Wireless Communication Device For Communication In A Wireless Communication Network
QUAGLIA; Elizabeth ; et al.
U.S. patent application number 16/577842 was filed with the patent office on 2020-12-03 for wireless communication device for communication in a wireless communication network. The applicant listed for this patent is Huawei Technologies Co., Ltd.. Invention is credited to Elizabeth QUAGLIA, Benjamin SMYTH, Tsz Hon YUEN.
| Application Number | 20200382949 16/577842 |
| Document ID | / |
| Family ID | 1000005218681 |
| Filed Date | 2020-12-03 |
| United States Patent Application | 20200382949 |
| Kind Code | A9 |
| QUAGLIA; Elizabeth ; et al. | December 3, 2020 |
WIRELESS COMMUNICATION DEVICE FOR COMMUNICATION IN A WIRELESS COMMUNICATION NETWORK
Abstract
Embodiments relate to a wireless communication device of a group of wireless communication devices configured to communicate with a base station, the wireless communication device comprising a transceiver configured to receive a token from the base station and a processor configured to generate a first data structure on the basis of a function of the token and of a key k.sub.i of the wireless communication device and a second data structure comprising an identity id.sub.i of the wireless communication device, wherein the transceiver is further configured to broadcast the first data structure and the second data structure to the group of wireless communication devices and the base station.
| Inventors: | QUAGLIA; Elizabeth; (Munich, DE) ; SMYTH; Benjamin; (Munich, DE) ; YUEN; Tsz Hon; (Singapore, SG) | ||||||||||
| Applicant: |
|
||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|
| Prior Publication: |
|
||||||||||
| Family ID: | 1000005218681 | ||||||||||
| Appl. No.: | 16/577842 | ||||||||||
| Filed: | September 20, 2019 |
Related U.S. Patent Documents
| Application Number | Filing Date | Patent Number | ||
|---|---|---|---|---|
| PCT/CN2018/079457 | Mar 19, 2018 | |||
| 16577842 | ||||
| Current U.S. Class: | 1/1 |
| Current CPC Class: | H04W 12/001 20190101; H04W 12/00305 20190101; H04L 9/3242 20130101; H04W 12/0401 20190101; H04L 9/0643 20130101; H04L 9/0825 20130101; H04W 12/06 20130101 |
| International Class: | H04W 12/00 20060101 H04W012/00; H04W 12/04 20060101 H04W012/04; H04W 12/06 20060101 H04W012/06; H04L 9/06 20060101 H04L009/06; H04L 9/32 20060101 H04L009/32; H04L 9/08 20060101 H04L009/08 |
Foreign Application Data
| Date | Code | Application Number |
|---|---|---|
| Mar 20, 2017 | EP | 17161898.6 |
Claims
1. A wireless communication device of a group of wireless communication devices configured to communicate with a base station, the wireless communication device comprising: a transceiver configured to receive a token from the base station; and a processor configured to generate a first data structure on the basis of a function of the token and of a key k.sub.i of the wireless communication device and a second data structure comprising an identity id.sub.i of the wireless communication device; wherein the transceiver is further configured to broadcast the first data structure and the second data structure to the group of wireless communication devices and the base station.
2. The wireless communication device of claim 1, wherein the function of the token and of the key k.sub.i of the wireless communication device has a uniform output distribution.
3. The wireless communication device of claim 1, wherein the first data structure is a Bloom filter.
4. The wireless communication device of claim 1, wherein the processor is further configured to compute the key k.sub.i of the wireless communication device on the basis of the following equation: k.sub.i=H'(e(H(id.sub.BS),H(id.sub.i).sup.s),r), wherein r is the token, H' and H are cryptographic hash functions, id.sub.BS is an identity of the base station, e is a bilinear pairing function, and s is a master key.
5. The wireless communication device of claim 3, wherein the length of the Bloom filter m, the number L of the wireless communication devices of the group of wireless communication devices, and the number n of cryptographic hash functions for adding an element to the Bloom filter are related by the following equation: 2.sup.-n=(0.6185).sup.m/L.
6. The wireless communication device of claim 1, wherein the processor is further configured to compute the key k.sub.i of the wireless communication device on the basis of the following equation: k.sub.i=tsP, wherein t is a random integer, P is a public parameter, tP is the token, (x, (P, Y=xP)) is a key pair, s=r+xH(R, id.sub.i), H is a cryptographic hash function, and r.di-elect cons..sub.RZ.sub.q*, R=rP.
7. The wireless communication device of claim 1, wherein the processor is further configured to compute the key k.sub.i of the wireless communication device on the basis of the following equation: k.sub.i=H'(sR'+sH(R',id.sub.BS)Y,t), wherein (R, s) is a private key of the wireless communication device (101i), (R', s') is a private key of the base station, t is the token, r.di-elect cons..sub.RZ.sub.q*, R=rP, (x, (P, Y=xP)) is a key pair, s=r+xH(R, id.sub.i), and H' and H are cryptographic hash functions.
8. A wireless communication device of a group of wireless communication devices configured to communicate with a base station and the group of wireless communication devices, the wireless communication device comprising: a transceiver configured to receive a token from the base station, a first data structure generated on the basis of a function of the token and of a key k.sub.i of a further wireless communication device and a second data structure comprising an identity id.sub.i of the further wireless communication device; and a processor configured to add a data element based on a function of the token and of a key k.sub.j of the wireless communication device to the first data structure, and to add an identity id.sub.j of the wireless communication device to the second data structure for obtaining a modified first data structure and a modified second data structure; wherein the transceiver is further configured to broadcast the modified first data structure and the modified second data structure to the group of wireless communication devices and the base station.
9. The wireless communication device of claim 8, wherein the function of the token and of the key k.sub.j of the wireless communication device has a uniform output distribution.
10. The wireless communication device of claim 8, wherein at least one of the first data structure or modified first data structure is a Bloom filter.
11. The wireless communication device of claim 8, wherein the processor is further configured to compute the key k.sub.j of the wireless communication device on the basis of the following equation: k.sub.j=H'(e(H(id.sub.Bs),H(id.sub.j).sup.s),r), wherein r is the token, H' and H are cryptographic hash functions, id.sub.BS is an identity of the base station, e is a bilinear pairing function, and s is a master key.
12. The wireless communication device of claim 8, wherein the processor is further configured to compute the key k.sub.j of the wireless communication device on the basis of the following equation: k.sub.j=tsP, wherein t is an integer, P is a public parameter, tP is the token, (x, (P, Y=xP)) is a key pair, s=r+xH(R, id.sub.j), H is a cryptographic hash function, and r.di-elect cons..sub.RZ.sub.q*, R=rP.
13. The wireless communication device of claim 8, wherein the processor is further configured to compute the key k.sub.j of the wireless communication device on the basis of the following equation: k.sub.j=H'(sR'+sH(R',id.sub.BS)Y,t), wherein (R, s) is a private key of the wireless communication device, (R', s') is a private key of the base station, t is the token, r.di-elect cons..sub.RZ.sub.q*, R=rP, (x, (P, Y=xP)) is a key pair, s=r+xH(R, id.sub.j), and H' and H are cryptographic hash functions.
14. A base station configured to communicate with at least one wireless communication device of a group of wireless communication devices in a wireless communication network, the base station comprising: a transceiver configured to receive a first data structure and a second data structure generated by the at least one wireless communication device, wherein the first data structure is based on a function of a token provided by the base station and of a key k.sub.i of the at least one wireless communication device, and wherein the second data structure comprises an identity id.sub.i of the at least one wireless communication device; and a processor configured to derive the key k.sub.i of the at least one wireless communication device on the basis of the second data structure and to authenticate the at least one wireless communication device on the basis of the key k.sub.i and of the first data structure of the at least one wireless communication device.
15. The base station of claim 14, wherein the processor is further configured to derive the key k.sub.i of the at least one wireless communication device on the basis of the following equation: k.sub.i=H'(e(H(id.sub.BS).sup.s,H(id.sub.i)),r), wherein r is the token, H' and H are cryptographic hash functions, id.sub.BS is an identity of the base station, and s is a master key.
16. The base station of claim 14, wherein the processor is further configured to derive the key k.sub.i of the at least one wireless communication device on the basis of the following equation: k.sub.i=tR+tH(R,id.sub.i)Y, wherein t is an integer, P is a public parameter, tP is the token, (x, (P, Y=xP)) is a key pair, s=r+xH(R, id.sub.i), H is a cryptographic hash function, and r.di-elect cons..sub.RZ.sub.q.sup.*, R=rP.
