-mode feature frame 648 is between approximately 8 ms and 32 ms. Each pulse-mode feature frame 648 is composed of eight radar frames 652. Within the active pulse-mode feature frame 648, all eight radar frames 652 are in the active state. This results in the duty cycle 665 being equal to 100%. A duration of each radar frame 652 is between approximately 1 ms and 4 ms. An active time 658 within each of the active radar frames 652 is between approximately 32 .mu.s and 128 .mu.s. As such, the resulting duty cycle 668 is approximately 3.2%. This example framing structure 642 has been found to yield good performance results. These good performance results are in terms of good gesture recognition and presence detection while also yielding good power efficiency results in the application context of a handheld smartphone in a low-power state (e.g., low-power state 504-3).
[0113] Based on the framing structure 642, the power management module 620 can determine a time for which the radar system 104 is not actively collecting radar data. Based on this inactive time period, the power management module 620 can conserve power by adjusting an operational state of the radar system 104 and turning off one or more components of the transceiver 606, as further described below.
[0114] As noted, the power-management module 620 can conserve power by turning off one or more components within the transceiver 606 (e.g., a voltage-controlled oscillator, a multiplexer, an analog-to-digital converter, a phase lock loop, or a crystal oscillator) during inactive time periods. These inactive time periods occur if the radar system 104 is not actively transmitting or receiving radar signals, which may be on the order of microseconds (.mu.s), milliseconds (ms), or seconds (s). Further, the power-management module 620 can modify transmission power of the radar signals by adjusting an amount of amplification provided by a signal amplifier. Additionally, the power-management module 620 can control the use of different hardware components within the radar system 104 to conserve power. If the processor 608 comprises a lower-power processor and a higher-power processor (e.g., processors with different amounts of memory and computational capability), for example, the power-management module 620 can switch between utilizing the lower-power processor for low-level analysis (e.g., detecting motion, determining a location of a user, or monitoring the environment) and the higher-power processor for situations in which high-fidelity or accurate radar data is requested by the radar manager 106 (e.g., for implementing the high-power state 504-1 of the authentication system 114 for authenticating a user using radar data).
[0115] In addition to the internal power-saving techniques described above, the power-management module 620 can also conserve power within the UE 102 by activating or deactivating other external components or sensors that are within the UE 102, either alone or at a command of the authentication system 114. These external components may include speakers, a camera sensor, a global positioning system, a wireless communication transceiver, a display, a gyroscope, or an accelerometer. Because the radar system 104 can monitor the environment using a small amount of power, the power-management module 620 can appropriately turn these external components on or off based on where the user is located or what the user is doing. In this way, the UE 102 can seamlessly respond to the user and conserve power without the use of automatic shut-off timers or the user physically touching or verbally controlling the UE 102.
[0116] FIG. 8 illustrates additional details of an example implementation 800 of the radar system 104 within the UE 102. In the example 800, the antenna array 604 is positioned underneath an exterior housing of the UE 102, such as a glass cover or an external case. Depending on its material properties, the exterior housing may act as an attenuator 802, which attenuates or distorts radar signals that are transmitted and received by the radar system 104. The attenuator 802 may include different types of glass or plastics, some of which may be found within display screens, exterior housings, or other components of the UE 102 and have a dielectric constant (e.g., relative permittivity) between approximately four and ten. Accordingly, the attenuator 802 is opaque or semi-transparent to a radar signal 806 and may cause a portion of a transmitted or received radar signal 806 to be reflected (as shown by a reflected portion 804). For conventional radars, the attenuator 802 may decrease an effective range that can be monitored, prevent small targets from being detected, or reduce overall accuracy.
[0117] Assuming a transmit power of the radar system 104 is limited, and re-designing the exterior housing is not desirable, one or more attenuation-dependent properties of the radar signal 806 (e.g., a frequency sub-spectrum 808 or a steering angle 810) or attenuation-dependent characteristics of the attenuator 802 (e.g., a distance 812 between the attenuator 802 and the radar system 104 or a thickness 814 of the attenuator 802) are adjusted to mitigate the effects of the attenuator 802. Some of these characteristics can be set during manufacturing or adjusted by the attenuation mitigator 614 during operation of the radar system 104. The attenuation mitigator 614, for example, can cause the transceiver 606 to transmit the radar signal 806 using the selected frequency sub-spectrum 808 or the steering angle 810, cause a platform to move the radar system 104 closer or farther from the attenuator 802 to change the distance 812, or prompt the user to apply another attenuator to increase the thickness 814 of the attenuator 802.
[0118] Appropriate adjustments can be made by the attenuation mitigator 614 based on pre-determined characteristics of the attenuator 802 (e.g., characteristics stored in the computer-readable media 404 of the UE 102 or within the system media 610) or by processing returns of the radar signal 806 to measure one or more characteristics of the attenuator 802. Even if some of the attenuation-dependent characteristics are fixed or constrained, the attenuation mitigator 614 can take these limitations into account to balance each parameter and achieve a target radar performance. As a result, the attenuation mitigator 614 enables the radar system 104 to realize enhanced accuracy and larger effective ranges for detecting and tracking the user that is located on an opposite side of the attenuator 802. These techniques provide alternatives to increasing transmit power, which increases power consumption of the radar system 104, or changing material properties of the attenuator 802, which can be difficult and expensive once a device is in production.
[0119] FIG. 9 illustrates an example scheme 900 implemented by the radar system 104. Portions of the scheme 900 may be performed by the processor 608, the computer processors 402, or other hardware circuitry. The scheme 900 can be customized to support different types of electronic devices and radar-based applications (e.g., the radar manager 106), and also enables the radar system 104 to achieve target angular accuracies despite design constraints.
[0120] The transceiver 606 produces raw data 902 based on individual responses of the receiving antenna elements 702 to a received radar signal. The received radar signal may be associated with one or more frequency sub-spectra 904 that were selected by the angle estimator 618 to facilitate angular ambiguity resolution. The frequency sub-spectra 904, for example, may be chosen to reduce a quantity of sidelobes or reduce an amplitude of the sidelobes (e.g., reduce the amplitude by 0.5 dB, 1 dB, or more). A quantity of frequency sub-spectra can be determined based on a target angular accuracy or computational limitations of the radar system 104.
[0121] The raw data 902 contains digital information (e.g., in-phase and quadrature data) for a period of time, different wavenumbers, and multiple channels respectively associated with the receiving antenna elements 702. A Fast-Fourier Transform (FFT) 906 is performed on the raw data 902 to generate pre-processed data 908. The pre-processed data 908 includes digital information across the period of time, for different ranges (e.g., range bins), and for the multiple channels. A Doppler filtering process 910 is performed on the pre-processed data 908 to generate range-Doppler data 912. The Doppler filtering process 910 may comprise another FFT that generates amplitude and phase information for multiple range bins, multiple Doppler frequencies, and for the multiple channels. The digital beamformer 616 produces beamforming data 914 based on the range-Doppler data 912. The beamforming data 914 contains digital information for a set of azimuths and/or elevations, which represents the field of view for which different steering angles or beams are formed by the digital beamformer 616. Although not depicted, the digital beamformer 616 may alternatively generate the beamforming data 914 based on the pre-processed data 908 and the Doppler filtering process 910 may generate the range-Doppler data 912 based on the beamforming data 914. To reduce a quantity of computations, the digital beamformer 616 may process a portion of the range-Doppler data 912 or the pre-processed data 908 based on a range, time, or Doppler frequency interval of interest.
[0122] The digital beamformer 616 can be implemented using a single-look beamformer 916, a multi-look interferometer 918, or a multi-look beamformer 920. In general, the single-look beamformer 916 can be used for deterministic objects (e.g., point-source targets having a single phase center). For non-deterministic targets (e.g., targets having multiple phase centers), the multi-look interferometer 918 or the multi-look beamformer 920 are used to improve accuracies relative to the single-look beamformer 916. Humans are an example of a non-deterministic target and have multiple phase centers 922 that can change based on different aspect angles, as shown at 924-1 and 924-2. Variations in the constructive or destructive interference generated by the multiple phase centers 922 can make it challenging for conventional radar systems to accurately determine angular positions. The multi-look interferometer 918 or the multi-look beamformer 920, however, perform coherent averaging to increase an accuracy of the beamforming data 914. The multi-look interferometer 918 coherently averages two channels to generate phase information that can be used to accurately determine the angular information. The multi-look beamformer 920, on the other hand, can coherently average two or more channels using linear or non-linear beamformers, such as Fourier, Capon, multiple signal classification (MUSIC), or minimum variance distortion less response (MVDR). The increased accuracies provided via the multi-look beamformer 920 or the multi-look interferometer 918 enable the radar system 104 to recognize small gestures or distinguish between multiple portions of the user (e.g., facial features).
[0123] The angle estimator 618 analyzes the beamforming data 914 to estimate one or more angular positions. The angle estimator 618 may utilize signal processing techniques, pattern matching techniques, or machine learning. The angle estimator 618 also resolves angular ambiguities that may result from a design of the radar system 104 or the field of view the radar system 104 monitors. An example angular ambiguity is shown within an amplitude plot 926 (e.g., amplitude response).
[0124] The amplitude plot 926 depicts amplitude differences that can occur for different angular positions of the target and for different steering angles 810. A first amplitude response 928-1 (illustrated with a solid line) is shown for a target positioned at a first angular position 930-1. Likewise, a second amplitude response 928-2 (illustrated with a dotted-line) is shown for the target positioned at a second angular position 930-2. In this example, the differences are considered across angles between -180 degrees and 180 degrees.
[0125] As shown in the amplitude plot 926, an ambiguous zone exists for the two angular positions 930-1 and 930-2. The first amplitude response 928-1 has a highest peak at the first angular position 930-1 and a lesser peak at the second angular position 930-2. While the highest peak corresponds to the actual position of the target, the lesser peak causes the first angular position 930-1 to be ambiguous because it is within some threshold for which conventional radars may be unable to confidently determine whether the target is at the first angular position 930-1 or the second angular position 930-2. In contrast, the second amplitude response 928-2 has a lesser peak at the second angular position 930-2 and a higher peak at the first angular position 930-1. In this case, the lesser peak corresponds to the target's location.
[0126] While conventional radars may be limited to using a highest peak amplitude to determine the angular positions, the angle estimator 618 instead analyzes subtle differences in shapes of the amplitude responses 928-1 and 928-2. Characteristics of the shapes can include, for example, roll-offs, peak or null widths, an angular location of the peaks or nulls, a height or depth of the peaks and nulls, shapes of sidelobes, symmetry within the amplitude response 928-1 or 928-2, or the lack of symmetry within the amplitude response 928-1 or 928-2. Similar shape characteristics can be analyzed in a phase response, which can provide additional information for resolving the angular ambiguity. The angle estimator 618 therefore maps the unique angular signature or pattern to an angular position.
