Communication Method and Communications Apparatus
Yan; Le ; et al.
U.S. patent application number 16/989256 was filed with the patent office on 2020-11-26 for communication method and communications apparatus. The applicant listed for this patent is Huawei Technologies Co., Ltd.. Invention is credited to Le Yan, Qinghai Zeng, Hongping Zhang.
| Application Number | 20200374938 16/989256 |
| Document ID | / |
| Family ID | 1000005005128 |
| Filed Date | 2020-11-26 |
| United States Patent Application | 20200374938 |
| Kind Code | A1 |
| Yan; Le ; et al. | November 26, 2020 |
Communication Method and Communications Apparatus
Abstract
Embodiments of this application provide a communication method and a communications apparatus. The method includes: receiving identification information of N beams of a target cell and random access channel configurations of M beams in the N beams, where N and M are positive integers; and determining a beam for accessing based on signal quality or signal strength of L beams in the N beams, the identification information of the N beams, and the random access channel configurations of the M beams, where L is a nonnegative integer.
| Inventors: | Yan; Le; (Shanghai, CN) ; Zeng; Qinghai; (Shanghai, CN) ; Zhang; Hongping; (Shanghai, CN) | ||||||||||
| Applicant: |
|
||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|
| Family ID: | 1000005005128 | ||||||||||
| Appl. No.: | 16/989256 | ||||||||||
| Filed: | August 10, 2020 |
Related U.S. Patent Documents
| Application Number | Filing Date | Patent Number | ||
|---|---|---|---|---|
| 16536003 | Aug 8, 2019 | 10785805 | ||
| 16989256 | ||||
| PCT/CN2018/091540 | Jun 15, 2018 | |||
| 16536003 | ||||
| Current U.S. Class: | 1/1 |
| Current CPC Class: | H04W 74/0833 20130101; H04B 7/0695 20130101; H04W 36/30 20130101; H04W 36/06 20130101 |
| International Class: | H04W 74/08 20060101 H04W074/08; H04W 36/30 20060101 H04W036/30; H04W 36/06 20060101 H04W036/06; H04B 7/06 20060101 H04B007/06 |
Foreign Application Data
| Date | Code | Application Number |
|---|---|---|
| Jun 16, 2017 | CN | 201710459115.0 |
Claims
1. A method, comprising: receiving, by a terminal, random access channel configurations corresponding to M beams of a target cell, wherein M is a positive integer, and each random access channel configuration of the random access channel configurations of the M beams comprises a respective preamble index and a respective time-frequency resource configuration; when the M beams comprise at least one beam whose signal strength is greater than or equal to a first beam signal strength threshold, determining, by the terminal, to use a first beam of the at least one beam for a random access procedure in the target cell; and when a signal strength of each of the M beams is less than the first beam signal strength threshold, determining, by the terminal, to use a second beam of L beams for the random access procedure in the target cell, wherein a signal strength of the second beam is greater than or equal to the first beam signal strength threshold, L is a nonnegative integer, and the L beams are all beams whose signal strength is detected.
2. The method according to claim 1, further comprising: receiving the first beam signal strength threshold.
3. The method according to claim 2, wherein receiving the first beam signal strength threshold comprises: receiving the first beam signal strength threshold through a radio resource control (RRC) connection reconfiguration message.
4. The method according to claim 1, further comprising: when a respective signal strength of each of the L beams and each of the M beams is less than the first beam signal strength threshold, or none of the M beams is found, performing the following: determining to use an earliest found beam for the random access procedure in the target cell; determining to use a beam with a highest signal strength for the random access procedure in the target cell; determining to use a randomly found beam for the random access procedure in the target cell; or determining to use a beam with a highest priority for the random access procedure in the target cell.
5. The method according to claim 1, wherein determining to use the first beam for the random access procedure in the target cell comprises: selecting the first beam based on a priority order of the at least one beam whose signal strength is greater than or equal to the first beam signal strength threshold.
6. The method according to claim 1, wherein identification information of each beam comprises respective synchronization signal block identification information of the respective beam or respective channel state information-reference signal identification information of the respective beam.
7. The method according to claim 6, wherein a priority of a beam that is used to transmit channel state information-reference signal identification information is higher than that of a beam that is used to transmit synchronization signal block identification information.
8. An apparatus, comprising: a first circuitry, configured to: receive random access channel configurations corresponding to M beams of a target cell, wherein M is a positive integer, and each random access channel configuration of the random access channel configurations of the M beams comprises a respective preamble index and a respective time-frequency resource configuration; and a second circuitry, configured to: when the M beams comprise at least one beam whose signal strength is greater than or equal to a first beam signal strength threshold, determine to use a first beam of the at least one beam for a random access procedure in the target cell; and when a signal strength of each of the M beams is less than the first beam signal strength threshold, determine to use a second beam of L beams for the random access procedure in the target cell, wherein a signal strength of the second beam is greater than or equal to the first beam signal strength threshold, L is a nonnegative integer, and the L beams are all beams whose signal strength is detected.
9. The apparatus according to claim 8, wherein the first circuitry is further configured to receive the first beam signal strength threshold.
10. The apparatus according to claim 9, wherein the first beam signal strength threshold is carried in a radio resource control (RRC) connection reconfiguration message.
11. The apparatus according to claim 8, wherein the second circuitry is further configured to: when a respective signal strength of each of the L beams and each of the M beams is less than the first beam signal strength threshold, or none of the M beams is found, perform the following: determine to use an earliest found beam for the random access procedure in the target cell; determine to use a beam with a highest signal strength for the random access procedure in the target cell; determine to use a randomly found beam for the random access procedure in the target cell; or determine to use a beam with a highest priority for the random access procedure in the target cell.
12. The apparatus according to claim 8, wherein the second circuitry is further configured to: select the first beam based on a priority order of the at least one beam whose signal strength is greater than or equal to the first beam signal strength threshold.
13. The apparatus according to claim 8, wherein identification information of each beam comprises respective synchronization signal block identification information of the respective beam or respective channel state information-reference signal identification information of the respective beam.
14. The apparatus according to claim 13, wherein a priority of a beam that is used to transmit channel state information-reference signal identification information is higher than that of a beam that is used to transmit synchronization signal block identification information.
15. A non-transitory computer readable storage medium, wherein the non-transitory computer readable storage medium stores a program to be executed by a processor, the program including instructions for: receiving random access channel configurations corresponding to M beams of a target cell, wherein M is a positive integer, and each random access channel configuration of the random access channel configurations of the M beams comprises a respective preamble index and a respective time-frequency resource configuration; when the M beams comprise at least one beam whose signal strength is greater than or equal to a first beam signal strength threshold, determining to use a first beam of the at least one beam for a random access procedure in the target cell; and when a signal strength of each of the M beams is less than the first beam signal strength threshold, determining to use a second beam of L beams for the random access procedure in the target cell, wherein a signal strength of the second beam is greater than or equal to the first beam signal strength threshold, L is a nonnegative integer, and the L beams are all beams whose signal strength is detected.
16. The medium according to claim 15, wherein the program further includes instructions for: receiving the first beam signal strength threshold.
17. The medium according to claim 15, wherein the program further includes instructions for: when a respective signal strength of each of the L beams and each of the M beams is less than the first beam signal strength threshold, or none of the M beams is found, performing the following: determining to use an earliest found beam for the random access procedure in the target cell; determining to use a beam with a highest signal strength for the random access procedure in the target cell; determining to use a randomly found beam for the random access procedure in the target cell; or determining to use a beam with a highest priority for the random access procedure in the target cell.
18. The medium according to claim 15, wherein the program further includes instructions for: selecting the first beam based on a priority order of the at least one beam whose signal strength is greater than or equal to the first beam signal strength threshold.
19. The medium according to claim 15, wherein identification information of each beam comprises respective synchronization signal block identification information of the respective beam or respective channel state information-reference signal identification information of the respective beam.
20. The medium according to claim 19, wherein a priority of a beam that is used to transmit the channel state information-reference signal identification information is higher than that of a beam that is used to transmit the synchronization signal block identification information.
Description
CROSS-REFERENCE TO RELATED APPLICATIONS
[0001] This application is a continuation of U.S. patent application Ser. No. 16/536,003, filed on Aug. 8, 2019, which is a continuation of International Application No. PCT/CN2018/091540, filed on Jun. 15, 2018. The International Application claims priority to Chinese Patent Application No. 201710459115.0, filed on Jun. 16, 2017. All of the afore-mentioned patent applications are hereby incorporated by reference in their entireties.
TECHNICAL FIELD
[0002] Embodiments of this application relate to the field of communications technologies, and in particular, to a communication method and a communications apparatus.
BACKGROUND
[0003] Mobile communications not only pursues maximization of a capacity, but also needs a broader coverage area. That is, a terminal that moves to anywhere needs to be covered by a wireless network signal. When a terminal moves towards another cell from a serving cell, to ensure service continuity of the terminal, the terminal needs to be handed over from the current serving cell to the another cell.
[0004] Currently, a serving cell handover process of a terminal in an LTE system is described as follows: A source base station (Source eNB, SeNB) determines to perform a serving cell handover on a terminal based on a measurement report reported by the terminal and initiates a handover request to a target base station (Target eNB, TeNB). After the SeNB obtains a handover request acknowledgement message from the TeNB, the SeNB sends a handover message to the terminal. The terminal initiates a random access process to the target base station based on an identifier of a target cell carried in the handover message, to obtain a TA value and an uplink resource, and sends a handover complete message to the target base station on the uplink resource.
[0005] However, a high-frequency technology is introduced in a current 5G system. During data transmission at a high frequency, a relatively large transmission loss is usually caused. To ensure effective service transmission, a high-frequency cell uses a beamforming technology to perform communication, that is, each high-frequency cell has a plurality of different beams used for communication. When a handover is performed on a terminal, how the terminal selects a beam for access needs an urgent solution.
SUMMARY
[0006] Embodiments of this application provide a communication method and a communications apparatus, to provide a proper beam access solution.
[0007] According to a first aspect, an embodiment of this application provides a communication method. The method includes receiving identification information of N beams of a target cell and random access channel configurations of M beams in the N beams, where N and M are positive integers. The method also includes determining a beam for accessing based on signal quality or signal strength of L beams in the N beams, the identification information of the N beams, and the random access channel configurations of the M beams, where L is a nonnegative integer.
[0008] In a possible design, the determining a beam for accessing based on signal strength of L beams in the N beams, the identification information of the N beams, and the random access channel configurations of the M beams includes: determining the beam for accessing based on the signal strength of the L beams in the N beams, strength threshold information, the identification information of the N beams, and the random access channel configurations of the M beams.
[0009] In a possible design, the method further includes: receiving the strength threshold information.
[0010] In a possible design, the strength threshold information includes a first beam signal strength threshold or strength threshold indication information, the strength threshold indication information is used to indicate a relationship between the first beam signal strength threshold and a second beam signal strength threshold, and the second beam signal strength threshold is a beam signal strength threshold carried in measurement configuration information.
[0011] In a possible design, the determining the beam for accessing based on the signal strength of the L beams in the N beams, strength threshold information, the identification information of the N beams, and the random access channel configurations of the M beams includes: determining, based on the signal strength of the L beams in the N beams, the strength threshold information, the identification information of the N beams, and the random access channel configurations of the M beams, a beam whose signal strength is greater than or equal to the first beam signal strength threshold from the M beams as the beam for accessing the target cell. Therefore, the beam that is for accessing the target cell and that is determined by the terminal has a random access channel configuration and high signal strength. In this way, a success rate of accessing the target cell by the terminal is higher.
[0012] In a possible design, the determining the beam for accessing based on the signal strength of the L beams in the N beams, strength threshold information, the identification information of the N beams, and the random access channel configurations of the M beams includes: when signal strength of each of the M beams is less than the first beam signal strength threshold, determining the beam for accessing, from the M beams based on the identification information of the N beams and the random access channel configurations of the M beams, the beam for accessing the target cell. Therefore, the beam that is for accessing the target cell and that is determined by the terminal has the random access channel configuration. In this way, a success rate of accessing the target cell by the terminal is high.
[0013] In a possible design, the determining the beam for accessing based on the signal strength of the L beams in the N beams, strength threshold information, the identification information of the N beams, and the random access channel configurations of the M beams includes: when signal strength of each of the M beams is less than the first beam signal strength threshold, determining, based on the identifiers of the N beams, the signal strength of the L beams, and the strength threshold information, a beam whose signal strength is greater than or equal to the first beam signal strength threshold from the L beams as the beam for accessing the target cell. Therefore, the beam that is for accessing the target cell and that is determined by the terminal belongs to the L beams. In this way, a success rate of accessing the target cell by the terminal is high.
[0014] In a possible design, the determining the beam for accessing based on the signal strength of the L beams in the N beams, strength threshold information, the identification information of the N beams, and the random access channel configurations of the M beams includes: determining, based on the signal strength of the L beams, the strength threshold information, the identification information of the N beams, a priority order of the N beams, and the random access channel configurations of the M beams, the beam for accessing the target cell.
[0015] In a possible design, the determining a beam for accessing based on signal strength of L beams in the N beams, the identification information of the N beams, and the random access channel configurations of the M beams includes: when none of the M beams is found, determining, based on the identification information of the N beams, a beam with highest signal strength in the L beams as the beam for accessing the target cell. Therefore, the terminal determines that the beam for accessing the target cell has a strongest signal in the L beams. In this way, a success rate of accessing the target cell by the terminal is high.
[0016] In a possible design, the identification information of the N beams includes synchronization signal block identification information and/or channel state information-reference signal identification information, where the determining a beam for accessing based on signal strength of L beams in the N beams, the identification information of the N beams, and the random access channel configurations of the M beams includes: determining the beam for accessing based on the signal strength of the L beams in the N beams, the strength threshold information, the identification information of the N beams, that a priority of a beam whose identification information is the channel state information-reference signal identification information is higher than that of a beam whose identification information is the synchronization signal block identification information, and the random access channel configurations of the M beams.
[0017] In a possible design, if none of the N beams is found, signal strength of the L beams or signal strength of each of the M beams is less than the first beam signal strength threshold, or none of the M beams is found, the method further includes: determining the first found beam as the beam for accessing, determining a beam with highest signal strength as the beam for accessing, randomly determining a found beam as the beam for accessing, or determining a beam with a highest priority in found beams as the beam for accessing. Therefore, the terminal determines, in a relatively flexible manner, the beam for accessing the target cell.
[0018] In a possible design, the random access channel configuration includes a preamble index and a time-frequency resource configuration.
[0019] According to a second aspect, an embodiment of this application provides a communication method. The method includes receiving, by a first network device, identification information of N beams of a target cell and random access channel configurations of M beams in the N beams that are sent by a second network device, where N and M are positive integers. The method also includes sending, by the first network device, the identification information of the N beams and the random access channel configurations of the M beams to a terminal.
[0020] In a possible design, the method further includes: receiving, by the first network device, serving beam change information of the terminal that is within a predetermined time period and that is sent by the terminal; and sending, by the first network device, the serving beam change information to the second network device, where the serving beam change information is used by the second network device to determine a validity period of the random access channel configurations of the M beams.
