System and Method for Attack Detection in Wireless Beacon Systems
Chan; Chun Fai Aldar ; et al.
U.S. patent application number 16/233285 was filed with the patent office on 2020-07-02 for system and method for attack detection in wireless beacon systems. The applicant listed for this patent is Logistics and Supply Chain MultiTech R&D Centre Limited. Invention is credited to Chun Fai Aldar Chan, Man Hon Chung.
| Application Number | 20200211350 16/233285 |
| Document ID | / |
| Family ID | 71124402 |
| Filed Date | 2020-07-02 |
View All Diagrams
| United States Patent Application | 20200211350 |
| Kind Code | A1 |
| Chan; Chun Fai Aldar ; et al. | July 2, 2020 |
System and Method for Attack Detection in Wireless Beacon Systems
Abstract
A system and a method for attack detection includes a constellation of beacons, wherein each beacon is adapted to broadcast a unique beacon identification code (beacon ID); a terminal device adapted to receive a user trace of beacon IDs, and send a query to a backend server or routing device to determine an occurrence of an intrusion via a network; wherein the backend server is adapted to determine an occurrence of an intrusion by carrying out the steps of: computing spatial relational metrics between beacon devices; transforming beacon IDs as states of a Markov chain model, and estimating state transition probabilities based on the spatial relational metrics; recording user traces of beacon ID transitions when terminal device make queries; and running hypothesis test on the user traces against the Markov chain model to determine a status of intrusion.
| Inventors: | Chan; Chun Fai Aldar; (Pok Fu Lam, HK) ; Chung; Man Hon; (Pok Fu Lam, HK) | ||||||||||
| Applicant: |
|
||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|
| Family ID: | 71124402 | ||||||||||
| Appl. No.: | 16/233285 | ||||||||||
| Filed: | December 27, 2018 |
| Current U.S. Class: | 1/1 |
| Current CPC Class: | G06K 9/6297 20130101; H04W 4/80 20180201; G08B 13/2451 20130101; H04W 76/11 20180201; H04W 40/244 20130101; G06F 17/18 20130101 |
| International Class: | G08B 13/24 20060101 G08B013/24; G06F 17/18 20060101 G06F017/18; G06K 9/62 20060101 G06K009/62; H04W 40/24 20060101 H04W040/24; H04W 76/11 20060101 H04W076/11; H04W 4/80 20060101 H04W004/80 |
Claims
1. A system for attack detection for a constellation of beacons, wherein each beacon is adapted to broadcast a unique beacon identification code (beacon ID), comprising a backend server or routing device, adapted to record a user trace of beacon IDs from queries sent by terminal devices, to determine an occurrence of an intrusion via a network; wherein the backend server is adapted to determine an occurrence of an intrusion by carrying out the steps of: computing spatial relational metrics between beacon devices; transforming beacon IDs as states of a Markov chain model, and estimating state transition probabilities based on the spatial relational metrics; recording user traces of beacon ID transitions when terminal device makes queries for location- or item-based content or services; and running hypothesis test on the user traces against the Markov chain model to determine a status of intrusion.
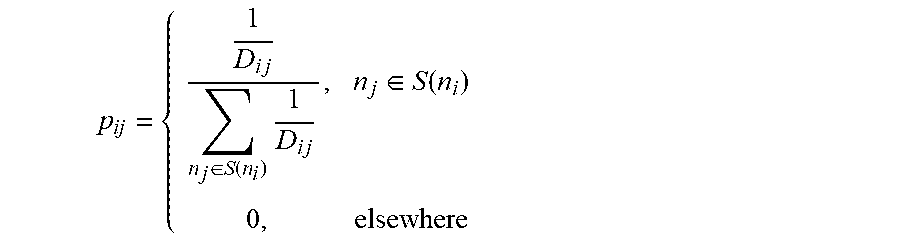
2. The system of claim 1, wherein the step of estimating state transition probabilities comprises the steps of: selecting a granularity resolution; fitting Hilbert curve to the beacon constellation and computing the Hilbert value for different beacons; defining a boundary limit B; for each beacon n.sub.i, selecting all n.sub.j with |h(n.sub.j)-h(n.sub.i)|.ltoreq.B, denoted by S(n.sub.i), and computing the sum D of 1/|h(n.sub.i)-h(n.sub.j)| for all n.sub.j.di-elect cons.S(n.sub.i); for each n.sub.j.di-elect cons.S(n.sub.i), setting a transition probability P.sub.ij=1/(D|h(n.sub.j)-h(n.sub.i)|); determining if all n.sub.j.di-elect cons.S(n.sub.i) with p.sub.ij are set, then process to next step, otherwise loop back to the setting transition probability step; and determining if all N beacons with p.sub.ij, then halt, otherwise loop back to the computing the sum D of beacon n.sub.i step.
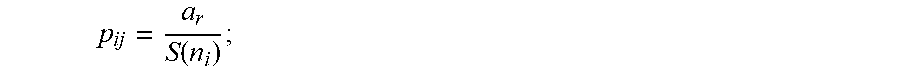
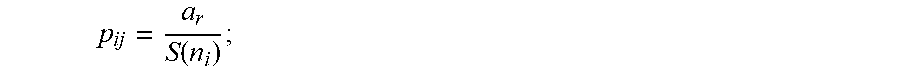
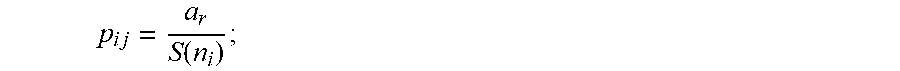
3. The system of claim 1, wherein the step of estimating state transition probabilities comprises the steps of: computing a Voronoi diagram mapping for the beacon constellation; determining a boundary value L; for each layer of cells, aassigning weight at r-th layer cells to be a.sub.r; for each beacon n, counting the number of neighbours X.sub.r in the r-th layer away, where 0<r.ltoreq.L; computing the sum S(n.sub.i)=a.sub.0X.sub.0+a.sub.1X.sub.1+ . . . +a.sub.LX.sub.L; for each n.sub.j in the r-th layer of neighbours of ni, assigning the transition probability p i j = a r S ( n i ) ; ##EQU00010## incrementing r; determining if r<L then returning to the assigning the transition probability p.sub.ij step, otherwise proceed to next step; and halting if the transition probabilities of all n beacons are set, otherwise returning to counting the number of neighbours step.
4. The system of claim 1, wherein the step of estimating state transition probabilities comprises the steps of: randomly wandering through the deployment of beacons; recording the user trace of beacon ID transitions, compute the statistics of the beacon distribution and the a posterior probability distribution; and assigning a transition probability between each pair of states.
5. The system of claim 4, wherein the step of assigning a transition probability comprises a step of using the user trace of beacon IDs are used to estimate the transition probabilities between pairs of beacon IDs.
6. The system of claim 4, wherein the step of assigning a transition probability comprises a step of using Bayesian statistical means to estimate the transition probabilities or machine learning such as deep neural network, etc. can be used to compute the transition probabilities.
7. The system of claim 4, wherein the step of assigning a transition probability comprises a step of assigning zero the probability value if no transition exists between two states.
8. The system of claim 1, wherein the status of intrusion comprises either one of: State H.sub.0: (c.sub.1, c.sub.2, . . . , c.sub.r, . . . , c.sub.T) being accepted trace distribution which fit to the Markov chain model where no intrusion is detected; or State H.sub.1 where intrusion or anomalous distribution of traces
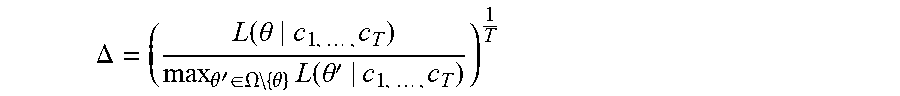
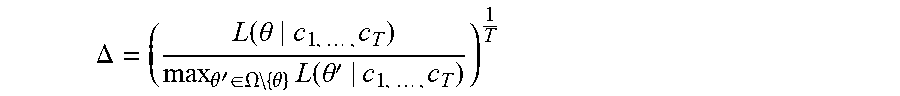
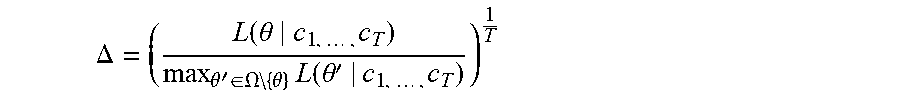
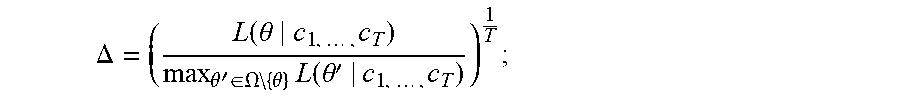
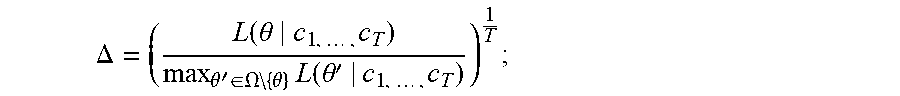
9. The system of claim 8, wherein the hypothesis test comprises the step of: deriving p.sub.ij(.theta.), where 1.ltoreq.i, j.ltoreq.N, as the transition probability from ID.sub.i to ID.sub.j for a n-state Markov chain with .theta. being the corresponding set of parameters, for all possible .theta. by .OMEGA.. for a received user trace C=(c.sub.1, . . . , c.sub.T), deriving a likelihood function as the conditional probability for C to occur given .theta., where L(.theta.|c.sub.1, . . . , c.sub.T)=.PI..sub.r=1.sup.T-1p.sub.c.sub.r.sub.c.sub.r+1 (q) computing the likelihood ratio as follows: .DELTA. = ( L ( .theta. c 1 , , c T ) max .theta. ' .di-elect cons. .OMEGA. { .theta. } L ( .theta. ' | c 1 , , c T ) ) 1 T ; ##EQU00011## and accepting H.sub.0 (with no intrusion detected) if .DELTA..gtoreq..lamda. where .lamda. is the threshold.
10. The system of claim 9, wherein the value of .lamda. is set through a Monte Carlo simulation or trial-and-error.
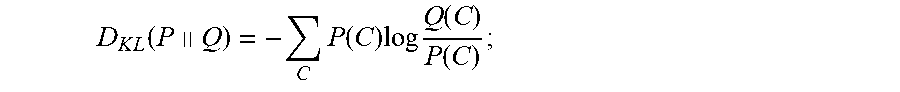
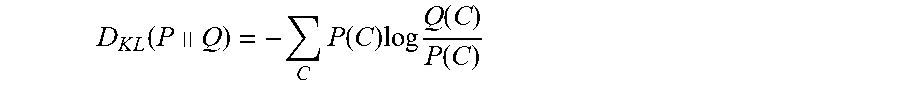
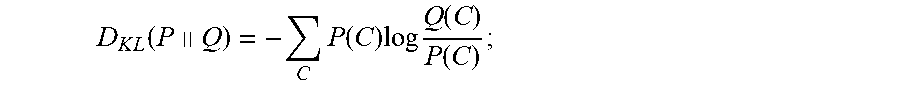
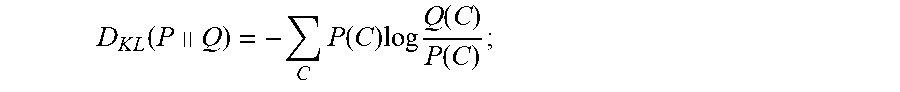
11. The system of claim 8, wherein the hypothesis test comprises the step of: collecting user traces of the same length and based on a set of user traces, estimate the probability distribution P(C) of the collected traces where C is a particular user trace; computing the reference probability distribution Q(C); computing a KLD, where D K L ( P .parallel. Q ) = - C P ( C ) log Q ( C ) P ( C ) ; ##EQU00012## and accept H.sub.0 if D.sub.KL (P||Q).ltoreq..xi. where .xi. is a threshold.
12. The system of claim 11, wherein the value of .xi. is set through a Monte Carlo simulation or trial-and-error.
13. A method for attack detection, comprising the steps of: computing spatial relational metrics between beacon devices at a backend server; transforming beacon IDs as states of a Markov chain model, and estimating state transition probabilities based on the spatial relational metrics at the backend server; receiving user traces of beacon ID transitions recorded from a terminal device; and running hypothesis test on the user traces against the Markov chain model to determine a status of intrusion at the backend server.
14. The method of claim 13, wherein the step of estimating state transition probabilities comprises the steps of: selecting a granularity resolution; fitting Hilbert curve to the beacon constellation and computing the Hilbert value for different beacons; defining a boundary limit B; for each beacon n.sub.i, selecting all n.sub.i with |h(n.sub.j)-h(n.sub.i)|.ltoreq.B, denoted by S(n.sub.i), and computing the sum D of 1/|h(n.sub.i)-h(n.sub.j)| for all n.sub.j.di-elect cons.S(n.sub.i); for each n.sub.j.di-elect cons.S(n.sub.i), setting a transition probability P.sub.ij=1/(D|h(n.sub.j)-h(n.sub.i)|); determining if all n.sub.j.di-elect cons.S(n.sub.i) with p.sub.ij are set, then process to next step, otherwise loop back to the setting transition probability step; and determining if all N beacons with p.sub.ij, then halt, otherwise loop back to the computing the sum D of beacon n.sub.i step.
15. The method of claim 13, wherein the step of estimating state transition probabilities comprises the steps of: computing a Voronoi diagram mapping for the beacon constellation; determining a boundary value L; for each layer of cells, aassigning weight at r-th layer cells to be a.sub.r; for each beacon n, counting the number of neighbours X.sub.r in the r-th layer away, where 0<r.ltoreq.L; computing the sum S(n.sub.i)=a.sub.0X.sub.0+a.sub.1X.sub.1+ . . . +a.sub.LX.sub.L; for each n.sub.j in the r-th layer of neighbours of ni, assigning the transition probability p i j = a r S ( n i ) ; ##EQU00013## incrementing r; determining if r<L then returning to the assigning the transition probability p.sub.ij step, otherwise proceed to next step; and halting if the transition probabilities of all n beacons are set, otherwise returning to counting the number of neighbours step.
16. The method of claim 13, wherein the step of estimating state transition probabilities comprises the steps of: randomly wandering through the deployment of beacons; recording the user trace of beacon ID transitions, compute the statistics of the beacon distribution and the a posterior probability distribution; and assigning a transition probability between each pair of states.
17. The system of claim 16, wherein the step of assigning a transition probability comprises a step of using the user trace of beacon IDs are used to estimate the transition probabilities between pairs of beacon IDs.
18. The system of claim 16, wherein the step of assigning a transition probability comprises a step of using Bayesian statistical means or through machine learning algorithms to estimate the transition probabilities.
19. The system of claim 16, wherein the step of assigning a transition probability comprises a step of assigning zero the probability value if no transition exists between two states.
20. The system of claim 13, wherein the status of intrusion comprises either one of: State H.sub.0: (c.sub.1, c.sub.2, . . . , c.sub.r, . . . , c.sub.T) conforming to the baseline Markov chain model; or State H.sub.1 where intrusion or anomalous distribution
21. The system of claim 19, wherein the hypothesis test comprises the step of: deriving p.sub.ij(.theta.), where 1.ltoreq.i, j.ltoreq.N, as the transition probability from ID.sub.i to ID.sub.j for a n-state Markov chain with .theta. being the corresponding set of parameters, for all possible .theta. by .OMEGA.. for a received user trace C=(c.sub.1, . . . , c.sub.T), deriving a likelihood function as the conditional probability for C to occur given .theta., where L(.theta.|c.sub.1, . . . , c.sub.T)=.PI..sub.r=1.sup.T-1p.sub.c.sub.r.sub.c.sub.r+1 (q) computing the likelihood ratio as follows: .DELTA. = ( L ( .theta. c 1 , , c T ) max .theta. ' .di-elect cons. .OMEGA. { .theta. } L ( .theta. ' | c 1 , , c T ) ) 1 T ; ##EQU00014## and accepting H.sub.0 (with no intrusion detected) if .DELTA..gtoreq..lamda. where .lamda. is the threshold.
