Sequence Encryption Method Accompanying Adjustable Random Reconfiguration Of Key
XU; Zhineng
U.S. patent application number 16/654045 was filed with the patent office on 2020-06-18 for sequence encryption method accompanying adjustable random reconfiguration of key. The applicant listed for this patent is Zhineng XU XU. Invention is credited to Zhineng XU.
| Application Number | 20200195430 16/654045 |
| Document ID | / |
| Family ID | 59871763 |
| Filed Date | 2020-06-18 |





| United States Patent Application | 20200195430 |
| Kind Code | A1 |
| XU; Zhineng | June 18, 2020 |
SEQUENCE ENCRYPTION METHOD ACCOMPANYING ADJUSTABLE RANDOM RECONFIGURATION OF KEY
Abstract
Disclosed is a random binary sequence-based sequence encryption method accompanied with random reconfiguration of a key. The method is mainly characterized in that (1) an existing random sequence is used to dynamically configure a seed random sequence at the beginning of each encryption operation, (2) the seed random sequence is used to pseudo-randomly configure a random key with a fixed-length or variable-length bit field, (3) the pseudo-random configuration of the random key accompanies an encryption process, (4) a transitive property of an exclusive-or operation is used to realize a variable-frequency nonlinear exclusive-or operation on a plaintext using the key, (5) adjustment of key configuration is realized by adjusting a characteristic vector, other operation vectors and a pseudo-random configuration function, such that adjustment of an encryption density can be realized without increasing time complexity, and (6) the characteristic vector are unable to be reversely inducted in polynomial time complexity.
| Inventors: | XU; Zhineng; (Nanjing, CN) | ||||||||||
| Applicant: |
|
||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|
| Family ID: | 59871763 | ||||||||||
| Appl. No.: | 16/654045 | ||||||||||
| Filed: | October 16, 2019 |
Related U.S. Patent Documents
| Application Number | Filing Date | Patent Number | ||
|---|---|---|---|---|
| PCT/CN2018/082638 | Apr 11, 2018 | |||
| 16654045 | ||||
| Current U.S. Class: | 1/1 |
| Current CPC Class: | H04L 9/0894 20130101; H04L 9/16 20130101; H04L 9/0662 20130101; H04L 9/0869 20130101; H04L 9/001 20130101 |
| International Class: | H04L 9/08 20060101 H04L009/08; H04L 9/06 20060101 H04L009/06; H04L 9/16 20060101 H04L009/16 |
Foreign Application Data
| Date | Code | Application Number |
|---|---|---|
| Apr 17, 2017 | CN | 201710249427.9 |
Claims
1. A sequence encryption method accompanied with adjustable randomly-reconstructed key, characterized by sequence encryption/decryption accompanied with reconstructing a random sequence key based on a random binary sequence during encryption/decryption, the method comprising steps of: (1) dynamically constructing a seed random sequence B.sub.i (i=1, 2, . . . , m) at beginning of each encryption/decryption through an existing random sequence, wherein the seed random sequence B.sub.i (i=1, 2, . . . , m) is derived from a pseudo-random reconstruction of an alternative random sequence B.sup.j (j=1, 2, . . . , v), or is directly taken from the alternative random sequence B.sup.j (j=1, 2, . . . , v) if a quantity of the alternative random sequence is more than/equal to a quantity of the seed random sequence; wherein the alternative random sequence B.sup.j (j=1, 2, . . . , v) is a part of a contract of encryption and decryption parties, and the seed random sequence B.sub.i (i=1, 2, . . . , m) is pseudo-randomly reconstructed or truncated from B.sup.j (j=1, 2, . . . , v) starting from an agreed position according to an agreement; (2) pseudo-randomly constructing a random key B using the seed random sequence B.sub.i (l<=i<=m), wherein the process of constructing the random key B is accompanied with reconstructing a bit segment of a fixed or unfixed length and is processed segment by segment, wherein the generation of the random key B is accompanied during encryption/decryption process and the random key B is generated step by step through pseudo-randomly reconstructing each bit in the seed random sequence B.sub.i (l<=i<=m); and selecting a key bit segment for XOR in each step according the secret agreement of the encryption and decryption parties, wherein the process of selecting comprises obtaining frequencies of XOR of the encrypting/decrypting, a starting position of bit segment in B seed random sequence at each frequency and length of the bit segment, and a process of the pseudo-random reconstruction is determined by the secret agreement; (3) encrypting/decrypting a segment of the plaintext by the bit segment of the fixed or unfixed length, wherein each segment of the plaintext XORs with several corresponding key bit segments obtained by the pseudo-random reconstruction with a fixed frequency or variable frequency, an increase or no increase of the bit segment length between frequencies and swapping or not swapping of bits in cipher text segment between frequencies, to generate the cipher text.
2. The sequence encryption method accompanied with adjustable randomly-reconstructed key according to claim 1, characterized by a part of convention in the secret convention being implemented by an agreement construction function which uses following random values as arguments: (1) a random value determined by the key bit segment in previous step according to the secret agreement for the pseudo-random reconstruction, (2) a random values determined by a pseudo-randomly agreed bit segment of other random sequences according to the secret agreement for the pseudo-random reconstruction, or (3) a random value determined by a value of a cipher text bit segment in the previous step according to the secret agreement for the pseudo-random reconstruction.
3. The sequence encryption method accompanied with adjustable randomly-reconstructed key according to claim 1, characterized by: (1) forward shifting the bit segment of the plaintext in turn in the process of encryption/decryption for the plaintext segment by segment, wherein the length of the bit segment of the plaintext is equal to the length of the key bit segment, and the length i.sub.s of the key bit segment b.sub.s and the starting position p.sub.s of the key bit segment in the seed random sequence B.sub.i (l<=i<=m) all are determined by the contract agreed by the encryption and decryption parties; a same bit segment of the plaintext is subjected to multi-frequency XOR in turn by a plurality of key bit segments, and the frequency f.sub.s of the multi-frequency XOR is determined by the contract agreed by the encryption and decryption parties; (2) except the first frequency, forward or backward shifting the starting position p.sup.g.sub.s of the multi-frequency seed bit segment b.sup.g.sub.s (g=1, 2, . . . , f.sub.s) participating in the multi-frequency XOR according to the position of the multi-frequency seed bit segment b.sup.g-1.sub.s in the previous frequency, that is, backward or forward shifting several bits according to the position of the multi-frequency seed bit segment in the previous frequency, wherein the starting position p.sup.g.sub.s of the multi-frequency seed bit segment b.sup.g.sub.s is forward or backward shifted to reach the last bit or first bit of the seed random sequence B.sub.i (l<=i<=m), the forward or backward shifting continues from the last bit or the first bit; (3) the length of the multi-frequency seed bit segment b.sup.g.sub.s in the multi-frequency XOR is still equal to l.sub.s; (4) determining the frequency f.sub.s of the multi-frequency XOR by the contract agreed by the encryption and decryption parties, wherein the pseudo-random reconstruction process of the seed random sequence B.sub.i (l<=i<=m) presents a morphology of forward or backward shifting equidistant from the plaintext when the selected frequency is 1, and the pseudo-random reconstruction process of the seed random sequence B.sub.i (l<=i<=m) presents a morphology of forward or backward shifting with hopping in times of distance from the plaintext when the selected frequency is greater than 1; (5) encrypting the bit segment of the plaintext with XOR at the fixed frequency step by step using the multi-frequency seed bit segment b.sub.s obtained above.
4. The sequence encryption method accompanied with adjustable randomly-reconstructed key according to claim 1, characterized by improving encryption density by following steps: (1) determining the unit for calculating by the agreed starting position and agreed length of the key bit segment b.sub.s-1 in the previous step; (2) determining the starting position p.sub.s of a reconstruction source b.sub.i,s (l<=i<=m) of the key bit segment b.sub.s of the random key B in the current step by a random value taken in the unit for calculating of the key b.sub.s-1 or an associated bit segment of the random key B in the previous step and a feature quantity S through a positioning function P, wherein P is any function whose value domain covers the whole seed random sequence B.sub.i (l<=i<=m), that is, the value domain P(b.sub.s) of P satisfies 0<P(b.sub.s).ltoreq.n, and n is the maximum position of element in the seed random sequence B.sub.i (l<=i<=m); (3) determining the length l.sub.s of the key bit segment b.sub.s of the random key B and the reconstruction source b.sub.i,s (l<=i<=m) in the current step by the random value taken in the unit for calculating of the key bit segment b.sub.s-1 or an associated bit segment of the random key B in the previous step and the feature quantity S through a length determining function L, wherein L is any function whose value domain is greater than 0, that is, the value domain L(b.sub.s) of L satisfies 0<L(b.sub.s).ltoreq.n, and n is the maximum position of element in the seed random sequence B.sub.i (l<=i<=m); (4) determining the frequency f.sub.s of XOR for the bit segment m.sub.s of the plaintext with the random key bit segment b.sub.s by the random value taken in the unit for calculating of the key bit segment b.sub.s-1 or an associated bit segment of the random key B in the previous frequency and the feature quantity S through a frequency determining function F, wherein F is any function whose value domain is greater than 0; (5) determining the key bit segment b, in the seed random sequence B.sub.i (l<=i<=m) by p.sub.s and/or l.sub.s selected by the steps (2) and (3), determining the frequency f.sub.s of XOR in the current step by the step (4), selecting f.sub.s bit segments b.sup.1.sub.s, b.sup.2.sub.s, . . . , b.sup.fs.sub.s from the seed random sequence B.sub.i (l<=i<=m) in a manner of forward shifting or a pseudo random manner, and performing the multi-frequency XOR f.sub.s times orderly for the bit segment m.sub.s of the plaintext in the current step with the above selected key bit segments.