[0021] In a possible design, the method further includes: receiving, by the first network device, serving beam change information of the terminal that is within a predetermined time period and that is sent by the terminal; determining, by the first network device, a validity period of the random access channel configurations of the M beams based on the serving beam change information; and sending, by the first network device, the validity period of the random access channel configurations of the M beams to the second network device.
[0022] In a possible design, the random access channel configuration includes a preamble index and a time-frequency resource configuration.
[0023] In a possible design, the method further includes: sending, by the first network device, strength threshold information or quality threshold information of a beam signal to the terminal through a handover message.
[0024] According to a third aspect, an embodiment of this application provides a communication method. The method includes sending, by a second network device, identification information of N beams of a target cell and random access channel configurations of M beams in the N beams to a first network device, where N and M are positive integers.
[0025] Optionally, the method further includes: receiving, by the second network device, serving beam change information of a terminal that is within a predetermined time period and that is sent by the first network device; determining, by the second network device, a validity period of the random access channel configurations of the M beams based on the serving beam change information; and when the validity period expires, releasing, by the second network device, the random access channel configurations of the M beams.
[0026] Optionally, the method further includes: receiving, by the second network device, the validity period of the random access channel configurations of the M beams that is sent by the first network device; and when the validity period expires, releasing, by the second network device, the random access channel configurations of the M beams.
[0027] Optionally, the method further includes: sending, by the second network device, strength threshold information or quality threshold information of a beam signal to the terminal through system information.
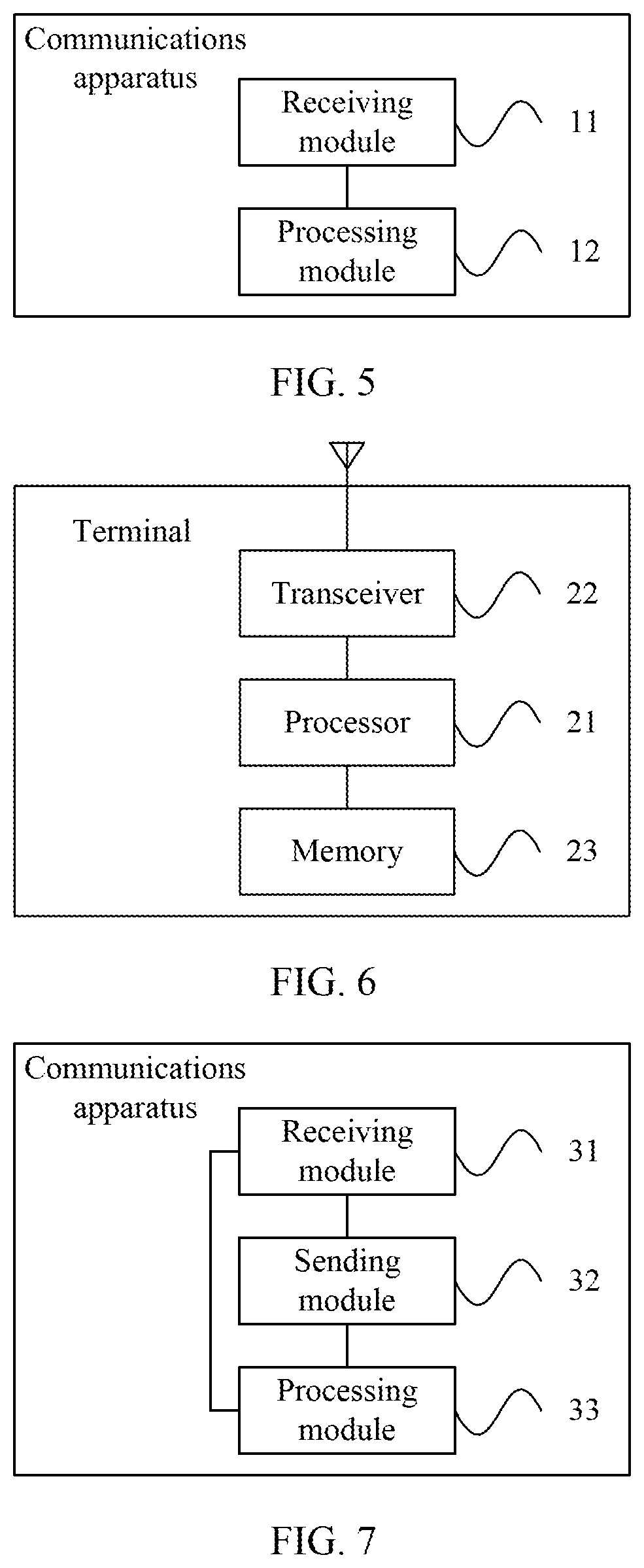
[0028] According to a fourth aspect, an embodiment of this application provides a communications apparatus. The apparatus includes a receiving module, configured to receive identification information of N beams of a target cell and random access channel configurations of M beams in the N beams, where N and M are positive integers. The apparatus also includes a processing module, configured to determine a beam for accessing based on signal quality or signal strength of L beams in the N beams, the identification information of the N beams, and the random access channel configurations of the M beams, where L is a nonnegative integer.
[0029] In a possible design, the processing module is specifically configured to determine the beam for accessing based on the signal strength of the L beams in the N beams, strength threshold information, the identification information of the N beams, and the random access channel configurations of the M beams.
[0030] In a possible design, the receiving module is further configured to receive the strength threshold information.
[0031] In a possible design, the strength threshold information includes a first beam signal strength threshold or strength threshold indication information, the strength threshold indication information is used to indicate a relationship between the first beam signal strength threshold and a second beam signal strength threshold, and the second beam signal strength threshold is a beam signal strength threshold carried in measurement configuration information.
[0032] In a possible design, the processing module is specifically configured to determine, based on the signal strength of the L beams in the N beams, the strength threshold information, the identification information of the N beams, and the random access channel configurations of the M beams, a beam whose signal strength is greater than or equal to the first beam signal strength threshold from the M beams as the beam for accessing the target cell.
[0033] In a possible design, the processing module is specifically configured to: when signal strength of each of the M beams is less than the first beam signal strength threshold, determine, from the M beams based on the identification information of the N beams and the random access channel configurations of the M beams, the beam for accessing the target cell.
[0034] In a possible design, the processing module is specifically configured to: when signal strength of each of the M beams is less than the first beam signal strength threshold, determine, based on the identifiers of the N beams, the signal strength of the L beams, and the strength threshold information, a beam whose signal strength is greater than or equal to the first beam signal strength threshold from the L beams as the beam for accessing the target cell.
[0035] In a possible design, the processing module is specifically configured to determine, based on the signal strength of the L beams, the strength threshold information, the identification information of the N beams, a priority order of the N beams, and the random access channel configurations of the M beams, the beam for accessing the target cell.
[0036] In a possible design, the processing module is specifically configured to: when none of the M beams is found, determine, based on the identification information of the N beams, a beam with highest signal strength in the L beams as the beam for accessing the target cell.
[0037] In a possible design, the identification information of the N beams includes synchronization signal block identification information and/or channel state information-reference signal identification information, where the processing module is specifically configured to determine the beam for accessing based on the signal strength of the L beams in the N beams, the strength threshold information, the identification information of the N beams, that a priority of a beam whose identification information is the channel state information-reference signal identification information is higher than that of a beam whose identification information is the synchronization signal block identification information, and the random access channel configurations of the M beams.
[0038] In a possible design, the processing module is further configured to: if none of the N beams is found, signal strength of the L beams or signal strength of each of the M beams is less than the first beam signal strength threshold, or none of the M beams is found, determine the first found beam as the beam for accessing, determine a beam with highest signal strength as the beam for accessing, randomly determine a found beam as the beam for accessing, or determine a beam with a highest priority in found beams as the beam for accessing.
[0039] In a possible design, the random access channel configuration includes a preamble index and a time-frequency resource configuration.
[0040] It should be noted that the communications apparatus in the fourth aspect may be a terminal, or may be a chip inside a terminal.
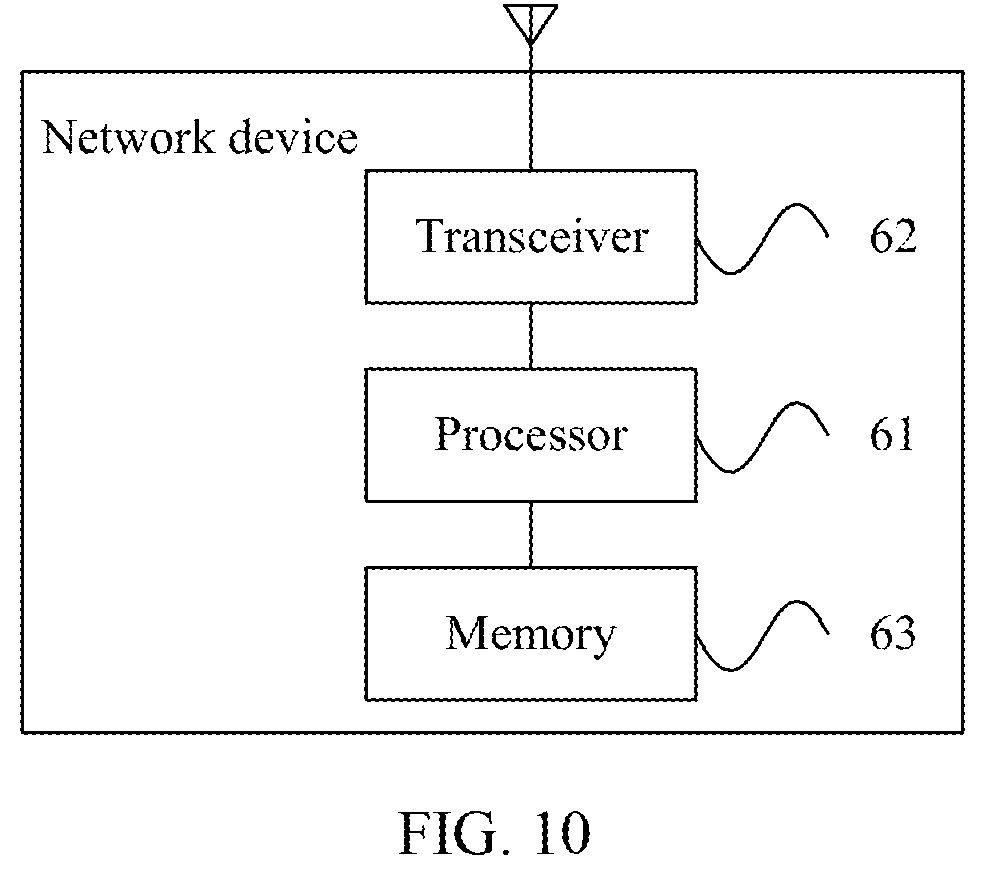
[0041] According to a fifth aspect, an embodiment of this application provides a communications apparatus. The apparatus includes a receiving module, configured to receive identification information of N beams of a target cell and random access channel configurations of M beams in the N beams that are sent by a second network device, where N and M are positive integers. The apparatus also includes a sending module, configured to send the identification information of the N beams and the random access channel configurations of the M beams to a terminal.
[0042] In a possible design, the receiving module is further configured to receive serving beam change information of the terminal that is within a predetermined time period and that is sent by the terminal; and the sending module is further configured to send the serving beam change information to the second network device, where the serving beam change information is used by the second network device to determine a validity period of the random access channel configurations of the M beams.
[0043] In a possible design, the communications apparatus further includes a processing module, where the receiving module is further configured to receive serving beam change information of the terminal that is within a predetermined time period and that is sent by the terminal; the processing module is configured to determine a validity period of the random access channel configurations of the M beams based on the serving beam change information; and the sending module is further configured to send the validity period of the random access channel configurations of the M beams to the second network device.
[0044] In a possible design, the random access channel configuration includes a preamble index and a time-frequency resource configuration; and the sending module is further configured to send strength threshold information or quality threshold information of a beam signal to the terminal through a handover message.
[0045] It should be noted that the communications apparatus in the fifth aspect may be a network device, or may be a chip inside a network device.
[0046] According to a sixth aspect, an embodiment of this application provides a communications apparatus. The apparatus includes a sending module, configured to send identification information of N beams of a target cell and random access channel configurations of M beams in the N beams to a first network device, where N and M are positive integers.
[0047] In a possible design, the network device further includes a receiving module and a processing module, where the receiving module is configured to receive serving beam change information of a terminal that is within a predetermined time period and that is sent by the first network device; and the processing module is configured to: determine a validity period of the random access channel configurations of the M beams based on the serving beam change information; and after the validity period expires, release the random access channel configurations of the M beams.
[0048] In a possible design, the network device further includes a receiving module and a processing module, where the receiving module is configured to receive the validity period of the random access channel configurations of the M beams that is sent by the first network device; and the processing module is configured to: after the validity period expires, release the random access channel configurations of the M beams.
[0049] In a possible design, the sending module is further configured to send strength threshold information or quality threshold information of a beam signal to the terminal through system information.
[0050] It should be noted that the communications apparatus in the sixth aspect may be a network device, or may be a chip inside a network device.
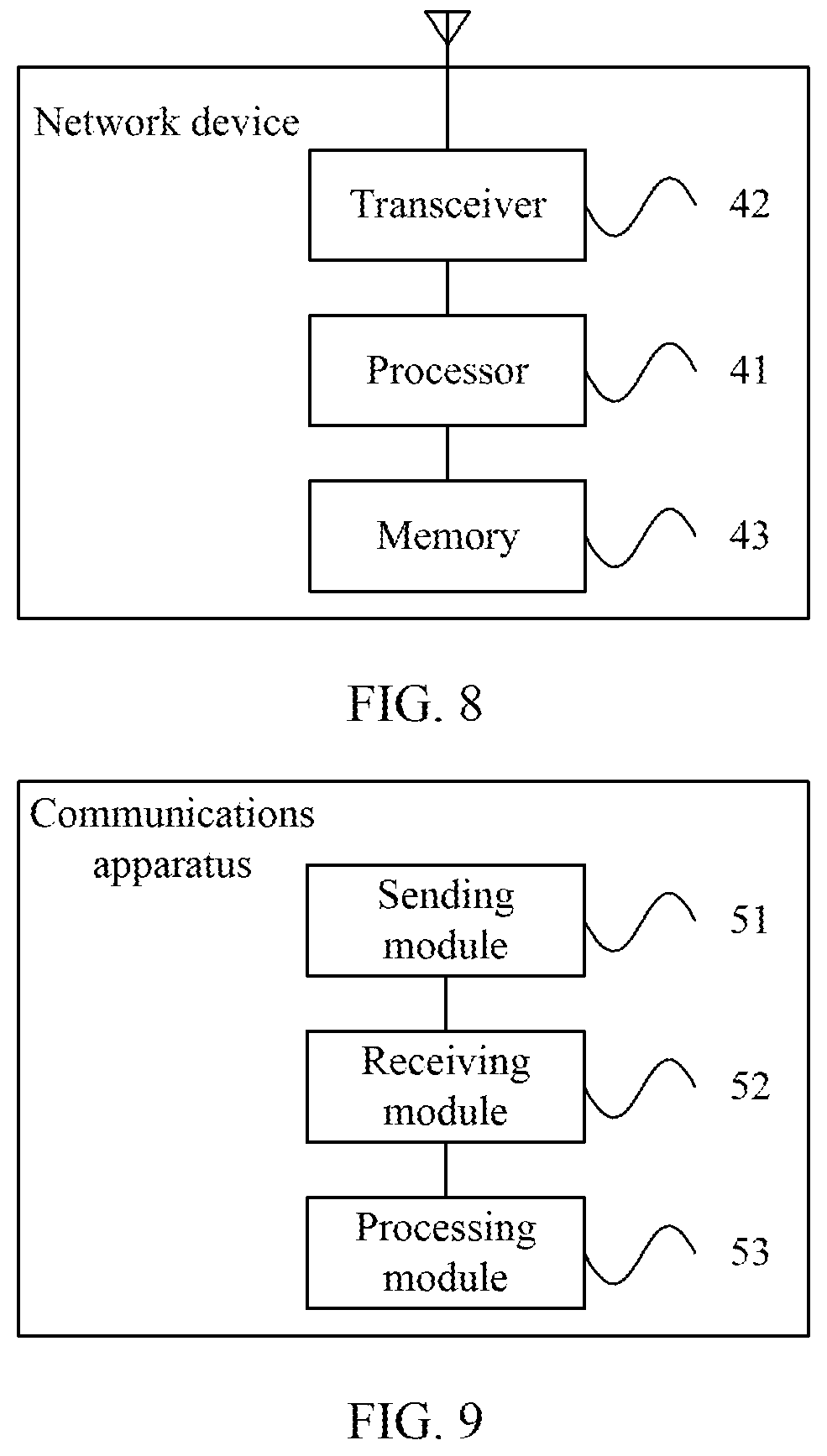
[0051] According to a seventh aspect, an embodiment of this application provides a terminal, including a processor and a transceiver. The processor and the transceiver are configured to perform the communication method according to any one of the embodiments of this application in the first aspect.