[0127] The angle estimator 618 can include a suite of algorithms or tools that can be selected according to the type of UE 102 (e.g., computational capability or power constraints) or a target angular resolution for the radar manager 106. In some implementations, the angle estimator 618 can include a neural network 932, a convolutional neural network (CNN) 934, or a long short-term memory (LSTM) network 936. The neural network 932 can have various depths or quantities of hidden layers (e.g., three hidden layers, five hidden layers, or ten hidden layers) and can also include different quantities of connections (e.g., the neural network 932 can comprise a fully-connected neural network or a partially-connected neural network). In some cases, the CNN 934 can be used to increase computational speed of the angle estimator 618. The LSTM network 936 can be used to enable the angle estimator 618 to track the target. Using machine-learning techniques, the angle estimator 618 employs non-linear functions to analyze the shape of the amplitude response 928-1 or 928-2 and generate angular probability data 938, which indicates a likelihood that the user or a portion of the user is within an angular bin. The angle estimator 618 may provide the angular probability data 938 for a few angular bins, such as two angular bins to provide probabilities of a target being to the left or right of the UE 102, or for thousands of angular bins (e.g., to provide the angular probability data 938 for a continuous angular measurement).
[0128] Based on the angular probability data 938, a tracker module 940 produces angular position data 942, which identifies an angular location of the target. The tracker module 940 may determine the angular location of the target based on the angular bin that has a highest probability in the angular probability data 938 or based on prediction information (e.g., previously-measured angular position information). The tracker module 940 may also keep track of one or more moving targets to enable the radar system 104 to confidently distinguish or identify the targets. Other data can also be used to determine the angular position, including range, Doppler, velocity, or acceleration. In some cases, the tracker module 940 can include an alpha-beta tracker, a Kalman filter, a multiple hypothesis tracker (MHT), and so forth.
[0129] A quantizer module 944 obtains the angular position data 942 and quantizes the data to produce quantized angular position data 946. The quantization can be performed based on a target angular resolution for the radar manager 106. In some situations, fewer quantization levels can be used such that the quantized angular position data 946 indicates whether the target is to the right or to the left of the UE 102 or identifies a 90-degree quadrant the target is located within. This may be sufficient for some radar-based applications, such as user proximity detection. In other situations, a larger number of quantization levels can be used such that the quantized angular position data 946 indicates an angular position of the target within an accuracy of a fraction of a degree, one degree, five degrees, and so forth. This resolution can be used for higher-resolution radar-based applications, such as gesture recognition, or in implementations of the attention state or the interaction state as described herein. In some implementations, the digital beamformer 616, the angle estimator 618, the tracker module 940, and the quantizer module 944 are together implemented in a single machine-learning module.
[0130] Among the advantages of the described implementations, including implementations in which radar is used to determine a user's intent to engage, disengage, or maintain engagement, and further including implementations in which radar is used to detect user action that is categorized as an indication of a user intent to engage or interact with the electronic device, either of which might alternatively be achievable using the on-device camera that is provided with most modern smartphones, is that the power usage of the radar system is substantially less than the power usage of the camera system, while the propriety of the results can often be better with the radar system than with the camera system. For example, using the radar system 104 described hereinabove, the desired user-intention detection can be achieved at average power ranging from single-digit milliwatts to just a few dozen milliwatts (e.g., 10 mW, 20 mW, 30 mW or 40 mW), even including the processing power for processing the radar vector data to make the determinations. At these low levels of power, it would be readily acceptable to have the radar system 104 enabled at all times. As such, for example, with the smartphone radar system 104 in the always-enabled state, the desired delightful and seamless experience presently described can still be provided for a user that has been sitting across the room from their smartphone for many hours.
[0131] In contrast, the optical cameras provided with most of today's smartphones typically operate at hundreds of milliwatts of power (e.g., an order of magnitude higher than 40 mW, which is 400 mW). At such power rates, optical cameras would be disadvantageous because they would significantly reduce the battery life of most of today's smartphones, so much so as to make it highly impractical, if not prohibitive, to have the optical camera in an always-on state. An additional advantage of the radar system 104 is that the field of view can be quite large, readily enough to detect a user walking up from any direction even when lying flat and face-up on a table (for many typical implementations in which the radar chip is facing outward in the same general direction as the selfie camera) and, furthermore, by virtue of its Doppler processing ability can be highly effective (especially at operating frequencies near 60 GHz) in detecting even relatively subtle movements of moving bodies from the variety of directions.
[0132] Additionally, the radar system 104 can operate in environments in which the performance of the camera system is reduced or restricted. For example, in lower-light environments, the camera system may have a reduced ability to detect shape or movement. In contrast, the radar system 104 performs as well in lower light as in full light. The radar system 104 can also detect presence and gestures through some obstacles. For instance, if the smartphone is in a pocket of a jacket or pair of pants, a camera system cannot detect a user or a gesture. The radar system 104, however, can still detect objects in its field, even through a fabric that would block the camera system. An even further advantage of using a radar system 104 over an onboard video camera system of a smartphone is privacy, because a user can have the advantages of the herein described delightful and seamless experiences while at the same time not needing to be worried that there is a video camera taking video of them for such purposes.
[0133] The entities of FIGS. 1, 2, 4, and 6-9 may be further divided, combined, used along with other sensors or components, and so on. In this way, different implementations of the UE 102, with different configurations of the radar system 104 and the IMU 108, can be used to implement maintaining an authenticated state. The example operating environment 100 of FIG. 1 and the detailed illustrations of FIGS. 2-9 illustrate but some of many possible environments and devices capable of employing the described techniques.
[0134] Example Methods
[0135] This section illustrates example methods, which may operate separately or together in whole or in part. Various example methods are described, each set forth in a subsection for ease of reading; these subsection titles are not intended to limit the interoperability of each of these methods one with the other.
[0136] Authentication Management
[0137] FIG. 10 depicts an example method 1000 for managing authentication through IMU and radar and is one example of managing power states for a user equipment. The method 1000 is shown as a set of blocks that specify operations performed but are not necessarily limited to the order or combinations shown for performing the operations by the respective blocks. Further, any of one or more of the operations may be repeated, combined, reorganized, or linked to provide a wide array of additional and/or alternate methods (e.g., methods 1200 and 1400). In portions of the following discussion, reference may be made to the example operating environment 100 of FIG. 1 or to entities or processes as detailed in other figures, reference to which is made for example only. The techniques are not limited to performance by one entity or multiple entities operating on one device.
[0138] At 1002, an intent to engage of a user is determined, based on radar data and by a user equipment, the intent to engage indicating that the user intends to engage with the user equipment. As noted above, the intent to engage can be indicated by determining that the user 120 is reaching toward the UE 102, looking at the UE 102, or leaning toward or orienting their body toward the UE 102, to name just three examples.
[0139] At 1004, alternatively or in addition to the determination of the intent to engage through the radar data, a movement of the user equipment is determined based on inertial data. This movement can indicate the user's 120 picking up the UE 102, touching the UE 102, and other movements as noted above.
[0140] At 1006, responsive to the determination of the intent to engage and, in some cases, the determination of movement of the user equipment, a power state of a power-consuming component of an authentication system is altered. The power state of the power-consuming component is altered from a first power state to a second power state, the second power state consuming greater power than the first power state. This alteration can be based on solely the intent to engage determined using the radar data or also through the movement determined through the inertial data. Furthermore, the power state of the power-consuming component can be further raised or other components powered based on the movement determination. As noted above, this movement determination may confirm the user's 120 intent to engage, also provide an intent to engage, or otherwise add speed and/or robustness to the determination to add power, resources, and so forth to the authentication system. Note that, in some cases, components of an authentication system remain powered even when a user has not been determined to be intending to engage. In such a case, the techniques act to perform an authentication process responsive to the intent to engage being determined. In such a case latency is reduced even if power is not conserved for that process. The techniques can, however, refrain from using resources not associated with the authentication system, thereby conserving power in other ways.
[0141] The power state to which the power-consuming component of the authentication system is altered may or may not be sufficient to enable the authentication system to perform an authentication process on the user. In some cases the second power state of the power-consuming component is not the high-power state 504-1. In such a case, the second power state is the intermediate-power state 504-2 as noted above. This intermediate-power state 504-2, in some cases, is sufficient for performance of the power-consuming component, such as a camera that includes an intermediate-power state that is still capable of providing sensor data for authentication without fully powering up (e.g., capturing an image of a user in full light rather than in darkness, etc.). Another example is the display 116, which can be powered to accept touch input for a password without powering the display's luminosity to full power. Another case includes the radar system 104, where at a fairly close range of a user's face to the radar system 104, full power is not required to provide sufficiently-accurate facial features to the authentication system 114.
[0142] In some cases, the powering up of the component is an intermediate step, such as a warm-up sequence, that may prepare the component or simply reduce latency by giving the component additional time. In such a case, the state manager 112 can determine not to proceed to high power, such as if an intent to disengage is determined prior to the component being ready to authenticate, the user 120 moving the UE 102 thereby preventing authentication (e.g., into a pocket), and so forth. In some cases, the powering is an intermediate step that is then fully powered responsive to determining that the user 120 has moved the UE 102, illustrated at 1004, and thus to a power sufficient to perform the authentication process. This warm-up sequence powers the component to the intermediate-power state 504-2 and then, after some short period of time, the component is powered sufficient to be used in the authentication process (e.g., to the high-power state 504-1). In such a case, the component is at high power (or nearly so) while in a post-warm-up sequence following the warm-up sequence. For components that consume substantial power if left on when not needed, but also require a noticeable amount of time to increase power to a sufficient level for full functionality, such as some infrared or near-infrared (IR, NIR) sensors, an intermediate-power state during which a warm-up sequence is performed can save substantial power or reduce noticeable and potentially user-experience-damaging latency.
[0143] Example power-consuming components of an authentication system are described above, such as face-unlock sensors 212 of the authentication system 114 of FIG. 1, a touchscreen of the display 116, the radar system 104, and the processor 608 (e.g., high-power processor 608-2). For specific details on the many potential power-consuming components of a facial-recognition system for authentication, see FIG. 2 and its description.
[0144] At 1008, an authentication process is performed by the authentication system. In doing so, the authentication system 114 uses the power-consuming component at the altered power state, such as the second power state or a third, higher-power state. The authentication process is effective to authenticate the user or determine that the user is not authenticated, indicating that access to the UE 102 should not be permitted. As noted, the authentication process can be through facial recognition, finger-print reading, password or other credential entry through a touch or audio interface (e.g., touch-screen data-entry component of the display 116), and so forth. The authentication process compares identifying features of the user or credentials with some secure storage of comparable features or credentials to determine the user's identity as authentic, and thus permitted access to the UE 102. This can be as simple as comparing a six-digit password entered through the display's touch screen, or require greater computations and system complexity, such as determining facial features based on sensor data received from the power-consuming component and comparing the determined facial features to a facial-feature library. While not required, this facial-feature library can be stored local to the UE 102 and created during a facial-feature initialization by the UE 102 with the authentication system 114. Furthermore, this library can be securely stored at the UE 102, such as in the form of an embedding on a secure chip integral with the UE 102. This is one way in which privacy of the user 120 can be maintained.
