Automated analysis of RF spectrum
LAPIERRE; Dominic ; et al.
U.S. patent application number 16/739812 was filed with the patent office on 2020-07-16 for automated analysis of rf spectrum. The applicant listed for this patent is EXFO Inc.. Invention is credited to Luc GERMAIN, Dominic LAPIERRE, Robert MATESEVAC.
| Application Number | 20200228210 16/739812 |
| Document ID | 20200228210 / US20200228210 |
| Family ID | 71517863 |
| Filed Date | 2020-07-16 |
| Patent Application | download [pdf] |








View All Diagrams
| United States Patent Application | 20200228210 |
| Kind Code | A1 |
| LAPIERRE; Dominic ; et al. | July 16, 2020 |
Automated analysis of RF spectrum
Abstract
Systems and methods e to automatically analyze and display results of tests of a link include obtaining data from one or more tests of a link, wherein the data includes samples for Antenna Carriers (AxC) for one or more AxCs auto-detected on the link; processing the data to detect peaks on any of the auto-detected AxCs on the link; performing an analysis of any detected peaks to identify any issues on the link; and causing display of a user interface that includes a reporting of any identified issues with the user interface including a display of the identified issues and a spectrum graph.
| Inventors: | LAPIERRE; Dominic; (Rigaud, CA) ; GERMAIN; Luc; (Candiac, CA) ; MATESEVAC; Robert; (Wake Forest, NC) | ||||||||||
| Applicant: |
|
||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|
| Family ID: | 71517863 | ||||||||||
| Appl. No.: | 16/739812 | ||||||||||
| Filed: | January 10, 2020 |
Related U.S. Patent Documents
| Application Number | Filing Date | Patent Number | ||
|---|---|---|---|---|
| 62861544 | Jun 14, 2019 | |||
| 62791202 | Jan 11, 2019 | |||
| 62819731 | Mar 18, 2019 | |||
| Current U.S. Class: | 1/1 |
| Current CPC Class: | H04W 24/02 20130101; H04B 17/30 20150115; H04B 15/04 20130101; H04L 43/50 20130101; G01R 23/16 20130101 |
| International Class: | H04B 15/04 20060101 H04B015/04; H04B 17/30 20150101 H04B017/30; G01R 23/16 20060101 G01R023/16; H04W 24/02 20090101 H04W024/02; H04L 12/26 20060101 H04L012/26 |
Claims
1. A non-transitory computer-readable storage medium having computer readable code stored thereon for programming a test system to perform the steps of: obtaining data from one or more tests of a link, wherein the data includes samples for Antenna Carriers (AxC) for one or more AxCs auto-detected on the link; processing the data to detect peaks on any of the auto-detected AxCs on the link; performing an analysis of any detected peaks to identify any issues on the link; and causing display of a user interface that includes a reporting of any identified issues with the user interface including a display of the identified issues and a spectrum graph.
2. The non-transitory computer-readable storage medium of claim 1, wherein the auto-detected AxCs are detected by the test system each time the link transitions from link down to link up, and wherein the auto-detected AxCs are maintained in an AxC list.
3. The non-transitory computer-readable storage medium of claim 1, wherein the computer readable code stored thereon further programs the test system to perform the steps of: automatically configuring Resolution Bandwidth (RBW) and Video Bandwidth (VBW) on the spectrum graph.
4. The non-transitory computer-readable storage medium of claim 1, wherein the display includes zero or more messages with a description of each associated issue and with the zero or more messages in an automatically prioritized order.
5. The non-transitory computer-readable storage medium of claim 1, wherein the spectrum graph includes a full graph and a zoomed-in graph, each having tokens to visually identify peaks in each.
6. The non-transitory computer-readable storage medium of claim 1, wherein the display includes at least one message with a description of a known interferer detected in the analysis, and wherein the known interferer is determined based on matching signatures in a database.
7. The non-transitory computer-readable storage medium of claim 1, wherein the issues include any of known interferers, internal Passive Intermodulation (PIM), external PIM, and identical interferers across all of the auto-detected AxCs.
8. The non-transitory computer-readable storage medium of claim 1, wherein the issues include known interferers detected by the steps of: detecting a presence of at least one interferer at a known frequency on at least one AxC of the link; and tagging this interferer at the known frequency as being potentially caused by a known device based on matching a signature.
9. The non-transitory computer-readable storage medium of claim 1, wherein the issues include internal Passive Intermodulation (PIM) detected by the steps of: detecting a presence of a PIM in an AxC of the auto-detected AxCs of a same tower of the link; determining a level of interference of the PIM; and if the level of interference of the PIM is greater than a PIM detection threshold and if not all of the AxCs have a PIM, determining that the internal PIM is present on corresponding AxCs.
10. The non-transitory computer-readable storage medium of claim 1, wherein the issues include external Passive Intermodulation (PIM) detected by the steps of: detecting a presence of a PIM in each AxC of the auto-detected AxCs of a same tower of the link; determining a level of interference of each PIM; and if the level of interference of each PIM is greater than a PIM detection threshold, determining that an external PIM is present.
11. The non-transitory computer-readable storage medium of claim 1, wherein the issues include identical interferes across all of the auto-detected AxCs detected by the steps of: detecting a presence of at least one interferer for at least one AxC of the auto-detected AxCs of a same tower of the link; determining a frequency of each interferer; comparing the list of interferers of each AxC with that of the other AxCs; if more than one AxC has an interferer at the same frequency, identifying that the interferers are the same; and tagging the interferer with the list of AxCs on which it appears and the frequency.
12. A test system comprising: a detector configured to connect to a link; a processor; and memory storing instructions that, when executed, cause the processor to obtain data from one or more tests of the link, wherein the data includes samples for Antenna Carriers (AxC) for one or more AxCs auto-detected on the link; process the data to detect peaks on any of the auto-detected AxCs on the link; perform an analysis of any detected peaks to identify any issues on the link; and cause display of a user interface that includes a reporting of any identified issues with the user interface including a display of the identified issues and a spectrum graph.
13. The test system of claim 12, wherein the auto-detected AxCs are detected by the test system each time the link transitions from link down to link up, and wherein the auto-detected AxCs are maintained in an AxC list.
14. The test system of claim 12, wherein the memory storing instructions that, when executed, further cause the processor to automatically configure Resolution Bandwidth (RBW) and Video Bandwidth (VBW) on the spectrum graph.
15. The test system of claim 12, wherein the display includes zero or more messages with a description of each associated issue and with the zero or more messages in an automatically prioritized order.
16. The test system of claim 12, wherein the spectrum graph includes a full graph and a zoomed-in graph, each having tokens to visually identify peaks in each.
17. The test system of claim 12, wherein the display includes at least one message with a description of a known interferer detected in the analysis, and wherein the known interferer is determined based on matching signatures in a database.
18. The test system of claim 12, wherein the issues include any of known interferers, internal Passive Intermodulation (PIM), external PIM, and identical interferers across all of the auto-detected AxCs.
19. A method comprising: obtaining, via a test system, data from one or more tests of a link, wherein the data includes samples for Antenna Carriers (AxC) for one or more AxCs auto-detected on the link; processing the data to detect peaks on any of the auto-detected AxCs on the link; performing an analysis of any detected peaks to identify any issues on the link; and causing display of a user interface that includes a reporting of any identified issues with the user interface including a display of the identified issues and a spectrum graph.
20. The method of claim 19, wherein the auto-detected AxCs are detected by the test system each time the link transitions from link down to link up, and wherein the auto-detected AxCs are maintained in an AxC list.
Description
CROSS-REFERENCE TO RELATED APPLICATION(S)
[0001] The present disclosure claims priority to U.S. Provisional Patent Application No. 62/861,544, filed Jun. 14, 2019, U.S. Provisional Patent Application No. 62/791,202, filed Jan. 11, 2019, and U.S. Provisional Patent Application No. 62/819,731, filed Mar. 18, 2019, the contents of each are incorporated by reference herein.
FIELD OF THE DISCLOSURE
[0002] The present disclosure generally relates to network testing. More particularly, the present disclosure relates to systems and methods for automated analysis of Radio Frequency (RF) spectrum.
BACKGROUND OF THE DISCLOSURE
[0003] Mobile network operators (MNOs) can locate RF interference issues in fiber-based mobile networks using real-time, high-resolution RF spectrum analysis over CPRI (Common Public Radio Interface), evolved eCPRI, etc. CPRI, eCPRI, etc. are standards that defines an interface between Radio Equipment Controllers (REC) and Radio Equipment (RE). CPRI and eCPRI allows replacement of copper or coaxial cables between a radio transceiver and a base station, such as via fiber. For example, EXFO's OpticalRF.TM. application provides access to the RF signal through the digital CPRI link available at the base station, located at the bottom of the cell tower or kilometers away as in a Centralized Radio Access Network (C-RAN) architecture. Technicians can quickly and accurately identify critical interference issues such as external RF interference, and internal and external Passive Intermodulation (PIM).
[0004] The detection of interferers in RF spectrum is a common task carried out by technicians in the field. Interference appears in spectrum as persisting peaks. The more powerful ones show up on an RF spectrum in just about any conditions. Other peaks are subtle and require careful tuning of the RF spectrum analysis equipment. An experienced technician will be able to adjust the Resolution Bandwidth (RBW), the Video Bandwidth (VBW), as well as other parameters to emphasize the particular interference being hunted for. The OpticalRF.TM. (ORF) application provides technicians with the speed, granularity, and clarity to identify what issues are present. ORF is a digital spectrum analyzer that extracts its information from a CPRI link instead of an analog coaxial cable. It can be used by mobile operators to measure/troubleshoot cell towers. ORF has various controls available in a spectrum analyzer: RBW, VBW, Center Frequency, Span, etc. To operate such an instrument, the user must be well trained and experimented, such as an RF expert. Mobile operators have a shortage of qualified personnel to operate such instruments.
[0005] Conventional analysis approaches can integrate some version of automated measurement, but this always revolves around the manipulation and visualization of a spectrum trace. Some automatically put markers on the trace with numbers on it, others put the measurements in a table next to the trace and so on. All this information centers around a spectrum trace, and this is overwhelming to a non-expert technician. As more and more antennas are installed, there is a shortage of skilled and experienced technicians able to analyze RF spectrum to find interference and other states of the antenna. There is, therefore, a need to automate the analysis of the RF spectrum to facilitate the work, i.e., turning up and troubleshooting a cell tower, of the technician who is not an RF expert.
BRIEF SUMMARY OF THE DISCLOSURE
[0006] In an embodiment, a non-transitory computer-readable storage medium has computer readable code stored thereon for programming a test system to perform the steps of obtaining data from one or more tests of a link, wherein the data includes samples for Antenna Carriers (AxC) for one or more AxCs auto-detected on the link; processing the data to detect peaks on any of the auto-detected AxCs on the link; performing an analysis of any detected peaks to identify any issues on the link; and causing display of a user interface that includes a reporting of any identified issues with the user interface including a display of the identified issues and a spectrum graph. As described herein, the link can be a CPRI, eCPRI, Over-the-Air (OTA) capture, etc.