[0052] According to an eighth aspect, an embodiment of this application provides a network device, including a processor and a transceiver. The processor and the transceiver are configured to perform the communication method according to any one of the embodiments of this application in the second aspect.
[0053] According to a ninth aspect, an embodiment of this application provides a network device, including a processor and a transceiver. The processor and the transceiver are configured to perform the communication method according to any one of the embodiments of this application in the third aspect.
[0054] According to a tenth aspect, an embodiment of this application provides a computer readable storage medium. When an instruction in the storage medium is executed by a processor of a communications apparatus, the communications apparatus can perform the communication method according to the embodiments of this application in the first aspect.
[0055] According to an eleventh aspect, an embodiment of this application provides a computer readable storage medium. When an instruction in the storage medium is executed by a processor of a communications apparatus, the communications apparatus can perform the communication method according to the embodiments of this application in the second aspect.
[0056] According to a twelfth aspect, an embodiment of this application provides a computer readable storage medium. When an instruction in the storage medium is executed by a processor of a communications apparatus, the communications apparatus can perform the communication method according to the embodiments of this application in the third aspect.
[0057] According to the communication method and the communications apparatus in the embodiments of this application, the terminal receives the identification information of the N beams and the random access channel configurations of the M beams in the N beams, and the terminal determines the beam for accessing based on the signal quality or signal strength of the L beams in the N beams, the identification information of the N beams, and the random access channel configurations of the M beams, providing a proper beam for accessing determining solution. Further, the beam for accessing in the embodiments is determined by the terminal based on the signal quality or signal strength of the L beams in the N beams and the received random access channel configurations of the M beams. Therefore, the beam for accessing determined in this manner can increase an access success rate of the terminal.
BRIEF DESCRIPTION OF THE DRAWINGS
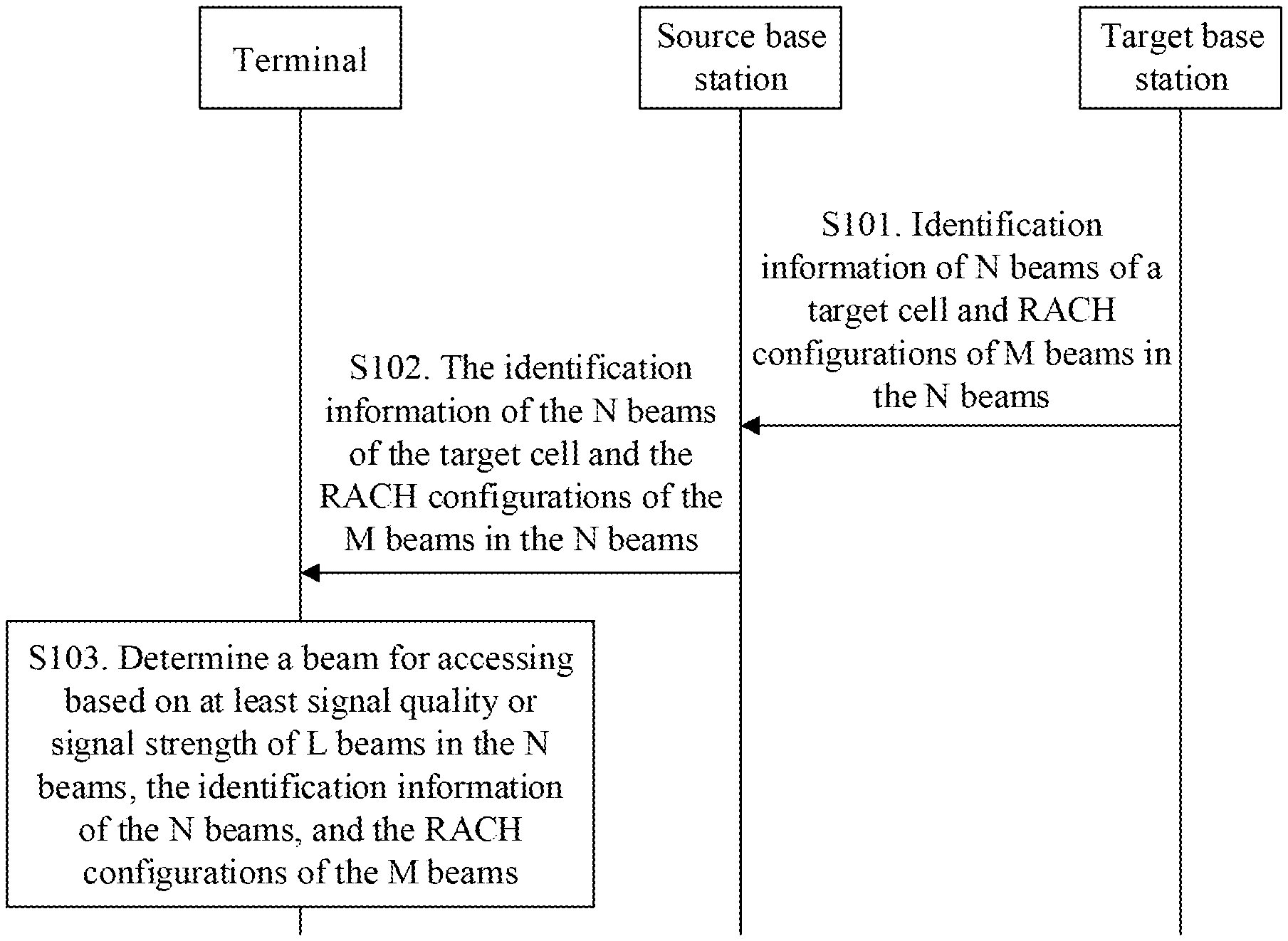
[0058] FIG. 1 is a schematic diagram of a communications system according to an embodiment of this application;
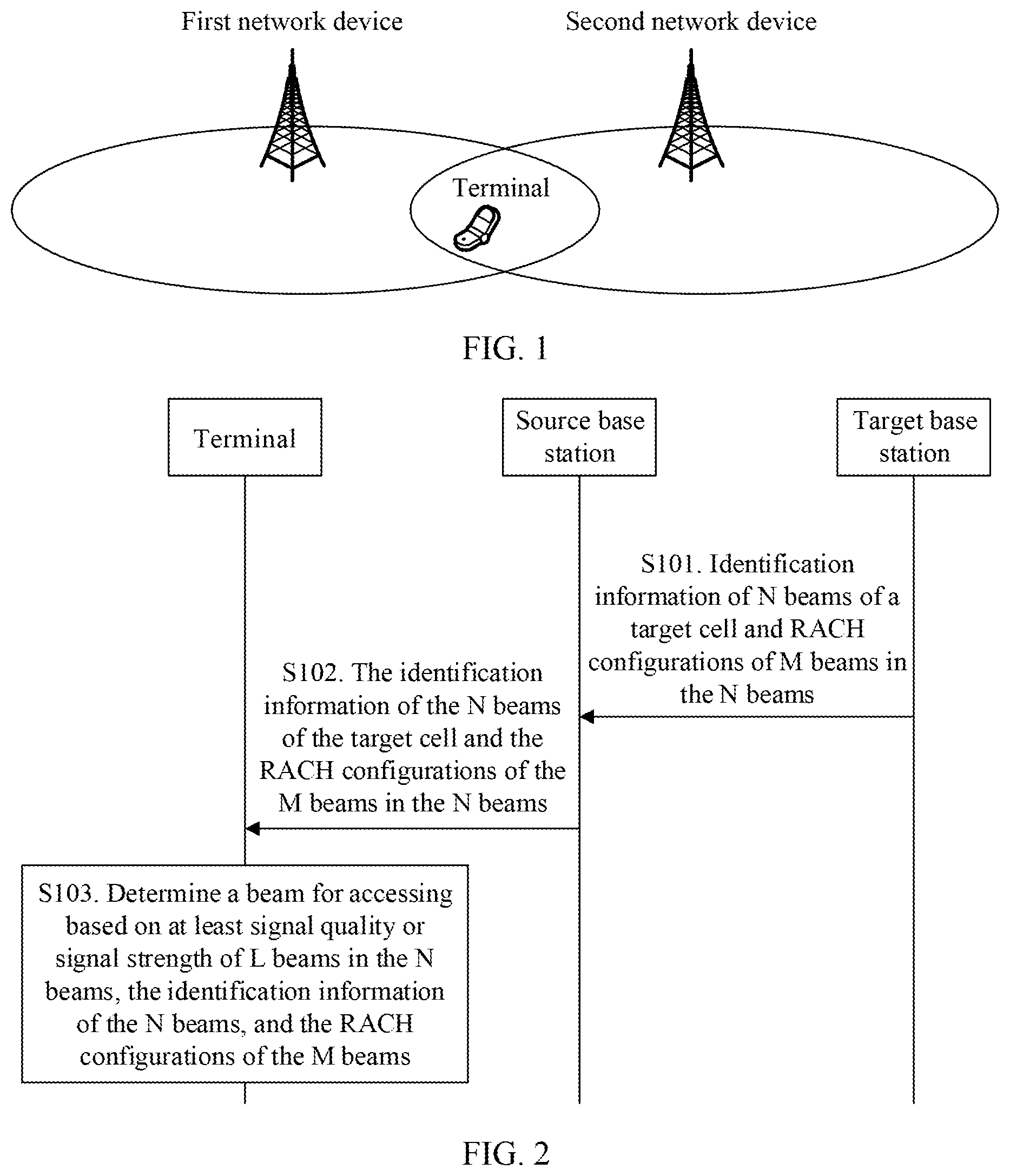
[0059] FIG. 2 is a flowchart of a communication method according to Embodiment 1 of this application;
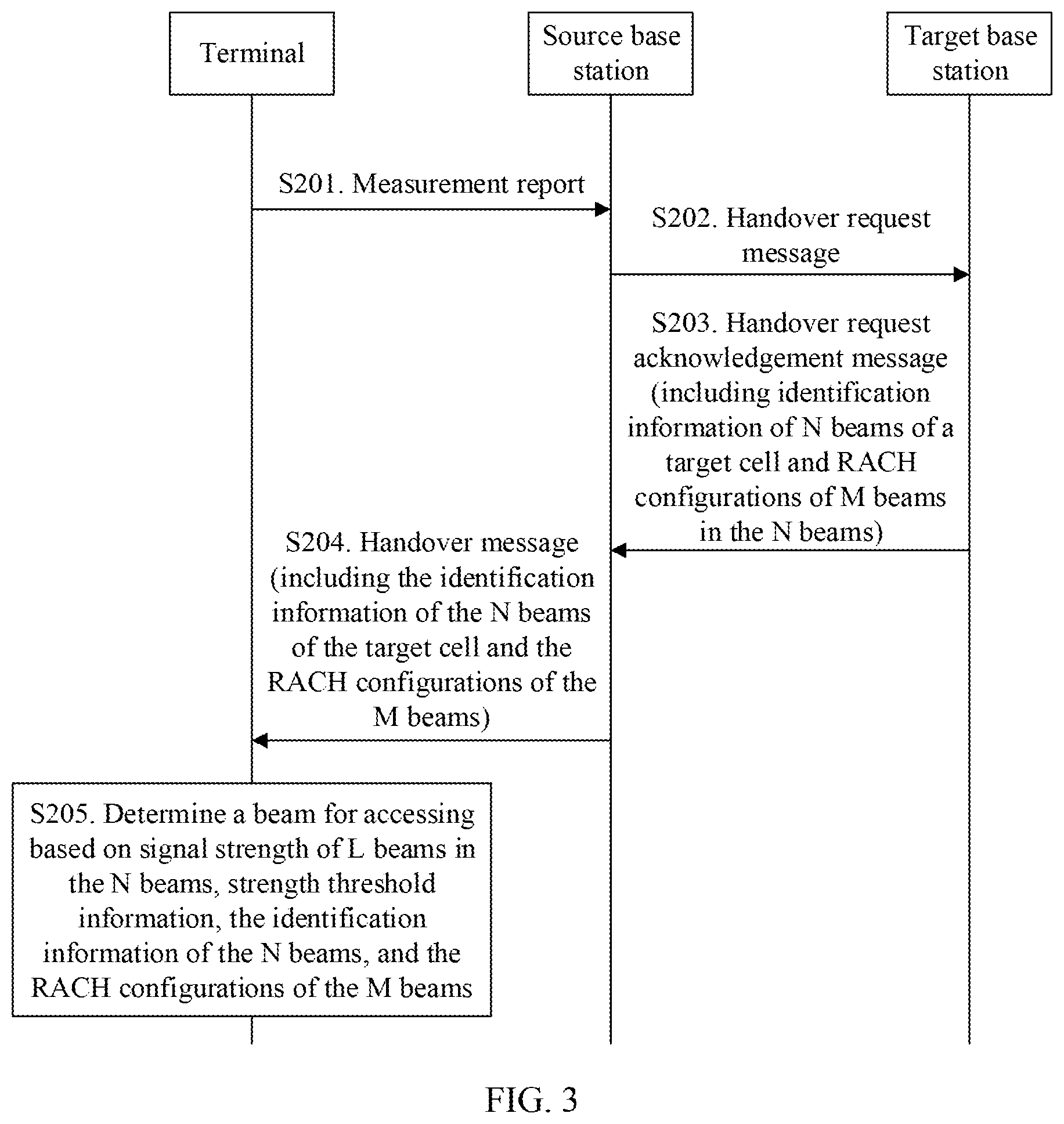
[0060] FIG. 3 is a flowchart of a communication method according to Embodiment 2 of this application;
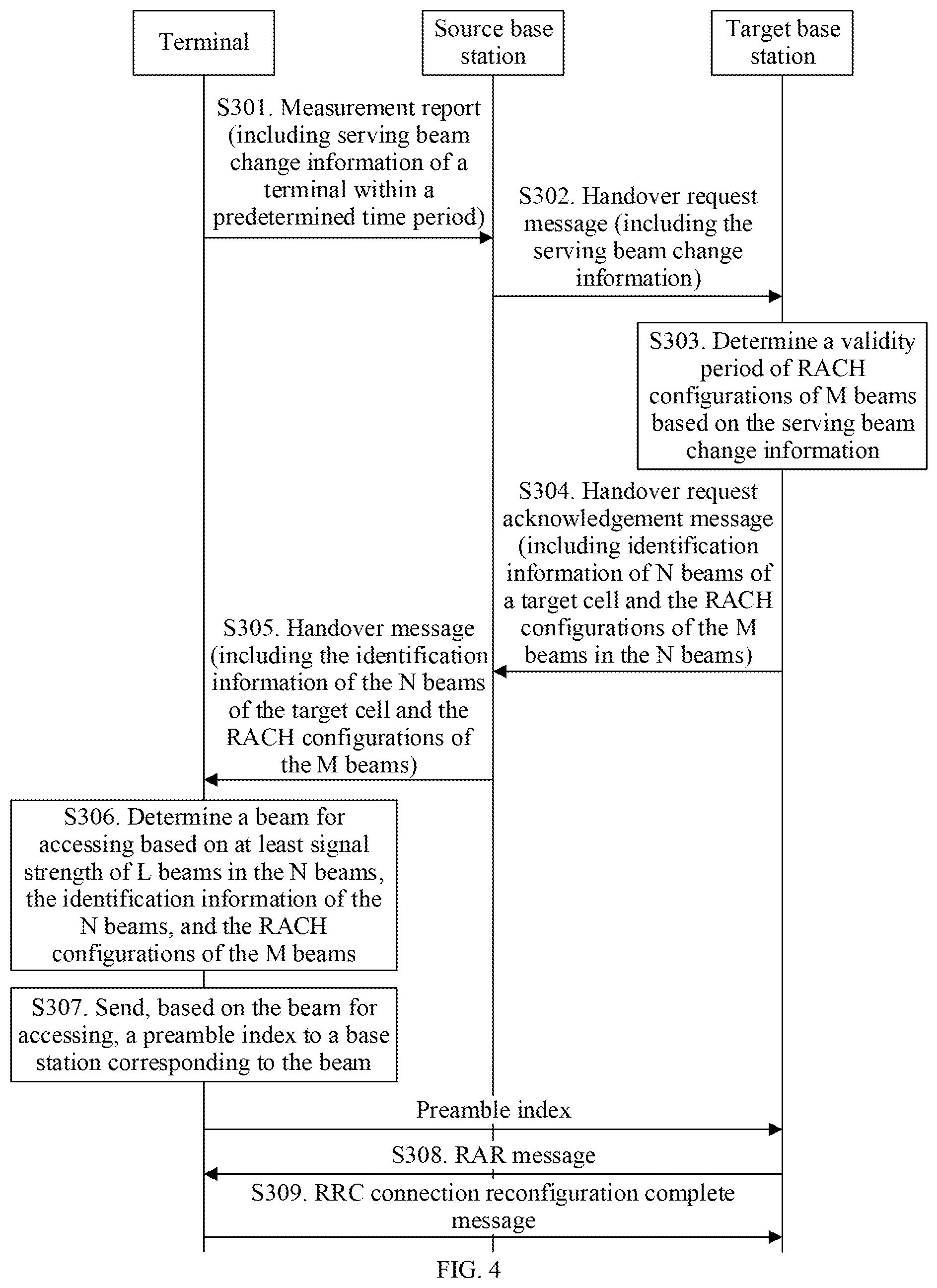
[0061] FIG. 4 is a flowchart of a communication method according to Embodiment 3 of this application;
[0062] FIG. 5 is a schematic structural diagram of a communications apparatus according to an embodiment of this application;
[0063] FIG. 6 is a schematic structural diagram of a terminal according to an embodiment of this application;
[0064] FIG. 7 is a schematic structural diagram of a communications apparatus according to an embodiment of this application;
[0065] FIG. 8 is a schematic structural diagram of a network device according to an embodiment of this application;
[0066] FIG. 9 is a schematic structural diagram of a communications apparatus according to an embodiment of this application; and
[0067] FIG. 10 is a schematic structural diagram of a network device according to an embodiment of this application.
DETAILED DESCRIPTION OF ILLUSTRATIVE EMBODIMENTS
[0068] FIG. 1 is a schematic diagram of a communications system according to an embodiment of this application. As shown in FIG. 1, the communications system includes at least two network devices and at least one terminal. The at least two network devices communicate with the at least one terminal by using a technical solution provided in the following embodiments of this application. FIG. 1 shows one terminal and two network devices: a first network device and a second network device.
[0069] Some terms in this application are explained in the following, to help a person skilled in the art have a better understanding:
[0070] A network device is also referred to as a radio access network (RAN) device, is a device that connects a terminal to a radio network, and may be an evolved NodeB (eNB or eNodeB) in long term evolution (LTE), a relay node, an access point, or a gNB in a 5G network, for example, a transmission and reception point (TRP) or a controller. This is not limited herein.
[0071] A terminal may be a wireless or wired terminal. The wireless terminal may be a device having a wireless receiving and sending function, and may be deployed on land, including an indoor or outdoor terminal, a handheld terminal, or an in-vehicle terminal; or may be deployed on the water (for example, in a steamship); or may be deployed in the air (for example, on an airplane, on a balloon, or on a satellite). The terminal may be a mobile phone a tablet computer (Pad), a computer having a wireless receiving and sending function, a virtual reality (VR) terminal, an augmented reality (AR) terminal, a wireless terminal in industrial control, a wireless terminal in self driving, a wireless terminal in telemedicine, a wireless terminal in smart grid, a wireless terminal in transportation safety, a wireless terminal in smart city, a wireless terminal in smart home, or the like. This is not limited herein.
[0072] In this embodiment of this application, beams may include a transmit beam and a receive beam. The transmit beam may be signal strength distribution formed in different spatial directions after signals are transmitted through an antenna, and the receive beam may be signal strength distribution formed in different spatial directions after wireless signals are received through an antenna. It can be understood that one or more antenna ports for one beam may also be considered as an antenna port set. In other words, one antenna port set includes at least one antenna port.
[0073] Specifically, the beam may refer to a precoding vector having specific energy transmission directivity, and the precoding vector can be identified by using identification information. The energy transmission directivity means that a signal obtained by performing precoding processing by using the precoding vector is received at a relatively high receive power in a specific spatial location, for example, the receive power meets a reception demodulation signal-to-noise ratio. However, a signal obtained by performing precoding processing by using the precoding vector is received at a relatively low power in another spatial location, for example, the receive power does not meet a reception demodulation signal-to-noise ratio. Different communications devices may have different precoding vectors, that is, corresponding to different beams. One communications device may use one or more of a plurality of different precoding vectors at a same time point based on a configuration or capability of the communications device, that is, one or more beams may be formed simultaneously. The beam may be understood as a spatial resource. The beam may be identified by using identification information. Optionally, the identification information may be corresponding to a configured corresponding resource identifier (ID) of user equipment. For example, the identification information may be corresponding to a configured ID or resource of a channel state information-reference signal (CSI-RS), or may be corresponding to a configured ID or resource of an uplink sounding reference signal (SRS). Alternatively, optionally, the identification information may be identification information explicitly or implicitly carried on a signal or channel that is carried on a beam. For example, the identification information includes but is not limited to identification information of the beam indicated by a synchronization signal or broadcast channel that is sent by using the beam, and includes but is not limited to identification information of the beam indicated by a synchronization signal block (SS block) that is sent by using the beam. The SS block includes at least a primary synchronization signal (PSS), and/or a secondary synchronization signal (SSS), and/or a broadcast channel (PBCH).
[0074] It should be noted that descriptions are provided in the following method embodiments by using an example in which the first network device is a source base station and the second network device is a target base station.
[0075] FIG. 2 is a flowchart of a communication method according to Embodiment 1 of this application. As shown in FIG. 2, the method in this embodiment may include the following steps.
[0076] S101. A target base station sends identification information of N beams of a target cell and random access channel (RACH) configurations of M beams in the N beams to a source base station.