[0145] Throughout this disclosure examples are described where a computing system (e.g., the UE 102, a client device, a server device, a computer, or other type of computing system) may analyze information (e.g., radar, inertial, and facial-recognition sensor data) associated with a user, such as the just-mentioned facial features at operation 1008. The computing system, however, can be configured to only use the information after the computing system receives explicit permission from the user of the computing system to use the data. For example, in situations where the UE 102 analyzes sensor data for facial features to authenticate the user 120, individual users may be provided with an opportunity to provide input to control whether programs or features of the UE 102 can collect and make use of the data. The individual users may have constant control over what programs can or cannot do with sensor data. In addition, information collected may be pre-treated in one or more ways before it is transferred, stored, or otherwise used, so that personally-identifiable information is removed. For example, before the UE 102 shares sensor data with another device (e.g., to train a model executing at another device), the UE 102 may pre-treat the sensor data to ensure that any user-identifying information or device-identifying information embedded in the data is removed. Thus, the user may have control over whether information is collected about the user and the user's device, and how such information, if collected, may be used by the computing device and/or a remote computing system.
[0146] Returning to the method 1000, at 1010, alternatively or in addition, the power state of a display is altered responsive to determining that the user equipment has moved or is moving. This alteration can be to increase power sufficient to enable a touch-input reception capability of the display or to simply change the visual presentation of the display. One example includes adding luminosity to the display 116 so that, when a user touches the UE 102, the user sees that the UE 102 is aware of the user's intent and thus, presumably, is preparing to engage with the user 120. Similarly, the UE 102 may do so responsive to the intent to engage determined at 1002.
[0147] In some cases, the authentication process is performed for some period of time or iterations without success (e.g., some pre-set number or time period). In such a case, the method 1000 can continue by re-performing the authentication process or continue the process responsive to the determination of the movement at 1004, shown at 1012. This alternative is shown with some of the dashed-line arrows in FIG. 10.
[0148] At 1014, responsive to the authentication process of the user at 1008 (or re-performance at 1012) being successful, the user is authenticated and an access state of the UE 102 is altered. This alteration can increase the access of the UE 102 to high-access state from a low-, no-, or intermediate-access state, and in such a case, the UE 102 is "unlocked." This high-access state (e.g., the high-access state 502-1 of FIG. 5) is not required, however. Some levels of authentication can reserve access, power, or information for subsequent authentication. Examples include authenticating the user for use of some but not all of the applications and/or accounts of the UE 102 (e.g., accounts to purchase music, bank accounts, etc.), and requiring additional authentication for those reserved access accounts and applications. For example, in addition to the high-access state 502-1, the state manager 112 can cause the UE 102 to be placed in the high-information state 506-1. Examples of this alteration to the information state include presenting a last-engaged-with application or webpage, including at a last-engaged-with portion, such as on page four of a ten-page article on a webpage, or half-way into a song or video that reproduces where the user 120 was last engaged or authenticated with the UE 102. The state manager 112 may alter these states quickly and seamlessly, responsive to authentication of the user 120.
[0149] By way of example, consider one implementation that applies the application of method 1000 to scenario 1100 illustrated in FIG. 11. The scenario 1100 includes five portions, each one chronologically following the prior portion. At a first portion of the scenario 1100, shown at scenario portion 1100-1, a user 1102 is not looking at, touching, or otherwise engaged with a smartphone 1104. Assume here that the smartphone 1104 is in low-access, low-power, and low-information states 502-3, 504-3, and 506-3, respectively (e.g., the smartphone 1104 looks off, but has sufficient power to determine an intent to engage). This scenario portion 1100-1 is assumed to be the situation prior to the operation of the method at 1002 in FIG. 10. A second portion is shown at 1100-2, during which the user 1102 turns toward and looks at, but does not touch, the smartphone 1104. At this point, the techniques, at operation 1002, determine, based on radar data, that the user 1102 intends to engage with the smartphone 1104. This intent to engage is determined without use of a reach movement but is instead based on the user 1102 looking toward and orienting their body toward the smartphone 1104. The techniques make this determination through the radar manager 106 at operation 1002, which passes the determination to the state manager 112. Following this, the state manager 112, at operation 1006, alters a power state of a power-consuming component (the face-unlock sensor 212) of the authentication system 114. Note that this is done well before the user reaches toward or picks up the smartphone 1104, reducing latency in causing the authentication system 114 to be ready to authenticate the user.
[0150] Assume also, that over the next half of a second, while the power-consuming component is powering up, the user 1102 moves closer to, and reaches toward the smartphone 1104 (the reach shown with hand 1106). This is shown at a third portion 1100-3. At this point the authentication system 114 performs an authentication process (operation 1008), but assume that the authentication process is unsuccessful for some number of iterations and/or a period of time. The techniques may cease the attempts to authenticate the user 1102, and thereby save power. Here, however, as shown at portion 1100-4, the user 1102 touches the smartphone 1104. This is determined, at operation 1004, to be movement of the smartphone 1104 through inertial data sensed by the IMU 108 of FIG. 1. This movement determination is passed to the state manager 112. Based on this movement, the state manager 112 continues to cause the authentication system 114 to attempt to authenticate the user 1102, as illustrated by operation 1012 of method 1000. Further still, at the operation 1010, and also based on the movement, the state manager 112 illuminates a display 1108 of the smartphone 1104. This illumination, or increasing a power level of the display 1108, can be performed at the scenario portion 1100-2, 1100-3, or 11004, but here is shown responsive to determining the user's 1102 touch of the smartphone 1104 (shown with time and notification information at 1110). By so doing, the user 1102 is given feedback that the smartphone 1104 is aware that they are intending to engage.
[0151] As noted, the state manager 112 causes the authentication system 114 to continue the authentication process and, through these continued attempts, authenticates the user 1102. This is shown at portion 1100-5, resulting in the smartphone 1104 being at different states, high-access, high-power, and high-information states 501-1, 504-1, and 506-1, respectively, with the high-access state 502-1 shown with the display 1108 presenting an unlock icon 1112. These state levels can be raised automatically by the state manager 112, providing a seamless user experience for the user 1102.
[0152] In this example scenario 1100 the inertial data provided by the IMU 108 causes the state manager 112 to ascertain, with a higher level of confidence and therefore justifying the additional power, that the user 1102 intends to engage with the smartphone 1104 and therefore that they want to be authenticated. This is but one example scenario showing how inertial data from an IMU and radar data from a radar system can be used to authenticate a user quickly, easily, and with reduced power consumption.
[0153] Reducing High-Level States
[0154] FIG. 12 depicts an example method 1200 for reducing a high-level state through IMU and radar. The method 1200 is shown as a set of blocks that specify operations performed but are not necessarily limited to the order or combinations shown for performing the operations by the respective blocks. Further, any of one or more of the operations may be repeated, combined, reorganized, or linked to provide a wide array of additional and/or alternate methods, including with other methods set forth in this document (e.g., methods 1000 and 1400). In portions of the following discussion, reference may be made to the example operating environment 100 of FIG. 1 or to entities or processes as detailed in other figures, reference to which is made for example only. The techniques are not limited to performance by one entity or multiple entities operating on one device.
[0155] Optionally, at 1202 and prior to operations 1204 or 1206, an inactivity time period is determined to have expired. In contrast to some other, conventional techniques that rely solely on expiration of a time period, method 1200 may use or refrain from using an inactivity time period to reduce a high-level state for a user equipment. While this inactivity timer is not required, use of a timer, even if a short timer, in some cases saves power. In more detail, an inactivity timer starts when a last user action with a user equipment is received, such as when a last touch to a touch screen or button, audio command, or gesture input was received by the user equipment. Note that while some conventional techniques use a timer solely, and because of this conventional timers often last minutes (e.g., one, three, five, or ten minutes), the method 1200 can use a time period that is relatively short, such as one half, one, three, five, ten, or twenty seconds. By so doing, the likelihood of the user equipment exposing information, making inappropriate access available, and so forth is very low, while use of a short inactivity time period can operate to save some amount of power by refraining from performing operations of 1204 and/or 1206 for the inactivity time period.
[0156] At 1204, a movement is determined, during a high-level state of a user equipment during which a user is interacting or has recently interacted with the user equipment. The movement manager 110 determines this movement based on inertial data received from the IMU 108, which is integral with the UE 102. As shown with the dashed-lined arrow, this operation can optionally be responsive to operation 1206 and/or 1202 (not shown). This determined movement can be one or more of the various movements set forth above, such a movement indicating that the user 120 is picking up the UE 102, walking with, placing down, putting in a pocket or enclosure, or simply touching near to or touching the UE 102. In some cases, the movement manager 110 determines that a movement is or is not sufficient to alter a state of the UE 102, and thus pass to the state manager 112. Examples include those noted above, such as not overcoming a threshold movement, those caused by ambient vibrations, and those that, while movement, are not a sufficient change to an ongoing movement. Thus, the movement manager 110 can determine that the UE 102 is moving as the user 120 walks along with the UE 102, but that movement can be determined not to be a change sufficient to indicate a potential that the user 120 may be disengaging from the UE 102. Another way to look at this is that movement can be based on a change and not simply a current moving of the UE 102. Example changes include moving and then not moving, such as a user walking with the UE 102 and placing it down on a table. While the inertial data from the IMU 108 might not catch the user 120 placing the UE 102 on the table, the determination that the inertial data shows little to no movement when there was movement immediately prior (the user 120 walking with the UE 102) may still be determined as movement at operation 1204 based on this immediately-prior movement.
[0157] In more detail, the techniques can tailor a user equipment's state to the user's engagement. Thus, in some cases the user equipment is in a high-level state (or states) due to the user being highly engaged with the user equipment. For example, the method 1200 may determine prior to operations 1204 or 1206 that the user is interacting with the user equipment. This determination of the user's engagement can be based on prior radar data indicating an intent to engage by the user, based on audio or touch input from the user, a command or input received from the user and through the audio or touch sensor, a successful authentication process, and so forth.
[0158] At 1206, an intent to disengage is determined based on radar data and by the user equipment. The radar manager 106 receives radar data from the radar system 104 and, using this radar data, determines whether the user intends to disengage from the UE 102. This intent to disengage includes the various types set forth above, such as a hand retraction of the user 120 from the UE 102, a facial orientation change relative to the UE 102, the user 120 turning away from or orienting their back to the UE 102, and so forth.
[0159] As shown with the dashed-lined arrow, this operation 1206 can optionally be responsive to operation 1204 (and/or 1202, not shown). In these cases the state manager 112 or the radar manager 106 acts to conserve power by refraining from determining the user's 120 intent to disengage until the movement is determined, and vice-versa for the movement determination at 1204. By so doing, power can be conserved. Thus, the power-management module 620 can be directed by the techniques to keep the radar system 104 at reduced power until the movement is determined at 1204. Once movement is determined, the state manager 112 causes the power-management module 620 to increase power to the radar system 104 in preparation to determine whether the user 120 is acting in a manner indicating an intent to disengage.