17. The base station of claim 14, wherein the processor is further configured to derive the key k.sub.i of the at least one wireless communication device on the basis of the following equation: k.sub.i=H'(s'R+s'H(R, id.sub.i)Y, t), wherein (R, s) is a private key of the at least one wireless communication device, (R', s') is a private key of the base station, t is the token, r.di-elect cons..sub.R Z.sub.q.sup.*, R=rP, (x, (P, Y=xP)) is a key pair, s=r+xH(R, id.sub.i), and H' and H are cryptographic hash functions.
Description
CROSS-REFERENCE TO RELATED APPLICATIONS
[0001] This application is a continuation of International Application No. PCT/CN2018/079457, filed on Mar. 19, 2018, which claims priority to European Patent Application No. EP17161898.6, filed on Mar. 20, 2017. The disclosures of the aforementioned applications are hereby incorporated by reference in their entireties.
TECHNICAL FIELD
[0002] In general, embodiments of the present invention relate to security in wireless communication systems. In particular, the embodiments relate to a wireless communication device for communication in a wireless communication network.
BACKGROUND
[0003] In an all-connected world, the Internet of Things (IoT) is becoming more and more important. A lot of devices can establish contact and communicate with each other, and the security of such communications is of paramount importance. Typically, in such an environment, there is a disparity between the resources associated to each device, for instance power and memory, which can range from large devices e.g., base stations or fixed readers, to small devices e.g., mobile nodes or sensors. Developing security protocols which successfully take such disparity into consideration is very important in order to allow a secure communication among different devices.
[0004] For the development of the IoT, several proposals for Future Network Architectures (FNA) are being put forth, and a clear common trait among such proposals is the importance of the identities of the communication devices. The basic idea of such proposals is to associate to each device an identity, and, therefore, the field of Identity-Based Cryptography (IBC) can play a key role.
[0005] The problem of authenticating a group of entities in an efficient way has also been studied in the prior art. In particular, the idea of aggregating signatures, i.e., putting together several signatures so that only a single signature should be verified, has emerged both in the symmetric and asymmetric setting of cryptography.
[0006] In the work "Aggregate message authentication codes", Topics in Cryptology--CT-RSA (2008) by Katz and Lindell, aggregate message authentication codes (MAC) are proposed. The basic idea is to have multiple MAC tags, computed by (possibly) different senders on multiple (possibly different) messages, which can be aggregated into a shorter tag that can still be verified by a recipient who shares a distinct key with each sender.
[0007] In the work "HB#: Increasing the Security and Efficiency of HB+", Eurocrypt (2008) by Gilbert H. et al., symmetric solutions are discussed and a lightweight three-pass symmetric key authentication protocol is introduced that extends a protocol by Hopper and Blum (HB) to fix a security problem. Furthermore, the aggregate message authentication codes (MAC), as discussed above, belong to the symmetric solutions as well.
[0008] Asymmetric solutions can make use of public-key aggregate signatures as presented, for example, in the work "Aggregate and verifiably encrypted signatures from bilinear maps", Eurocrypt (2003), by Boneh et al. and in the work "Sequential aggregate signatures and multi-signatures without random oracles", Eurocrypt (2006), by Lu et al. The verifying entity or base station only needs to know the public key of the senders (instead of a shared key between the verifier and each sender). Most of the existing solutions rely on bilinear pairings and, therefore, are inefficient and inadequate for the IoT setting.
[0009] Although the above mentioned solutions address the problem of authenticating a group of resource-constrained devices to a verifying entity or base station with larger resources, they, however, are not group authentication schemes, they are inefficient, and they are not identity-based in the case of symmetric solutions.
[0010] Therefore, there is a need for improved devices for communication in a wireless communication network, which, in particular, allow to solve the problem of authenticating a group of resource-constrained devices to a base station with larger resources, where all the entities are equipped with identities, and are immerged in an identity-based cryptography (IBC) infrastructure.
SUMMARY
[0011] It is an object of the embodiments to provide for improved devices for communication in a wireless communication network.
[0012] The foregoing and other objects are achieved by the subject matter of the independent claims. Further implementation forms are apparent from the dependent claims, the description and the figures.
[0013] According to a first aspect, an embodiment relates to a wireless communication device of a group of wireless communication devices configured to communicate with a base station, the wireless communication device comprising a transceiver configured to receive a token from the base station, and a processor configured to generate a first data structure on the basis of a function of the token and of a key k.sub.i of the wireless communication device and a second data structure comprising an identity id.sub.i of the wireless communication device, wherein the transceiver is further configured to broadcast the first data structure and the second data structure to the group of wireless communication devices and the base station.
[0014] In a first possible implementation form of the wireless communication device according to the first aspect as such, the function of the token and of the key k.sub.i of the wireless communication device has a uniform output distribution, i.e. an output that is looking random.
[0015] In a second possible implementation form of the wireless communication device according to the first aspect as such or the first implementation form thereof, at least one of the first data structure or modified first data structure is a Bloom filter.
[0016] In a third possible implementation form of the wireless communication device according to the first aspect as such or the first or second implementation form thereof, the processor is further configured to compute the key k.sub.i of the wireless communication device on the basis of the following equation:
k.sub.i=H'(e(H(id.sub.BS),H(id.sub.i).sup.s),r),
wherein r is the token, H' and H are cryptographic hash functions, id.sub.BS is an identity of the base station, e is a bilinear pairing function, and s is a master key. In an implementation form, s can be a master key available to the base station.
[0017] In a fourth possible implementation form of the wireless communication device according to the second implementation form of the first aspect, the length of the Bloom filter m, the number L of the wireless communication devices of the group of wireless communication devices, and the number n of cryptographic hash functions for adding an element to the Bloom filter are related by the following equation:
2.sup.-n=(0.6185).sup.m/L,
[0018] In a fifth possible implementation form of the wireless communication device according to the first aspect as such or the first or second implementation form thereof, the processor is further configured to compute the key k.sub.i of the wireless communication device on the basis of the following equation:
k.sub.i=tsP,
wherein t is a random integer, P is a public parameter, tP is the token, (x, (P, Y=xP)) is a key pair, s=r+xH(R, id.sub.i), H is a cryptographic hash function, and r.di-elect cons..sub.RZ.sub.q*, R=rP.
[0019] In a sixth possible implementation form of the wireless communication device according to the first aspect as such or the first or second implementation form thereof, the processor is further configured to compute the key k.sub.i of the wireless communication device on the basis of the following equation:
k.sub.i=H'(sR'+sH(R',id.sub.BS)Y,t),
wherein (R, s) is a private key of the wireless communication device, (R', s') is a private key of the base station, t is the token, r.di-elect cons..sub.RZ.sub.q*, R=rP, (x, (P, Y=xP)) is a key pair, s=r+xH(R, id.sub.i), and H' and H are cryptographic hash functions.
[0020] According to a second aspect, an embodiment relates to a wireless communication device of a group of wireless communication devices configured to communicate with a base station and the group of wireless communication devices, the wireless communication device comprising a transceiver configured to receive a token from the base station, a first data structure generated on the basis of a function of the token and of a key k.sub.i of a further wireless communication device and a second data structure comprising an identity id.sub.i of the further wireless communication device, and a processor configured to add a data element based on a function of the token and of a key k.sub.j of the wireless communication device to the first data structure, and to add an identity id.sub.j of the wireless communication device to the second data structure for obtaining a modified first data structure and a modified second data structure, wherein the transceiver is further configured to broadcast the modified first data structure and the modified second data structure to the group of wireless communication devices and the base station.
[0021] In a first possible implementation form of the wireless communication device according to the second aspect as such, the function of the token and of the key k.sub.j of the wireless communication device has a uniform output distribution.
[0022] In a second possible implementation form of the wireless communication device according to the second aspect as such or the first implementation form thereof, the first data structure is a Bloom filter.
[0023] In a third possible implementation form of the wireless communication device according to the second aspect as such or the first or second implementation form thereof, the processor is further configured to compute the key k.sub.j of the wireless communication device on the basis of the following equation:
k.sub.j=H'(e(H(id.sub.B),H(id).sup.s),r),
wherein r is the token, H' and H are cryptographic hash functions, id.sub.BS is an identity of the base station, e is a bilinear pairing function, and s is a master key.
[0024] In a fourth possible implementation form of the wireless communication device according to the second aspect as such or the first or second implementation form thereof, the processor is further configured to compute the key k.sub.j of the wireless communication device on the basis of the following equation:
k.sub.j=tsP,
wherein t is an integer, P is a public parameter, tP is the token, (x, (P, Y=xP)) is a key pair, s=r+xH(R, id.sub.j), H is a cryptographic hash function, and r.di-elect cons..sub.RZ.sub.q*, R=rP.