[0077] In this embodiment, the target base station performs admission control, to allow a terminal to be handed over from a serving cell to the target cell; and then the target base station sends the identification information of the N beams of the target cell and the RACH configurations of the M beams in the N beams to the source base station. The RACH configuration may be corresponding to an SS block, or may be corresponding to a CSI-RS. N and M are positive integers. Further, the target base station may alternatively send a cell identifier of the target cell to the source base station.
[0078] Optionally, before the target base station sends the information described in step S101 to the source base station, the target base station may receive a handover request message sent by the source base station. This is not limited in this embodiment.
[0079] The identification information of the N beams and the RACH configurations of the M beams may be included in a same message or different messages sent by the target base station to the source base station. Alternatively, the target base station may send the identification information of the N beams and the RACH configurations of the M beams to the source base station at a same time point or different time points.
[0080] Optionally, the identification information of the N beams and the RACH configurations of the M beams may be included in a handover request acknowledgement message sent by the target base station to the source base station.
[0081] S102. The source base station sends the identification information of the N beams of the target cell and the RACH configurations of the M beams in the N beams to a terminal.
[0082] In this embodiment, after receiving the identification information of the N beams and the RACH configurations of the M beams in the N beams that are sent by the target base station, the source base station sends the identification information of the N beams and the RACH configurations of the M beams in the N beams to the terminal.
[0083] The identification information of the N beams and the RACH configurations of the M beams may be included in a same message or different messages sent by the source base station to the terminal. Alternatively, the source base station may send the identification information of the N beams and the RACH configurations of the M beams to the terminal at a same time point or different time points.
[0084] Optionally, the identification information of the N beams and the RACH configurations of the M beams in the N beams may be included in a handover message sent by the source base station to the terminal. The handover message may be a radio resource control (RRC) connection reconfiguration message that carries a mobility control information element or another message such as another RRC message different from the RRC connection reconfiguration message, layer-1 signaling, or layer-2 signaling.
[0085] S103. The terminal determines a beam for accessing based on at least signal quality or signal strength of L beams in the N beams, the identification information of the N beams, and the RACH configurations of the M beams.
[0086] In this embodiment, the terminal determines the beam for accessing based on the signal quality or signal strength of the L beams, the identification information of the N beams, and the RACH configurations of the M beams. After determining the beam for accessing, the terminal uses the beam to access the target cell to which the beam belongs.
[0087] It can be understood that the terminal measures at least one found beam, to obtain signal quality or signal strength of the beam. The found beam is not limited to the N beams of the target cell. In other words, a beam of a cell other than the target cell may also be found. In addition, there is no limitation that each of the N beams needs to be measured.
[0088] Optionally, in one case, L herein may alternatively be considered as a quantity of beams whose signal quality or signal strength is detected.
[0089] Herein, the M beams and the L beams may have an intersection or may have no intersection. This is not limited in this embodiment of this application.
[0090] Signal quality of a beam may be first signal received quality of the beam. Signal strength of a beam may be a first signal received power of the beam. A first signal includes a synchronization signal and/or a reference signal.
[0091] In this embodiment, the source base station sends the identification information of the N beams and the RACH configurations of the M beams in the N beams to the terminal, and then the terminal determines the beam for accessing based on the signal quality or signal strength of the L beams in the N beams, the identification information of the N beams, and the RACH configurations of the M beams. Therefore, this embodiment provides a proper beam for accessing determining solution. Further, the beam for accessing in this embodiment is determined by the terminal based on the signal quality or signal strength of the L beams in the N beams and the received RACH configurations of the M beams. Therefore, the beam for accessing determined in this manner can increase a success rate of accessing a cell by the terminal, increasing a handover success rate.
[0092] The following describes, by using signal strength of a beam as an example, how to determine a beam for accessing. A solution of the signal quality is similar to the solution of the signal strength, and details are not described in the embodiments.
[0093] FIG. 3 is a flowchart of a communication method according to Embodiment 2 of this application. As shown in FIG. 3, the method in this embodiment may include the following steps.
[0094] S201. A terminal sends a measurement report to a source base station.
[0095] Optionally, before sending the measurement report to the source base station, the terminal receives measurement configuration information sent by the source base station, and performs measurement for a serving cell and a neighboring cell based on the configuration information.
[0096] In a possible implementation, the configuration information is used to configure the terminal to measure beams of the serving cell and the neighboring cell. The configuration information includes but is not limited to a beam quantity K and a beam signal strength threshold that is X for short. The terminal determines signal strength of the serving cell and signal strength of the neighboring cell based on signal strength of K beams whose signal strength is greater than or equal to X. When the determined signal strength of the serving cell and the determined signal strength of the neighboring cell meet a corresponding measurement event determining condition, for example, a determining condition for an event A3, an event A4, an event A5, or another measurement event in LTE, the terminal sends the measurement report. The measurement report includes signal strength of at least one neighboring cell, and/or signal strength of K beams of each neighboring cell, identification information of the serving cell, and identification information of the at least one neighboring cell. The identification information of the serving cell and the identification information of the at least one neighboring cell include a cell ID or a cell index. Optionally, the measurement report may alternatively include identification information of K beams used to generate the signal strength of the neighboring cell or signal strength of K beams used to generate the signal strength of the neighboring cell.
[0097] It can be understood that the neighboring cell includes the target cell in the embodiment shown in FIG. 2. The configuration information may alternatively not carry the beam quantity or beam signal strength threshold information. In this case, the terminal measures signal strength of a cell.
[0098] Optionally, an SS block and a CSI-RS are reference signals and are transmitted on a beam. The measurement configuration information is specifically used to configure the terminal to measure the SS block and/or the CSI-RS transmitted on the beam. Correspondingly, signal strength of the beam includes signal strength of the SS block on the beam and/or signal strength of the CSI-RS on the beam. A quantity of beams whose signal strength is obtained by measuring the SS block may be the same as or different from a quantity of beams whose signal strength is obtained by measuring the CSI-RS. Correspondingly, a beam signal strength threshold corresponding to the measurement configuration information may include an SS block beam signal strength threshold and/or a CSI-RS beam signal strength threshold. In other words, X includes X1 and X2, where X1 is corresponding to the SS block beam signal strength threshold, X2 is corresponding to the CSI-RS beam signal strength threshold, and X1 may or may not be equal to X2.
[0099] Identification information of a beam in this embodiment may be identification information of an SS block transmitted on the beam and/or identification information of a CSI-RS transmitted on the beam.
[0100] The SS block is transmitted on a wide beam. The beam may be identified by using the identification information of the SS block. For example, the identification information of the SS block may be a time index indication (implicitly or explicitly) carried on a PBCH in the SS block.