[0160] At 1208, the high-level state of the user equipment is reduced to an intermediate-level or low-level state, responsive to the determination of the movement and/or the intent to disengage. In more detail, see an example high-level state 1208-1, which can be one or multiple states involving access, power, or information, e.g., those illustrated in FIG. 5 (the high-access state 502-1, the high-power 504-1, or the high-information state 506-1). The state manager 112, responsive to determination of movement or an intent to disengage, or both, determines to reduce one or more of the states of the UE 102. This is illustrated in FIG. 12 with arrows showing a reduction from the high-level 1208-1 to an intermediate level 1208-2 or a low level 1208-3. These are but two of various granularities of power, access, and information. As illustrated in FIG. 5, the intermediate level 1208-2 and the low level 1208-3 include the intermediate-access state 502-2, the intermediate-power state 504-2, and the intermediate-information state 506-2, each of which is described above. The low level 1208-3 is illustrated with three low states, the low-access state 502-3, the low-power state 504-3, and the low-information state 506-3. These states are described in detail above. Note that any one, two, or all three of these states can be reduced by the state manager 112 at operation 1208, either each to a same level or differing levels. Thus, the state manager 112 may reduce the high-access state 502-1 to an intermediate or low state, and keep the power state and the information state at high or a mix of levels. Similarly, the state manager 112 may reduce the power state 504 to the low-power state 504-3 while keeping the UE 102 at the high-access state 502-1 (e.g., "unlocked").
[0161] By way of example, consider the application of method 1200 to scenario 1300 illustrated in FIG. 13. The scenario 1300 includes three portions, each one chronologically following the prior portion. Prior to the first portion of the scenario 1300, assume that user 1302 is actively engaged with smartphone 1304 and that the smartphone 1304 is in high-level states, namely power, access, and information states. At the first portion, shown at scenario portion 1300-1, the user 1302 walks up to a table, and places the smartphone 1304 on the table. At operation 1204, the IMU 108 receives inertial data either for the touching of the smartphone 1304 on the table or a lack of inertial data when, previous to being placed on the table, inertial data indicated movement (based on the user 1302 walking with the smartphone 1304). Based on either or both of these inertial data, the movement manager 110 determines a movement for the smartphone 1304 and passes this determination to the radar manager 106 and/or the state manager 112.
[0162] Assume that the radar manager 106 provides the radar field 118 (not shown for visual brevity, see FIG. 1 for an example) either immediately responsive to the movement data or was already doing so, and therefore receives radar data indicating the user's 1302 body position and so forth. Based on this radar data, the radar manager 106 determines for a first iteration (and likely multiple others) that, at operation 1206 for the body, arm, and hand placement, the user 1302 is not intending to disengage at the scenario portion 1300-1. This is due to the user 1302 having a body orientation toward the smartphone 1304 and the user's hand and arm being oriented toward the smartphone 1304. Because of this, a high-information state 1306-1 is not altered.
[0163] At the scenario portion 1300-2, however, assume that roughly two seconds later, the user 1302 picks up their coffee cup and begins to walk away while turning their body away from the smartphone 1304. At this point, the radar manager 106 determines that the user 1302 is intending to disengage from the smartphone 1304 based on the body orientation of the user 1302 being turned partly away from the smartphone 1304, and the user's 1302 arm and hand oriented toward the coffee cup and not the smartphone 1304. The radar manager 106 passes this determination to the state manager 112.
[0164] At operation 1208, responsive to receiving the movement and intent to disengage determinations, the state manager 112 reduces the information state of the smartphone 1304 from the high-information state 1306-1 shown at scenario portion 1300-1 to the intermediate-information state 1306-2. These example information states are shown with information displayed at scenario portion 1300-1 showing content from two text messages and a time of day Immediately at the user 1302 turning their body and picking up their coffee cup, the information state is reduced to the intermediate-information state 1306-2, shown with the time of day and reduced information about the text messages (shown with the name of the sender but no context). This intermediate amount of information can be useful to the user 1302, as they may change their mind about engaging, or want to look back at the smartphone 1304 to see if a new notification has arrived, such as a text from a different person.
[0165] Also or instead of showing the intermediate-information state 1306-2, and as part of operation 1208, the state manager 112 may proceed to a low level either immediately or after first being at an intermediate state. Here assume that the state manager 112, responsive to additional determinations by the radar manager 106 indicating that the user 1302 intends to disengage or a higher confidence level thereof (e.g., here shown with a high confidence as the user 1302 is now a few meters away and has their back fully turned to the smartphone 1304), reduces the information state further to the low-information state 1306-3, shown as scenario portion 1300-3 presenting only a current time of day.
[0166] While this example shows changes to an information state, access and power may also or instead be changed. This is shown in part with an unlock icon 1310 shown at scenario portion 1300-1, indicating a high level of access (e.g., the high-level access 502-1 of FIG. 5). At the scenario portion 1300-2 after the state manager 112 receives the movement data and the intent to disengage, the state manager 112 reduces the access to a low level, which is indicated to the user with the lock icon 1312. Further still, power states can be altered, such as by reducing a luminosity of the smartphone's 1304 display (not shown) at the scenario portions 1300-2 and/or 1300-3.
[0167] Maintaining an Authenticated State
[0168] FIG. 14 depicts an example method 1400 for maintaining an authenticated state. The method 1400 is shown as a set of blocks that specify operations performed but are not necessarily limited to the order or combinations shown for performing the operations by the respective blocks. Further, any of one or more of the operations may be repeated, combined, reorganized, or linked to provide a wide array of additional and/or alternate methods, including with other methods set forth in this document (e.g., methods 1000 and 1200). In portions of the following discussion, reference may be made to the example operating environment 100 of FIG. 1 or to entities or processes as detailed in other figures, reference to which is made for example only. The techniques are not limited to performance by one entity or multiple entities operating on one device.
[0169] Prior to discussing method 1400, note that any of the methods described above, in whole or in part, can be combined with method 1400. Consider, for example, the performance of method 1000 in FIG. 10. This method 1000 describes one example of authentication management resulting in authentication of a user of a user equipment. Responsive to this authentication, the user equipment enters into an authenticated state. This state is described in greater detail above. Thus, the method 1000 (or some other manner of authentication of a user) is performed prior to method 1400.
[0170] At 1402, during an authenticated state of a user equipment, a potential disengagement by a user of the user equipment is determined. This determination of a potential disengagement by a user can include determining an intent to disengage by the user, as noted above, and other determinations set forth below. Also, as noted above, the authenticated state permits access, by the user, of one or more of the data, applications, functions, accounts, or components of the user equipment. Examples of an authenticated state include the high-access state 502-1 and the intermediate access state 502-2 noted in FIG. 5 above. While either of these access states can be permitted by the UE 102 when in the authenticated state (often based on a user preference or an operating system default setting), the authenticated state assumes a previous authentication of the user. A user-selected preference or setting, however, can permit a high or intermediate access of the UE 102 without authentication. Thus, while the authenticated state may include access permitted by the high and intermediate access states noted above, the high and intermediate access are not necessarily authenticated states.
[0171] As illustrated in FIG. 14, determination of the potential disengagement can be performed, optionally, responsive to (or through performing) operation 1404 or operation 1406, as well as other manners described herein, such as through determining an intent to disengage at operation 1206 of method 1200. At 1404, expiration of an inactivity time period is determined. As noted above, this inactivity time period can start when a last user action is received, an active engagement with the user equipment ends (or is last received), or when a last intent to engage was determined. For example, an inactivity timer (e.g., a time period) begins when a user last touches a touch-sensitive display or button, a last-received audio command is spoken, or a last-determined touch-independent gesture (e.g., a gesture determined using the radar system 104 noted above) is performed.
[0172] At 1406, a movement of the user equipment is determined based on inertial data of an inertial measurement unit (IMU) integral with the user equipment. Example movements and inertial data are described above, such as inertial data received from the IMU 108 of FIG. 1. Thus, a movement determination is one way in which the method may determine that a user is potentially disengaging, such as by placing the UE 102 in a locker, bag, or pocket (though placing in a bag or pocket may later be determined to be a passive engagement, noted below).
[0173] At 1408, a passive engagement by the user with the user equipment is determined based on radar data. This determination of a passive engagement can be responsive to determination at 1402 of the potential disengagement (shown with a dashed-line arrow), or it can be independent of, or coincident with, that determination. Performing operation 1408 responsive to the determination of the potential disengagement can, in some cases, save power or reduce latency. For example, the method 1400 may increase power to components of the radar system 104 (see also FIGS. 6-1 and 6-2) responsive to the determination of a potential disengagement. This can save power as noted above or give additional time for the radar system 104 to prepare to determine whether the user is passively engaged with the radar system 104.
[0174] In the context of FIG. 1, the radar manager 106 determines that the user 120 is passively engaged with the UE 102. This passive engagement can be determined by the radar manager 106 in multiple ways, which can be exclusive or overlap one with the other. For example, the radar manager 106 can determine that the user is passively engaged based on the radar data indicating that a hand of the user 120 is holding the user equipment 102 at an orientation at which the display 116 of the user equipment 102 is maintained. Thus, if the user 120 is holding the UE 102 steady (or steady enough to view content or permit another person to view content) the user 120 is passively engaged. Other examples of determining passive engagement are described above, including the user 120 looking at or orienting their body toward the UE 102.
[0175] Furthermore, the radar manager 106 can determine passive engagement based on the radar data indicating that the user 120 is present, such as by being within two meters of the UE 102. Other distances can also or instead be used, such as 1.5 meters, one meter, or even one half of one meter. In effect, the radar manager 106 can determine that the user 120 is passively engaged by being roughly within reach of the UE 102. The radar manager 106 may do so explicitly by indicating that the user 120 is passively engaged, or simply pass information indicating a distance from the UE 102, to the state manager 112. The state manager 112 then determines passive engagement based on the proximity of the user 120 and, in some cases, context, such as other people (or lack thereof), whether or not the user 120 is in a vehicle (car, bus, train), at a desk, and so forth. A user sitting in their home, for example, may have a larger permitted distance than the user sitting in a crowded coffee shop or train.
[0176] At 1410, responsive to the determination of the passive engagement by the user with the user equipment, the authenticated state is maintained. This maintaining of the authenticated state can continue until another potential disengagement is determined, or for some time period, after which method 1400 can again be performed. One example of an authenticated state is the high-access state 502-1 of FIG. 5. In many situations this authenticated state is an unlock state for the UE 102, but in some other cases the authenticated state permits some but not all access to the UE 102, such as the above-described intermediate-access state 502-2.
[0177] This maintaining of the authenticated state for the UE 102 does not require that other states be maintained. For example, in cases where the user 120 is within two meters of the UE 102, but may or may not be looking toward or oriented toward the UE 102, the state manager 112 can reduce a power state or information state of the UE 102, such as from the high-power state 504-1 and the high-information state 506-1 to intermediate or low power or information states noted in FIG. 5. If, however, the passive engagement includes the user looking at the UE 102, the power or information states can also be maintained, such as to continue to present, through the display 116, content to the user 120.
[0178] Optionally, the method 1400 can proceed to operation 1412, in which a presence or an intent to engage of a non-user is determined based on radar data. This radar data can be the same or later-received radar data, such as radar data from the radar system 104 received some number of seconds or minutes after the radar data on which the passive engagement was based. Thus, at 1412 the radar manager 106 determines that a non-user is present or intends to engage with the UE 102. If a non-user, therefore, reaches for the UE 102, or looks at the display 116 of the UE 102, the radar manager 106 can determine this presence or intent, and pass it to the state manager 112.