[0007] In another embodiment, a test system includes a detector configured to connect to a Common Public Radio Interface (CPRI) link; a processor; and memory storing instructions that, when executed, cause the processor to obtain data from one or more tests of the link, wherein the data includes samples for Antenna Carriers (AxC) for one or more AxCs auto-detected on the link; process the data to detect peaks on any of the auto-detected AxCs on the link; perform an analysis of any detected peaks to identify any issues on the link; and cause display of a user interface that includes a reporting of any identified issues with the user interface including a display of the identified issues and a spectrum graph.
[0008] In a further embodiment, a method includes obtaining data from one or more tests of a Common Public Radio Interface (CPRI) link, wherein the data includes samples for Antenna Carriers (AxC) for one or more AxCs auto-detected on the link; processing the data to detect peaks on any of the auto-detected AxCs on the link; performing an analysis of any detected peaks to identify any issues on the link; and causing display of a user interface that includes a reporting of any identified issues with the user interface including a display of the identified issues and a spectrum graph.
BRIEF DESCRIPTION OF THE DRAWINGS
[0009] The present disclosure is illustrated and described herein with reference to the various drawings, in which like reference numbers are used to denote like system components/method steps, as appropriate, and in which:
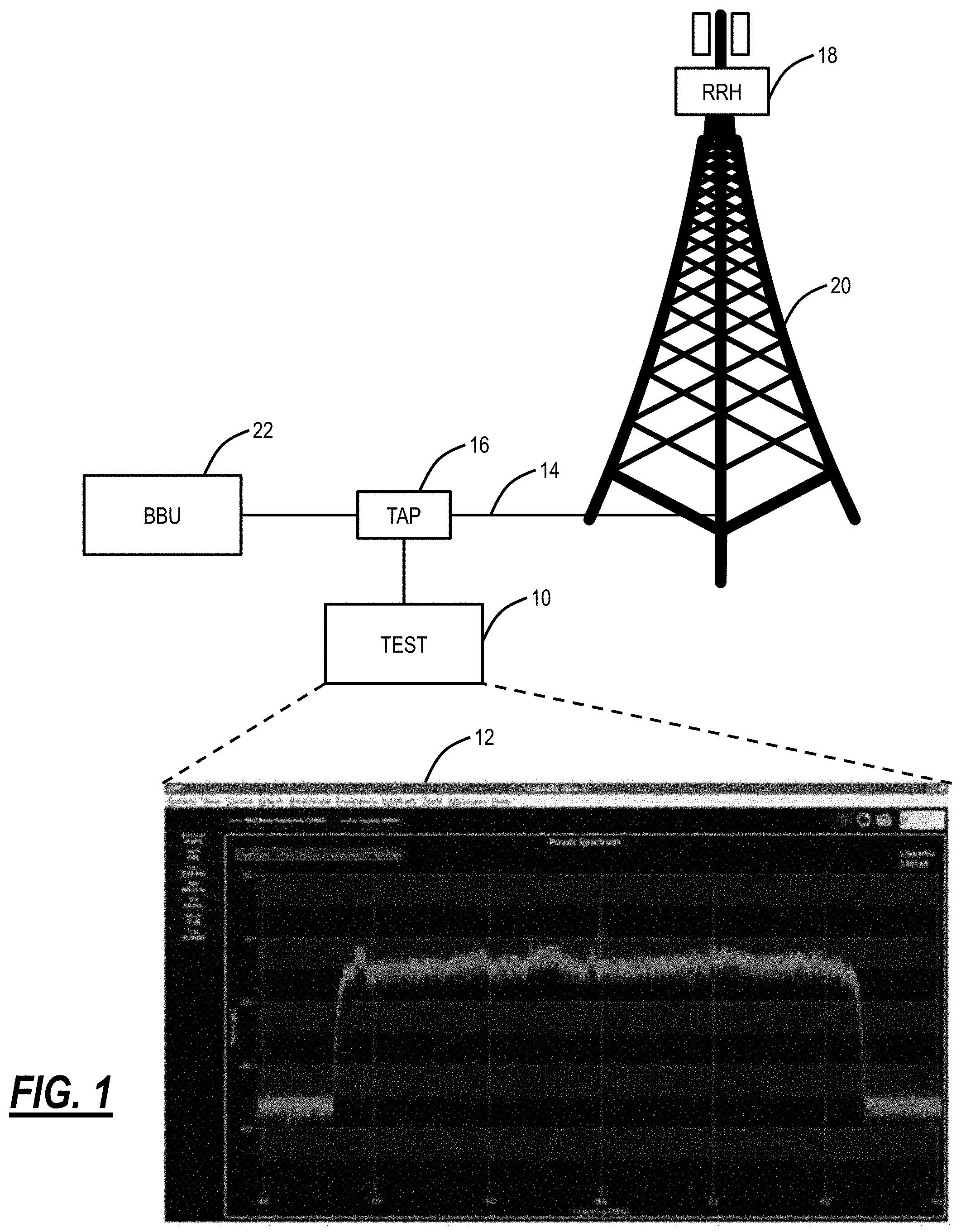
[0010] FIG. 1 is a block diagram of a test system with an associated User Interface (UI);
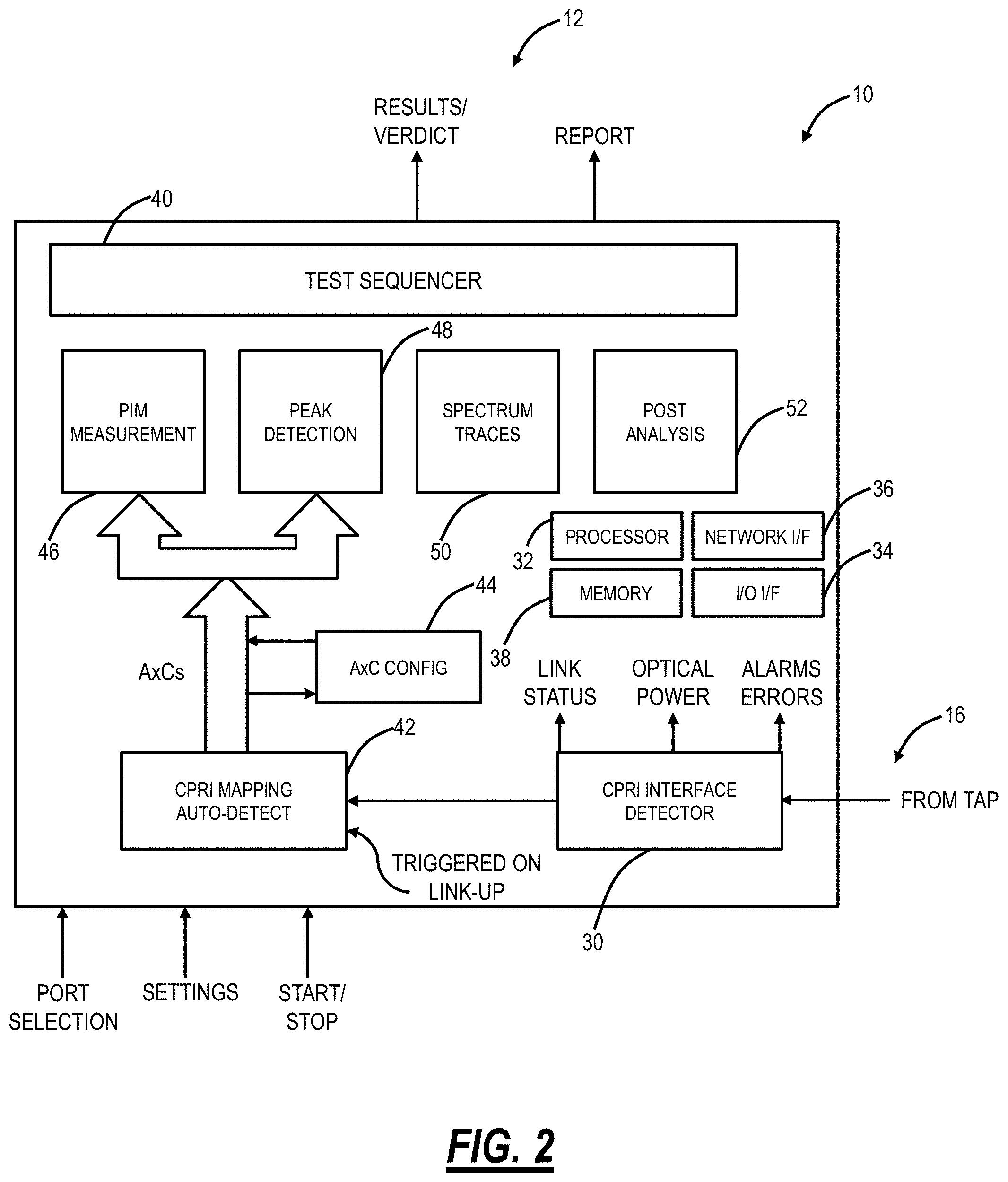
[0011] FIG. 2 is a functional block diagram of the test system;
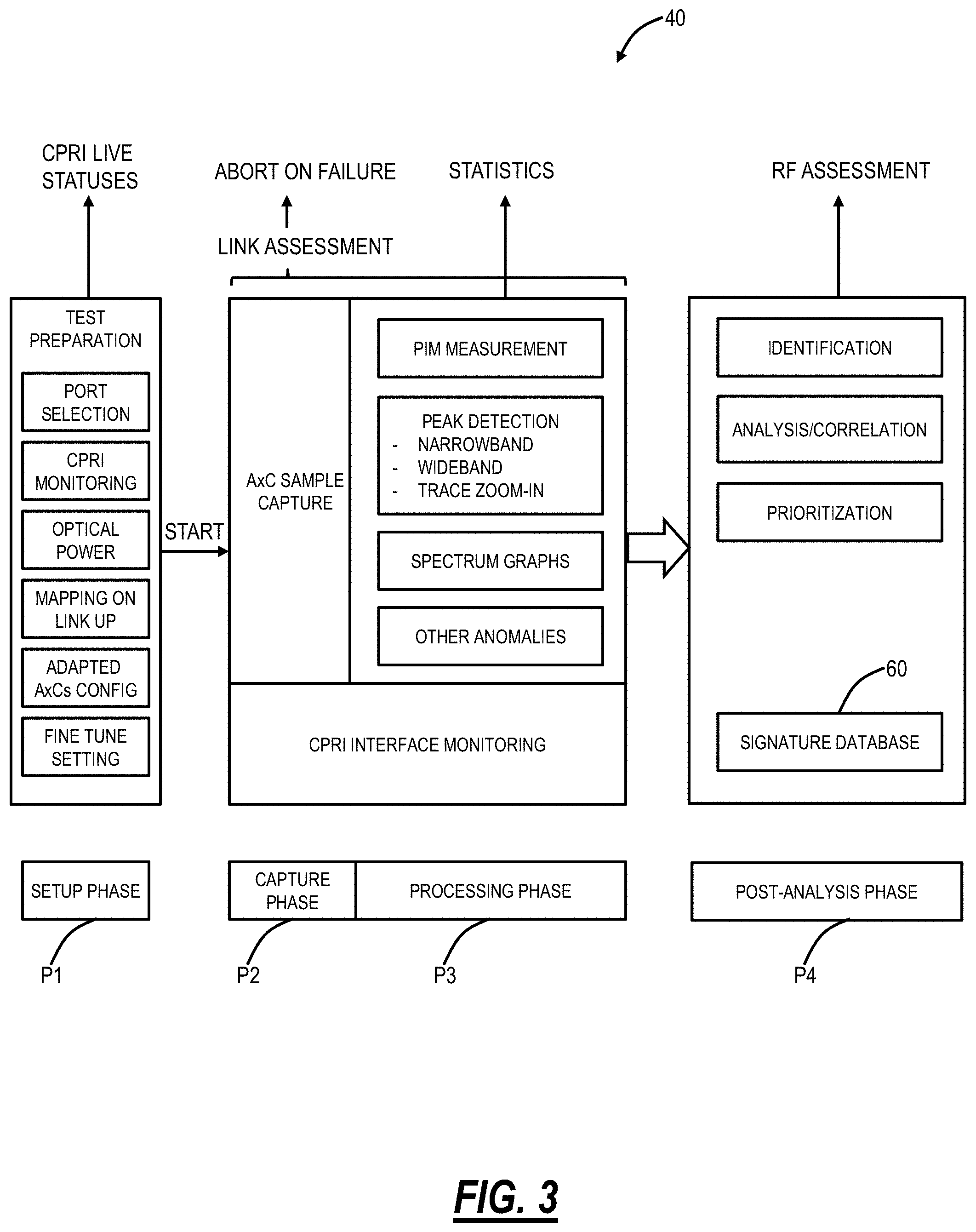
[0012] FIG. 3 is a block diagram of phases implemented by the test sequencer of the test system;
[0013] FIG. 4 is a diagram of a Graphical User Interface (GUI) for the test system at setup;
[0014] FIG. 5 is a diagram of a GUI for results through the test system;
[0015] FIG. 6 is a screenshot of an example results GUI in which a test has already been performed;
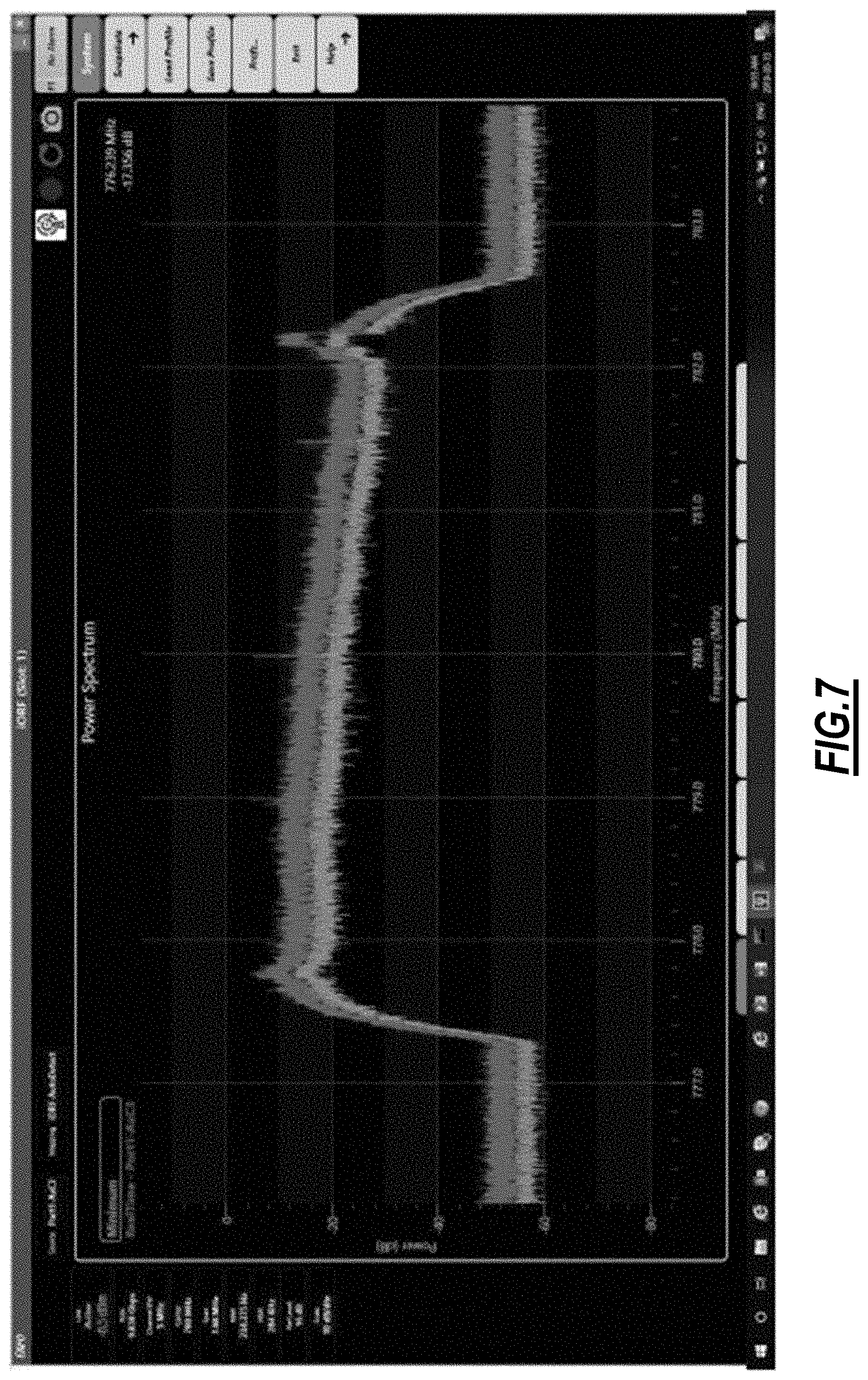
[0016] FIG. 7 is a screenshot of an example corresponding live view which has been triggered from the results window of FIG. 6;
[0017] FIGS. 8A-8J are diagrams of an example report based on the results in FIG. 6;
[0018] FIG. 9 is a flowchart of an external PIM detection process;
[0019] FIG. 10 is a flowchart of an internal PIM detection process;
[0020] FIG. 11 is a flowchart of an identical interferer detection process;
[0021] FIG. 12 is a flowchart of a known interferer detection process;
[0022] FIG. 13 is a screenshot of an example RF spectrum analysis tool in a state with no errors currently detected;
[0023] FIG. 14 is a screenshot of the example RF spectrum analysis tool in a state with a detected internal PIM and identical interferers detected on a plurality of antennas of the same tower;
[0024] FIG. 15 is a screenshot of the example RF spectrum analysis tool in a state with a detected external PIM;
[0025] FIGS. 16A-16C are screenshots of the example RF spectrum analysis tool in a state with a detected internal PIM and a potential Wi-Fi interferer in the summary mode for AxC 1;
[0026] FIG. 17 is a screenshot of the example RF spectrum analysis tool in a state with a detected internal PIM on AxC 4, the RF spectrum of AxC 4 being shown in the spectrum section and for which peak 2 of AxC 4 is displayed in the peak detail;
[0027] FIG. 18 is a screenshot of the example RF spectrum analysis tool with a results page;
[0028] FIG. 19 is a screenshot of the example RF spectrum analysis tool and a setup page where specific AxCs are enabled/disabled in a post-analysis process; and
[0029] FIG. 20 is a flowchart of a process implemented by the test system or the like to automatically analyze and display results of tests of the link.
DETAILED DESCRIPTION OF THE DISCLOSURE
[0030] The present disclosure relates to systems and methods for automated analysis of Radio Frequency (RF) spectrum. Specifically, the systems and methods include the automatic configuration and detection of issues on a single trace or correlated traces of a CPRI, an eCPRT, etc. link with contextual reporting to a user. The present disclosure relates to analysis of links between Radio Equipment Controllers (REC) and Radio Equipment (RE). Those skilled in the art recognize examples of such interfaces are CPRI, eCPRT, Over-the-Air (OTA) capture, etc. and the present disclosure contemplates any such links. That is, the present disclosure contemplates operation to monitor CPRI, eCPRT, variants of CPRI and eCPRT, OTA capture, and the like, and the term link used herein is meant to cover all such embodiments. The objective is automated analysis and reporting enabling non-expert user interaction of such links. The systems and methods include minimal or no configuration by the user. Every other parameter such as RBW, VBW is automatically tuned for the measurement in progress, and other parameters such as Peak Sensitivity and PIM threshold are presented with default values. The systems and methods perform automatic measurement of key parameters, detect the presence of interferers, identify interferers, and present those results is an easily understandable format, such as a tabular and text form. The trace is presented but as a secondary element, not the main. The solution is also able to make correlations between traces. The measurement/detection being automated, it is easy once the results of each antenna are known to cycle through them all and find common interferers. This task is time-consuming and prone to error when the user tries to do it using multiple overlays of antenna traces. A qualitative assessment is provided, avoiding the user to make a manual assessment.
[0031] In an embodiment, the systems and methods include an RF spectrum analysis tool (i.e., "test system") that is configured to automatically analyze an/the RF spectrum, such as on a link. The RF spectrum analysis tool includes various diagnostic processes including a known interferer detection process, an identical interferer detection process, an external PIM detection process, and an internal PIM detection process, each of which can be performed individually or combined. The RF spectrum analysis tool can include a User Interface (UI) for technician troubleshooting.
[0032] The external PIM detection process can include the steps of detecting the presence of PIM in each antenna of a plurality of antennas of the same tower of a link, determining a level of interference of each PIM; and if the level of interference of each PIM is greater than a PIM detection threshold, determining that an external PIM is present. For example, the PIM detection threshold can be 6 dB as well as other values that are adjustable.
[0033] The internal PIM detection process can include the steps of detecting the presence of a PIM in an antenna of a plurality of antennas of the same tower of a link, determining a level of interference of the PIM; and if the level of interference of the PIM is greater than a PIM detection threshold and if not all antennas of the plurality of antennas have a PIM, determining that an internal PIM is present on that specific antenna.
[0034] The identical interferer detection process can include the steps of detecting the presence of at least one interferer for at least one antenna of a plurality of antennas of a link; determining a frequency of each interferer; comparing the list of interferers of each antenna with that of the other antennas; if more than one antenna has an interferer at the same frequency, identifying that the interferers are the same; and tagging the interferer with the list of antennas on which it appears and the frequency. The known interferer detection process can include the steps of detecting the presence of at least one interferer at a known frequency on at least one antenna of the link; and tagging this interferer at the known frequency as being potentially caused by a known device.
Test System
[0035] FIG. 1 is a block diagram of a test system 10 with an associated User Interface (UI) 12. The test system 10 is connected to a link 14 via a tap 16. For example, the link 14 can be a fiber connection between a Remote Radio Head (RRH) 18 on a cell tower 20 and a Baseband Unit (BBU) 22. For example, the link 14 can be a CPRI, eCPRI, or a variant thereof. In another embodiment, the link 14 can be an Over-the-Air (OTA) capture of RF spectrum between the BBU 22 and the RRH 18. For the OTA capture, the RF signal can be received by an antenna and processed (e.g., low-noise amplifying, band filtering, etc.). The resulting signal is sampled and optionally pre-processed (e.g. digital filtering, decimation, etc.). The resulting stream of I/Q time-domain samples can be used for the analysis of the RF spectrum in the same way as described herein for CPRI, eCPRI, etc. The tap 16 can be an optical power tap which provides a portion of the optical power on the link 14 to the test system 10 for analysis thereof.
[0036] An AxC within the link 14 is an Antenna Carrier. It is a portion of the link where IQ samples of a particular antenna are transported. For the untrained eye, it is difficult to provide an assessment of the quality of the link 14 by looking at the spectrum trace in the UI 12. Experience is required to properly set the different parameters and values such as RBW, VBW, min trace, max trace, etc. on the test system 10. Furthermore, the user has to correlate interferences on multiple AxCs manually by bringing up multiple graphs and comparing them in order to identify interferers.
[0037] FIG. 2 is a functional block diagram of the test system 10. The test system 10 can be a processing device that, in terms of hardware architecture, generally includes a CPRI interface detector 30, a processor 32, input/output (I/O) interfaces 34, a network interface 36, and memory 38. It should be appreciated by those of ordinary skill in the art that FIG. 2 depicts the test system 10 in an oversimplified manner, and a practical embodiment may include additional components and suitably configured processing logic to support known or conventional operating features that are not described in detail herein. The components (30, 32, 34, 36, and 38) are communicatively coupled via a local interface such as, for example, one or more buses or other wired or wireless connections, as is known in the art. The CPRI interface detector 30 is configured to connect to the link 14, such as via the tap 16. For example, when the link 14 is a fiber optic link, the CPRI interface detector 30 can be a receiver, i.e., a photodetector, that is configured to receive a signal for processing by the test system 10. Alternatively, the link 14 can be an electrical link as well with the tap 16 being a splitter or the like.
[0038] The processor 32 is a hardware device for executing software instructions. The processor 32 may be any custom made or commercially available processor, a Central Processing Unit (CPU), an auxiliary processor among several processors associated with the test system 10, a semiconductor-based microprocessor (in the form of a microchip or chip set), or generally any device for executing software instructions. When the test system 10 is in operation, the processor 32 is configured to execute software stored within the memory 38, to communicate data to and from the memory 38, and to generally control operations of the test system 10 pursuant to the software instructions. The I/O interfaces 34 may be used to receive user input from and/or for providing system output to one or more devices or components. The user input may be provided via, for example, a keyboard, touchpad, and/or a mouse. System output may be provided via a display device and a printer (not shown).
[0039] The network interface 36 may be used to enable the test system 10 to communicate on a network, such as the Internet. The network interface 36 may include, for example, an Ethernet card or adapter (e.g., 10BaseT, Fast Ethernet, Gigabit Ethernet, 10 GbE) or a wireless local area network (WLAN) card or adapter (e.g., 802.11a/b/g/n/ac). The network interface 36 may include address, control, and/or data connections to enable appropriate communications on the network. For example, the UI 12 in FIG. 1 can be provided via a display device connected to the I/O interfaces 34 and/or via a remote device connected via a network through the network interface 36.
[0040] The memory 38 may include any of volatile memory elements (e.g., Random Access Memory (RAM, such as DRAM, SRAM, SDRAM, etc.)), nonvolatile memory elements (e.g., ROM, hard drive, tape, CDROM, etc.), and combinations thereof. Moreover, the memory 38 may incorporate electronic, magnetic, optical, and/or other types of storage media. Note that the memory 38 may have a distributed architecture, where various components are situated remotely from one another, but can be accessed by the processor 32. The software in memory 38 may include one or more software programs, each of which includes an ordered listing of executable instructions for implementing logical functions. The software in the memory 38 includes a suitable operating system (O/S) and programs. The operating system essentially controls the execution of other computer programs, such as the programs, and provides scheduling, input-output control, file and data management, memory management, and communication control and related services. The programs may be configured to implement the various processes, algorithms, methods, techniques, etc. described herein.