22. The system of claim 21, wherein the value of .lamda. is set through a Monte Carlo simulation or trial-and-error.
23. The system of claim 19, wherein the hypothesis test comprises the step of: collecting user traces of the same length and based on a set of user traces, estimate the probability distribution P(C) of the collected traces where C is a particular user trace; computing the reference probability distribution Q(C); computing a KLD, where D K L ( P .parallel. Q ) = - C P ( C ) log Q ( C ) P ( C ) ; ##EQU00015## and accept H.sub.0 if D.sub.KL (P||Q).ltoreq..xi. where .xi. is a threshold.
24. The system of claim 21, wherein the value of .lamda. is set through a Monte Carlo simulation or trial-and-error.
25. An intrusion detection device carrying a method comprising the steps of: computing a Markov chain based probability distribution for acceptable traces of beacon IDs reported from the terminal device as it queries for location based services or content; verifying through a hypothesis test to determine whether the received trace of beacon IDs is outside an acceptable value range of the Markov chain based probability distribution. in the event that a trace of beacon IDs is outside the acceptable value range, generating a signal indicating that an intrusion occurs.
26. An intrusion detection device of claim 25, wherein the Markov chain based probability distribution is predetermined through Hilbert value, VORONOI diagram or field test with Bayesian statistics or machine learning through DNN.
Description
TECHNICAL FIELD
[0001] The present invention relates to a system and methods for attack detection in wireless beacon systems, and more particularly to system and methods for attack detection in Bluetooth Low Energy (BLE) beacon systems.
BACKGROUND
[0002] Beacons are starting to be deployed to provide micro-location information to receivers, which in-turn, can be used to invoke location-based applications. For example, beacons (BLE, iBeacon, etc.) tag physical objects and locations economically, with active broadcasts to facilitate contextualized, customized content or services to be delivered to users' mobile devices. Beacon identification (ID) picked up by user devices would guide them to look up and download detailed information of the tagged object. Correct content and service delivery hinges on that beacons are deployed correctly according to a prescribed constellation mapping beacon IDs. However, the correct operation of beacon technology could be disrupted by cyber or physical threats, that is, spoofing attacks and re-shuffling attacks respectively.
[0003] Shuffling beacons leads to "wrong" spatially-specific information to user devices. Typically, beacon IDs should be available to all people to guide them to look up correct content. But this also undesirably makes the job of the attacker easier. There is no defence mechanism available to protect beacons from shuffling attack. A spoofing attack eavesdrops (lunch-time attack vs. adaptive query) all beacon IDs and plays them back at wrong locations. A more sophisticated attack could craft the beacon data before retransmission.
SUMMARY
[0004] In one aspect of the present invention there is provided a system for attack detection, comprising:
[0005] a constellation of beacons, wherein each beacon is adapted to broadcast a unique beacon identification code (beacon ID);
[0006] a terminal device adapted to receive beacon IDs, and send a query to a backend server or routing device to record and keep traces of the beacon IDs; [0007] wherein the backend server is adapted to determine an occurrence of an intrusion by carrying out the steps of: [0008] computing spatial relational metrics between beacon devices; [0009] transforming beacon IDs as states of a Markov chain model, and estimating state transition probabilities based on the spatial relational metrics; [0010] recording user traces of beacon ID transitions when terminal device makes queries; [0011] running hypothesis test on the user traces against the Markov chain model to determine a status of intrusion.
