Unique transaction identifier, which may also include a time expiration value, is assigned by a first network website to an electronic instruction to collect specified distinctive identifiers from a local/mobile computing device seeking access to said first network website
Streuter; Gary William ; et al.
U.S. patent application number 15/860452 was filed with the patent office on 2020-12-24 for unique transaction identifier, which may also include a time expiration value, is assigned by a first network website to an electronic instruction to collect specified distinctive identifiers from a local/mobile computing device seeking access to said first network website. The applicant listed for this patent is William Pat Price, Gary William Streuter. Invention is credited to William Pat Price, Gary William Streuter.
| Application Number | 20200402046 15/860452 |
| Document ID | / |
| Family ID | 1000005064648 |
| Filed Date | 2020-12-24 |


| United States Patent Application | 20200402046 |
| Kind Code | A1 |
| Streuter; Gary William ; et al. | December 24, 2020 |
Unique transaction identifier, which may also include a time expiration value, is assigned by a first network website to an electronic instruction to collect specified distinctive identifiers from a local/mobile computing device seeking access to said first network website
Abstract
This invention discloses a system and methods for defeating a so-called man-in-the-middle (MITM) attack. An electronic instruction to collect specified distinctive identifiers from a local/mobile computing device seeking access to a first network website, is generated by said first network website and that electronic instruction is assigned a unique onetime identification token. Said electronic instruction with said unique onetime identification token is transmitted by said first network website to said local/mobile computing device. Said unique onetime identification token is also maintained in a database of unique onetime identification tokens resident on said first network website. In addition, said unique onetime identification token is sent to a secondary network website, where it is also stored in a database of unique onetime identification tokens. Said unique onetime identification token may also contain a time expiration value which defines the validity period for said unique transaction identifier.
| Inventors: | Streuter; Gary William; (Laguna Niguel, CA) ; Price; William Pat; (Henderson, NV) | ||||||||||
| Applicant: |
|
||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|
| Family ID: | 1000005064648 | ||||||||||
| Appl. No.: | 15/860452 | ||||||||||
| Filed: | January 2, 2018 |
Related U.S. Patent Documents
| Application Number | Filing Date | Patent Number | ||
|---|---|---|---|---|
| 14693707 | Apr 22, 2015 | |||
| 15860452 | ||||
| 62134980 | Mar 18, 2015 | |||
| Current U.S. Class: | 1/1 |
| Current CPC Class: | G06Q 20/409 20130101; G06Q 20/40 20130101; G06Q 20/1085 20130101; G06Q 20/4097 20130101; H04L 2463/082 20130101; G06Q 20/382 20130101; G06Q 20/40145 20130101; H04L 63/102 20130101; H04L 63/083 20130101; G06Q 20/02 20130101; H04L 63/0861 20130101 |
| International Class: | G06Q 20/40 20060101 G06Q020/40; H04L 29/06 20060101 H04L029/06; G06Q 20/38 20060101 G06Q020/38; G06Q 20/02 20060101 G06Q020/02; G06Q 20/10 20060101 G06Q020/10 |
Claims
1-7. (canceled)
8. A system for defeating a man in the middle attack against network servers whereby a first network website and a secondary network website are communicably coupled to each other and to a user's computing device, said user's computing device receives from said first network website a unique onetime identification token and an electronic instruction to collect a set of specified distinctive identifiers drawn from said user's computing device, said user's computing device sends to said secondary network server said unique onetime identification token and said set of specified distinctive identifiers, said first network website sends said unique onetime identification token to said secondary network server, and whereby said secondary network server uses said unique onetime identification token to validate said set of specified distinctive identifiers received from said user's computing device, comprising the system method steps of: said first network website: i. maintains sets of users account credentials and authorization policies, and ii. receives from said user's computing device a request for access, said request for access containing said user's account credentials, and iii. verifies said user's account credentials received from said user's computing device against said authorization policies for said first network website and if said user's account credentials are valid and are within said authorization policies, said first network website generates said unique onetime identification token and sends said unique onetime identification token to said user's computing device and to said secondary network server, and iv. generates said electronic instruction sent to said user's computing device, said electronic instruction directs said user's computing device to collect and secure a set of said specified distinctive identifiers to be sent to said secondary network server with said unique onetime identification token, and v. receives from said secondary network server an indication that said user's computing device has been validated or has not been validate, and vi. if said user's computing device has not been validated by said secondary network server, said first network website notifies said user's computing device that said user's computing device is not being granted access to said first network website, and vii. if said user's computing device has been validated by said secondary network server, said first network website notifies said user's computing device that said user's computing device is being granted access to said first network website; said secondary network server: i. maintains a validation database containing sets of preregistered specified distinctive identifiers of user's computing devices, and ii. receives from said first network website said onetime unique identification token and stores said onetime unique identification token in a token database, and iii. receives from said user's computing device a set of specified distinctive identifiers and said unique onetime identification token, and iv. performs a matching of said unique onetime identification token received from said user's computing device against those unique onetime identification tokens received from said first network website and saved in said identification token database, and if said unique onetime identification token received from said user's computing device is not matched against one of said unique onetime identification tokens in said token database, said secondary network server notifies said first network website that said user's computing device is NOT to be granted access to said first network website, and v. and if said unique onetime identification token received from said user's computing device is matched against one of said unique onetime identification tokens in said token database, said secondary network server performs a matching of said set of specified distinctive identifiers received from said user's computing device against a plurality of said sets of specified distinctive identifiers residing in said validation database and if said matching is not successful, said secondary network server notifies said first network website that said user's computing device is NOT to be granted access to said first network website, and if said matching is successful, said secondary network server notifies said first network website that said user's computing device is to be granted access to said first network website; said user's computing device: i. sends to said first network website a request for access, said request for access may include a username or email address, one or more passwords, and biometric marker information identifying said account owner, and ii. receives from said first network website a unique onetime identification token and an electronic instruction directing said user's computing device to gather a set of specified distinctive identifiers, and iii. selects a set of specified distinct identifiers as instructed by said first network website, secures said set of specified distinctive identifiers creating a secured set of selected distinctive identifiers and sends said secured set of selected distinctive identifier and said unique onetime identification token to said secondary network server, and iv. receives from said first network website an indication that said user's computing device is granted access to said first network website or that said user's computing device is not granted access to said first network website.
9. The system of claim 8 whereby said unique onetime identification token sent by said first network website is sent simultaneously to both said user's computing device and said secondary network server.
10. The system of claim 8 whereby said unique onetime identification token sent by said first network website is sent at staggered times to said user's computing device and said secondary network server.
11. The system of claim 8 whereby said first network website sends a time expiration value with said unique onetime identification token sent by said first network website to said secondary network server, and said secondary network server starts a timer using said time expiration value, and if said timer expires prior to said secondary network server receiving said unique onetime identification token and said set of specified distinctive identifiers from said user's computing device, said secondary network server sends an indication to said first network website that said user's computing device is NOT to be granted access to said first network website.
12. A method for defeating a man in the middle attack against network servers whereby a first network server web site assigns a unique onetime identification token to an electronic instruction to gather a set of specified distinctive identifiers that are sent by said first network website to a user's computing device seeking account access to said first network website comprising the method steps of: a) creation of a unique onetime identification token by said first network website, and b) sending of said electronic instruction to gather a set of specified distinctive identifiers and said unique onetime identification token to said to said user's computing device, and c) sending of said unique onetime identification token to a secondary network server, said secondary network server adds said unique onetime identification token to a database of authorized unique onetime identification tokens received from said first network server and maintained by said secondary network server, and d) sending of said unique onetime identification token and said set of specified distinctive identifiers gathered and secured by said user's computing device to said secondary network server, and e) comparing by said secondary network server of said unique onetime identification token received by said secondary network server and said unique onetime identification token received by said secondary network server from said user's computing device, and f) if said unique onetime identification tokens are matched, said secondary network server performs a matching of a said set of specified distinctive identifiers residing in a validation database against said set of specified distinctive identifiers received from said user's computing device and if said match is made, said secondary network server notifies said first network website that said user's computing device IS validated for access and if said match is not made, said secondary network server notifies said first network website that said user's computing device is NOT validated for access.