[0041] In addition to the components (30, 32, 34, 36, and 38), the test system 10 includes functional components such as a test sequencer 40, a CPRI mapping auto-detect function 42, an AxC configuration function 44, a PIM measurement function 46, a peak detection function 48, a spectrum traces function 50, and a post-analysis function 52. These various functions (40, 42, 44, 46, 48, 50, 52) can be software instructions executed on the processor 32 for automated RF analysis. Generally, the test system 10 is configured to connect to the link 14 to perform multiple measurements orchestrated by the test sequencer 40. The measurements are performed on the AxCs detected by the CPRI mapping auto-detect function 42.
[0042] The test system 10 is a turn-up and troubleshooting tool and may be referred to as a test application or system. The test system 10 includes the test sequencer 40 which is an automated sequencer configured to fully assess the link 14 and all active AxCs, This automated sequence includes auto-discovery of link rate and Key Performance Indicator (KPI) measurements, auto-discovery of AxC mapping, automated AxC KPI measurements (e.g., PIM), automated detection of anomalies with key characteristics (e.g., frequency, bandwidth, level), identification of pre-defined Interference Types (e.g., a UHF Monitor, Wi-Fi hotspot), etc. The test system 10 requires minimal User Configuration (e.g., Center Frequency, Reference Power). Further, the test system 10 includes progressive reporting as tests are running, correlation of anomalies/interferences observed in more than 1 AxC (e.g., external PIM), and a reporting view with complete link assessment (e.g., tabular views, annotated RF Spectrum graphs, etc.).
Test Sequencer
[0043] FIG. 3 is a block diagram of phases P1, P2, P3, P4 implemented by the test sequencer 40. The test sequencer 40 controls the order and assesses the results of tests. The test system 10 can automatically abort a test if any of the following conditions are met and report the applicable state.
[0044] If the test is started while the Auto-Detect was in progress but not yet completed, the test continues and lets the auto-detect complete before starting the phases. In the event the test is aborted, a global pass/fail verdict is failed. The test system 10 automatically stops once the last phase in the sequence is completed. In the event that a test has run partially but has aborted, the partial results are available. Control is available to restore to default the values for the test system 10 configuration and monitoring parameters upon request when the test is stopped.
[0045] The phases include a setup phase P1, a capture phase P2, a processing phase P3, and a post-analysis phase P4. The setup phase P1 includes various configurations as well as a live CPRI status. The configurations can include port selection, CPRI monitoring, optical power, mapping on/link up, adapted AxCs configuration, and fine-tune settings. The port selection parameter determines which port is used for the test. When a test is not running and the physical port selected for the test changes from any state to Link-Up, it is considered a trigger for an auto-detect process. When the result status of the auto-detect process is a success, the mapping is automatically applied. The auto-detect process is not triggered as long as the test is running. In the event that the link is unstable and transitions again to Link-Up (possibly multiple times) while the previous auto-detect process has not yet completed (either failure or success), the triggering of a new auto-detect process is held until the previous one completed.
[0046] The AxC configuration function 44 can include an AxC List with the AxCs associated to the Link 14. By default, the AxC list contains a set number of AxCs. In the event that the auto-detect process result is a failure or shows no activity, the previous AxC List is kept. Each AxC is characterized using the following parameters: AxC number, center frequency, bandwidth, and an enable/disable parameter (to include a particular AxC). The AxC number can be a sequential number starting at 0 assigned from the first AxC to the last. The bandwidth is automatically determined from the auto-detect process (e.g., in units of MHz). The center frequency parameter determines the center frequency of the AxC. The center frequency can be fixed when the auto-detect process is in progress, i.e., not configurable. Example values of the center frequency can be in a range of 0 to 50 000 MHz with a resolution of 0.001 MHz.
[0047] Upon a start, entering the capture phase P2 from the setup phase P1, a snapshot of the configuration is kept such that any subsequent auto-detect that could occur after the test is stopped does not disrupt the results.
[0048] Note, the measured values in the captured A.times.C samples do not represent the real signal level. The present disclosure can provide the actual signal level from the captured samples. Each equipment has a fixed offset between the measured values and the real signal level. It is possible for the user to input this offset in the configuration, but the present disclosure provides automation of the test. As such, the user can select a type of equipment (e.g., radio equipment (RRH)) from a menu with the test system 10 having the corresponding offset in a database.
[0049] The test system 10 can support a calibration value that is applicable to one or more AxCs of the AxC List, e.g., a range of 0 to -200 dBm/bit with a granularity of 1 dBm/bit.
[0050] For capturing A.times.C samples, the test system 10 can carry out RF calibration from the IQ samples with dBm/bit to obtain absolute values of the real power levels instead of a normalized amplitude reading. The calibration parameters are fixed based on the radio equipment (RRH). During setup, the user can pick the RRH equipment from a list of predetermined equipment. The test system 10 uses a lookup table to retrieve a compensation offset value. The user may use the real power levels, for example, in complaints for competing power levels. Example test results would be as follows: The user selects a specific RRH type during configuration that has an offset of 58, the interferer generates -32 dBm of noise in the spectrum, the test system converts this measured valued into a real signal level of -90 dBm.
[0051] Once the test is started, IQ samples from each item in the AxC list are captured in the capture phase P2 and provided to the processing phase P3. The processing phase P3 includes a PIM measurement, peak detection, spectrum graphs, and other anomaly detection. The test system 10 supports the PIM measurement with a PIM threshold parameter. A unique PIM Threshold parameter is applicable for all items of the AxC List. A single PIM Threshold is applied to one or more AxCs. The duration of the PIM Measurement phase is of sufficient length to allow for stable and accurate measurement.
[0052] The test system 10 detects peaks for each item of the AxC List. The duration of the peak detection is of sufficient length to allow for accurate detection. For each item of the AxC list, a full span spectrum trace snapshot is produced. The spectrum trace snapshot shows the minimum, maximum, and average traces. The spectrum trace snapshot span can be the bandwidth of the AxC. The spectrum trace snapshot amplitude and scale can be adjusted to show all traces, including the peaks. The RBW used to produce the spectrum trace snapshot is reported. Each detected peak can be marked with a special symbol.
[0053] For each peak of each AxC in the AxC List, a zoomed-in spectrum trace snapshot is produced. The zoomed-in spectrum trace snapshot shows the average trace allowing a clear view of the peak. The zoomed-in spectrum trace snapshot span can be at least twice the bandwidth of the detected peak. The zoomed-in spectrum trace snapshot amplitude and scale can be adjusted to show the peak clearly. The RBW used to produce the zoomed-in spectrum trace snapshot is reported. Each detected peak can be marked with a special symbol.
[0054] The post-analysis phase P4 includes a post-analysis list with entries generated therein. In the event that the test sequencer 40 needs to abort the test due to alarms/errors on the link 14, a CPRI Link Fault entry is added in the post-analysis list. For each peak of each AxC in the AxC List, the test system 10 tries to identify the peak and adds an entry in the post-analysis list on a positive match. When the same peak is identified on more than one AxC, all occurrences are reported as a single entry in the post-analysis list, listing AxCs where the peak was identified.
[0055] For automated analysis, if the PIM verdict is failed for items of the AxC List (e.g., the enabled AxCs), the PIM assessment is external PIM for all AxCs of the AxC List. If the PIM verdict is failed for some items of the AxC List, but not all, the PIM assessment is internal PIM for the AxCs having a failed verdict. The PIM assessment is reported in the post-analysis list as a single entry with all affected AxCs.
[0056] For AxCs of the AxC List that have unidentified peaks, the test system 10 finds peaks that are at the same frequency on more than one AxC. The criteria to declare the same frequency is a peak that falls within the resolution of the peak detector. An identical interferer entry in the post-analysis list can report the following information: frequency, list of AxCs having this peak, worst relative power, etc. Out of all the unidentified peaks and identical interferers entries in the post-analysis list, entries can be sorted based on the strongest relative power for top interferers. For the identical interferer entries, the AxC presenting the strongest relative power can be used to compare with the other entries. All other entries that go beyond the top interferers can be dropped from the post-analysis list.
[0057] Once the post-analysis phase P4 is completed, the post-analysis list entries can be re-ordered with the following priority: CPRI Link assessment, PIM assessment, peak identification, and top interferers. If the post-analysis list is empty at the end of the post-analysis phase P4 (meaning no anomalies were found), then an entry can be added for no anomalies detected.
[0058] Control is available to view a selected AxC or a selected peak in a live view application in the UI 12. Any configuration changes done in the live view application do not affect the configuration and results of the test system 10. Once in the live view application, there is a control to return back to the main page. When jumping to the live view application to view an AxC or multiple AxCs, the following conditions are observed: the source configuration is automatically selected to the affected AxCs. The minimum and maximum traces are displayed. The real-time trace of each affected AxCs is displayed and overlaid when multiple. The span can be the bandwidth of the largest AxC. The amplitude and scale can be adjusted to show all traces, including the peaks. The RBW is the same as the one used to produce the snapshot. The VBW is adjusted to show a trace similar to the snapshot. The PIM Measurement is enabled on the affected traces with the same threshold as set in the test system 10.
[0059] When jumping to the live view application to view a peak, the following conditions are observed: the source configuration is automatically selected to this AxC. The minimum, maximum, and real-time traces are displayed. The frequency of the graph is centered on the selected peak. The span is the same as the peak zoom-in. The amplitude and scale are adjusted to show all traces, including the peaks. The RBW is the same as the one used to produce the snapshot. The VBW is adjusted to show a trace similar to the snapshot.
[0060] Further details are provided for the phases P1, P2, P3, P4 of the test sequencer 40. The test preparation involves all the steps that have to be done before starting the test. In its minimal form for the user, the test preparation only includes connecting the optical fiber coming from the tap 16 to the test system 10. The mapping auto-detect determines the AxCs from the link 14. Once the test is started by the user, the test sequencer 40 automatically executes each step. The CPRI monitoring provides link detection to provide a link state live status and the detected rate. The optical power monitoring monitors the optical power, with power range validation.
[0061] The CPRI mapping auto-detect 42 is automatically triggered each time the link transitions from Link Down to Link Up. Only the Detected AxCs are presented with the following information: AxC number, bandwidth. The AxC configuration function 44 has multiple features. For each AxC detected, the user can enter the center frequency. By default, the Center Frequency (CF) is 0 MHz.