[0179] At 1414, responsive to the determination that the non-user is present or intends to engage with the user equipment, the maintenance of the authenticated state is ceased. Thus, if a non-user walks up, reaches for, or looks at the display 116 of the UE 102, the state manager 112 ceases to maintain the authenticated state (or actively de-authenticates) the UE 102. Along with this cessation, the state manager 112 may also reduce other states, such as an information state effective to reduce or eliminate information presented to the non-user. Assume, for example, that an authenticated user is reading a private email on the subway train. If a person sitting behind the user looks at the display, possibly to read the private email, the state manager 112 can lock the UE 102 and cease to display the private email. This can be performed quickly and seamlessly, further improving the privacy of a user.
[0180] A 1416, optionally after ceasing to maintain the authenticated state, the method can be returned to the authenticated state responsive to a determination that the non-user is no longer present or no longer intending to engage. Continuing the example above, when the non-user in the subway train looks away from the display 116 of the UE 102, the state manager 112 may re-authenticate the user 120 through an authentication process or simply by switching back to the authentication state without re-authenticating. Thus, the user 120 can simply go back to the previous states immediately on cessation of the condition that caused the de-authentication. While some authentication processes, such as the system and process described herein, are both fast and power-efficient, not performing an authentication process can be faster and more-power-efficient. On returning to the authenticated state, the state manager 112 can return the information state to the prior level and at content matching the content last presented to the user 120. In this example, when the non-user looks away, the display 116 presents the private email at a same location last presented by the UE 102 to the user 120. By so doing, seamless management of authentication and improved information privacy is provided to users. Note that a selection by the user 120 can override operations of the techniques, such as a user selection to de-authenticate. In some cases, the user 120 simply turns off the UE 102, which is permitted by the methods described herein.
[0181] Consider another example illustrated in FIG. 15 through a scenario 1500. The scenario 1500 includes four portions. At a first portion 1500-1, assume that a user 1502 has been authenticated to the smartphone 1504, such as through credential or facial-feature analysis, and thus that the smartphone 1504 is in an authenticated state 1506. This authenticated state 1506 allows the user 1502 access to the smartphone 1504, which is shown through the user 1502 accessing content of the smartphone 1504 by watching a television program about volcanic eruptions.
[0182] The scenario 1500 is shown diverging along two different paths. In one path an inactivity timer begins when the user 120 ceases to touch or provide input to the smartphone 1504, which here is when they relax to watch the television program. In another case an inactivity timer can begin or not, but a potential disengagement will be determined without its expiration. Thus, at scenario portion 1500-2, after three minutes of inactivity, the inactivity timer expires. Returning to FIG. 14, operation 1402 determines that a potential disengagement by the user has occurred, due to the inactivity time period expiring at operation 1404. For the second path shown at scenario portion 1500-3, operation 1402 determines that a potential disengagement by the user has occurred by determining, based on inertial data, that a movement of the smartphone 1504 has occurred through performing operation 1406. The cause of this movement is the user 1502 putting their foot on the edge of the table on which the smartphone 1504 is resting.
[0183] The radar manager 106, responsive to either of these determinations of a potential disengagement, determines, based on radar data, that the user 1502 is passively engaged with the smartphone 1504. This operation is performed at 1408. Here assume that the user's 1502 presence or their looking at the smartphone 1504 are determined, either of which indicate that the user 1502 is passively engaged.
[0184] In response, at operation 1410, the state manager 112 maintains the authenticated state. All of this can be performed seamlessly and without the user 1502 noticing that it has been performed. As shown in scenario portion 1500-4, the smartphone 1504 simply continues to present the television program through either path.
[0185] Consider another scenario 1600 of FIG. 16, which can follow the scenario 1500 or be an alternative, stand-alone scenario. The scenario 1600 includes three scenario portions, in a first scenario portion 1600-1, the user 1502 is watching the television program about volcanoes, similarly to as shown in FIG. 15, here marked at content 1602 of the smartphone 1504. The smartphone 1504 is in an authenticated state during this presentation of the program, such as the authenticated state 1506 noted in FIG. 15.
[0186] At scenario portion 1600-2, however, a non-user 1604 sits down on the couch with the user 1502. This non-user 1604 is a colleague of the user 1502 and so the user 1502 turns their head to them and begins talking to them. These actions of the user 1502 can be considered a potential disengagement, either turning their head or talking or both, as noted above. If considered a potential disengagement by the user 1502, the state manager 112 reduces the state of the smartphone 1504, such as to reduce the access state or the information state, noted in FIGS. 5 and 12 (e.g., operations 1206 and 1208 of method 1200).
[0187] Assume, however, that the radar manager 106 determines, through operation 1412 of method 1400 and based on radar data, the presence of the non-user 1604. Based on this presence of the non-user 1604, the state manager 112 ceases to maintain the authenticated state 1506 after the state manager 112 previously acted to maintain the authenticated state of the smartphone 1504 (e.g., through operation 1410 shown in FIG. 15). Thus, the state manager 112 can cause the smartphone 1504 to be reduced to a non-authenticated state 1604, shown at an expanded view of the scenario portion 1600-2. This change is shown to the user 1502 through a lock icon 1606, as well as by ceasing to present the content 1602.
[0188] At scenario portion 1600-3, the non-user 1604 has left and the user 1502 returns to looking at the smartphone 1504. The radar manager 106 determines that the non-user 1604 is no longer present, indicates this determination to the state manager 112, which then returns the smartphone 1504 to the authenticated state 1506. Note that the state manager 112 may also require a determination that the user 1502 is intending to engage with the smartphone 1504, or may simply return to the authenticated state based on the non-user 1604 leaving the presence of the smartphone 1504. Note also that the techniques described in this document can return a user to the spot at which they left off, seamlessly, thereby providing an excellent user experience. This is shown in FIG. 16 with the state manager 112 returning the smartphone 1504 to a same television program and at a same or nearly a same point that was last presented to the user 1502. For some embodiments the techniques allow the user, in a setup screen or similar device configuration screen, to dictate whether, at step 1416, the smartphone 1504 will return to the authenticated state responsive to the determination that the non-user is no longer present or intending to engage, versus whether the smartphone 1504 will stay in a non-authenticated state until a more-rigorous authentication process using a power-consuming component of an authentication system (e.g., step 1006, supra) is carried out. Stated differently, the techniques can provide a user-selected setting, through a setup or similar device configuration, that causes the smartphone 1504 to remain de-authenticated once there has been the taint of a non-user, even if the taint is no longer there.
EXAMPLES
[0189] In the following section, examples are provided.
[0190] Example 1: A method comprising: determining, during an authenticated state of a user equipment, a potential disengagement by the user of the user equipment, the authenticated state permitting access by the user of data, applications, functions, accounts, or components of the user equipment; determining, based on radar data and by the user equipment, a passive engagement by the user with the user equipment; and responsive to the determination of the passive engagement by the user with the user equipment, maintaining the authenticated state.
[0191] Example 2: The method of example 1, wherein the authenticated state permits access by the user to the data, the applications, the functions, at least one of the accounts, and at least one of the components of the user equipment.
[0192] Example 3: The method of examples 1 or 2, further comprising determining that an inactivity time period has expired and wherein determining the potential disengagement is based on the determination that the inactivity time period has expired.
[0193] Example 4: The method of example 3, wherein the inactivity timer period begins at a last user action with the user equipment, a last active engagement with the user equipment, or a last-determined intent to engage with the user equipment.
[0194] Example 5: The method of examples 1 or 2, further comprising determining, based on inertial data of an inertial measurement unit (IMU) integral with the user equipment, a movement of the user equipment, and wherein determining the potential disengagement is based on the determined movement.
[0195] Example 6: The method of any of the preceding examples, wherein determining the passive engagement by the user with the user equipment is responsive to the determination of the potential disengagement and further comprising, prior to determining the passive engagement by the user, increasing a power state of a component of a radar system from which the radar data is received.
[0196] Example 7: The method of any of the preceding examples, wherein determining passive engagement by the user determines, based on the radar data, that a hand of the user is holding the user equipment at an orientation at which a display of the user equipment is maintained.
[0197] Example 8: The method of any of examples 1 through 6, wherein determining passive engagement by the user of the user equipment determines, based on the radar data, that the user is oriented toward or looking toward the user equipment.
[0198] Example 9: The method of examples 1 through 6, wherein determining passive engagement by the user of the user equipment determines, based on the radar data, that the user is within two meters of the user equipment.
[0199] Example 10: The method of any of the preceding examples, further comprising reducing an information state of the user equipment from a high-information state to an intermediate-information state or a low-information state.
[0200] Example 11: The method of example 10, wherein reducing the information state is responsive to determining that the user is oriented or looking away from the user equipment.
[0201] Example 12: The method of any of the preceding examples, further comprising determining, based on the radar data or later-received radar data, an intent to engage or a presence of a non-user and, responsive to the determination of the intent to engage or the presence, ceasing to maintain the authenticated state.
[0202] Example 13: The method of example 12, further comprising returning to the authenticated state responsive to determining that the non-user is no longer present.
[0203] Example 14: The method of example 13, further comprising, responsive to the determination of the intent to engage or the presence of the non-user, reducing an information state of the user equipment and, responsive to returning to the authenticated state, increasing the information state of the user equipment.
[0204] Example 15: The method of example 14, wherein increasing the information state of the user equipment presents information as presented prior to the reduction of the information state.
[0205] Example 16: An apparatus configured to perform a method of any one of examples 1 through 15.
[0206] Conclusion
[0207] Although implementations of techniques for, and apparatuses enabling, maintaining an authenticated state have been described in language specific to features and/or methods, it is to be understood that the subject of the appended claims is not necessarily limited to the specific features or methods described. Rather, the specific features and methods are disclosed as example implementations enabling maintaining an authenticated state.