5. The sequence encryption method accompanied with adjustable randomly-reconstructed key according to claim 1, characterized by further improving encryption density by following steps: (1) pseudo-randomly constructing the random key B with a plurality of seed random sequences B.sub.i (i=1, 2, 3, . . . , m; m is any positive integer), wherein the constructing comprises: (a) pseudo-randomly selecting or constructing a plurality of seed bit segments b.sub.i,s (i=1, 2, 3, . . . , m, b.sub.i,s is a seed bit segment selected in the s-th step from the i-th seed random sequence B.sub.i) according to the value of the key bit segment b.sub.s-1 or the associated bit segment in the previous step in the agreed contract, performing orderly paired XOR for the seed bit segments one by one and taking a result as the key bit segment b.sub.s in the current step; (b) pseudo-randomly selecting one of b.sub.i,s (0<i<=m) as the key bit segment b.sup.q.sub.s (q=1, 2, . . . , f.sub.s) in the current step according to the value of the key bit segment b.sub.s-1 or the associated bit segment in the previous step in the agreed contract; or (c) pseudo-randomly selecting part of b.sub.i,s (i=1, 2, 3, . . . , j; j<=m) in the current step according to the value of the key bit segment b.sub.s-1 or the associated bit segment in the previous step in the agreed contract, one by one to XOR and performing the result as the key bit segment b.sup.q.sub.s (q=1, 2, . . . , f.sub.s); (Note: b.sub.i,s in (b) and (c) refers to m bit segments them picking up from B.sub.i in the sth step) (2) performing f-frequency ordered XOR on the bit segment m.sub.s of the plaintext through the key bit segment b.sup.q.sub.s (q=1, 2, . . . , f.sub.s) constructed by above (1).(b) or (1).(c); or (3) directly using various bit segments b.sub.i,s (i=1, 2, 3, . . . , m) selected by above (1).(a) as f.sub.s frequency key bit segments b.sub.gs (1, 2, . . . , f.sub.s), or constructing frequency seed bit segments b.sup.g.sub.s (1, 2, . . . , f.sub.s; i=1, 2, . . . , m; b.sup.g.sub.i,s is the g-th frequency seed bit segment selected in s-th step in respective seed random sequence b.sub.i) in a pseudo random manner one by one by any of above function P and function L and constructing frequency key bit segment b.sup.q.sub.s with m frequency seed bit segments b.sup.q.sub.i,s in each frequency, and then performing the multi-frequency XOR for f.sub.s times on the bit segment m.sub.s of the plaintext one by one or in a mixing way; wherein b.sup.q.sub.s (q=1, 2, . . . , f.sub.s) in (2) refers to f.sub.s bit segments constructed from B.sub.i in the sth step; b.sup.q.sub.i,s (q=1, 2, . . . , f.sub.s) in (3) refers to m*f.sub.s bit segments constructed from B.sub.i in the sth step.
6. The sequence encryption method accompanied with adjustable randomly-reconstructed key according to claim 1, characterized by further improving encryption density by following steps: (1) constructing a bit hopping function J for selecting the key bit segment in the current step; or (2) in obtaining seed bit segment b.sub.i,s (i=1, 2, . . . , m) and/or frequency seed bit segment b.sup.q.sub.i,s (q=1, 2, . . . , f.sub.s), extracting or reconstructing each bit of each key bit segment in the current step or at the current frequency bit by bit starting from a source random sequence position determined by p.sub.s with pseudo-randomly hopping according to the bit hopping function J, until reaching the length l; (3) performing the multi-frequency ordered XOR for the bit segment m.sub.s of the plaintext after constructing key bit segment in a pseudo random manner with the seed bit segment b.sub.i,s (i=1, 2, . . . , m)_and/or frequency seed bit segment b.sup.g.sub.i,s (q=1, 2, . . . , f.sub.s).
7. The sequence encryption method accompanied with adjustable randomly-reconstructed key according to claim 1, characterized by adding a step of pairing bits of the target bit segment between frequencies of the multi-frequency XOR to swap according to a pseudo-random secret agreement in the process of multi-frequency XOR to further improve the encryption density: (1) constructing a bit pairing function C for selecting the target bit segment in the current step; (2) performing swapping for the target bit segment of each frequency with the selected paired bits during encrypting in the manner of above 5.(2) or 5.(3); and (3) performing swapping for the cipher text bit segment with the selected paired bits during decrypting for the encrypted cipher text in above 5.(2) or 5.(3).
8. The sequence encryption method accompanied with adjustable randomly-reconstructed key according to claim 1, characterized by adding a step of increasing the length of bit segment for XOR per frequency according to the contract agreed in the process of multi-frequency XOR to further improve the encryption density: (1) constructing a length extension function A for the bit segment between frequencies in the current step; (2) extending the plaintext bit segment and the key bit segment by a determined increase value frequency by frequency during encrypting in the manner of above 5.(2) or 5.(3); and (3) extending the cipher text bit segment and the key bit segment by the determined increase value frequency by frequency during decrypting in the manner of above 5.(2) or 5.(3); (4) after calculating at each frequency, backfilling the increased bits to the corresponding positions of the source sequence.
9. The sequence encryption method accompanied with adjustable randomly-reconstructed key according to claim 1, characterized by adding alternative random sequences in implementing pseudo-randomly constructing the seed random sequence to improve a chaos degree of the seed random sequence B: (1) pre-generating more than one alternative random sequence B.sup.j (j=1, 2, . . . , m) for constructing the seed random sequence B.sub.i (l<=i<=m), establishing a positioning function P.sub.0 and the feature quantity S by using an instant random number E.sup.j (j=1, 2, . . . , m) called as engine the number of which matches B.sup.j (j=1, 2, . . . , m), and after the multi-alternate random sequence starting position p.sup.j.sub.0 (j=1, 2, . . . , m) of each B.sup.j (j=1, 2, . . . , m) is determined by P.sup.j.sub.0 driven with E.sup.j and S, obtaining multiple alternate random segments b.sup.j.sub.i,s(l<=i<=m; j=1, 2, . . . , m) by each alternate random sequence B.sup.j (j=1, 2, . . . , m), and then obtaining the seed segment bs by performing orderly paired XOR on the obtained m Multi-alternate random segments b.sup.j.sub.i,s (l<=i<=m; j=1, 2, . . . , m), wherein in the process of XOR, it continues with the bit of any B.sup.j from the starting of B.sup.j when the last bit of the B.sup.j is reached, until reaching a desired length of the seed bit segment b.sub.i,s (l<=i<=m); (2) determining the corresponding bit segment of the seed random sequence B.sub.i (l<=i<=m) from the bit segment b.sub.s-1 of the previous step by substituting functions P, L, F, J, C and A for corresponding functions for generating a pseudo-random reconstruction element in (1), constructing the seed random sequence B.sub.i (l<=i<=m) segment by segment with the manner in (1), and changing the length of the generated seed random sequence B as desired; (3) for a plurality of seed random sequences B.sub.i (i=1, 2, . . . , m), repeating the above steps (1) and (2) to obtain different seed random sequences B.sub.i (i=1, 2, . . . , m).
10. The sequence encryption method accompanied with adjustable randomly-reconstructed key according to claim 1, characterized by: the feature quantity S participating in the pseudo-random reconstruction being a constant or a variable of a function, a plurality of constants or variables of the function or an integration of the plurality of constants or variables of the function: (1) in the encryption process, P function, L function, F function, J function, C function and A function all allowing to use a plurality of S=S.sub.1, S.sub.2, S.sub.3, . . . , S.sub.m to participate in the pseudo-random reconstruction, and pseudo-randomly determining whether each S.sub.i is allowed to participate in the pseudo-random reconstruction by a manipulation function K randomly selecting k S.sub.i (i=1, 2, . . . , m) from the m S.sub.i to participate in calculating, k.ltoreq.m; (2) when S is a plurality of groups of feature quantities S.sup.r (r is a positive integer) for the pseudo-random reconstruction, supporting the sequence encryption/decryption for j series of plaintext based on r pairs of paired exclusive sequence keys B.sup.g (g=1, 2, . . . , r) of the common seed random sequence B.sub.i (i=1, 2, . . . , m), and when S is a plurality of groups of variables generated by a plurality of functions, supporting a plaintext sequence encryption/decryption architecture implemented based on multi-party paired exclusive sequence keys B.sup.q (q=1, 2, . . . , r) of the common seed random sequence B.sub.i(i=1, 2, 3, . . . , m).
Description
CROSS-REFERENCE TO RELATED APPLICATIONS
[0001] This application is a continuation of International Patent Application No. PCT/CN2018/082638, filed on Apr. 11, 2018, which claims the benefit of priority from Chinese Patent Application No. 201710249427.9, filed on Apr. 17, 2017. The contents of the aforementioned application, including any intervening amendments thereto, are incorporated herein by reference in its entirety.
TECHNICAL FIELD
[0002] The invention relates to the field of sequence cryptography in information security cryptography.
