System, Certification Authority, Vehicle-mounted Computer, Vehicle, Public Key Certificate Issuance Method, And Program
TAKEMORI; Keisuke ; et al.
U.S. patent application number 16/303943 was filed with the patent office on 2020-06-04 for system, certification authority, vehicle-mounted computer, vehicle, public key certificate issuance method, and program. This patent application is currently assigned to KDDI CORPORATION. The applicant listed for this patent is KDDI CORPORATION. Invention is credited to Hideaki KAWABATA, Ayumu KUBOTA, Seiichiro MIZOGUCHI, Keisuke TAKEMORI.
| Application Number | 20200177398 16/303943 |
| Document ID | / |
| Family ID | 60664303 |
| Filed Date | 2020-06-04 |
View All Diagrams
| United States Patent Application | 20200177398 |
| Kind Code | A1 |
| TAKEMORI; Keisuke ; et al. | June 4, 2020 |
SYSTEM, CERTIFICATION AUTHORITY, VEHICLE-MOUNTED COMPUTER, VEHICLE, PUBLIC KEY CERTIFICATE ISSUANCE METHOD, AND PROGRAM
Abstract
A system includes a certification authority and a vehicle-mounted computer mounted in a vehicle. The certification authority includes a certification authority key storage that stores a certification authority public key certificate and a certification authority private key, a first communicator that receives an issuance request that is configured to request issuance of a vehicle-mounted computer public key certificate, and a vehicle-mounted computer public key certificate issuer that is configured to apply a signature to the vehicle-mounted computer public key included in the issuance request with the certification authority private key and issue the vehicle-mounted computer public key certificate. The first communicator is configured to transmit the vehicle-mounted computer public key certificate to the vehicle-mounted computer that is a transmission source of the issuance request. The vehicle-mounted computer includes a vehicle-mounted computer key generator and a public key certificate acquirer.
| Inventors: | TAKEMORI; Keisuke; (Tokyo, JP) ; MIZOGUCHI; Seiichiro; (Tokyo, JP) ; KAWABATA; Hideaki; (Tokyo, JP) ; KUBOTA; Ayumu; (Tokyo, JP) | ||||||||||
| Applicant: |
|
||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|
| Assignee: | KDDI CORPORATION Tokyo JP |
||||||||||
| Family ID: | 60664303 | ||||||||||
| Appl. No.: | 16/303943 | ||||||||||
| Filed: | March 28, 2017 | ||||||||||
| PCT Filed: | March 28, 2017 | ||||||||||
| PCT NO: | PCT/JP2017/012536 | ||||||||||
| 371 Date: | November 21, 2018 |
| Current U.S. Class: | 1/1 |
| Current CPC Class: | H04L 9/0643 20130101; H04L 9/3271 20130101; H04L 63/0823 20130101; H04L 2209/84 20130101; H04L 9/3268 20130101; H04W 12/04031 20190101; G06F 21/44 20130101; H04W 4/40 20180201; H04L 9/0897 20130101; H04L 63/062 20130101; H04L 9/0877 20130101; G06F 21/33 20130101 |
| International Class: | H04L 9/32 20060101 H04L009/32; H04L 9/08 20060101 H04L009/08; H04L 9/06 20060101 H04L009/06; H04L 29/06 20060101 H04L029/06; H04W 12/04 20060101 H04W012/04; H04W 4/40 20060101 H04W004/40 |
Foreign Application Data
| Date | Code | Application Number |
|---|---|---|
| Jun 17, 2016 | JP | 2016-121229 |
Claims
1. A system comprising a certification authority and a vehicle-mounted computer which is mounted in a vehicle, wherein the certification authority includes: a certification authority key storage configured to store a certification authority public key certificate and a certification authority private key; a first communicator configured to receive an issuance request that is configured to request issuance of a vehicle-mounted computer public key certificate of a vehicle-mounted computer public key from the vehicle-mounted computer; and a vehicle-mounted computer public key certificate issuer configured to apply a signature to the vehicle-mounted computer public key included in the issuance request with the certification authority private key and to issue the vehicle-mounted computer public key certificate, wherein the first communicator is configured to transmit the issued vehicle-mounted computer public key certificate to the vehicle-mounted computer that is a transmission source of the issuance request, and the vehicle-mounted computer includes: a vehicle-mounted computer key generator configured to generate the vehicle-mounted computer public key and a vehicle-mounted computer private key that is paired with the vehicle-mounted computer public key; and a public key certificate acquirer configured to transmit the issuance request to the certification authority and to acquire the vehicle-mounted computer public key certificate that the certification authority transmits in response to the issuance request.
2. The system according to claim 1, wherein: the certification authority further includes a first authenticator configured to perform authentication with the vehicle-mounted computer on the basis of a common key; the vehicle-mounted computer further includes a second authenticator configured to perform authentication with the first authenticator of the certification authority on the basis of the common key; and the vehicle-mounted computer public key certificate issuer is configured to issue the vehicle-mounted computer public key certificate if the authentication of the first authenticator succeeds.
3. The system according to claim 2, wherein the common key includes an initial key held in the vehicle-mounted computer, the vehicle-mounted computer further includes: a first storage configured to store the initial key; and a second communicator configured to transmit identification information of the vehicle-mounted computer to the certification authority, and the certification authority further includes: a second storage configured to store a master key used to generate the initial key; and an initial key generator configured to generate the initial key on the basis of the master key and the identification information of the vehicle-mounted computer transmitted by the vehicle-mounted computer.
4. The system according to claim 2, wherein: the first authenticator is configured to exchange the common key with the second authenticator whose authentication has succeeded; and the second authenticator is configured to exchange the common key with the first authenticator whose authentication has succeeded.
5. The system according to claim 1, wherein the certification authority is an intermediate certification authority included in the vehicle.
6. The system according to claim 1, wherein the certification authority is arranged in the vehicle-mounted computer or in a communication module in the vehicle.
7. The system according to claim 1, wherein the certification authority is arranged in a server device to which the certification authority is connected via a communication module of the vehicle or in a maintenance tool to which the certification authority is connected via a diagnostic port of the vehicle.
8. A certification authority comprising: a certification authority key storage configured to store a certification authority public key certificate and a certification authority private key; a communicator configured to receive an issuance request that is configured to request issuance of a vehicle-mounted computer public key certificate of a vehicle-mounted computer public key transmitted by a vehicle-mounted computer; and a vehicle-mounted computer public key certificate issuer configured to apply a signature to the vehicle-mounted computer public key included in the issuance request with the certification authority private key and to issue the vehicle-mounted computer public key certificate, wherein the communicator is configured to transmit the issued vehicle-mounted computer public key certificate to the vehicle-mounted computer that is a transmission source of the issuance request.
9. A vehicle-mounted computer that is mounted in a vehicle, the vehicle-mounted computer comprising: a vehicle-mounted computer key generator configured to generate a vehicle-mounted computer public key and a vehicle-mounted computer private key that is paired with the vehicle-mounted computer public key; and a public key certificate acquirer configured to transmit an issuance request that is configured to request issuance of a vehicle-mounted computer public key certificate of the vehicle-mounted computer public key to a certification authority and to acquire the vehicle-mounted computer public key certificate that the certification authority transmits in response to the issuance request.
10. A vehicle comprising a vehicle-mounted computer, wherein the vehicle-mounted computer includes, a vehicle-mounted computer key generator configured to generate a vehicle-mounted computer public key and a vehicle-mounted computer private key that is paired with the vehicle-mounted computer public key; and a public key certificate acquirer configured to transmit an issuance request that is configured to request issuance of a vehicle-mounted computer public key certificate of the vehicle-mounted computer public key to a certification authority and to acquire the vehicle-mounted computer public key certificate that the certification authority transmits in response to the issuance request.
11. A vehicle comprising: a certification authority; and a vehicle-mounted computer, wherein the certification authority includes: a certification authority key storage configured to store a certification authority public key certificate and a certification authority private key; a communicator configured to receive an issuance request that is configured to request issuance of a vehicle-mounted computer public key certificate of a vehicle-mounted computer public key transmitted by a vehicle-mounted computer; and a vehicle-mounted computer public key certificate issuer configured to apply a signature to the vehicle-mounted computer public key included in the issuance request with the certification authority private key and to issue the vehicle-mounted computer public key certificate, wherein the communicator is configured to transmit the issued vehicle-mounted computer public key certificate to the vehicle-mounted computer that is a transmission source of the issuance request, wherein the vehicle-mounted computer includes: a vehicle-mounted computer key generator configured to generate a vehicle-mounted computer public key and a vehicle-mounted computer private key that is paired with the vehicle-mounted computer public key; and a public key certificate acquirer configured to transmit an issuance request that is configured to request issuance of a vehicle-mounted computer public key certificate of the vehicle-mounted computer public key to a certification authority and to acquire the vehicle-mounted computer public key certificate that the certification authority transmits in response to the issuance request.
12. A public key certificate issuing method that is performed by a system including a certification authority and a vehicle-mounted computer that is mounted in a vehicle, the public key certificate issuing method comprising: storing, by the certification authority, a certification authority public key certificate and a certification authority private key; generating, by the vehicle-mounted computer, a vehicle-mounted computer public key and a vehicle-mounted computer private key that is paired with the vehicle-mounted computer public key; transmitting, by the vehicle-mounted computer, an issuance request that is configured to request issuance of a vehicle-mounted computer public key certificate of the vehicle-mounted computer public key to the certification authority; receiving, by the certification authority, the issuance request transmitted by the vehicle-mounted computer; applying, by the certification authority, a signature to the vehicle-mounted computer public key included in the issuance request with the certification authority private key and issuing the vehicle-mounted computer public key certificate; transmitting, by the certification authority, the issued vehicle-mounted computer public key certificate to the vehicle-mounted computer that is a transmission source of the issuance request; and acquiring, by the vehicle-mounted computer, the vehicle-mounted computer public key certificate transmitted by the certification authority.
13. A non-transitory computer-readable recording medium storing a program causing a computer of a certification authority to execute processes of: storing a certification authority public key certificate and a certification authority private key; receiving an issuance request that is configured to request issuance of a vehicle-mounted computer public key certificate of a vehicle-mounted computer public key from a vehicle-mounted computer; applying a signature to the vehicle-mounted computer public key included in the issuance request with the certification authority private key and issuing the vehicle-mounted computer public key certificate; and transmitting the issued vehicle-mounted computer public key certificate to the vehicle-mounted computer that is a transmission source of the issuance request.
14. A non-transitory computer-readable recording medium storing a program causing a vehicle-mounted computer to execute processes of: generating a vehicle-mounted computer public key and a vehicle-mounted computer private key that is paired with the vehicle-mounted computer public key; transmitting an issuance request that is configured to request issuance of a vehicle-mounted computer public key certificate of the vehicle-mounted computer public key to a certification authority; and acquiring the vehicle-mounted computer public key certificate transmitted by the certification authority.
Description
TECHNICAL FIELD
[0001] Embodiments of the present invention relate to a system, a certification authority, a vehicle-mounted computer, a vehicle, a public key certificate issuing method, and a program.
[0002] Priority is claimed on Japanese Patent Application No. 2016-121229, filed Jun. 17, 2016, the content of which is incorporated herein by reference.
BACKGROUND ART
[0003] When an automobile communicates with a roadside device, an external server, or the like, it is necessary for devices outside the automobile to authenticate the automobile, electronic control units (ECUs) included in the automobile, applications installed in the ECUs, or the like.
[0004] A scheme of issuing a public key certificate relating to Vehicle to X (V2X) communication (see, for example, Non-Patent Document 1) is known for technology related to devices other than automobiles to authenticate an automobile or the like.
CITATION LIST
Non-Patent Literature
[Non-Patent Document 1]
[0005] "Security Guidelines for Driver Assistance Communications System, ITS FORUM RC-009 ver. 1.0," p. 50, FIG. 6-1, Internet <URL: http://www.itsforum.gr.jp/Public/J7Database/p41/ITS_FORUM_RC009V1_0.pdf&g- t;
SUMMARY OF INVENTION
Problem to be Solved by the Invention
[0006] When communication is performed between an automobile and a device that cannot be directly managed by an automobile manufacturer, it is assumed that there is a need to perform authentication using a public key certificate issued by a trusted third party.
[0007] Among certification authority service providers (certification authorities: CA) that issue public key certificates to websites on the Internet or the like, there are service providers that issue public key certificates without strictly checking the authenticated party. Therefore, due to their low trustworthiness, existing certification authorities on the Internet may sometimes be inappropriate for issuing public key certificates to equipment (automobiles) relating to human life.
[0008] Further, in general, certification authorities check the existence of a business entity to which a public key certificate is to be issued by acquiring a certified copy of registration of the business entity or by making a call to a representative telephone number described in the certified copy of registration. Assuming that a public key certificate is issued to an automobile, an ECU (Electronic Control Unit), or an application installed in the ECU, there is no way to check whether or not issuance is possible, since it is not possible to confirm with a certified copy of registration or a phone call.
[0009] The present invention has been made to solve the above problems and it is an object of the present invention to appropriately issue a public key certificate to an automobile, an ECU, or an application installed in the ECU.
Means for Solving the Problem
[0010] (1) An aspect of the present invention is a system including a certification authority and a vehicle-mounted computer which is mounted in a vehicle, wherein the certification authority includes a certification authority key storage configured to store a certification authority public key certificate and a certification authority private key, a first communicator configured to receive an issuance request that is configured to request issuance of a vehicle-mounted computer public key certificate of a vehicle-mounted computer public key from the vehicle-mounted computer, and a vehicle-mounted computer public key certificate issuer configured to apply a signature to the vehicle-mounted computer public key included in the issuance request with the certification authority private key and to issue the vehicle-mounted computer public key certificate, wherein the first communicator is configured to transmit the issued vehicle-mounted computer public key certificate to the vehicle-mounted computer that is a transmission source of the issuance request, and the vehicle-mounted computer includes a vehicle-mounted computer key generator configured to generate the vehicle-mounted computer public key and a vehicle-mounted computer private key that is paired with the vehicle-mounted computer public key, and a public key certificate acquirer configured to transmit the issuance request to the certification authority and to acquire the vehicle-mounted computer public key certificate that the certification authority transmits in response to the issuance request.
[0011] (2) An aspect of the present invention is the system according to the above aspect (1), wherein: the certification authority further includes a first authenticator configured to perform authentication with the vehicle-mounted computer on the basis of a common key; the vehicle-mounted computer further includes a second authenticator configured to perform authentication with the first authenticator of the certification authority on the basis of the common key; and the vehicle-mounted computer public key certificate issuer is configured to issue the vehicle-mounted computer public key certificate if the authentication of the first authenticator succeeds.
[0012] (3) An aspect of the present invention is the system according to the above aspect (2), wherein the common key includes an initial key held in the vehicle-mounted computer, the vehicle-mounted computer further includes a first storage configured to store the initial key, and a second communicator configured to transmit identification information of the vehicle-mounted computer to the certification authority, and the certification authority further includes a second storage configured to store a master key used to generate the initial key, and an initial key generator configured to generate the initial key on the basis of the master key and the identification information of the vehicle-mounted computer transmitted by the vehicle-mounted computer.
[0013] (4) An aspect of the present invention is the system according to the above aspect (2), wherein: the first authenticator is configured to exchange the common key with the second authenticator whose authentication has succeeded; and the second authenticator is configured to exchange the common key with the first authenticator whose authentication has succeeded.
[0014] (5) An aspect of the present invention is the system according to any one of the above aspects (1) to (4), wherein the certification authority is an intermediate certification authority included in the vehicle.
[0015] (6) An aspect of the present invention is the system according to any one of the above aspects (1) to (5), wherein the certification authority is arranged in the vehicle-mounted computer or in a communication module in the vehicle.
[0016] (7) An aspect of the present invention is the system according to any one of the above aspects (1) to (4), wherein the certification authority is arranged in a server device to which the certification authority is connected via a communication module of the vehicle or in a maintenance tool to which the certification authority is connected via a diagnostic port of the vehicle.
[0017] (8) An aspect of the present invention is a certification authority including a certification authority key storage configured to store a certification authority public key certificate and a certification authority private key, a communicator configured to receive an issuance request that is configured to request issuance of a vehicle-mounted computer public key certificate of a vehicle-mounted computer public key transmitted by a vehicle-mounted computer, and a vehicle-mounted computer public key certificate issuer configured to apply a signature to the vehicle-mounted computer public key included in the issuance request with the certification authority private key and to issue the vehicle-mounted computer public key certificate, wherein the communicator is configured to transmit the issued vehicle-mounted computer public key certificate to the vehicle-mounted computer that is a transmission source of the issuance request.
[0018] (9) An aspect of the present invention is a vehicle-mounted computer that is mounted in a vehicle, the vehicle-mounted computer including a vehicle-mounted computer key generator configured to generate a vehicle-mounted computer public key and a vehicle-mounted computer private key that is paired with the vehicle-mounted computer public key, and a public key certificate acquirer configured to transmit an issuance request that is configured to request issuance of a vehicle-mounted computer public key certificate of the vehicle-mounted computer public key to a certification authority and to acquire the vehicle-mounted computer public key certificate that the certification authority transmits in response to the issuance request.
[0019] (10) An aspect of the present invention is a vehicle including the vehicle-mounted computer according to the above aspect (9).
[0020] (11) An aspect of the present invention is a vehicle including the certification authority according to the above aspect (8), and the vehicle-mounted computer according to the above aspect (9).