[0101] The CSI-RS is transmitted on a narrow beam. The beam may be identified by using the identification information of the CSI-RS. For example, the identification information of the CSI-RS may be an identifier of a CSI-RS configuration. The CSI-RS configuration includes at least a resource configuration. The CSI-RS configuration may further include an antenna port used to send the CSI-RS, and the like.
[0102] Optionally, the measurement report may include information about at least one beam (the information about the beam herein may be signal strength of the beam and/or identification information of the beam) of the neighboring cell. The information about the at least one beam may be included in the measurement report in a form of a list. For example, beam identifiers of beams of each neighboring cell are arranged based on signal strength. The information about the at least one beam may be used by a target base station to determine beams (that is, M beams) configured with RACH configurations.
[0103] The terminal may determine report information about which beams of the neighboring cell in the measurement report, for example, in the following three manners. This is not limited in this embodiment.
[0104] In one manner, if a CSI-RS is measured, because a CSI-RS resource is configured by the source base station for the terminal in a measurement configuration message, if W CSI-RS resources are configured in the measurement configuration message, the terminal reports information about beams corresponding to the W CSI-RS resources, that is, information about a beam corresponding to each of the W CSI-RS resources.
[0105] In another manner, a measurement configuration message received by the terminal includes a threshold. The threshold Q is not equal to X. The threshold is used by the terminal to determine whether information about a beam needs to be reported. That is, if signal strength, measured by the terminal, of a beam of the neighboring cell is higher than (not lower than) the threshold, the terminal reports the information about the beam in the measurement report.
[0106] In another manner, optionally, the terminal reports information about a maximum of P beams based on a value P, or may report, based on the threshold Q, information about a maximum of P beams whose signal quality or signal strength is higher than Q. The value P may be a preset maximum value P, or may be included in the measurement configuration message sent by the source base station to the terminal.
[0107] It can be understood that the measurement report reporting manner and content of the measurement configuration information may be independent of this embodiment of this application, that is, may be applied to another solution different from this embodiment of this application.
[0108] S202. The source base station sends a handover request message to a target base station.
[0109] In this embodiment, the source base station receives the measurement report sent by the terminal, and performs handover decision based on the measurement report. The source base station may send the handover request message to a target base station to which a target cell belongs, where a neighboring cell with highest signal strength in a plurality of reported neighboring cells may be used as the target cell, and the handover request message may include an identifier of the target cell.
[0110] Optionally, the handover request message may further include information about at least one beam of the target cell (including signal strength of the beam and/or identification information of the beam).
[0111] Optionally, the source base station may send the handover request message to each of the plurality of neighboring cells based on signal strength of the plurality of neighboring cells in the measurement report. This can ensure that when the target base station does not allow the terminal to be handed over to the target cell, a base station to which another neighboring cell belongs can allow, based on the handover request message, the terminal to be handed over to the another neighboring cell.
[0112] The source base station may alternatively send the handover request message to the target base station based on, but not limited to, the measurement report sent by the terminal. For example, the source base station alternatively sends the handover request message to the target base station based on a current network status, or the like.
[0113] It can be understood that the handover request message is used as an example for description. Corresponding handover preparation interaction may alternatively be completed through another message, and such a type of message may be referred to as a first message.
[0114] S203. The target base station sends a handover request acknowledgement message to the source base station.
[0115] In this embodiment, the target base station replies to the source base station with the handover request acknowledgement message after performing admission control based on the handover request message. The handover request acknowledgement message includes identification information of N beams of the target cell and RACH configurations of M beams in the N beams.
[0116] It can be understood that the handover request acknowledgement message is used as an example for description. Corresponding handover preparation interaction may alternatively be completed through another message, and such a type of message may be referred to as a second message. The second message is an acknowledgement message for the first message.
[0117] S204. The source base station sends a handover message to the terminal.
[0118] In this embodiment, after receiving the handover request acknowledgement message, the source base station sends the handover message to the terminal. The handover message includes the identification information of the N beams of the target cell and the RACH configurations of the M beams.
[0119] It can be understood that the handover message is used as an example for description. A corresponding handover indication may alternatively be completed through another message, and such a type of message may be referred to as a third message.
[0120] Optionally, the identification information of the N beams may be sent in a form of a list. Certainly, the identification information of the N beams may alternatively be sent in another form. This is not limited in this embodiment.
[0121] It can be understood that the handover message may further carry corresponding priority information, and the priority information may be notified in different manners, and examples are as follows.
[0122] In a first manner, the identification information of the N beams is sent in the form of a list. The list has a priority order, that is, a beam order and a beam priority are bound in the list. For example, for identification information of the first beam in the list, the beam has a highest priority, and beams are arranged sequentially based on a priority order. Identification information of two beams is used as an example. If a list is {identification information of a beam 2, identification information of a beam 1}, a priority of the beam 2 is higher than a priority of the beam 1.
[0123] In a second manner, the identification information of the N beams is sent in a form of a list. The list further includes priority information corresponding to a beam. The priority information is used to indicate a beam priority. Two beams are used as an example. The two beams are sent in a form of a list. The list does not have a priority order, but the list includes priority information of the beams. If the list is {identification information of a beam 1 and priority information=2, identification information of a beam 2 and priority information=1}, it indicates that a priority of the beam 2 is higher than a priority of the beam 1.
[0124] S205. The terminal determines abeam for accessing based on signal strength of L beams in N beams, strength threshold information, identification information of the N beams, and RACH configurations of the M beams.
[0125] The strength threshold information may be pre-specified, or may be received by the terminal.
[0126] It can be understood that if the beam for accessing the target cell is determined based on signal quality, corresponding quality threshold information is used.
[0127] The terminal may receive the strength threshold information sent by the source base station. For example, the strength threshold information is included in the handover message sent by the source base station to the terminal. In a manner, the strength threshold information is included in the handover message. Alternatively, optionally, minimum system information (minimum SI) is carried in the handover message, and the strength threshold information is included in the minimum system information (minimum SI) in the handover message. The strength threshold information may be determined by the source base station, or the strength threshold information may be sent by the target base station and received by the source base station. For example, the strength threshold information is included in the handover request acknowledgement message sent by the target base station to the source base station.
[0128] The terminal may receive the strength threshold information sent by the target base station. For example, the strength threshold information is included in system information (SI) that is broadcast by the target base station by using the target cell. The SI may include minimum system information (minimum SI) and other system information (other SI) different from the minimum system information. The strength threshold information may be included in the minimum SI in the SI, or may be included in the OSI.
[0129] The strength threshold information includes a first beam signal strength threshold and/or strength threshold indication information, the strength threshold indication information is used to indicate a relationship between the first beam signal strength threshold and a second beam signal strength threshold, and the second beam signal strength threshold is a beam signal strength threshold carried in the measurement configuration message, namely, X mentioned above.
[0130] In this embodiment, after receiving the handover message, the terminal determines the first beam signal strength threshold based on the strength threshold information; and compares the signal strength of the L beams in the N beams with the first beam signal strength threshold based on the identification information of the N beams, and determines, based on the RACH configurations of the M beams in the N beams, the beam for accessing the target cell.
[0131] The following provides descriptions by using a first beam signal strength threshold Y as an example.
[0132] The strength threshold indication information may indicate a relationship between X and Y, for example, indicating whether X is equal to Y. The strength threshold indication information may be a binary bit value. For example, "o" indicates that X is not equal to Y, and "1" indicates that X is equal to Y; vice versa. Alternatively, the strength threshold indication information is a Boolean value. `TRUE` indicates that X is equal to Y, and `FALSE` indicates that X is not equal to Y; vice versa. Alternatively, the strength threshold indication information is an information element. When the information element is carried, it indicates that X is not equal to Y, and when the information element is not carried, it indicates that X is equal to Y; vice versa.
[0133] If X is equal to Y, optionally, the strength threshold information may not carry the value Y, and after parsing out that "X is equal to Y" indicated in the strength threshold indication information, the terminal determines, based on the value X, the beam for accessing the target cell. Optionally, if X is not equal to Y, the strength threshold information carries the value Y. Optionally, the strength threshold information may not carry the strength threshold indication information.
[0134] Optionally, when the identification information of the N beams include identification information of an SS block transmitted on a beam and/or identification information of a CSI-RS transmitted on a beam, the strength threshold indication information may be SS block strength threshold indication information and CSI-RS strength threshold indication information. The first beam signal strength threshold (Y) includes a first SS block beam signal strength threshold (Y1) and a first CSI-RS beam signal strength threshold (Y2).
[0135] Optionally, the strength threshold information further includes first indication information. The first indication information is used to indicate a relationship between Y1 and Y2, for example, whether Y1 is equal to Y2. The first indication information may be a binary bit value. For example, "0" indicates that Y1 is not equal to Y2, and "1" indicates that Y1 is equal to Y2; vice versa. Alternatively, the first indication information is a Boolean value. `TRUE` indicates that Y1 is equal to Y2, and `FALSE` indicates that Y1 is not equal to Y2; vice versa. Alternatively, the first indication information is an information element. When the information element is carried, it indicates that Y1 is not equal to Y2, and when the information element is not carried, it indicates that Y1 is equal to Y2; vice versa.
[0136] If the threshold Y1 is equal to the threshold Y2, optionally, the strength threshold information may carry a threshold, to be specific, Y, where both Y1 and Y2 are Y. Because the strength threshold information carries the threshold Y, after parsing out that "Y1 is equal to Y2" indicated by the first indication information, the terminal uses the value Y (corresponding to both signal strength of the SS block transmitted on a beam and signal strength of a CSI-RS transmitted on a beam) to determine the beam for accessing the target cell. If Y1 is not equal to Y2, the strength threshold information carries two values, that is, Y1 and Y2, and the terminal uses Y1 and Y2 to determine the beam for accessing the target cell.
[0137] Based on the description of the strength threshold information, S205 may be specifically: The terminal can determine, based on the received RACH configurations of the M beams in the N beams, that a RACH configuration is configured for each of the M beams (that is, a RACH configuration corresponding to each beam is configured for the beam); and the terminal can obtain the signal strength of the L beams in the N beams, compare the signal strength of the L beams with the first beam signal strength threshold, and determine the beam for accessing on this.
[0138] In a first feasible implementation, the N beams include a beam that meets the following two conditions: A RACH configuration is configured for the beam, and signal strength of the beam is greater than or equal to the first beam signal strength threshold.
[0139] The terminal determines at least one beam whose signal strength is greater than or equal to the first beam signal strength threshold from the M beams as the beam for accessing the target cell. That is, if determining that a RACH configuration is configured for a beam and signal strength of the beam is greater than or equal to the first beam signal strength threshold, the terminal determines the beam as the beam for accessing the target cell. In this implementation, the determined beam for accessing the target cell belongs to the N beams, and belongs to the M beams.
[0140] Optionally, the identification information of the N beams includes identification information of an SS block and/or identification information of a CSI-RS. Therefore, when the N beams include both a beam identified by the identification information of the SS block and a beam identified by the identification information of the CSI-RS, a priority of the beam identified by the identification information of the CSI-RS is higher than that of the beam identified by the identification information of the SS block, and the terminal preferentially determines, as the beam the target cell, a beam configured with a RACH configuration, whose signal strength is greater than or equal to the first beam signal strength threshold, and that is identified by the identification information of the CSI-RS. If no beam identified by identification information of CSI meets the following conditions: The RACH configuration of the beam belongs to the RACH configurations of the M beams and signal strength is greater than or equal to the first beam signal strength threshold; the terminal determines a beam configured with a RACH configuration, whose signal strength is greater than or equal to the first beam signal strength threshold, and that is identified by the identification information of the SS block as the beam for accessing the target cell.
[0141] It can be understood that if a plurality of beams that meet the foregoing two conditions are determined in the foregoing manners, the terminal may determine the first found beam that meets the foregoing conditions as the beam for accessing the target cell; or the terminal may randomly select, from the beams that meet the foregoing conditions, the beam for accessing the target cell; or the terminal may select a beam with highest signal strength from the beams that meet the foregoing conditions, as the beam for accessing the target cell; or the terminal may select a beam with a highest priority from the beams that meet the foregoing conditions, as the beam for accessing the target cell. For a beam priority order, refer to the foregoing related descriptions.
[0142] Optionally, a priority order of the beam identified by the identification information of the CSI-RS and the beam identified by the identification information of the SS block may be predefined, or may be configured by a network device. For example, the priority order is indicated through the handover message.
[0143] A RACH configuration of each of the M beams includes a preamble index and a time-frequency resource configuration. The RACH configuration may be considered as a contention free random access (CFRA) configuration. When the beam that is for accessing the target cell and that is determined by the terminal belongs to the M beams, the terminal initiates a random access process to the target cell based on the RACH configuration of the beam.
[0144] In this implementation, the beam that is for accessing the target cell and that is determined by the terminal has the RACH configuration and high signal strength. In this way, a success rate of accessing the target cell by the terminal is higher.
[0145] In a second feasible implementation, when signal strength of each of the M beams is less than the first beam signal strength threshold, the beam for accessing the target cell is determined from the M beams. For example, the terminal searches the N beams for the signal strength of M beams, and when the signal strength of each of the M beams is less than the first beam signal strength threshold, determines the beam for accessing the target cell from the M beams. The determined beam for accessing the target cell in this embodiment belongs to the M beams.
[0146] When M is greater than 1, the terminal may determine the first found beam in the M beams as the beam for accessing the target cell, the terminal may randomly select, from the M beams, the beam for accessing the target cell, the terminal may select a beam with highest signal strength from the M beams as the beam for accessing the target cell, or the terminal may select a beam with a highest priority from the M beams as the beam for accessing the target cell. For a beam priority order, refer to the foregoing related descriptions.
[0147] Optionally, the identification information of the N beams includes identification information of an SS block and/or identification information of a CSI-RS. Therefore, when the N beams include both a beam identified by the identification information of the SS block and a beam identified by the identification information of the CSI-RS, a priority of the beam identified by the identification information of the CSI-RS is higher than that of the beam identified by the identification information of the SS block, and the terminal preferentially determines the beam for accessing the target cell from the beam identified by the identification information of the CSI-RS in the M beams. If the M beams do not include a beam identified by identification information of CSI, the terminal determines the beam for accessing the target cell from the beam identified by the identification information of the SS block in the M beams.
[0148] It can be understood that the manner of determining the beam for accessing the target cell from the beam identified by the identification information of the CSI-RS or determining the beam for accessing the target cell from the beam identified by the identification information of the SS block in the M beams is similar to the manner of determining the beam for accessing the target cell from the M beams in the second feasible implementation.
[0149] In this implementation, the beam that is for accessing the target cell and that is determined by the terminal has the RACH configuration. In this way, a success rate of accessing the target cell by the terminal is high.
[0150] In a third feasible implementation, signal strength of each of the M beams is less than the first beam signal strength threshold, and the L beams include a beam whose signal strength is greater than or equal to the first beam signal strength threshold.