BACKGROUND OF THE PRESENT INVENTION
[0003] Encryption with the sequence cipher is a process of obtaining a cipher text by bitwise XOR of a pseudo-random sequence generated according to a seed key and a plaintext bit stream using a sequence cipher generator. The sequence cipher encryption method may encrypt plaintext of any length as long as the chaos degree of the generated sequence cipher is large enough. The density of the sequence cipher encryption depends on the randomness of the sequence key generated by the sequence cipher generator. When the probability of acquiring the sequence key is small enough, the probability that the cipher is deciphered is small enough.
SUMMARY
[0004] A concept called pseudo-random reconstruction in the present invention is first introduced: a function F has a value domain which covers a random sequence or other determined range and arguments which can comprise a number of random values. A process for obtaining a target random sequence segment by segment, where segment constructed via calculating the start positions of source bit segments, the lengths of source bit segments, and some random value which associated or unassociated with source random sequence, substituting them into the function to obtain a target random bit segment.
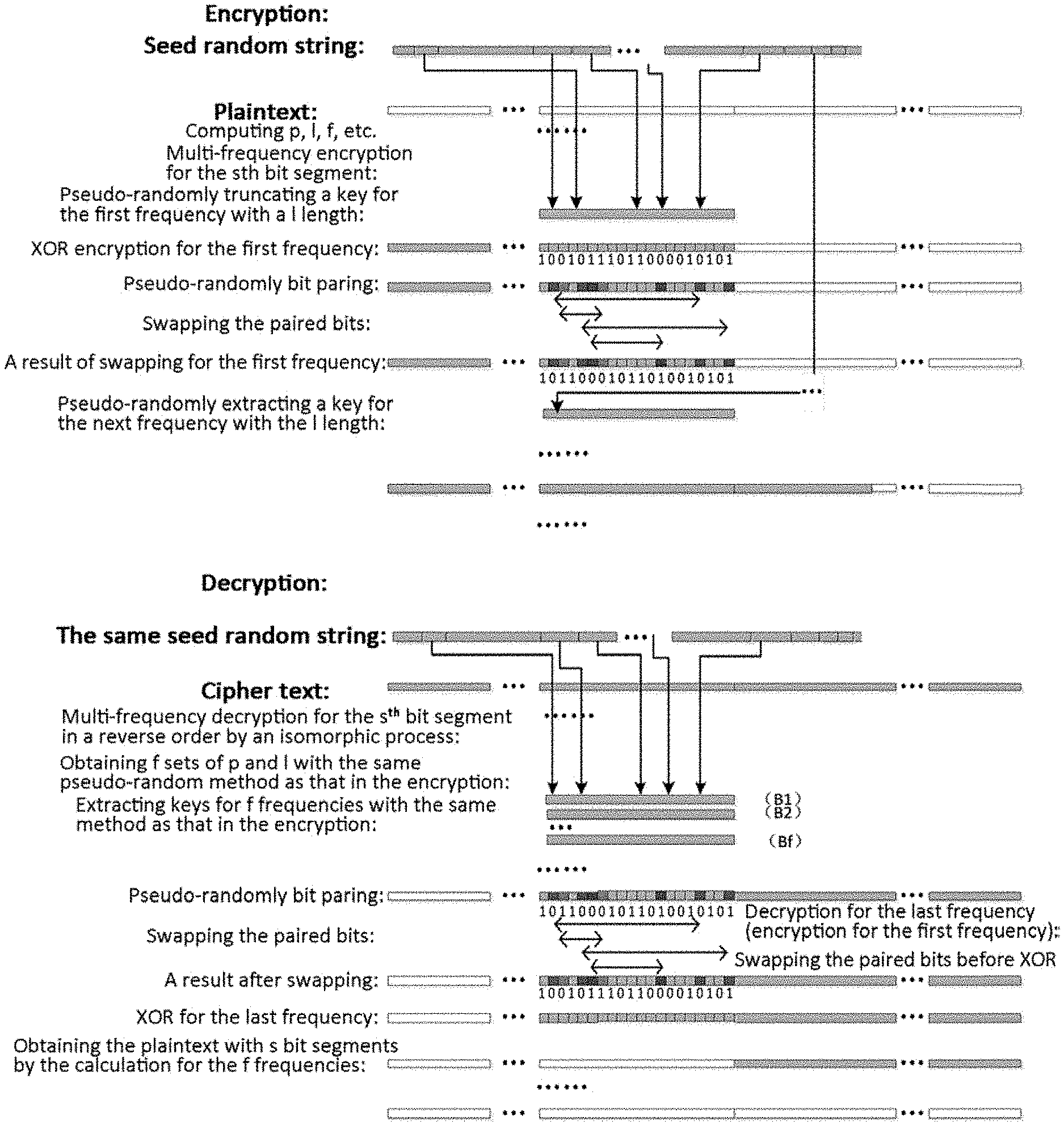
[0005] The purpose of the present invention is to implement sequence encryption by generating a seed random sequence through pseudo-random construction using a random number called as engine for an existing random number sequence, and in turn, obtaining random key bit segments from the seed random sequence through pseudo-random reconstruction step by step. The pseudo-random reconstruction process is accompanied throughout the encryption process, where in each step, the key bit segment selected by the random number obtained through the pseudo-random reconstruction in the previous step is used for XOR encryption with the plaintext bit segment in the current step. The key bit segments in the steps are combined into an encryption key at current time. Random reconstruction in each step may have a current random bit segment for which a feature number participates in the manipulation of the seed sequence, and the entire reconstruction process presents a chaotic morphology determined by the randomness of the seed sequence manipulated by the feature number. A function sequence is formed by the random number sequence reconstruction function as the encryption process proceeds. The function sequence may be adjusted by the secret rules agreed by the encryption and decryption parties. An instant key sequence obtained by manipulating the random seed sequence using the function sequence presents randomness and concealment, and has the effect of approximate one chaotic codebook per time.
[0006] Another important purpose of the present invention is to take advantage of the transitivity of a XOR operation, such that in each XOR step, a multi-frequency XOR is performed by a random number of times determined by the value of the key bit segment in the previous step and the constructed corresponding plurality of key bit segments. This random multi-frequency XOR manipulated by the pseudo-random reconstruction enables the entire encryption process to present random nonlinear morphology with variable frequencies. Further, by a means of pseudo-randomly determining the length of the bit segment in the encryption process, the plaintext bit segment and the key bit segment can be pseudo-randomly extended between frequencies in the multi-frequency XOR, achieving an encryption effect of each bit segment of the cipher text being associated with each other.
[0007] The two basic principles described above are further expressed as follows:
[0008] Infinite pseudo-random reconstruction is carried out on the finite random sequence to construct an infinite random sequence. Let B be as follows: b.sub.1, b.sub.2, b.sub.3, . . . , b.sub.n which is an infinite binary random sequence with enough large size. Assuming b.sub.n+1=b.sub.i1, b.sub.n+2=b.sub.i2, . . . b.sub.2n+1=b.sub.j1, b.sub.2n+2=b.sub.j2, . . . ; i,j<n. B is pseudo-randomly reconstructed with a random number sequence L=L.sub.1, L.sub.2, . . . to obtain B={b.sub.i1+1, b.sub.i1+2, b.sub.i1+3, . . . , b.sub.i1+L1}, {b.sub.i2+1, b.sub.i2+2, b.sub.i2+3, . . . , b.sub.i2+L2}, . . . where L.sub.1, L.sub.2, . . . are constructed based on the value of the bit segment of B in the previous step. Thus, B is an infinite random sequence b.sub.1, b.sub.2, b.sub.3, . . . . This process, called as pseudo-random reconstruction in the present invention, is accompanied in the XOR process of B and plaintext to implement chaos of whole bits in the random sequence B. The run of elements in the random sequence B is more chaotic when above B={b.sub.i1,1, b.sub.i1,2, b.sub.i1,3, . . . , b.sub.i1,L1}, {b.sub.i2,1, b.sub.i2,2, . . . , b.sub.i2,L2}, . . . are selected by pseudo-random hopping or no hopping with alternative bit segments B.sup.j={b.sup.j.sub.i1,1, b.sup.j.sub.i1,2, b.sup.j.sub.i1,3, . . . , b.sup.j.sub.i1,L1}, {b.sup.j.sub.i2,1, b.sup.j.sub.i2,2, b.sup.j.sub.i2,3, . . . , b.sup.j.sub.i2,L2}, . . . one or more random sequences and then are each paired orderly to XOR.
[0009] When a certain bit segment of plaintext m.sub.s={m.sub.s1, m.sub.s2, m.sub.s3, . . . , m.sub.sL} is multi-XOR with finite b.sub.s1={b.sub.i1, b.sub.i2, b.sub.i3, . . . , b.sub.iL}, b.sub.s2={b.sub.j1, b.sub.j2, b.sub.j3, . . . , b.sub.jL}, . . . , c.sub.s=(m.sub.s.sym.b.sub.s1).sym.b.sub.s2, . . . , the plaintext can be recovered by the alike multi-XOR of above result and the keys (b.sub.s1, b.sub.s2, . . . ), m.sub.s=(c.sub.s.sym.b.sub.s1).sym.b.sub.s2, . . . . When the frequency of the multi-XOR is determined pseudo-randomly by the random value of key bit segment or associated bit segment in the previous step and is randomly distributed in the encryption process, the XOR process for the plaintext presents a nonlinear morphology with variable frequencies.