[0021] (12) An aspect of the present invention is a public key certificate issuing method that is performed by a system including a certification authority and a vehicle-mounted computer that is mounted in a vehicle, the public key certificate issuing method including storing, by the certification authority, a certification authority public key certificate and a certification authority private key, generating, by the vehicle-mounted computer, a vehicle-mounted computer public key and a vehicle-mounted computer private key that is paired with the vehicle-mounted computer public key, transmitting, the vehicle-mounted computer, an issuance request that is configured to request issuance of a vehicle-mounted computer public key certificate of the vehicle-mounted computer public key to the certification authority, receiving, the certification authority, the issuance request transmitted by the vehicle-mounted computer, applying, the certification authority, a signature to the vehicle-mounted computer public key included in the issuance request with the certification authority private key and issuing the vehicle-mounted computer public key certificate, transmitting, the certification authority, the issued vehicle-mounted computer public key certificate to the vehicle-mounted computer that is a transmission source of the issuance request, and acquiring, the vehicle-mounted computer, the vehicle-mounted computer public key certificate transmitted by the certification authority.
[0022] (13) An aspect of the present invention is a program causing a computer of a certification authority to execute processes of storing a certification authority public key certificate and a certification authority private key, receiving an issuance request that is configured to request issuance of a vehicle-mounted computer public key certificate of a vehicle-mounted computer public key from a vehicle-mounted computer, applying a signature to the vehicle-mounted computer public key included in the issuance request with the certification authority private key and issuing the vehicle-mounted computer public key certificate, and transmitting the issued vehicle-mounted computer public key certificate to the vehicle-mounted computer that is a transmission source of the issuance request.
[0023] (14) An aspect of the present invention is a program causing a vehicle-mounted computer to execute processes of generating a vehicle-mounted computer public key and a vehicle-mounted computer private key that is paired with the vehicle-mounted computer public key, transmitting an issuance request that is configured to request issuance of a vehicle-mounted computer public key certificate of the vehicle-mounted computer public key to a certification authority, and acquiring the vehicle-mounted computer public key certificate transmitted by the certification authority.
Advantageous Effects of Invention
[0024] According to the present invention, it is possible to appropriately issue a public key certificate to an automobile, an ECU, or an application installed in the ECU.
BRIEF DESCRIPTION OF DRAWINGS
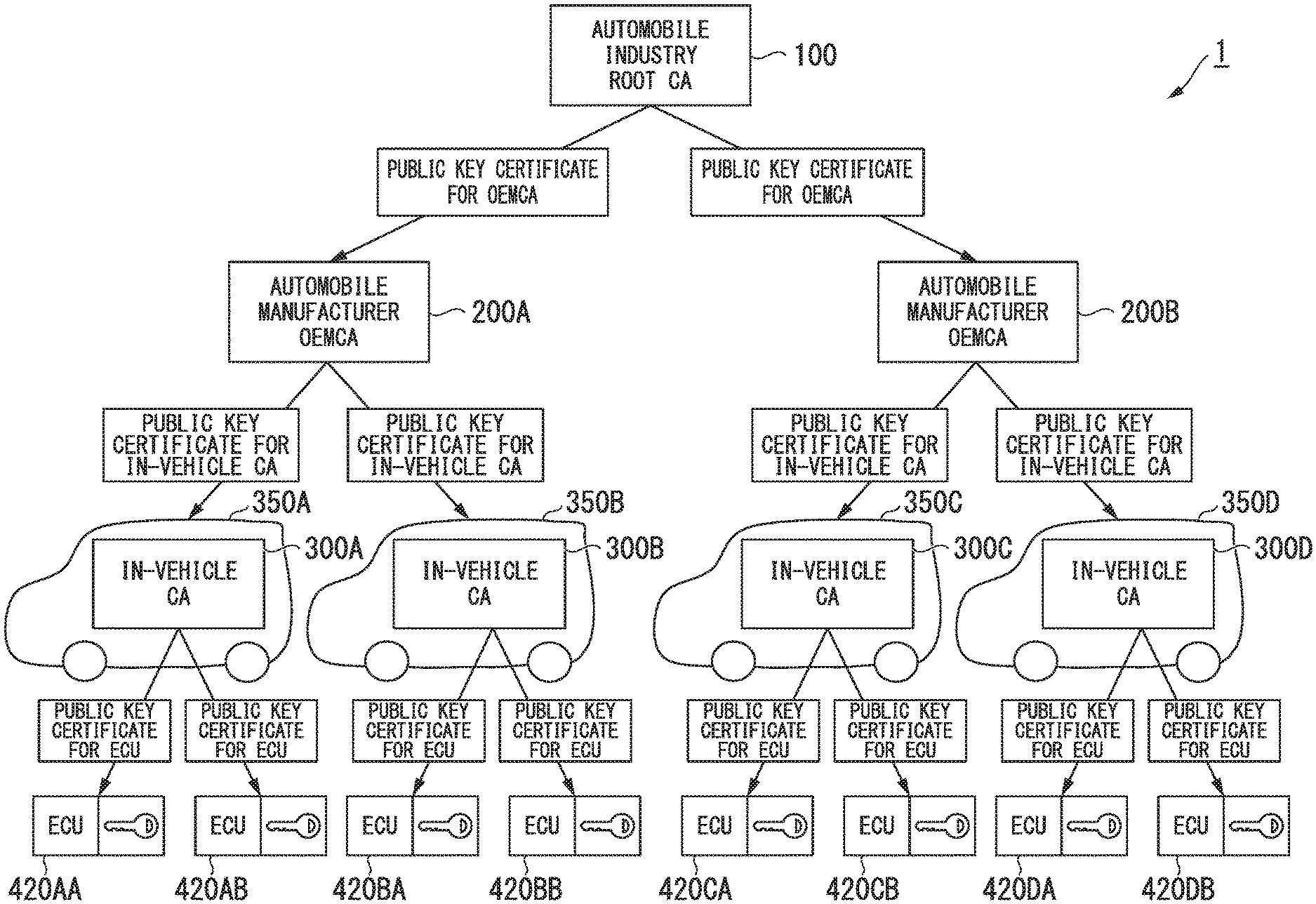
[0025] FIG. 1 is a configuration diagram showing a hierarchical structure for issuing a public key certificate according to the present embodiment.
[0026] FIG. 2 is a functional block diagram showing a root certification authority, an OEM certification authority, and an in-vehicle certification authority according to the present embodiment.
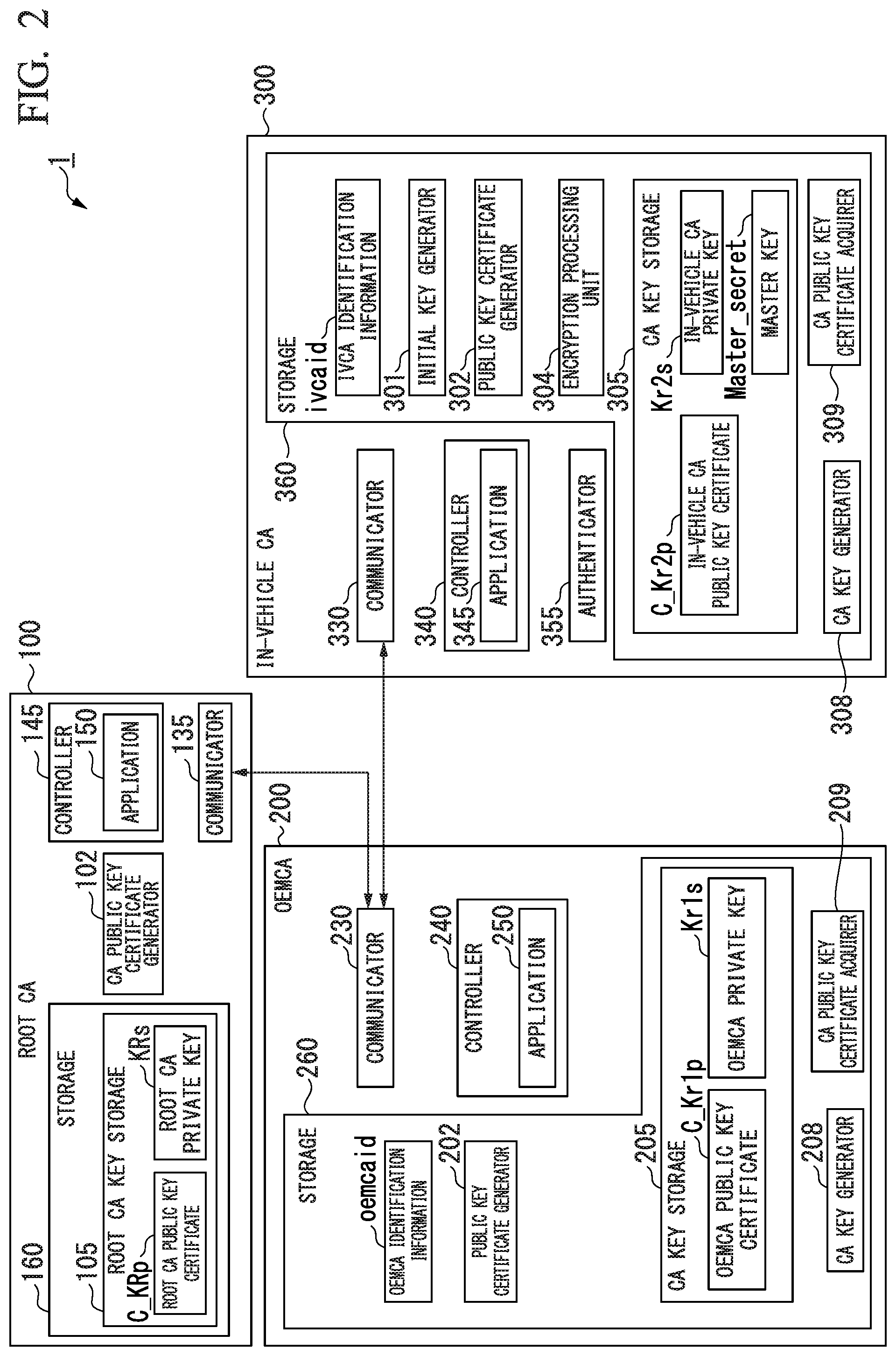
[0027] FIG. 3 is a sequence chart showing an example of an operation for issuing a public key certificate according to the present embodiment.
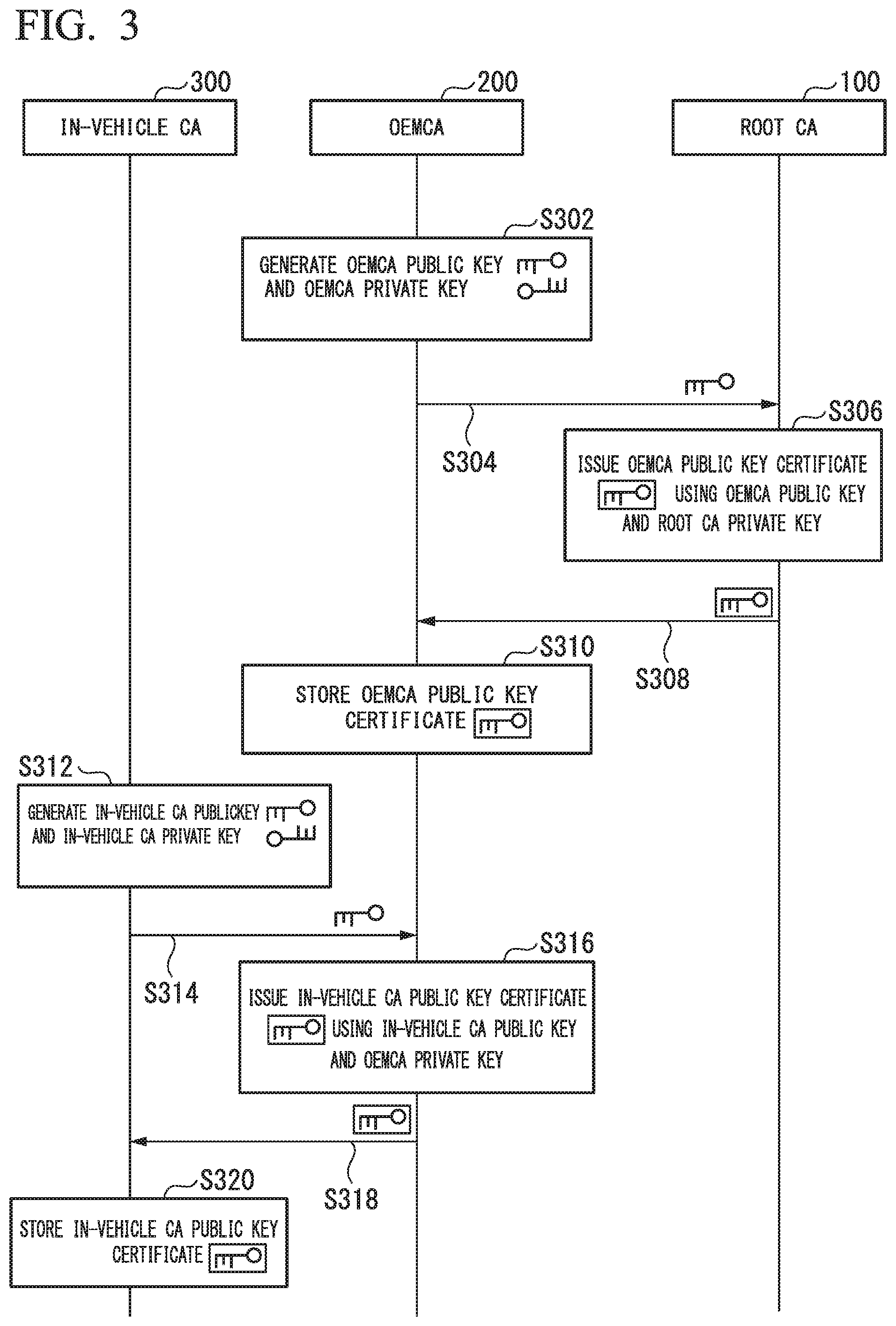
[0028] FIG. 4 is a configuration diagram showing an exemplary configuration of an automobile according to the present embodiment.
[0029] FIG. 5 is a functional block diagram showing a first ECU according to the present embodiment.
[0030] FIG. 6 is a functional block diagram showing a second ECU according to the present embodiment.
[0031] FIG. 7 is a diagram showing an operation for issuing a public key certificate according to the present embodiment.
[0032] FIG. 8 is a sequence chart showing an operation of an initial key writing device according to the present embodiment.
[0033] FIG. 9 is a diagram showing an operation for distributing an in-vehicle common key according to the present embodiment.
[0034] FIG. 10 is a configuration diagram showing an exemplary configuration of an automobile according to the present embodiment.
[0035] FIG. 11 is a diagram showing an operation for issuing a public key certificate according to the present embodiment.
[0036] FIG. 12 is a configuration diagram showing an exemplary configuration of an automobile according to the present modification.
[0037] FIG. 13 is a diagram showing an operation for issuing a public key certificate according to the present modification.
[0038] FIG. 14 is a configuration diagram showing an exemplary configuration of an automobile according to the present embodiment.
[0039] FIG. 15 is a diagram showing an operation for issuing a public key certificate according to the present embodiment.
[0040] FIG. 16 is a configuration diagram showing a hierarchical structure for issuing a public key certificate according to the present modification.
[0041] FIG. 17 is a diagram showing an operation for issuing a public key certificate according to the present modification.
DESCRIPTION OF EMBODIMENTS
[0042] Next, modes for carrying out the present invention will be described with reference to the drawings. Embodiments described below are merely examples and embodiments to which the present invention is applied are not limited to the following embodiments.
[0043] In all drawings for explaining the embodiments, the same reference signs are used for components having the same functions and repeated descriptions will be omitted. In the following embodiments, an automobile will be described as an example of a vehicle.
[0044] FIG. 1 is a diagram showing an example of a hierarchical structure 1 for issuing a public key certificate according to an embodiment. The hierarchical structure 1 includes a root certification authority (Root CA) 100, an original equipment manufacturer CA (OEMCA) 200A, an OEMCA 200B, an in-vehicle CA 300A, an in-vehicle CA 300B, an in-vehicle CA 300C, and an in-vehicle CA 300D. The in-vehicle CA 300A is mounted in an automobile 350A, the in-vehicle CA 300B is mounted in an automobile 350B, the in-vehicle CA 300C is mounted in an automobile 350C, and the in-vehicle CA 300D is mounted in an automobile 350D.
[0045] Further, an ECU 420AA and an ECU 420AB are mounted in the automobile 350A. An ECU 420BA and an ECU 420BB are mounted in the automobile 350B. An ECU 420CA and an ECU 420CB are mounted in the automobile 350C. An ECU 420DA and an ECU 420DB are mounted in the automobile 350D.
[0046] Hereinafter, the OEMCA 200A and the OEMCA 200B will be referred to as OEMCAs 200 unless otherwise distinguished. The in-vehicle CA 300A, the in-vehicle CA 300B, the in-vehicle CA 300C, and the in-vehicle CA 300D will be referred to as in-vehicle CAs 300 unless otherwise distinguished. The automobile 350A, the automobile 350B, the automobile 350C, and the automobile 350D will be referred to as automobiles 350 unless otherwise distinguished. The ECU 420AA, the ECU 420AB, the ECU 420BA, the ECU 420BB, the ECU 420CA, the ECU 420CB, the ECU 420DA, and the ECU 420DB will be referred to as ECUs 420 unless otherwise distinguished. The same is true for components of each of the OEMCAs 200, the in-vehicle CAs 300, and the ECUs 420.
[0047] In the hierarchical structure 1, the root CA 100 is the top layer, the OEMCAs 200 are a layer lower than the root CA 100, and the in-vehicle CAs 300 are a layer lower than the OEMCAs 200. On the basis of this hierarchical structure, a public key certificate is issued in the automobile.
[0048] The root CA 100 has a public key and a private key. Each of the OEMCAs 200 has a public key and a private key. Each of the ECUs 420 has a public key and a private key.
[0049] The root CA 100 is an authority that authenticates the OEMCAs 200 operated by their automobile manufacturers. By providing the root CA 100 in the hierarchical structure 1, mutual authentication based on public key certificates can be performed between automobiles manufactured by different automobile manufacturers, between ECUs and applications provided in each automobile, and between them and devices outside the automobiles.