13. A method for defeating a man in the middle attack against network servers on a network whereby a first software program executing on a first network server website sends a unique onetime identification token to a secondary network server for inclusion in a database of authorized unique control identifiers, said unique onetime identification token includes a time expiration value, defining a time period during which said unique onetime identification token is considered valid for matching with an identical unique onetime identification token received by said secondary network server from a user's computing device, comprising the method steps of: a. said secondary network server receives said unique onetime identification token and logs said time expiration value and places said unique onetime identification token received from said first network website into its database of authorized unique onetime identification tokens; b. said secondary network server only considers said unique onetime identification token to be valid in said database of authorized unique onetime identification tokens during a period of time defined by said time expiration value; c. said secondary network server applies said time expiration value to said unique onetime identification token beginning when said unique onetime identification token is placed into said database of said authorized unique onetime identification tokens; d. said unique onetime identification token is only considered valid and available for matching for the time period beginning with insertion of said unique onetime identification token into said database of authorized unique onetime identification tokens and its validity expires upon reaching said time expiration value defined as starting with its insertion into said database of authorized unique onetime identification tokens, plus the time expiration value assigned by said first network website; e. said unique onetime identification token that has an expired time expiration value is marked as used and cannot be matched to incoming said unique onetime identification tokens received from said users computing devices.
Description
CROSS REFERENCE
[0001] This application is a continuation in part from U.S. patent application Ser. No. 15/082,727, filed Mar. 28, 2016, which is a continuation of Ser. No. 14/717,352, filed May 20, 2015, which claims priority from provisional No. 62/134,980, filed Mar. 18, 2015.
[0002] This application is related to U.S. patent application Ser. No. 13/297,322 now U.S. Pat. No. 9,715,598, the entire contents of both which are herewith incorporated by reference.
[0003] A unique transaction identifier, which may also include a time expiration value, is assigned by a first network website to an electronic instruction to collect specified distinctive Identifiers from a local/mobile computing device seeking access to said first network website
FIELD OF INVENTION
[0004] This invention relates to defeating an account access attempt by an unauthorized actor seeking to breach an online network or account by capturing identification data from a transmission stream and maliciously adopting said data in an attempt to gain unauthorized account access to a network or account.
BACKGROUND
[0005] As taught in U.S. Pat. No. 9,691,067 & 9,715,598 and referenced herein, an electronic instruction is issued by a first network website to a local/mobile computing device seeking account access to said first network website. Said electronic instruction directs a companion application residing on said local/mobile computing device to collect specified distinctive identifiers from said local/mobile computing device which is seeking account access to said first network website.
[0006] During a registration process of a said local/mobile computing device, specific distinctive identifiers from local/mobile computing devices authorized by the rightful account owners, are collected and stored in a validation database residing on a secondary network website.
[0007] When a local/mobile computing device is seeking account access to a protected first network website, an electronic instruction is sent from said first network website to said local/mobile computing device and specific distinctive identifiers are recollected and sent to the validation database residing on said secondary network website for comparison & match to the values previously registered by rightful account holder. Our concern is the ability of an unauthorized party to insert themselves into the data transmission stream between said local/mobile computing device and said secondary network website, acting as said validation database server. Our concern is also to protect the data transmission stream between said secondary network website acting as said validation database and said first network website. Capture by an unauthorized actor of said collected specified distinctive identifiers could lead to their unauthorized use in gaining account access to said first network website. This is often referred to as a "Man-in-The Middle Attack" or MiTM.
[0008] In a MiTM attack, an unauthorized actor inserts themselves into a data transmission stream to intercept and redirect for their own purposes, the digital information captured from said data transmission stream. In doing so, said unauthorized actor can use the captured digital data to present themselves as an authorized user, and thus gain unauthorized account access to a network website or account.
[0009] Our invention describes a system and method to insure the authenticity of said specified distinctive identifiers collected per said electronic instruction sent by said first network website to said local/mobile computing device which has requested account access to said first network website. This is accomplished by using said unique transaction identifier to specifically alert all stations involved in this access request that said access request has been legitimately made and said unique transaction identifier represents the totally unique nature of said account access request.
[0010] Said electronic instruction directs a companion application residing on said local/mobile computing device to process a set of electronic instructions for collecting specific hardware and/or software identifiers (referred to herein as specified distinctive identifiers) from said local/mobile computing device. Said specified distinctive identifiers are used to build an identification key that can be used to positively identify and authenticate the identity of said local/mobile computing device seeking account access to said first network website. Said companion application present on said local/mobile computing device executes the actions specified within said electronic instruction. These collected specified distinctive identifiers are then secured and sent by said companion application on said local/mobile computing device to said secondary network website, which is used to validate the identity of said local/mobile computing device.
[0011] This disclosure describes the inclusion of a unique transaction identifier assigned to each said electronic instruction to collect specified distinctive identifiers issued by said first network website to said local/mobile computing device seeking account access to said first network website. This unique transaction identifier is unique and represents this, and only this electronic instruction. Said unique transaction identifier thus becomes a totally unique designation for said electronic instruction issued by said first network website to said local/mobile computing device.
[0012] Said first network website also enters said unique transaction identifier into a database of issued unique transaction identifiers residing on said first network website. Issued unique transaction identifiers entered into said database maintained by said first network website, are considered a one-time-use entry and upon receipt of an access approval with a matching unique transaction identifier from said secondary network website, said unique transaction identifier will no longer be considered valid.
[0013] To protect against an instance where a MiTM attack might compromise the contents of a data transmission of specified distinctive identifiers between said local/mobile computing device and said secondary network website, said first network website also sends an a notice of said unique transaction identifier uniquely assigned to this particular electronic instruction, to said secondary network website. Said secondary network website is used to compare said specified distinctive identifiers collected as a result of each electronic instruction and performs a matching function to determine if said local/mobile computing device requesting account access to said first network website has been previously authorized for account access during a registration process.
[0014] The purpose of said first network website sending said unique transaction identifier to said secondary network website is to provide a method of cross-checking the validity of said specified distinctive identifiers received from said local/mobile computing device and submitted to said secondary network website were legitimately collected and authorized by said first network website. When said secondary network website receives said unique transaction identifier from said first network website, it inserts said unique transaction identifier into a database resident on and maintained by said second network website.
[0015] The presence of a said unique transaction identifier in both the data transmission of said specified distinctive identifiers from said local/mobile computing device and said database of unique transaction identifiers residing on said secondary network, allows a cross-check of the authenticity of said specified distinctive identifiers received from said local/mobile computing devices. This assures that the specified distinctive identifiers collected per said transaction were not submitted as a result of a MiTM attack that previously had intercepted a transmission of said specified distinctive identifiers.
[0016] When said secondary network website receives said specified distinctive identifiers from said local/mobile computing device, its intention is to perform a matching function of those specified distinctive identifiers to the authorized specified distinctive identifiers incorporated into, or managed by, said second network website's validation database. The purpose of this matching function is to insure that said local/mobile computing device represented by this collection of said specified distinctive identifiers has been previously authorized for account access to said first network website.
[0017] However, said secondary network website, prior to matching said specified distinctive identifiers collected from said local/mobile computing device, will match said unique transaction identifier associated with said collected specified distinctive identifiers submitted by said local/mobile computing device to said database of said unique transaction identifiers previously provided to said secondary network website by said first network website. Said secondary network website will determine, based on its database of said unique transaction identifiers, if a match exists between said unique transaction identifier assigned to said collected specified distinctive identifiers being submitted by said local/mobile computing device and said unique transaction identifiers residing in said secondary network website's database of said unique transaction identifiers. If a match of said unique transaction identifiers occurs, said secondary network website will allow said specified distinctive identifiers collected from said local/mobile computing device to be matched against said secondary network website's validation database of authorized specified distinctive identifiers. If a match is not confirmed between said unique transaction identifier being submitted from said local/mobile computing device, said specified distinctive identifiers collected from said local/mobile computing device will not be matched with said secondary network website's validation database of authorized specified distinctive identifiers.
[0018] Thus, in the event an unauthorized actor were able to compromise said transmission stream between said local/mobile computing device seeking account access and said secondary network, the distinctive identifiers would be rendered useless, as said secondary network website would have no record or notification of the unique transaction identifier presented from said local/mobile computing device.
[0019] In a further attempt to defeat MiTM attacks, said unique transaction identifier sent by said first network website to said secondary network website and maintained in said secondary network website's database of unique transaction identifiers may also contain a time expiration value.
[0020] It is important to note that while the unique transaction identifier sent to said local/mobile computing device and to said secondary network website are identical, said time expiration value assigned by said first network website to said unique transaction identifiers is only transmitted to said secondary network website and is not included within the unique transaction identifier sent by said first network website to said local/mobile computing device.
[0021] Said time expiration value is supplied with said unique transaction identifier by said first network website to said secondary network website. Said elapsed time value establishes a duration for the validity of said unique control identifier.
[0022] In the event said time expiration value expires, even a valid match of said unique transaction identifier received from said local/mobile computing device to the same unique transaction identifier present in said database of unique transaction identifiers residing on said secondary network website, will be deemed expired and not valid, and said specified distinctive identifiers received from said local/mobile computing device will not be matched to said second network web site's database of authorized specified distinctive identifiers.