[0025] In a fifth possible implementation form of the wireless communication device according to the second aspect as such or the first or second implementation form thereof, the processor is further configured to compute the key k.sub.j of the wireless communication device on the basis of the following equation:
k.sub.j=H'(sR'+sH(R',id.sub.BS)Y,t),
wherein (R, s) is a private key of the wireless communication device, (R', s') is a private key of the base station, t is the token, r.di-elect cons..sub.RZ.sub.q*, R=rP, (x, (P, Y=xP)) is a key pair, s=r+xH(R, id.sub.j), and H' and H are cryptographic hash functions.
[0026] According to a third aspect, an embodiment relates to a base station configured to communicate with at least one wireless communication device of a group of wireless communication devices in a wireless communication network, the base station comprising a transceiver configured to receive a first data structure and a second data structure generated by the at least one wireless communication device, wherein the first data structure is based on a function of a token provided by the base station and of a key k.sub.i of the at least one wireless communication device, and wherein the second data structure comprises an identity id.sub.i of the at least one wireless communication device, and a processor configured to derive the key k.sub.i of the at least one wireless communication device on the basis of the second data structure and to authenticate the at least one wireless communication device on the basis of the key k.sub.i and of the first data structure of the at least one wireless communication device.
[0027] In a first possible implementation form of the base station according to the third aspect as such, the processor is further configured to derive the key k.sub.i of the at least one wireless communication device on the basis of the following equation:
k.sub.i=H'(e(H(id.sub.BS).sup.s,H(id.sub.i)),r),
wherein r is the token, H' and H are cryptographic hash functions, id.sub.BS is an identity of the base station, and s is a master key.