[0010] In order to ensure the concealment and chaos degree of the keys, the present invention provides a method of pseudo-random reconstruction of a seed random sequence B in which a drive random number E privately agreed by the encryption and decryption parties participates. With the method, it makes the encryption key more chaotic and hidden, while the seed random sequences employed in encryption at different times on basis of the same alternate random sequence present randomness variation. The present invention also provides the feature number S specific to each encrypted user to participate in above pseudo-random reconstruction. This makes the seed random sequences of different users on basis of the same alternate random sequence present randomness variation.
[0011] The pseudo-random reconstruction method of the present invention is applicable to both the pseudo-random reconstruction process of the seed random sequence B and the pseudo-random reconstruction process of the key B, and the pseudo-random reconstruction can employ a combination of the following methods (1) through (13) according to the density needs:
[0012] (0) defining B.sup.j={b.sup.j.sub.1, b.sup.j.sub.2, . . . , b.sup.j.sub.n} as an alternative random sequence and B.sub.i={b.sub.i,1, b.sub.i,2, . . . , b.sub.i,n} as a seed random sequence (i may be omitted when there is only one seed random sequence), B={b.sub.1, b.sub.2, . . . , b.sub.n};
[0013] (1) determining a starting bit b.sup.0.sub.0 (or b.sub.0) in an agreed manner (e.g., by an operation participated by the E and/or S) and truncating the target random sequence B (or B) by forward/backward shifting any source random sequence B.sup.0 (or B) by a fixed length;
[0014] (2) obtaining the target random sequence B (or B) by orderly paring segments from more than one source random sequences B.sup.j (or B.sub.i) to XOR, where the segments are obtained by forward/backward shifting the source random sequences by the fixed length with the start bit b.sup.j.sub.k (or b.sub.i,h) determined in the agreed manner (e.g., by an operation participated by the E and/or S) respectively;
[0015] (3) obtaining the target random sequence B (or B) by paring segments from one or more source random sequences B.sup.j (or B.sub.i) one by one to multi-frequency XOR, where the segments are obtained by forward/backward shifting the source random sequences by the fixed length with the start bit b.sup.j.sub.k (or b.sub.i,h) determined in the agreed manner (e.g., by an operation participated by the E and/or S) respectively;
[0016] (4) after determining the value b.sup.0'.sub.0 (or b'.sub.0) of the start bit of the segments in the agreed manner, for any source random sequence B.sup.j (or B), performing the following operations according to the value b.sup.0'.sub.s-1 (or b'.sub.s-1) of the target random bit segment or associated segment (e.g., a corresponding bit segment of the cipher text) in the previous step: {circle around (1)} determining the start bit p of the target bit segment b.sup.j.sub.s (or b.sub.s) in the source random sequence in the current step with a positioning function P; {circle around (2)} determining the length l of the source random bit segment b.sup.0.sub.s (or b.sub.s) and the target random bit segment b.sup.0.sub.s (or b.sub.s) in the current step with a length determining function L; and {circle around (3)} substituting the position and/or length in above (1) with the start position and/or length of the random source bit segment pseudo-random constructed in {circle around (1)} and/or {circle around (2)} to truncate the target random bit segment;
[0017] (5) after determining the value b.sup.j'.sub.0 (or b.sub.i'.sub.0) of the start bit of the segments in the agreed manner, for more than one source random sequences B.sup.j (or B.sub.i), performing the following operations according to the value b.sup.j'.sub.s-1 (or b.sub.i'.sub.s-1) of the target random bit segment or associated segment in the previous step: {circle around (1)} determining the start bit b.sup.j.sub.s (or b.sub.i,s) in each of the source random sequences with the positioning function P respectively; {circle around (2)} determining 1 of each of the source random bit segments in the current step with the length determining function L; and {circle around (3)} substituting the position and/or length in above (1) with the start position and/or length of each of the random source bit segments pseudo-random determined in {circle around (1)} and/or {circle around (2)} to orderly pair each of segments one by one to perform XOR thereby obtaining the target random bit segment b.sub.s (or {circle around (b.sub.s)});
[0018] (6) after determining the value b.sup.i'.sub.0 (or b.sub.i'.sub.0) of the start bit of the segments in the agreed manner, for more than one source random sequences B.sup.j (or B.sub.i), performing the following operations according to the value b.sup.j'.sub.s-1 (or b.sub.i'.sub.s-1) of the target random bit segment or associated segment in the previous step: {circle around (1)} determining the start bit b.sup.j.sub.s (or b.sub.i,s) in each of the source random sequences with the positioning function P respectively; {circle around (2)} determining 1 of each of the source random bit segments in the current step with the length determining function L; {circle around (3)} determining frequency value f.sup.j (or f.sub.i) with a frequency determining function F; obtaining the target random bit segment by performing the processes in {circle around (4)} and {circle around (5)} below: {circle around (4)} selecting the source random bit segment b.sup.j,1.sub.s, b.sup.j,1+1.sub.s, b.sup.j,1+2.sub.s, . . . , b.sup.j,1+fj.sub.s (or b.sub.i.sup.1.sub.s, b.sub.i.sup.1+1.sub.s, b.sub.i.sup.1+2.sub.s, . . . , b.sub.i.sup.1+fi.sub.s) by the manner of forward shifting each of the source random sequences or the manners in above {circle around (1)} and/or {circle around (2)} substituting those in (1) or (2) to orderly pair each of the segments one by one to perform the multi-frequency XOR, and the result being taken as the target random bit segment b.sub.s (or b.sub.s); or {circle around (5)} for each of the source sequences, selecting the frequency f.sup.j (or f.sub.i) for XOR by {circle around (3)}, and then selecting the source random bit segment b.sup.j,1.sub.s, b.sup.j,1+1.sub.s, b.sup.j,1+2.sub.s, . . . , b.sup.j,1+fj.sub.s (or b.sub.i.sup.1.sub.s, b.sub.i.sup.1+1.sub.s, b.sub.i.sup.1+2.sub.s, . . . , b.sub.i.sup.1+fi.sub.s) by the manner of forward shifting or the manners in above {circle around (1)} and/or {circle around (2)} substituting those in (1) or (2) or (3) to pair each of the segments one by one to perform the multi-frequency XOR (the XOR frequencies for each of b.sup.j.sub.s (or b.sub.i,s) are different), and the result being taken as the target random bit segment;
[0019] (7) a further pseudo-random reconstruction step of enhancing chaos degrees for pseudo-random reconstruction in (4), (5) and (6): constructing a bit hopping function J (whose argument is 1 random values determined by the key bit segment or associated bit segment in the previous step, with the 1 values range being J(b.sup.j'.sub.s-1) or J(b.sub.i.sup.'.sub.s-1), 0.ltoreq.J(b.sup.j'.sub.s-1) or 0.ltoreq.J(b.sub.i.sup.'.sub.s-1) for selecting the bit segment of the source random sequence in the current step, starting from the source random sequence position p determined by P, according to the hopping function, the bits of the key bit segment in the current step being extracted bit by bit with hopping (when J(b.sup.j'.sub.s-1)>0) or without hopping (when J(b.sub.i.sup.'.sub.s-1)=0) until the length l of the target bit segment in the current step determined by L is reached;
[0020] (8) another enhanced pseudo-random reconstruction to determine the current step source random bit segment b.sup.j.sub.s-1 or b.sub.is-1 or b.sup.j,fj.sub.s-1 or according to one of the manners in above (4) or (5) or (6) or (7) to, frequency by frequency, select the source random sequence bit segment to perform XOR on the target bit segment one by one;
[0021] (9) a further enhanced pseudo-random reconstruction operation for the pseudo-random reconstruction in above (8): in encryption, the target bit segment after XOR per frequency (in decryption, the source bit segment before XOR per frequency) being swapping by the pairing bit determined by the pairing function C according to the random value of the key bit segment or associated bit segment in the previous step;
[0022] (10) a further enhanced pseudo-random reconstruction form for the pseudo-random reconstruction in above (8): for each frequency, determining the increase value of the current frequency key bit segment by the extension function A according to the value of the frequency key bit segment or associated bit segment in the previous step, where the source bit segment increases correspondingly with the increase value, and so on to increase the length of bit segment for XOR frequency by frequency; after the operation of the current step is completed, the increase operation part of the target bit segment is backfilled to the corresponding position of the source sequence. (the starting position of the source target bit segment in the next step is still stepped by the target bit segment of the first frequency); as a result, the increased bits have been subjected to several XOR pretreatments before the next XOR, since the pseudo-random reconstruction of these XOR pretreatments in the decryption process is still determined by the value of the same key bit segment or corresponding bit segment, its inverse operation process is an reverse order process; this enhanced form enabling the accompanied pseudo-random reconstruction to present the encryption effect of being associated with each other;
[0023] (11) a different form of flexible pseudo-random reconstruction with same principle for the pseudo-random reconstruction in (4), (5), (6), (7), (8), (9), (10): the bit segment determined by P, L, F, J, C and A are changed to be extracted from another random sequence or extracted from a different source random sequence; the effect of constructing the random key in such a random bit still has concealment and chaotic characteristics;
[0024] (12) in above (4), (5), (6), (7), (8), (9), (10), the P, L, F, J, C and A functions may add S as an argument to implement a pseudo-random reconstruction with S features, where S may be one or more constants, variables of a function, or a combination thereof (13) the method for obtaining each bit segment of the target sequence can be implemented by combining above pseudo-random reconstruction manners in an agreed manner.