[0151] The terminal determines, based on the identifiers of the N beams, the signal strength of the L beams, and the strength threshold information, the beam whose signal strength is greater than or equal to the first beam signal strength threshold as the beam for accessing the target cell. In this case, the beam whose signal strength is greater than or equal to the first beam signal strength threshold may be understood as one of the L beams. That is, the terminal searches the N beams for the signal strength of the L beams, and when the signal strength of each of the M beams is less than the first beam signal strength threshold, the terminal determines the beam for accessing the target cell from the L beams based on that a signal strength threshold of the beam for accessing the target cell is greater than or equal to the first beam signal strength threshold. If the L beams include a plurality of beams whose signal strength is greater than or equal to the first beam signal strength threshold, the terminal may determine the first found beam whose signal strength is greater than or equal to the first beam signal strength threshold as the beam for accessing the target cell. Alternatively, the terminal may randomly select, from the beams whose signal strength is greater than or equal to the first beam signal strength threshold, the beam for accessing the target cell, or the terminal may select a beam with highest signal strength from the beams whose signal strength is greater than or equal to the first beam signal strength threshold as the beam for accessing the target cell, or the terminal may select a beam with a highest priority from the beams whose signal strength is greater than or equal to the first beam signal strength threshold as the beam for accessing the target cell. For a beam priority order, refer to the foregoing related descriptions.
[0152] Optionally, the identification information of the N beams includes identification information of an SS block and/or identification information of a CSI-RS. Therefore, when the N beams include both a beam identified by the identification information of the SS block and a beam identified by the identification information of the CSI-RS, a priority of the beam identified by the identification information of the CSI-RS is higher than that of the beam identified by the identification information of the SS block, and the terminal preferentially determines, as the beam for accessing the target cell, a beam whose signal strength is greater than or equal to the first beam signal strength threshold and that is identified by the identification information of the CSI-RS. If the beam identified by identification information of CSI does not include a beam whose signal strength is greater than or equal to the first beam signal strength threshold, the terminal determines, as the beam for accessing the target cell, a beam whose signal strength is greater than or equal to the first beam signal strength threshold and that is identified by the identification information of the SS block.
[0153] It can be understood that when there are a plurality of determined beams whose signal strength is greater than or equal to the first beam signal strength threshold and that is identified by the identification information of the CSI-RS or the identification information of the SS block, a processing manner similar to the processing manner used in the third feasible implementation when the L beams include a plurality of beams whose signal strength is greater than or equal to the first beam signal strength threshold, and details are not described herein again.
[0154] Optionally, when the beam that is for accessing the target cell and that is determined by the terminal does not belong to the M beams, the terminal may listen to and parse system information of the target cell, and initiate random access to the target cell based on a common RACH configuration in the system information.
[0155] In this implementation, the terminal determines that the beam for accessing the target cell has high signal strength. In this way, a success rate of accessing the target cell by the terminal is high.
[0156] In a fourth feasible implementation, signal strength of each of the M beams is less than the first beam signal strength threshold, and the L beams do not include a beam whose signal strength is greater than or equal to the first beam signal strength threshold.
[0157] The terminal determines, from the L beams based on the identifiers of the N beams and the signal strength of the L beams, a beam with highest signal strength as the beam for accessing the target cell; or the terminal may determine the first found beam in the L beams as the beam for accessing the target cell; or the terminal may randomly select, from the L beams, the beam the target cell; or the terminal may select a beam with a highest priority from the L beams as the beam for accessing the target cell, where for a beam priority order, refer to the foregoing related descriptions.
[0158] The determined beam for accessing the target cell in this embodiment belongs to the L beams, but the beam that is for accessing the target cell and that is determined in this case may or may not belong to the M beams.
[0159] Optionally, the identification information of the N beams includes identification information of an SS block and/or identification information of a CSI-RS. Therefore, when the N beams include both a beam identified by the identification information of the SS block and a beam identified by the identification information of the CSI-RS, a priority of the beam identified by the identification information of the CSI-RS is higher than that of the beam identified by the identification information of the SS block, and the terminal preferentially determines, as the beam for accessing the target cell, a beam with highest signal strength from the beam identified by the identification information of the CSI-RS in the L beams. If the L beams do not include a beam identified by identification information of CSI, the terminal determines, as the beam the target cell, a beam with highest signal strength from the beam identified by the identification information of the SS block in the L beams. It can be understood that the manner of determining the beam the target cell from the beam identified by the identification information of the CSI-RS or from the beam identified by the identification information of the SS block may alternatively be determining the first found beam as the beam for accessing the target cell, or randomly selecting a beam, or selecting a beam with a highest priority. This is not limited in this embodiment of this application.
[0160] In this implementation, the terminal determines, in a relatively flexible manner, the beam for accessing the target cell.
[0161] It can be understood that in the foregoing feasible implementations, descriptions are provided by using a case in which M is greater than or equal to 1 as an example. In a possible case, M may alternatively be equal to 0, indicating that the target base station provides no RACH configuration for the beam of the target cell. In this case, the beam for accessing the target cell may be determined in the following manner: The terminal finds L beams in the N beams, and the terminal may determine the beam for accessing the target cell from the L beams. For example, the terminal determines a beam with highest signal strength from the L beams as the beam for accessing the target cell, or the terminal determines the first found beam in the L beams as the beam for accessing the target cell, or the terminal determines a beam with a highest priority from the L beams as the beam the target cell, or the terminal randomly determines, from the L beams, the beam the target cell. It can be understood that when M=0, the manner of determining the beam for accessing the target cell may also be applicable to a scenario in which none of the M beams is found.
[0162] In another possible implementation, when none of the M beams is found, or M is equal to 0, or none of the N beams is found, or signal strength of each of the L or M beams is less than the first beam signal strength threshold, it indicates that when the target base station provides no RACH configuration for the beam of the target cell, the beam for accessing may alternatively be determined in one of the following manners.
[0163] (1) The terminal determines a beam with highest signal strength from a found beam of the target cell as the beam for accessing the target cell, or the terminal determines the first found beam of the target cell as the beam for accessing the target cell, or the terminal determines a beam with a highest priority from a found beam of the target cell as the beam for accessing the target cell, or the terminal randomly determines, from a beam of the target cell, the beam for accessing the target cell. According to this manner, the terminal preferentially accesses the target cell, to avoid an access failure as much as possible.
[0164] (2) The terminal determines a beam with highest signal strength from a found beam as the beam for accessing. Alternatively, the terminal determines the first found beam as the beam for accessing; in this case, the beam may belong to the target cell. Alternatively, the terminal determines a beam with a highest priority from a found beam as a beam for accessing a neighboring cell. Alternatively, the terminal randomly determines the beam for accessing, and the beam may belong to the target cell. The beam for accessing may belong to the target cell, or the beam for accessing may belong to a neighboring cell other than the target cell.
[0165] (3) The terminal initiates an RRC connection re-establishment process, and optionally, the terminal performs the RRC connection re-establishment process in a current serving cell.
[0166] Based on the foregoing embodiment of this application, optionally, the terminal initiates an RRC connection re-establishment process if the terminal determines the beam in the foregoing manner and initiates a random access process, but the random access process fails, for example, a quantity of times of sending a preamble index by the terminal reaches a maximum quantity of sending times, but the terminal does not receive a random access response (RAR) message returned by the base station. Optionally, the terminal performs the RRC connection re-establishment process in the current serving cell.
[0167] The foregoing embodiment of this application provides a plurality of beam for accessing determining manners, so that the terminal flexibly selects a beam for accessing.
[0168] FIG. 4 is a flowchart of a communication method according to Embodiment 3 of this application. As shown in FIG. 4, the method in this embodiment may include the following steps.
[0169] S301. A terminal sends a measurement report to a source base station, where the measurement report includes serving beam change information of the terminal within a predetermined time period.
[0170] For the measurement report in this embodiment, refer to related descriptions in the embodiment shown in FIG. 3. In addition, the measurement report in this embodiment further includes the serving beam change information of the terminal within the predetermined time period. The serving beam change information is information, for example, a quantity of serving beam changes of the terminal within the predetermined time period or duration for which the terminal stays in each serving beam.
[0171] Optionally, the beam change information is not limited to being included in the measurement report, or may be included in a new RRC message, layer-1 signaling, or layer-2 signaling sent by the terminal to the source base station.
[0172] S302. The source base station sends a handover request message to a target base station, where the handover request message includes the serving beam change information.
[0173] For the handover request message in this embodiment, refer to related descriptions in the embodiment shown in FIG. 3. In addition, the handover request message in this embodiment further includes the serving beam change information.
[0174] S303. The target base station determines a validity period of RACH configurations of M beams based on the serving beam change information.
[0175] In this embodiment, the target base station may substantially determine a movement status of the terminal based on the serving beam change information, and determine the validity period of the RACH configurations of the M beams based on the movement status of the terminal. If it is determined, based on the serving beam change information, that the terminal changes a serving beam frequently, the validity period of the RACH configurations that are of the M beams and that are to be allocated by the target base station is relatively short, otherwise, the validity period of the RACH configurations that are of the M beams and that are to be allocated by the target base station is relatively long.
[0176] In a replaceable solution of S302 and S303, the source base station determines the validity period based on the serving beam change information; and then the source base station sends the handover request message to the target base station, where the handover request message includes the validity period. The target base station determines, based on the handover request message, that the validity period in the handover request message is the validity period of the RACH configurations of the M beams.
[0177] It can be understood that after the validity period of the RACH configurations expires, the target base station releases the RACH configurations of the M beams, thereby avoiding wasting resources for a long time.
[0178] All of steps S301 to S303 may alternatively be independent of subsequent steps and applied to another scenario or solution. S301 to S303 in this embodiment are applied to, but not limited to, the scenario or solution in this embodiment.
[0179] S304. The target base station sends a handover request acknowledgement message to the source base station.
[0180] In this embodiment, the handover request acknowledgement message includes identification information of N beams and the RACH configurations of the M beams. For the handover request message in this embodiment, refer to related descriptions in the embodiment shown in FIG. 3.
[0181] There is no particular order for performing steps S303 and S304.
[0182] S305. The source base station sends a handover message to the terminal, where the handover message includes identification information of N beams of a target cell and the RACH configurations of the M beams.
[0183] S306. The terminal determines a beam for accessing based on at least signal strength of L beams in the N beams, the identification information of the N beams, and the RACH configurations of the M beams.
[0184] In this embodiment, for S305 and S306, refer to related descriptions in the foregoing embodiments. Details are not described herein again.
[0185] S307. The terminal sends, based on the beam for accessing, a preamble index to a base station corresponding to the beam.
[0186] Herein, the base station corresponding to the beam may be the target base station, or may be another base station. FIG. 4 shows an example in which the base station corresponding to the beam is the target base station, but this is not limited in this embodiment.
[0187] S308. The base station corresponding to the beam sends a random access response (RAR) message to the terminal.
[0188] If the terminal determines that a beam for accessing the target cell belongs to the M beams, it indicates that a RACH configuration is configured for the beam for accessing the target cell. In this case, the terminal sends a preamble index to the target base station by using the RACH configuration. The target base station determines, based on the preamble index sent by the terminal and/or a time-frequency resource used for sending the preamble index, a beam selected for random access performed by the terminal to the target cell, the target base station sends an RAR message to the terminal based on the beam, and the target base station releases RACH configurations of other beams in the M beams.
[0189] If the terminal determines that a beam for accessing the target cell does not belong to the M beams, it indicates that no RACH configuration is configured for the beam for accessing the target cell. In this case, the terminal sends a randomly selected preamble index to the target base station on a common random access channel time-frequency resource.
[0190] S309. The terminal sends an RRC connection reconfiguration complete message to the base station corresponding to the beam.
[0191] After receiving the RAR message, the terminal sends the RRC connection reconfiguration complete message to the base station corresponding to the beam.
[0192] In this embodiment, according to the foregoing solution, the terminal determines the beam for accessing the target cell, and a success rate of accessing the target cell by the terminal can be improved based on the beam, increasing a handover success rate. In addition, the terminal further reports the serving beam change information of the terminal, so that the target base station determines the validity period of the RACH configurations of the M beams, and after the validity period expires, releases the RACH configurations of the M beams, avoiding occupying resources for a long time and increasing resource utilization.
[0193] It can be understood that in the foregoing embodiments, the methods or steps implemented by the terminal may alternatively be implemented by a chip inside the terminal. The methods or steps implemented by a base station such as the source base station may alternatively be implemented by a chip inside the base station.
[0194] An embodiment of this application provides a communications apparatus. The communications apparatus may be a terminal, or may be a chip inside a terminal. As shown in FIG. 5, the communications apparatus in this embodiment may include a receiving module 11 and a processing module 12.
[0195] The receiving module 11 is configured to receive identification information of N beams of a target cell and random access channel configurations of M beams in the N beams, where N and M are positive integers.
[0196] The processing module 12 is configured to determine a beam for accessing based on signal quality or signal strength of L beams in the N beams, the identification information of the N beams, and the random access channel configurations of the M beams, where L is a nonnegative integer.
[0197] Optionally, the processing module 12 is specifically configured to determine the beam for accessing based on the signal strength of the L beams in the N beams, strength threshold information, the identification information of the N beams, and the random access channel configurations of the M beams.
[0198] Optionally, the receiving module 11 is further configured to receive the strength threshold information.
[0199] Optionally, the strength threshold information includes a first beam signal strength threshold or strength threshold indication information, the strength threshold indication information is used to indicate a relationship between the first beam signal strength threshold and a second beam signal strength threshold, and the second beam signal strength threshold is a beam signal strength threshold carried in measurement configuration information.
[0200] Optionally, the processing module 12 is specifically configured to determine, based on the signal strength of the L beams in the N beams, the strength threshold information, the identification information of the N beams, and the random access channel configurations of the M beams, a beam whose signal strength is greater than or equal to the first beam signal strength threshold from the M beams as the beam for accessing the target cell.
[0201] Optionally, the processing module 12 is specifically configured to: when signal strength of each of the M beams is less than the first beam signal strength threshold, determine, from the M beams based on the identification information of the N beams and the random access channel configurations of the M beams, the beam for accessing the target cell.
[0202] Optionally, the processing module 12 is specifically configured to: when signal strength of each of the M beams is less than the first beam signal strength threshold, determine, based on the identifiers of the N beams, the signal strength of the L beams, and the strength threshold information, a beam whose signal strength is greater than or equal to the first beam signal strength threshold from the L beams as the beam for accessing the target cell.
[0203] Optionally, the processing module 12 is specifically configured to determine, based on the signal strength of the L beams, the strength threshold information, the identification information of the N beams, a priority order of the N beams, and the random access channel configurations of the M beams, the beam for accessing the target cell.
[0204] Optionally, the processing module 12 is specifically configured to: when none of the M beams is found, determine, based on the identification information of the N beams, a beam with highest signal strength in the L beams as the beam for accessing the target cell.
[0205] Optionally, the identification information of the N beams includes synchronization signal block identification information and/or channel state information-reference signal identification information.
[0206] The processing module 12 is specifically configured to determine the beam for accessing based on the signal strength of the L beams in the N beams, the strength threshold information, the identification information of the N beams, that a priority of a beam whose identification information is the channel state information-reference signal identification information is higher than that of a beam whose identification information is the synchronization signal block identification information, and the random access channel configurations of the M beams.
[0207] Optionally, the processing module 12 is further configured to: if none of the N beams is found, the signal strength of the L beams or signal strength of the M beams is less than the first beam signal strength threshold, or none of the M beams is found, determine the first found beam as the beam for accessing, determine a beam with highest signal strength as the beam for accessing, randomly determine a found beam as the beam for accessing, or determine a beam with a highest priority in found beams as the beam for accessing.