[0012] Preferably, the step of estimating state transition probabilities comprises the steps of:
[0013] selecting a granularity resolution;
[0014] fitting Hilbert curve to the beacon constellation and computing the Hilbert value for different beacons;
[0015] defining a boundary limit B;
[0016] for each beacon n.sub.i, selecting all n.sub.j with |h(.sub.j-h(n.sub.i)|.ltoreq.B, denoted by S(n.sub.i), and computing the sum D of 1/|h(n.sub.i)-h(n.sub.j)| for all n.sub.j.di-elect cons.S(n.sub.i);
[0017] for each n.sub.j.di-elect cons.S(n.sub.i), setting a transition probability P.sub.ij=1/(D|h(n.sub.j)-h(n.sub.i)|);
[0018] determining if all n.sub.j.di-elect cons.S(n.sub.i) with p.sub.ij are set, then process to next step, otherwise loop back to the setting transition probability step;
[0019] determining if all N beacons with p.sub.ij, then halt, otherwise loop back to the computing the sum D of beacon n.sub.i step.
[0020] Preferably, the step of estimating state transition probabilities comprises the steps of:
[0021] computing a Voronoi diagram mapping for the beacon constellation;
[0022] determining a boundary value L;
[0023] for each layer of cells, aassigning weight at r-th layer cells to be a.sub.r;
[0024] for each beacon n, counting the number of neighbours X.sub.r in the r-th layer away, where 0<r.ltoreq.L;
[0025] computing the sum S(n.sub.i)=a.sub.0X.sub.0+a.sub.1X.sub.1+ . . . +a.sub.LX.sub.L;
[0026] for each n.sub.j in the r-th layer of neighbours of ni, assigning the transition probability
p ij = a r S ( n i ) ; ##EQU00001##
[0027] incrementing r;
[0028] determining if r<L then returning to the assigning the transition probability p.sub.ij step, otherwise proceed to next step;
[0029] halting if the transition probabilities of all n beacons are set, otherwise returning to counting the number of neighbours step.
[0030] Preferably, the step of estimating state transition probabilities comprises the steps of:
[0031] randomly wandering through the deployment of beacons;
[0032] recording the user trace of beacon ID transitions, computing the statistics of the beacon distribution and the a posterior probability distribution,
[0033] assigning a transition probability between each pair of states.
[0034] Preferably, the step of assigning a transition probability comprises a step of using the user trace of beacon IDs to estimate the transition probabilities between pairs of beacon IDs.
[0035] Preferably, the step of assigning a transition probability comprises a step of using Bayesian statistical means to estimate the transition probabilities or machine learning such as deep neural network, etc. can be used to compute the transition probabilities.
[0036] Preferably, the step of assigning a transition probability comprises a step of assigning zero the probability value if no transition exists between two states.
[0037] Preferably, the status of intrusion comprises either one of:
[0038] State H.sub.0: (c.sub.1, c.sub.2, . . . , c.sub.r, . . . , c.sub.T) conforming to the baseline Markov chain model; or
[0039] State H.sub.1 where intrusion or anomalous distribution.
[0040] Preferably, the hypothesis test comprises the step of:
[0041] deriving p.sub.ij(.theta.), where 1.ltoreq.i, j.ltoreq.N, as the transition probability from ID.sub.i to ID.sub.j for a n-state Markov chain with .theta. being the corresponding set of parameters, for all possible .theta. by .OMEGA..
[0042] for a received user trace C=(c.sub.1, . . . , c.sub.T), deriving a likelihood function as the conditional probability for C to occur given .theta., where