[0028] In a second possible implementation form of the base station according to the third aspect as such, the processor is further configured to derive the key k.sub.i of the at least one wireless communication device on the basis of the following equation:
k.sub.i=tR+tH(R,id.sub.i)Y,
wherein t is an integer, P is a public parameter, tP is the token, (x, (P, Y=xP)) is a key pair, s=r+xH(R, id.sub.i), H is a cryptographic hash function, and r.di-elect cons..sub.RZ.sub.q*, R=rP.
[0029] In a third possible implementation form of the base station according to the third aspect as such, the processor is further configured to derive the key k.sub.i of the at least one wireless communication device on the basis of the following equation:
k.sub.i=H'(s'R+s'H(R,id.sub.i)Y,t),
wherein (R, s) is a private key of the at least one wireless communication device, (R', s') is a private key of the base station, t is the token, r.di-elect cons..sub.RZ.sub.q*, R=rP, (x, (P, Y=xP)) is a key pair, s=r+xH(R, id.sub.i), and H' and H are cryptographic hash functions.
[0030] The embodiments can be implemented in hardware and/or software.
BRIEF DESCRIPTION OF THE DRAWINGS
[0031] Further embodiments of the invention will be described with respect to the following figures, wherein:
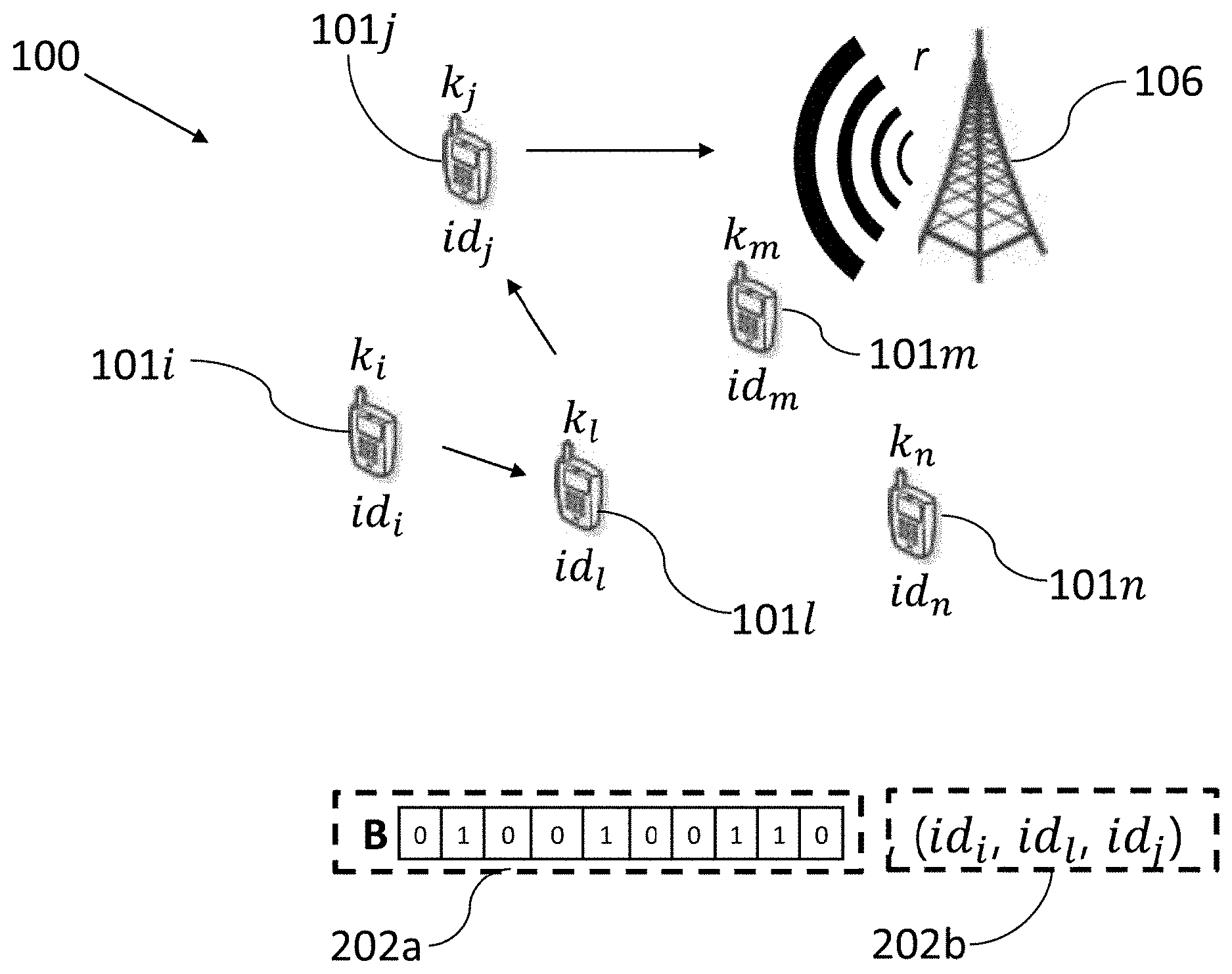
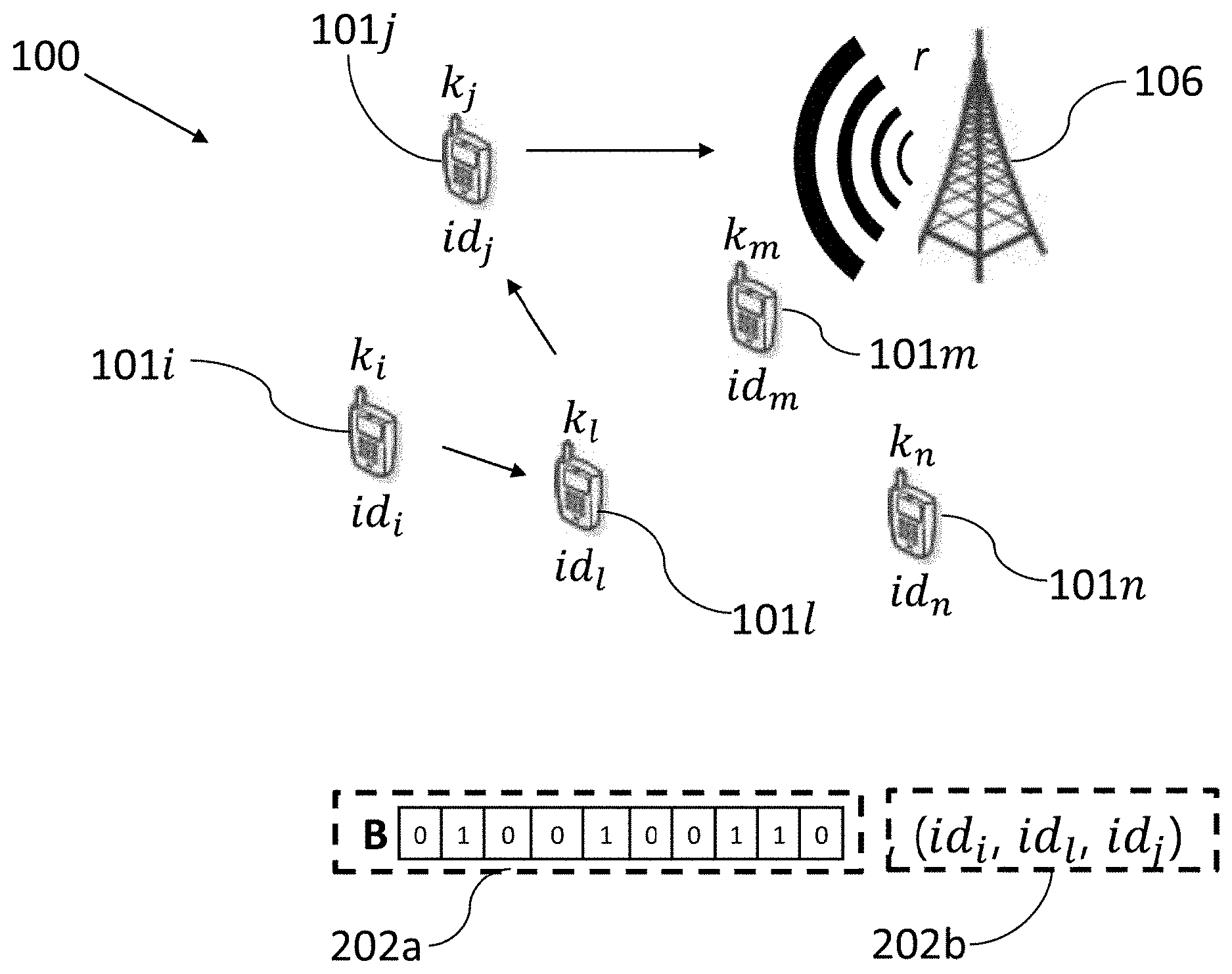
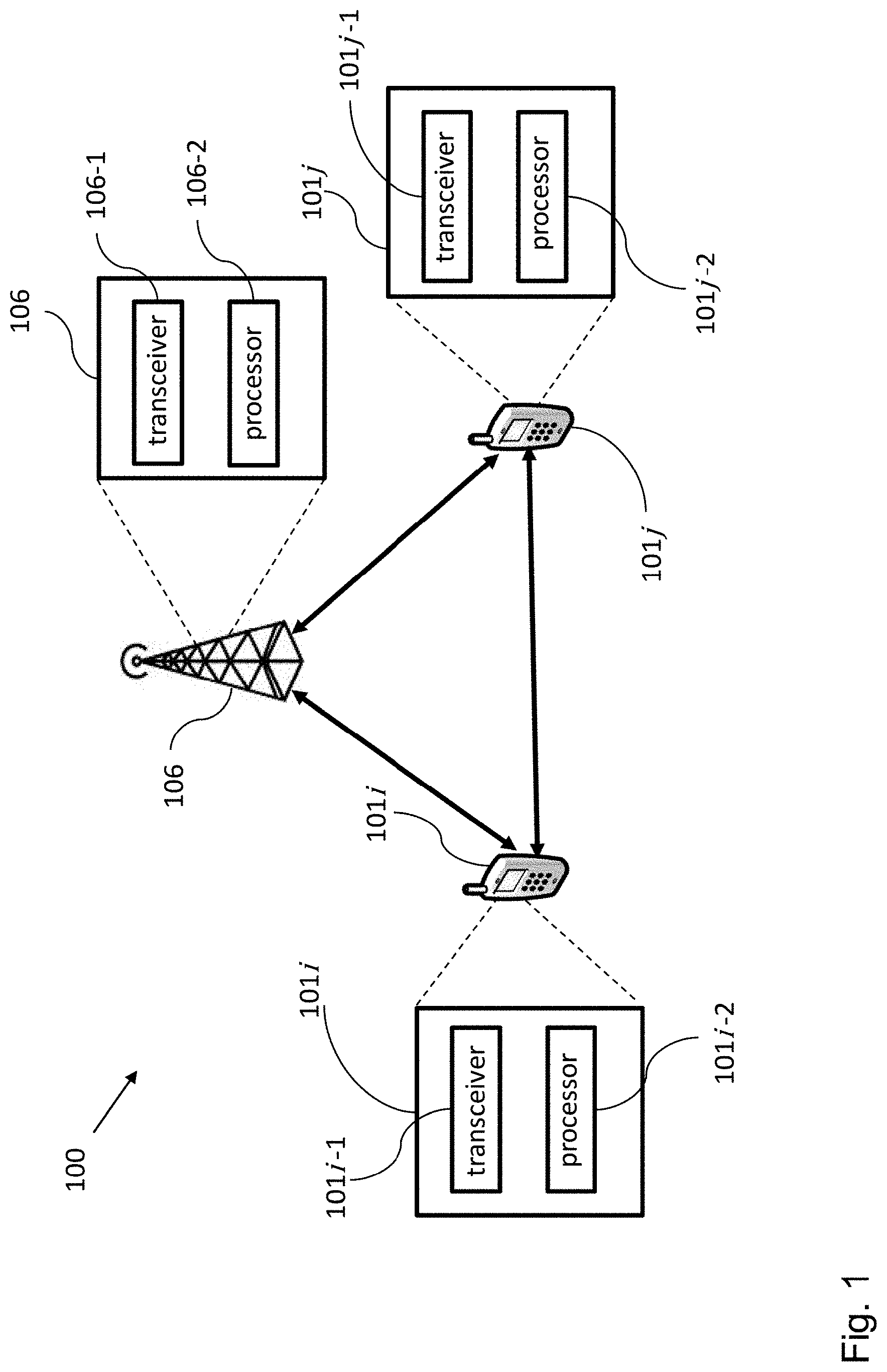
[0032] FIG. 1 shows a schematic diagram of a wireless communication system comprising a wireless communication device, a further wireless communication device, and a base station according to embodiments of the invention;
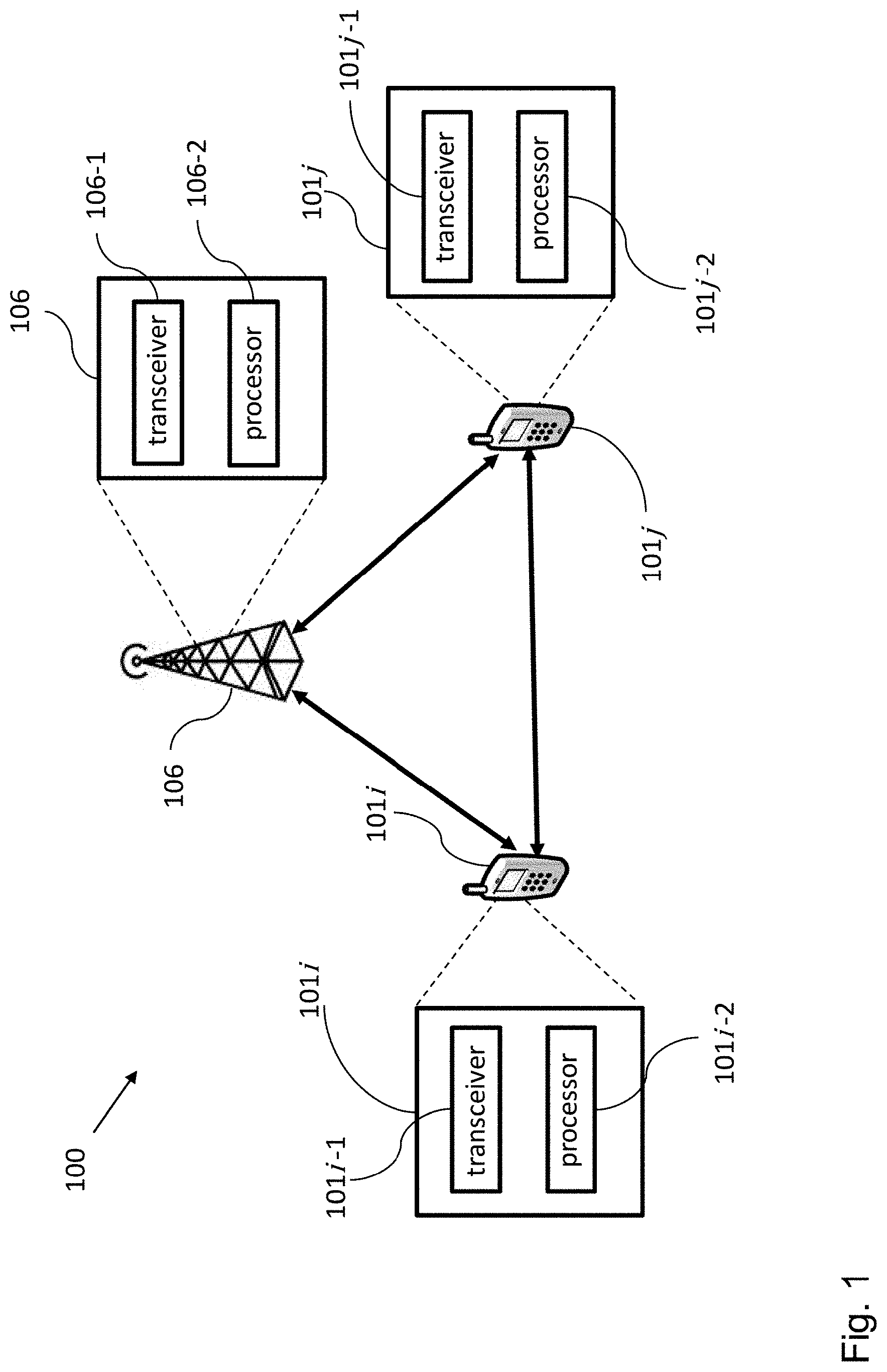
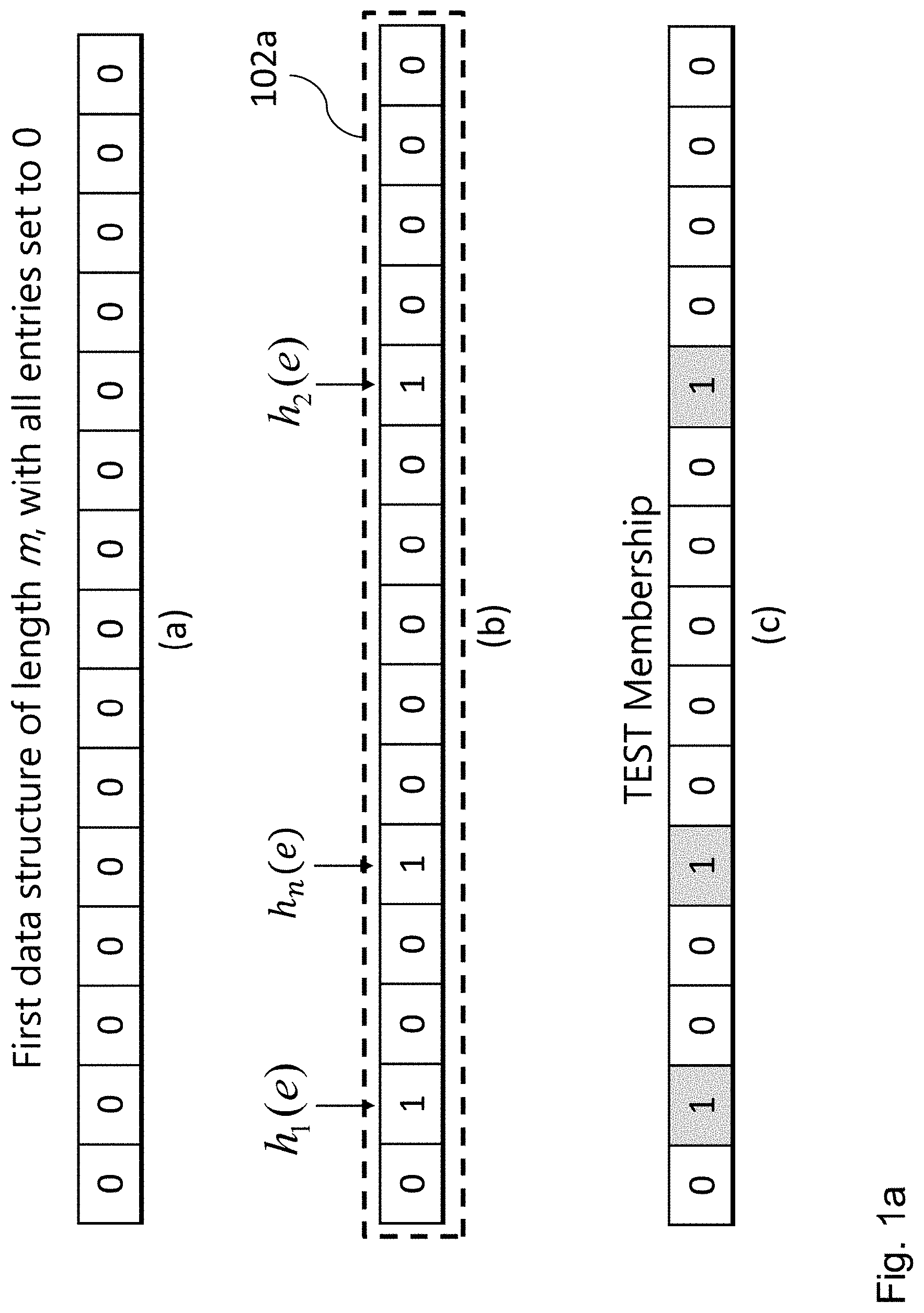
[0033] FIG. 1a shows an exemplary first data structure according to an embodiment of the invention; and
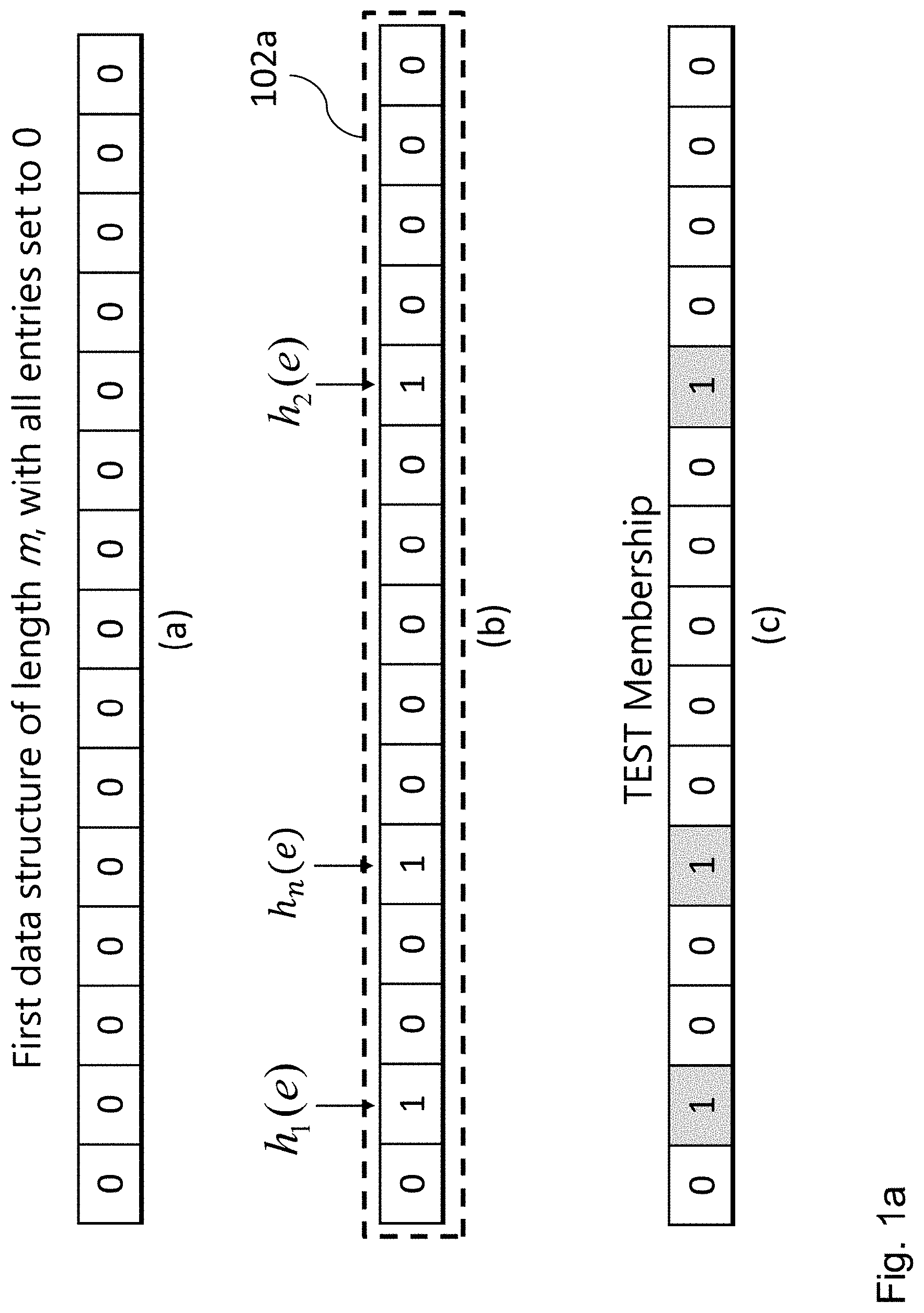
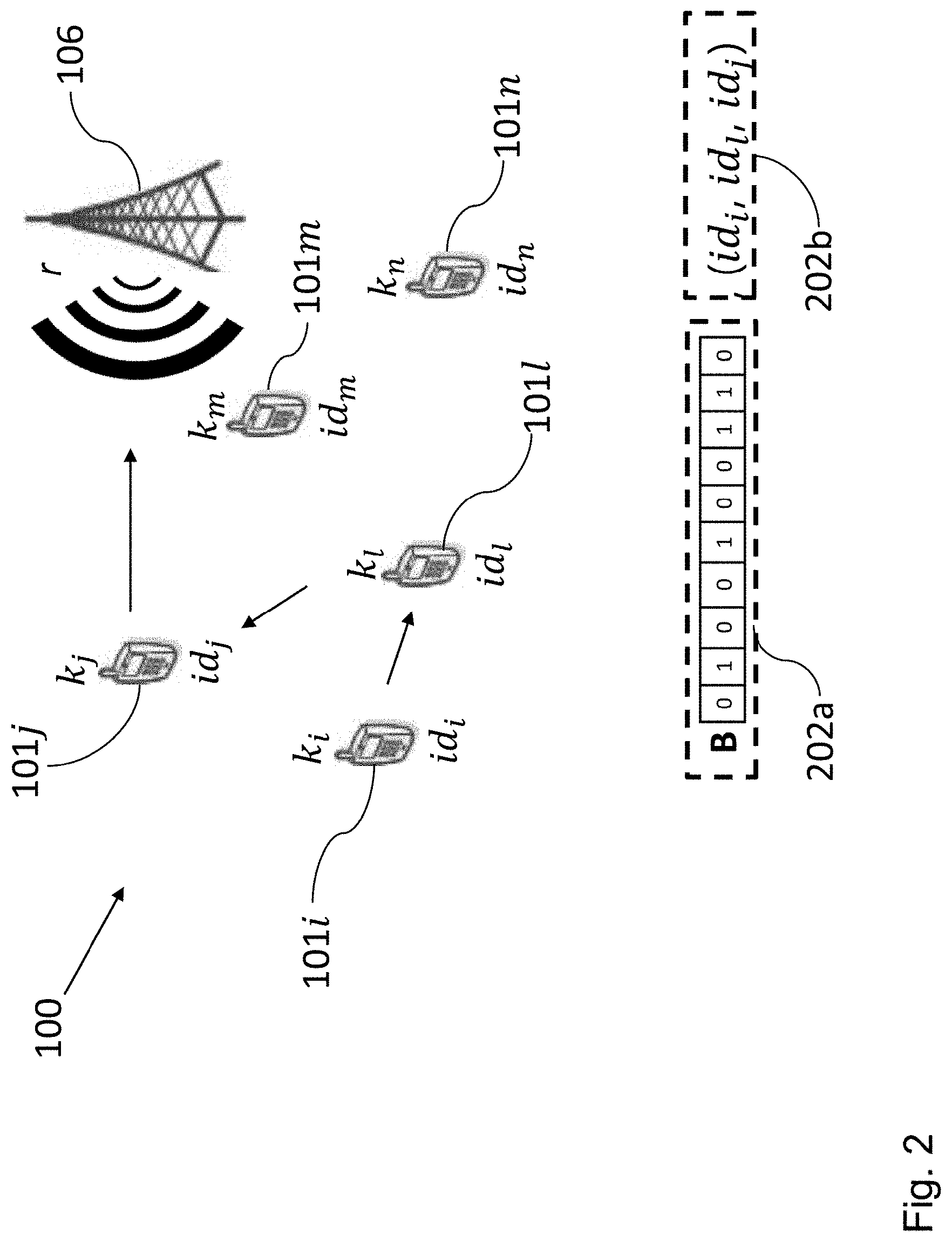
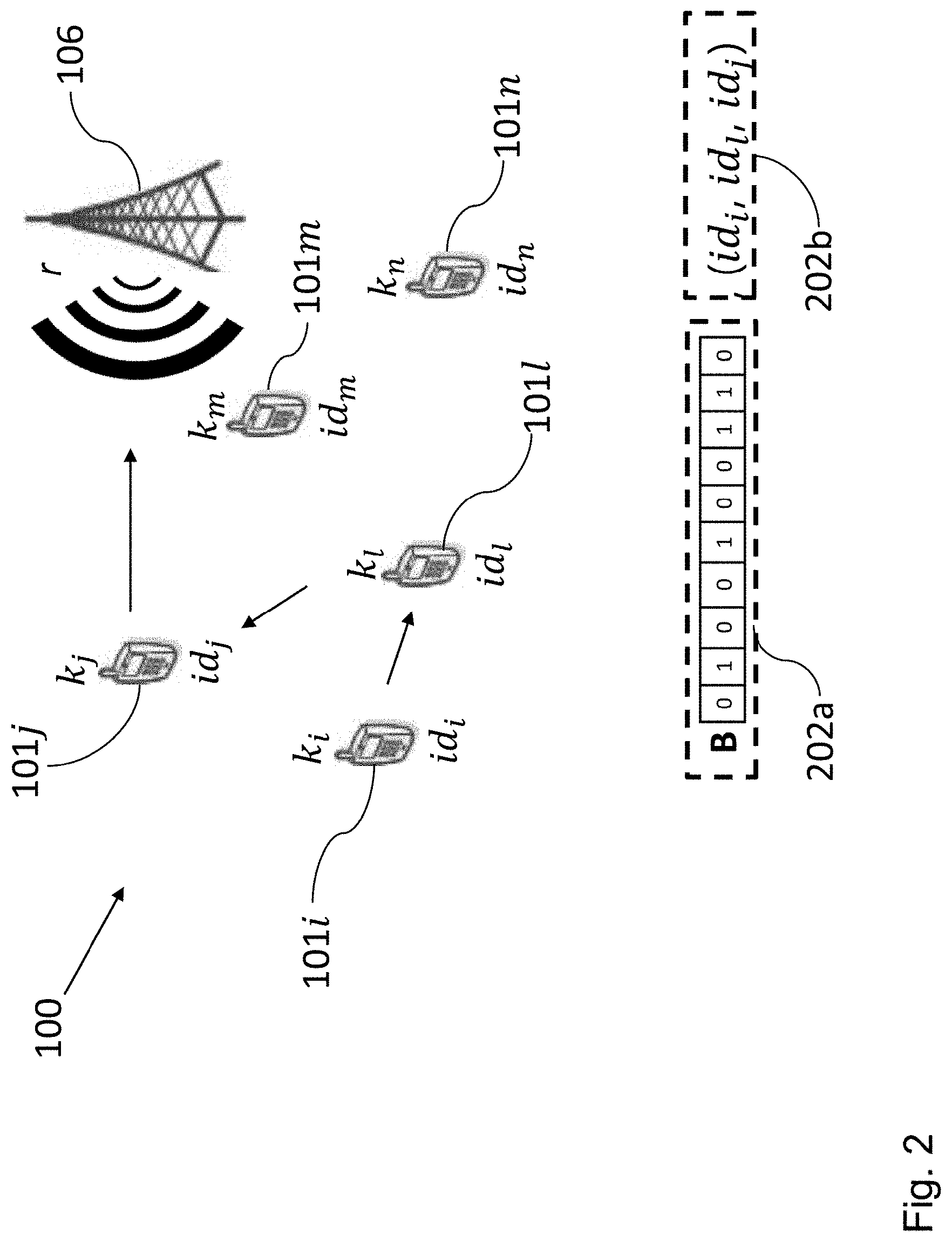
[0034] FIG. 2 shows a schematic diagram of a wireless communication system comprising a plurality of wireless communication devices, a base station, an exemplary modified first data structure and an exemplary modified second data structure according to embodiments of the invention.