* * * * *
D00000

D00001

D00002
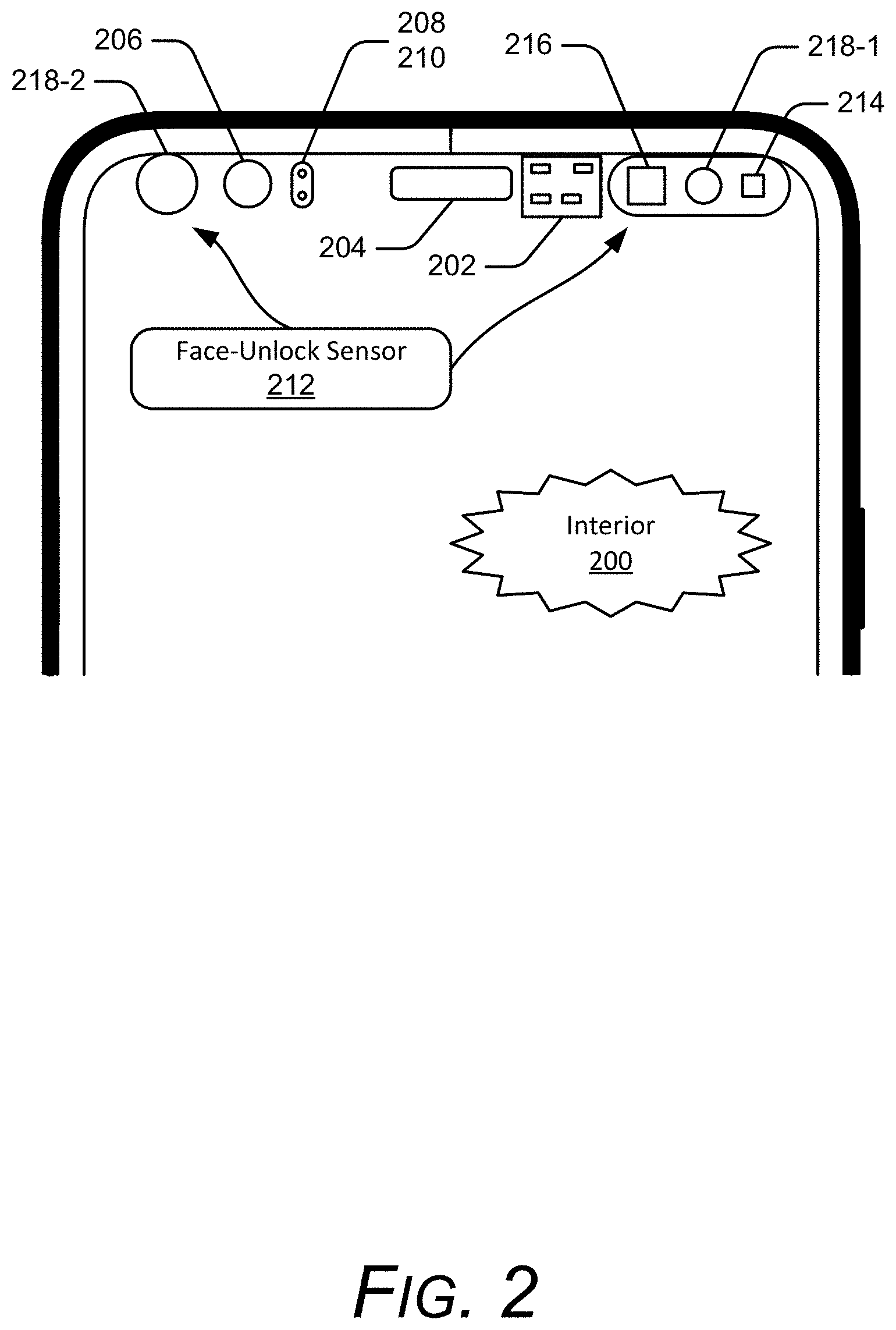
D00003

D00004
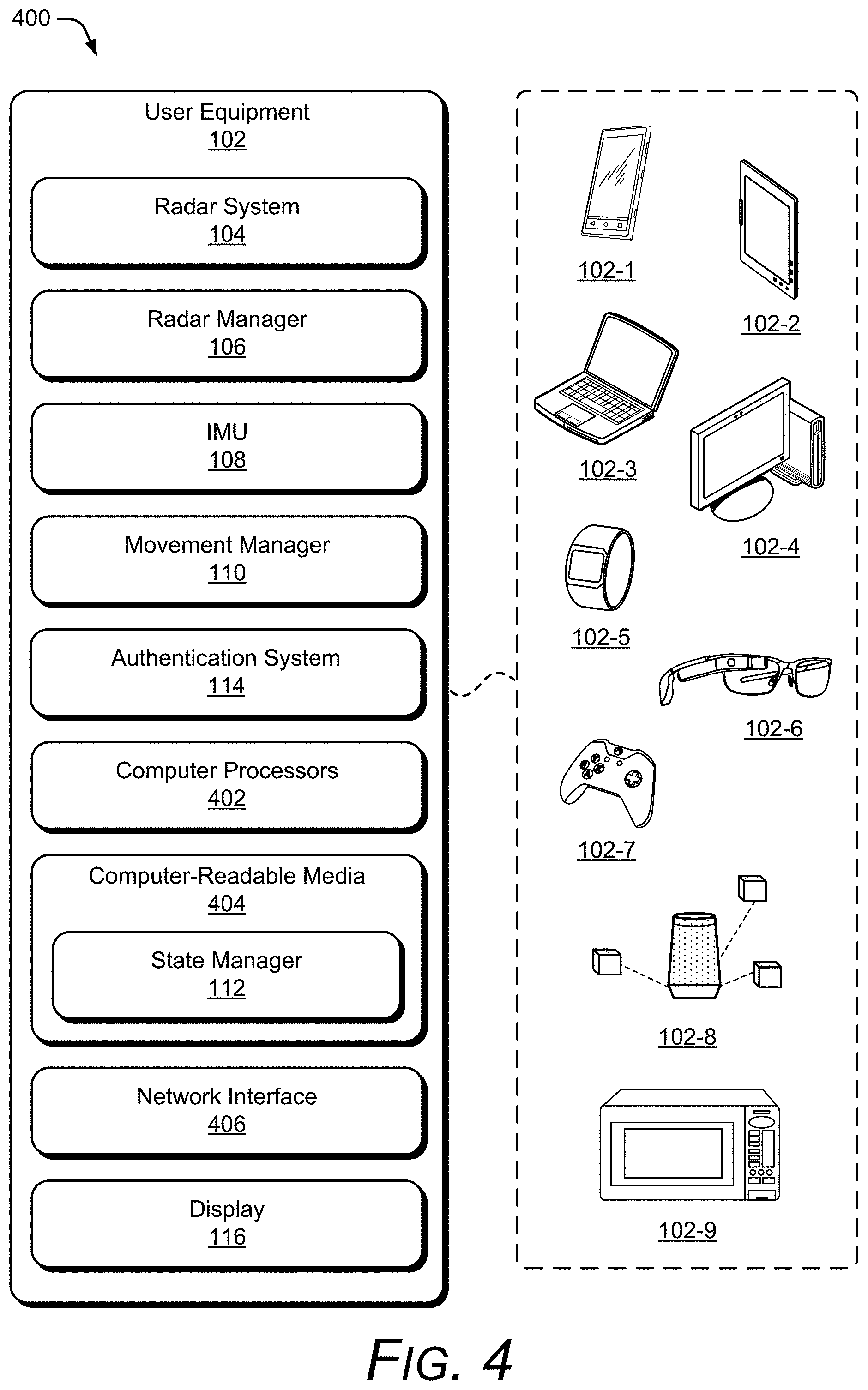
D00005
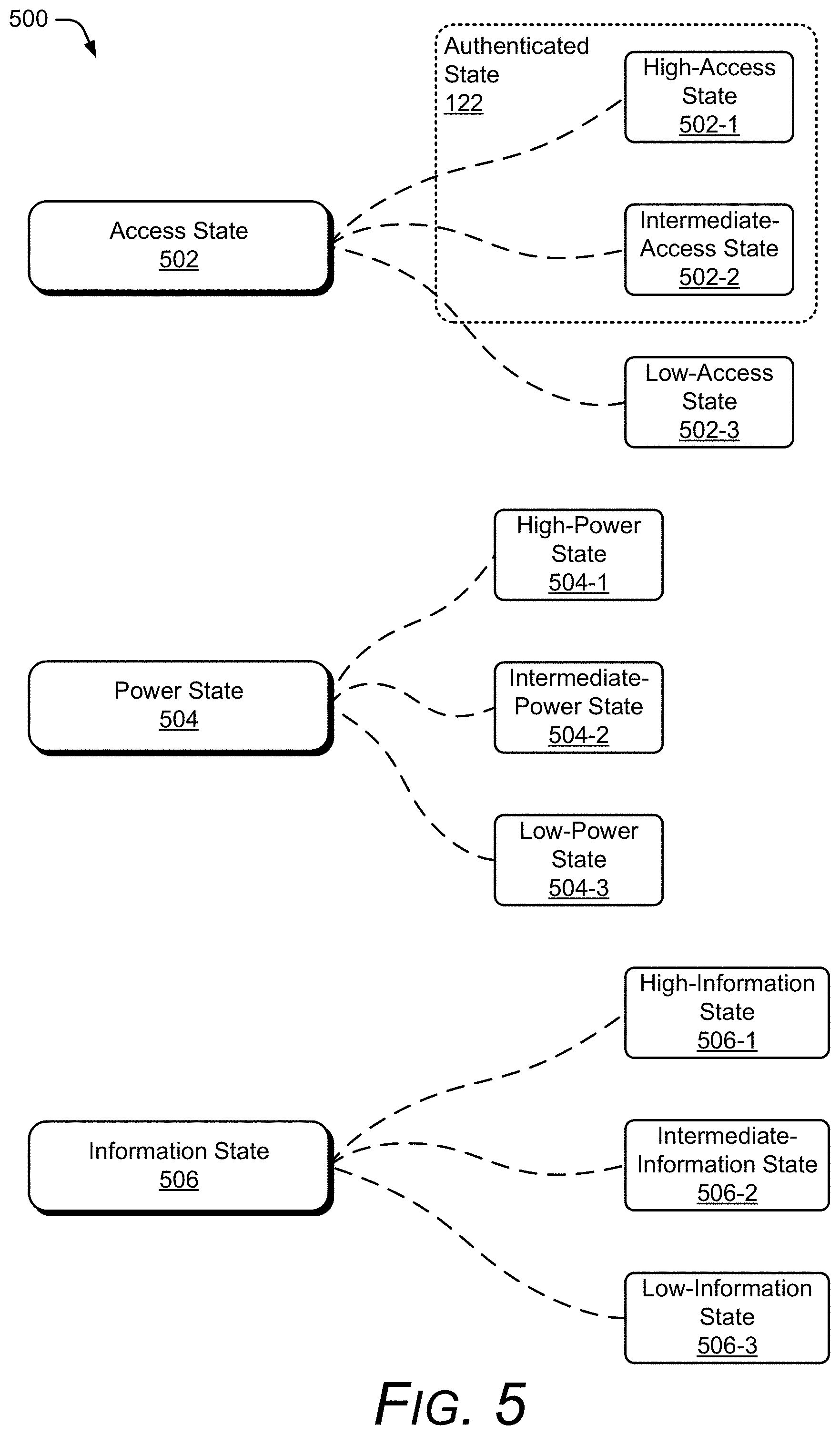
D00006

D00007
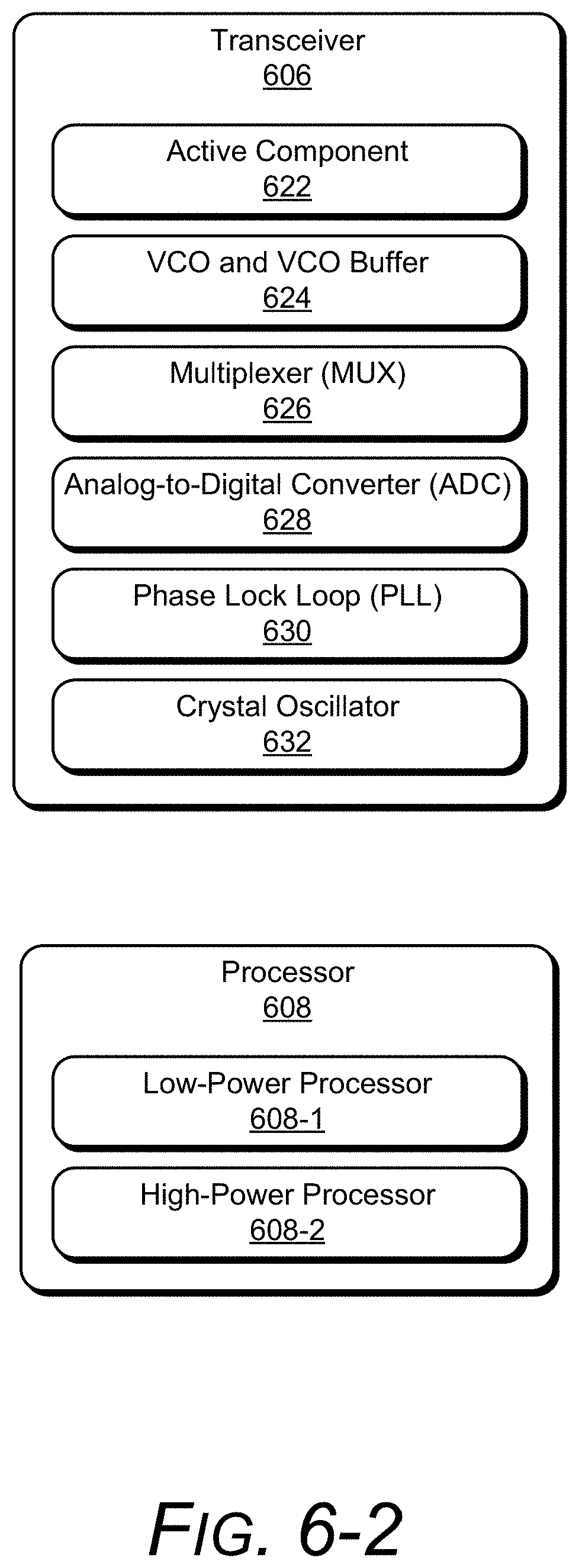
D00008

D00009

D00010

D00011

D00012

D00013

D00014

D00015
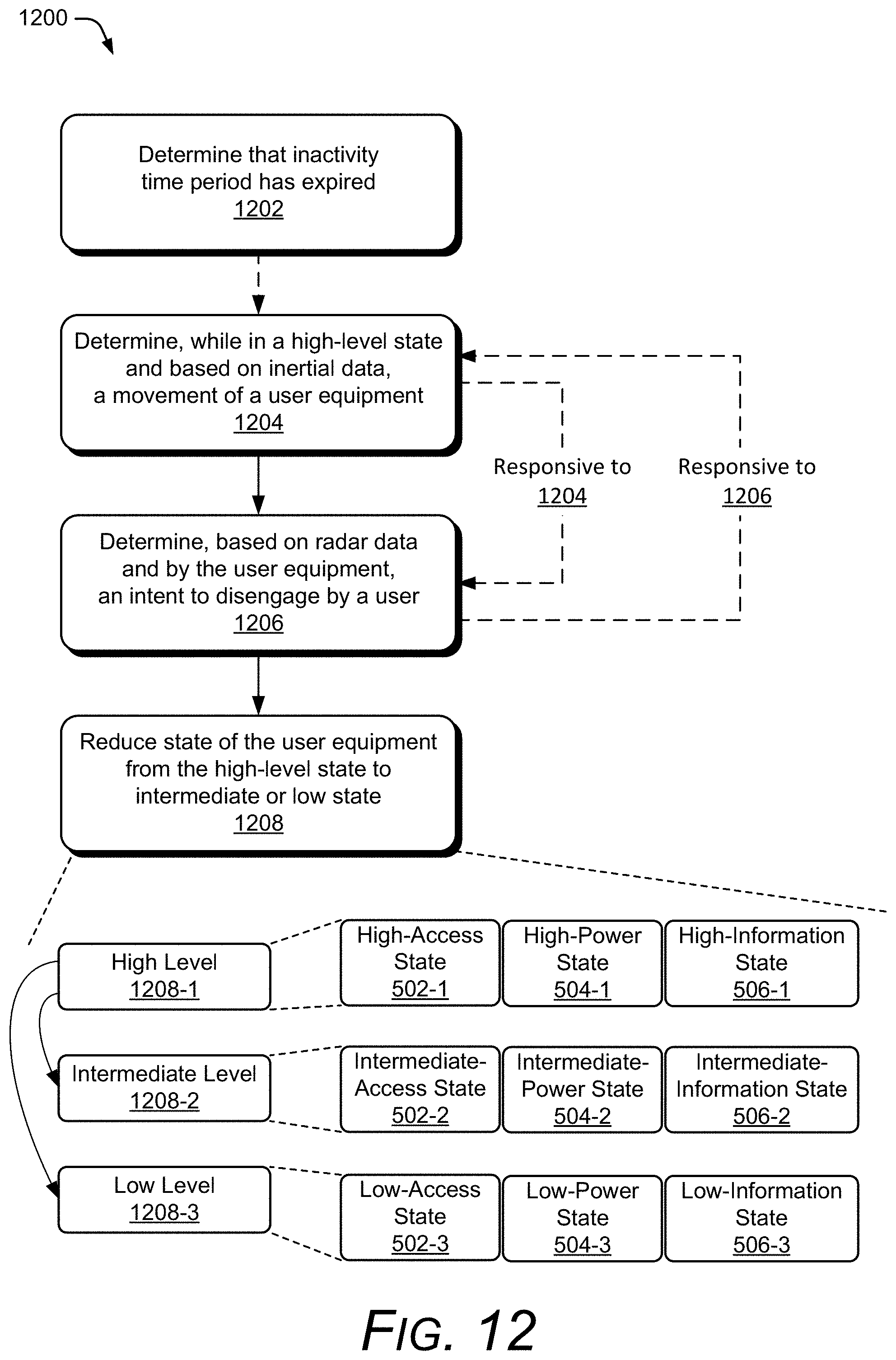
D00016
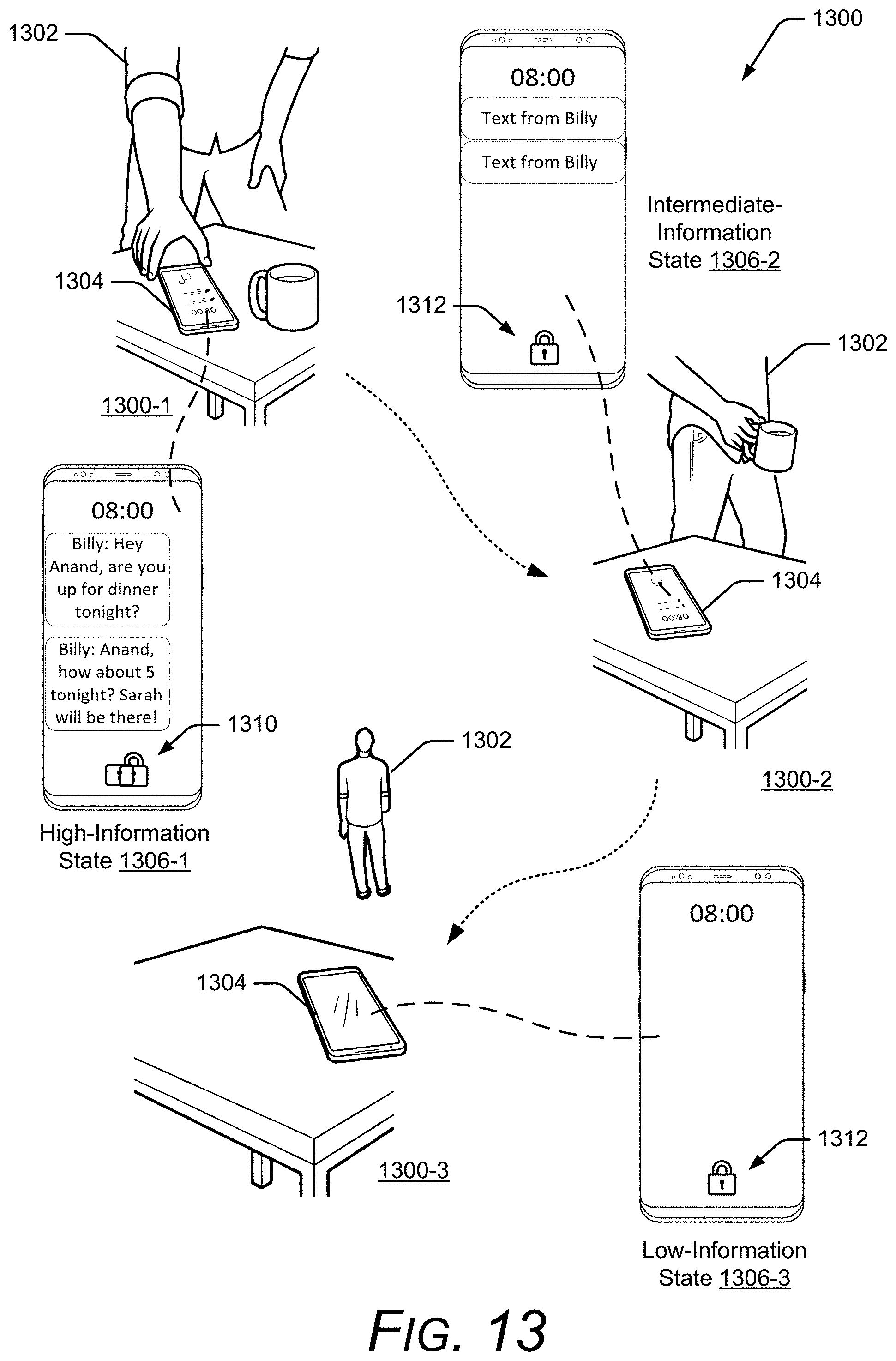
D00017
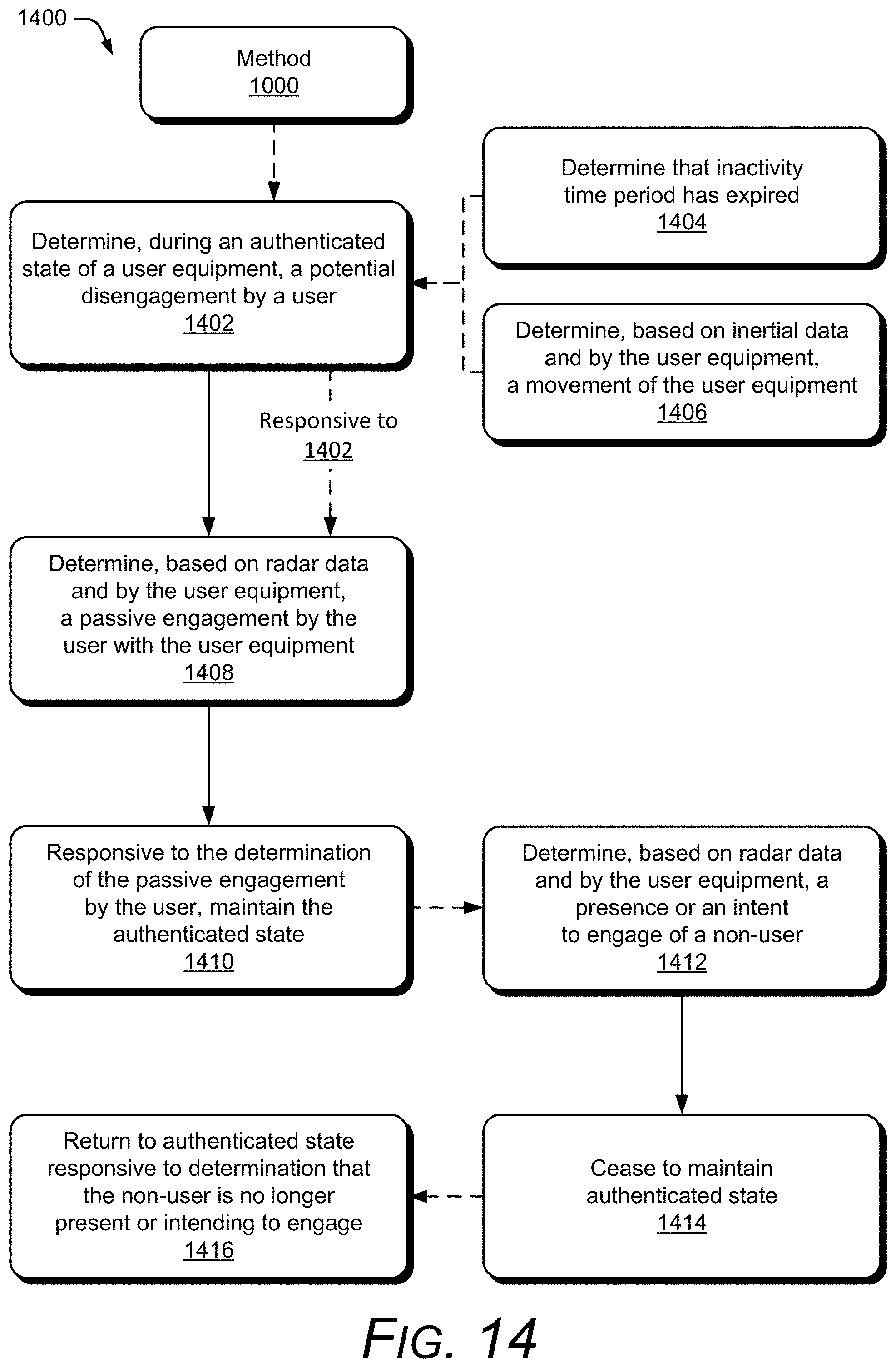
D00018
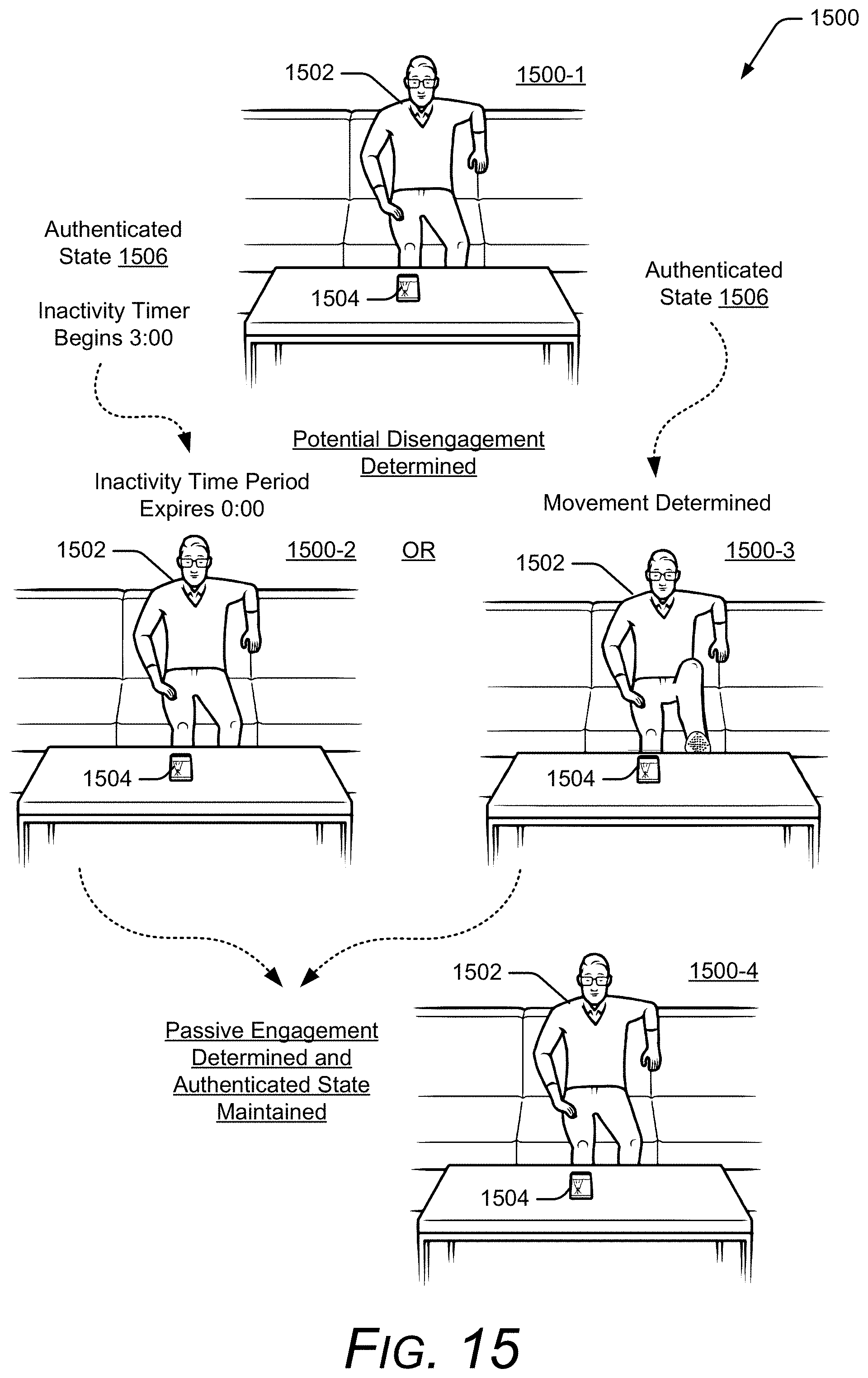
D00019