[0023] In the event that said unique transaction identifier submitted with specified distinctive identifiers collected from said local/mobile computing device matches a valid unique transaction identifier resident in said database of unique transaction identifiers residing on said secondary network website, said specified distinctive identifiers will be matched against said database of specified distinctive identifiers maintained by said secondary network website. The matching of these specified distinctive identifiers will produce either a match or no match condition.
[0024] Once said secondary network website has determined a match/no match condition, that match/no match result is packaged with said unique transmission identifier and sent to said first network website.
[0025] When said first network website receives said match/no match result with said unique transmission identifier from secondary website network, said first network website first matches said unique transmission identifier against its one-time-use database of said unique transmission identifiers previously issued and maintained in its one-time-use database on said first network website. If said first network website confirms a match of the unique transmission identifier transmitted from said secondary network website to a unique transmission identifier stored in first network websites one-time-use database, the match/no match result from secondary network website will be honored. In the case of a match result for said specified distinctive identifiers and said unique transmission identifier, first network website will grant account or network access to said local/mobile computing device seeking access. In the case of a no match result for said specified distinctive identifiers and said unique transmission identifier, first network website will NOT grant account or network access to said local/mobile computing device seeking access.
Definitions
[0026] Companion Application: A software application executing on said local/mobile computing device that receives said electronic instruction from said first network website, and said electronic instruction defines the collection of said specified distinctive identifiers from said local/mobile computing device on which said companion application is resident. [0027] Data Transmission Stream: A digital communication between said local/remote computing device and a secondary network website and between said secondary network website and said first network website [0028] Electronic Instruction: A notification which includes parameters to be used to collect specified