L(.theta.| c.sub.1, . . . , c.sub.T)=.PI..sub.r=1.sup.T-1p.sub.c.sub.r.sub.c.sub.r+1 (q)
[0043] computing the likelihood ratio as follows:
.DELTA. = ( L ( .theta. c 1 , , c T ) max .theta. ' .di-elect cons. .OMEGA. { .theta. } L ( .theta. ' | c 1 , , c T ) ) 1 T ##EQU00002##
[0044] accepting H.sub.0 (with no intrusion detected) if .DELTA..gtoreq..lamda. where .lamda. is the threshold.
[0045] Preferably, the value of .lamda. is set through a Monte Carlo simulation or trial-and-error.
[0046] Preferably, the hypothesis test comprises the step of:
[0047] collecting user traces of the same length and based on a set of user traces, estimate the probability distribution P(C) of the collected traces where C is a particular user trace;
[0048] computing the reference probability distribution Q(C);
[0049] computing a Kullback-Leibler Divergence, where
D K L ( P .parallel. Q ) = - C P ( C ) log Q ( C ) P ( C ) ; ##EQU00003##
and
[0050] accept H.sub.0 if D.sub.KL(P||Q).ltoreq..xi. where .xi. is a threshold.
[0051] Preferably, the value of .xi. is set through a Monte Carlo simulation or trial-and-error.
[0052] In another aspect of the present invention, there is provided a method for attack detection, comprising the steps of:
[0053] computing spatial relational metrics between beacon devices at a backend server;
[0054] transforming beacon IDs as states of a Markov chain model, and estimating state transition probabilities based on the spatial relational metrics at the backend server;
[0055] receiving user traces of beacon ID transitions recorded from a terminal device;
[0056] running hypothesis test on the user traces against the Markov chain model to determine a status of intrusion at the backend server.
[0057] Preferably, the present invention provides a system and method for attack detection in wireless beacon systems, and an improvement of attack detection method in a constellation of beacons.
[0058] Preferably, the system and method for attack detection in wireless beacon systems do not require any modification of any beacon in the constellation of beacons.
[0059] In another aspect of the present invention, there is provided an intrusion detection device carrying a method comprising the steps of:
[0060] computing a Markov chain based probability distribution for acceptable traces of beacon IDs reported from the terminal device as it queries for location based services or content;
[0061] verifying through a hypothesis test to determine whether the received trace of beacon IDs is outside an acceptable value range of the Markov chain based probability distribution.
[0062] in the event that a trace of beacon IDs is outside the acceptable value range, generating a signal indicating that an intrusion occurs.
[0063] Preferably, the Markov chain based probability distribution is predetermined through Hilbert value, VORONOI diagram or field test with Bayesian statistics or machine learning through DNN.
[0064] Other advantages will become apparent when taken into consideration with the following specification and drawings.
[0065] The embodiments of the present invention also overcome or ameliorate at least one of the disadvantages of the prior art, or to provide a useful alternative.
BRIEF DESCRIPTION OF THE DRAWINGS
[0066] Features and advantages of the present invention will become apparent from the following description of embodiments thereof, by way of example only, with reference to the accompanying drawings, in which:
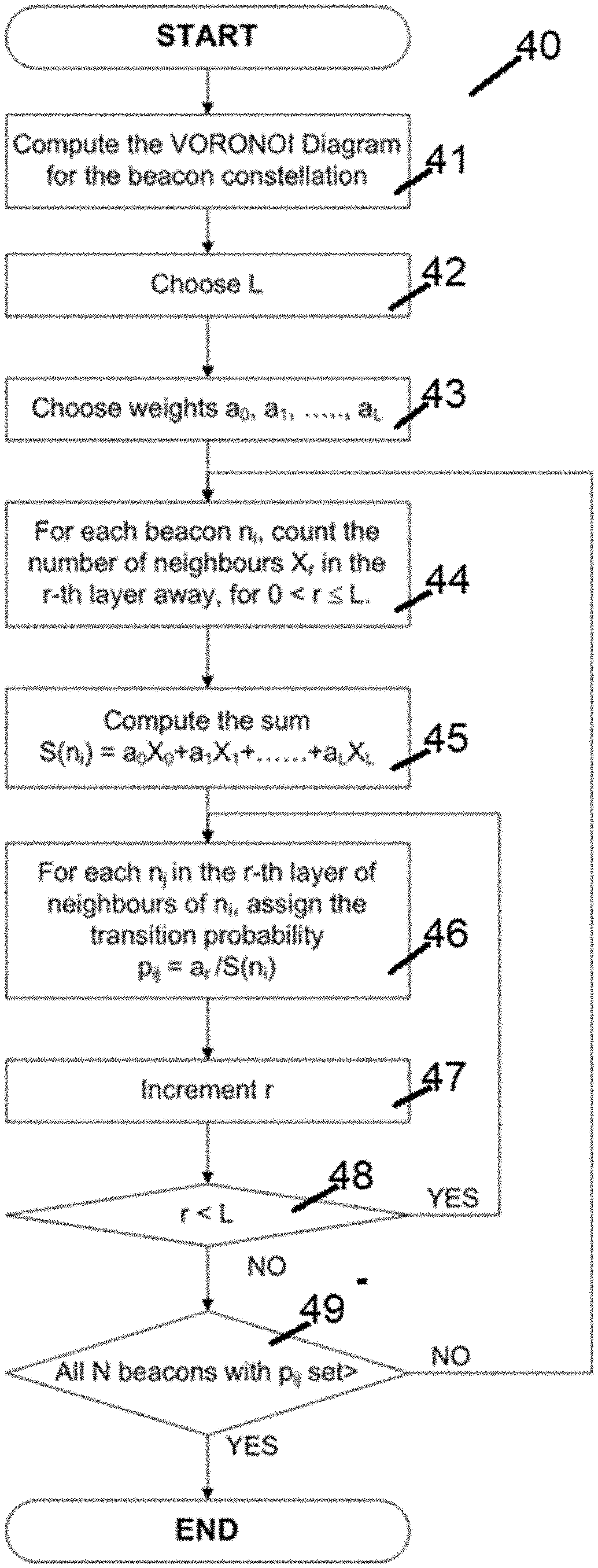
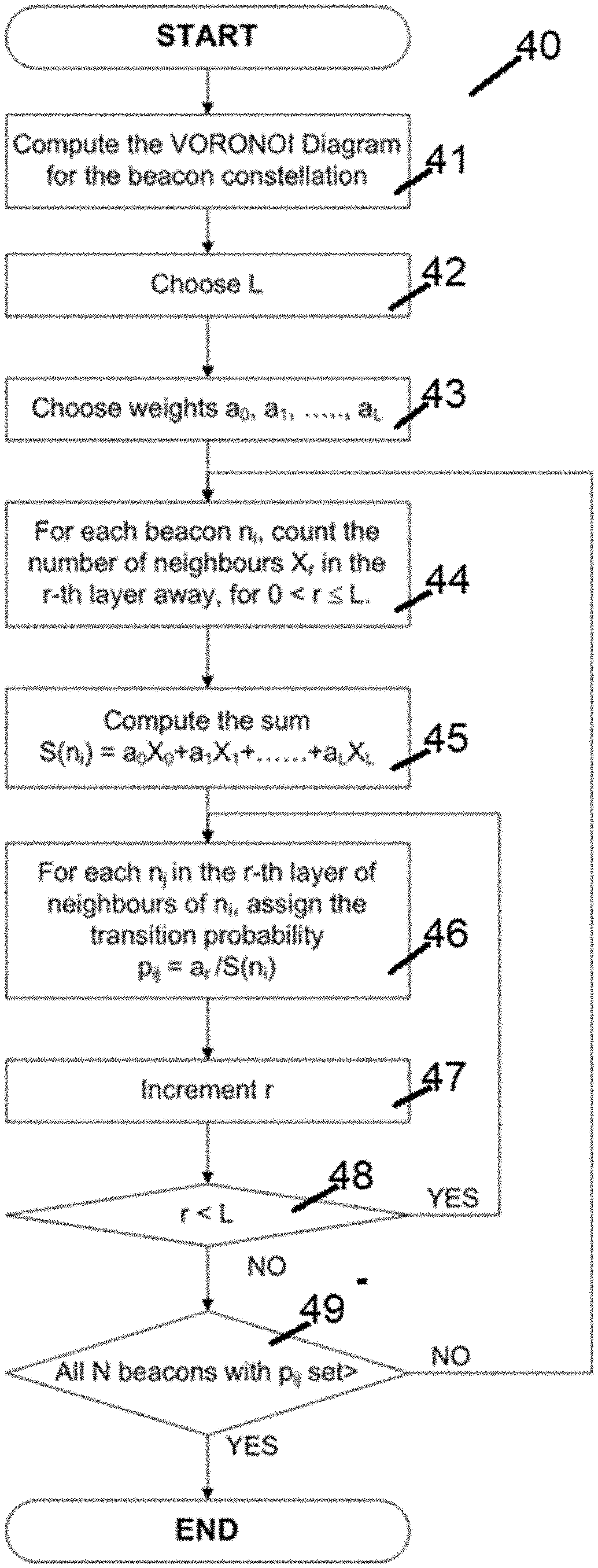
[0067] FIG. 1 shows a schematic diagram of a method for attack detection in wireless beacon systems according to an embodiment of the present invention;
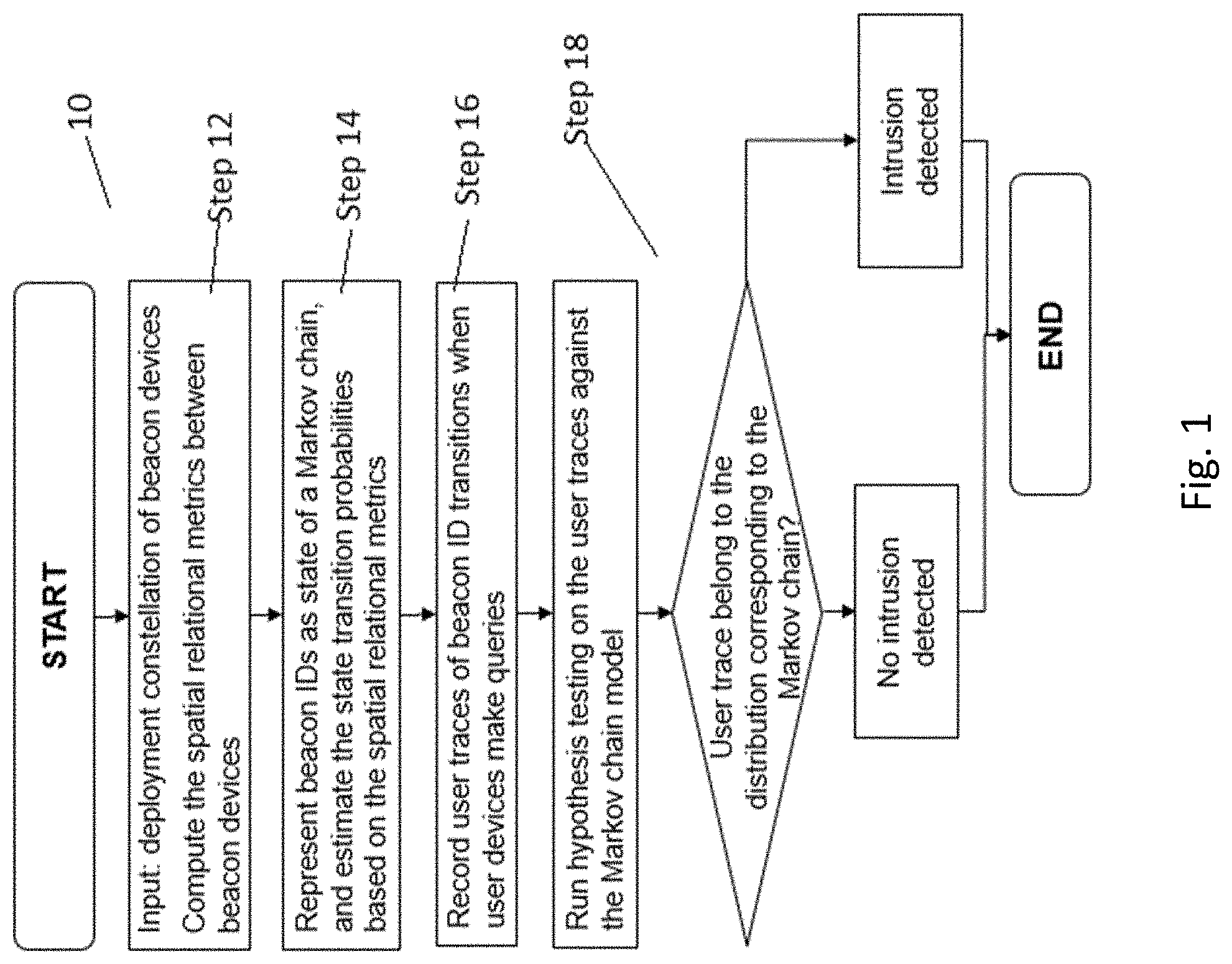
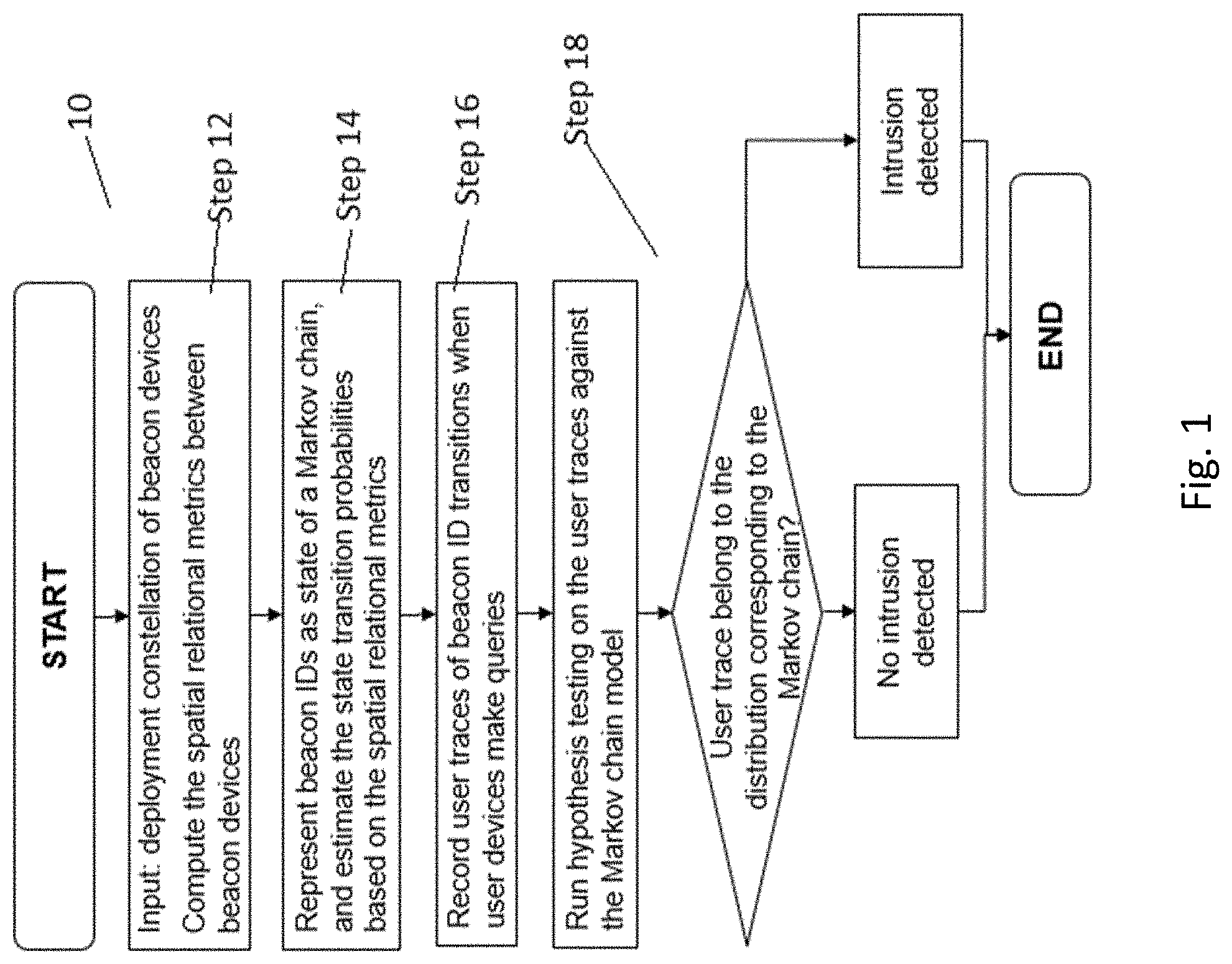