[0062] Aggregation configuration is used for aggregation. Aggregation is the logical grouping of two or more component carriers (physical carriers). Long Term Evolution (LTE) higher layers use the resources blocks of the aggregation as a single pool of resources. On the air, these component carriers can be Intra-band contiguous, Intra-band non-contiguous, or inter-band. In the test system 10, aggregation makes sense for Intra-band contiguous, which is the most common. The center frequency would be applied to the aggregation. For other types of aggregation, it would be better for the user to consider the component carrier individually instead of an aggregation.
[0063] There can be a grouping of AxCs within the link 14 to know which AxCs belong to a particular RRH within the link 14. It can be used during the correlation phase for PIM assessment and reporting. The RF Calibration includes a predefined list of RRH with known dBm/bit values and also includes user-defined lists. If the link 14 goes down, the parameters can be preserved and re-applied if the same AxCs are detected (same quantity and bandwidth per AxC). The fine tune settings include the PIM Threshold and the peak sensitivity. The peak sensitivity is used to adjust the peak detection sensitivity.
[0064] Any change in setup does not affect any results of a previous test run. As an example, the mapping may change following a Link Up. The AxCs presented in the results do not change in this case. A test duration setting allows for increasing the processing duration to improve the detection of intermittent or moving interferers. Profiles are used to load a pre-defined site configuration. For example, pre-defined RRH profiles can be used in which center frequencies would be already populated.
[0065] After the setup phase P1, a user can activate a start button or the like to enter the capture phase P2. A full snapshot of the setup is taken and used as a basis for the results. Any subsequent change of setup or configuration does not affect the results of a test run. Once the test is started, the test can be manually stopped at any moment, but it will also stop automatically once all the steps are completed. If a condition prevents the test from being executed, it is aborted with a reason. Pressing the start button clears the previous results. During the execution of the test sequence, statistics can be presented as they become available. A test execution status can be presented throughout the test with meaningful messages such as "Collecting A.times.C samples," "Measuring PIM," etc. Results are frozen on stop.
[0066] In the capture phase P2, there is the execution of the test sequence. While IQ samples are extracted from the link 14 for processing, the CPRI interface is monitored in parallel. If any of the following alarms/errors are present, the test automatically aborts and reports the condition: Alarms: Loss of Signal (LOS), Link Down, Loss of Frame (LOF), R-LOS, R-LOF, Remote Alarm Indication (RAI), Defect Indication. Errors: SH, 66B Block, FAS. This helps avoid inducing false peak detection. The Optical power is also monitored although no automatic action is performed if an anomaly is detected. The condition can be simply reported. The Optical Power is reported, with power range validation. If the CPRI Interface is nominal, IQ Samples are captured from the link and provided to the processing phase P3.
[0067] In the processing phase P3, PIM measurement does not require configuration. PIM is measured on all detected AxCs. A verdict is given based on the configurable threshold. For each AxC, peak detection is performed. Both narrowband and wideband are detected. These steps can be performed simultaneously or sequentially as needed by the detection algorithm. The following statistics are reported: center frequency, relative power, bandwidth, duration/cycle of the peak. For each AxC, a spectrum graph is produced. The graph contains the minimum, average, and maximum traces. The RBW, VBW, and other settings used to produce the graph are collected. For each peak detected in each AxC, a spectrum graph zoom-in is produced showing an optimized view of the peak (single trace). Again, the RBW, VBW, and other settings used to produce the graph are collected. The spectrum graph and spectrum graph zoom-in provide control to access an embedded live view. When accessed, the live view appears with the selected AxC. proper RBW, VBW, and so on are selected for an optimized display. The spectrum graph live view can show all 3 traces. The spectrum graph zoom-in can show the average trace but is zoomed-in for optimal interferer view. Once in the live view, the user has full control as per the live RF Spectrum viewing application offering.
[0068] A peak detector function is a process that takes a number of spectrum trace samples from an AxC and applies various filters to detect the presence of interferer that is not regular LTE traffic and management signals. It is possible to initiate the peak detector function on a given AxC for a specified amount of time specified by the application running the measurements. The peak detector operates over the full mapping bandwidth of the AxC. The peak detector detects the presence of interferers, narrowband, and wideband, that are not regular LTE traffic and management. Management Channels on each side of the spectrum shoulders do not create false positive. The peak detector uses a sufficient amount of traces to provide a stable measurement.
[0069] For example, the peak detector can report the following statistics for each interferer found: relative power: Range: +/-200 dB, Resolution: 0.01 dB; Power (Amplitude): Range: +/-200 dB, Resolution: 0.01 dB; Frequency: Range: +/-50 000 MHz, Resolution: 0.001 MHz; Bandwidth: Range: 0.001 MHz to 1 MHz, Resolution: 0.001 MHz.
[0070] When more than one peak is detected within a bin of 1 kHz, the peak detector can only report the peak with the strongest relative power. The peak detector automatically adjusts the amplitude value and its unit on a per AxC basis. The frequency value is always adapted with respect to the current center frequency value associated with the AxC being processed. A peak sensitivity parameter determines the sensitivity of the peak detector function. For example, a higher number can signify a greater sensitivity.
[0071] In the post-analysis phase P4, each peak found can be compared to a signature database 60 for a potential match in an identification step. When a match is found, the peak is identified with a descriptive name, aggregating multiple instances found on many AxCs as a single entry. An example message is as follows: "Potential <name of interferer> interferer found at <CF> detected on <list of AxC>." The signature database 60 contains a collection of known interference signatures. It contains all relevant RF characteristics to positively identify an interferer, including waveform, RF Settings to detect it, margin, etc. It can be pre-built with known interferers. It is possible to update the signature database 60. A capture/report feature allows sending information about a found interferer that is not in the signature database 60 for incorporation in the pre-built database.
[0072] Peak identification is a function that takes the peaks found by the peak detector, and one by one tries to match the signature to a collection of known interferers. When found, the peak is identified with the name of the suspected equipment causing this interference. Initially, only static interferers are identified. A static interferer is defined as a peak that does not change frequency or amplitude during the peak detection process. The peak identification function tries to identify each by matching its key characteristics to the collection of known interferer signatures. The peak identification function can support static and dynamic peaks. The peak signature is associated with the following key characteristics: center frequency, waveform, peak detector Settings to detect it. On a positive match, the peak identification function reports the name of the Interferer.
[0073] The peak identification function considers a margin for each signature. Indeed, by definition, an interferer is an unwanted source of RF energy that is emitted by a device that is not under the control of the owner/operator of the spectrum where the interferer is located. This uncontrolled device might be of varying quality and may be made with a local oscillator of poor quality. The interferer might, therefore, emit energy at a frequency that is not very precise depending on various factors such as temperature and aging. The peak identification function needs a margin to detect it; the interferer will not be at the same exact frequency from site to site. The margin is dependent on the known variance of the peak signature. The collection of signatures is kept in a repository on the platform (the signature database 60) that can be modified independently of the software package. Changes made to the collection of signatures is applied next time the test is started.
[0074] Analysis/Correlation identifies anomalies that cannot be identified when each AxC is analyzed individually. Types of correlations include internal/external PIM determination, identical interferers among AxCs, and top interferers. External PIM detection is another feature of the post-analysis phase P4. When PIM is present on AxCs simultaneously, it is unlikely that all antennas are affected simultaneously by an internal connection problem such as a bad connector. In this case, the most probable root cause is external PIM, such as a metallic object in front of the antennas which affects all antennas. Therefore, when a PIM verdict is declared on the AxCs, external PIM is declared. An example message is as follows: "External PIM detected on <list of AxC>." Internal PIM detection occurs when PIM affects some AxCs but not all. An example message is as follows: "Internal PIM detected on <list of AxC>." For each detected peak on each AxCs, a correlation is performed to find interferers that are at the same frequency. If found, they are declared as identical interferers. An example message is as follows: "Identical interferer at <CF> detected on <list of AxC>."
[0075] When a system (e.g., the RRH 18 connected to the BBU 22 via the link 14) is in a very noisy environment, the number of peaks can grow large. The peaks that most likely cause a problem for the operator are the most powerful ones. Unidentified peaks, either unique or listed as identical interferers, are analyzed to pick a top set presenting the highest relative power. These are the top interferers.
[0076] When the number of detected peaks is large, the post-analysis message window can be overwhelming for the user. Some problems are more serious than others. It is, therefore, useful to prioritize the post-analysis messages. The post-analysis messages can be presented, for example, with the following priority: PIM, identified peaks, top interferers. This is done by the Prioritization module.
[0077] The test system 10 can detect that the link 14 itself has an issue. A discontinuity on the link 14 will cause an enormous peak, detectable by the test system 10. A bit error in the encoding can also hint at such an issue. The link 14 should be fixed first (for example, with an optical link, using an Optical Time Domain Reflectometer (OTDR) to detect and determine the issue) before other RF issues are addressed.
Example GUI Screens
[0078] FIG. 4 is a diagram of a Graphical User Interface (GUI) 100 for the test system 10 at setup. In this example, the test system 10 is connected to port P1 of an SFP+ with an optical power of 0.0 dBm (as illustrated in the bottom left of the GUI 100). A CPRI port 101 displays a port selection as well as link status, the detected rate, and the optical power. An adapted AxCs table 103 displays the detected AxCs with the AxC number, bandwidth, and center frequency. The adapted AxCs table can include an aggregation button to access a pop-up screen. The adapted AxCs table can include a calibration button to access a list of predefined RRH. The adapted AxCs table can also include an advanced button to access a pop-up screen with the PIM threshold and peak sensitivity settings. A restore default button 105 is also provided.
[0079] FIG. 5 is a diagram of a GUI 100 for results through the test system 10. A test status area 149 includes the start time, progress bar, and test status. The CPRI Port 101 indicates link status, detected rate, optical power with range, current alarms/errors. An AxC summary table 153 lists the AxC number, bandwidth, center frequency, PIM value, and the number of peaks. A selection of an AxC in the AxC summary table 153 will trigger the displays in a peak table 157 and a spectrum graph area 159. The peak table 157 lists the peak number, the center frequency, the bandwidth, the relative power, and the power. The spectrum graph area 159 shows the RF spectrum. The settings can be shown on the graph legend (RBW, VBW, etc.). When selecting a peak in the peak table 157, a spectrum trace zoom-in is displayed in a zoom-in window 163.