[0025] The encryption process of the present invention is carried out as follows:
[0026] (S0) preparing basic data
[0027] (S0.1) pre-generating one or more groups of alternative seed random sequences: B.sup.1: b.sup.1.sub.1, b.sup.1.sub.2, b.sup.1.sub.2, . . . , b.sup.1.sub.n; B.sup.2: b.sup.2.sub.1, b.sup.2.sub.2, b.sup.2.sub.3, . . . , b.sup.2.sub.n; . . .
[0028] (S0.2) the agreed physical feature quantity S (can be one element, multiple elements, or the integration of multiple elements in a constant set and/or variable set) being used as the feature weight of the encrypted object to participate in the operations of function P, L, F, J, C, and A, where a number of drive engine random numbers E1, E2, . . . that match the alternate random sequences are generated (randomly selected from generated sets) for each encryption, as a trigger element or control elements for the pseudo-random construction (determining the starting state of the pseudo-random construction);
[0029] (S0.3) pseudo-randomly-reconstructed seed random sequence B={b.sub.1, b.sub.2, b.sub.3, . . . , b.sub.s, . . . , b.sub.n} which may be one or more sequences and can be pseudo-randomly constructed one by one with any of the following methods when more than one seed random sequence is used:
after locating s.sub.0 with E, constructing b.sub.i=b.sup.J.sub.(S.sub.0.sub.+i)%n i=1, 2, 3, . . . , n by forward shifting (1)
or
after locating s.sub.0 with E, randomly constructing b.sub.s=Build(b.sup.J'.sub.(s-1)) s=1, 2, 3, . . . , n (1')
or
after locating s.sub.0 with E, randomly multi-frequency constructing b.sub.s=Build(b.sup.fJ'.sub.(s-1)) s=1, 2, 3, . . . , n (1'')
[0030] where:
[0031] b.sup.J.sub.S.sub.0.sub.+i)%n represents one of the pseudo-random constructions in (1), (2), (3), and % n represents continuing from the start after forward shifting to the end of the random sequence;
[0032] Build(b.sup.J'.sub.(s-1)) represents pseudo-randomly constructing the seed random bit segment by arguments of P, L, F, and J obtained by one of (4), (5), (6), (7), (8), (9), (10), and (11) in conjunction with S, E.sup.J;
[0033] bs=Build(b.sup.fJ'.sub.s-1)) represents pseudo-randomly multi-frequency constructing the seed random bit segment by arguments of P, L, F, and J obtained by one of (4), (5), (6), (7), (8), (9), (10), and (11) in conjunction with S, E.sup.J;
[0034] (S1) calculating L.sub.s:
[0035] (S1.1) when the plaintext stepped to L.sub.s is less than or equal to the remaining plaintext length,
L.sub.s=L(S, b'.sub.s-1), (2)
[0036] where L is a function of calculating a new bit segment length, for s=1, taking any b'.sub.0 with L(S, b'.sub.s-1) being not 0 (e.g., b'.sub.(E+S)%n);
[0037] b'.sub.s represents the random value carried by the bit segment b.sub.s (the same below);
[0038] (S1.2) when the plaintext stepped to L.sub.s is greater than the remaining plaintext length, the processing for the last bit segment is performed:
L.sub.s=remaining plaintext length (3)
[0039] (S2) calculating F.sub.s
F.sub.s=F(S, b'.sub.s-1), (4)
[0040] where F is a function of calculating the XOR frequency of the S.sup.th bit segment;
[0041] for s=1, same as (S1.1);
[0042] (S3) calculating P.sub.s
P.sub.s=P(S,b'.sub.s-1), (5)
[0043] where P is a function of calculating the start bit of a new bit segment;
[0044] for s=1, same as (S1.1);
[0045] (S4) obtaining Fs bit segments from B for multi-frequency repeated XOR
b.sup.f.sub.s=P(S,b.sup.f-1'.sub.s) (6)
[0046] where P is a function of calculating the start bit of B bit segment for each frequency of the multi-frequency XOR;
[0047] b.sup.f.sub.s is the current frequency key bit segment (the same below);
[0048] b.sup.f'.sub.s is the random value determined by the current frequency (the same below); for S=1 and f=1, same as (S1.1);
[0049] (S5) performing pseudo-random reconstruction to obtain b.sub.s:
[0050] (S5.1)
b.sub.s=b.sup.qs.sub.s(q,p.sub.s,l.sub.s) where 0<q.sub.s<F.sub.s; (7)
[0051] where b.sup.qs.sub.s refer to qth new bit segments of B determined by P, L, F, J based on the bit segment calculation unit in the previous step;
[0052] or
[0053] (S5.2)
b.sub.s=CAL(q.sub.s,b.sup.qs.sub.s) (7')
[0054] where CAL(qs, b.sup.qs.sub.s) represents to reconstruct the bit segment based on q.sub.s and b.sup.qs.sub.s;
[0055] (S6) encrypting plaintext bit segment
[0056] (S6.1) taking the stepping size of m.sub.s same as the stepping size of b.sub.s, selecting m.sub.s=m.sub.s-1+L.sub.s-1 by forward shifting,
[0057] (S6.2) performing multi-frequency XOR in the current step
c.sub.s=c.sup.1.sub.sc.sup.2.sub.s . . . c.sup.k.sub.s . . . c.sup.h.sub.s . . . c.sup.Fs.sub.s= . . . (((m.sub.s.sym.b.sup.1.sub.s).sym.b.sup.2.sub.s).sym.b.sup.3.sub.s) . . . .sym.b.sup.Fs.sub.s (8)
[0058] (S6.3) swapping the paired bits selected with the pairing function C for c.sup.f.sub.s between XORs at each frequency
c.sup.f.sub.s=c.sup.f1.sub.sc.sup.f2.sub.s. . . c.sup.h.sub.s. . . c.sup.k.sub.s. . . c.sup.Fs.sub.s, which represents the paired bits of pseudo-random in operation at f.sup.th frequency (8')
[0059] (note that 1. (8') merely illustrates an example of swapping paired bits
[0060] 2. the decryption process for above swapping by pairing is implemented by isomorphic reverse order:
c.sup.f.sub.s=c.sup.f1.sub.sc.sup.f2.sub.s . . . c.sup.h.sub.s . . . c.sup.k.sub.s . . . c.sup.Fs.sub.s (8'')
m.sub.s=m.sup.1.sub.sm.sup.2.sub.s . . . m.sup.k.sub.s . . . m.sup.h.sub.s . . . m.sup.Fs.sub.s( . . . (c.sub.s.sym.b.sup.1.sub.s).sym.b.sup.2.sub.s).sym.b.sup.3.sub.s) . . . .sym.b.sup.Fs.sub.s) (8''')
[0061] (S6.4) calculating for increasing length of bit segments in operation at each frequency
[0062] (S6.4.1) for (8)/(8'), determining the increase value with the increase function A for c.sup.f.sub.s and b.sup.f.sub.s between XORs in each of steps, and increasing the bit segment by a subsequent bit of the plaintext, selecting the increased key bit in the same pseudo-random method as before, thereby increasing the XOR frequency by frequency
[0063] (S6.4.2) truncating bit segment of the current step cipher text in the length determined by L.sub.s
[0064] (S6.4.3) substituting the increase of the accumulated increased XOR bit segment for the corresponding bit of the original plaintext
[0065] (S7) stepping
S=S+1 (9).
DESCRIPTION OF THE INVENTION FEATURES
[0066] (1) B is derived from a pseudo-random reconstruction of different random bit segments of random sequences B.sup.1, B.sup.2, . . . , and is still a random sequence. Since the elements of the random sequences are independent of each other, the sequence keys obtained by the reconstruction for the random sequences depended on the variations in the position, the length and the frequency of the random elements are a random sequence as well. This target random key B depended on the seed random sequence B has concealment.
[0067] (2) The generation process of the random secret key is generated in a staggered manner accompanying the encryption process, that is: the position, the length and the next XOR frequency of key in the next step as well as the hopping control in selecting each key bit, the swapping control for target bit segment of each frequency and the increasing control for bit segment between frequencies are determined by the position function, the length determining function, the frequency determining function, the hopping function, the swapping function and the increasing function according to the value of the random number at the position of target sequence or associated position in the previous step, and the pseudo-random reconstruction process is accompanied throughout the encryption process.
[0068] (3) A nonlinear mixed morphology of the encryption process is presented based on XOR process with variable frequencies of orderly transitivity of XOR operation.
[0069] (4) The logic process of reconstructing the source random seed can be adjusted by the present methods. In particular, the reconstruction function is extended to a functional, and the chaos degree of the random element runs can be increased.
[0070] (5) The participation of the engine random number E and the feature quantity S enables each encryption process and each encrypted object having uniqueness. The change in S will improve the application space of the present invention:
[0071] (5.1) in the encryption process, P, L, F, J, C and A allow the use of multiple S=S.sub.1, S.sub.2, S.sub.3, . . . S.sub.n to participate the pseudo-random reconstruction, and the value of bit segment or associated bit segment in the previous step is used to control whether each S.sub.i participates the pseudo-random reconstruction or not;
[0072] (5.2) when S is a series of constants S.sup.j or a series of variables generated by a plurality of functions, a plaintext sequence encryption architecture implemented with an exclusive sequence key B.sup.f based on the same alternative random sequence B.sup.J is supported.