distinctive Identifiers that is sent from a first software program executing on a first network website to a companion application executing on a local/mobile computing device where said local/mobile computing device is seeking account access to said first network website. [0029] First Network Website: An intelligent network website to which said local/mobile computing device is seeking network or account access and said first network website issues said unique control identifier and said electronic instruction to collect specified distinctive identifiers to said local/mobile computing device seeking access to said first network website and said first network website also issues said unique control identifier to said secondary network website. [0030] Local/Mobile Computing Device: Personal computer, Laptop, Smartphone, PDA, Tablet etc or similar mobile or desktop devices containing a processor, memory and storage, and also capable of addressing a network or account via an Internet connection and is seeking access to said first network website. [0031] One-Time-Use: Refers to unique control identifiers maintained in a database on said first and secondary network websites, and whereby said unique control identifiers present in said databases are only allowed to be matched with incoming said unique control identifiers a single time. [0032] Regeneration: The process whereby said companion application resident on said local/mobile computing device extracts anew said specified distinctive identifiers from said local/mobile computing device that is initiating a an access request to said first network website. [0033] Secondary Network Website: An intelligent network website which hosts said validation database used for matching said specified distinctive identifiers drawn from said local/mobile computing device to a database of said specified distinctive identifiers drawn from previously authorized local/mobile computing devices and maintained on said secondary network website. [0034] Specified Distinctive Identifiers: One or more defined device identifiers and/or other digital characteristics, which may be considered unique and collected by a companion application resident on said local/mobile computing device from certain hardware and software modules resident on said local/mobile computing device and for purposes of this disclosure, may also include a unique string of data inputted by the account owner, such as a password, biometric marker, and/or a unique transaction identifier. [0035] Time Expiration Value: A segment of time that defines the period for which said unique