[0050] Next, by using public key certificates issued by an OEMCA 200, it is possible to incorporate different in-vehicle CAs respectively into vehicle-mounted secure elements. Thereby, even if an in-vehicle CA is compromised, for example, due to analysis of a vehicle-mounted secure element, it is possible to not affect in-vehicle CAs of other vehicles. A public key certificate can also be issued from an in-vehicle CA to its own automobile, ECUs, and applications embedded in ECUs.
<Hierarchical Structure>
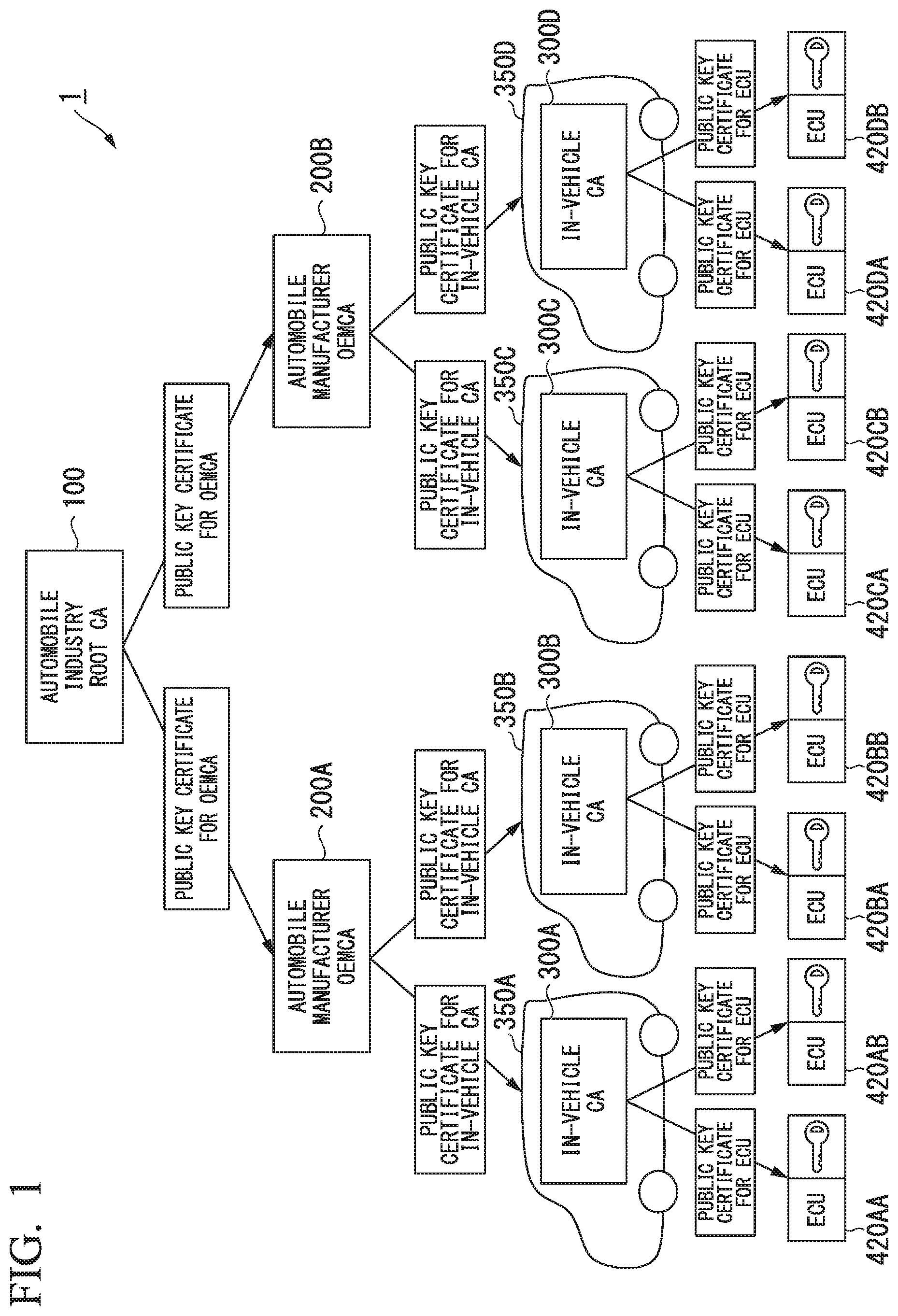
[0051] FIG. 2 is a diagram showing the root CA 100, the OEMCAs 200, and the in-vehicle CAs 300 that constitute the hierarchical structure 1 according to the embodiment.
<Root CA>
[0052] The root CA 100 includes a storage 160, a CA public key certificate generator 102, a communicator 135, and a controller 145.
[0053] The storage 160 includes a root CA key storage 105. The root CA key storage 105 stores a root CA public key certificate C_KRp and a root CA private key KRs.
[0054] The root CA public key certificate C_KRp is a public key certificate relating to a root CA public key KRp which is paired with the root CA private key KRs. The root CA public key certificate C_KRp and the root CA private key KRs are securely stored in the storage 160, for example, when the storage 160 is manufactured. The root CA key storage 105 is provided in a nonvolatile storage area, which cannot be accessed from the outside of the storage 160, in the storage area of the storage 160.
[0055] The CA public key certificate generator 102 issues an OEMCA public key certificate C_Kr1p using the root CA private key KRs stored in the root CA key storage 105 and an OEMCA public key Kr1p transmitted by an OEMCA 200. The CA public key certificate generator 102 transmits the issued OEMCA public key certificate C_Kr1p to the OEMCA 200 through the communicator 135.
[0056] The controller 145 controls each part of the root CA 100. The controller 145 includes an application 150.
<OEMCA>
[0057] The OEMCA 200 includes a storage 260, a communicator 230, and a controller 240. An example of the storage 260 is a secure element such as a subscriber identity module (SIM).
[0058] The controller 240 controls each part of the OEMCA 200. The controller 240 includes an application 250.
[0059] The storage 260 includes a public key certificate generator 202, a CA key storage 205, a CA key generator 208, and a CA public key certificate acquirer 209.
[0060] The storage 260 stores OEMCA identification information oemcaid. The OEMCA identification information oemcaid is identification information unique to the OEMCA 200.
[0061] The public key certificate generator 202 issues an in-vehicle CA public key certificate C_Kr2p using an OEMCA private key Kr1s stored in the CA key storage 205.
[0062] The CA key storage 205 stores the OEMCA public key certificate C_Kr1p and the OEMCA private key Kr1s. The OEMCA public key certificate C_Kr1p is a public key certificate relating to an OEMCA public key Kr1p which is paired with the OEMCA private key Kr1s. The OEMCA public key certificate C_Kr1p is acquired from the root CA 100 and is securely stored in the CA key storage 205 together with the OEMCA private key Kr1s.
[0063] The CA key generator 208 generates a pair of the OEMCA public key Kr1p and the OEMCA private key Kr1s and stores the OEMCA private key Kr1s in the CA key storage 205.
[0064] The CA public key certificate acquirer 209 requests the root CA 100 to issue the OEMCA public key certificate, and acquires the OEMCA public key certificate C_Kr1p from the root CA 100. For example, the CA public key certificate acquirer 209 transmits a CA public key certificate issuance request including the OEMCA public key Kr1p generated by the CA key generator 208 to the root CA 100. Upon receiving the OEMCA public key certificate C_Kr1p transmitted by the root CA 100, the CA public key certificate acquirer 209 stores the OEMCA public key certificate C_Kr1p in the CA key storage 205.
<In-Vehicle CA>
[0065] The in-vehicle CA 300 includes a storage 360, a communicator 330, a controller 340, and an authenticator 355. The in-vehicle CA 300 is an example of an intermediate CA. An example of the storage 360 is a secure element such as an SIM.
[0066] The controller 340 controls each part of the in-vehicle CA 300. The controller 340 includes an application 345.
[0067] The storage 360 includes an initial key generator 301, a public key certificate generator 302, an encryption processing unit 304, a CA key storage 305, a CA key generator 308, and a CA public key certificate acquirer 309.
[0068] The storage 360 stores IVCA identification information ivcaid. The IVCA identification information ivcaid is identification information unique to the in-vehicle CA 300.
[0069] The initial key generator 301 generates an initial key of the ECU 420.
[0070] The public key certificate generator 302 issues a first ECU public key certificate using an in-vehicle CA private key Kr2s stored in the CA key storage 305.
[0071] The encryption processing unit 304 encrypts data and decrypts encrypted data.
[0072] The CA key storage 305 stores the in-vehicle CA public key certificate C_Kr2p, the in-vehicle CA private key Kr2s, and a master key Master_Secret. The in-vehicle CA public key certificate C_Kr2p is a public key certificate relating to an in-vehicle CA public key Kr2p which is paired with the in-vehicle CA private key Kr2s. The in-vehicle CA public key certificate C_Kr2p is acquired from the OEMCA 200 and is securely stored in the CA key storage 305 together with the in-vehicle CA private key Kr2s.
[0073] The CA key generator 308 generates a pair of the in-vehicle CA public key Kr2p and the in-vehicle CA private key Kr2s and stores the in-vehicle CA private key Kr2s in the CA key storage 305.
[0074] The CA public key certificate acquirer 309 requests the OEMCA 200 to issue the in-vehicle CA public key certificate C_Kr2p, and acquires the in-vehicle CA public key certificate C_Kr2p from the OEMCA 200. For example, the CA public key certificate acquirer 309 transmits a CA public key certificate issuance request including the in-vehicle CA public key Kr2p generated by the CA key generator 308 to the OEMCA 200. Upon receiving the in-vehicle CA public key certificate C_Kr2p transmitted by the OEMCA 200, the CA public key certificate acquirer 309 stores the in-vehicle CA public key certificate C_Kr2p in the CA key storage 305.
[0075] The communicator 135 of the root CA 100, the communicator 230 of the OEMCA 200, and the communicator 330 of the in-vehicle CA 300 communicate with each other. Communication between the communicator 135, the communicator 230, and the communicator 330 may be wireless or wired. For example, the communicator 135, the communicator 230, and the communicator 330 may communicate with each other via a wireless communication network such as a wireless LAN or a mobile phone network.
[0076] Alternatively, the communicator 135, the communicator 230, and the communicator 330 may perform communication directly by transmitting and receiving signals using a short-range wireless communication technology or may perform communication via the Internet, a fixed telephone network, a communication network such as a wired LAN or may be connected through a communication cable to perform communication.
[0077] The authenticator 355 performs authentication with the ECU 420.
<Operations of Root CA, OEMCA and in-Vehicle CA>
[0078] FIG. 3 is a sequence chart showing an example of an operation for issuing a public key certificate according to the embodiment. FIG. 3 shows a process in which the root CA 100 issues an OEMCA public key certificate to the OEMCA 200 and the OEMCA 200 issues an in-vehicle CA public key certificate to the in-vehicle CA 300.
[0079] (Step S302) In the OEMCA 200, the CA key generator 208 generates the OEMCA public key Kr1p and the OEMCA private key Kr1s.
[0080] (Step S304) In the OEMCA 200, the CA public key certificate acquirer 209 outputs a public key certificate issuance request including the OEMCA public key Kr1p generated by the CA key generator 208 to the communicator 230. The communicator 230 transmits a public key certificate issuance request to the root CA 100 to apply for issuance of a public key certificate from the root CA 100.
[0081] (Step S306) In the root CA 100, the CA public key certificate generator 102 issues the OEMCA public key certificate C_Kr1p using the OEMCA public key Kr1p included in the public key certificate issuance request transmitted by the OEMCA 200 and the root CA private key KRs stored in the root CA key storage 105. Upon receiving the public key certificate issuance request from the OEMCA 200, the root CA 100 confirms the location of the OEMCA 200 or the like and then issues the OEMCA public key certificate C_Kr1p using the OEMCA public key Kr1p and the root CA private key KRs stored in the root CA key storage 105.
[0082] An example of an electronic signature of the OEMCA public key Kr1p is encrypted data as a result of encrypting a digest of data including the OEMCA public key Kr1p and the OEMCA identification information oemcaid with the root CA private key KRs. Here, a hash value is used as an example of the digest. A public key certificate format of the X.509 standard specified in International Telecommunication Union-telecommunication (ITU-T) or the like is used as an example of the public key certificate format. The OEMCA public key Kr1p is stored at a predetermined position in the public key certificate format of the X.509 standard. The OEMCA identification information oemcaid is also stored at the position of "subject parameter: subject name" in the public key certificate format of the X.509 standard.
[0083] An example of a method of issuing the OEMCA public key certificate C_Kr1p by the CA public key certificate generator 102 will be described below in detail. The CA public key certificate generator 102 calculates a hash value "hash" (Kr1p, oemcaid) of the data of the public key certificate format of the X.509 standard in which the OEMCA public key Kr1p and the OEMCA identification information oemcaid are stored. Next, the CA public key certificate generator 102 encrypts the hash value "hash" (Kr1p, oemcaid) with the root CA private key KRs stored in the root CA key storage 105 of the storage 160. This encrypted data KRs (hash (Kr1p, oemcaid)) is an electronic signature of the OEMCA public key Kr1p. Next, the CA public key certificate generator 102 constructs an OEMCA public key certificate C_Kr1p "Kr1p, oemcaid, KRs (hash (Kr1p, oemcaid))" in the public key certificate format of the X.509 standard which includes the OEMCA public key Kr1p, the OEMCA identification information oemcaid, and the electronic signature KRs (hash (Kr1p, oemcaid)) of the OEMCA public key Kr1p.
[0084] (Step S308) In the root CA 100, the communicator 135 transmits the OEMCA public key certificate C_Kr1p issued by the CA public key certificate generator 102 to the OEMCA 200.
[0085] (Step S310) In the OEMCA 200, the CA public key certificate acquirer 209 acquires the OEMCA public key certificate C_Kr1p transmitted by the root CA 100. Then, the CA public key certificate acquirer 209 stores the OEMCA public key certificate C_Kr1p in the CA key storage 205.
[0086] (Step S312) In the in-vehicle CA 300, the CA key generator 308 generates an in-vehicle CA public key Kr2p and an in-vehicle CA private key Kr2s.
[0087] (Step S314) In the in-vehicle CA 300, the CA public key certificate acquirer 309 outputs a public key certificate issuance request including the in-vehicle CA public key Kr2p generated by the CA key generator 308 to the communicator 330. The communicator 330 transmits a public key certificate request to the OEMCA 200 to apply for issuance of a public key certificate from the OEMCA 200.
[0088] (Step S316) In the OEMCA 200, the public key certificate generator 202 issues an in-vehicle CA public key certificate C_Kr2p using the in-vehicle CA public key Kr2p included in the public key certificate issuance request provided from the in-vehicle CA 300 and the OEMCA private key Kr1s stored in the CA key storage 205.
[0089] An example of the electronic signature of the in-vehicle CA public key Kr2p is encrypted data as a result of encrypting a digest of data including the in-vehicle CA public key Kr2p and the IVCA identification information ivcad with the OEMCA private key Kr1s. Here, a hash value is used as an example of the digest. A public key certificate format of the X.509 standard specified in ITU-T or the like is used as an example of the public key certificate format. The in-vehicle CA public key Kr2p is stored at a predetermined position in the public key certificate format of the X.509 standard. The IVCA identification information ivcaid is also stored at the position of "subject parameter: subject name" in the public key certificate format of the X.509 standard.
[0090] An example of a method of generating the in-vehicle CA public key certificate C_Kr2p in the storage 260 will be specifically described. In the storage 260, the public key certificate generator 202 calculates a hash value "hash" (Kr2p, ivcaid) of the data of the public key certificate format of the X.509 standard in which the in-vehicle CA public key Kr2p and the IVCA identification information ivcaid are stored. Next, the public key certificate generator 202 encrypts the hash value "hash" (Kr2p, ivcaid) with the OEMCA private key Kr1s stored in the CA key storage 205 of the storage 260. The encrypted data Kr1s (hash (Kr2p, ivcaid)) is an electronic signature of the in-vehicle CA public key Kr2p. Next, the public key certificate generator 202 constructs an in-vehicle CA public key certificate C_Kr2p "Kr2p, ivcaid, Kr1s (hash (Kr2p, ivcaid))" in the public key certificate format of the X.509 standard which includes the in-vehicle CA public key Kr2p, the IVCA identification information ivcaid, and the electronic signature Kr1s (hash (Kr2p, ivcaid)) of the in-vehicle CA public key Kr2p.
[0091] (Step S318) In the OEMCA 200, the communicator 230 transmits the in-vehicle CA public key certificate C_Kr2p issued by the public key certificate generator 202 to the in-vehicle CA 300.
[0092] (Step S320) In the in-vehicle CA 300, the CA public key certificate acquirer 309 acquires the in-vehicle CA public key certificate C_Kr2p transmitted by the OEMCA 200. Then, the CA public key certificate acquirer 309 stores the in-vehicle CA public key certificate C_Kr2p in the CA key storage 305.
[0093] In the sequence chart shown in FIG. 3, steps S312 to S320 are performed during a trusted process such as that of a factory line of the automobile manufacturer. This allows the OEMCA 200 to securely confirm the presence of the in-vehicle CA 300.
[0094] Alternatively, the storage 360 of the in-vehicle CA 300 may be constituted of an SIM. While the SIM is authenticated by an SIM application area maintenance server of a communication company, an application which has received a public key certificate issued from the OEMCA 200 over the air may be securely written to an application area in the SIM.
[0095] The description of the present embodiment will continue below with regard to the case in which the in-vehicle CA 300 is constructed, in a telecommunication unit (TCU), using an SIM of a communication module.