[0080] A post-analysis message window 165 contains a list of post-analysis messages. It contains a global assessment. When no problems are found, a message is provided, such as "No Errors Detected." When any other anomaly is detected, the post-analysis message window 165 simply contains messages about the anomalies. The list of post-analysis messages can be automatically sorted for priority. For example, the priority can be to list the easy-to-fix issues first and the time-consuming ones below. Also, the priority can be to list the issues based on impact or severity. Other embodiments are also contemplated.
[0081] On selection of an entry in the post-analysis message window 165, the peak table 157, the spectrum graph area 159, and the zoom-in window 163 show the entry. When more than one AxC is affected, a spectrum overlay is shown, without the peak table 157.
[0082] Rows in the AxC summary table 153, the peaks table 157, and the list of post-analysis messages is selectable only when the test is not running. The AxC summary table 153 can present the following information, for example, in tabular format AxC: AxC Number; Frequency (MHz): Center Frequency; Bandwidth (MHz): Bandwidth; PIM (dB): PIM Measurement; Peaks: Number of peaks detected. The AxC summary table 153 can present only the AxCs that were detected in the link 14. When selecting a row in the AxC summary table 153, its peak table 157 and the spectrum trace is displayed.
[0083] The list of post-analysis messages in the post-analysis message window 165 include entries displayed as per the following, for example, depending on the type of entry: no anomalies detected: No anomalies detected; CPRI Link Assessment: CPRI Link Fault; Internal PIM Assessment: Internal PIM Detected on <List of AxC>; External PIM Assessment: External PIM Detected on <List of AxC>; Identified Peak: Potential <name> interferer at <Center Frequency> detected on <List of AxC>; Unidentified Peak: Interferer (<ISR> dB) detected at <Center Frequency> on <List of AxC>; Identical Interferer: Identical interferer at <Center Frequency> detected on <List of AxC>.
[0084] When selecting an entry in the list of post-analysis messages, the spectrum trace full span and zoom-in are displayed in the spectrum graph area 159 for the AxC or AxCs affected by the entry. When a single AxC is affected by the entry, its corresponding row in the AxC summary table 153 and the peak table 157 is automatically selected. When more than one AxC is affected by the entry, the spectrum traces are displayed as overlays, and the AxC summary table 153 and the peak table 157 are not displayed.
[0085] The peak table 157 can present the following information, for example, in tabular format: Number: Peak Number; Frequency (MHz): Peak Frequency; relative power (dB): relative power; Power (<unit>): Power. When selecting a row in the peak table 157, the following behavior is observed, namely its spectrum trace zoom-in is displayed, and a special symbol for the selected peak is visibly different than the other symbols.
[0086] FIG. 6 is a screenshot of an example results GUI in which a test has already been performed. Here, Peak 1 of AxC 3 is currently highlighted and displayed in the spectrum graph area 159 and the zoom-in window 163 with a marker 170. FIG. 7 is a screenshot of an example corresponding live view which has been triggered by the results window of FIG. 6. When in live-view mode, the spectrum graph area 159 and zoom-in window 163 can call upon a live RF spectrum application to show live views.
[0087] FIGS. 8A-8J are diagrams of an example report based on the results in FIG. 6. FIG. 8A is a job information table which is blank in this example. FIG. 8B is a table of the CPRI link details including the port, state, receive power, and rate. FIG. 8C is a table of a site configuration including each AxC, its frequency, and bandwidth. FIG. 8D is a summary table of the detected anomalies including the bandwidth, PIM, and peaks on each AxC. FIG. 8E is a list of diagnostics obtained during the analysis. FIG. 8F is tables of the details of each peak identified on each AxC with its frequency and power. FIGS. 8G, 8H, 8I, and 8J are graphs illustrating the best representative graph for each AxC with its detected peaks and the zoom-in graph for each detected peak.
Automated RF Analysis
[0088] The systems and methods automate the evaluation/analysis of the state of the link 14. The auto-detection of the mapping of the antennas (AxC) on the link 14 is one component of this automation. Another component is the detection and tracking of interferers in the RF spectrum. The auto-detection of PIM on an RF spectrum is yet another component. Advantageously, the systems and methods aggregate results about the link 14 to then provide analysis and preliminary diagnosis via the UI to a technician looking at interpreting the collected data about the link.
[0089] FIG. 9 is a flowchart of an external PIM detection process 200. The external PIM detection process 200 includes the steps of detecting the presence of a PIM in each antenna of a plurality of antennas of the same tower of a link (step 202), determining a level of interference of each PIM (step 204), and, if the level of interference of each PIM is greater than a PIM detection threshold, determining that an external PIM is present (step 206). In an example embodiment, the PIM detection threshold is 6 dB. The external PIM detection process 200 operates under the assumption that if all antennas of a tower have detected PIM, the PIM is caused by an external source.
[0090] FIG. 10 is a flowchart of an internal PIM detection process 220. The internal PIM detection process 220 includes the steps of detecting the presence of a PIM in an antenna of a plurality of antennas of the same tower of a link (step 222), determining a level of interference of the PIM (step 224), and if the level of interference of the PIM is greater than a PIM detection threshold and if not all antennas of the plurality of antennas have a PIM, determining that an internal PIM is present on that specific antenna (step 226). In an example embodiment, the PIM detection threshold is 6 dB. The internal PIM detection process 220 operates under the assumption that if not all antennas of a tower have detected PIM, the PIM is caused by an internal source.
[0091] FIG. 11 is a flowchart of an identical interferer detection process 240. The identical interferer detection process 240 includes the steps of detecting the presence of at least one interferer for at least one antenna of a plurality of antennas of a same tower of a link (step 242), determining a frequency of each interferer (step 244), comparing the list of interferers of each antenna with that of the other antennas (step 246), if more than one antenna has an interferer at the same frequency, identifying that the interferers are the same (step 248), and tagging the interferer with the list of antennas on which it appears and the frequency (step 250). It will be readily understood that the "same frequency" is within an acceptable range defined by the user.
[0092] FIG. 12 is a flowchart of a known interferer detection process 260. The known interferer detection process 260 includes the steps of detecting the presence of at least one interferer at a known frequency on at least one antenna of the link (step 262), and tagging this interferer at said known frequency as being potentially caused by a known device (step 264). The known device is one predetermined to interfere at the known frequency. In an example embodiment, the known device is a third-party Wi-Fi device known to cause interferences at 780 MHz. The known interferer detection process 260 therefore identifies that a Ubiquiti device has likely caused the interference detected at the known frequency of 780 MHz. In another example embodiment, the known device is a Takstar device or an Ultra High Frequency (UHF) monitor. For example, the Takstar device can be a UHF monitoring system and can cause interference at 780.00551 MHz, 783.00552 MHz, 785.00553 MHz, etc.
[0093] Those skilled in the art will appreciate the known device can be any type of device that is predetermined to cause interference. Each different known device can have a unique signature in the database 60 that can be detected along with a description to provide the user useful information for troubleshooting.
[0094] In one example embodiment, some of the interferers could exhibit modulation. The known interferer detection process 260 can detect this modulation and measures the symbol rate of the modulation. This information can be displayed on the user interface. It can further be used to correlate the information with that of a known interferer to help identify a potential cause for the interferer.
[0095] In one example embodiment, the test system 10 also prioritizes the anomalies. This could prevent overcrowding of the analysis display section in the GUI 100, which could overwhelm the user. The most serious issue among the detected interferers is identified through a set of decision rules and is displayed with an emphasis, either by displacing it at the top of the Analysis section or by discarding lower priority messages about less serious issues. Another way of prioritizing the issue is via color coding. The decision rules could take into account severity of the issue with respect to its impact on the link status, the impact that fixing an issue would have on the status of the link or the sequence in which the issues should be addressed to reach a better status. This would guide the technician in assessing the health of the link and in choosing what to fix first.
[0096] The test system 10 can include an RF spectrum analysis tool that implements the processes 200, 220, 240, 260. Also, the test system 10 can implement all of the processes 200, 220, 240, 260 in some combination as well as a subset of the processes 200, 220, 240, 260 in some combination. The test system 10 can include a plurality of other detection and diagnosis processes. For example, the RF spectrum analysis tool could include the detection of the UHF monitor and the detection of the diversity imbalance.
User Interface Example
[0097] FIGS. 13-19 are screenshots of an example UI 300 of an RF spectrum analysis tool via the test system 10 in different example states. FIG. 13 is a screenshot of an example RF spectrum analysis tool in a state with no errors currently detected. FIG. 14 is a screenshot of the example RF spectrum analysis tool in a state with a detected internal PIM and identical interferers detected on a plurality of antennas of the same tower. FIG. 15 is a screenshot of the example RF spectrum analysis tool in a state with a detected external PIM. FIGS. 16A-16C are screenshots of the example RF spectrum analysis tool in a state with a detected internal PIM and a potential Ubiquiti interferer in the summary mode for AxC 1. FIG. 17 is a screenshot of the example RF spectrum analysis tool in a state with a detected internal PIM on AxC 4, the RF spectrum of AxC 4 being shown in the spectrum section and for which peak 2 of AxC 4 is displayed in the peak detail. FIG. 18 is a screenshot of the example RF spectrum analysis tool and a setup page. FIG. 19 is a screenshot of the example RF spectrum analysis tool where specific AxCs are enabled/disabled in a post-analysis process.
[0098] The GUI 300 is similar to the GUI 100 presented herein. The GUI 300 includes various sections such as a port section 302, a summary section 304, an analysis section 306, a pass/fail state 308, a test configuration section 310, a status bar 312, a peaks section 314, and a spectrum section 316. The port section 302 displays the port identification, the port state, the port Receive Power (RxPwr), and the port rate. Other information that could be displayed about the port include the CPRI alarms, 66B Block Error, Synch Header, FAS, etc. The summary section 304 displays a table including all antennas on the link 14 and their bandwidth in MHz, their detected PIM strength in dB, and their detected peaks. The analysis section 306 displays a message related to the diagnosis made by the test system 10 about the status of the antennas. In FIG. 13, the analysis returns a "No errors detected" message.
[0099] The pass/fail state 308 displays a message related to an overall state of health of the link 14. If no errors are currently detected, the overall state is determined to be "Pass" (as in FIG. 13) and a message, typically highlighted with a color associated with success, such as green, is displayed. If at least one error is currently detected, the analysis section 306 can contain information about the potential issue and/or its cause, and the overall state will be determined to be "Fail." The "fail" message will typically be highlighted with a color associated with failure, such as red (see FIG. 14). The fail status could be subdivided in a plurality of fail sub-status depending on the severity of the detected anomalies or issues. For example, the Pass/Fail state could include 6 sub-statuses, for example, not functional, Bad, Poor, Fair, Good, Excellent. A color coding could be used to highlight the sub-status from red for not functional to green for excellent passing via shades of yellow and orange for intermediary statuses.