[0068] FIG. 2 shows a schematic diagram of a Markov chain model generated by the method shown in FIG. 1;
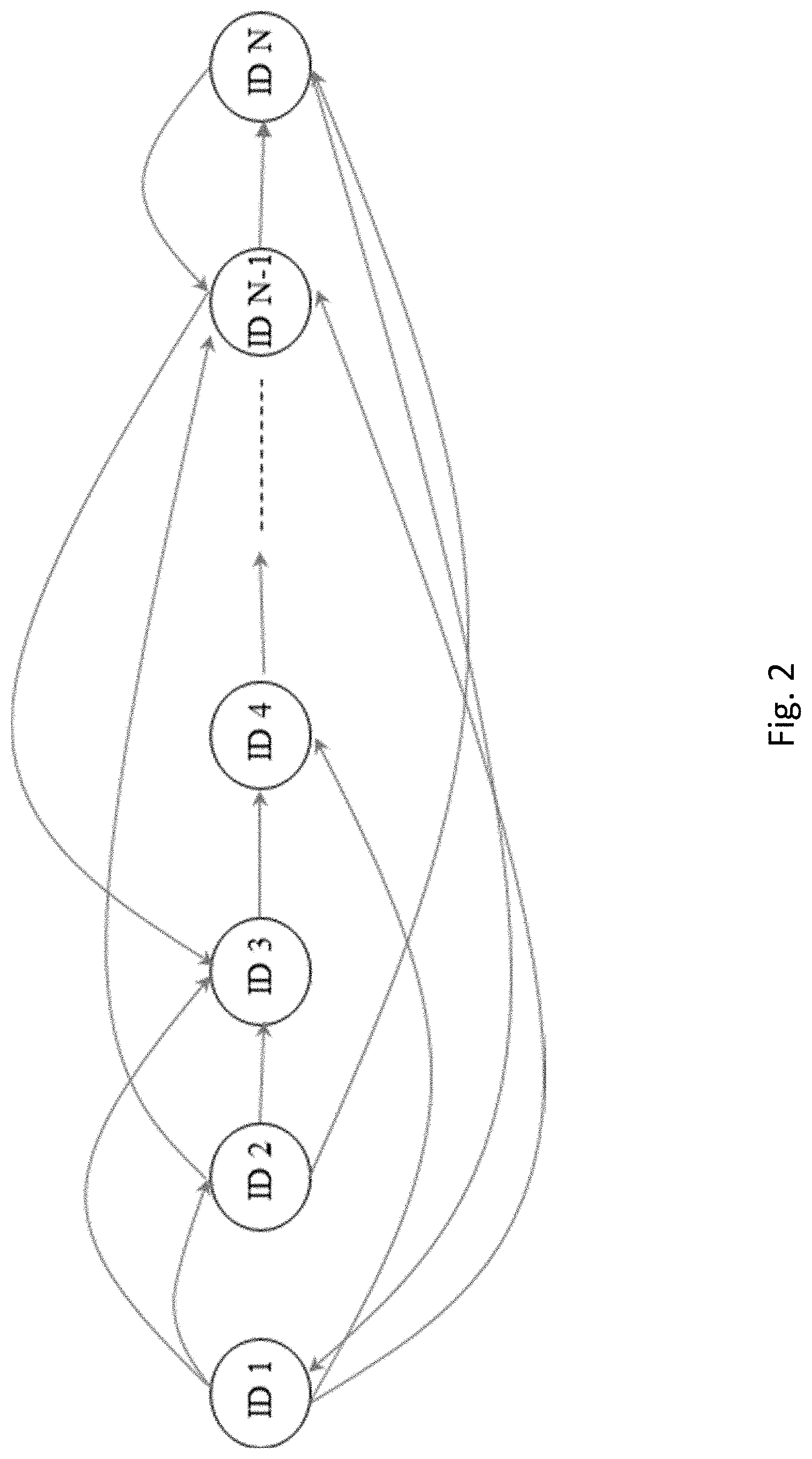
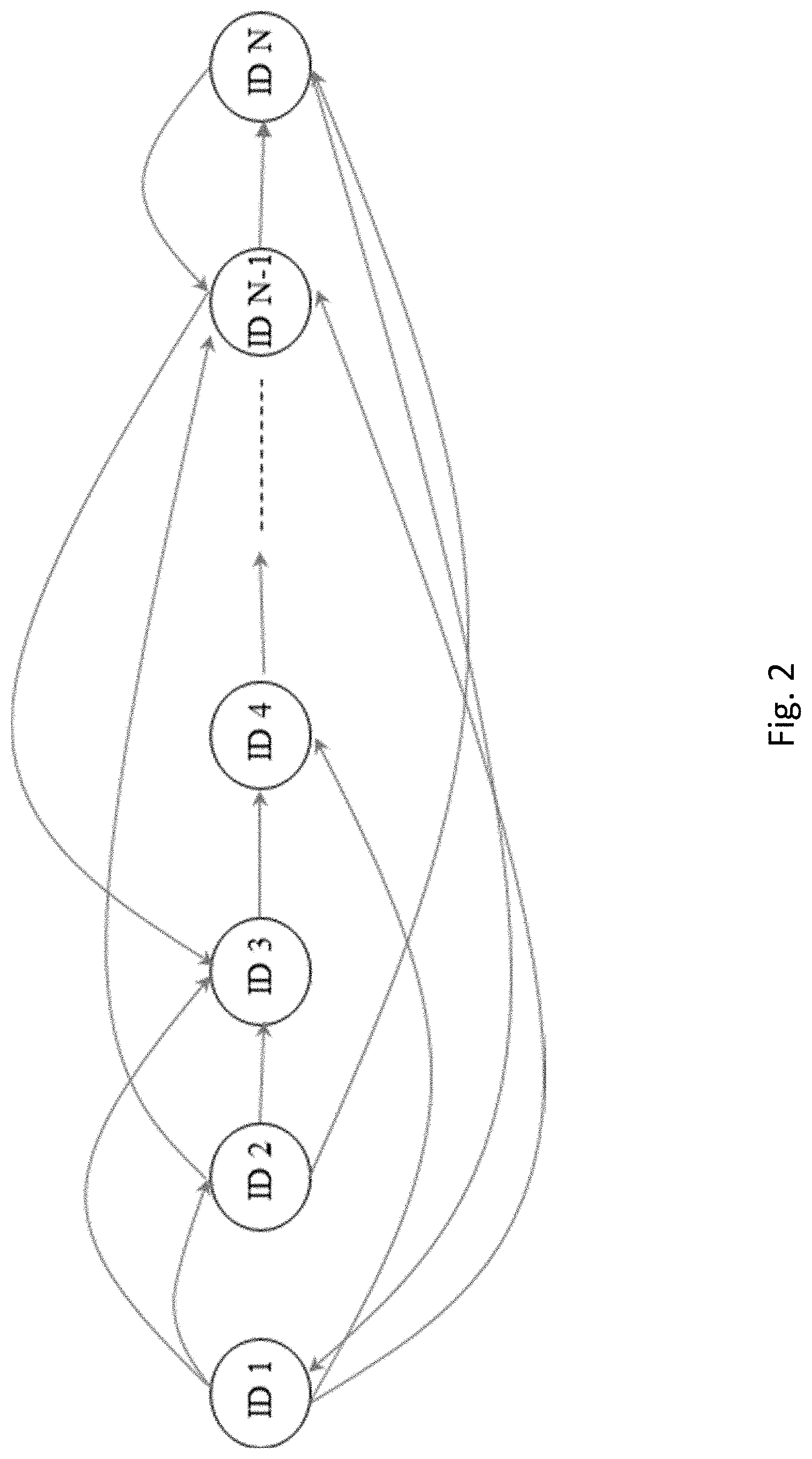
[0069] FIG. 3 shows a schematic diagram of a method for generating state transition probabilities for the Markov chain model shown in FIG. 2;
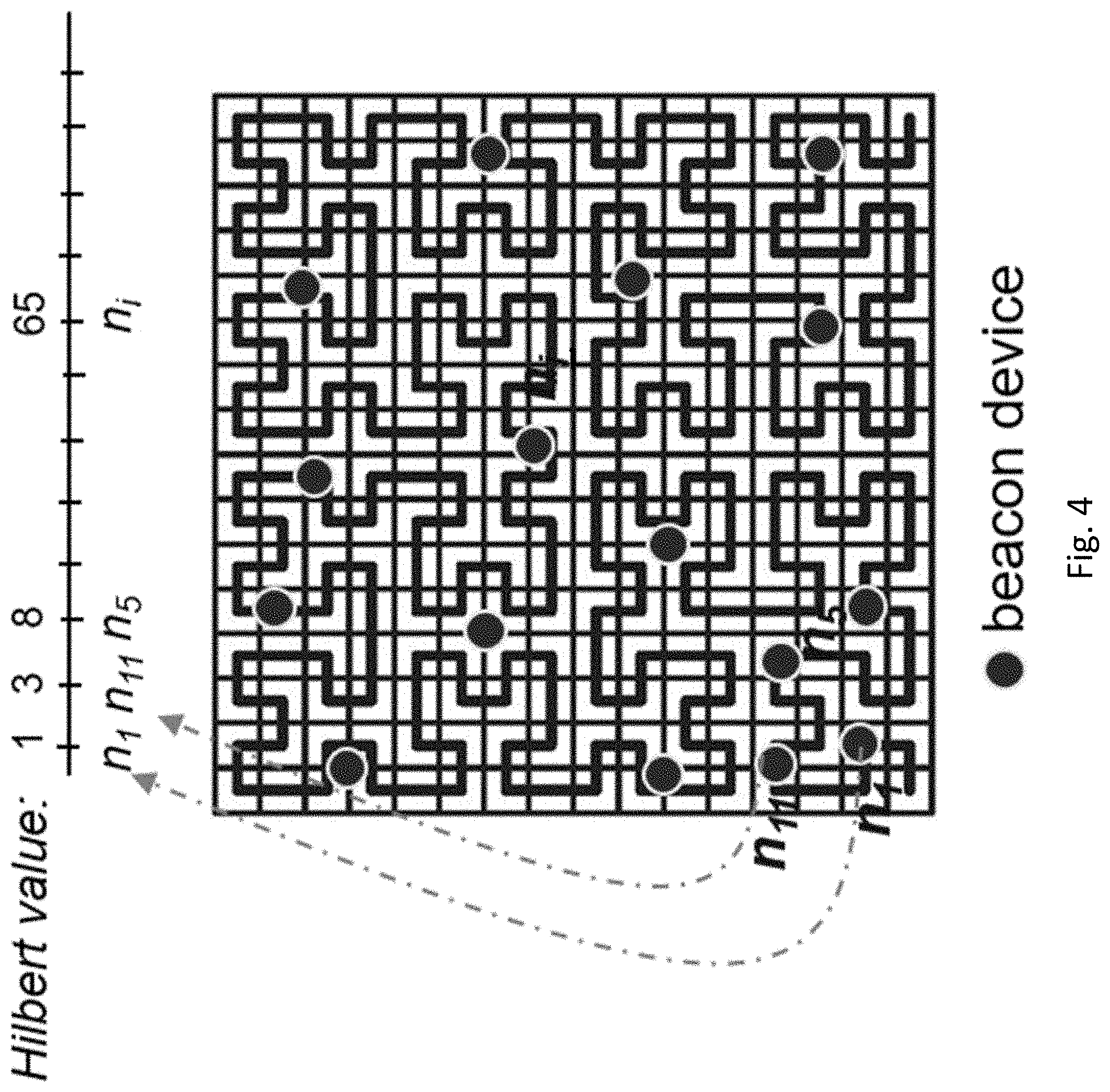
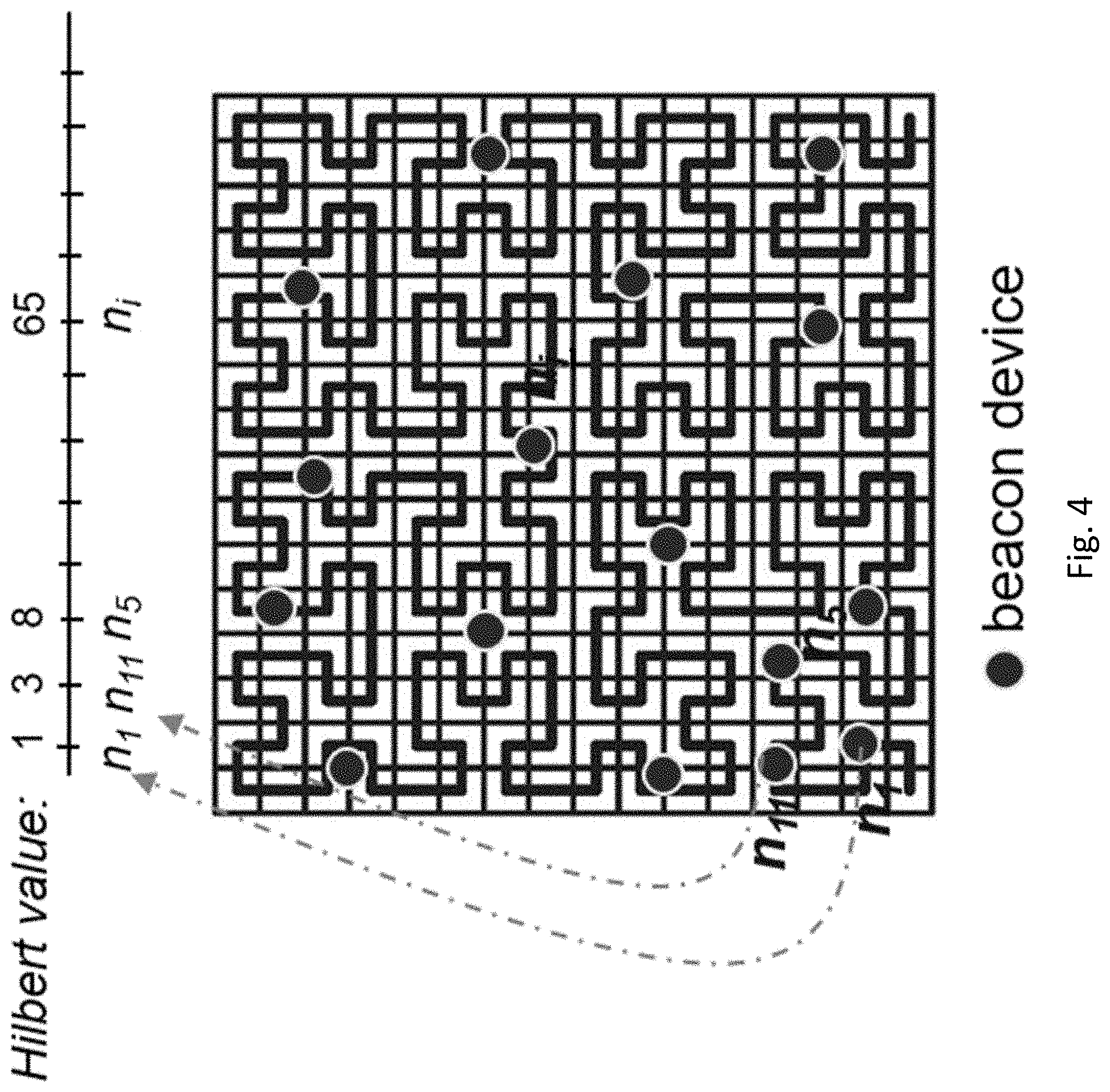
[0070] FIG. 4 shows a schematic diagram of a graphical representation of the method shown in FIG. 3;
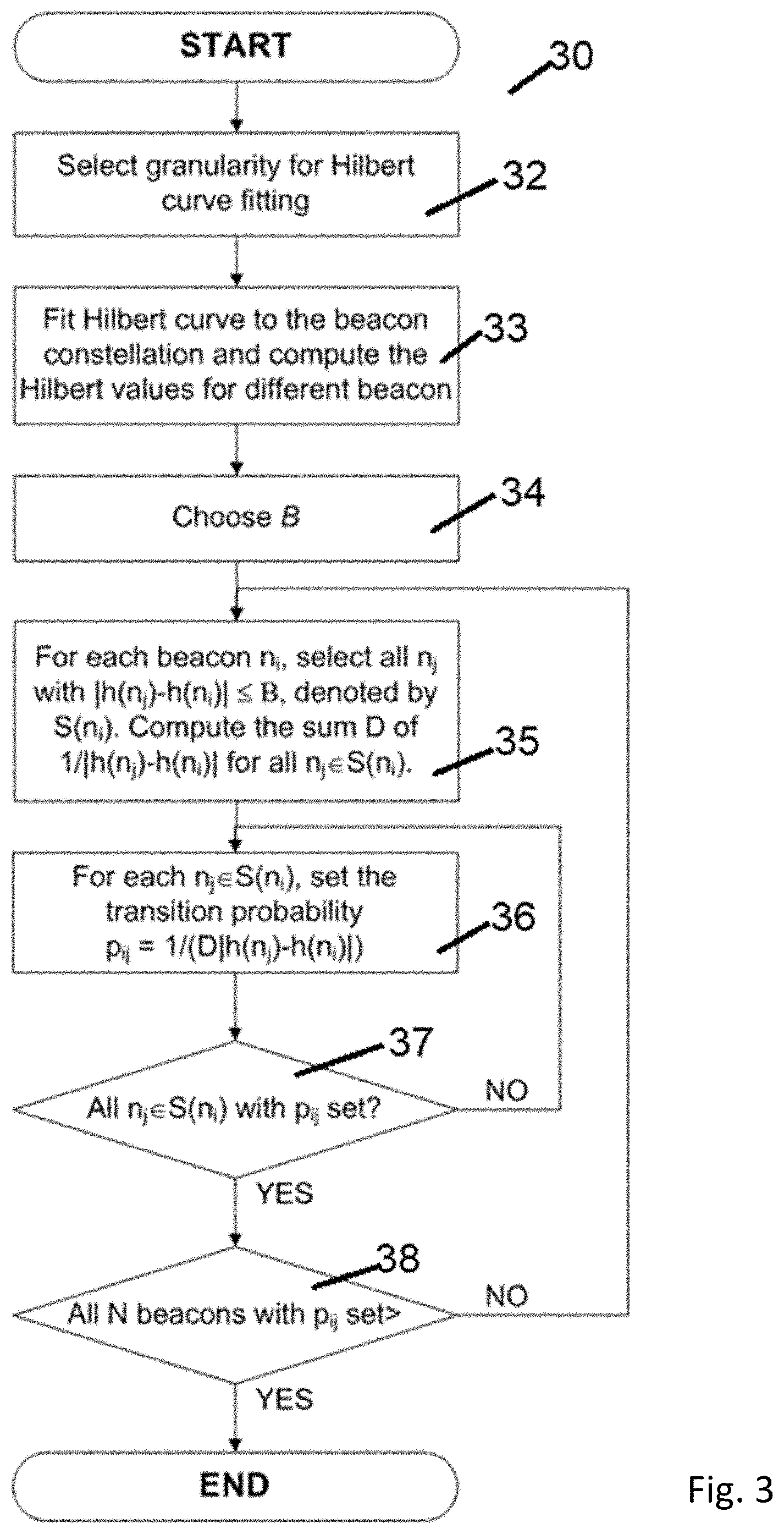
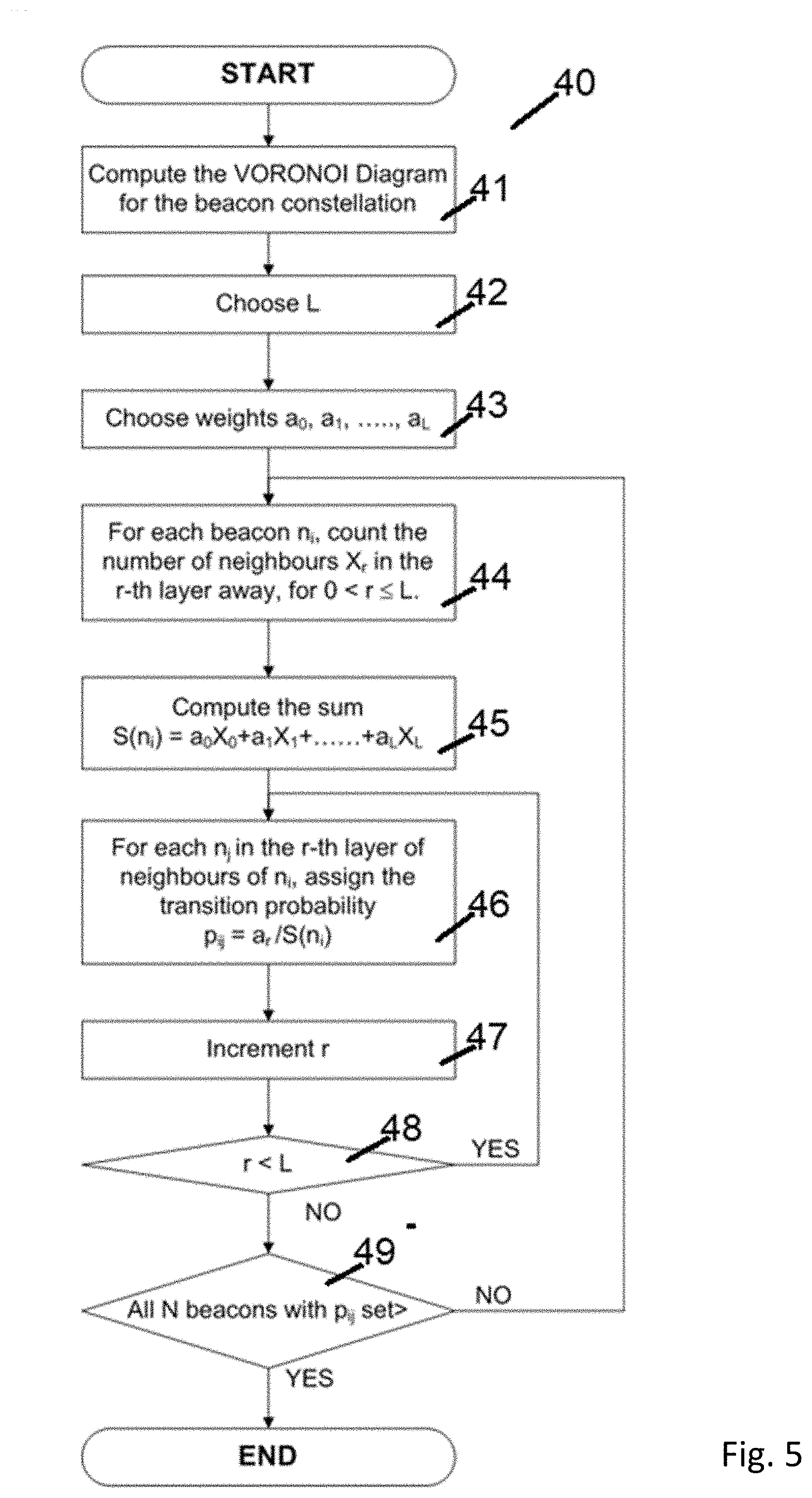
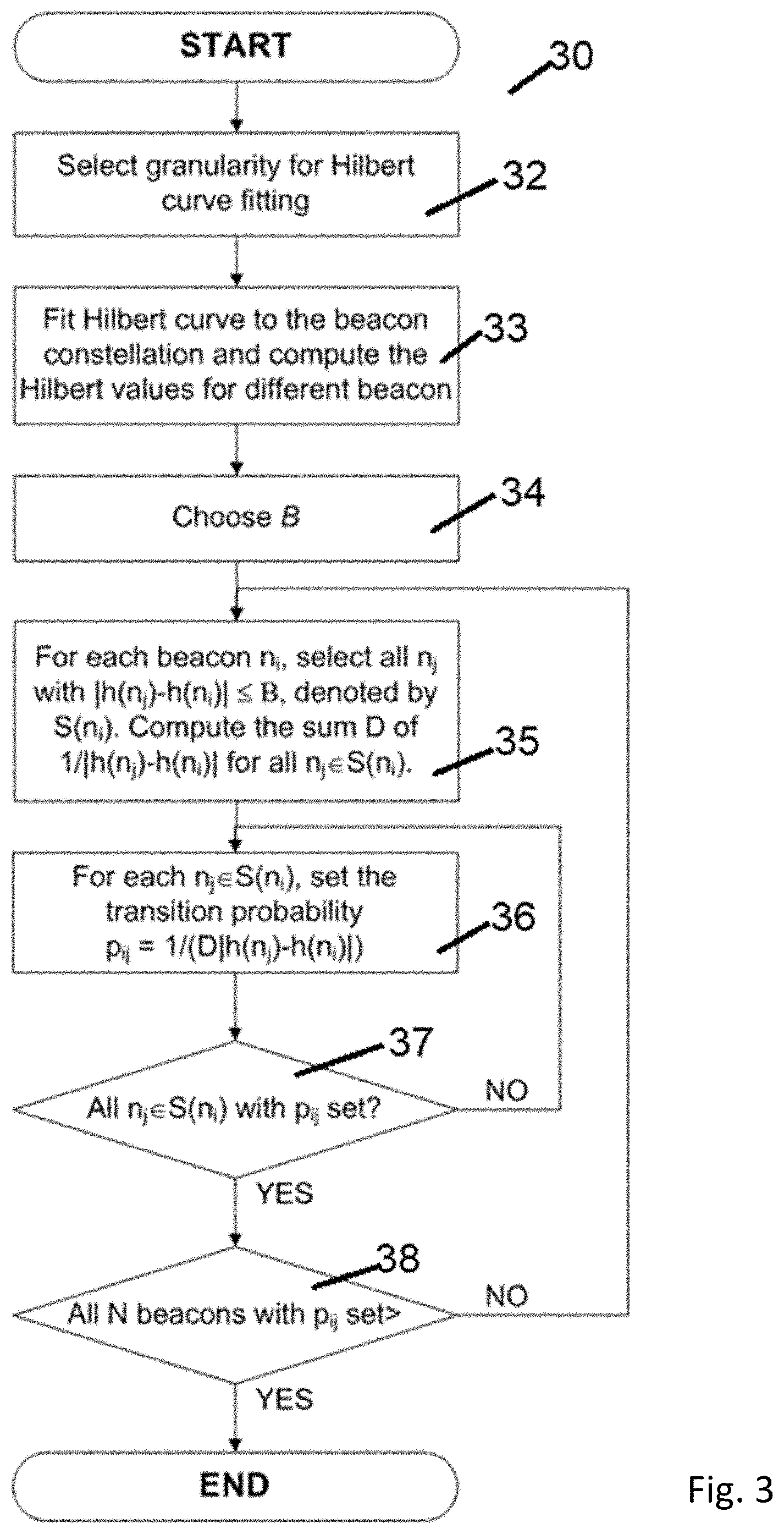
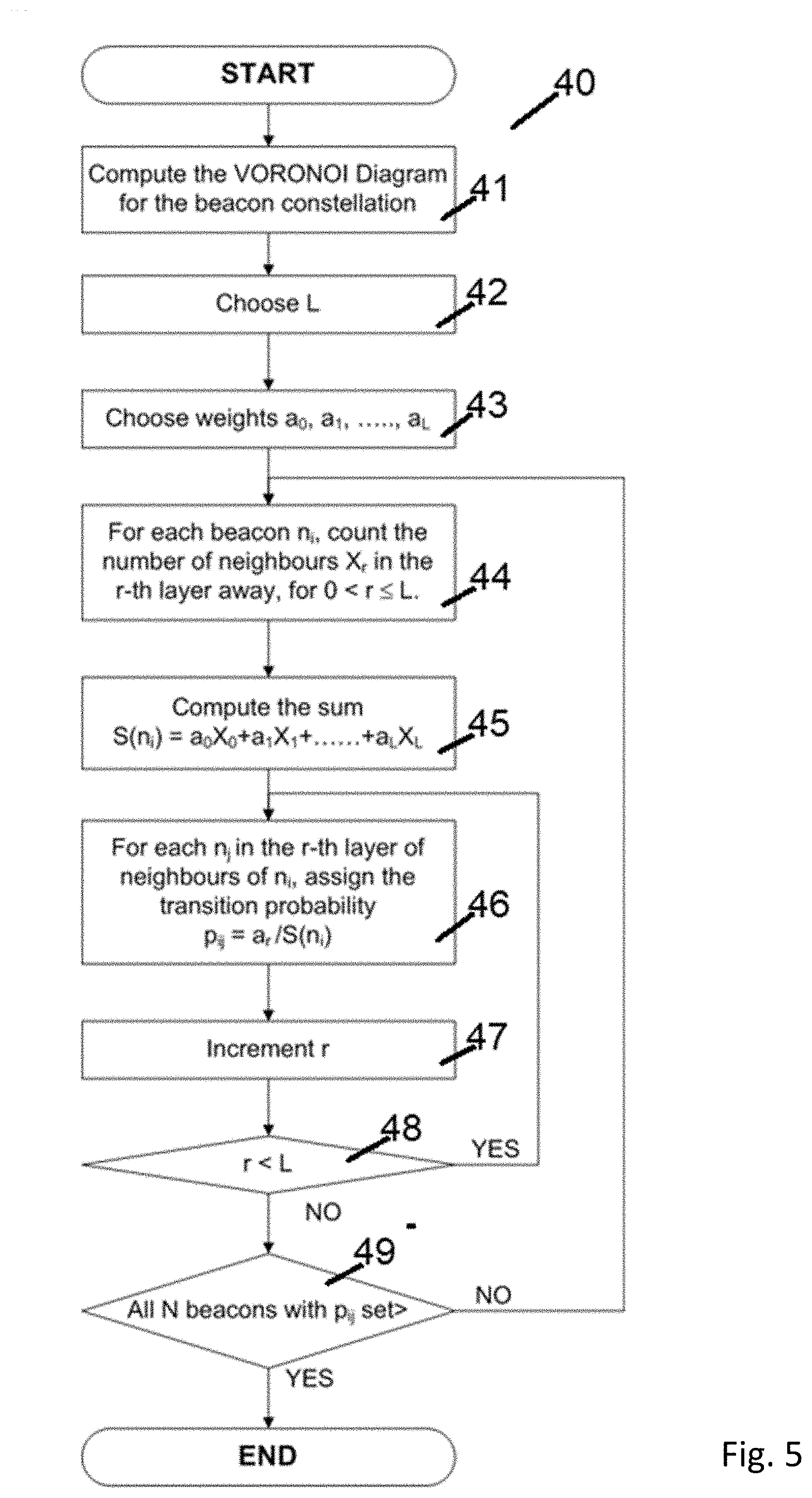
[0071] FIG. 5 shows a schematic diagram of another method for generating state transition probabilities for the Markov chain model shown in FIG. 2;
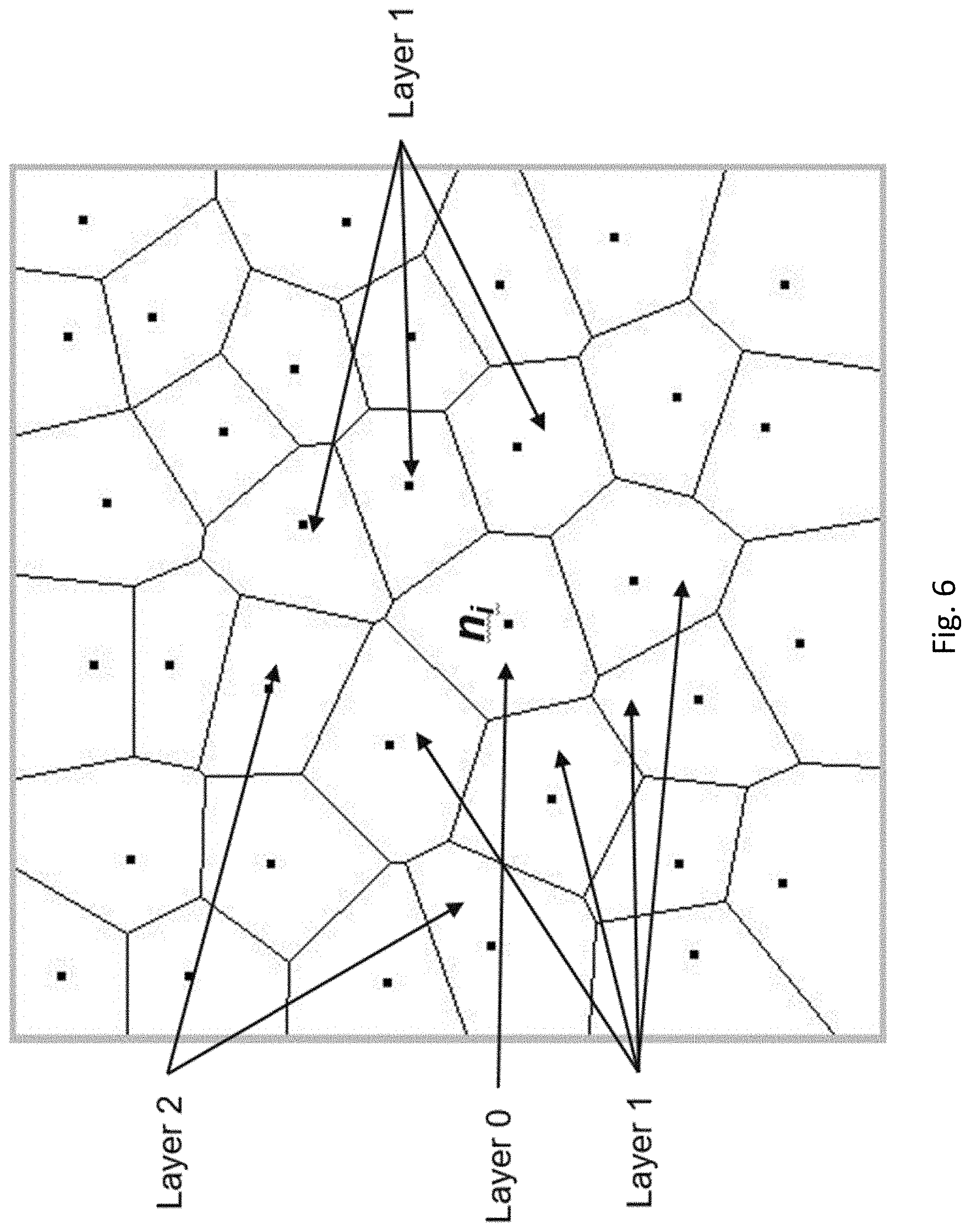
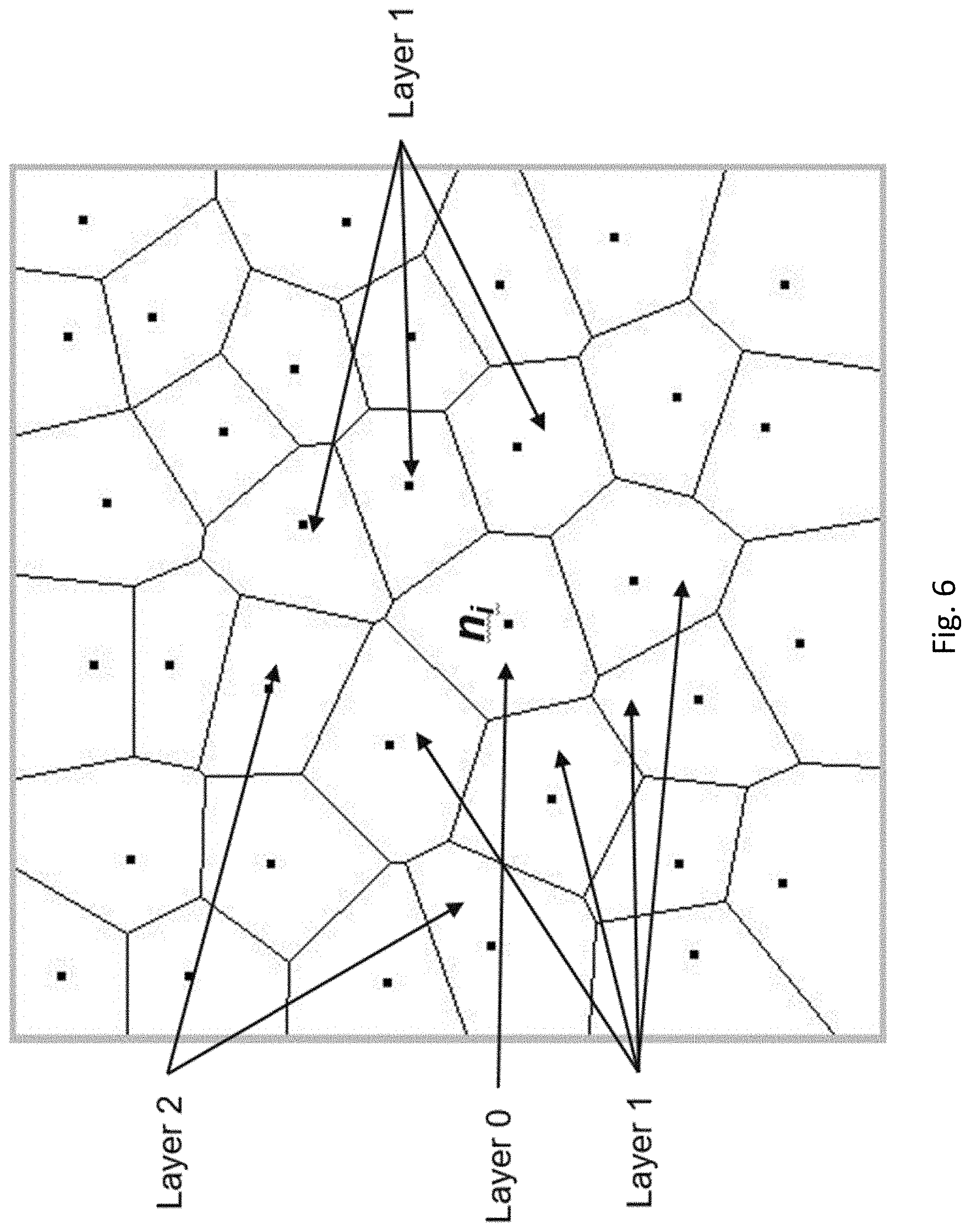
[0072] FIG. 6 shows a schematic diagram of a graphical representation of the method shown in FIG. 5;
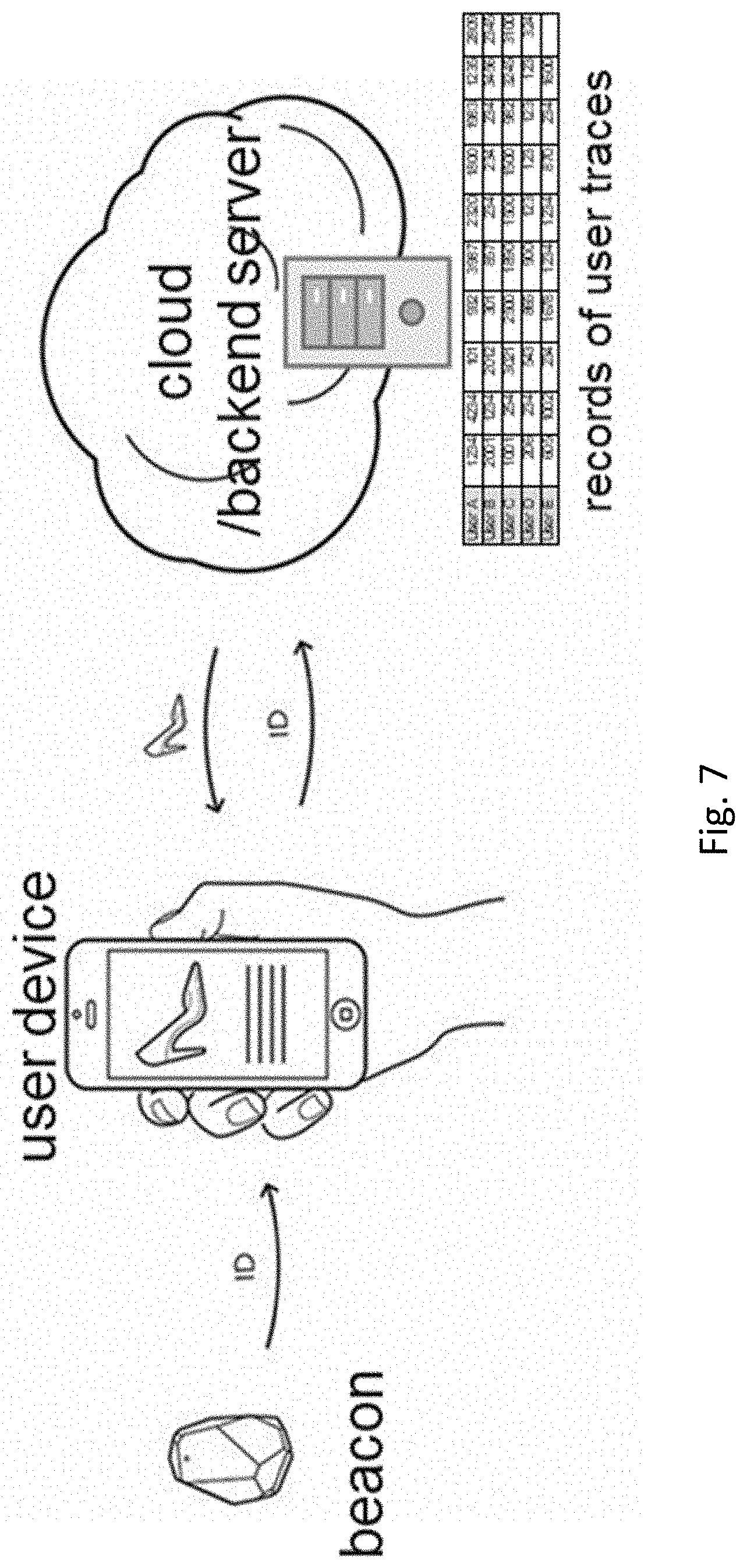
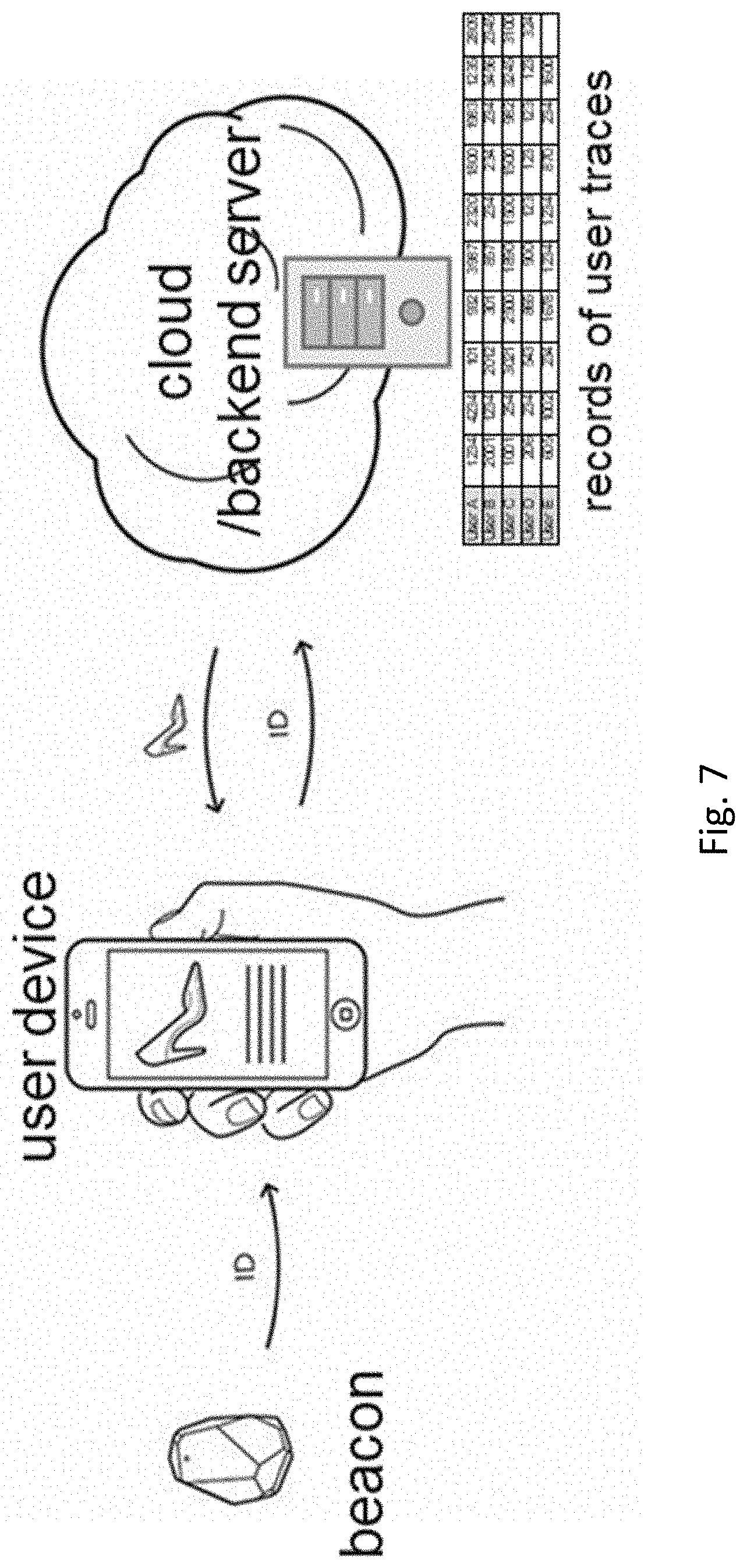
[0073] FIG. 7 shows a system for attack detection in wireless beacon systems according to an embodiment of the present invention;
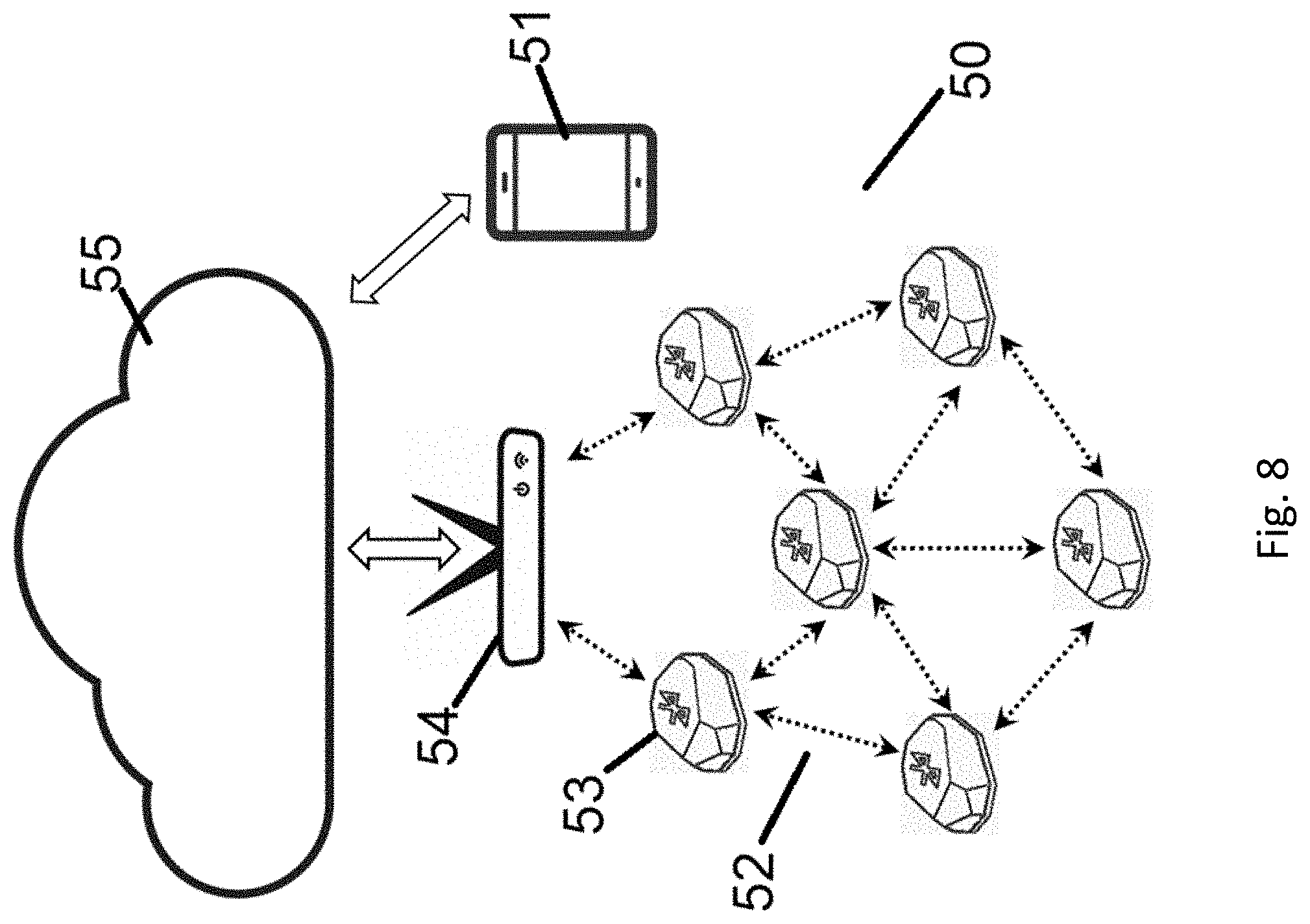
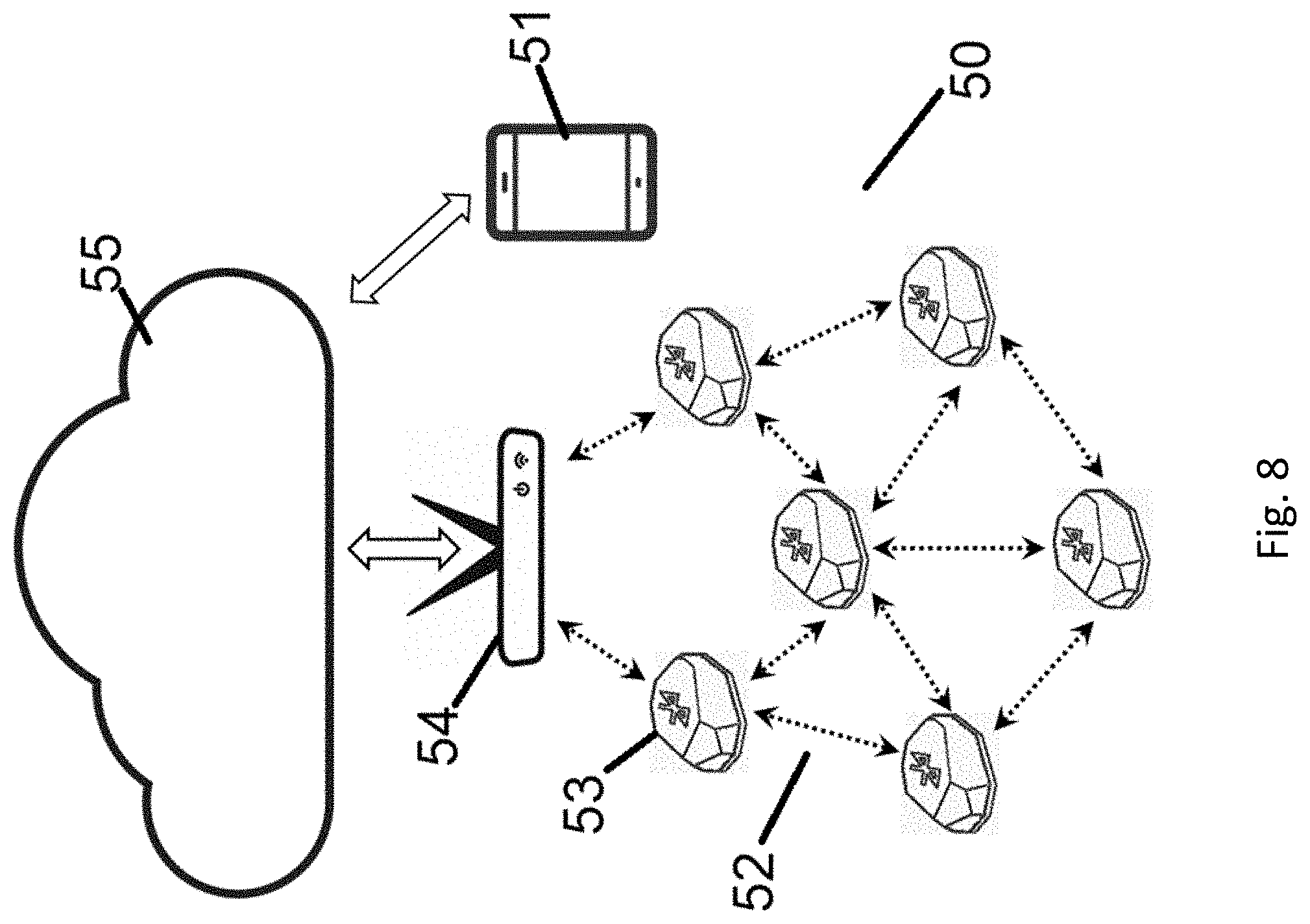
[0074] FIG. 8 shows another system for attack detection in wireless beacon systems according to an embodiment of the present invention; and
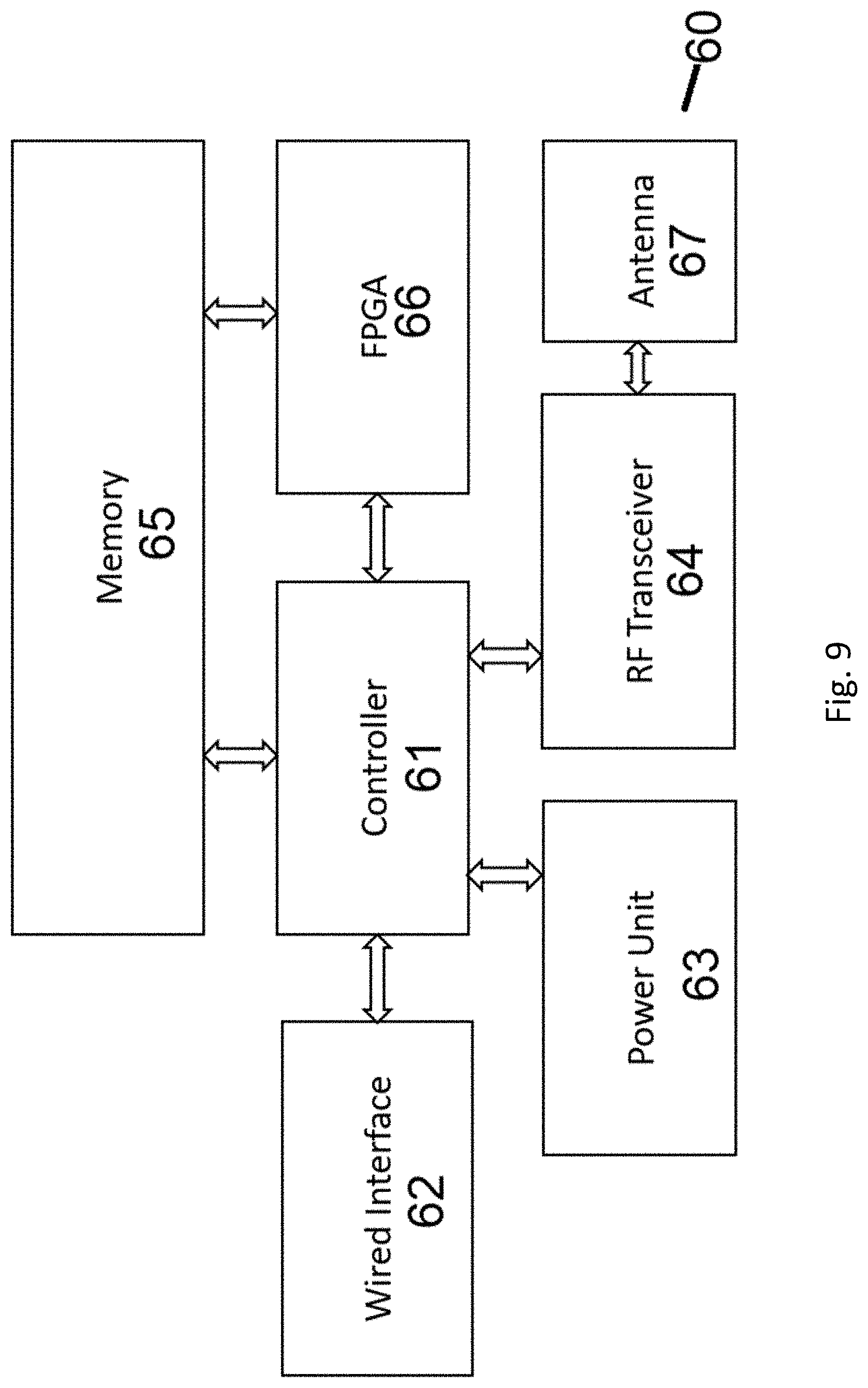
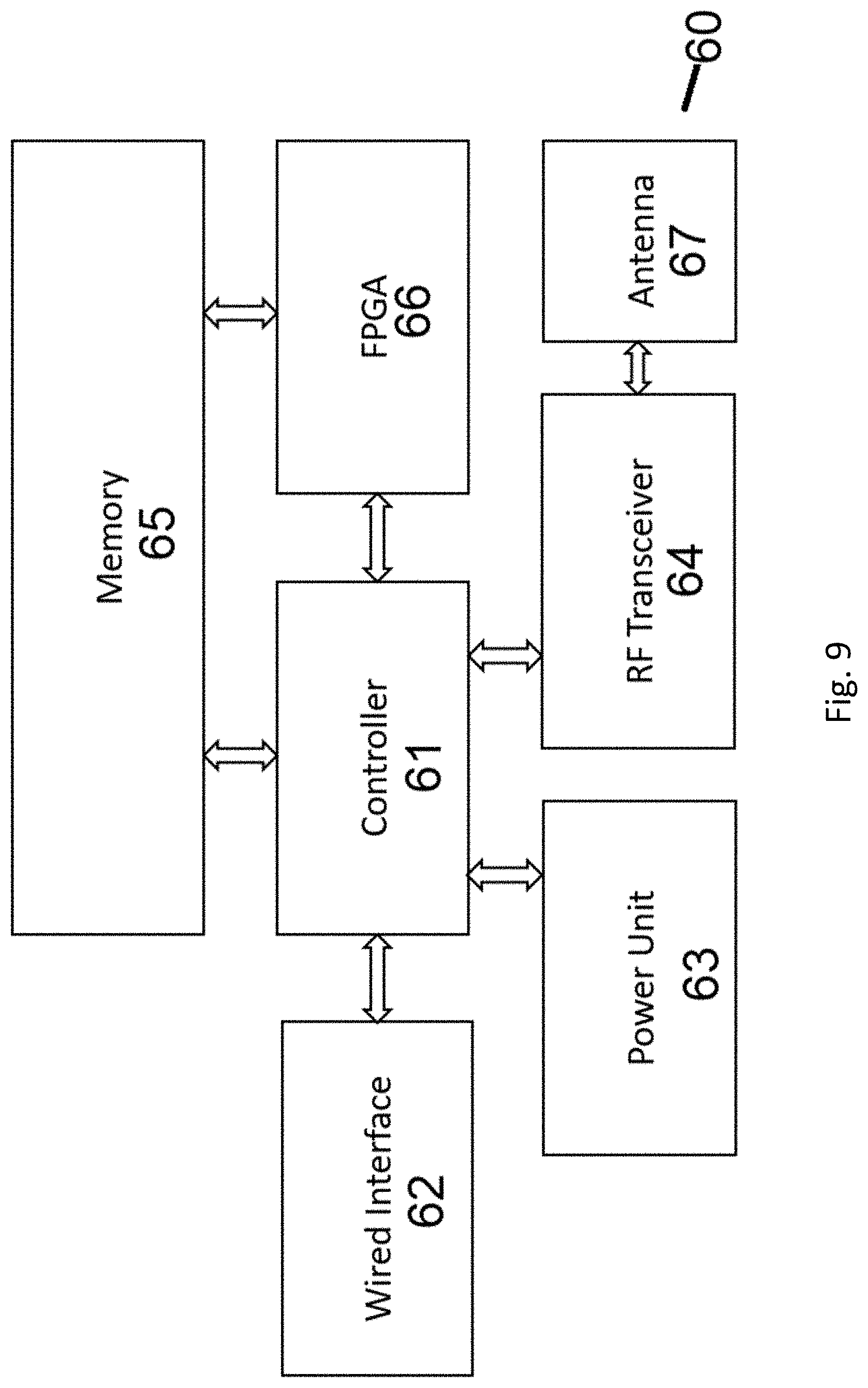
[0075] FIG. 9 shows another terminal device for attack detection in wireless beacon systems according to an embodiment of the present invention.
DESCRIPTION OF THE INVENTION
[0076] The inventors have, through their own research, devised that, for beacons security, computational constraints may be a main impediment to implementing effective defence.
[0077] In one example, there is a data protection method for iBeacon base station. The data protection method comprising: modifying the iBeacon base station identification information after a controlling device has established a communication connection with the iBeacon base station, and uploading the modified iBeacon base station identification information to a server; updating by the server a mapping table of locations and identification information of iBeacon base stations according to the modified iBeacon base station identification information.
[0078] In another example, a Low energy Bluetooth system with authentication during connectionless advertising and broadcasting may be used. The authenticated data is generated using said authenticated information. An advertisement string is broadcast from the BLE device in a connectionless session along with said validation data.
[0079] Alternatively, an iBeacon based data encryption method and system may be adopted. The iBeacon base station generates and sends changed UUID (Universally Unique Identifier) information at a fixed time interval, wherein the UUID information is encrypted; the end user devices determine whether received UUID belongs to one of the UUID information or not; and after the user device determines that the received UUID belongs to one of the UUID information, the user device decrypts the UUID information, and the UUID information is accessed into a network.
[0080] In one example embodiment, the method may use pseudonyms to protect privacy and anonymity of communication messages. In this example, a pseudonym is extracted from a received message for comparison against a precomputed set of pseudonyms associated respectively with a plurality of communities of wireless nodes. The pseudonyms are valid only for a particular time period.