[0073] (6) As one of the application selection, the alternative seed random sequences B.sup.1, B.sup.2, . . . do not have to be generated during the encryption process (e.g., changed by a secret convention), so that the alternative seed random sequences can be previously stored at parties in the communication together with the manipulation functions P, L, F, J, C, A and S as a secret contract of the encryption and decryption parties. Such a contract can be altered and easy to be maintained.
[0074] (7) In practical applications, the plaintext can be prefixed and/or suffixed with a piece of chaotic code to increase the difficulty of cracking.
[0075] (8) The pseudo-random reconstruction process in each step has the same computation amount, and the complexity of the whole encryption process is related to n.
[0076] (9) Since P, L, F, J, C and A functions use the random value of key bit segment or associated bit segment in the previous step as argument for computing and can randomly use a modulo operation, S is impossible to be back-stepped within the polynomial time complexity (other manipulations that need to be introduced also have this characteristic).
DETAILED DESCRIPTION OF EMBODIMENTS
[0077] The invention will be further illustrated by the following examples.
[0078] Embodiment 0:
[0079] (S0.1) Length n of a random sequence is selected as 2048; one group of alternative random seed sequences are selected: B.sup.1: b.sup.1.sub.1, b.sup.12, b.sup.1.sub.3, . . . , b.sup.1.sub.n; for any determined number of engine E1, P=(E+S)% 2048 is used to obtain a start position p of B.sup.1. B.sup.1 is extracted starting from p by forward shifting and if b.sup.1.sub.n is reached the extraction continues from b.sup.1.sub.0, thereby obtaining an instant random seed sequence B={b.sup.1.sub.p, b.sup.1.sub.p1+1, . . . , b.sup.1.sub.p1+2, b.sup.1.sub.n, b.sup.1.sub.1, . . . , b.sup.1.sub.p-1}.
[0080] (S0.2) A unit length for calculating of each step is selected as 8 (1 byte), so (1) the corresponding maximum random value is 255; (2) the length of B is 256 bytes and a character array B [256] with 256 elements can be made up.
[0081] (S1) It defines L.sub.s=8.
[0082] (S2) It defines F.sub.s=1.
[0083] (S3) It calculates stepping amount of a plaintext bit segment as P(m.sub.s)=P(m.sub.s-1)+L.sub.s-1=P(m.sub.s-1)+8, and stepping amount of a key bit segment as P(b.sub.s)=(P(b.sub.s-1)+L.sub.s-1)%2048=(P(b.sub.s-1)+8)% 2048.
[0084] (S4) Stepping amount of a bit segment in B is 0 in a multi-frequency repeat XOR (because F.sub.s=1).
[0085] (S5) b.sub.s=b.sub.s(P.sub.s, L.sub.s, F.sub.s)=b.sub.s-1+8.
[0086] (S6) XOR in the current step is performed c.sub.s=m.sub.s.sym.b.sub.s.
[0087] (S7) S=S+1.
[0088] The decryption process is the same as the encryption process, but only (S6) is changed to (S6'):
[0089] (S6') m.sub.s=c.sub.s.sym.b.sub.s.
[0090] Embodiment 0 implements the simplest flow accompanied with pseudo-random reconstruction. Although practical significance is not large, the overall structure of the invention is shown.
EMBODIMENT 1
[0091] (S0.1) Length n of a random sequence is selected as 2048; two groups of alternative random seed sequences are selected: B.sup.1: b.sup.1.sub.1, b.sup.1.sub.2, b.sup.1.sub.3, . . . , b.sup.1.sub.n; B.sup.2: b.sup.2.sub.1, b.sup.2.sub.2, b.sup.2.sub.3, . . . , b.sup.2.sub.n; for any determined number of engines E1, E2, and any determined feature number SP=(E+S)% 2048 is used to obtain start positions p1 and p2 of B.sup.1 and B.sup.2. B.sup.1 and B.sup.2 are paired to XOR by forward shifting starting from p.sub.1 and p.sub.2 respectively, thereby obtaining an instant random seed sequence B={b.sup.1.sub.p1.LAMBDA.b.sup.2.sub.p2, b.sup.1.sub.(p1+1)%2048.LAMBDA.b.sup.2.sub.(p2+1)%2048), . . . b.sup.1.sub.(p1+1 )%2048.LAMBDA..sup.2.sub.(p1+1)%2048}={b.sub.1, b.sub.2, b.sub.3, . . . }.
[0092] (S0.2) A unit length for calculating of each step is selected as 8 (1 byte), so (1) the corresponding maximum random value is 255; (2) the length of B is 256 bytes and a character array B [256] with 256 elements can be made up.
[0093] (S1) It defines L.sub.s.
[0094] (S1.1) When the remaining plaintext stepped to is greater than or equal to L.sub.s, L.sub.s=B[P.sub.s-1% 256]% 16+1.
[0095] (S1.2) When the remaining plaintext stepped to is shorter than L.sub.s, it sets L.sub.s=the remaining plaintext length.
[0096] (S2) It defines F.sub.s=B[P.sub.s-1/8]% 2+1.
[0097] (S3) Stepping of a plaintext bit segment is P (m.sub.s)=P(m.sub.s-1)+L.sub.s-1, and stepping of a key bit segment is P(b.sub.s)=(P(b.sub.s-1)+L.sub.s-1)% 2048.
[0098] (S4) Stepping of a bit segment in B is 0 in a multi-frequency repeat XOR is P(b.sup.f.sub.s)=(P(b.sup.f-1.sub.s)+L.sub.s)% 2048.
[0099] (S5) b.sub.s=b.sub.s(P.sub.s, L.sub.s) when F.sub.s=1; or b.sup.f(2).sub.s=b.sup.f(2).sub.s(P.sub.s, L.sub.s) when F.sub.s=2.
[0100] (S6) XOR in the current step is C.sub.s=m.sub.s.sym.b.sub.s when F.sub.s=1;
[0101] or C.sub.s=(m.sub.s.sym.b.sub.s).sym.b.sup.f(2).sub.s when F.sub.s=2,
[0102] where the step size of m.sub.s is taken same as that of b.sub.s.
[0103] (S7) S=S+1.
[0104] The decryption process is the same as the encryption process, but only (S6) is changed to (S6'):
m.sub.s=c.sub.s.sym.b.sub.s when Fs=1; (S6')
or C.sub.s=(m.sub.s.sym.b.sub.s).sym.b.sup.f(2).sub.s when F.sub.s=2.
[0105] P(m.sub.s), P(b.sub.s) and P(b.sup.f.sub.s) are the start bits of plaintext bit in the current step, key bit in the current step and key bit at the current frequency, respectively.
[0106] % 2048 represents continuing from beginning when the last bit is reached.
[0107] Embodiment 1 implements a simple pseudo-random reconstruction process with variable length and variable frequencies by forward shifting.
EMBODIMENT 2
[0108] The following changes are made to Embodiment 1.
[0109] (S0.1.sup.2) Length n of a random sequence is selected as 524288; two groups of alternative random seed sequences are selected: B.sup.1: b.sup.1.sub.i, b.sup.1.sub.2, b.sup.1.sub.3, . . . , b.sup.1.sub.n; B.sup.2: b.sup.2.sub.1, b.sup.2.sub.2, b.sup.2.sub.3, . . . , b.sup.2.sub.n, for any determined number of engines E1 and E2, p.sub.1 and p.sub.2 are calculated with P being p.sub.s(B.sup.i)=(p.sub.s-1(B.sup.i)*12345+1103515245+E.sub.i+S)% 524288; a random seed sequence is calculated as B={b.sub.1, b.sub.2, b.sub.3, . . . }={b.sup.1.sub.p1.LAMBDA.b.sup.2.sub.p2, b.sup.1.sub.(p1+1)%524288.LAMBDA.b.sup.2.sub.(p2+1)%524288, . . . , b.sup.1.sub.(p1+n)%524288.LAMBDA.b.sup.2.sub.(p2+n)%524288}.
[0110] (S0.2.sup.2) A unit length for calculating of each step is selected as 16 (2 bytes), so (1) the corresponding maximum random value is 65535; (2) the length of B is 655356 bytes and a character array B [66536] with 65536 elements can be made up.
[0111] (S1.1.sup.2) It defines L.sub.s=B[P.sub.s-1% 65536]% 68+64 when the remaining plaintext stepped to is greater than or equal to L.sub.s.
[0112] (S1.2.sup.2) When the remaining plaintext stepped to is less than L.sub.s, it sets L.sub.s=the remaining plaintext length.
[0113] (S2.sup.2) It defines F.sub.s=(S+B[P.sub.s-1% 65536])% 8+16.
[0114] (S3.sup.2) The position for B in the embodiment (S3) is changed as
P(b.sub.s)=(B[(P(b.sub.s-1)+S)% 65536]+1103515245)% 524288.
[0115] (S4.sup.2) The position for B in the embodiment (S4) is changed as
P(b.sup.f.sub.s)=(B[(P(b.sup.f-1.sub.s)+S)% 65536]+1103515245)% 524288,
f=1, 2, . . . , F.sub.s.sup.-; P(b.sup.f.sup.(1).sub.s)=P(b.sub.s).