[0100] The test configuration section 310 includes a start button, a report button, a setup button, a results button, and tool maintenance buttons. The start button triggers the RF test on the link 14. The report button generates a report containing information about the test results, which can be automatically or manually transmitted to another user. The report may include the contents of any of the sections of the interface. In an example embodiment, the report is a Portable Document File (PDF) file containing screenshots of the appearance of the interface at the time the report button was clicked. The setup button is used to access setup parameters which can be adjusted. The results button generates the view shown in FIGS. 13-17 to view test results. The tool maintenance buttons include information about the version of the tool, contextual help, and a power off button. The status bar 312 shows a message indicating whether the RF test has completed appropriately. In FIG. 13, the status bar shows a "Test Complete" message. When the RF test is currently taking place, the status bar may show a "Test currently being performed."
[0101] FIG. 14 shows the GUI 300 in a state with a detected internal PIM and identical interferers detected on a plurality of antennas of the same tower. The pass/fail state 308 shows a Fail state. In the analysis section 306, a message indicates that at least one error has been detected. Additional messages give a diagnosis of what the issue may be. In this case, an internal PIM is detected on AxC 4. Further, identical interferers are detected on AxC 1 and AxC 2 at 776.99 MHz, 778.16 MHz, 779.7 MHz, and 784.11 MHz.
[0102] As can be seen in the summary section 304, AxC 1, and AxC 2 each have 4 detected interferers. Comparing this to the messages displayed in the analysis section 306, one can deduct that all 4 of their interferers are the same. AxC 4 has a PIM detected with a value of 7.6 dB and is the only antenna with a PIM detected with a value higher than the threshold. The PIM is, therefore, determined to be an internal PIM. It further has 3 peaks which are not identical to those of AxC 1 or AxC 2. AxC 2 is highlighted with a dashed frame and is therefore selected.
[0103] The peaks section 314 displays a table containing the identification of the peaks detected for the selected antenna, the center frequency at which they appear in MHz, and their power level in dB. Because AxC 2 is selected in the summary section 304, the peaks section 314 displays information about the peaks of AxC 2. The peaks section 314 could also include the bandwidth of the peaks.
[0104] The spectrum section 316 displays the RF spectrum graph, which was captured during the live test. On this graph, the average (middle curve 320), the minimum (bottom curve 322) and the maximum (top curve 324) traces are shown. The maximum trace is a maximum hold of all traces. The minimum trace is a minimum hold of all traces. The average trace shows the average. The location of the peaks is identified by a triangular token 328 located at the top of the peak and aligned on the center frequency of the peak. Because AxC2 is selected in the summary section 304 and no specific peak is selected in the peaks section 314, the whole RF spectrum is shown in the spectrum section 316 with all peaks of AxC 2 identified.
[0105] FIG. 15 shows the GUI 300 in an example state with a detected external PIM. The pass/fail state 308 shows a Fail state. In the analysis section 306, a message indicates that at least one error has been detected. A second message gives a diagnosis of what the issue may be, in this case, "External PIM detected on AxC 1, AxC 2, AxC 3, and AxC 4." The summary section 304 shows the values which led to this diagnosis (with highlighting) for emphasis. In this example, all four antennas have a detected PIM of at least 6 dB. The AxC 1 antenna is currently selected as is apparent from the dashed highlighting of the AxC 1 row in the table of the summary section 304.
[0106] FIG. 16A is a screenshot of the GUI 300 in a state with a detected internal PIM and a potential Ubiquiti interferer in the summary mode for AxC 1, FIG. 16B is a screenshot of the example of FIG. 16A in the peak mode for AxC 1, and FIG. 16C is a screenshot of the example of FIG. 16A in the peak mode for AxC 2 with the detail of peak 1. FIG. 16A presents a summary mode view for AxC 1, similar to that shown in FIG. 15. FIG. 16B presents a peak mode view for AxC 1 with the detail of its only peak. FIG. 16C presents a peak mode view for AxC 2 with the detail of peak 1.
[0107] In FIG. 16A, antenna AxC 1 has a detected interferer at 780 MHz. The diagnosis system, therefore, suggests that this could be caused by a Ubiquiti device in the area of the antenna. This is based on the signature database 60 and/or the known interferer detection process 260.
[0108] In FIG. 16B, peak 1 of antenna AxC 1 is selected for viewing in the peaks section 314 as is evidenced by the dashed highlighting. The peaks section 314 now appears next to the spectrum section 316. It shows a zoomed-in section 330 of the RF spectrum centered around the detected peak. A zoomed-in trace in the zoomed-in section 330 is displayed in green because it is also an average. The green trace on the full spectrum is an average of all the traces. The zoom-in trace is an average of a subset of traces, relevant to the interferer.
[0109] In FIG. 16C, peak 1 of antenna AxC 2 is selected for viewing in the peaks section 314. FIG. 16C now shows the zoomed-in section 330 of the RF spectrum around 98 MHz. The triangular token icon for peak 1 on the RF Spectrum section has a modified appearance to highlight the fact that peak 1 is being displayed in the peaks section 314.
[0110] In FIG. 17, there is a detected internal PIM on AxC 4. The RF spectrum of AxC 4 is shown in the spectrum section 316. Detected peak 2 of AxC 4 is displayed in the zoomed-in section 330. The presence of a PIM is detected by calculating the slope of the average curve in the RF spectrum.
[0111] As will be readily understood, the highlighting of rows in the tables is simply used to facilitate consultation of the tables. Odd numbered rows are shown with grey highlighting, even numbered rows are shown with different highlighting. This display scheme does not provide information about the test results.
Automated Link Analysis Process
[0112] FIG. 20 is a flowchart of a process 400 implemented by the test system 10 or the like to automatically analyze and display results of tests of the link 14. The process 400 includes obtaining data from one or more tests of a link, wherein the data includes samples for Antenna Carriers (AxC) for one or more AxCs auto-detected on the link (step 402); processing the data to detect peaks on any of the auto-detected AxCs on the link (step 404); performing an analysis of any detected peaks to identify any issues on the link (step 406); and causing display of a user interface that includes a reporting of any identified issues with the user interface including a display of the identified issues and a spectrum graph (step 408). Again, the link can be a CPRI, an eCPRI, OTA capture, etc. for connectivity between between Radio Equipment Controllers (REC) and Radio Equipment (RE).
[0113] The auto-detected AxCs can be detected by the test system each time the link transitions from link down to link up, and wherein the auto-detected AxCs are maintained in an AxC list. The process 400 can further include automatically configuring Resolution Bandwidth (RBW) and Video Bandwidth (VBW) on the spectrum graph. The display can include zero or more messages with a description of each associated issue and with the zero or more messages in an automatically prioritized order. The spectrum graph can include a full graph and a zoomed-in graph, each having tokens to identify peaks in each visually. The display can include at least one message with a description of a known interferer detected in the analysis, and the known interferer can be determined based on matching signatures in a database.
[0114] The issues can include any of known interferers, internal Passive Intermodulation (PIM), external PIM, and identical interferers across all of the auto-detected AxCs. In an embodiment, the issues include known interferers detected by the steps of detecting a presence of at least one interferer at a known frequency on at least one AxC of the link; and tagging this interferer at the known frequency as being potentially caused by a known device based on matching a signature.
[0115] In another embodiment, the issues include internal Passive Intermodulation (PIM) detected by the steps of detecting the presence of a PIM in an AxC of the auto-detected AxCs of a same tower of the link; determining a level of interference of the PIM; and, if the level of interference of the PIM is greater than a PIM detection threshold and if not all of the AxCs have a PIM, determining that the internal PIM is present on corresponding AxCs. In a further embodiment, the issues include external Passive Intermodulation (PIM) detected by the steps of detecting the presence of a PIM in each AxC of the auto-detected AxCs of a same tower of the link; determining a level of interference of each PIM; and, if the level of interference of each PIM is greater than a PIM detection threshold, determining that an external PIM is present.
[0116] In yet another embodiment, the issues include identical interferes across all of the auto-detected AxCs detected by the steps of detecting the presence of at least one interferer for at least one AxC of the auto-detected AxCs of a same tower of the link; determining a frequency of each interferer; comparing the list of interferers of each AxC with that of the other AxCs; if more than one AxC has an interferer at the same frequency, identifying that the interferers are the same; and tagging the interferer with the list of AxCs on which it appears and the frequency.
[0117] It will be appreciated that some embodiments described herein may include one or more generic or specialized processors ("one or more processors") such as microprocessors; Central Processing Units (CPUs); Digital Signal Processors (DSPs): customized processors such as Network Processors (NPs) or Network Processing Units (NPUs), Graphics Processing Units (GPUs), or the like; Field Programmable Gate Arrays (FPGAs); and the like along with unique stored program instructions (including both software and firmware) for control thereof to implement, in conjunction with certain non-processor circuits, some, most, or all of the functions of the methods and/or systems described herein. Alternatively, some or all functions may be implemented by a state machine that has no stored program instructions, or in one or more Application Specific Integrated Circuits (ASICs), in which each function or some combinations of certain of the functions are implemented as custom logic or circuitry. Of course, a combination of the aforementioned approaches may be used. For some of the embodiments described herein, a corresponding device in hardware and optionally with software, firmware, and a combination thereof can be referred to as "circuitry configured or adapted to," "logic configured or adapted to," etc. perform a set of operations, steps, methods, processes, algorithms, functions, techniques, etc. on digital and/or analog signals as described herein for the various embodiments.
[0118] Moreover, some embodiments may include a non-transitory computer-readable storage medium having computer readable code stored thereon for programming a computer, server, appliance, device, processor, circuit, etc. each of which may include a processor to perform functions as described and claimed herein. Examples of such computer-readable storage mediums include, but are not limited to, a hard disk, an optical storage device, a magnetic storage device, a ROM (Read Only Memory), a PROM (Programmable Read Only Memory), an EPROM (Erasable Programmable Read Only Memory), an EEPROM (Electrically Erasable Programmable Read Only Memory), Flash memory, and the like. When stored in the non-transitory computer-readable medium, software can include instructions executable by a processor or device (e.g., any type of programmable circuitry or logic) that, in response to such execution, cause a processor or the device to perform a set of operations, steps, methods, processes, algorithms, functions, techniques, etc. as described herein for the various embodiments.
[0119] Although the present disclosure has been illustrated and described herein with reference to preferred embodiments and specific examples thereof, it will be readily apparent to those of ordinary skill in the art that other embodiments and examples may perform similar functions and/or achieve like results. All such equivalent embodiments and examples are within the spirit and scope of the present disclosure, are contemplated thereby, and are intended to be covered by the following claims.
* * * * *
D00000