transaction identifier is considered valid and available for matching. [0036] Unique Transaction Identifier/Unique Transaction ID: A word, number, letter, symbol, or any combination of those that is used to uniquely identify a transaction that applies to an electronic instruction to collect specified distinctive identifiers that is issued by a first network website to said local/mobile computing device. [0037] Unique One Time Identification Token: A data object whose contents consists of a Unique Transaction Identifier or Unique Transaction ID. [0038] Unique Transaction Identifier Database: A database composed of said unique transaction identifiers that have been issued by said first network website to a local/mobile computing device seeking access to said first network website and said database of unique transaction identifiers is maintained on either or both of said secondary network website and/or said first network website. [0039] Validation Database: A remote database of registered specified distinctive identifiers drawn from previously authorized local/mobile computing devices and said validation database is maintained on said secondary network website.
SUMMARY
[0040] A first exemplary embodiment of this invention describes a system and method for validating the authenticity of said electronic instruction to collect said specified distinctive identifiers which sent from said first network website to said local/mobile computing device seeking network or account access to said first network website. Said first network website attaches a unique onetime identification token to an electronic instruction being sent to a local/mobile computing device. Said first network website also enters said unique onetime identification token into a one-time-use database of said unique onetime identification tokens issued by said first network website and said database is resident on said first network website. Said first network website also sends said unique onetime identification token to said secondary network website, which also maintains a one-time-use database of said unique onetime identification tokens received from said first network website. Said secondary network website will match said unique onetime identification token resident in said one-time-database of unique transaction identifiers resident on said secondary network website to a unique onetime identification token sent to a secondary network website by said local/mobile computing devices seeking access to said first network website. A positive match in said one-time-use database between said unique onetime identification