[0081] In an alternative method, after an event, the apparatus may create a wireless message based on the event and then send the wireless message to a peripheral apparatus. The peripheral apparatus utilizes some or all of the message data to formulate and display a user interface. Inputs (e.g., soft-coded or hardware based buttons) in the peripheral device are actuated in accordance with the user interface, which results in a response message being sent to the apparatus. The response message, in turn, trigger functionality in the apparatus.
[0082] Without wishing to be bound by theory, the use of dynamic beacon identification (ID) which changes with time, such that collected identifications (through lunch-time attacks) may not be useful later one. Hence, modifications on beacons are necessary. Besides, this method might not withhold adequate query attacks which eavesdrop and immediately forward to the spoofing beacons to play back.
[0083] For example, a secure beacon-based beacon may be used to generate dynamic beacon identifiers. A mobile device application may send a request to an application server, including a dynamic beacon identifier. The application server can locally compute the dynamic beacon identifier and compare it to the received beacon identifier to validate the request and determine whether to respond to the request.
[0084] Alternatively, beacon signals may be received from a beacon device, such as a mobile device or a server, that identifies a beacon authentication value from the beacon signal. The beacon device calculates a local verification value from a security algorithm. A comparison of the authentication value to the local verification value is performed, and a location service is provided based on the comparison.
[0085] These examples may provide a baseline model of normal behavior regarding the transactions of beacon IDs, and hence detect outlier behavior attributed to spoofing and re-shuffling attacks, as well as, other causes.
[0086] In another example embodiment, there is provided a system of detection of spoof attacks on the Internet of Things (IoT) location broadcasting by a stream of beacons. The stream of beacons comprising at least a unique source identifier is generated. A list of broadcasted beacons is stored in a table along with a time and location of broadcast. Subsequent to broadcasting, a stream of beacons is detected. The detected beacon stream comprises a unique source identifier along with a time and a location of a broadcast. The unique source identifier, the time and the location of at least one beacon of the detected beacon stream can be compared to the unique source identifier, the time and the location of at least one beacon of the broadcast beacon stream. Responsive to a match between the unique source identifiers and a mismatch of at least one of the times and locations, it is determined that the broadcast beacon stream has been spoofed by the detected beacon stream. Once a spoof has been detected, various remediation actions can be taken, such as sending alerts to admin, cautioning end users, and other security mode procedures.
[0087] Some other systems may detect poisoning attacks of the Internet of Things (IoT) location beacons in wireless local area networks (WLANs) with silence periods. The silence periods are associated with the location beacons and are unknown to the public. The location beacon transmission time is compared to the silence periods. Responsive to the location beacon transmission time corresponding to at least one of the silence periods, the location device flagged as poisoned.
[0088] Aiming at defence against adaptive query attacks, new wireless networking devices may be installed in proximity of fake beacon devices to transmit dummy beacons and detect play-back from them with a wrong timestamp to infer the existence of an attack.