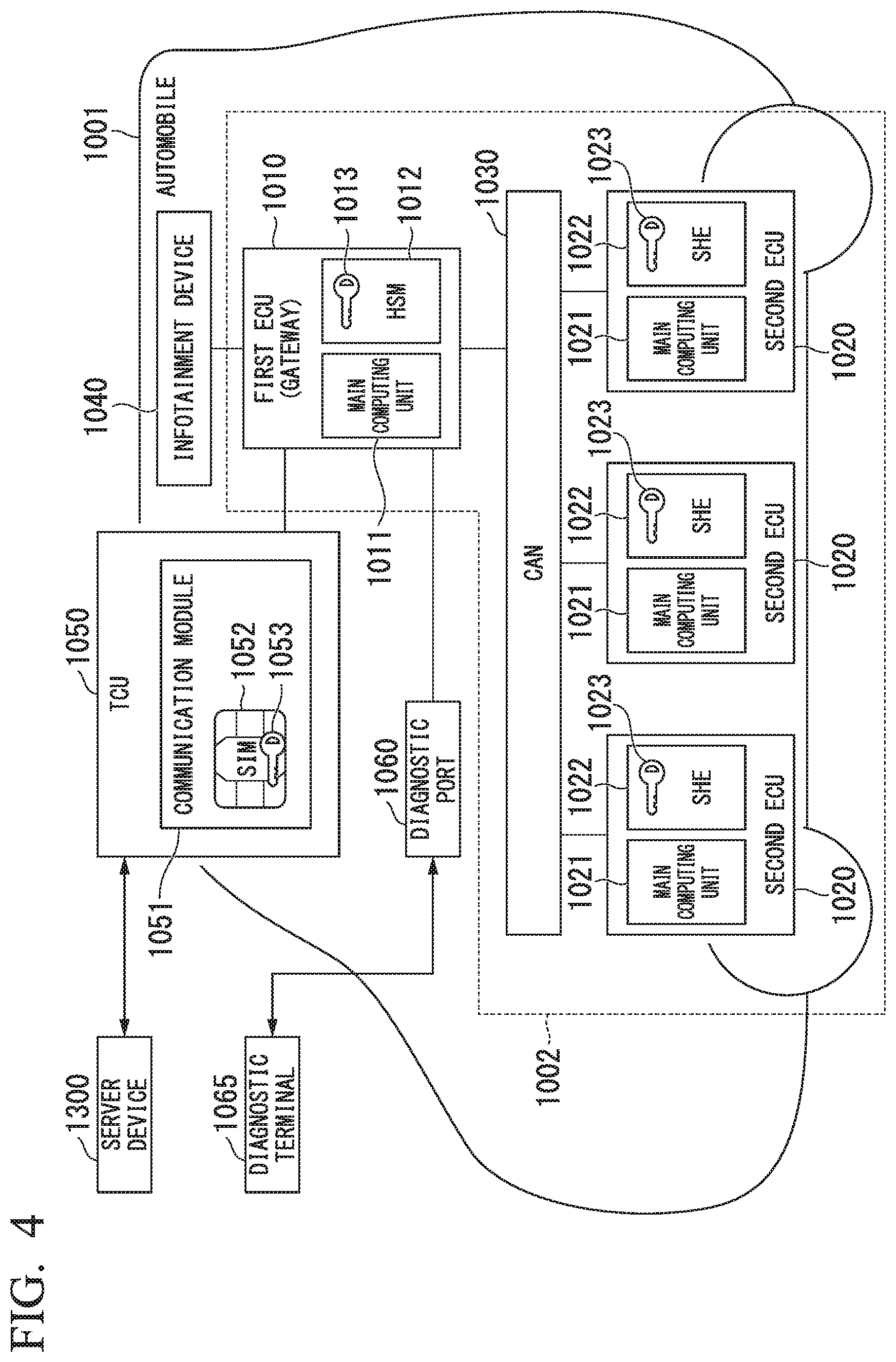
[0096] FIG. 4 is a diagram showing an exemplary configuration of an automobile 1001 according to the present embodiment.
[0097] In FIG. 4, the automobile 1001 includes a first ECU 1010 and a plurality of second ECUs 1020. The first ECU 1010 and the second ECUs 1020 are vehicle-mounted computers provided in the automobile 1001. The first ECU 1010 is an ECU having a gateway function among the ECUs mounted in the automobile 1001. The second ECUs 1020 are ECUs having functions such as engine control among the ECUs mounted in the automobile 1001. Examples of the second ECUs 1020 include an ECU having an engine control function, an ECU having a steering wheel control function, and an ECU having a brake control function.
[0098] The first ECU 1010 and the plurality of second ECUs 1020 are connected to a controller area network (CAN) 1030 provided in the automobile 1001. The CAN 1030 is a communication network. The CAN is known as one of the communication networks installed in vehicles.
[0099] The first ECU 1010 exchanges data with each second ECU 1020 via the CAN 1030. Each of the second ECUs 1020 exchanges data with another second ECU 1020 via the CAN 1030.
[0100] It is to be noted that a communication network other than the CAN may be provided in the automobile 1001 as a communication network installed in the vehicle and data exchange between the first ECU 1010 and the second ECUs 1020 and data exchange between the second ECUs 1020 may be performed via the communication network other than the CAN. For example, a local interconnect network (LIN) may be provided in the automobile 1001. Both the CAN and the LIN may also be provided in the automobile 1001. Further, a second ECU(s) 1020 connected to the LIN may be provided in the automobile 1001. The first ECU 1010 may also be connected to both the CAN and the LIN. Furthermore, the first ECU 1010 may exchange data with a second ECU 1020 connected to the CAN via the CAN and exchange data with a second ECU 1020 connected to the LIN via the LIN. The second ECUs 1020 may also exchange data with each other via the LIN.
[0101] The automobile 1001 includes a diagnostic port 1060. For example, an on-board diagnostics (OBD) port may be used as the diagnostic port 1060. A diagnostic terminal 1065 can be connected to the diagnostic port 1060. The diagnostic port 1060 is connected to the first ECU 1010. The first ECU 1010 and the diagnostic terminal 1065 connected to the diagnostic port 1060 exchange data with each other via the diagnostic port 1060.
[0102] The automobile 1001 includes an infotainment device 1040. Examples of the infotainment device 1040 include those having a navigation function, a position information service function, a multimedia playback function such as for music and movies, a voice communication function, a data communication function, and an internet connection function. The infotainment device 1040 is connected to the first ECU 1010. The first ECU 1010 transmits information input from the infotainment device 1040 to the second ECU 1020.
[0103] The automobile 1001 includes a TCU 1050. The TCU 1050 is a communication device. The TCU 1050 includes a communication module 1051. The communication module 1051 performs wireless communication using a wireless communication network. The communication module 1051 includes an SIM 1052. The SIM 1052 is an SIM in which information for using the wireless communication network is written. The SIM 1052 includes a storage 1053 that stores data such as keys. The communication module 1051 can perform wireless communication by connecting to a wireless communication network using the SIM 1052. An embedded subscriber identity module (eSIM) may also be used as the SIM 1052. The SIM and the eSIM are tamper-resistant. The SIM and the eSIM are examples of secure elements. The secure element is tamper-resistant.
[0104] The TCU 1050 is connected to the first ECU 1010. The first ECU 1010 exchanges data with the communication module 1051 of the TCU 1050.
[0105] In the configuration of FIG. 4, the first ECU 1010 and the TCU 1050 are connected directly to each other to allow data exchange between the first ECU 1010 and the communication module 1051, but the present invention is not limited to this. For example, the TCU 1050 may be connected to the infotainment device 1040 and the first ECU 1010 may exchange data with the communication module 1051 of the TCU 1050 via the infotainment device 1040. Alternatively, instead of the diagnostic terminal 1065, the TCU 1050 may be connected to the diagnostic port 1060 and the first ECU 1010 may exchange data with the communication module 1051 of the TCU 1050 connected to the diagnostic port 1060 via the diagnostic port 1060. Alternatively, the first ECU 1010 may include the communication module 1051 including the SIM 1052. When the first ECU 1010 includes the communication module 1051 including the SIM 1052, the automobile 1001 may not include the TCU 1050.
[0106] The first ECU 1010 includes a main computing unit 1011 and a hardware security module (HSM) 1012. The main computing unit 1011 executes a computer program for realizing the functions of the first ECU 1010. The HSM 1012 has an encryption processing function or the like. The HSM 1012 is tamper-resistant. The HSM 1012 is an example of a secure element (SE). The HSM 1012 includes a storage 1013 for storing data such as keys. The main computing unit 1011 uses the HSM 1012.
[0107] The second ECU 1020 includes a main computing unit 1021 and a secure hardware extension (SHE) 1022. The main computing unit 1021 executes a computer program for realizing the functions of the second ECU 1020. The SHE 1022 has an encryption processing function or the like. The SHE 1022 is tamper-resistant. The SHE 1022 is an example of a secure element. The SHE 1022 includes a storage 1023 for storing data such as keys. The main computing unit 1021 uses the SHE 1022.
[0108] A vehicle-mounted computer system 1002 provided in the automobile 1001 is constructed by connecting the first ECU 1010 and the plurality of second ECUs 1020 to the CAN 1030. The first ECU 1010 has a gateway function and monitors communication between the inside and the outside of the vehicle-mounted computer system 1002. In the present embodiment, the vehicle-mounted computer system 1002 functions as a vehicle-mounted control system of the automobile 1001.
[0109] In the following description, the first ECU 1010 and the second ECU 1020 are simply referred to as ECUs unless specifically distinguished.
[0110] A server device 1300 transmits and receives data to and from the communication module 1051 of the TCU 1050 of the automobile 1001 via a communication line. The server device 1300 transmits and receives data to and from the communication module 1051 of the TCU 1050 of the automobile 1001 via a wireless communication network used by the communication module 1051. Alternatively, the server device 1300 may transmit and receive data to and from the communication module 1051 via the wireless communication network and a communication network such as the Internet. For example, a dedicated line such as a virtual private network (VPN) line may also be connected between the server device 1300 and the communication module 1051 and data may be transmitted and received therebetween via the dedicated line. For example, a dedicated line such as a VPN line may be provided by a wireless communication network corresponding to the SIM 1052.
<First ECU>
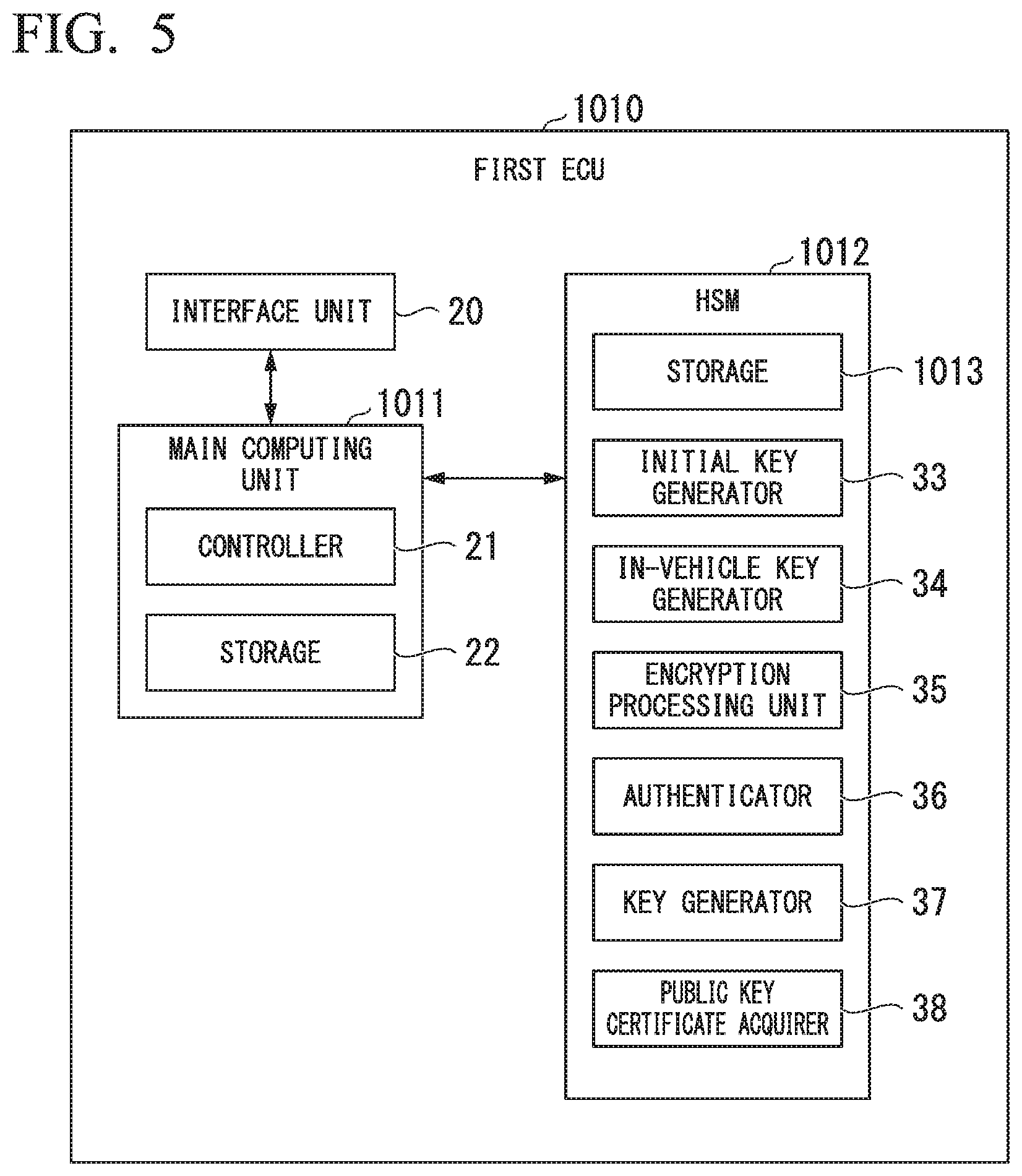
[0111] FIG. 5 is a diagram showing an exemplary configuration of the first ECU 1010. In FIG. 5, the first ECU 1010 includes a main computing unit 1011, an HSM 1012, and an interface unit 20.
[0112] The main computing unit 1011 includes a controller 21 and a storage 22. The HSM 1012 includes a storage 1013, an initial key generator 33, an in-vehicle key generator 34, an encryption processing unit 35, an authenticator 36, a key generator 37, and a public key certificate acquirer 38.
[0113] The interface unit 20 includes an interface for transmitting and receiving data via the CAN 1030, an interface for transmitting and receiving data to and from the infotainment device 1040, an interface for transmitting and receiving data to and from the TCU 1050, and an interface for transmitting and receiving data via the diagnostic port 1060. The main computing unit 1011 transmits and receives data to and from devices other than the first ECU 1010 via the interface unit 20.
[0114] In the interface unit 20, an interface for transmitting and receiving data via the CAN 1030 may include a plurality of ports connected to the CAN 1030. This allows the first ECU 1010 to transmit and receive data to and from the plurality of second ECUs 1020 via the CAN 1030 at the same time.
[0115] The controller 21 controls the first ECU 1010. The storage 22 stores data. The storage 1013 stores data such as keys. The initial key generator 33 generates initial keys of the second ECUs 1020. The in-vehicle key generator 34 generates an in-vehicle key which is a key used inside the automobile 1001. The encryption processing unit 35 encrypts data and decrypts encrypted data. The authenticator 36 performs authentication processing with the TCU 1050. The authenticator 36 also performs authentication processing with the second ECU 1020. The key generator 37 generates a pair of a first ECU public key and a first ECU private key and stores the first ECU private key in the storage 1013. The public key certificate acquirer 38 requests issuance of a first ECU public key certificate from the TCU 1050 and acquires the first ECU public key certificate from the TCU 1050. For example, the public key certificate acquirer 38 transmits a public key certificate issuance request including the first ECU public key generated by the key generator 37 to the TCU 1050. Upon receiving the first ECU public key certificate transmitted by the TCU 1050, the public key certificate acquirer 38 stores the first ECU public key certificate in the storage 1013.