[0116] By above modifications, (1) the XOR frequency of multi-frequency XOR is increased; (2) the chaos degree of selecting cipher bit segment is improved by changing the selection mode for bit segment of the key B from a forward shifting mode to a pseudo-random mode of determining the position based on a value in the previous step; (3) the modulus in (S1.1.sup.2) is 68 rather than 64 or 32, which allows the longest length for selecting bit segment to be more than twice of the shortest length.
[0117] The embodiment 2 implements the encryption process in which key in the current step is pseudo-randomly reconstructed by the random value of the key bit segment in the previous step.
EMBODIMENT 3
[0118] The following changes are made to Embodiment 2.
[0119] (S0.4.sup.3) A further random sequence B.sup.T is defined with length equal to that of B.
[0120] (S2.sup.3) It defines F.sub.s=(S+B[b'.sub.s-1% 65536])% 8+16.
[0121] (S3.sup.3) The positioning for B in the embodiment (S3.sup.2) is changed to position for B.sup.T:
P(b.sup.T.sub.s)=(B[(b'.sub.s-1+S)% 65536]+1103515245)% 524288.
[0122] (S4.sup.3) The positioning for B in the embodiment (S4.sup.2) is changed as
P(b.sup.T,.sup.f.sub.s)=(B[(b'.sup.f-1.sub.s+S)% 65536]+1103515245)% 524288;
f=1, 2, . . . , F.sub.s; P(b.sup.T,f.sup.(1).sub.s)=P(b.sup.T.sub.s).
[0123] By above modifications, the random value obtained from B to perform pseudo-random reconstruction for B.sup.T also allows B having concealment and chaotic characteristics.
[0124] Embodiment 3 implements the process of scheduling another random sequence from a random value obtained from the previous step to implement a pseudo-random reconstruction for key.
EMBODIMENT 4
[0125] The following changes are made to Embodiment 2.
[0126] (S0.4.sup.4) It defines the bit length to which the cipher text C is reached in the current step is c.sub.s.
[0127] (S1.1.sup.4) The length of bit segment is modified: L.sub.s=B[P.sub.s-1% 65536]% (c.sub.s-1/8)+64.
[0128] By above modifications, an XOR bit segment of B is selected by utilizing the progress of the generated cipher text without changing the concealment and chaotic characteristics of B.
[0129] Embodiment 4 implements the process of controlling the pseudo-random reconstruction for key according to the progress of the cipher text sequence.
EMBODIMENT 5
[0130] The following changes are made to Embodiment 2.
[0131] (S0.2.sup.5) A unit length for calculating of each step is selected as 20 (2.5 bytes), so the corresponding maximum random value is much greater than 65535; it is modulo 65536, and still distributed in array B [65536] in byte.
[0132] (S7.sup.5) The positioning function for B in (S3.sup.2) is selected by the formula i=(b'.sub.s-1*S)% 3 from the following three functions:
P[0](b.sub.s)=(B[(b'.sub.s-1+S)% 65536].sym.(B[c'.sub.s-1% 65536]))% 524288;
P[1](b.sub.s)=(B[(b'.sub.s-1/8]+(S*12347))% 524288;
P[2](b.sub.s)=(B[(b'.sub.s-1+S+1103515245)% 65536])% 524288;
[0133] where c'.sub.s-1 represents the value taken from a cipher text in the previous step in the agreed calculation unit, and the chaos degree of the key element run is further improved.
[0134] Note that (1) the decryption algorithm in this embodiment is modified, such that c'.sub.s-1 is the generated term of the corresponding construction function in encryption while c'.sub.s-1 is the source item of the corresponding construction function in decryption; (2) the cipher text bit segment is not used to construct the key bit segment, but instead is used to change the run of the key construction.
[0135] Embodiment 5 implements a run of ciphertext indirectly scheduling pseudo-random reconstruction for key.
EMBODIMENT 6
[0136] The following changes are made to Embodiment 2.
[0137] (S0.4.sup.6) It defines an array S[2]={cell number of a user; a user name;}.
[0138] (S0.5.sup.6) It defines K=S[b.sub.s-1% 2].
[0139] (S2.sup.6) It defines F.sub.s=(S[b'.sub.s-1% 2]+B[P.sub.s-1/8])% 8+16.
[0140] (S3.sup.6) The positioning for B in (S3.sup.2) is changed as
P(b.sub.s)=(B[(b'.sub.s-1+(S[b' .sub.s-1% 2]))% 65536])% 52428.
[0141] (S4.sup.6) The positioning for B in (S4.sup.2) is changed as
P(b.sup.f.sub.s)=(B[(b'.sup.f-1.sub.s+(S[b'.sub.s-1% 2]))%65536])%524288, f=1,2, . . . F.sub.s.
[0142] The chaos degree of the run of positioning and determining frequency is further improved.
[0143] Embodiment 6 implements the process of implementing the pseudo-random reconstruction for key from a random value obtained from the previous step and a plurality of feature values.
EMBODIMENT 7
[0144] The following changes are made to Embodiment 2.
[0145] (S0.1.sup.7) One group of alternative random seed sequences is added: B.sup.3: b.sup.3.sub.1, b.sup.3.sub.2, b.sup.3.sub.3, . . . , b.sup.3.sub.n. Another seed random sequence B2 is generated from B.sup.2 and B.sup.3 using the same method.
[0146] (S0.4.sup.7) It defines a seed sequence array B[2]={B.sub.1, B.sub.2}.
[0147] (S0.5.sup.7) It defines G=B[b.sub.s-1]% 2+1.
[0148] (S2.sup.7) It define F.sub.s=(S+B.sub.G[P.sub.s-1/8])% 8+16.
[0149] The following changes are made to Embodiment 6.
[0150] (S3.sup.7) The positioning for B in (S3.sup.2) is changed as
P(b.sub.s)=(B.sub.G[(b'.sub.s-1+(S[b'.sub.s-1%2]))%65536])%524288.
[0151] (S4.sup.7) The positioning for B in (S4.sup.2) is changed as
P(b.sup.f.sub.s)=(B.sub.G[(b'.sup.f-1.sub.s+(S[b'.sup.f-1.sub.s%2]))%655- 36])%524288.
[0152] The chaos degree of the run of positioning and determining frequency is further improved.
[0153] Embodiment 7 implements the process of pseudo-randomly selecting the seed random sequence reconstructed key in the current step from a plurality of seed random sequences.
EMBODIMENT 8
[0154] The following changes are made to Embodiment 2.
[0155] (S0.1.sup.8) One group of alternative random seed sequences is added: B.sup.3: b.sup.3.sub.1, b.sup.3.sub.2, b.sup.3.sub.3, . . . , b.sup.3.sub.n. Another seed random sequence B2 is generated from B.sup.2 and B.sup.3 using the same method.
[0156] (S0.4.sup.8) It defines a seed sequence array B[2]={B.sub.1, B.sub.2}.
[0157] (S0.5.sup.8) It defines G=B[b.sub.s-1% 2]+1.
[0158] (S2.sup.8) It define F.sub.s=(K+B.sub.G[P.sub.s-1/8])% 8+16.
[0159] (S3.sup.8) The positioning for B in (S3.sup.2) is changed as P(b.sub.s)=(B.sub.1[b'.sub.s-1% 65536]).sym.(B.sub.2[b'.sub.s-1% 65536]).
[0160] (S4.sup.8) The positioning for B in (S4.sup.2) is changed as P(b.sup.f.sub.s)=(B.sub.1[b'.sup.f-1.sub.s% 65536]).sym.(B.sub.2[b'.sup.f-1.sub.s% 65536]).
[0161] The chaos degree of the run of positioning and determining frequency is further improved.
[0162] Embodiment 8 implements the process of implementing pseudo-random reconstruction for key using a plurality of seed random sequences at the same time.
EMBODIMENT 9
[0163] The following changes are made to Embodiment 2.
[0164] (S0.1.sup.9) One group of alternative random seed sequences is added: B.sup.3: b.sup.3.sub.1, b.sup.3.sub.2, b.sup.3.sub.3, . . . , b.sup.3.sub.n. Another seed random sequence B.sup.2 is generated from B.sup.2 and B.sup.3 using the same method.
[0165] (S0.4.sup.9) It defines a seed sequence array B[2]={B.sub.1, B.sub.2}.
[0166] (S0.5.sup.9) It defines G=B[b'.sub.s-1% 2].
[0167] (S2.sup.9) It define F.sub.s=(B.sub.G[b'.sub.s-1/8])% 8+8.
[0168] (S3.sup.9) The positioning for B in (S3.sup.2) is changed as positioning for two seeds respectively P(b.sub.1.sub.,s)=B.sub.1[(b'.sub.s-1+S)% 65536], P(b.sub.2.sub.,s)=B.sub.2[(b'.sub.s-1 +S)% 65536].
[0169] (S4.sup.9) The positioning for B in (S4.sup.2) is changed as positioning for two seeds respectively P(b.sup.f.sub.1,s)=B.sub.1[(b'.sup.f-1.sub.s+S)% 65536], P(b.sup.f.sub.2, .sub.s)=B.sub.2[(b'.sup.f-1.sub.s+S)% 65536];
f=0,1, . . . , F.sub.s.
[0170] The encryption process is defined as:
[0171] (S6.sup.9) in the current step, c.sub.s=( . . . (m.sub.s.sym.b.sub.1,s).sym.b.sub.2,s.sym.b.sup.f2.sub.1,s).sym.b.sup.f2.- sub.2,s) . . . .sym.b.sup.Fs.sub.1,s).sym.b.sup.Fs.sub.2,s).