DETAILED DESCRIPTION OF THE EMBODIMENTS
[0035] In the following description, reference is made to the accompanying drawings, which form part of the disclosure, and in which are shown, by way of illustration, specific aspects in which embodiments of the present invention may be placed. It is understood that other aspects may be utilized and structural or logical changes may be made without departing from the scope of the present invention. The following detailed description, therefore, is not to be taken in a limiting sense, as the scope of the present invention is defined by the appended claims.
[0036] For instance, it is understood that a disclosure in connection with a described method may also hold true for a corresponding device or system configured to perform the method and vice versa. For example, if a specific method step is described, a corresponding device may include a unit to perform the described method step, even if such unit is not explicitly described or illustrated in the figures. Further, it is understood that the features of the various exemplary aspects described herein may be combined with each other, unless specifically noted otherwise.
[0037] FIG. 1 shows a schematic diagram of a wireless communication system 100 comprising a wireless communication device 101i, a further wireless communication device 101j, and a base station 106 according to embodiments of the invention.
[0038] The wireless communication device 101i is configured to communicate with the base station 106 and the wireless communication device 101j. The wireless communication device 101i comprises a transceiver 101i-1 configured to receive a token from the base station 106, and a processor 101i-2 configured to generate a first data structure 102a (see FIG. 1a (b)) on the basis of a function of the token and of a key k.sub.i of the wireless communication device 101i, and a second data structure comprising an identity id.sub.i of the wireless communication device 101i. The transceiver 101i-1 is further configured to broadcast the first data structure 102a and the second data structure to the further wireless communication device 101j and the base station 106.
[0039] The further wireless communication device 101j is configured to communicate with the base station 106 and the wireless communication device 101i. The further wireless communication device 101j comprises a transceiver 101j-1 configured to receive the token from the base station 106, the first data structure 102a generated on the basis of the function of the token and of the key k.sub.i of the wireless communication device 101i, and the second data structure comprising the identity id.sub.i of the wireless communication device 101i, and a processor 101j-2 configured to add a data element based on a function of the token and of a key k.sub.j of the further wireless communication device 101j to the first data structure 102a, and to add an identity id.sub.j of the further wireless communication device 101j to the second data structure for obtaining a modified first data structure and a modified second data structure. The transceiver 101j-1 is further configured to broadcast the modified first data structure and the modified second data structure to the wireless communication device 101i and the base station 106.
[0040] The base station 106 is configured to communicate with the wireless communication device 101i and the further wireless communication device 101j. The base station 106 comprises a transceiver 106-1 configured to receive the first data structure 102a and the second data structure generated by the wireless communication device 101i (or the modified first data structure and the modified second data structure generated by the further wireless communication device 101j), wherein the first data structure 102a is based on the function of the token provided by the base station 106 and of the key k.sub.i of the wireless communication device 101i, and wherein the second data structure comprises the identity id.sub.i of the wireless communication device 101i, and a processor 106-2 configured to derive the key k.sub.i of the wireless communication device 101i on the basis of the second data structure and to authenticate the wireless communication device 101i on the basis of the key k.sub.i and of the first data structure 102a of the wireless communication device 101i.
[0041] In an embodiment, the function applied to the token and the key k.sub.i of the wireless communication device 101i has a uniform output distribution and, preferably, is collision resistant, namely it is difficult to find two different tokens that result in the same output.
[0042] In an embodiment, the first data structure 102a is a Bloom Filter (BF) (see FIG. 1a), which is a space-efficient data structure that can be used to perform a set-membership test, wherein the set-membership test allows to check if, for example, the wireless communication device 101i is a legitimate device, i.e., an identifiable wireless communication device that shares a secret key, e.g. k.sub.i, with the base station 106.
[0043] In particular, a BF is an array of length m, with all entries set to 0 (see FIG. 1a (a)). To perform the set-membership test, the processor 101i-2 can be configured to select n hash functions mapping elements from the set to values 1 to m uniformly at random (see FIG. 1a (b)). In embodiments of the invention, n is much smaller than m.
[0044] Moreover, in order to add an element e to the BF, the processor 101i-2 can be configured to compute the value of all hash functions on e, and to set the entry of the BF equal to one accordingly (see FIG. 1a (b)). Furthermore, for testing the set-membership of e, the processor 101i-2 can be configured to re-compute the hashes (see FIG. 1a (c)): if at least one value corresponds to a 0-entry, then e is not in the BF; and if all values correspond to 1-entries, then e may be in the BF, i.e., false positives are possible.
[0045] In embodiments of the invention, the false positive rate of the BF can be kept low in order to avoid attempts from an adversary to get authenticated to the base station 106 while not being authorized to. This can be ensured by selecting the parameters (m, n, L) defining the BF accordingly, wherein m is the length of the BF, n is the number of hashes for adding an element to the BF, and L is the number of the wireless communication devices authenticating to the base station 106. In an embodiment, the number of hash functions n to minimize the probability of false positives is given by the following equation:
2.sup.-n=(0.6185).sup.m/L.
[0046] In embodiments of the invention, in order to maintain the secrecy of the key k.sub.i added to the BF, cryptographic hash functions can be used with the Bloom Filter.
[0047] In embodiments of the invention, the processor 101i-2 can be configured to use, for example, the parameters (m, n, L) shown in table 1 in order to define the BF.
TABLE-US-00001 TABLE 1 Parameters (m, n, L) defining the BF according to an embodiment. n m L 9 128 15 18 256 50
[0048] Embodiments of the invention making use of BFs as first data structures have the advantage of providing very efficient data structures in terms of space, since the time to add elements or test membership is constant, namely it does not depend on the number of elements in the BF or the set. Moreover, this has the advantage of improving the performance of the authentication protocol. Another advantage of using a BF is due to the fact that there are no false negatives, namely the membership test for the secret values, e.g., keys k.sub.i and k.sub.j, shared between the wireless communication devices 101i, 101j and the base station 106, and which have been added to the Bloom Filter, will always succeed.
[0049] In another embodiment, the first data structure 102a is an aggregate message authentication code (MAC).
[0050] In an embodiment of the invention, the processor 106-2 of the base station 106 is configured to generate by means of a Private Key Generator (PKG) a pair of master keys (msk, mpk)=(s, (g, g.sup.s)). In this embodiment, the wireless communication devices 101i, 101j, and the base station 106 comprise a private key H(id.sub.i).sup.s provided by the PKG, wherein H is a cryptographic hash function. In this embodiment, the following steps take place:
[0051] 1st step: the base station 106 broadcasts the token r;
[0052] 2.sup.nd step: in order to authenticate, the processor 101i-2 of the wireless communication device 101i computes its key k.sub.i on the basis of the following equation:
k.sub.i=H'(e(H(id.sub.BS),H(id.sub.i).sup.s),r),
wherein r is the token, H' and H are cryptographic hash functions, id.sub.BS is the identity of the base station 106, e is a bilinear pairing function, and s is a master key. For example, s is the master secret key hold by the base station 106. The processor 101i-2 of the wireless communication device 101i is configured to add k.sub.i to the first data structure 102a, e.g., the BF, to append the identity id.sub.i of the wireless communication device 101i to the second data structure, and to pass the two arrays or data structures (the BF and the one containing the identities) to the further wireless communication device 101j.
[0053] 3.sup.rd step: in order to verify whether the wireless communication devices that populate the BF are legitimate, for each identity id.sub.i/j in the second data structure, the processor 106-2 of the base station 106 computes the key k.sub.i/j on the basis of the following equation:
k.sub.i/j=H'(e(H(id.sub.BS).sup.s,H(id.sub.i/j)),r),
wherein H' and H are cryptographic hash functions, id.sub.BS is the identity of the base station 106, and s is the key of the pair of master keys. Then, the processor 106-2 checks if the key k.sub.i/j belongs to the BF. Namely, if any of the entries of the BF is 0, then the key k.sub.i/j is rejected, and if all and only those entries are 1, then the key k.sub.i/j is accepted.
[0054] This embodiment has the advantage of introducing a separate PKG, which decouples the role of the base station 106 and of the master key holder, which can be useful in many scenarios (e.g., group authentication between a base station and mobile nodes). Moreover, this embodiment maintains the lightweight performance in terms of communication, while adding some computational costs due to the use of pairings.