token received from said local/mobile computing device and said unique onetime identification token sent from said first network website will result in said secondary network website allowing said specified distinctive identifiers sent from said local/mobile computing device to be matched against said specified distinctive identifiers resident in said validation database resident on said secondary network website. In the event of a non-match of said unique onetime identification token received from said local/mobile computing device against said one-time-use database of unique onetime identification tokens received from said first network website, said secondary network website will not allow said specified distinctive identifiers sent from said local/mobile computing device to be matched against said database of authorized specified distinctive identifiers resident on said secondary network website.
[0041] A second exemplary embodiment of this invention discloses a system and method for limiting the time-period during which said unique onetime identification token received by said secondary network website from said first network website shall remain valid and available for matching. Said first network website assigns to said unique onetime identification token sent to said secondary network website a time expiration value which defines a segment of time for which said unique onetime identification token received from said first network website shall remain valid. Upon expiration of said time expiration value, said unique onetime identification token received from said first network website will be considered void and cannot be considered for a match against said unique transaction identifiers received from said local/mobile computing devices.
BRIEF DESCRIPTION OF THE DRAWINGS
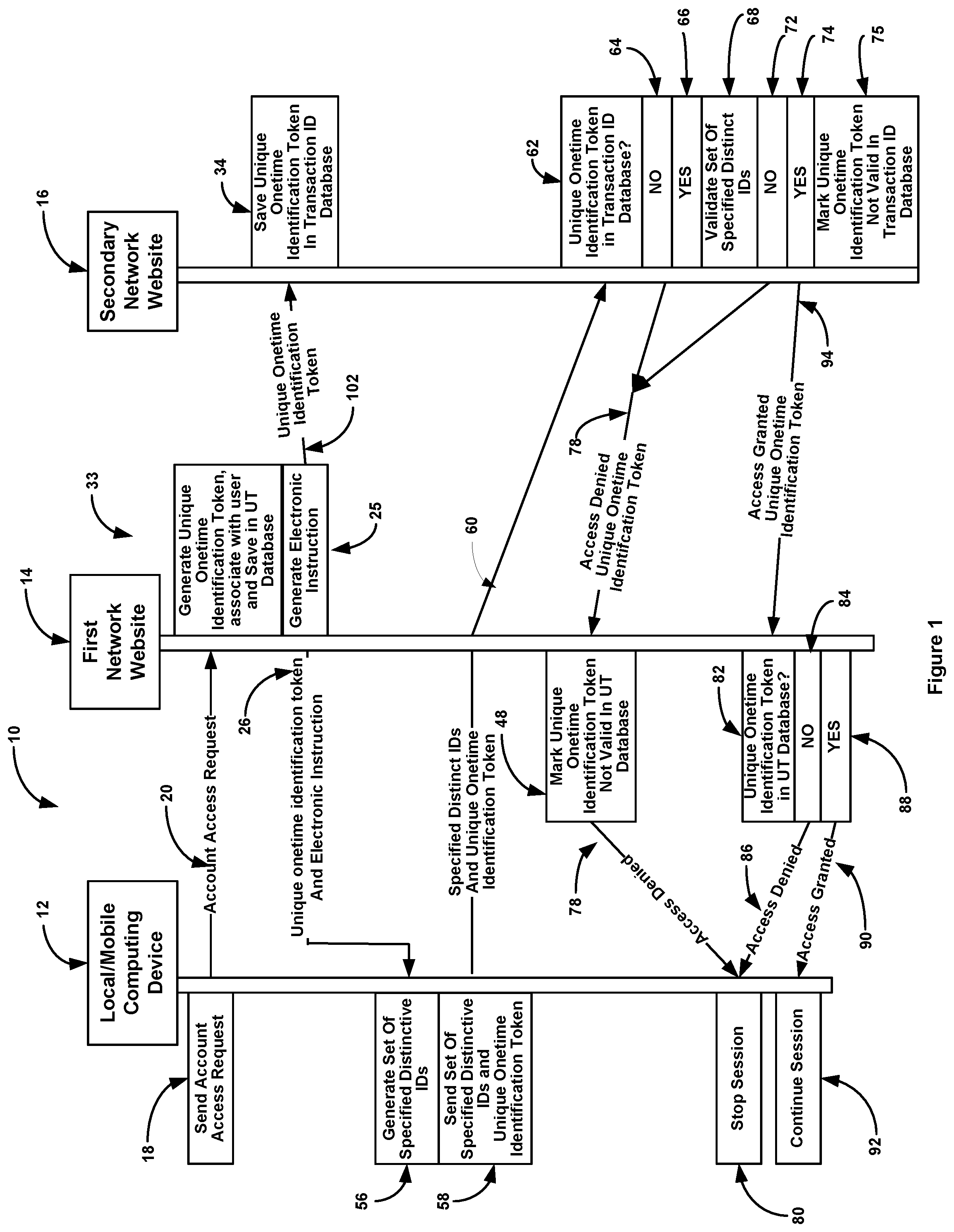
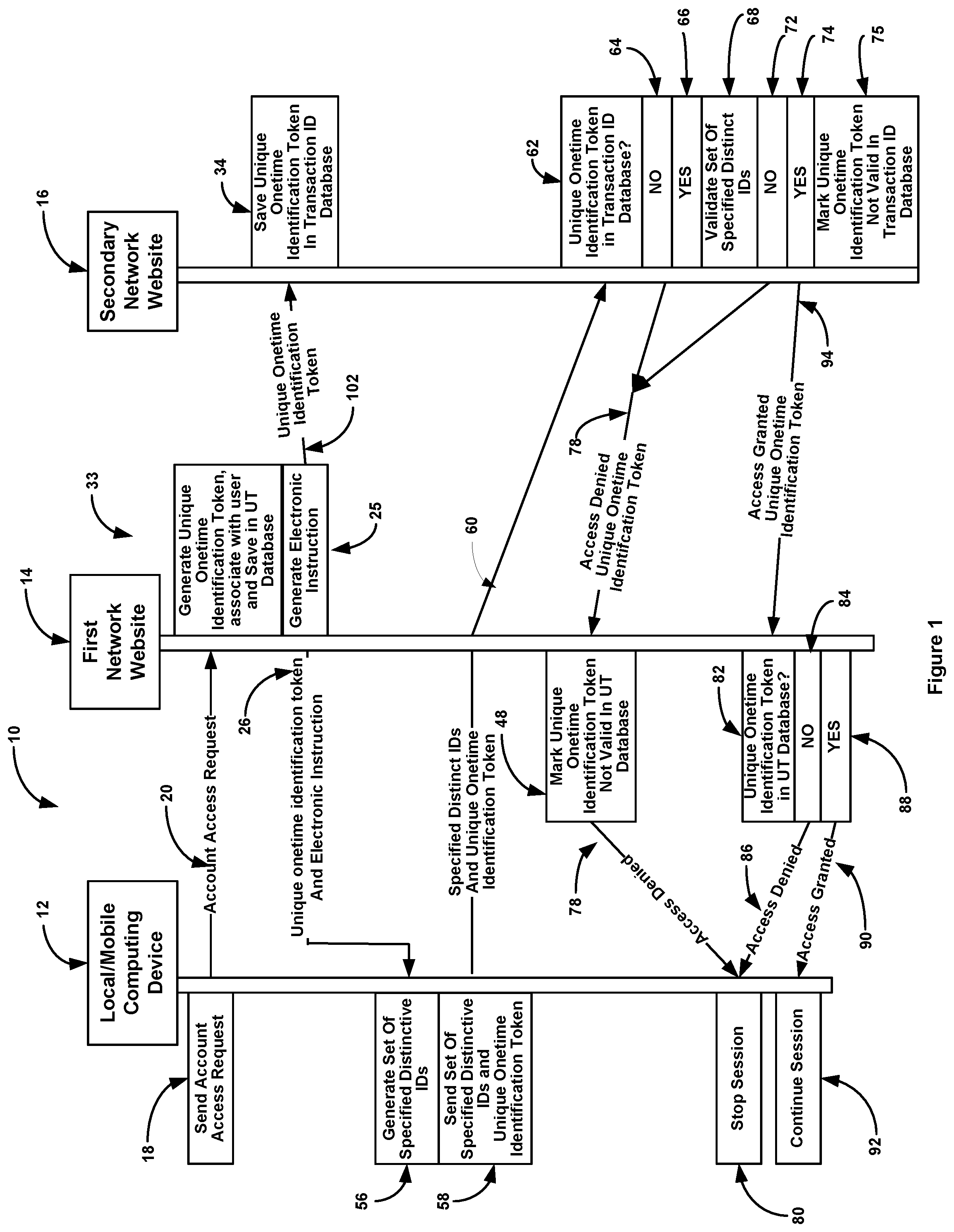
[0042] FIG. 1 shows a depiction of an embodiment showing processing between local/mobile computing device, first network website, and secondary network website;
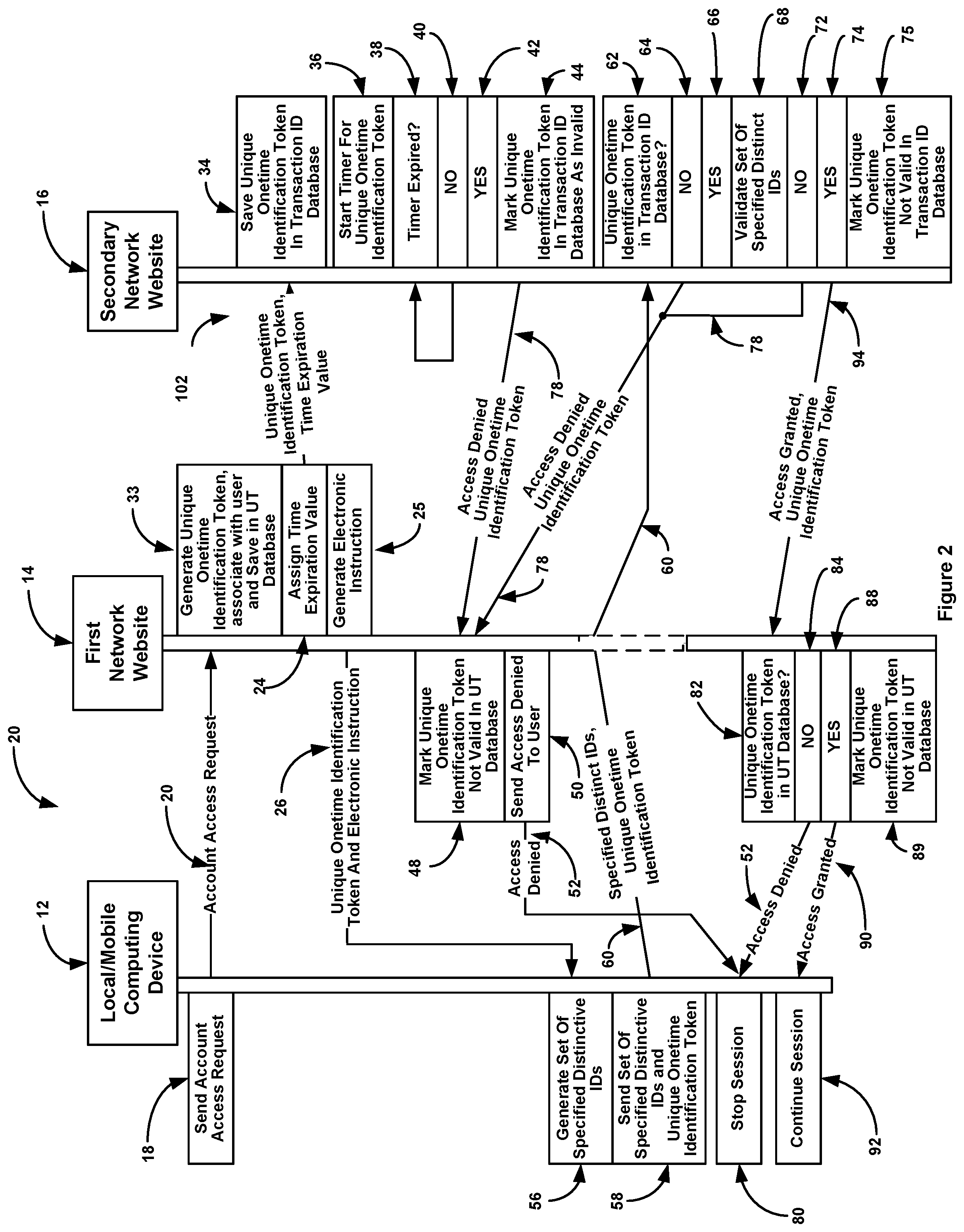
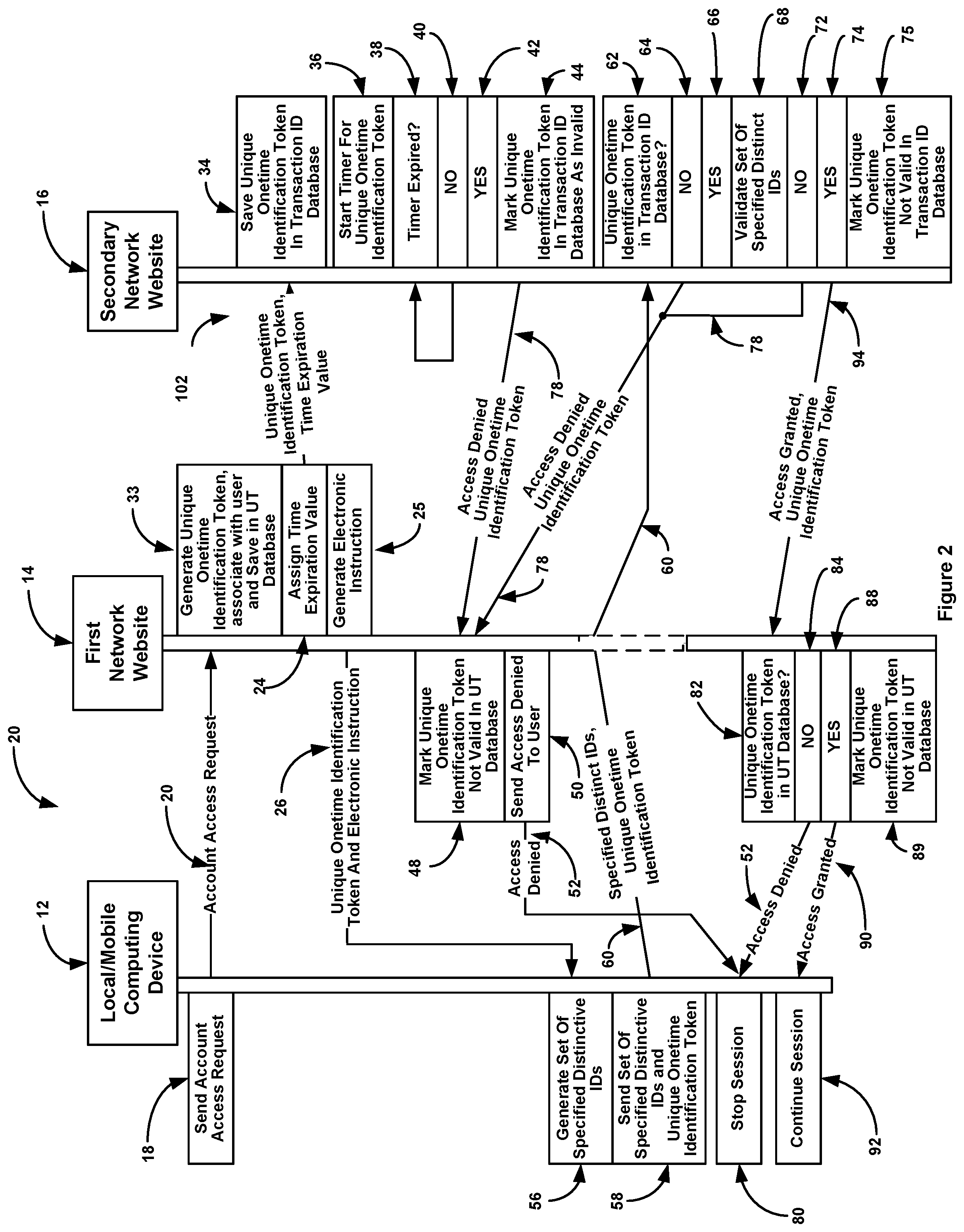
[0043] FIG. 2 shows an embodiment where the unique transaction ID is only valid for a period of time;
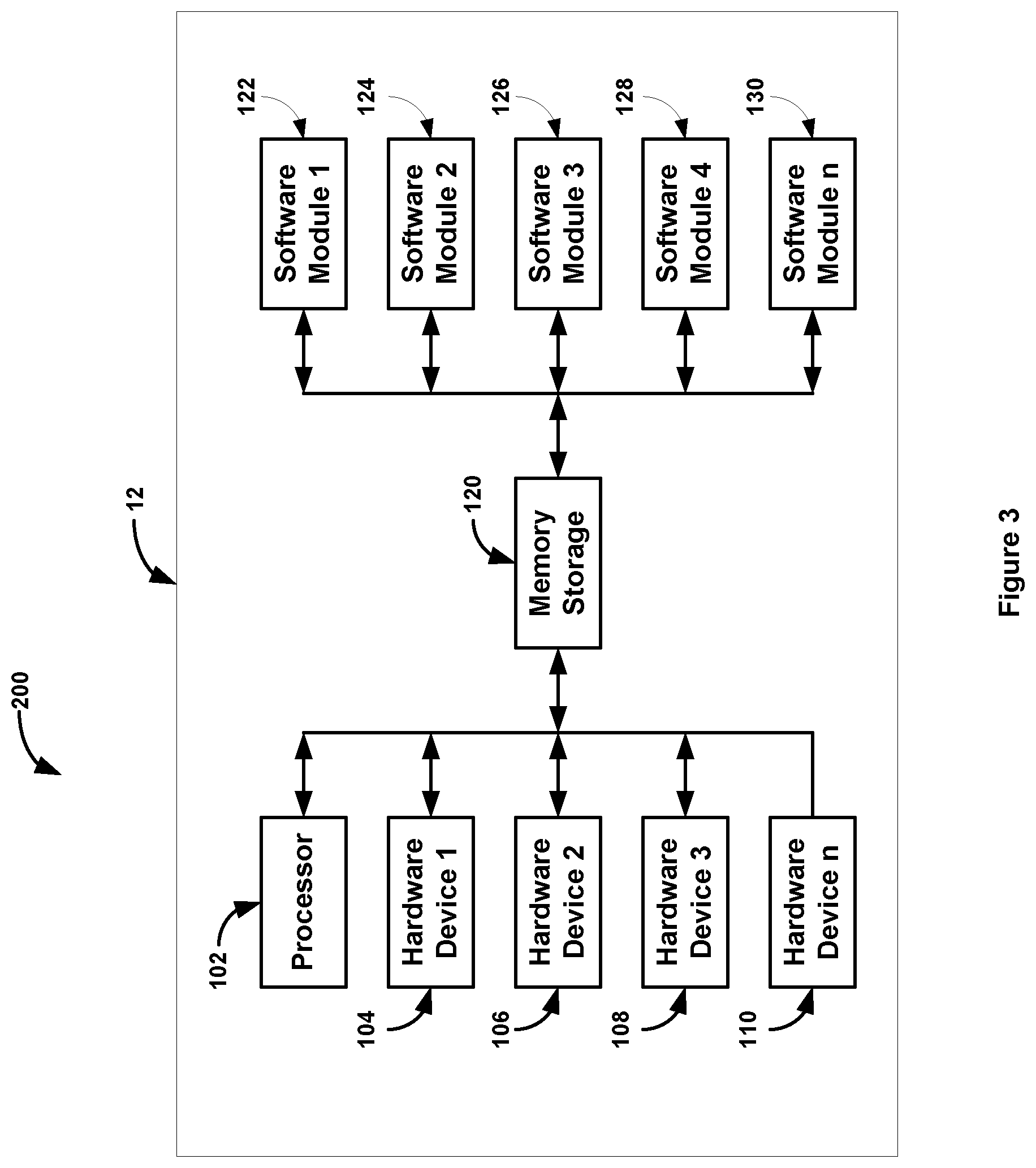
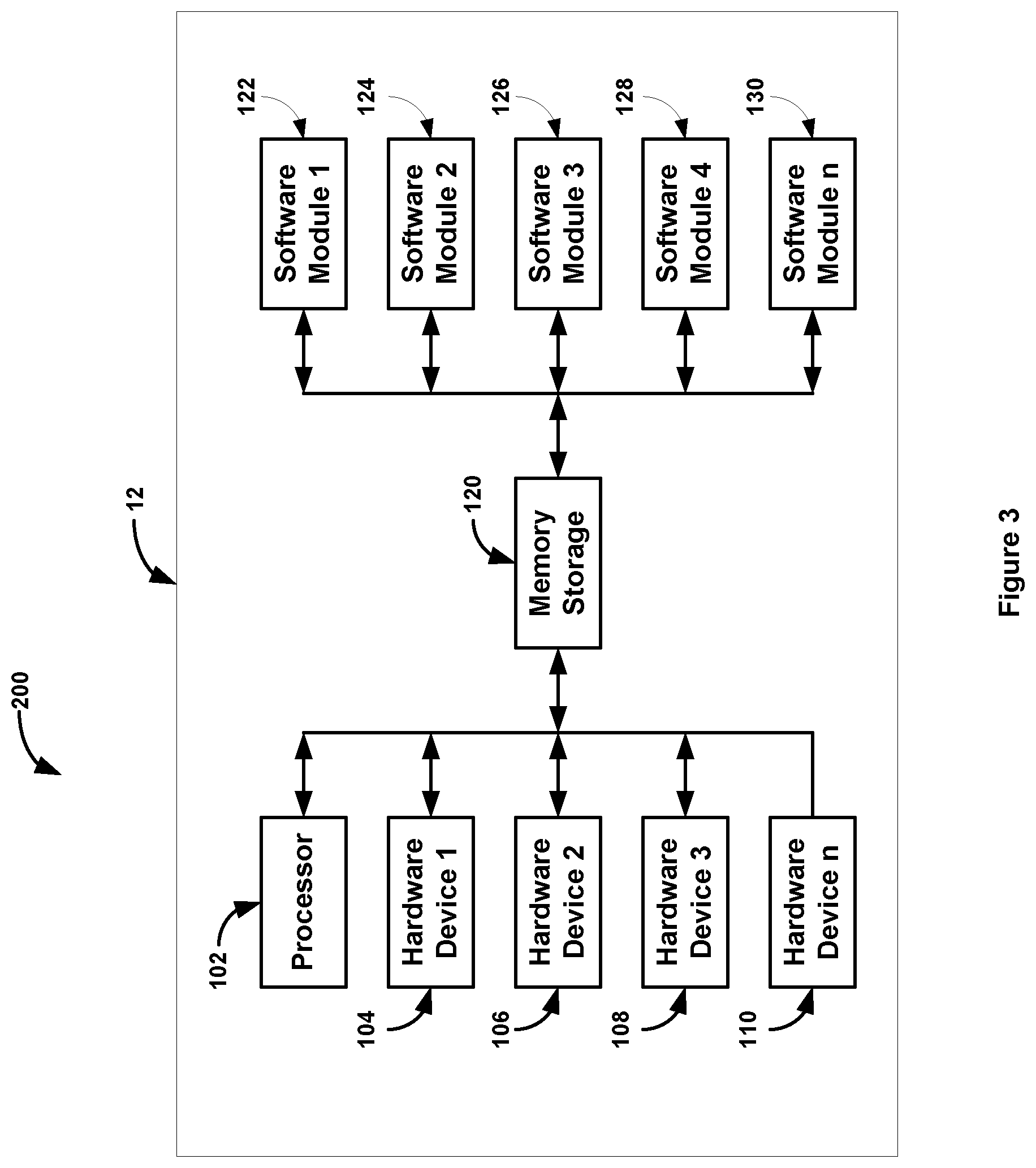
[0044] FIG. 3 shows the major components of local/mobile computing device;
[0045] FIG. 4 shows the major components of first network website; and
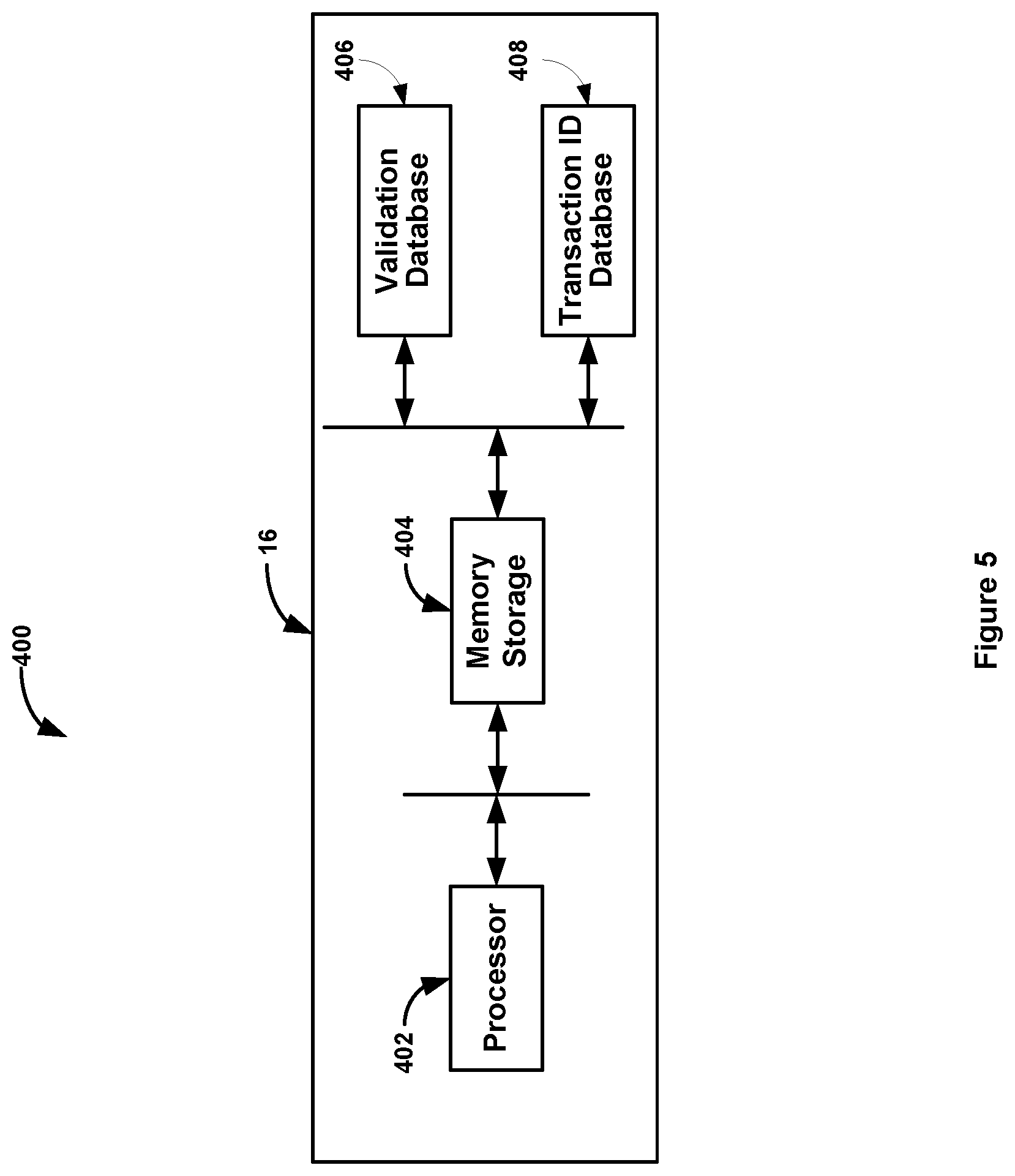
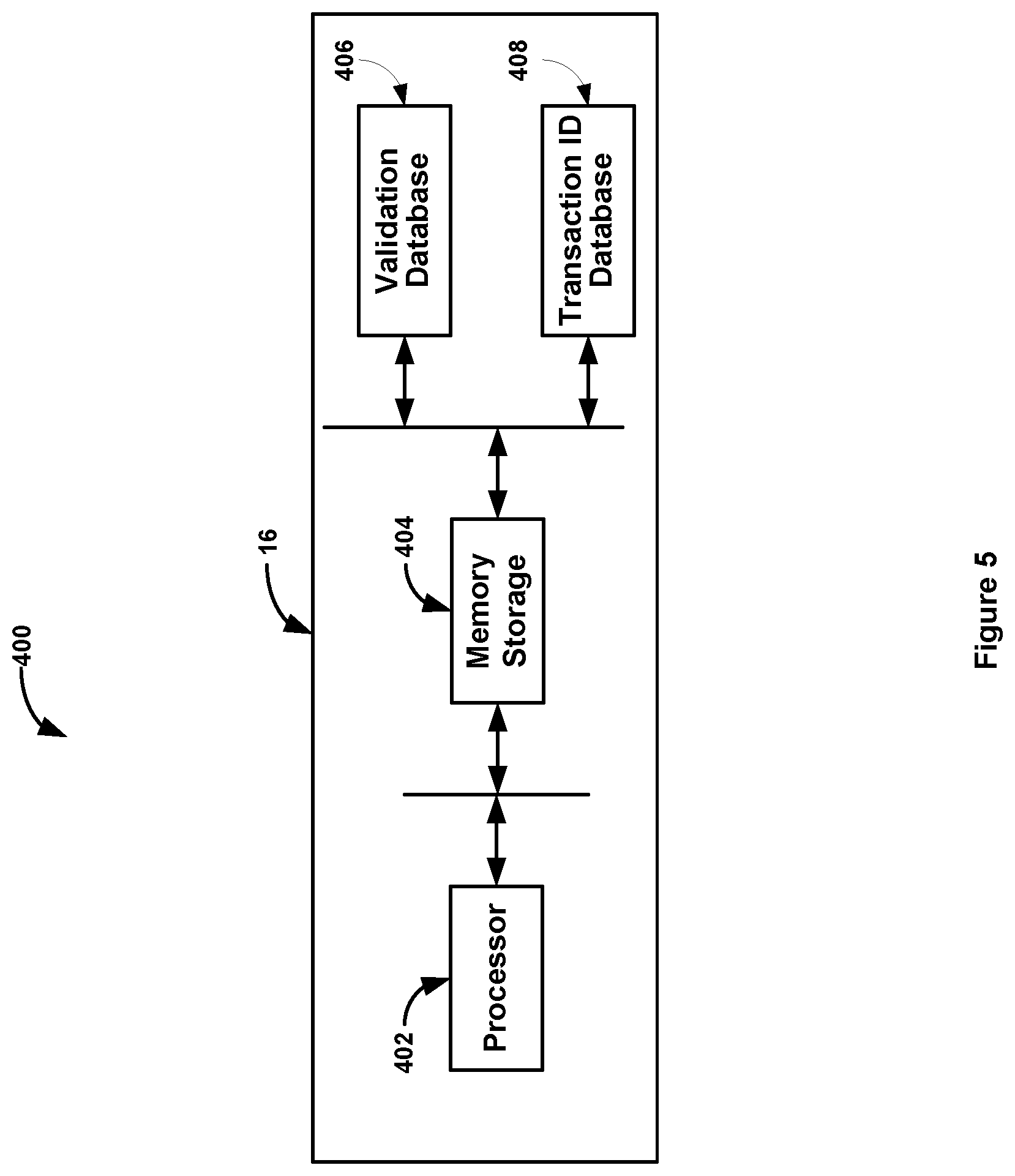
[0046] FIG. 5 shows the major components of secondary network website.