[0208] Optionally, the random access channel configuration includes a preamble index and a time-frequency resource configuration.
[0209] The communications apparatus described in this embodiment may be configured to execute the technical solutions executed by the terminal/the terminal chip in the foregoing method embodiments. An implementation principle and a technical effect of the communications apparatus are similar to those of the foregoing method embodiments. For functions of the modules, refer to corresponding descriptions in the method embodiments. Details are not described herein.
[0210] FIG. 6 is a schematic structural diagram of a terminal according to an embodiment of this application. As shown in FIG. 6, the terminal in this embodiment may include a processor 21 and a transceiver 22. The processor 21 is communicatively connected to the transceiver 22.
[0211] In hardware implementation, the receiving module 11 may be the transceiver 22 in this embodiment. Alternatively, the transceiver 22 includes a transmitter and a receiver; in this case, the receiving module 11 may be the receiver of the transceiver 22. The processing module 12 may be embedded in or independent of the processor 21 of the terminal in a form of hardware.
[0212] The transceiver 22 may include necessary radio frequency communications devices such as a frequency mixer. The processor 21 may include at least one of a central processing unit (CPU), a digital signal processor (DSP), a microcontroller unit (MCU), an application-specific integrated circuit (ASIC), or a field-programmable gate array (FPGA).
[0213] Optionally, the terminal in this embodiment may further include a memory 23. The memory 23 is configured to store a program instruction. The processor 21 is configured to invoke the program instruction in the memory 23 to execute the foregoing solutions.
[0214] The program instruction may be implemented in a form of a software functional unit and can be sold or used as an independent product. The memory 23 may be a computer readable storage medium in any form. Based on such understanding, all or some of the technical solutions of this application may be represented in a form of a software product, and the software product includes several instructions for instructing a computer device, which may be specifically the processor 21, to perform all or some of the steps of the terminal in the embodiments of this application. The computer readable storage medium includes various media that can store program code, such as a USB flash drive, a removable hard disk, a read-only memory (ROM), a random access memory (RAM), a magnetic disk, and a compact disc.
[0215] The terminal described in this embodiment may be configured to execute the technical solutions executed by the terminal or the chip inside the terminal in the foregoing method embodiments of this application. An implementation principle and a technical effect of the terminal are similar to those of the foregoing method embodiments. For functions of the modules, refer to corresponding descriptions in the method embodiments. Details are not described herein.
[0216] An embodiment of this application provides a communications apparatus. The communications apparatus may be a network device or a chip inside a network device. As shown in FIG. 7, the communications apparatus may include a receiving module 31 and a sending module 32.
[0217] The receiving module 31 is configured to receive identification information of N beams of a target cell and random access channel configurations of M beams in the N beams that are sent by a second network device, where N and M are positive integers.
[0218] The sending module 32 is configured to send the identification information of the N beams and the random access channel configurations of the M beams to a terminal.
[0219] Optionally, the receiving module 31 is further configured to receive serving beam change information of the terminal that is within a predetermined time period and that is sent by the terminal.
[0220] The sending module 32 is further configured to send the serving beam change information to the second network device, where the serving beam change information is used by the second network device to determine a validity period of the random access channel configurations of the M beams.
[0221] Optionally, the communications apparatus in this embodiment further includes a processing module 33.
[0222] The receiving module 31 is further configured to receive serving beam change information of the terminal that is within a predetermined time period and that is sent by the terminal.
[0223] The processing module 33 is configured to determine a validity period of the random access channel configurations of the M beams based on the serving beam change information.
[0224] The sending module 32 is further configured to send the validity period of the random access channel configurations of the M beams to the second network device.
[0225] Optionally, the random access channel configuration includes a preamble index and a time-frequency resource configuration.
[0226] Optionally, the sending module 32 is further configured to send strength threshold information or quality threshold information of a beam signal to the terminal through a handover message.
[0227] The communications apparatus described in this embodiment may be configured to execute the technical solutions executed by the source base station or a chip inside the source base station in the foregoing method embodiments. An implementation principle and a technical effect of the communications apparatus are similar to those of the foregoing method embodiments. For functions of the modules, refer to corresponding descriptions in the method embodiments. Details are not described herein.
[0228] FIG. 8 is a schematic structural diagram of a network device according to an embodiment of this application. As shown in FIG. 8, the network device in this embodiment may include a processor 41 and a transceiver 42. The processor 41 is communicatively connected to the transceiver 42.
[0229] In hardware implementation, the receiving module 31 and the sending module 32 may be the transceiver 42 in this embodiment. Alternatively, the transceiver 42 includes a transmitter and a receiver; in this case, the receiving module 31 may be the receiver of the transceiver 42, and the sending module 32 may be the transmitter of the transceiver 42. The processing module 33 may be embedded in or independent of the processor 41 of the network device in a form of hardware.
[0230] The transceiver 42 may include necessary radio frequency communications devices such as a frequency mixer. The processor 41 may include at least one of a CPU, a DSP, an MCU, an ASIC, or an FPGA.
[0231] Optionally, the network device in this embodiment may further include a memory 43. The memory 43 is configured to store a program instruction. The processor 41 is configured to invoke the program instruction in the memory 43 to execute the foregoing solutions.
[0232] The program instruction may be implemented in a form of a software functional unit and can be sold or used as an independent product. The memory 43 may be a computer readable storage medium in any form. Based on such understanding, all or some of the technical solutions of this application may be represented in a form of a software product, and the software product includes several instructions for instructing a computer device, which may be specifically the processor 41, to perform all or some of the steps of the network device in the embodiments of this application. The computer readable storage medium includes various media that can store program code, such as a USB flash drive, a removable hard disk, a ROM, a RAM, a magnetic disk, and a compact disc.
[0233] The network device in this embodiment may be configured to execute the technical solutions of the source base station in the foregoing method embodiments of this application. An implementation principle and a technical solution of the network device are similar to those of the foregoing method embodiments, and details are not described herein.
[0234] An embodiment of this application provides a communications apparatus. The communications apparatus may be a network device or a chip inside a network device. As shown in FIG. 9, the communications apparatus may include a sending module 51.
[0235] The sending module 51 is configured to send identification information of N beams of a target cell and random access channel configurations of M beams in the N beams to a first network device, where N and M are positive integers.
[0236] Optionally, the communications apparatus further includes a receiving module 52 and a processing module 53.
[0237] In a feasible implementation, the receiving module 52 is configured to receive serving beam change information of a terminal that is within a predetermined time period and that is sent by the first network device.
[0238] The processing module 53 is configured to: determine a validity period of the random access channel configurations of the M beams based on the serving beam change information; and after the validity period expires, release the random access channel configurations of the M beams.
[0239] In a feasible implementation, the receiving module 52 is configured to receive the validity period of the random access channel configurations of the M beams that is sent by the first network device.
[0240] The processing module 53 is configured to: after the validity period expires, release the random access channel configurations of the M beams.
[0241] Optionally, the sending module 51 is further configured to send strength threshold information or quality threshold information of a beam signal to the terminal through system information.
[0242] The communications apparatus described in this embodiment may be configured to execute the technical solutions executed by the target base station or a chip inside the target base station in the foregoing method embodiments. An implementation principle and a technical effect of the communications apparatus are similar to those of the foregoing method embodiments. For functions of the modules, refer to corresponding descriptions in the method embodiments. Details are not described herein.
[0243] FIG. 1o is a schematic structural diagram of a network device according to an embodiment of this application. As shown in FIG. 10, the network device in this embodiment may include a processor 61 and a transceiver 62. The processor 61 is communicatively connected to the transceiver 62.
[0244] In hardware implementation, the receiving module 52 and the sending module 51 may be the transceiver 62 in this embodiment. Alternatively, the transceiver 62 includes a transmitter and a receiver; in this case, the receiving module 52 may be the receiver of the transceiver 62, and the sending module 51 may be the transmitter of the transceiver 62. The processing module 53 may be embedded in or independent of the processor 61 of the network device in a form of hardware.
[0245] The transceiver 62 may include necessary radio frequency communications devices such as a frequency mixer. The processor 61 may include at least one of a CPU, a DSP, an MCU, an ASIC, or an FPGA.
[0246] Optionally, the network device in this embodiment may further include a memory 63. The memory 63 is configured to store a program instruction. The processor 61 is configured to invoke the program instruction in the memory 63 to execute the foregoing solutions.
[0247] The program instruction may be implemented in a form of a software functional unit and can be sold or used as an independent product. The memory 63 may be a computer readable storage medium in any form. Based on such understanding, all or some of the technical solutions of this application may be represented in a form of a software product, and the software product includes several instructions for instructing a computer device, which may be specifically the processor 61, to perform all or some of the steps of the network device in the embodiments of this application. The computer readable storage medium includes various media that can store program code, such as a USB flash drive, a removable hard disk, a ROM, a RAM, a magnetic disk, and a compact disc.
[0248] The network device in this embodiment may be configured to execute the technical solutions of the target base station in the foregoing method embodiments of this application. An implementation principle and a technical solution of the network device are similar to those of the foregoing method embodiments, and details are not described herein.
[0249] It should be noted that module division in the embodiments of this application is an example and is merely logical function division. During actual implementation, there may be another division manner. Functional modules in the embodiments of this application may be integrated into one processing module, or each of the modules may exist alone physically, or two or more modules are integrated into one module. The integrated module may be implemented in a form of hardware, or may be implemented in a form of a software functional module.
[0250] When the integrated module is implemented in a form of a software functional module and sold or used as an independent product, the integrated module may be stored in a computer readable storage medium. Based on such an understanding, the technical solutions of this application essentially, or the part contributing to the prior art, or all or some of the technical solutions may be implemented in a form of a software product. The computer software product is stored in a storage medium and includes several instructions for instructing a computer device (which may be a personal computer, a server, a network device, or the like) or a processor to perform all or some of the steps of the methods described in the embodiments of this application. The storage medium includes various media that can store program code, such as a USB flash drive, a removable hard disk, a read-only memory (ROM), a random access memory (RAM), a magnetic disk, and a compact disc.
[0251] All or some of the foregoing embodiments may be implemented by using software, hardware, firmware, or any combination thereof. When software is used to implement the embodiments, all or some of the embodiments may be implemented in a form of a computer program product. The computer program product includes one or more computer instructions. When the computer program instructions are loaded and executed on a computer, all or some of the procedures or functions according to the embodiments of this application are generated. The computer may be a general-purpose computer, a special-purpose computer, a computer network, or another programmable apparatus. The computer instructions may be stored in a computer readable storage medium or may be transmitted from one computer readable storage medium to another computer readable storage medium. For example, the computer instructions may be transmitted from a website, computer, server, or data center to another website, computer, server, or data center in a wired (for example, a coaxial cable, an optical fiber, or a digital subscriber line (DSL)) or wireless (for example, infrared, radio, or microwave) manner. The computer readable storage medium may be any usable medium accessible by a computer, or a data storage device, such as a server or a data center, integrating one or more usable media. The usable medium may be a magnetic medium (for example, a floppy disk, a hard disk, or a magnetic tape), an optical medium (for example, a DVD), a semiconductor medium (for example, a solid state disk (SSD)), or the like.