[0055] In another embodiment of the invention the PKG generates a master key pair (msk, mpk)=(x, (P, Y=xP)), wherein P is a public parameter. In this embodiment, each wireless communication device 101i/101j is equipped with an identity id.sub.i/j and the private key (R, s) such that:
r.di-elect cons..sub.RZ.sup.q*, R=rP and
s=r+xH(R,id.sub.i/j),
wherein H is a cryptographic hash function. In this embodiment, the following steps take place:
[0056] 1.sup.st step: the base station 106 broadcasts the token tP, wherein t is an integer chosen uniformly at random;
[0057] 2.sup.nd step: in order to authenticate, the processor 101i-2 of the wireless communication device 101i with identity id.sub.i computes its key k.sub.i on the basis of the following equation:
k.sub.i=tsP.
[0058] Then, the processor 101i-2 of the wireless communication device 101i adds the key k.sub.i to the BF, and appends its identity (id.sub.i, R) to the second data structure, and passes the two arrays (the first data structure 102a, in this embodiment the BF, and the second data structure containing the identities) to the further wireless communication device 101j;
[0059] 3.sup.rd step: in order to verify whether the wireless communication devices 101i and 101j that have populated the BF are legitimate, the processor 106-2 of the base station 106, for each (id.sub.i/j, R) appended in the second data structure, computes the key k.sub.i/j of the wireless communication device 101i/j on the basis of the following equation:
k.sub.i/j=tR+tH(R,id.sub.i/j)Y,
and checks if it belongs to the first data structure 102a, which in this embodiment is a BF. In other words, if any of the entries of the BF is 0, then the key k.sub.i/j is rejected, and if all and only those entries are 1, then the key k.sub.i/j is accepted.
[0060] This embodiment of the invention provides the advantage of having a separate PKG, which decouples the role of the base station 106 and master key holder, and of recovering computation efficiency by eliminating the need for pairings. Communication costs are slightly increased since in the appended array devices have to transmit their identity together with their value R.
[0061] In another embodiment of the invention the PKG generates a master key pair (msk, mpk)=(x, (P, Y=xP)). In this embodiment, each wireless communication device 101i, 101j, and the base station 106 are equipped with the respective identities (id.sub.i, id.sub.j, and id.sub.BS) and the private key (R, s) provided by the PKG in such a way that:
r.di-elect cons..sub.RZ.sub.q*, and
s=r+xH(R,id.sub.i),
wherein H' and H are cryptographic hash functions. In this embodiment, the following steps take place:
[0062] 1.sup.st step: the transceiver 106-1 of the base station 106 broadcasts the token t. The base station 106 has a private key (R', s');
[0063] 2.sup.nd step: in order to authenticate, the processor 101i-2 of the wireless communication device 101i computes the key k.sub.i of the wireless communication device 101i on the basis of the following equation:
k.sub.i=H'(sR'+sH(R',id.sub.BS)Y,t).
[0064] Then, the processor 101i-2 adds k.sub.i to the BF, appends its identity (id.sub.i, R) to the second data structure, and passes the two data structures (the BF and the one containing the identities) to the further wireless communication device 101j;
[0065] 3.sup.rd step: in order to verify whether the wireless communication devices 101i and 101j are legitimate, the processor 106-2 of the base station 106, for each (id.sub.i/j, R) in the second data structure, derives the key k.sub.i/j of the wireless communication device 101i/101j on the basis of the following equation:
k.sub.i/j=H'(s'R+s'H(R,id.sub.i/j)Y,t),
and checks if it belongs to the first data structure 102a, which in this embodiment is a BF. In other words, if any of the entries of the BF is 0, then the key k.sub.i/j is rejected, and if all and only those entries are 1, then the key k.sub.i/j is accepted.
[0066] This embodiment of the invention provides the advantage of having a separate PKG, which decouples the role of the base station 106 and of the master key holder, and of recovering computation efficiency by eliminating the need for pairings. Communication costs are slightly increased since in the first data structure 102a and in the second data structure the wireless communication devices 101i and 101j should transmit their identities id.sub.i and id.sub.j together with their value R. Moreover, if there is any subsequent session with a new token t', then the wireless communication devices 101i and 101j and the base station 106 can simply recompute H' by changing the second input only. Therefore, the computation involved is minimized.
[0067] In another embodiment of the invention, the wireless communication devices 101i and 101j are a set of sensors which want to communicate with a local reader (e.g., in a smart home) and, in order to do so, should authenticate to the reader. In this embodiment, the nodes may be static, and the network topology would be typically known.
[0068] The aforementioned embodiments of the invention solve the problem of lightweight group authentication in a network in which the wireless communication devices 101i and 101j are equipped with identities. Moreover, embodiments of the invention advantageously overcome the limitations of prior art solutions since, simultaneously, they are lightweight, they handle group authentication and they are suitable for an identity-based setting.
[0069] FIG. 2 shows a schematic diagram of a wireless communication system 100 comprising a plurality of wireless communication devices 101i, 101j, 101l, 101m, 101n, and the base station 106, an exemplary modified first data structure 202a, and an exemplary modified second data structure 202b according to embodiments of the invention.
[0070] In this embodiment of the invention, the base station 106 broadcasts the token r, which is received by the wireless communication devices 101i, 101j, 101l, 101m, and 101n. Then, the processor 101i-2 of the wireless communication device 101i adds its key k.sub.i to the first data structure 102a, which in this embodiment is a BF, and appends its identity id.sub.i to the second data structure, and passes the first data structure 102a and the second data structure to the wireless communication device 101l. Afterwards, the wireless communication device 101l, similarly to the wireless communication device 101i, adds its key k.sub.i to the first data structure 102a and appends its identity id.sub.l to the second data structure. Then, the wireless communication device 101j, similarly to the wireless communication devices 101i and 101l, adds its key k.sub.j to the BF 202a, so that the modified first data structure 202a is obtained, and appends its identity id.sub.j to the second data structure 202b, so that the modified second data structure 202b is obtained. Finally, the wireless communication device 101j sends the modified first data structure 202a and the modified second data structure 202b to the base station 106.
[0071] While a particular feature or aspect of the disclosure may have been disclosed with respect to only one of several implementations or embodiments, such feature or aspect may be combined with one or more other features or aspects of the other implementations or embodiments as may be desired and advantageous for any given or particular application. Furthermore, to the extent that the terms "include", "have", "with", or other variants thereof are used in either the detailed description or the claims, such terms are intended to be inclusive in a manner similar to the term "comprise". Also, the terms "exemplary", "for example" and "e.g." are merely meant as an example, rather than the best or optimal. The terms "coupled" and "connected", along with derivatives may have been used. It should be understood that these terms may have been used to indicate that two elements cooperate or interact with each other regardless whether they are in direct physical or electrical contact, or they are not in direct contact with each other.
[0072] Although specific aspects have been illustrated and described herein, it will be appreciated by those of ordinary skill in the art that a variety of alternate and/or equivalent implementations may be substituted for the specific aspects shown and described without departing from the scope of the present disclosure. This application is intended to cover any adaptations or variations of the specific aspects discussed herein.
[0073] Although the elements in the following claims are recited in a particular sequence with corresponding labeling, unless the claim recitations otherwise imply a particular sequence for implementing some or all of those elements, those elements are not necessarily intended to be limited to being implemented in that particular sequence.
[0074] Many alternatives, modifications, and variations will be apparent to those skilled in the art in light of the above teachings. Of course, those skilled in the art readily recognize that there are numerous applications of the invention beyond those described herein. While the present invention has been described with reference to one or more particular embodiments, those skilled in the art recognize that many changes may be made thereto without departing from the scope of the present invention. It is therefore to be understood that within the scope of the appended claims and their equivalents, the invention may be practiced otherwise than as specifically described herein.
* * * * *
D00000
D00001
D00002
D00003
XML
uspto.report is an independent third-party trademark research tool that is not affiliated, endorsed, or sponsored by the United States Patent and Trademark Office (USPTO) or any other governmental organization. The information provided by uspto.report is based on publicly available data at the time of writing and is intended for informational purposes only.
While we strive to provide accurate and up-to-date information, we do not guarantee the accuracy, completeness, reliability, or suitability of the information displayed on this site. The use of this site is at your own risk. Any reliance you place on such information is therefore strictly at your own risk.
All official trademark data, including owner information, should be verified by visiting the official USPTO website at www.uspto.gov. This site is not intended to replace professional legal advice and should not be used as a substitute for consulting with a legal professional who is knowledgeable about trademark law.