DETAILED DESCRIPTION
[0047] Now referencing FIG. 1 where 10 is a depiction of the invention illustrating local/mobile computing device 12, first network website 14, and secondary network website 16.
[0048] In this depiction, processing begins with process block 18, send signal 20, account access request, to process block 33, generate unique onetime identification token, associate with user and save in UT database. This process block generates a unique onetime identification token identifying this single transaction, associates the unique onetime identification token with the user (local/mobile computing device) and saves the information in local UT database 306 (FIG. 3). This database is resident on first network website 14. After the unique onetime identification token and the associated user is saved in local UT database 306, control falls through to processing block 25, generate electronic instruction. This process block sends signal 26, unique onetime identification token and electronic instruction, to processing block 56, generate set of specified distinctive IDs, and sends signal 102, unique onetime identification token to processing block 34, save unique onetime identification token in transaction ID database (FIG. 5). Processing block 56 receives electronic instruction which specifies which distinctive IDs to gather.
[0049] These IDs may consist of serial numbers or other IDs such as MAC addresses of hardware components/modules and/or serial numbers of software modules residing in local/mobile computing device 12. These IDs are then hashed into hexadecimal numbers that resemble random numbers. After the specified distinctive IDs have been gathered, they are appended with the unique onetime identification token and sent as signal 60, specified distinctive IDs and unique onetime identification token, to decision processing block 62, unique onetime identification token in unique transaction ID database?.
[0050] Decision processing block 62, unique onetime identification token in transaction ID database?, attempts to match the received unique onetime identification token in the unique transaction ID local database 408 (FIG. 5). If the match is not made, control falls through to determination processing block 64, NO, else control is transferred to determination processing block 66, YES.
[0051] If control fell through to determination processing block 64, NO, signal 78, access denied, unique onetime identification token, is send to processing block 48, mark unique onetime identification token not valid in UT Database. After process block 48 marks the unique onetime identification token invalid in UT database 306 (FIG. 4) after which processing block 48 sends signal 78, access denied, to processing block 80, stop session, residing in local/mobile computing device, 12. Process block 80, denies the user's local/mobile computing device from gaining access to first network website 14.
[0052] If control was transferred to determination processing block 66, YES, control will fall through to decision processing block 68, validate received set of specific distinctive IDs. Processing block 68 attempts to match the received specified distinct IDs received in signal 60, to a set of specified distinct IDs resident in local validation database 406. If the match is not made, control falls through to determination processing block 72, NO, else control is transferred to determination processing block 74, YES.
[0053] If control fell through to determination processing block 72, signal 78, access denied, unique onetime identification token, is sent to processing block 48, mark unique onetime identification token not valid in UT database, After process block 48 marks the unique onetime identification token invalid in UT database 306 (FIG. 4) after which processing block 48 sends signal 78, access denied, to processing block 80, stop session, residing in local/mobile computing device, 12. Process block 80, denies the user's local/mobile computing device from gaining access to first network website 14.
[0054] If control fell through to determination processing block 74, YES, signal 94, access granted and unique onetime identification token, is sent to decision processing block 82, unique onetime identification token in UT database?. Processing block 82 attempts to match the received unique onetime identification token to one in the local UT database.
[0055] If a match is made, control is transferred to determination processing block 88, YES. If a match is not made, control falls through to determination processing block 84, NO.
[0056] If control fell through to determination processing block 84, signal 86, access denied, is send to processing block 80, stop session, residing in local/mobile computing device 12. Process block 80, denies the user's local/mobile computing device from gaining access to first network website 14.
[0057] If control was transferred to determination processing block 88, YES, access granted, is send to processing block 92, continue session. Processing block 92 will permit the logon process in user's local/mobile computing device 12 to continue.
[0058] Now referencing FIG. 2 where 20 is a depiction of the invention illustrating local/mobile computing device 12, first network website 14, and secondary network website 16. This depiction shows the invention where the unique transaction ID is only valid for a period of time. This time period is used to prevent a man in the middle attack from succeeding dur to the additional time a MiTM attack requires to capture an original request, alter the request and to send the modified request on to the secondary network website 12. Note that in this depiction, secondary network website 16 contains a timing loop consisting of process blocks 36 through 44 which, if the time expiration value expires, the unique transaction ID is marked as invalid in the transaction ID database 408 resident in secondary network website thus preventing any validation of the set of specified distinctive IDs from being validated.
[0059] In this depiction, processing begins with process block 18, send account access request, as signal 20, account access request, to process block 33, generate unique onetime identification token, associate with user and save in UT database. This process block generates the unique onetime identification token which identifies this single transaction, associates the unique onetime identification token with the user (local/mobile computing device) and saves the information in a local database, UT database, 306, of unique onetime identification tokens and users. This database is resident on first network website 14. After the unique onetime identification token and the associated user is saved in UT database, control falls through to processing block 24, assign time expiration vale.
[0060] This processing block assigns a time expiration value to the unique onetime identification token. This time expiration value is the amount of time the unique transaction ID is valid, after which, the unique transaction ID and the time expiration value is sent as signal 102, unique onetime identification token, time expiration value to processing block 34 save unique transaction ID in transaction ID database, after which control falls through to processing block 36 start timer for unique transaction ID.
[0061] Process blocks 38 through 44 form a timing loop which determines when the time expiration value has expired. Decision processing block 38, timer expired?, determines if the timer value assigned to timer in process block 38, start timer for unique onetime identification token, has expired. After process block 38 makes the decision, control will fall through to determination processing block 40, NO. If the timer has not expired, control will be transferred to decision processing block 38, timer expired?. If the timer has expired, control will fall through to determination processing block 42, YES, after which control will fall through to process block 44, mark unique transaction ID in transaction ID database as invalid.
[0062] This process block will mark the unique onetime identification token contained in the unique transaction ID local database (408 FIG. 5) in secondary network website 16 as invalid then sends signal 78, access denied, unique transaction ID, to process block 48 in first network website 14. Process block, 48, mark unique transaction ID not valid in UT database. This process block marks the unique onetime identification token in UT database (306 FIG. 4) residing in first network website, as not valid after which control will fall through to process block 50, send access denied to user. Process block 50 sends signal 52, access denied, to process block 80, stop session, residing in local/mobile computing device 12. Process block 80, denies the user's local/mobile computing device from gaining access to first network website 14.