* * * * *
D00000
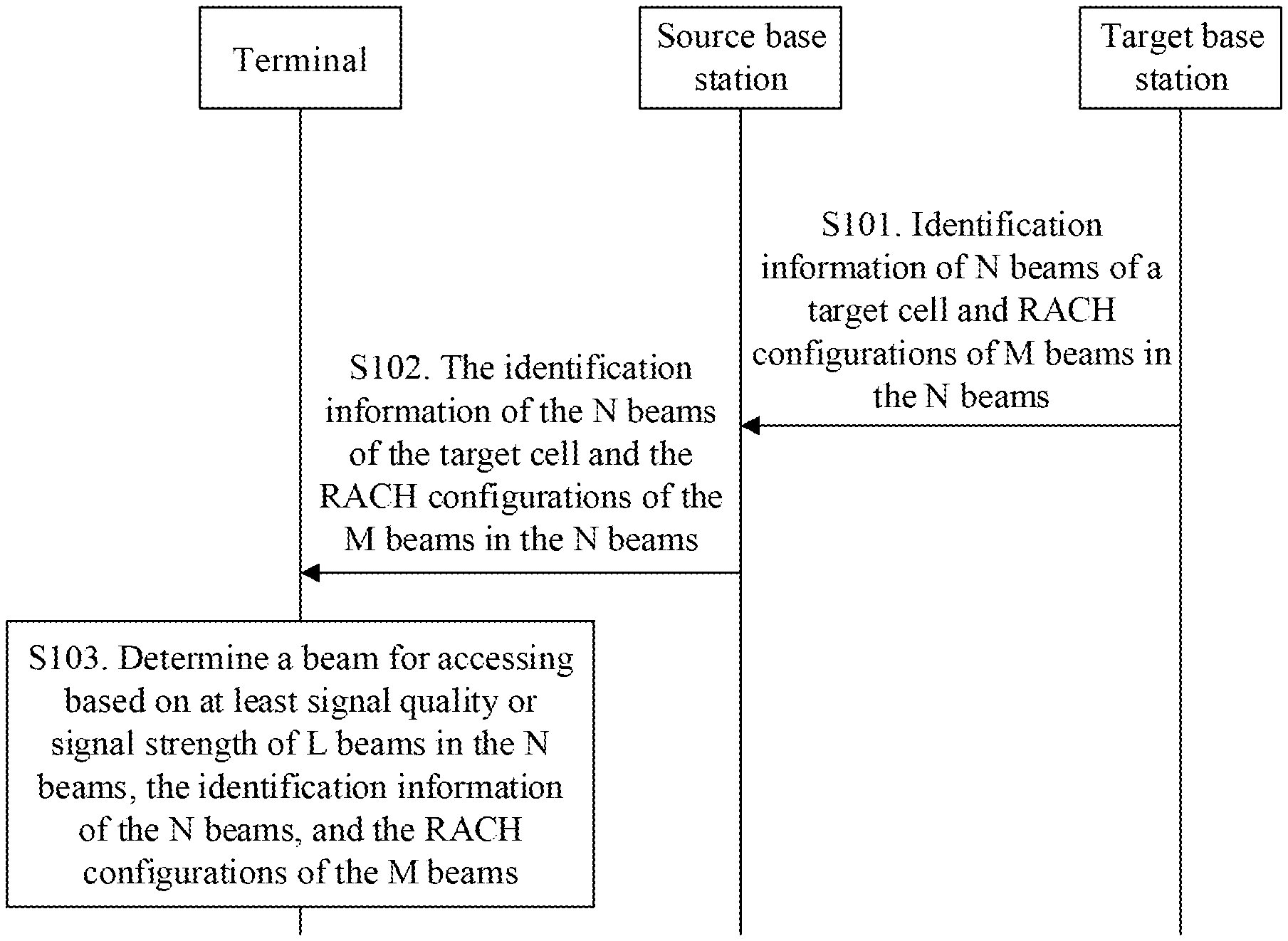
D00001
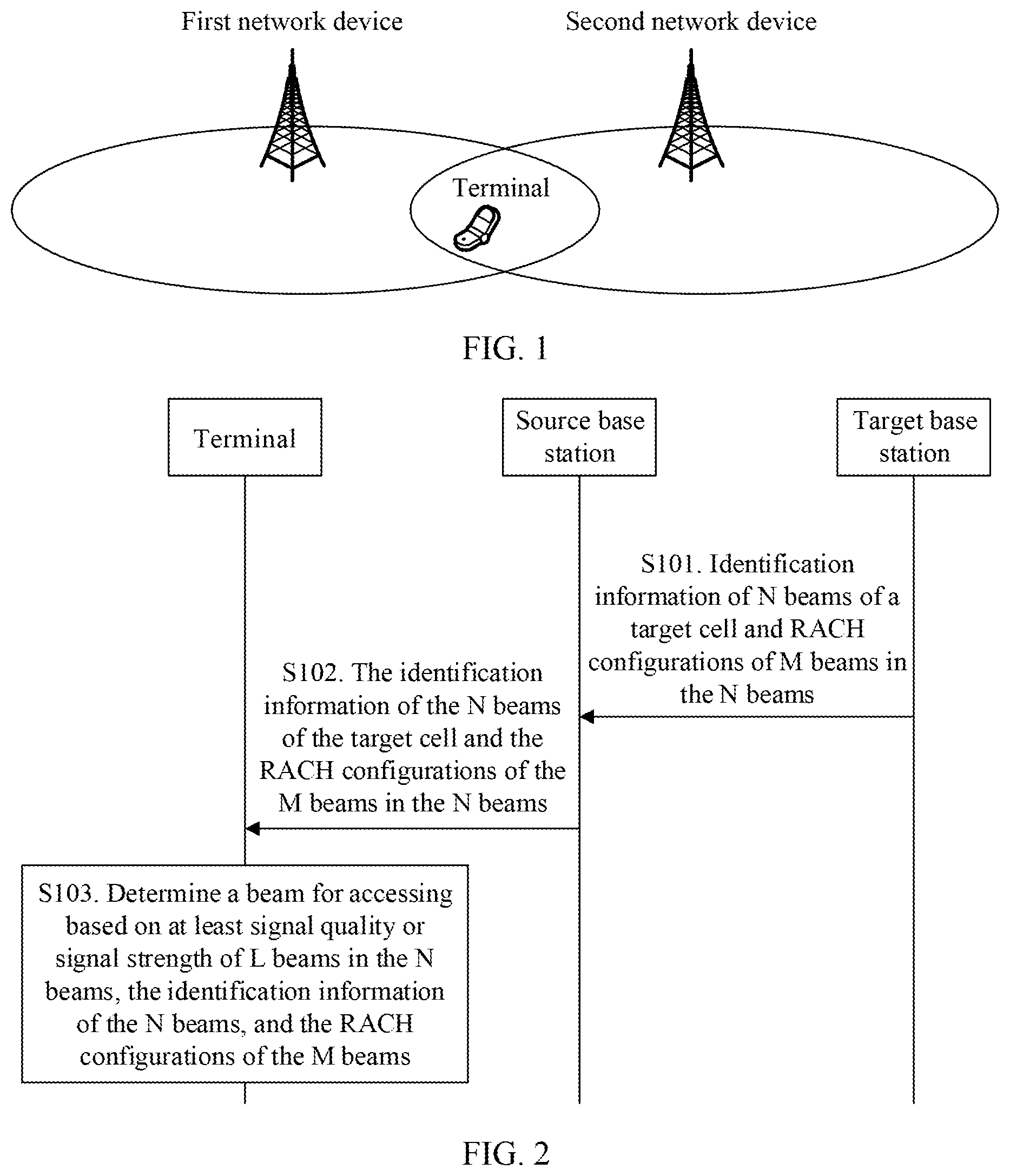
D00002
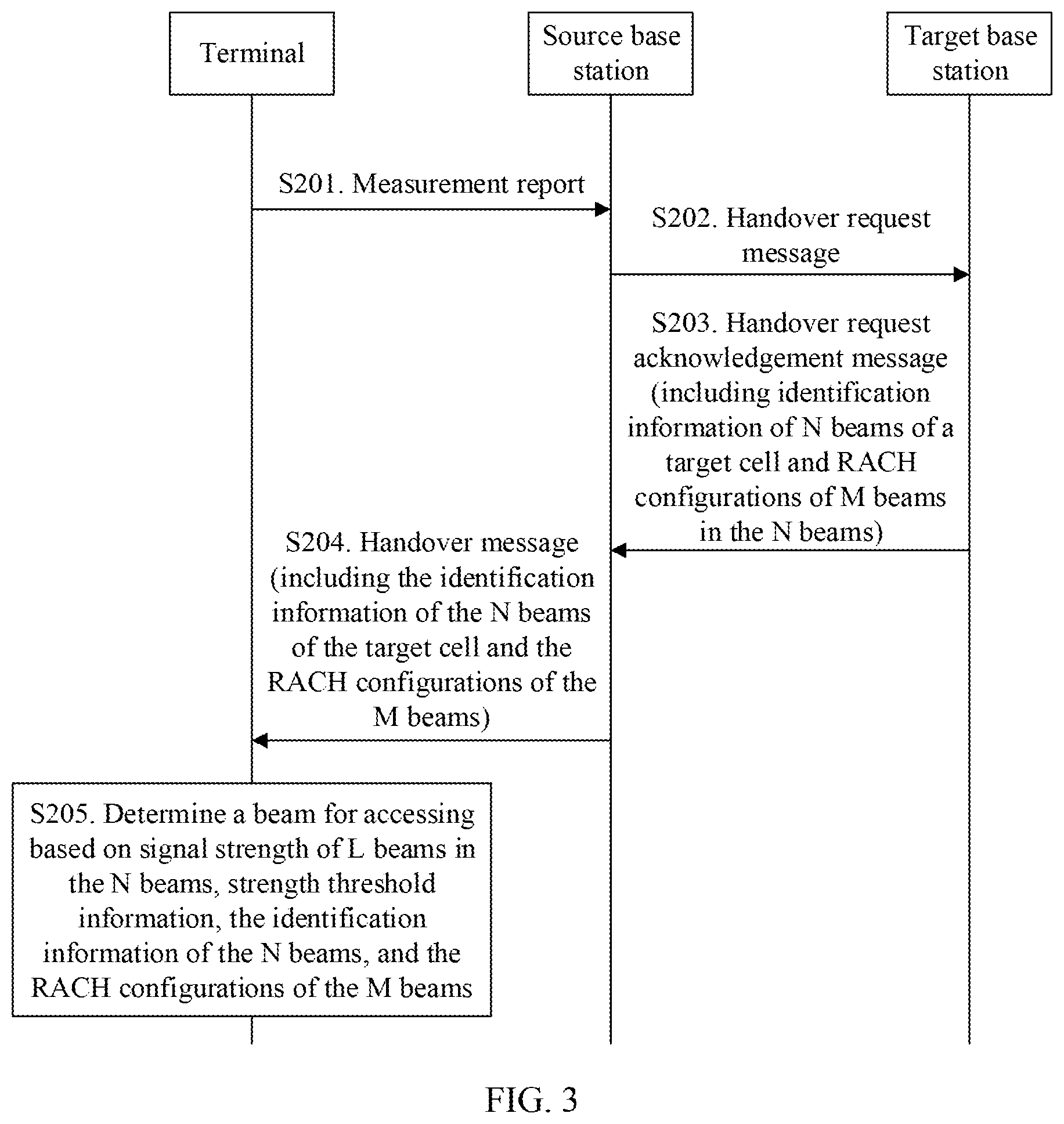
D00003
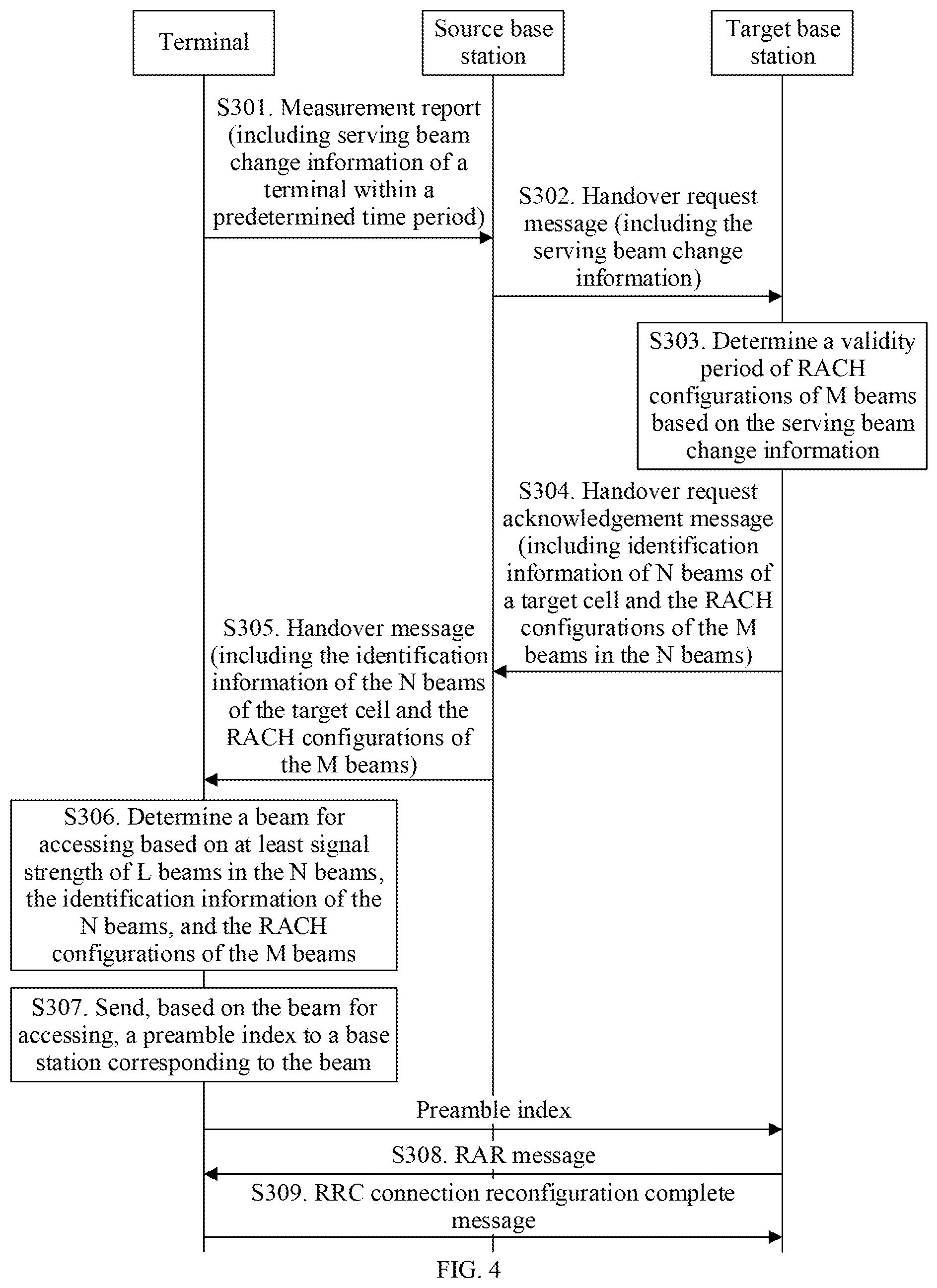
D00004
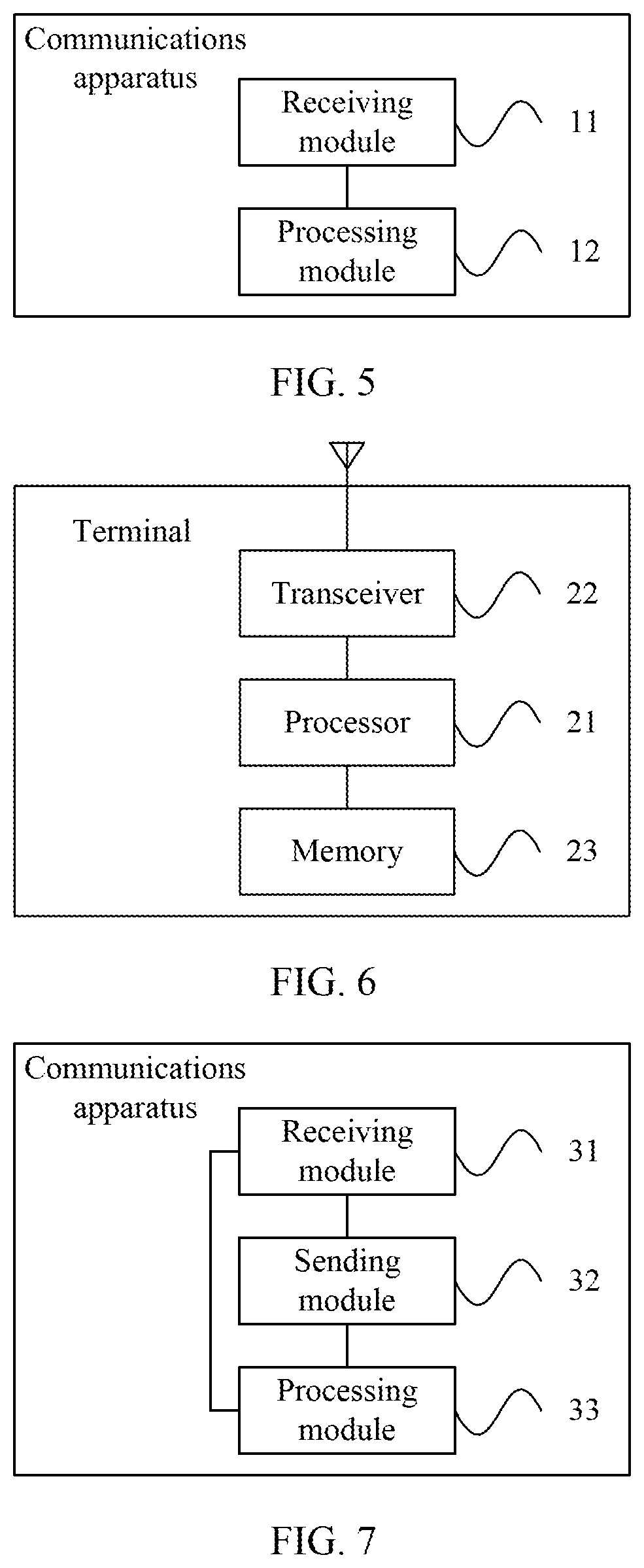
D00005
D00006
XML
uspto.report is an independent third-party trademark research tool that is not affiliated, endorsed, or sponsored by the United States Patent and Trademark Office (USPTO) or any other governmental organization. The information provided by uspto.report is based on publicly available data at the time of writing and is intended for informational purposes only.
While we strive to provide accurate and up-to-date information, we do not guarantee the accuracy, completeness, reliability, or suitability of the information displayed on this site. The use of this site is at your own risk. Any reliance you place on such information is therefore strictly at your own risk.
All official trademark data, including owner information, should be verified by visiting the official USPTO website at www.uspto.gov. This site is not intended to replace professional legal advice and should not be used as a substitute for consulting with a legal professional who is knowledgeable about trademark law.