D00001
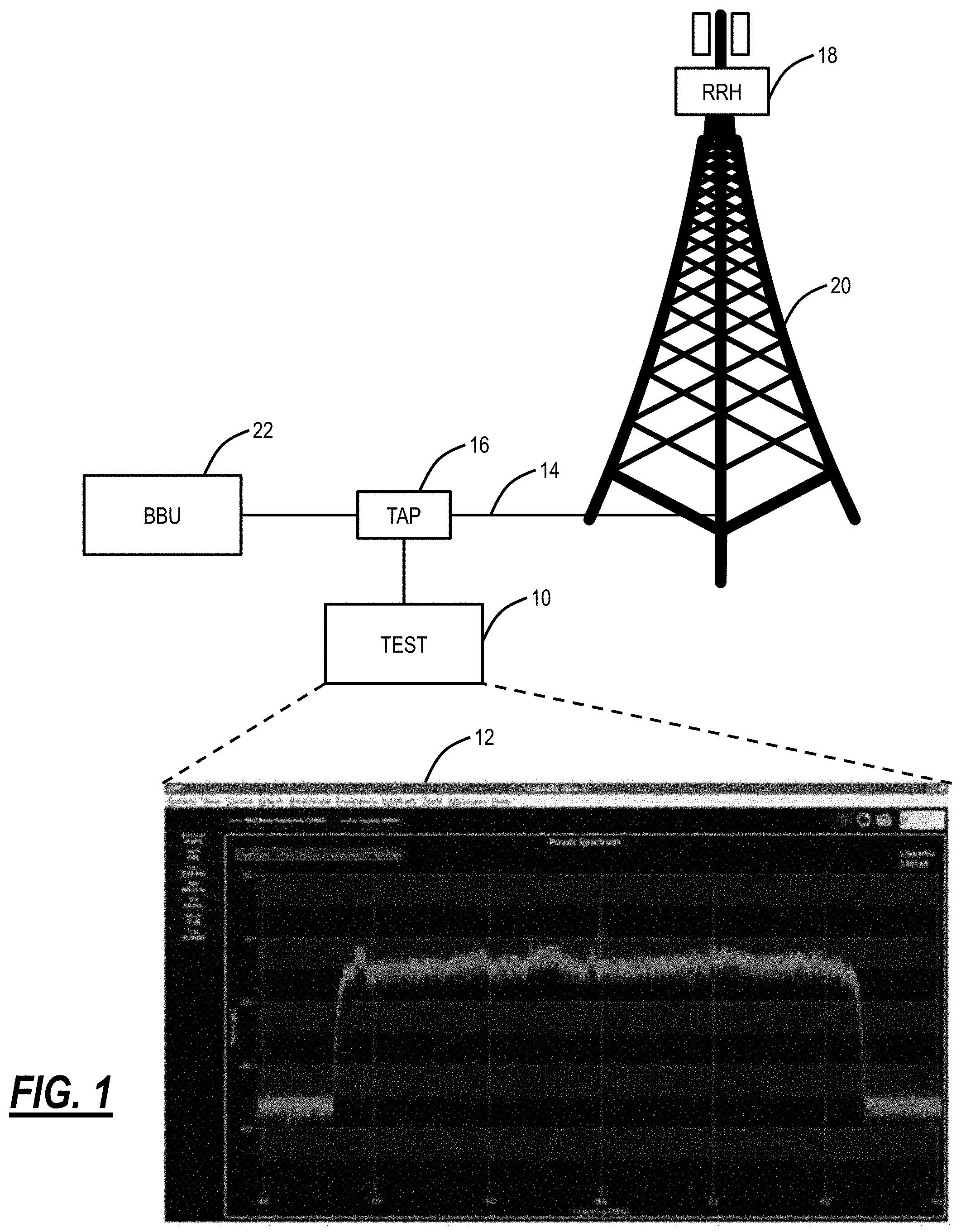
D00002
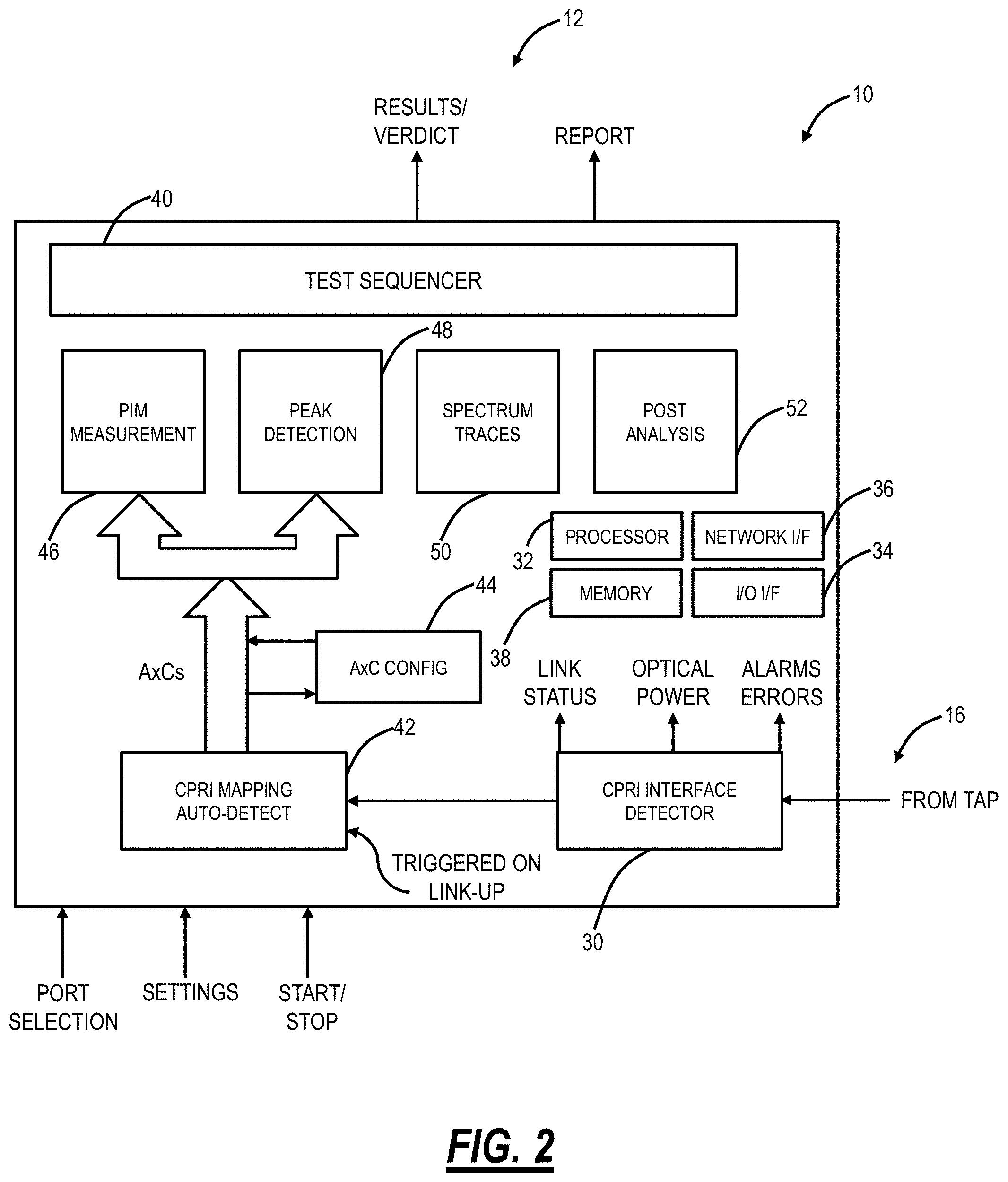
D00003
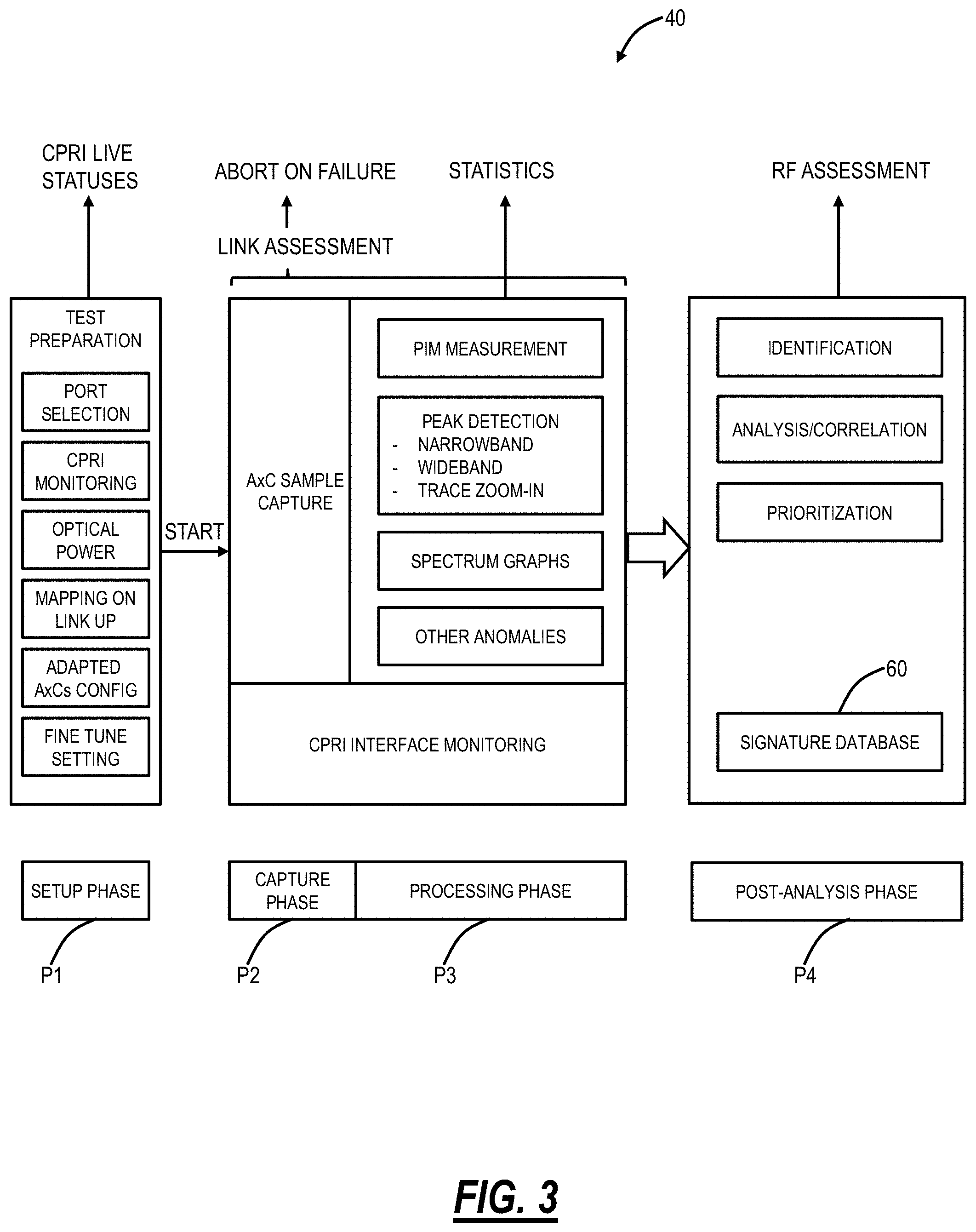
D00004