<Second ECU>
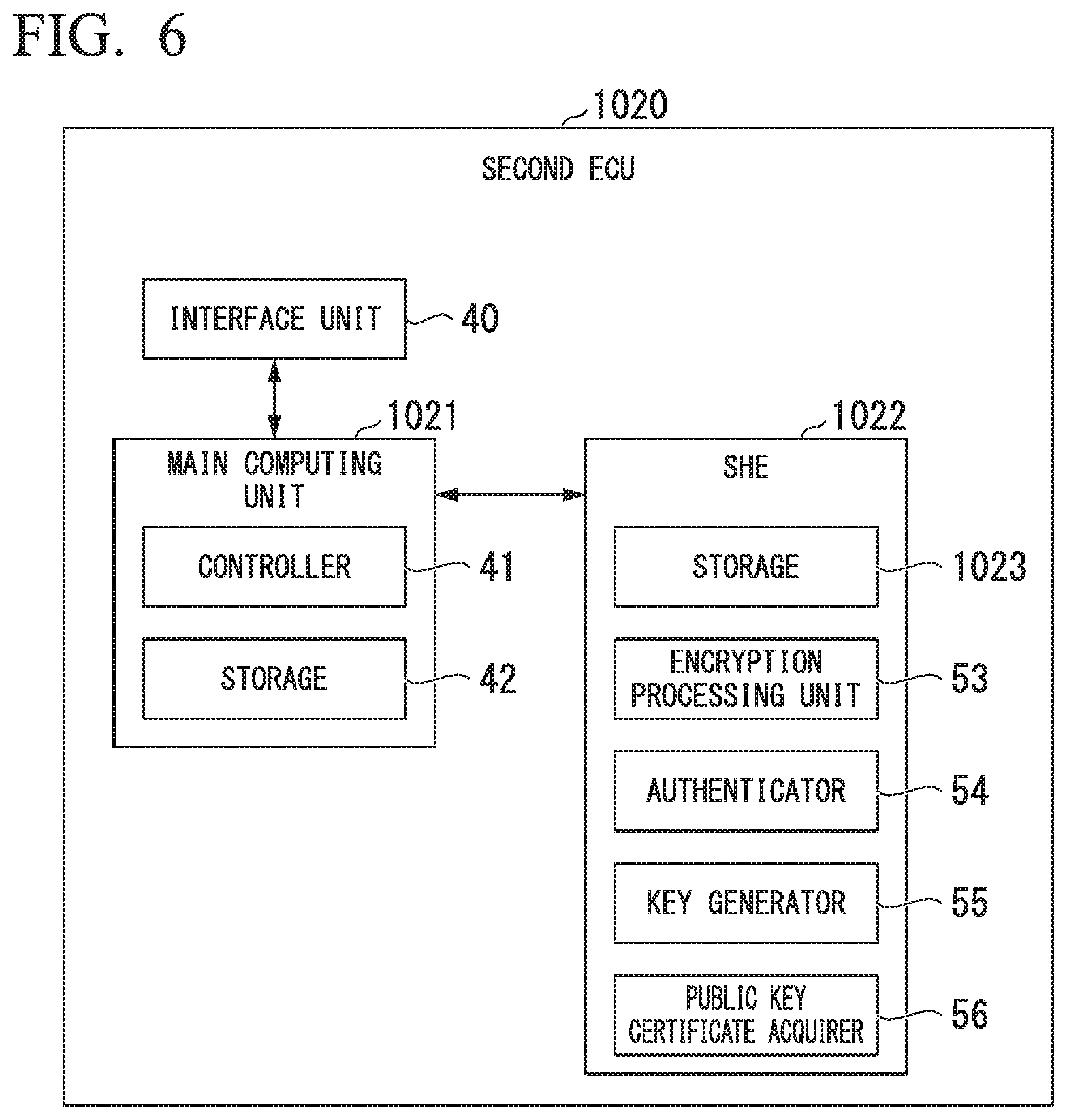
[0116] FIG. 6 is a diagram showing an exemplary configuration of the second ECU 1020. In FIG. 6, the second ECU 1020 includes a main computing unit 1021, an SHE 1022, and an interface unit 40. The main computing unit 1021 includes a controller 41 and a storage 42. The SHE 1022 includes a storage 1023, an encryption processing unit 53, an authenticator 54, a key generator 55, and a public key certificate acquirer 56.
[0117] The interface unit 40 includes an interface for transmitting and receiving data via the CAN 1030. The main computing unit 1021 exchanges data with devices other than the second ECU 1020 via the interface unit 40.
[0118] The controller 41 controls the second ECU 1020. The storage 42 stores data. The storage 1023 stores data such as keys. The encryption processing unit 53 encrypts data and decrypts encrypted data. The authenticator 54 performs authentication processing with the TCU 1050. The authenticator 54 also performs authentication processing with the first ECU 1010. The key generator 55 generates a pair of a second ECU public key and a second ECU private key and stores the second ECU private key in the storage 1023. The public key certificate acquirer 56 requests issuance of a second ECU public key certificate from the TCU 1050 and acquires the second ECU public key certificate from the TCU 1050. For example, the public key certificate acquirer 56 transmits a public key certificate issuance request including the second ECU public key generated by the key generator 55 to the TCU 1050. Upon receiving the second ECU public key certificate transmitted by the TCU 1050, the public key certificate acquirer 56 stores the second ECU public key certificate in the storage 1023.
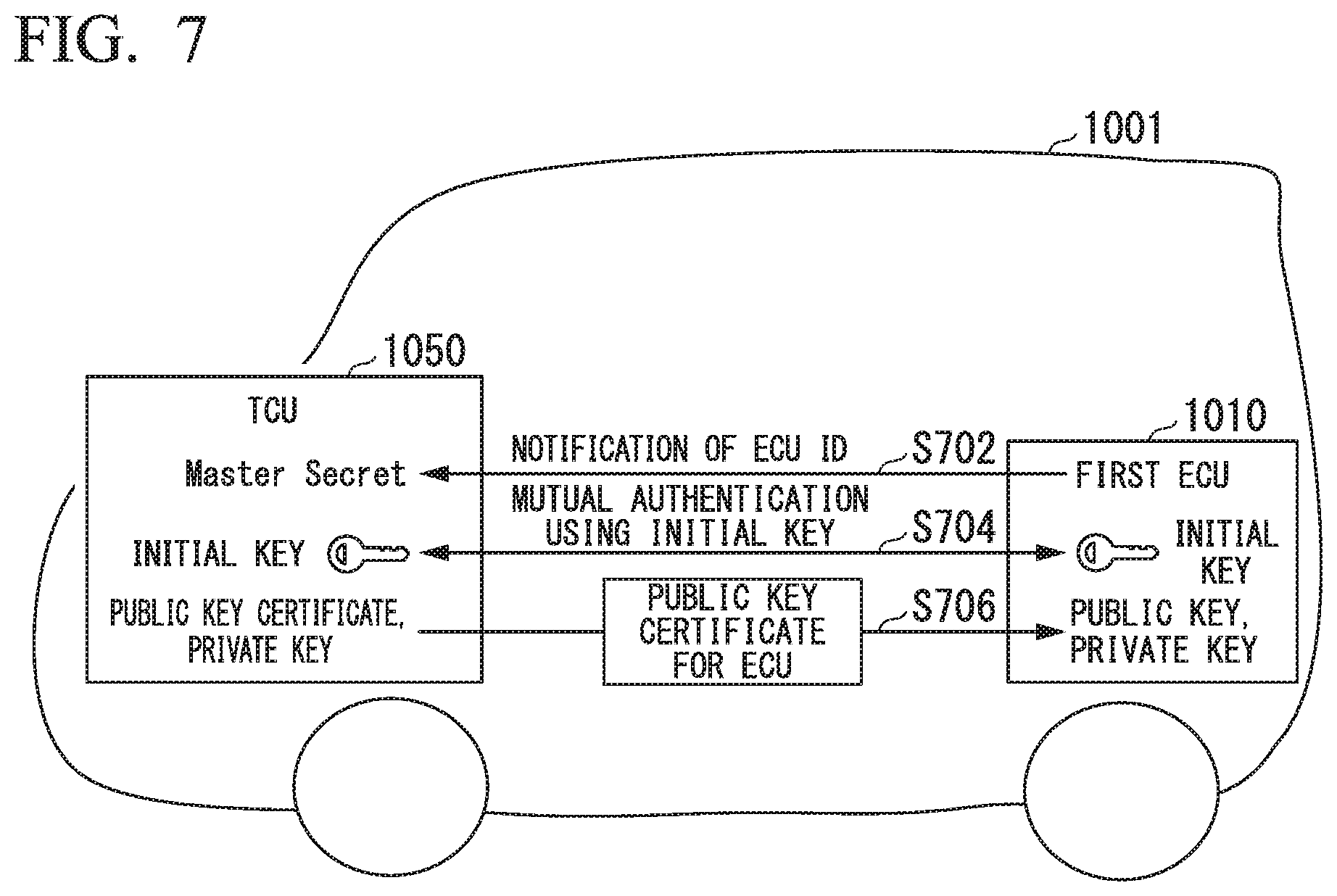
[0119] Next, an example of a method of issuing a public key certificate according to an embodiment will be described with reference to FIG. 7. Here, the case in which the TCU 1050 issues a public key certificate to the first ECU 1010 will be described as an example. It is to be noted that the present invention can also be applied to the case in which the TCU 1050 issues a public key certificate to a second ECU 1020.
[0120] (Step S702) The first ECU 1010 transmits an ECU_ID of the first ECU 1010 to the TCU 1050.
[0121] (Step S704) Upon receiving the ECU_ID of the first ECU 1010 transmitted by the first ECU 1010, the TCU 1050 performs mutual authentication with the first ECU 1010 using an initial key (="digest (Master_Secret, ECU_ID)") generated from both the ECU_ID of the first ECU 1010 and a master key (Master_Secret). In the present embodiment, a challenge/response authentication method is used as an example of this mutual authentication method.
[0122] In the challenge/response authentication method, a challenge value (for example, a random number generated by the authenticator 355 of the SIM 1052 of the TCU 1050) is sent from one side (the authenticator 355) to the other side (the authenticator 36 of the HSM 1012 of the first ECU 1010). The authenticator 36 of the HSM 1012 of the first ECU 1010 encrypts the challenge value with an initial key stored in the storage 1013 and sends the encrypted data of the challenge value to the authenticator 355 of the SIM 1052 of the TCU 1050 as a response value. The authenticator 355 of the SIM 1052 of the TCU 1050 decrypts the response value with the initial key and checks whether or not the decryption result matches the challenge value. If the checking of the response value passes, authentication in one direction (the direction in which the SIM 1052 of the TCU 1050 authenticates the first ECU 1010) succeeds. The same is performed for the other direction (the direction in which the first ECU 1010 authenticates the SIM 1052 of the TCU 1050) and, if the checking of the response value passes, authentication in the other direction (the direction in which the first ECU 1010 authenticates the SIM 1052 of the TCU 1050) succeeds. If the authentication succeeds in both directions, the mutual authentication between the SIM 1052 of the TCU 1050 and the first ECU 1010 succeeds, and if the authentication fails in either direction, the mutual authentication between the SIM 1052 of the TCU 1050 and the first ECU 1010 fails.
[0123] (Step S706) If the authentication of the first ECU 1010 succeeds, a public key certificate is issued from the TCU 1050 to the first ECU 1010.
<Process of Writing ECU Initial Key to ECU>
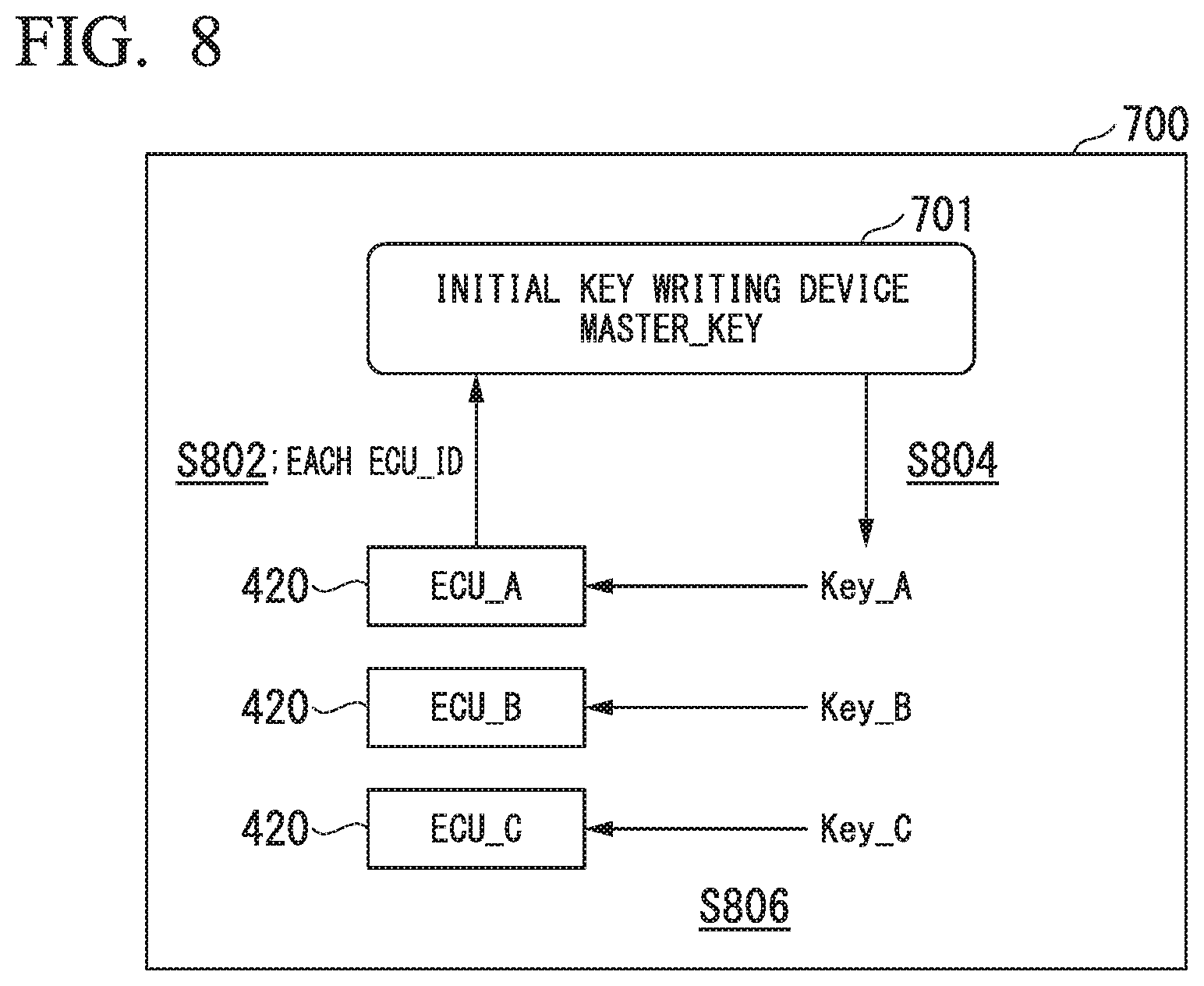
[0124] A process of writing ECU initial keys to the first ECU 1010 and the second ECUs 1020 will be described with reference to FIG. 8. In FIG. 8, the first ECU 1010 and the second ECUs 1020 are referred to as ECUs 420.
[0125] In FIG. 8, an initial key writing device 701 is installed in a room 700 in a manufacturing factory of ECUs 420. The room 700 is a room where security (safety) of information is secured. The initial key writing device 701 has a master key (MASTER_KEY) Master_Secret. The master key Master_Secret is set in the initial key writing device 701 in advance. The setting of the master key Master_Secret in the initial key writing device 701 is securely performed. The master key Master_Secret of the initial key writing device 701 is the same as the master key Master_Secret stored in the storage 1013 of the HSM 1012 of the first ECU 1010 of the automobile 1001. The master key Master_Secret is securely managed.
[0126] It is to be noted that the master key Master_Secret is not necessarily stored in the HSM 1012 of the first ECU 1010.
[0127] The initial key writing device 701 has ECU connection interfaces for exchanging data with ECUs 420. The initial key writing device 701 exchanges data with the ECUs 420 connected to the ECU connection interfaces. Here, it is assumed that the initial key writing device 701 has three ECU connection interfaces and thus can be simultaneously connected to three second ECUs 1020 through the ECU connection interfaces.
[0128] In FIG. 8, three ECUs 420 are shown as the ECUs 420 mounted in the automobile 1001. The three ECUs 420 will be referred to as ECU_A_420, ECU_B_420, and ECU_C_420. Here, a description will be provided with reference to the ECU_A_420, ECU_B_420, and ECU_C_420 as an example.
[0129] The initial key writing device 701 is simultaneously connected to the ECU_A_420, the ECU_B_420, and the ECU_C_420 through the ECU connection interfaces.
[0130] (Step S802) Each of the ECU_A_420, the ECU_B_420, and the ECU_C_420 transmits its own ECU identifier (ECU_ID) to the initial key writing device 701. Specifically, the ECU_A_420 transmits an ECU identifier ECU_ID_A to the initial key writing device 701. The ECU_B_420 transmits an ECU identifier ECU_ID_B to the initial key writing device 701. The ECU_C_420 transmits an ECU identifier ECU_ID_C to the initial key writing device 701.
[0131] For example, an identifier which is embedded in a semiconductor integrated circuit such as an LSI which is hardware constituting the ECU 420 when it is manufactured may be used as the ECU identifier. For example, an identifier embedded in an LSI of a microcomputer of the ECU 420 may be used as the ECU identifier.
[0132] (Step S804) The initial key writing device 701 generates an ECU initial key using the master key Master_Secret and the ECU identifier. Specifically, the initial key writing device 701 generates an ECU initial key Key_A of the ECU_A_420 using the master key Master_Secret and the ECU identifier ECU_ID_A of the ECU_A_420. The initial key writing device 701 generates an ECU initial key Key_B of the ECU_B_420 using the master key Master_Secret and the ECU identifier ECU_ID_B of the ECU_B_420. The initial key writing device 701 generates an ECU initial key Key_C of the ECU_C_420 using the master key Master_Secret and the ECU identifier ECU_ID_C of the ECU_C_420.
[0133] Examples 1 and 2 of the method of generating an ECU initial key will be described.
Example 1 of Method of Generating ECU Initial Key
[0134] Example 1 of the method of generating an ECU initial key uses a hash function. For example, a hash value may be calculated using connection data of the ECU identifier and the master key Master_Secret as an input value and the calculated hash value may be used as the ECU initial key.
Example 2 of the Method of Generating ECU Initial Key
[0135] Example 2 of the method of generating an ECU initial key uses an exclusive OR operation. For example, an exclusive OR operation between the master key Master_Secret and the ECU identifier may be performed and the resulting value of the operation "master key Master_Secret xor ECU identifier" may be used as the ECU initial key. Here, "A xor B" is the exclusive OR of A and B.
[0136] (Step S806) The initial key writing device 701 writes the generated ECU initial key to the corresponding second ECU 1020. Specifically, the initial key writing device 701 writes the ECU initial key Key_A to the ECU_A_420. The initial key writing device 701 writes the ECU initial key Key_B to the ECU_B_420. The initial key writing device 701 writes the ECU initial key Key_C to the ECU_C_420.
[0137] The ECU_A_420, the ECU_B_420, and the ECU_C_420 are mounted in the automobile 1001 after the ECU initial keys are written thereto.