[0089] Alternatively, using secret silent periods in legitimate beacons may detect poisoning attacks. To implement these systems, there is a need of installing a new device in proximity of fake beacon devices to pick up spoofing beacons, while all detection is done in the backend server seamlessly to users.
[0090] It may be more preferable to provide an attack detection method such that minimum or ideally no workload needs to be imposed on beacon devices while achieving detection of wrong beacon ID constellation attributed to spoofing attacks, re-shuffling attacks or others. The majority of overhead should be on the mobile devices or the backend servers.
[0091] Some of the abovementioned examples may only defend against spoofing attack. Alternatively, some preferably embodiments of the present invention may work for both spoofing and re-shuffling attacks.
[0092] Preferably, the attack detection method requires no modification on beacon devices (neither hardware nor firmware) is necessary. That is, standard beacon IDs could still be broadcast to all people (including the attacker) in the typical way. Passive detection should be used such that there is no need to install additional devices.
[0093] In an embodiment of the present invention, a method to form the baseline, Markov chain model of device identity transition probabilities for active (such as beacons) and passive (RFID tags) IoT devices to "passively" detect both spoofing and re-shuffling attacks, and others. The active (such as beacons) and passive (RFID tags) IoT devices form a constellation of beacons.
[0094] In one implementation of an embodiment of the present invention, there is provided a backend server or a routing device receiving queries from a terminal device such as a smartphone, tablet, routing device, or other mobile devices, and detecting an intrusion, such as spoofing and re-shuffling attacks has taken place.
[0095] The backend server or routing device is adapted to form a Markov chain with states being beacon device identities, and calculate the transition probability between each pair of Markov chain states from the given constellation of device deployment.
[0096] The terminal device will send a series of beacon IDs to the backend server or routing device. The backend server records traces of beacon IDs sent from various terminal devices. Whenever a terminal device receives a beacon ID, it will forward it to the backend server in the usual scenarios to query content or services based on the beacon ID. Over time, the backend server records/stores up the sequence of transitions of IDs picked up by a particular terminal device. This sequence of transitions forms a trace. The backend server then runs hypothesis testing on the trace against the predetermined Markov chain transition probabilities.
[0097] Once the backend server or routing device receives the beacon ID transitions from requests of terminal devices, it will run a hypothesis test to decide if a given user trace is an outlier with respect to the baseline model. If it is found that the user trace is an outlier with respect to the baseline model, the backend server will flag out a possible intrusion to the system administrator.
[0098] FIG. 1 shows a schematic diagram of a method 10 of detecting for attack detection in a constellation of beacon devices. The method 10 comprises the steps of:
[0099] computing spatial relational metrics between beacon devices as shown in Step 12;
[0100] transforming beacon IDs as states of a Markov chain model, and estimating state transition probabilities based on the spatial relational metrics to form the baseline model as shown in Step 14;
[0101] recording user traces of beacon ID transitions when terminal devices make queries as shown in Step 16;
[0102] running hypothesis test on the user traces against the Markov chain model (baseline model) to determine a status of intrusion as shown in Step 18.