D00005

D00006

D00007
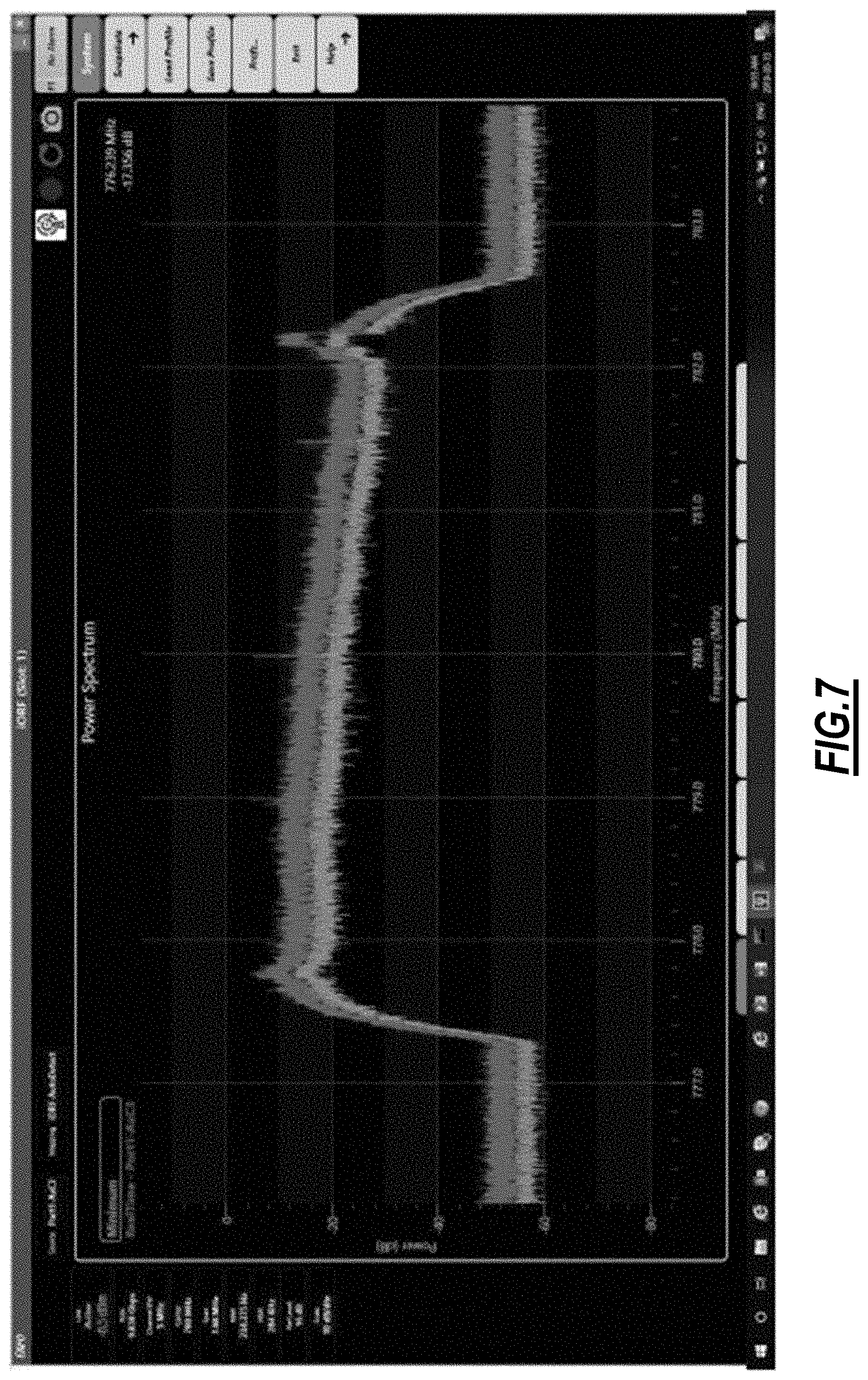
D00008

D00009

D00010

D00011

D00012

D00013

D00014

D00015

D00016

D00017

D00018

D00019
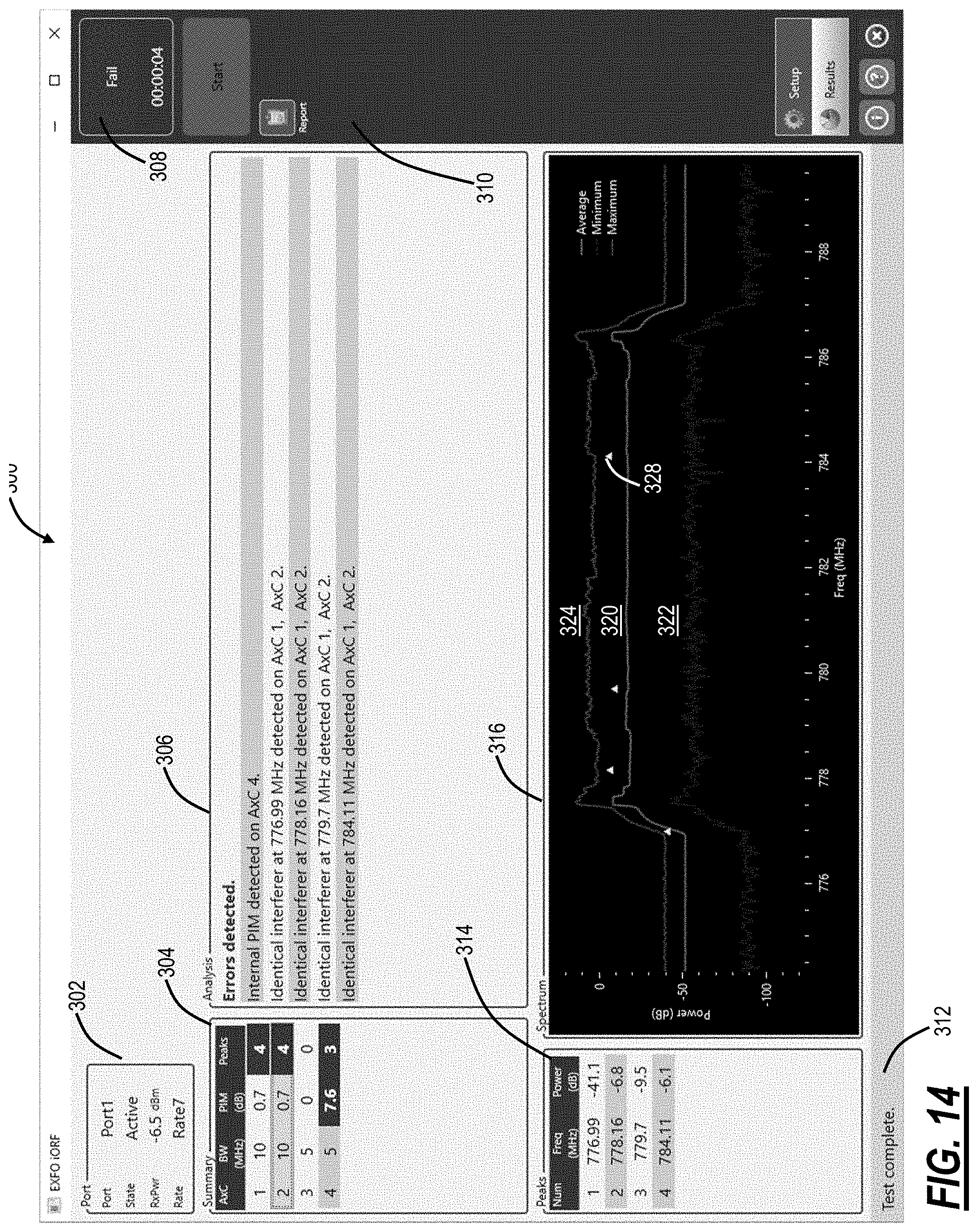
D00020
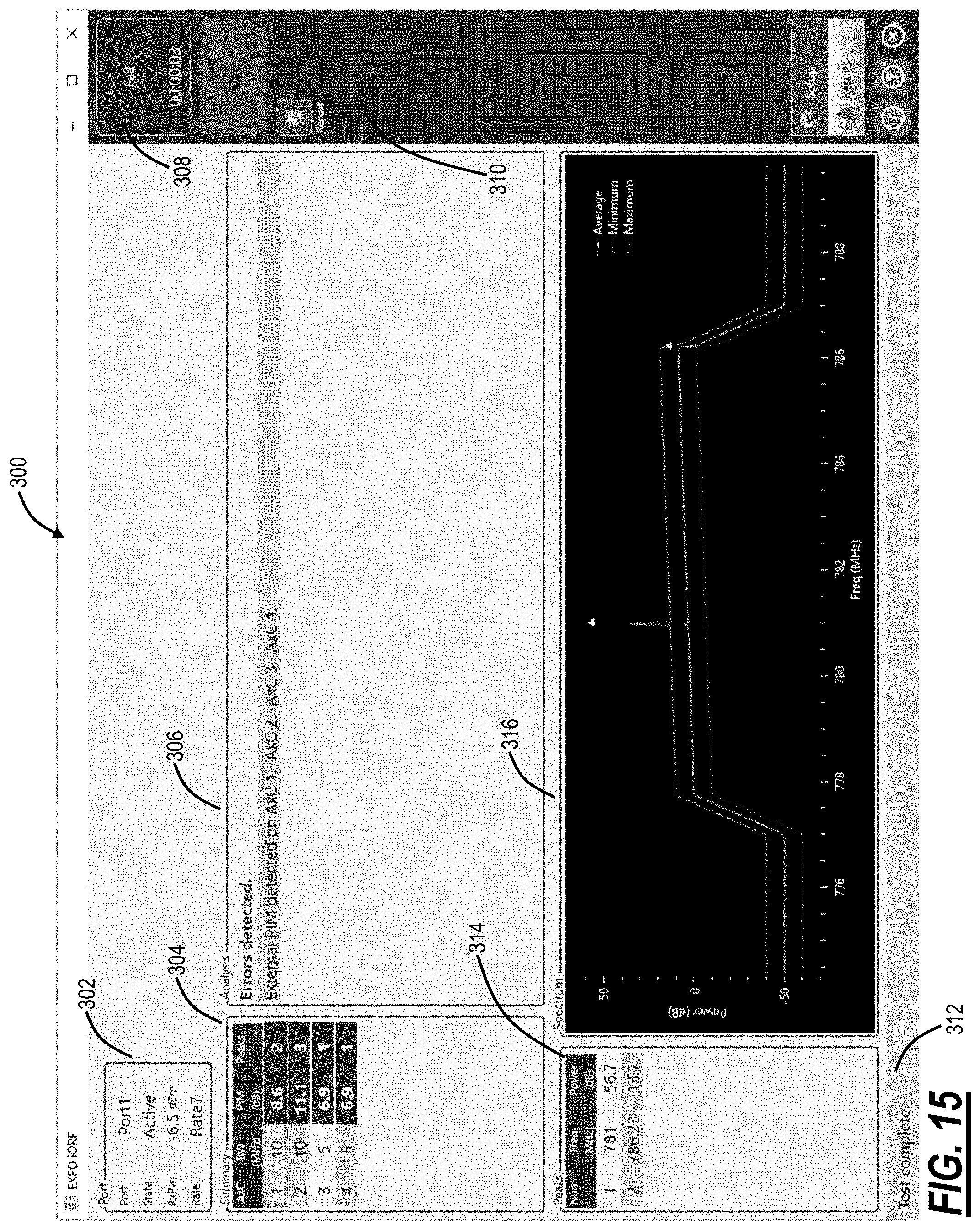
D00021

D00022

D00023

D00024
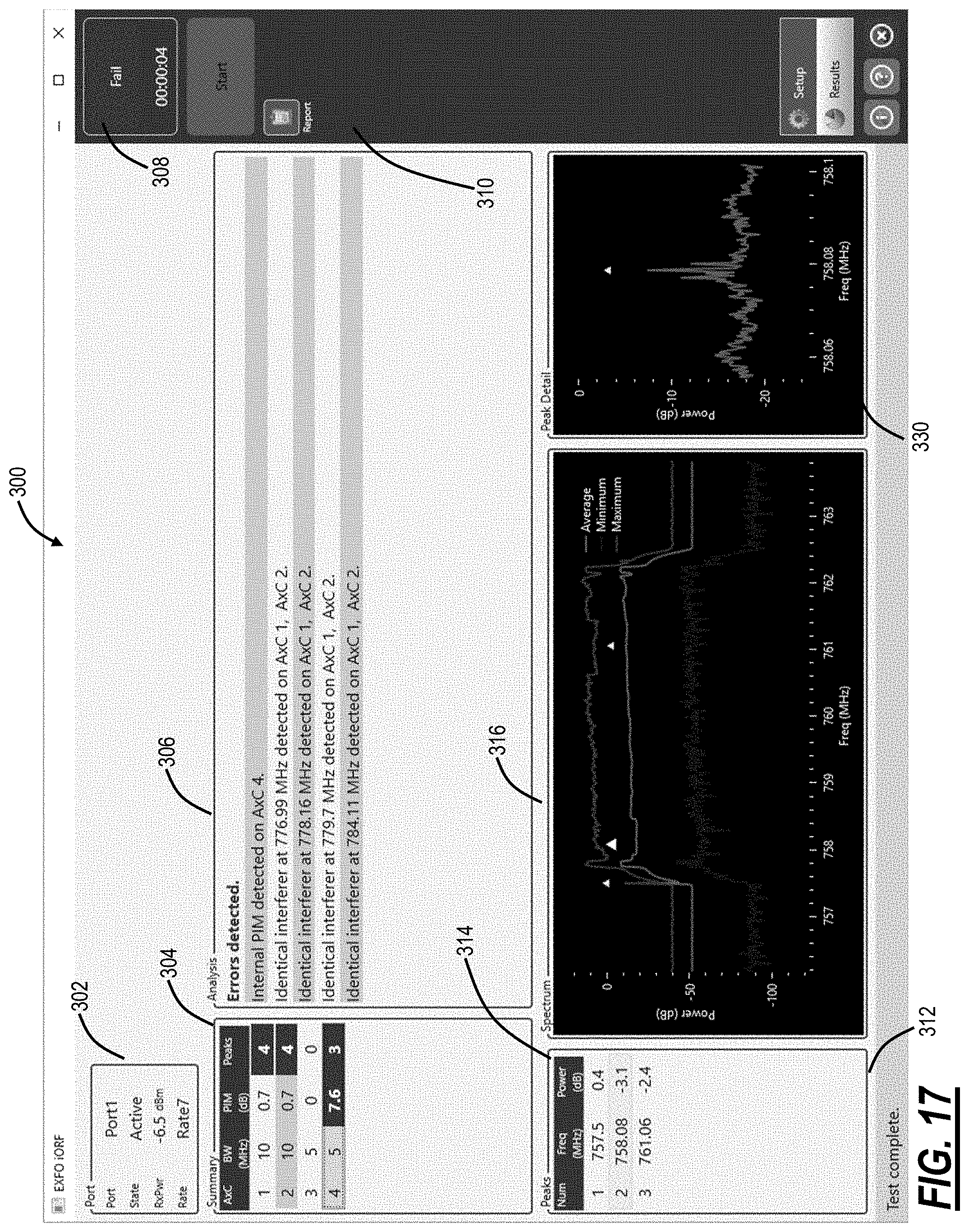
D00025

D00026
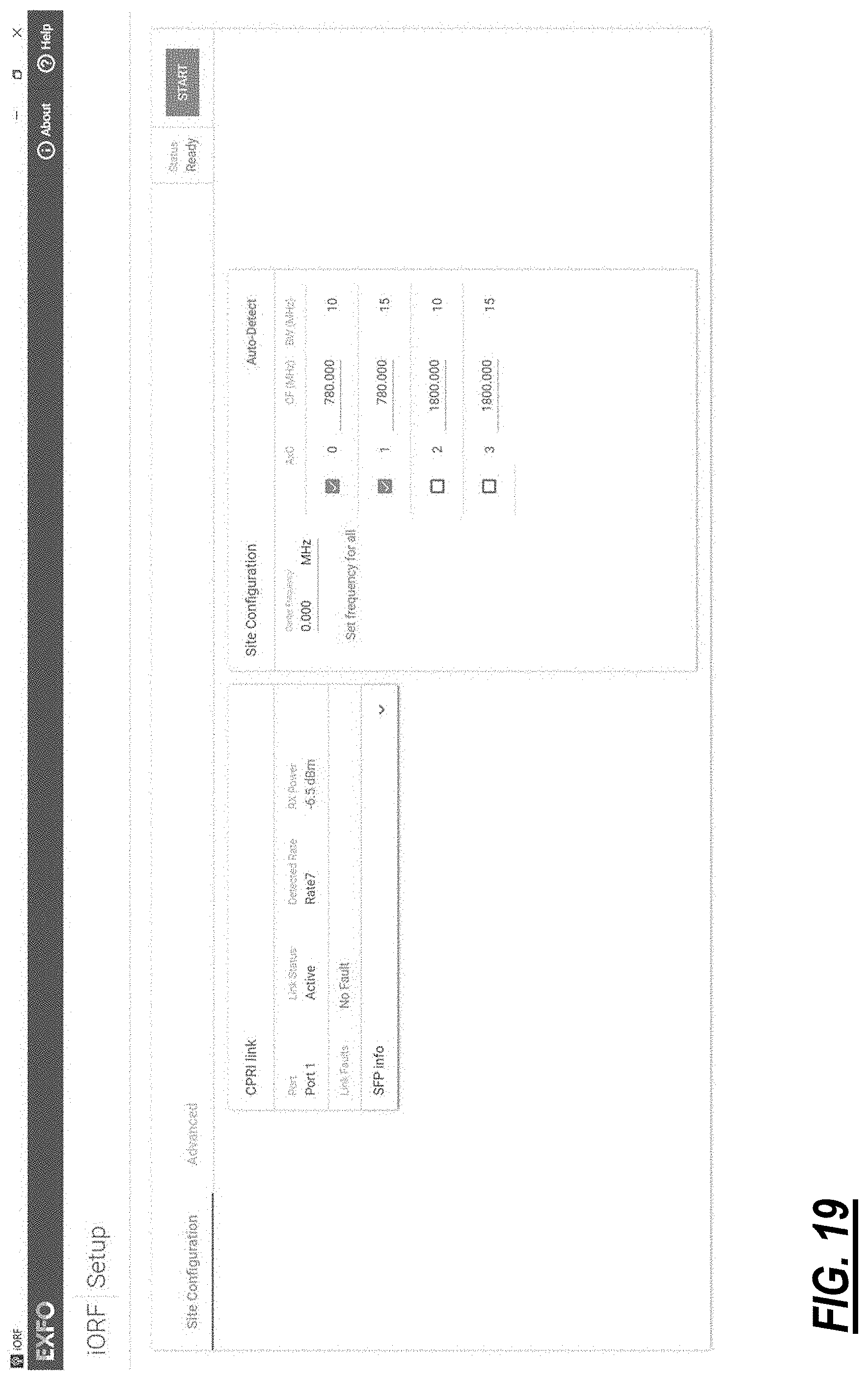
D00027

XML
uspto.report is an independent third-party trademark research tool that is not affiliated, endorsed, or sponsored by the United States Patent and Trademark Office (USPTO) or any other governmental organization. The information provided by uspto.report is based on publicly available data at the time of writing and is intended for informational purposes only.
While we strive to provide accurate and up-to-date information, we do not guarantee the accuracy, completeness, reliability, or suitability of the information displayed on this site. The use of this site is at your own risk. Any reliance you place on such information is therefore strictly at your own risk.
All official trademark data, including owner information, should be verified by visiting the official USPTO website at www.uspto.gov. This site is not intended to replace professional legal advice and should not be used as a substitute for consulting with a legal professional who is knowledgeable about trademark law.