Example 1 of Distribution of in-Vehicle Common Key
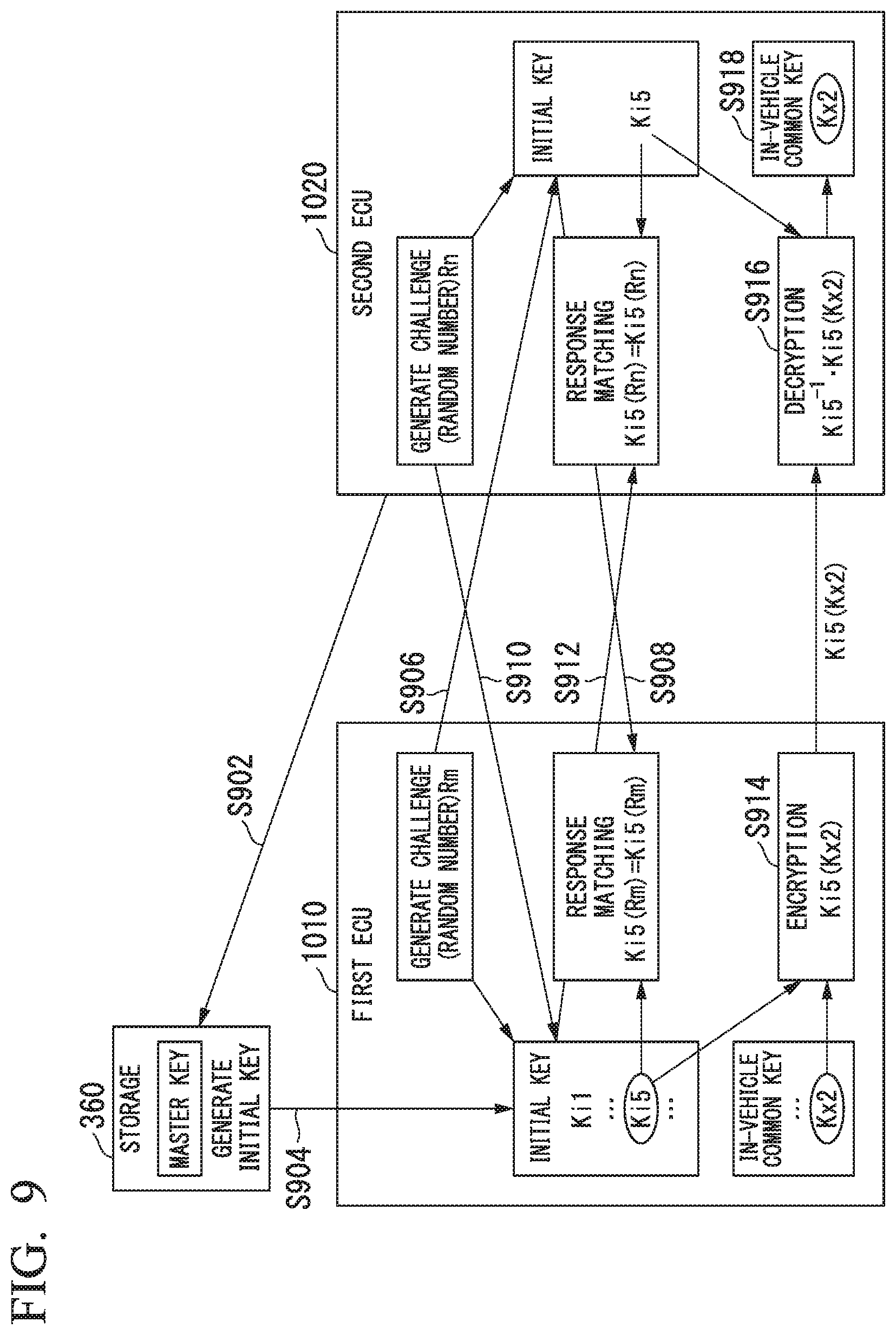
[0138] Example 1 of distribution of an in-vehicle common key according to the embodiment will be described with reference to FIG. 9. FIG. 9 shows a method of distributing an in-vehicle common key to the second ECU 1020 in the automobile 1001.
[0139] The storage 1013 in the HSM 1012 of the first ECU (master ECU) 1010 stores the initial key of the second ECU 1020 already mounted in the automobile 1001. The storage 1013 also stores the latest in-vehicle common key Kx2. The in-vehicle common key Kx2 is the latest in-vehicle common key distributed in the past to the second ECU 1020 already mounted in the automobile 1001.
[0140] Here, a description will be provided with regard to one second ECU 1020 installed in the automobile 1001. The SHE 1022 of the second ECU 1020 stores an initial key Ki5 of the second ECU 1020 in the storage 1023. The second ECU 1020 has its own identifier ECU JD. The storage 360 of the in-vehicle CA 300 stores the master key in the CA key storage 305. The master key stored in the CA key storage 305 of the storage 360 is the same as the master key used together with the identifier ECU JD of the second ECU 1020 when generating the initial key Ki5 stored in the storage 1023 of the second ECU 1020.
[0141] (Step S902) The second ECU 1020 provides its own identifier ECU JD to the storage 360 when power is turned on for the first time after the second ECU 1020 is mounted in the automobile 1001. The identifier ECU JD of the second ECU 1020 is transmitted from the second ECU 1020 to the communication module 1051 via the first ECU 1010. The communication module 1051 provides the received identifier ECU_ID of the second ECU 1020 to the storage 360.
[0142] (Step S904) The initial key generator 301 acquires the master key from the CA key storage 305 and uses the acquired master key and the identifier ECU_ID of the second ECU 1020 to generate the initial key Ki5 of the second ECU 1020. The communicator 330 transmits a pair of the initial key Ki5 of the second ECU 1020 generated by the initial key generator 301 and the identifier ECU JD of the second ECU 1020 to the first ECU 1010.
[0143] The first ECU 1010 provides the received pair of the initial key Ki5 of the second ECU 1020 and the identifier ECU JD of the second ECU 1020 to the HSM 1012. The HSM 1012 stores the initial key Ki5 of the second ECU 1020 in the storage 1013 in association with the identifier ECU_ID of the second ECU 1020. As a result, the first ECU 1010 shares the initial key Ki5 of the second ECU 1020 with the second ECU 1020.
[0144] The method of generating the initial key of the second ECU 1020 is predetermined. Examples 1 and 2 of the method of generating the initial key of the second ECU 1020 will be described below.
Example 1 of Method of Generating Initial Key of Second ECU 1020
[0145] Example 1 of the method of generating the initial key of the second ECU 1020 uses a hash function. For example, a hash value may be calculated using connection data of the identifier ECU_ID of the second ECU 1020 and the master key as an input value and the calculated hash value may be used as the initial key of the second ECU 1020.
Example 2 of Method of Generating Initial Key of Second ECU 1020
[0146] Example 2 of the method of generating the initial key of the second ECU 1020 uses an exclusive OR operation. For example, an exclusive OR operation between the master key and the identifier ECU_ID of the second ECU 1020 may be performed and the resulting value of the operation "master key xor identifier ECU_ID" may be used as the initial key of the second ECU 1020. Here, "A xor B" is the exclusive OR of A and B.
[0147] (Step S906) The HSM 1012 of the first ECU 1010 generates a random number Rm and sets the generated random number Rm as a challenge value. The first ECU 1010 transmits the challenge value Rm to the second ECU 1020.
[0148] (Step S908) The second ECU 1020 provides the challenge value Rm received from the first ECU 1010 to the SHE 1022. The SHE 1022 of the second ECU 1020 encrypts the challenge value Rm with the initial key Ki5 of the second ECU 1020 stored in the storage 1023 to generate encrypted data Ki5(Rm). The second ECU 1020 transmits the encrypted data Ki5(Rm) to the first ECU 1010 as a response value. The first ECU 1010 provides the received response value Ki5(Rm) to the HSM 1012.
[0149] The HSM 1012 performs a response matching process on the response value Ki5(Rm). In the response matching process, the HSM 1012 verifies the response value Ki5(Rm) using the initial key Ki5 of the second ECU 1020 stored in the storage 1013. Examples of the method of verifying the response value Ki5(Rm) include examples 1 and 2 of the verification method shown below.
Example 1 of Verification Method
[0150] The HSM 1012 encrypts the challenge value Rm with each of a plurality of initial keys Ki1, . . . , Ki5, . . . stored in the storage 1013 and determines whether or not each encryption result matches the response value Ki5(Rm). The verification of the response value Ki5(Rm) succeeds if the determination result is that there is only one encryption result matching the response value Ki5(Rm). On the other hand, the validation of the response value Ki5(Rm) fails if the determination result is that there is no encryption result matching the response value Ki5(Rm) or that there are a plurality of encryption results matching the response value Ki5(Rm).
Example 2 of Verification Method
[0151] The HSM 1012 decrypts the response value Ki5(Rm) with each of the plurality of initial keys Ki1, . . . , Ki5, . . . stored in the storage 1013 and determines whether or not each decryption result matches the challenge value Rm. The verification of the response value Ki5(Rm) succeeds if the determination result is that there is only one decryption result matching the challenge value Rm. On the other hand, the verification of the response value Ki5(Rm) fails if the determination result is that there is no decryption result matching the challenge value Rm or that there are a plurality of decryption results matching the challenge value Rm.
[0152] If the verification of the response value Ki5(Rm) succeeds, the process proceeds to the subsequent step. On the other hand, if the verification of the response value Ki5(Rm) fails, the process of FIG. 9 ends. If the verification of the response value Ki5(Rm) fails, predetermined error processing may be performed.
[0153] (Step S910) The SHE 1022 of the second ECU 1020 generates a random number Rn and sets the generated random number Rn as a challenge value. The second ECU 1020 transmits the challenge value Rn to the master ECU 1010.
[0154] (Step S912) The first ECU 1010 provides the challenge value Rn received from the second ECU 1020 to the HSM 1012. The HSM 1012 generates encrypted data Ki5(Rn) by encrypting the challenge value Rn with the initial key Ki5 of the second ECU 1020 used when the verification of the response value Ki5(Rm) succeeds in the step S908. The first ECU 1010 transmits the encrypted data Ki5(Rn) as a response value to the second ECU 1020. The second ECU 1020 provides the received response value Ki5(Rn) to the SHE 1022.
[0155] The SHE 1022 performs a response matching process on the response value Ki5(Rn). In the response matching process, the SHE 1022 verifies the response value Ki5(Rn) using the initial key Ki5 of the second ECU 1020 stored in the storage 1023. Examples of the method of verifying the response value Ki5(Rn) include the same methods as those of the examples 1 and 2 of the verification method described above.
[0156] If the verification of the response value Ki5(Rn) succeeds, the process proceeds to the subsequent step. On the other hand, if the verification of the response value Ki5(Rn) fails, the process of FIG. 9 ends. If the verification of the response value Ki5(Rn) fails, predetermined error processing may be performed.
[0157] (Step S914) The HSM 1012 of the first ECU 1010 encrypts the in-vehicle common key Kx2 stored in the storage 1013 using the initial key Ki5 of the second ECU 1020 used when the verification of the response value Ki5(Rn) succeeds in the step S908 to generate an in-vehicle exchange key Ki5(Kx2). The first ECU 1010 transmits the in-vehicle exchange key Ki5(Kx2) to the second ECU 1020. The second ECU 1020 provides the received in-vehicle exchange key Ki5(Kx2) to the SHE 1022.
[0158] (Step S916) The SHE 1022 of the second ECU 1020 decrypts the encrypted in-vehicle common key Ki5(Kx2) with the initial key Ki5 of the second ECU 1020 stored in the storage 1023. An in-vehicle common key Kx2 is obtained as the decryption result.
[0159] (Step S918) The SHE 1022 of the second ECU 1020 stores the in-vehicle common key Kx2 of the decryption result in the storage 1023.
[0160] In example 1 of the communication method described above, the storage 360 has a master key having a relatively high level of demand for key security and uses the master key to generate initial keys of the second ECUs 1020. Also, the HSM 1012 performs processing for distributing the in-vehicle common key having a relatively high level of demand for high-speed key distribution.
Second Embodiment
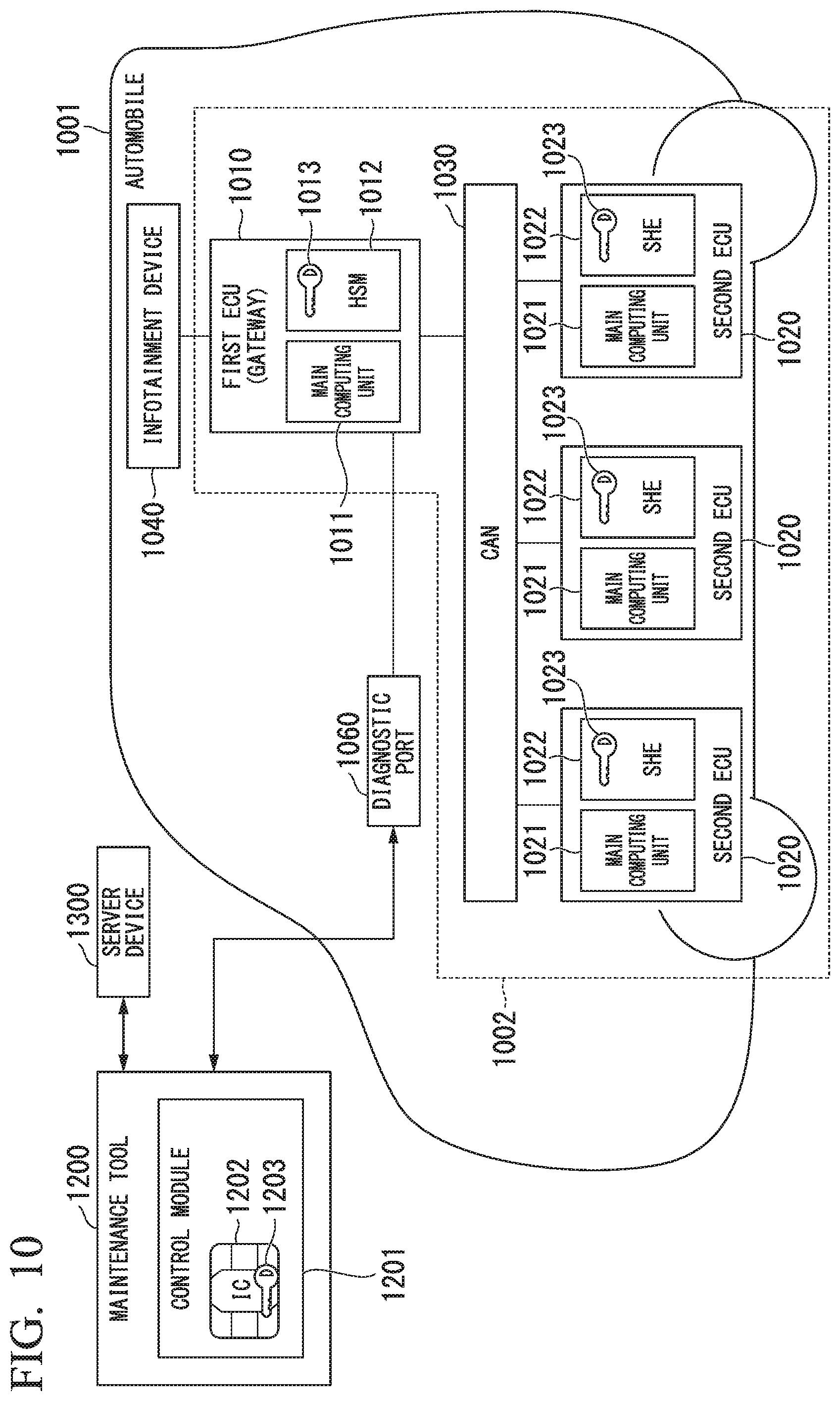
[0161] FIG. 10 is a diagram showing an exemplary configuration of an automobile 1001 according to the present embodiment. The present embodiment will be described with reference to the case in which a public key certificate is issued from a maintenance tool outside the automobile to a first ECU 1010 and second ECUs 1020 as an example.
[0162] In FIG. 10, portions corresponding to those in FIG. 4 are denoted by the same reference signs and descriptions thereof will be omitted. In the exemplary configuration of the automobile 1001 shown in FIG. 10, a maintenance tool 1200 can be connected to a diagnostic port 1060. The first ECU 1010 and the maintenance tool 1200 connected to the diagnostic port 1060 exchange data via the diagnostic port 1060. The maintenance tool 1200 may have the function of a diagnostic terminal of the related art connected to an OBD port.
[0163] The maintenance tool 1200 includes a control module 1201. The control module 1201 includes an integrated circuit (IC) chip 1202. The IC chip 1202 includes a storage 1203 that stores data such as keys. The IC chip 1202 is tamper-resistant. The IC chip 1202 is an example of a secure element. The IC chip 1202 is a type of computer and realizes a desired function by a computer program.
[0164] The configuration of the in-vehicle CA 300 shown in FIG. 2 can be applied as the configuration of a CA constructed using the IC chip 1202 in the maintenance tool 1200.
[0165] A server device 1300 transmits and receives data to and from the maintenance tool 1200 via a communication line. For example, a dedicated line such as a VPN line may be connected between the server device 1300 and the maintenance tool 1200 and data may be transmitted and received therebetween via the dedicated line.