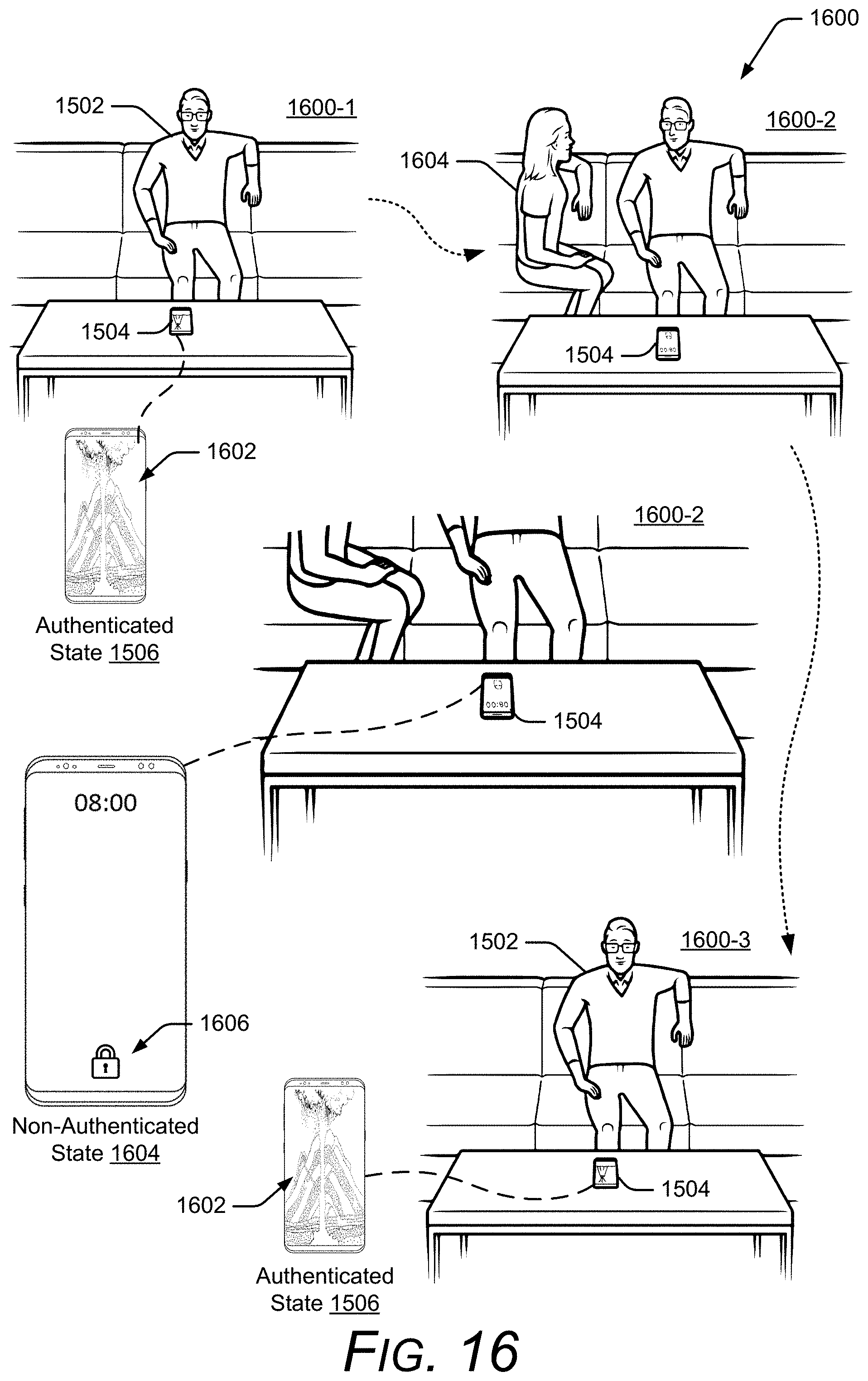
XML
uspto.report is an independent third-party trademark research tool that is not affiliated, endorsed, or sponsored by the United States Patent and Trademark Office (USPTO) or any other governmental organization. The information provided by uspto.report is based on publicly available data at the time of writing and is intended for informational purposes only.
While we strive to provide accurate and up-to-date information, we do not guarantee the accuracy, completeness, reliability, or suitability of the information displayed on this site. The use of this site is at your own risk. Any reliance you place on such information is therefore strictly at your own risk.
All official trademark data, including owner information, should be verified by visiting the official USPTO website at www.uspto.gov. This site is not intended to replace professional legal advice and should not be used as a substitute for consulting with a legal professional who is knowledgeable about trademark law.