[0172] The chaos degree of the run of positioning and determining frequency is further improved.
[0173] The decryption process is the same as the encryption process, but only (S6.sup.9) is changed to (S6.sup.9'):
m.sub.s=( . . . (c.sub.s.sym.b.sub.1,s).sym.b.sub.2,s).sym.b.sup.f2.sub.1,s).sym.b.sup.f2- .sub.2,s) . . . .sym.b.sup.Fs.sub.1,s).sym.b.sup.Fs.sub.2,s. (S6.sup.9')
[0174] Embodiment 9 implements the process of scheduling multiple seed random sequences from a random value obtained from the previous step to directly perform multi-frequency XOR encryption on plaintext.
EMBODIMENT 10
[0175] The following changes are made to Embodiment 9.
[0176] (S5.sup.10) It implements key pseudo-random reconstruction with or without hopping.)
[0177] (S5.1.sup.10) It defines J.sup.1={j.sup.1.sub.1, j.sup.1.sub.2, . . . , j.sup.1.sub.L}, where j.sup.1.sub.1 is the first bit of B.sub.1[b'.sub.s-1] and the subsequence shifts forward in turn;
[0178] J.sup.2={j.sup.2.sub.1, j.sup.2.sub.2, . . . , j.sup.2.sub.L}, where j.sup.2.sub.1 is the first bit of B.sub.2[b'.sub.s-1] and the subsequence shifts forward in turn;
[0179] J.sup.f,1={j.sup.f,1.sub.1, j.sup.f,1.sub.2, . . . , j.sup.f,1.sub.L}, where j.sup.f,1.sub.1 is the first bit of B.sub.1[b'.sup.f-1.sub.s] and the subsequence shifts forward in turn;
[0180] J.sup.f,2={j.sup.f,2.sub.1, j.sup.f,2.sub.2, . . . , j.sup.f,2.sub.L}, where j.sup.f,2.sub.1 is the first bit of B.sub.2[b'.sup.f-1.sub.s] and the subsequence and the subsequence shifts forward in turn;
[0181] f=1, 2, . . . , F.sub.s (note that the argument domain of J is not B.sub.1[(P(b.sub.2-1)+16)% 65536].)
[0182] (S5.2.sup.10)
[0183] Each bit is selected from B.sub.i by the following formula according to the element in above array J hopping forward or not hopping to concatenate the key bit segment:
b i , s = l = 1 Ls b i , l >> j l , b i fs s = l = 1 Ls b i fs l >> j l ##EQU00001##
[0184] Embodiment 10 implements the selection of a plurality of key segment bits with or without hopping to perform a multi-frequency encryption process on a plaintext bit segment directly.
[0185] Embodiment 11: (S6.sup.9) in Embodiment 9 is decomposed as following:
[0186] (S6.0.sup.11) establishing a pairing function C for determining that the bits to be swapped are L/2+8 and L/2-8 from the start bit in the multi-frequency;
[0187] (S6.1.sup.11) decomposing (S6.sup.9) as F.sub.s frequencies:
c.sub.1=m.sub.s.sym.b.sub.1,s; c.sub.2=c.sub.1.sym.b.sub.2,s; c.sub.3=c.sub.2.sym.b.sup.f2.sub.1,s; . . . ; c.sub.Fs-1.sym.b.sup.Fs.sub.2,s;
[0188] (S6.2.sup.11) pairing the target bit segment c.sub.fs for swapping after XOR of each frequency:
c.sup.q.sub.L/2+8<->c.sup.q.sub.L/2-8.
[0189] Note that: in the decryption, the above pairing for swapping is performed on the source bit segment (cipher text) prior to XOR in each frequency of (S6.1.sup.11).
[0190] Embodiment 11 implements an encryption process with pseudo-random reconstruction with a pair of bits pairing for swapping, and the swapping by pseudo-randomly bit pairing can be performed multiply times at one frequency, and the number of times can be pseudo-randomly determined as well.
EMBODIMENT 12
[0191] (S6.2.0.sup.12) The bit length in (S6.1.sup.11) in embodiment 11 is extended by increase amount calculated by function A in each frequency
A.sub.f,s=L.sup.f-1,s+(S*F.sub.s+12345)%3+1
[0192] (6.2.1.sup.12) For the target of XOR in each frequency, the extended bits of the length of A.sub.f,s from a plaintext are concatenated until the plaintext reaches the end (in decryption, the extended bits from cipher text are concatenated)
C.sub.f=(c.sub.f-1.sym.b.sub.2,s).parallel.m.sub.(Lf-1,s+S%Fs); . . . ; c.sub.Fs-1=(c.sub.Fs-2.sym.b.sub.1,s).parallel.m.sub.(LFs-1,s+S%Fs)
[0193] m.sub.(LFs-1,s+S%Fs) is the extended bits of the plaintext with length determined by the previous frequency
[0194] b.sub.1,s the pseudo-randomly constructed key with the extended bits.
[0195] (S6.2.2.sup.12) After XOR (with the extended bits) at each frequency is completed, all bits of the extended portion are backfilled to the corresponding bits of the plaintext to participate in XOR in the next step.
[0196] The decryption process is the same as the encryption process, but only (S6.2.sup.12) is changed to (S6.2.sup.12'):
[0197] (S6.2.sup.12') for the target of XOR in each frequency, the extended bits from the cipher text are concatenated until the cipher text reaches the end
m.sub.f=(m.sub.f-1.sym.b.sub.2,s).parallel.c.sub.(Lf-1,s+S%Fs); . . . ; m.sub.Fs-1=(m.sub.Fs-2.sym.b.sub.1,s).parallel.c.sub.(LFs-1,s+S%Fs).
[0198] (S6.2.2.sup.12') After XOR (without the extended bits) at each frequency is completed, XOR with extension is performed frequency by frequency in a reverse order by the extended key bits of each frequency in the previous step.
[0199] Note that: the source bit segment in the current step has been partially processed by the S.sup.th step, that is, the starting portion of the target bit segment in the S+1.sup.th step is XORed with both the key in the S.sup.th step and the key in the S+1.sup.th step. Since each step follows a pseudo-random convention at work, the process does not change in the decryption, and the plaintext can be recovered by the decryption.
[0200] Embodiment 12 implements a variation of the length of bit segment in XOR of each frequency. This makes the accompanied pseudo-random reconstruction method presents the encryption effect of being associated with each other.
EMBODIMENT 13
[0201] The following changes are made to Embodiment 9.
[0202] (S0.1.sup.13) Length n of a random sequence is selected as 524288; two groups of alternative random seed sequences are selected: B.sup.1: b.sup.1.sub.1, b.sup.1.sub.2, b.sup.1.sub.3, . . . , b.sup.1.sub.n; B.sup.2: b.sup.2.sub.1, b.sup.2.sub.2, b.sup.2.sub.3, . . . , b.sup.2.sub.n; for any determined number of engines E1 and E2, p.sub.1 and p.sub.2 are calculated with P being p.sub.i=((p.sub.i-1+1)*12345+1103515245+E+S)% 524288.
[0203] (S0.3.sup.13) It defines F.sup.j.sub.s=(S+B[P.sup.j.sub.s-1% 65536])% 8+16.
[0204] (S0.4.sup.13) It defines a positioning function for B.sub.j P(b.sup.j.sub.s)=B[(b'.sup.j.sub.s-1+S)% 65536]% 524288.
[0205] (S0.5.sup.13) It defines the length L.sub.s of bit segment of the seed random sequence for pseudo-random reconstruction.
[0206] (S0.5.1.sup.13) When the remaining length of the alternative random sequence B.sup.i is greater than or equal to L.sub.s, L.sub.s=B.sup.1[b'.sub.s-1% 65536]% 16+64.
[0207] (S0.5.2.sup.13) When the remaining length of the alternative random sequence B.sup.i is less than L.sub.s, it sets L.sub.s=the remaining plaintext length.
[0208] (S0.6.sup.13) b.sup.j.sub.s=b.sup.j.sub.s(P.sup.j.sub.s, L.sup.j.sub.s, F.sup.j.sub.s).
[0209] (S0.7.sup.13) XOR in the current step b.sub.s=b.sup.1.sub.s.sym.b.sup.2.sub.s.
[0210] (S0.8.sup.13) S=S+1.
[0211] Then the chaos degree of obtaining the seed random sequence is improved.
[0212] Embodiment 13 implements a pseudo-random reconstruction process with a seed random sequence in a manner of non-forward shifting.
[0213] The various manipulation functions used in the various embodiments described above all have an adjustable space, and provide sufficient application space for the method accompanied with pseudo-random construction.
* * * * *
uspto.report is an independent third-party trademark research tool that is not affiliated, endorsed, or sponsored by the United States Patent and Trademark Office (USPTO) or any other governmental organization. The information provided by uspto.report is based on publicly available data at the time of writing and is intended for informational purposes only.
While we strive to provide accurate and up-to-date information, we do not guarantee the accuracy, completeness, reliability, or suitability of the information displayed on this site. The use of this site is at your own risk. Any reliance you place on such information is therefore strictly at your own risk.
All official trademark data, including owner information, should be verified by visiting the official USPTO website at www.uspto.gov. This site is not intended to replace professional legal advice and should not be used as a substitute for consulting with a legal professional who is knowledgeable about trademark law.