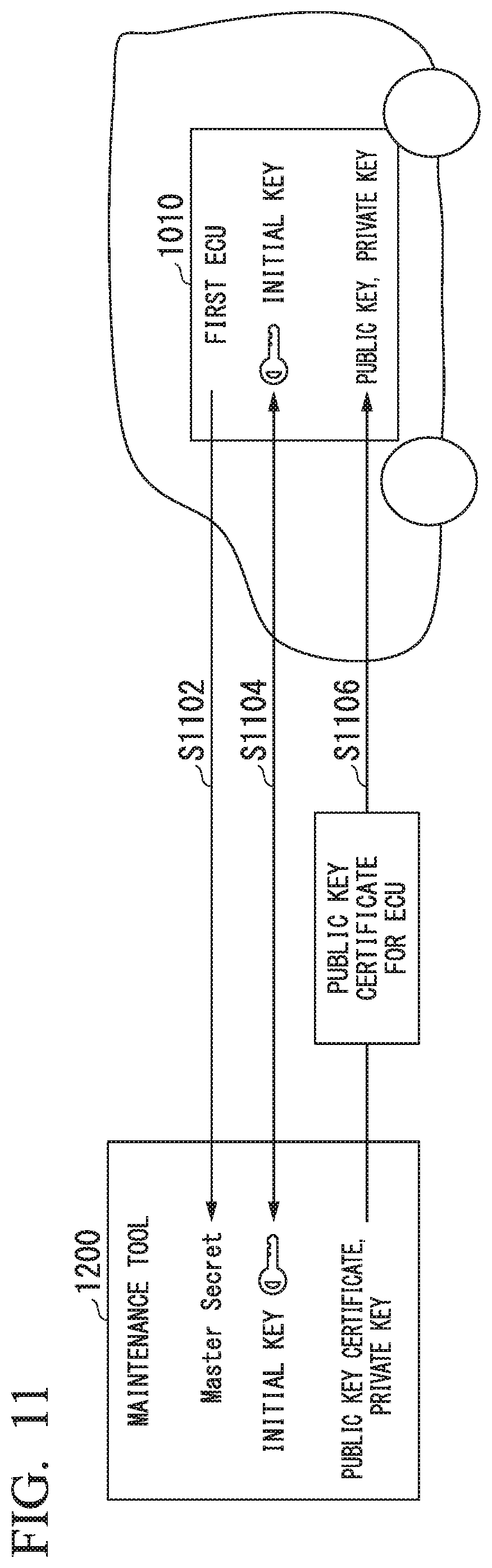
[0166] Next, an example of a method of issuing a public key certificate according to an embodiment will be described with reference to FIG. 11. Here, a description will be provided with regard to the case in which the maintenance tool 1200 issues a public key certificate to the first ECU 1010 as an example. It is to be noted that the present invention can also be applied to the case in which the maintenance tool 1200 issues a public key certificate to a second ECU 1020.
[0167] (Step S1102) The first ECU 1010 transmits an ECU_ID of the first ECU 1010 to the maintenance tool 1200.
[0168] (Step S1104) Upon receiving the ECU_ID of the first ECU 1010 transmitted by the first ECU 1010, the maintenance tool 1200 performs mutual authentication with the first ECU 1010 using an initial key (="digest (Master_Secret, ECU_ID)") generated from the ECU_ID of the first ECU 1010 and the master key (Master_Secret).
[0169] (Step S1106) If the authentication of the first ECU 1010 succeeds, a public key certificate is issued from the maintenance tool 1200 to the first ECU 1010.
Third Embodiment
[0170] FIG. 12 is a diagram showing an exemplary configuration of an automobile 1001 according to the present embodiment. The present embodiment will be described with reference to the case in which a public key certificate is issued from a server device 1300 outside the automobile to a first ECU 1010 as an example.
[0171] In FIG. 12, portions corresponding to those in FIG. 4 are denoted by the same reference signs and descriptions thereof will be omitted. In the exemplary configuration of the automobile shown in FIG. 12, an SIM 1052 of a communication module 1051 of a TCU 1050 does not have a storage 1053 that stores data such as keys.
[0172] The configuration of the in-vehicle CA 300 in FIG. 2 can be applied as the configuration of a CA disposed in the server device 1300.
[0173] Next, an example of a method of issuing a public key certificate according to an embodiment will be described with reference to FIG. 13. Here, a description will be provided with regard to the case in which the server device 1300 issues a public key certificate to the first ECU 1010 as an example. It is to be noted that the present invention can also be applied to the case in which the server device 1300 issues a public key certificate to a second ECU 1020.
[0174] (Step S1302) The first ECU 1010 transmits an ECU_ID of the first ECU 1010 to the server device 1300.
[0175] (Step S1304) Upon receiving the ECU_ID of the first ECU 1010 transmitted by the first ECU 1010, the server device 1300 performs mutual authentication with the first ECU 1010 using an initial key (="digest (Master_Secret, ECU_ID)") generated from the ECU_ID of the first ECU 1010 and the master key (Master_Secret).
[0176] (Step S1306) If the authentication of the first ECU 1010 succeeds, a public key certificate is issued from the server device 1300 to the first ECU 1010.
Fourth Embodiment
[0177] FIG. 14 is a diagram showing an exemplary configuration of an automobile 1001 according to the present embodiment. The present embodiment will be described with reference to the case in which a public key certificate is issued from a first ECU 1010 to a second ECU 1020 as an example.
[0178] In FIG. 14, portions corresponding to those in FIG. 4 are denoted by the same reference signs and descriptions thereof will be omitted.
[0179] Next, an example of a method of issuing a public key certificate according to an embodiment will be described with reference to FIG. 15. Here, a description will be provided with regard to the case in which the first ECU 1010 issues a public key certificate to the second ECU 1020 as an example.
[0180] (Step S1502) The second ECU 1020 transmits an ECU_ID of the second ECU 1020 to the first ECU 1010.
[0181] (Step S1504) Upon receiving the ECU_ID of the second ECU 1020 transmitted by the second ECU 1020, the first ECU 1010 performs mutual authentication with the second ECU 1020 using an initial key (="digest (Master_Secret, ECU_ID)") generated from the ECU_ID of the second ECU 1020 and the master key (Master_Secret). In the present embodiment, the challenge/response authentication method described above is used as an example of this mutual authentication method.
[0182] (Step S1506) If the authentication of the second ECU 1020 succeeds, a public key certificate is issued from the first ECU 1010 to the second ECU 1020.
[0183] In the embodiments described above, authentication is performed between the SIM 1052 of the communication module 1051 of the TCU 1050 and the first ECU 1010, between the IC chip 1202 of the maintenance tool 1200 and the first ECU 1010, between the server device 1300 and the first ECU 1010, and between the first ECU 1010 and the second ECU 1020 using the initial key. However, the present invention is not limited to these examples. For example, authentication may be performed between the SIM 1052 of the communication module 1051 of the TCU 1050 and the first ECU 1010, between the IC chip 1202 of the maintenance tool 1200 and the first ECU 1010, between the server device 1300 and the first ECU 1010, and between the first ECU 1010 and the second ECU 1020 using an in-vehicle common key instead of the initial key. When authenticating is performed with the in-vehicle common key, the first ECU 1010 transmits the in-vehicle common key to the SIM 1052 of the communication module 1051 of the TCU 1050, the IC chip 1202 of the maintenance tool 1200, and the server device 1300. The first ECU 1010 may encrypt the in-vehicle common key with the initial key and transmit the encrypted common key.
<Modification>
[0184] FIG. 16 is a diagram showing a hierarchical structure according to a modification. The hierarchical structure 2 according to the modification is identical to the hierarchical structure 1 according to the above embodiments with the in-vehicle CA 300 omitted. That is, in the hierarchical structure 2 according to the modification, an OEMCA 200 issues a public key certificate to a first ECU 1010 and an application installed in the first ECU 1010. The configuration of the in-vehicle CA 300 in FIG. 2 can be applied as the configuration of the OEMCA 200.
<Operations of OEMCA and First ECU>