[0063] After process block 24, assign timer expiration value, sends signal 102, unique onetime identification token, time expiration value, control will fall through to process block 25, generate electronic instruction. This process block sends signal 26, unique onetime identification token and electronic instruction, to processing block 56, generate set of specified distinctive IDs. Processing block 56 receives electronic instruction specifying which distinctive IDs to gather. These IDs may consist of serial numbers or other IDs such as MAC addresses of hardware components/modules and/or serial numbers of software modules residing in said local/mobile computing device 12. These IDs are then each hashed into a hexadecimal number that appears to be a random number. After the specified distinctive IDs have been gathered, they are appended with the unique onetime identification token and sent as signal 60, specified distinctive IDs and unique onetime identification token to decision processing block 62, unique onetime identification token in unique transaction ID database?.
[0064] Decision processing block 62, unique onetime identification token in database? attempts to match the received unique onetime identification token in signal 60 to one of unique onetime identification tokens contained in the transaction ID database (408 FIG. 5) residing in secondary network website 16. If the match is made, control transfers through to determination processing block 66, YES, else control is falls through to determination processing block 64, NO.
[0065] If control fell through to determination processing block 64, NO, signal 78, access denied, unique onetime identification token, is send to processing block 48, mark unique onetime identification token not valid in UT database (306 FIG. 4). This process block marks the current unique onetime identification token contained in UT database as not valid after which control falls through to process block 50, send access denied to user. This process block sends signal 52, access denied, to process block 80, stop session, residing in local/mobile computing device 12. Process block 80, denies the user's local/mobile computing device from gaining access to first network website 14.
[0066] If control was transferred to determination processing block 66, YES, control will fall through to decision processing block 68, validate received set of specific distinctive IDs. Processing block 68 attempts to match the received specified distinct IDs received in signal 60, to a set of specified distinct IDs resident in local validation database 406. If the match is not made, control falls through to determination processing block 72, NO, else control is transferred to determination processing block 74, YES.
[0067] If control fell through to determination processing block 72, signal 78, access denied unique transaction ID, is sent to processing block 48, mark unique onetime identification token not valid in UT database (306 FIG. 4). If control fell through to determination processing block 74, YES, signal 94, access granted, unique onetime identification token, is sent to decision processing block 82, unique onetime identification token in UT database?. Processing block 82 attempts to match the received unique onetime identification token to one in the local UT database.
[0068] If a match is made, control is transferred to determination processing block 88, YES. If a match is not made, control falls through to determination processing block 84, NO.
[0069] If control fell through to determination processing block 84, NO, signal 86, access denied, is send to processing block 80, stop session, residing in local/mobile computing device 12 after which control is transferred to process block 89, mark unique onetime identification token not valid in UT database. Process block 80, denies the user's local/mobile computing device from gaining access to first network website 14.
[0070] If control was transferred to determination processing block 88, YES, access granted, is send to processing block 92, continue session after which control falls through to process block 89, mark unique onetime identification token not valid in UT database. Processing block 92 will permit the logon process in user's local/mobile computing device 12 to continue.
[0071] Now referencing FIG. 3 where 200 is a depiction of the major components of local/mobile computing device 12. Local/mobile computing device 12 is a cellular phone, tablet computer, laptop computer, or desktop computer. These types of computing devices are well known in the art. These devices generally have hardware modules such as Bluetooth chip sets, Wifi chip sets, USB hubs and ports, processors, audio chip sets, and other hardware modules. Each of these hardware modules have unique serial numbers as well as MAC addresses for any of the modules with radio interfaces or serial interfaces. Software modules executing on these devices also have serial numbers.
[0072] Local/mobile computing device receives signal 26 unique onetime identification token and an electronic instruction from first network website 14. Electronic instruction contains a coded instruction that defines which hardware and/or software identifiers are to be gathered and hashed. Unique onetime identification token is appended or joined to the hashed specified distinctive identifiers and sent, as signal 60, to secondary network website. Local/mobile computing device 12 then waits at processing block 80, stop session, and processing block 92, continue session, for either access denied signal 78 received by process block 80, stop session, or signal 90, access granted, received by processing block 92, continue session, after which local/mobile computing device will be granted access to first network website.
[0073] Now referencing FIG. 4 where 300 is a depiction of the major components of first network website 14. In this depiction, 14 is a network connected server computer. This type of computing devices is well known in the art. First network website consists of a computer processor 302, a memory storage device 304, UT database 306, and first software program 308. Memory storage device 304 may consist of a combination of random access memory and larger storage devices such as hard disk drives and/or solid state drives.
[0074] First software program 308 resides in said memory storage device 304. First software program 308 is executed by computer processor 302 and controls the logon process when local/mobile computing device 12 attempts to logon to first network website 14. When first network website 14 receives a logon account access request 20 from local/mobile computing device 12, first network website 14 generates a unique onetime identification token and saves it in UT database along with an optional time expiration value. First network website then generates an electronic instruction that, along with unique onetime identification token, is sent to local/mobile computing device 12. First network website then sends signal 102, unique onetime identification token, to secondary network website 16. Optional time expiration value may also be sent to secondary network website at the same time as an optional value in signal 102. If said first network website 14 receives an access denied signal 78 from secondary network website 16, it will mark the associated unique onetime identification token residing in UT database as not valid. If first network website 14 receives an access granted, signal 94, from secondary network website 16, first network website 14 will check to see if the associated unique transaction ID is in UT database and if it is and is marked not valid, first network website 14 will send signal 52 access denied to local/mobile computing device 12. This check ensures that a second request to said secondary website 16 by a man-in-the-middle will be denied. If said first network website 14 receives an access granted from said secondary network website 16, said first network website 14 will check to see if the associated unique onetime identification token is currently marked as valid in UT database 306 and if it is not marked invalid, first network website 14 will send signal 90 access granted to local/mobile computing device 12.
[0075] Now referencing FIG. 5 where 400 is a depiction of the major components of secondary network website 16. Secondary network website 16 consists of a computer processor 402, a memory storage device 404, validation database 406 and transaction ID database 408. Memory storage device 404 may consist of a combination of random access memory and larger storage devices such as hard disk drives and/or solid state drives. When secondary network website 16 receives signal 102 unique onetime identification token, said secondary website 16 will save unique transaction ID in transaction ID database 408. If secondary network website 16 also receives optional time expiration value with unique onetime identification token, it will start a timer with the time expiration value after unique onetime identification token has been saved in transaction ID database 408. Once the timer associated with unique onetime identification token has been started, a timing loop ranging from process block 36 to processing block 44 (FIG. 1) will monitor the timer for expiration. If the timer expires before secondary network website 16 receives signal 60 specified distinct IDs and unique onetime identification token, secondary network website 16 will mark unique onetime identification token received in signal 60, in transaction ID database 408 and will send signal 78 access denied, associated unique transaction ID, to first network website 14.
[0076] Once secondary website 16 receives signal 60 specified distinct IDs and unique onetime identification token, secondary network website 16 will first check to verify that unique onetime identification token, received in signal 102, is in transaction ID database 408 and if it is not or has been marked as invalid, secondary network website 16 will send signal 78 access denied, unique onetime identification token to first network website 14. If unique onetime identification token is found in transaction ID database, control falls through to process block 68, validate set of specified distinct IDs received in signal 60. This process block will attempt to match the set of specified distinct IDs in signal 60, specified distinct IDs, unique onetime identification token, against validation database 406. If received set of specified distinct IDs is not matched against any sets of specified distinct IDs in validation database 406, secondary network website sends signal 78, access denied, unique onetime identification token, to first network website 14. If received set of specified distinct IDs is matched against any sets of specified distinct IDs in validation database 406, secondary network website sends signal 94, access granted, unique onetime identification token, to first network website 14 after which control falls through to process block 75, mark unique onetime identification token in transaction ID database as invalid.
* * * * *
D00000

D00001
D00002
D00003
D00004

D00005
XML
uspto.report is an independent third-party trademark research tool that is not affiliated, endorsed, or sponsored by the United States Patent and Trademark Office (USPTO) or any other governmental organization. The information provided by uspto.report is based on publicly available data at the time of writing and is intended for informational purposes only.
While we strive to provide accurate and up-to-date information, we do not guarantee the accuracy, completeness, reliability, or suitability of the information displayed on this site. The use of this site is at your own risk. Any reliance you place on such information is therefore strictly at your own risk.
All official trademark data, including owner information, should be verified by visiting the official USPTO website at www.uspto.gov. This site is not intended to replace professional legal advice and should not be used as a substitute for consulting with a legal professional who is knowledgeable about trademark law.