[0103] The principle of an embodiment of the present invention utilises the statistical property of the user trace in a Markov chain model generated by beacon IDs as states and the corresponding state transition probabilities. Each beacon ID represents a state. The transition probability p.sub.ij from the beacon ID.sub.i to beacon ID.sub.j can then be derived as shown in FIG. 2. The present invention presents a number of different methods to calculate the state transition probabilities.
[0104] In one embodiment, the transition probability is calculated with Hilbert Transform algorithm. The Hilbert Transformation algorithm is a space fitting curve algorithm that uses ordered Hilbert values of beacons to find nearest neighbors, and assign transition probabilities based on the order. The algorithm transforms the two-dimensional coordinate of a planar constellation of beacon devices into a linear arrangement of device identities with weights in Hilbert values. Then the weights (based on the selected maximum no. of hops of neighbours) are normalized into transition probabilities such that all the conditional probabilities are summed up to 1 for any state.
[0105] The spatial constellation of beacons in the 2-D space is transformed into a linear ordering of beacon IDs with Hilbert value h(n.sub.i) where n.sub.i is the beacon ID. The closeness of two beacons n.sub.i, n.sub.j can be estimated by:
D.sub.ij=|h(n.sub.i)-h(n.sub.j)|
[0106] By choosing a bound B, the nearest neighbours of a beacon device n.sub.i are then the set S(n.sub.i)={n.sub.j: |h(n.sub.j)-h(n.sub.i)|.ltoreq.B}. The transition probabilities from ID.sub.i to ID.sub.j can be estimated as:
p ij = { 1 D i j n j .di-elect cons. S ( n i ) 1 D i j , n j .di-elect cons. S ( n i ) 0 , elsewhere ##EQU00004##
[0107] The process 30 of the Hilbert Space Fitting Curve of an embodiment of the present invention is shown in FIG. 2 and FIG. 3. The process 30 comprises the steps of:
[0108] selecting a granularity resolution in Step 32;
[0109] fitting Hilbert curve to the beacon constellation and computing the Hilbert value for different beacons in Step 33;
[0110] defining a boundary limit B in Step 34;
[0111] for each beacon n.sub.i, selecting all n.sub.i with |h(n.sub.j)-h(n.sub.i)|.ltoreq.B, denoted by S(n.sub.i), and computing the sum D of 1/|h(n.sub.i)-h(n.sub.j)| for all n.sub.j.di-elect cons.S(n.sub.i) in Step 35;
[0112] in Step 36, for each n.sub.j.di-elect cons.S(n.sub.i), set a transition probability P.sub.ij=1/(D|h(n.sub.j)-h(n.sub.i)|);
[0113] if all n.sub.j.di-elect cons.S(n.sub.i) with p.sub.ij are set in Step 36, then process to Step 37, otherwise loop back to Step 36;
[0114] if all N beacons with p.sub.ij in Step 37, then halt, otherwise loop back to Step 35.
[0115] Alternatively, an embodiment of the present invention uses Voronoi diagram mapping in order to generate the transition probability. The Voronoi diagram mapping method comprises the step of partitioning a two dimensional space into cells. For any beacon n.sub.i, the system assigns different weights to other beacons based on how far the Voronoi cells these beacons belong to from the cell with n.sub.i. Nearer cells are assigned with a higher weight. The system then assigns the weight at the r-th layer cells to be a.sub.r. That is, a.sub.0>a.sub.1>. . . .
[0116] The system then assigns a maximum bound L on the layers to be included in setting the transition probabilities, beyond which the transition probability is zero. Assign the transition probability p.sub.ij such that
[0117] a. the ratio of p.sub.ij: p.sub.ij'=a.sub.x:a.sub.y if n.sub.j and n.sub.j' belong to cells at layer x and layer y respectively, and
[0118] b. sum of all p.sub.ij=1 for any n.sub.i
[0119] The process 40 of the Voronoi diagram mapping of an embodiment of the present invention is shown in FIG. 4 and FIG. 5. The process 40 comprises the steps of:
[0120] computing a Voronoi diagram mapping for the beacon constellation in Step 41;
[0121] determining a boundary value L in Step 42;
[0122] for each layer of cells, aassigning weight at r-th layer cells to be a.sub.r in Step 43;
[0123] for each beacon n, counting the number of neighbours X.sub.r in the r-th layer away, where 0<r.ltoreq.L in Step 44;
[0124] computing the sum S(n.sub.i)=a.sub.0X.sub.0+a.sub.1X.sub.1+ . . . +a.sub.LX.sub.L in Step 45;
[0125] for each n.sub.j in the r-th layer of neighbours of n.sub.i, assigning the transition probability
p i j = a r S ( n i ) ##EQU00005##
in Step 46;
[0126] incrementing r in Step 47;
[0127] in Step 48, checking if r<L, then returning to Step 46, otherwise proceed to Step 49;
[0128] in Step 49, halt if the transition probabilities of all n beacons are set, otherwise returning to Step 44.
[0129] In another embodiment of the present invention, the transition probabilities between the beacons is derived with an empirical method which comprises the step of
[0130] randomly wandering through the deployment of beacons (pre-launch or after-launch);
[0131] recording the trace of beacon ID transitions, compute the statistics of the beacon distribution and the a posterior probability distribution,
[0132] assigning a transition probability between each pair of states.
[0133] In the step of assigning a transition probability, the system may use the trace to estimate the transition probabilities between pairs of beacon IDs. Alternatively, the system may use Bayesian statistical means or any machine learning algorithm to estimate the transition probabilities. If no transition between two states, zero or a very small probability value can be assigned.
[0134] In one embodiment of the present invention as shown in FIG. 7, a terminal device picks up broadcast beacon IDs and use them as keys to query a backend server or a routing device for location-based information or services. The backend server (which could be in the cloud) or routing device can, therefore, record a user trace of the terminal device which is a temporal sequence of beacon IDs recorded by the terminal device.
[0135] A user trace can be viewed as a discrete random process parameterized by the underlying Markov chain. First, the baseline model represents one probability distribution. Second, user traces could form another probability distribution. If there is no intrusion, the two distributions should resemble each other probabilistically. If the user trace distribution deviates significantly and forms an outlier, we can conclude that it is significantly different from the baseline model, and an intrusion probably has occurred.
[0136] An outlier of user traces probability distribution likely indicates an intrusion has taken place. Altering the parameters of the underlying Markov chain model or base model can adjust the accuracy of the intrusion detection system. In one embodiment, the backend server or routing device will use the user trace to determine whether it belongs to the distribution corresponding to the Markov chain model or base model at the time when the terminal device makes a query to the backend server or routing device.
[0137] The randomness of beacon ID transitions depends largely on user mobility pattern in most cases. The underlying probability distribution of beacon ID transitions is therefore relatively time-invariant or slowly varying. The Markov chain model could be of a lower order as well. Therefore, based on the Markov chain model, it is possible to test if an observed user trace belongs to the corresponding distribution of the Markov chain. If not, it can be assumed an intrusion has likely happened.
[0138] In one embodiment of the present invention, a user trace with T IDs is recorded and encoded by a backend server as:
[0139] (c.sub.1, c.sub.2, . . . , c.sub.r, . . . , c.sub.T)
[0140] This user trace will be recorded a backend server or routing device as the terminal device send a query to the backend server or routing device. The backend server or routing device then runs a hypothesis test to determine whether the received user trace conforms to the distribution as derived by the Markov chain model process. The testing process will generate either one of two opposing hypotheses, which are:
[0141] H.sub.0: (c.sub.1, c.sub.2, . . . , c.sub.r, . . . , c.sub.T) conforming to the baseline Markov chain model; or
[0142] H.sub.1: intrusion or anomalous distribution
[0143] There are many different hypothesis tests that can be implemented in an embodiment of the present invention. For example, the backend server or routing device may carry out a Generalized Likelihood Ratio Test (GLRT) or Kullback-Leibler Divergence (KLD) to test the hypotheses.
[0144] In one embodiment of the present invention, the hypothesis test in Step 18 comprises a method of Generalized Likelihood Ratio Test (GLRT), wherein the GLRT comprises the steps of: [0145] deriving p.sub.ij(.theta.), where 1.ltoreq.i, j.ltoreq.N, as the transition probability from ID.sub.i to ID.sub.j for a n-state Markov chain with .theta. being the corresponding set of parameters, for all possible .theta. by .OMEGA.. [0146] for a received user trace C=(c.sub.1, . . . , c.sub.T) , deriving a likelihood function as the conditional probability for C to occur given .theta., where
[0146] L(.theta.| c.sub.1, . . . , c.sub.T)=.PI..sub.r=1.sup.T-1p.sub.c.sub.r.sub.c.sub.r+1 (q)
[0147] computing the likelihood ratio as follows:
.DELTA. = ( L ( .theta. c 1 , , c T ) max .theta. ' .di-elect cons. .OMEGA. { .theta. } L ( .theta. ' | c 1 , , c T ) ) 1 T ##EQU00006##
[0148] accepting H.sub.0 (with no intrusion detected) if .DELTA..gtoreq..lamda. where .lamda. is the threshold.
[0149] The values of p.sub.ij (.theta.) are derived by one of the three (3) methods described previously, including Hilbert transform, VORONOI diagram and field trial plus Bayesian statistics or machine learning algorithms.
[0150] In one embodiment, the value of .lamda. is set through a Monte Carlo simulation or trial-and-error. The value of .lamda. can be adjusted by the backend server or routing device after the backend server or routing device received feedbacks from the terminal devices according to a number of false positives and false negatives received.
[0151] In general,
.DELTA. .gtoreq. L ( .theta. | c 1 , , c T ) 1 T . ##EQU00007##
In one embodiment, the backend server or routing device accepts H.sub.0 if
L ( .theta. | c 1 , , c T ) 1 T .gtoreq. .lamda. ##EQU00008##
since this implies .DELTA..gtoreq..lamda.. This will reduce the number of calculation process and speed up the testing process.
[0152] In another embodiment of the present invention, the hypothesis test in Step 18 comprises a method of Kullback-Leibler Divergence (KLD), wherein the KLD comprises the steps of:
[0153] collecting user traces of the same length and based on a set of user traces, estimate the probability distribution P(C) of the collected traces where C is a particular user trace;
[0154] computing the reference probability distribution Q(C);
[0155] computing a KLD, where
D K L ( P .parallel. Q ) = - C P ( C ) log Q ( C ) P ( C ) ##EQU00009##
[0156] Accept H.sub.0 if D.sub.KL (P||Q).ltoreq..xi. where .xi. is a threshold.
[0157] In one embodiment, the value of .xi. is set through a Monte Carlo simulation or trial-and-error. In another embodiment, the value of .xi. is set empirically. The value of .xi. can be adjusted by the backend server or routing device after the backend server or routing device received feedbacks from the terminal devices according to a number of false positives and false negatives received.
[0158] In one embodiment, the step of collecting user traces comprises the step of setting a moving window over all user traces, such that C at a particular time is all user traces in the window.
[0159] In one embodiment of the present invention as shown in FIG. 8, there is provided a system 50 for attack detection in wireless beacon systems, comprising a constellation 52 of beacons, wherein each beacon 53 is adapted to broadcast a unique beacon identification code (beacon ID). The system 50 also has a terminal device 51 adapted to receive a user trace of beacon IDs, and send a query to a backend server 54 or routing device to determine an occurrence of an intrusion via a network 55. The backend server 54 is adapted to determine an occurrence of an intrusion by carrying out the steps of computing spatial relational metrics between beacon devices as shown in Step 12. Then the backend server 54 transforms beacon IDs as states of a Markov chain model, and estimating state transition probabilities based on the spatial relational metrics as shown in Step 14. The backend server 64 will then record user traces of beacon ID transitions when terminal device 51 make queries as shown in Step 16; and run hypothesis test on the user traces against the Markov chain model to determine a status of intrusion as shown in Step 18.
[0160] In one aspect of the present invention as shown in FIG. 9, there is provided a terminal device 60 which comprises a controller 61 for controlling the radio signals through a radio frequency (RF) transceiver 64, wherein the RF transceiver is connected to an antenna 67. The terminal device 60 also has a field-programmable gate array (FPGA) for encoding the radio signals to beacon IDs, and a memory module 65 for storing a user trace of beacon IDs. The controller 61 is adapted to forward the user trace of beacon IDs for detecting an occurrence of instruction by subjected the user trace to a hypothesis test against a Markov chain model to determine a status of intrusion as shown in Step 18. The Markov chain model is generated by computing at a backend server or routing device spatial relational metrics between beacon devices as shown in Step 12, and transforming beacon IDs as states of a Markov chain model, and estimating state transition probabilities based on the spatial relational metrics as shown in Step 14.
[0161] Advantageously, the embodiments of the present invention are based on a completely passive detection method with the baseline formed wholly based on passively observing user traces or computed offline and does not require additional equipment to inject beacons and detect spoofed beacons.
[0162] The embodiments of the present invention may be advantageous over methods of injecting time-varying dummy beacons in the proximity of the suspected fake beacon devices to form a baseline model and assumes these fake beacon devices to pick up the dummy beacons and replay them with a different timestamp.
[0163] Further, the method of injecting time-varying dummy beacons would still be vulnerable to re-shuffling attacks which do not involve beacon signal playbacks.
[0164] The present invention works well for both spoofing and re-shuffling attacks, as both will cause a deviation of transition probabilities from the baseline case.
[0165] Advantageously, the method of the present invention does not require a new detector equipment to be placed near the suspected fake beacon devices.
[0166] The present invention has all the detection will be done in the backend server or router with the previously formed baseline models and beacon ID traces extracted from user requests in normal operation of the beacon system.
[0167] Advantageously, the method of the present invention does not require a dedicated device to pick up beacon signals to verify whether an intrusion has occurred.
[0168] The present invention only uses recorded traces from usual queries from users to run a hypothesis test to verify possible intrusion.
[0169] It is understood that those skilled in the art will realize that variations may be made in the core teachings of this invention.
[0170] It will also be appreciated that where the methods and systems of the present invention are either wholly implemented by computing system or partly implemented by computing systems then any appropriate computing system architecture may be utilised. This will include standalone computers, network computers and dedicated hardware devices. Where the terms "computing system" and "computing device" are used, these terms are intended to cover any appropriate arrangement of computer hardware capable of implementing the function described.
[0171] It will be appreciated by persons skilled in the art that numerous variations and/or modifications may be made to the invention as shown in the specific embodiments without departing from the spirit or scope of the invention as broadly described. The present embodiments are, therefore, to be considered in all respects as illustrative and not restrictive.
[0172] Any reference to prior art contained herein is not to be taken as an admission that the information is common general knowledge, unless otherwise indicated. Although the invention has been described with reference to specific examples, it will be appreciated by those skilled in the art that the invention may be embodied in many other forms, in keeping with the broad principles and the spirit of the invention described herein.
* * * * *
D00000
D00001
D00002
D00003
D00004
D00005
D00006
D00007
D00008
D00009




XML
uspto.report is an independent third-party trademark research tool that is not affiliated, endorsed, or sponsored by the United States Patent and Trademark Office (USPTO) or any other governmental organization. The information provided by uspto.report is based on publicly available data at the time of writing and is intended for informational purposes only.
While we strive to provide accurate and up-to-date information, we do not guarantee the accuracy, completeness, reliability, or suitability of the information displayed on this site. The use of this site is at your own risk. Any reliance you place on such information is therefore strictly at your own risk.
All official trademark data, including owner information, should be verified by visiting the official USPTO website at www.uspto.gov. This site is not intended to replace professional legal advice and should not be used as a substitute for consulting with a legal professional who is knowledgeable about trademark law.