[0185] Next, an example of a method of issuing a public key certificate according to the modification will be described with reference to FIG. 17. Here, a description will be provided with regard to the case in which the OEMCA 200 issues a public key certificate to the first ECU 1010 as an example. It is to be noted that the present invention can also be applied to the case in which the OEMCA 200 issues a public key certificate to a second ECU 1020.
[0186] (Step S1702) The first ECU 1010 transmits an ECU_ID of the first ECU 1010 to the OEMCA 200.
[0187] (Step S1704) Upon receipt of the ECU_ID of the first ECU 1010 transmitted by the first ECU 1010, the OEMCA 200 performs mutual authentication with the first ECU 1010 using an initial key (="digest (Master_Secret, ECU_ID)") generated from the ECU_ID of the first ECU 1010 and the master key (Master_Secret).
[0188] (Step S1706) If the authentication of the first ECU 1010 succeeds, a public key certificate is issued from the OEMCA 200 to the first ECU 1010.
[0189] According to the embodiments and modification, a new public key infrastructure is provided for authentication of automobiles, vehicle-mounted ECUs, and applications installed in ECUs. Specifically, this has three layers, i.e., a layer of a root CA that authenticates automobile manufacturers, a layer of OEMCAs operated by their automobile manufacturers, and a layer of in-vehicle CAs that issue public key certificates to in-vehicle ECUs or applications.
[0190] Furthermore, an initial key derived from a master key preset in each ECU or an in-vehicle common key that the first ECU delivers to the second ECU using the initial key is used when a public key certificate is issued from an in-vehicle CA to an automobile, ECUs, or applications installed in ECUs. Thereby, it is possible to issue public key certificates after confirming the trustworthiness of ECUs.
[0191] In addition, it is possible to prevent issuance of public key certificates to fake ECUs or fake applications installed in ECUs. Further, authentication based on a public key certificate can be performed between automobiles of different automobile manufacturers, between ECUs, and between applications installed in ECUs.
[0192] Although the embodiments of the present invention have been described above in detail with reference to the drawings, the specific configurations thereof are not limited to those of the embodiments and also include designs or the like without departing from the spirit of the present invention.
[0193] Although vehicles are exemplified by automobiles in the above embodiments, the present invention can also be applied to vehicles other than automobiles such as motorized bicycles or railroad cars.
[0194] A computer program for realizing the functions of the root CA, the OEMCA, the first ECU, or the second ECUs may be recorded on a computer-readable recording medium and a computer system may be caused to read and execute the program recorded on the recording medium. The "computer system" referred to here may include an OS or hardware such as peripheral devices. The "computer-readable recording medium" refers to a portable medium such as a flexible disk, a magneto-optical disk, a ROM, a writable nonvolatile memory such as a flash memory, or a digital versatile disc (DVD), or a storage device such as a hard disk provided in a computer system.
[0195] The "computer readable recording medium" includes one that holds the program for a certain period of time, like a volatile memory (for example, a dynamic random access memory (DRAM)) provided in a computer system which serves as a server or a client when the program has been transmitted via a network such as the Internet or a communication line such as a telephone line.
[0196] The program may also be transmitted from a computer system in which the program is stored in a storage device or the like to another computer system via a transmission medium or by transmission waves in the transmission medium. Here, the "transmission medium" for transmitting the program refers to a medium having a function of transmitting information, like a network (a communication network) such as the Internet and a communication line (a communication wire) such as a telephone line.
[0197] The program may be one for realizing some of the above-described functions.
[0198] The program may also be a so-called differential file (differential program) which can realize the above-described functions in combination with a program already recorded in the computer system.
INDUSTRIAL APPLICABILITY
[0199] According to the present invention, it is possible to appropriately issue a public key certificate to an automobile, an ECU, or an application installed in the ECU.
REFERENCE SIGNS LIST
[0200] 100 Root CA [0201] 102 CA public key certificate generator [0202] 105 Root CA key storage [0203] 145 Controller [0204] 150 Application [0205] 135 Communicator [0206] 160 Storage [0207] 200 OEMCA [0208] 202 Public key certificate generator [0209] 205 CA key storage [0210] 208 CA key generator [0211] 209 CA public key certificate acquirer [0212] 230 Communicator [0213] 240 Controller [0214] 250 Application [0215] 260 Storage [0216] 300 In-vehicle CA [0217] 301 Initial key generator [0218] 302 Public key certificate generator [0219] 304 Encryption processing unit [0220] 305 CA key storage [0221] 308 CA key generator [0222] 309 CA public key certificate acquirer [0223] 330 Communicator [0224] 340 Controller [0225] 345 Application [0226] 355 Authenticator [0227] 360 Storage [0228] 1001 Automobile [0229] 1010 First ECU [0230] 1011 Main computing unit [0231] 1012 HSM [0232] 1013 Storage [0233] 1021 Main computing unit [0234] 1022 SHE [0235] 1023 Storage [0236] 20 Interface unit [0237] 21 Controller [0238] 22 Storage [0239] 33 Initial key generator [0240] 34 In-vehicle key generator [0241] 35 Encryption processing unit [0242] 36 Authenticator [0243] 37 Key generator [0244] 38 Public key certificate acquirer [0245] 1020 Second ECU [0246] 40 Interface unit [0247] 41 Controller [0248] 42 Storage [0249] 53 Encryption processing unit [0250] 54 Authenticator [0251] 55 Key generator [0252] 56 Public key certificate acquirer [0253] 1030 CAN [0254] 1050 TCU [0255] 1051 Communication module [0256] 1052 SIM [0257] 1060 Diagnostic port
* * * * *
References
D00000
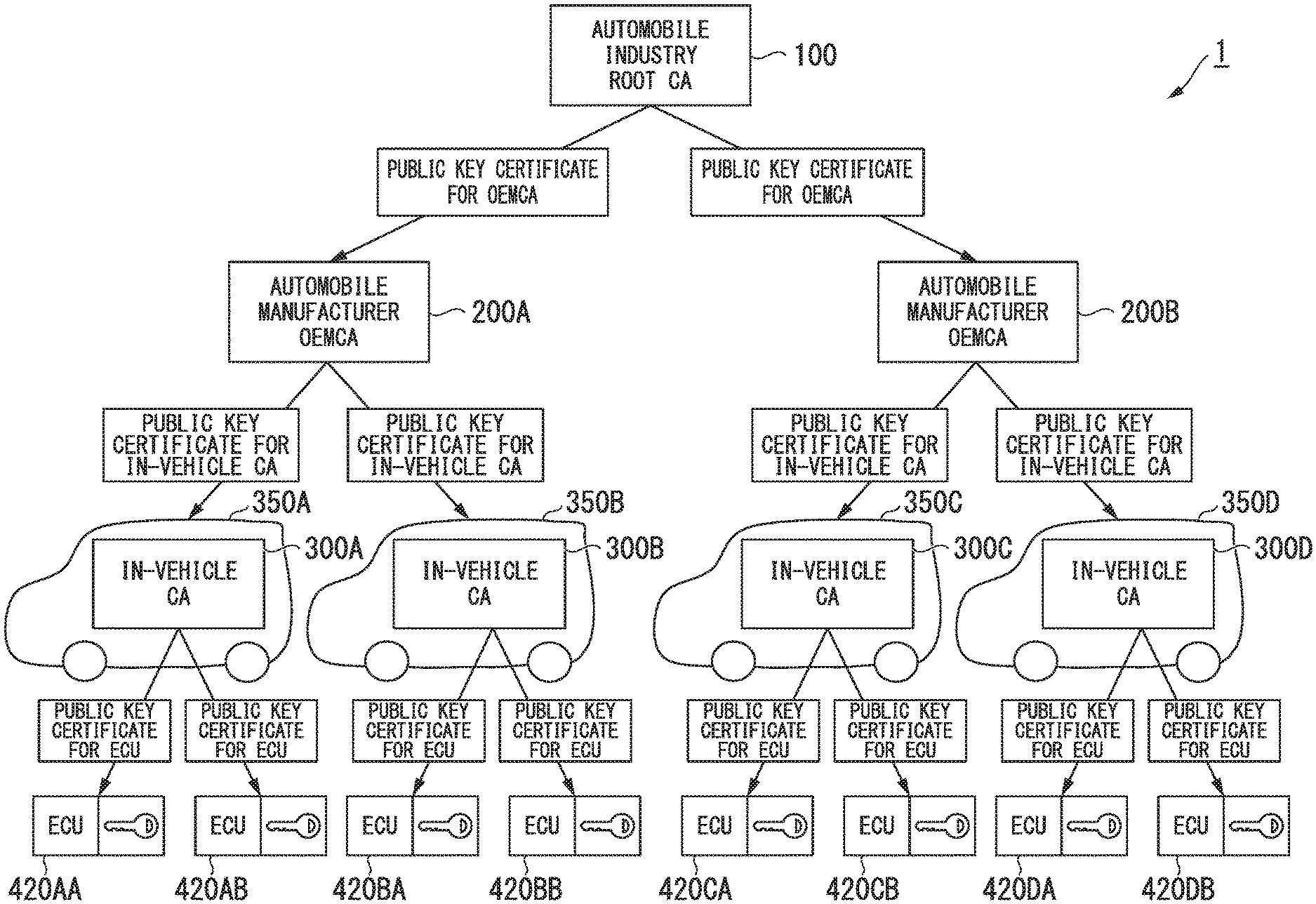
D00001
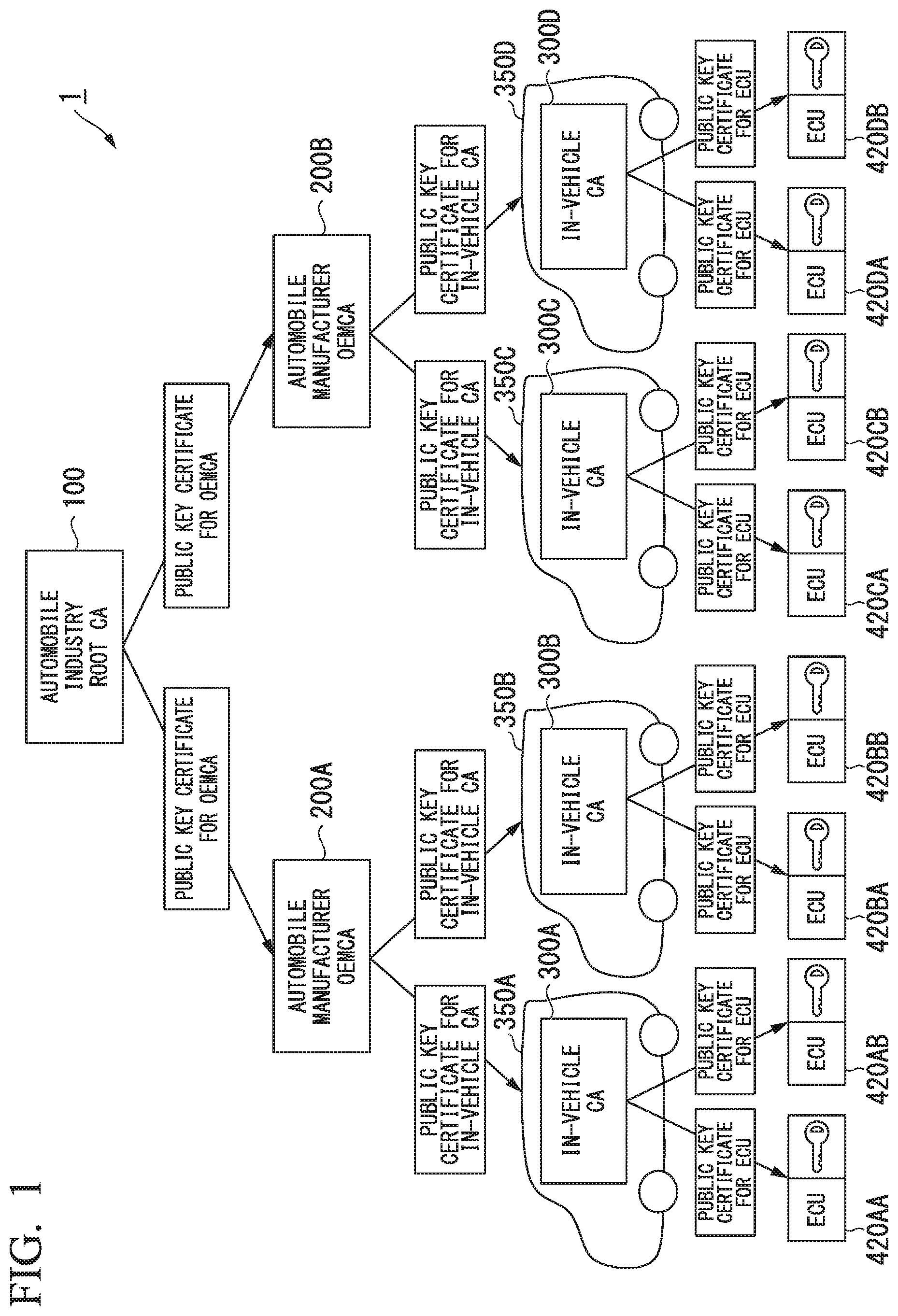
D00002
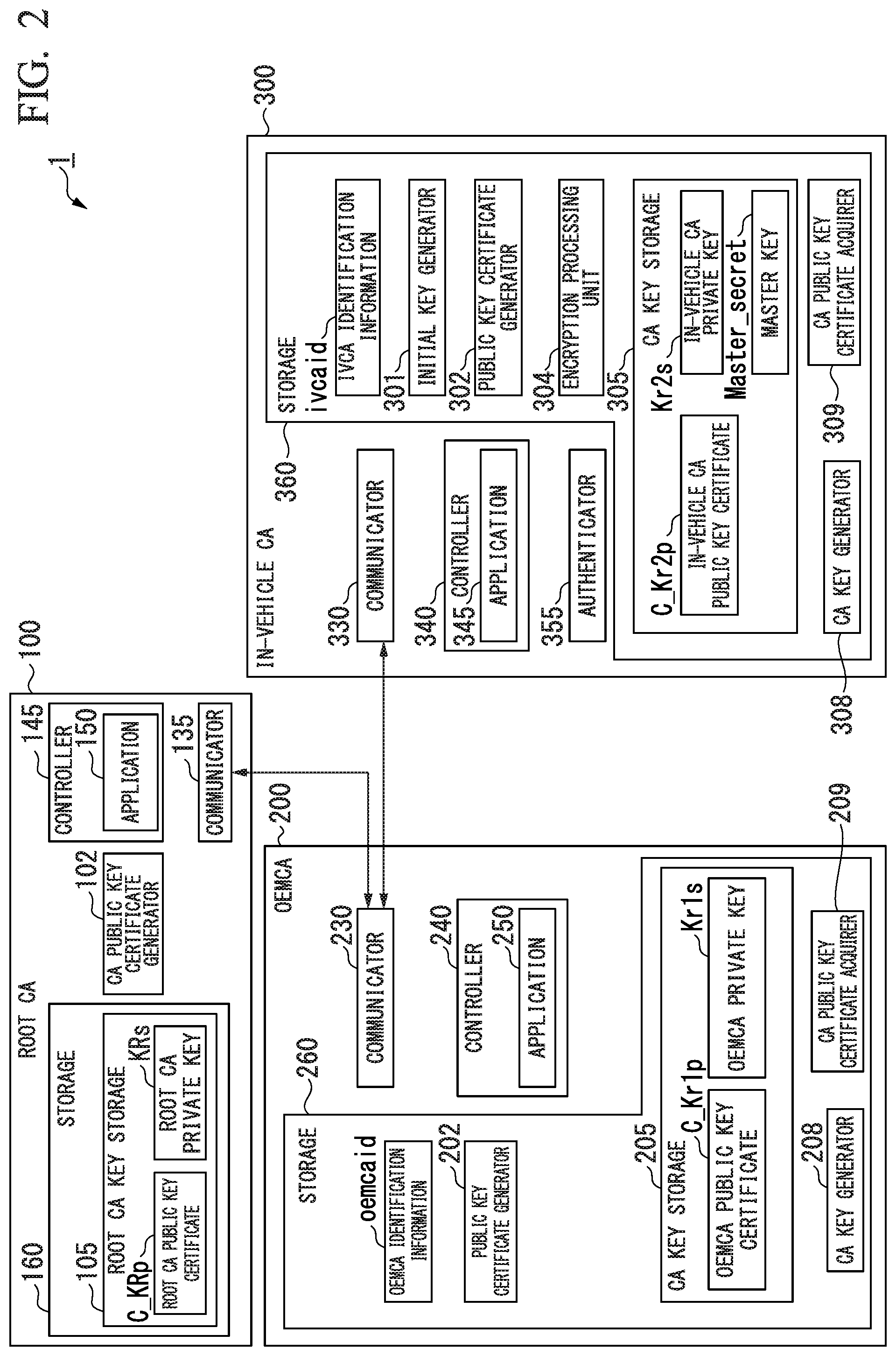
D00003
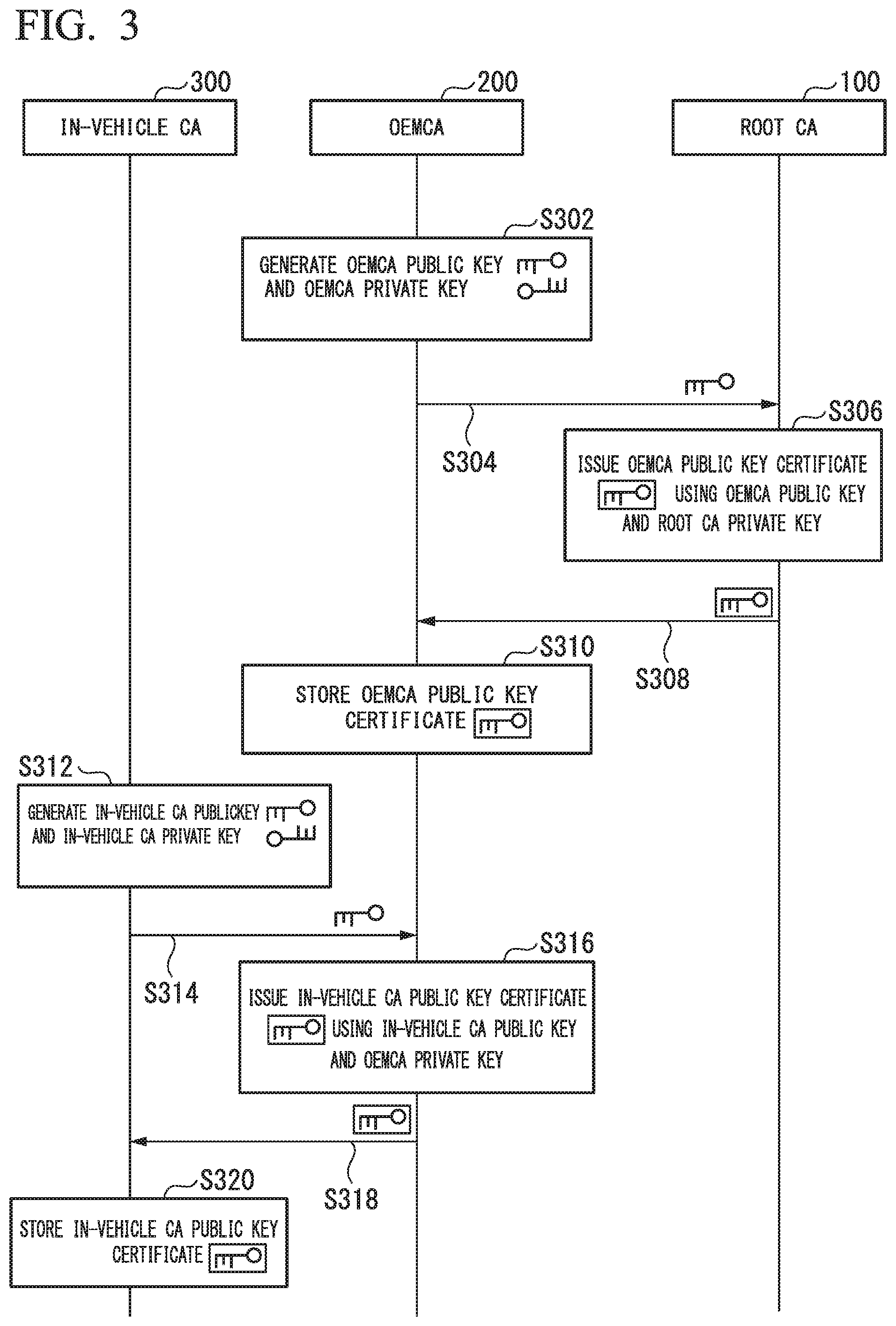
D00004
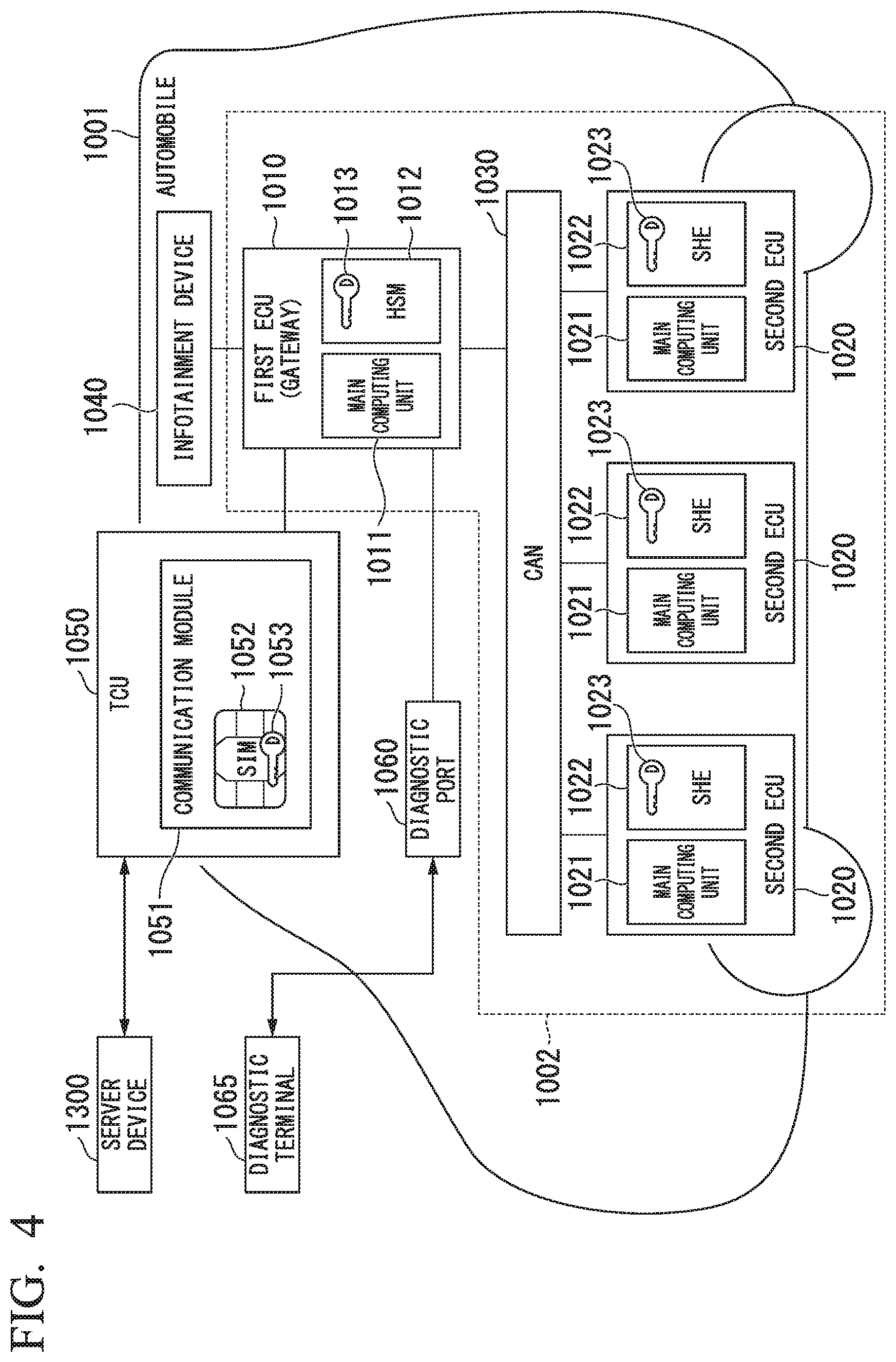
D00005
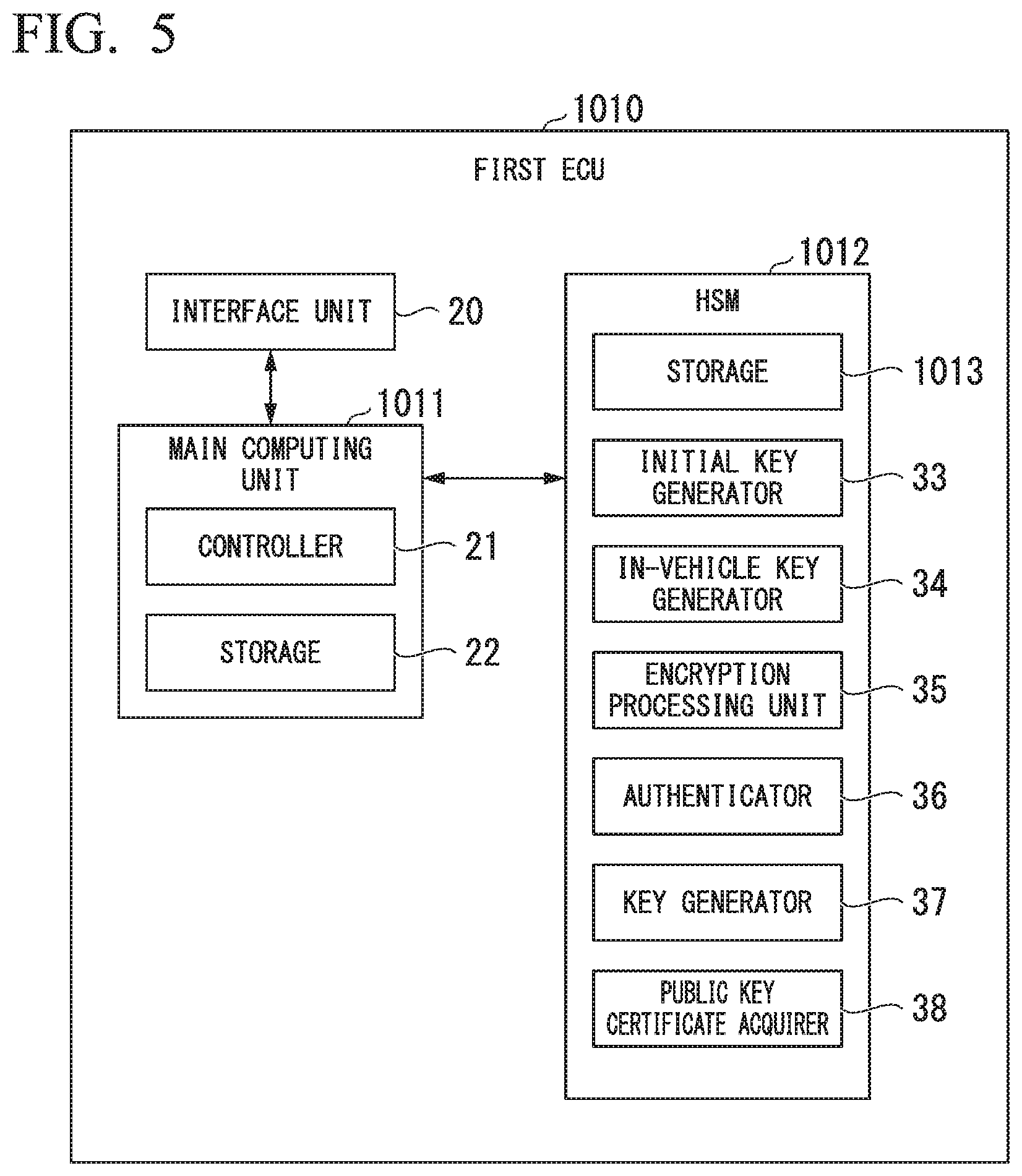
D00006
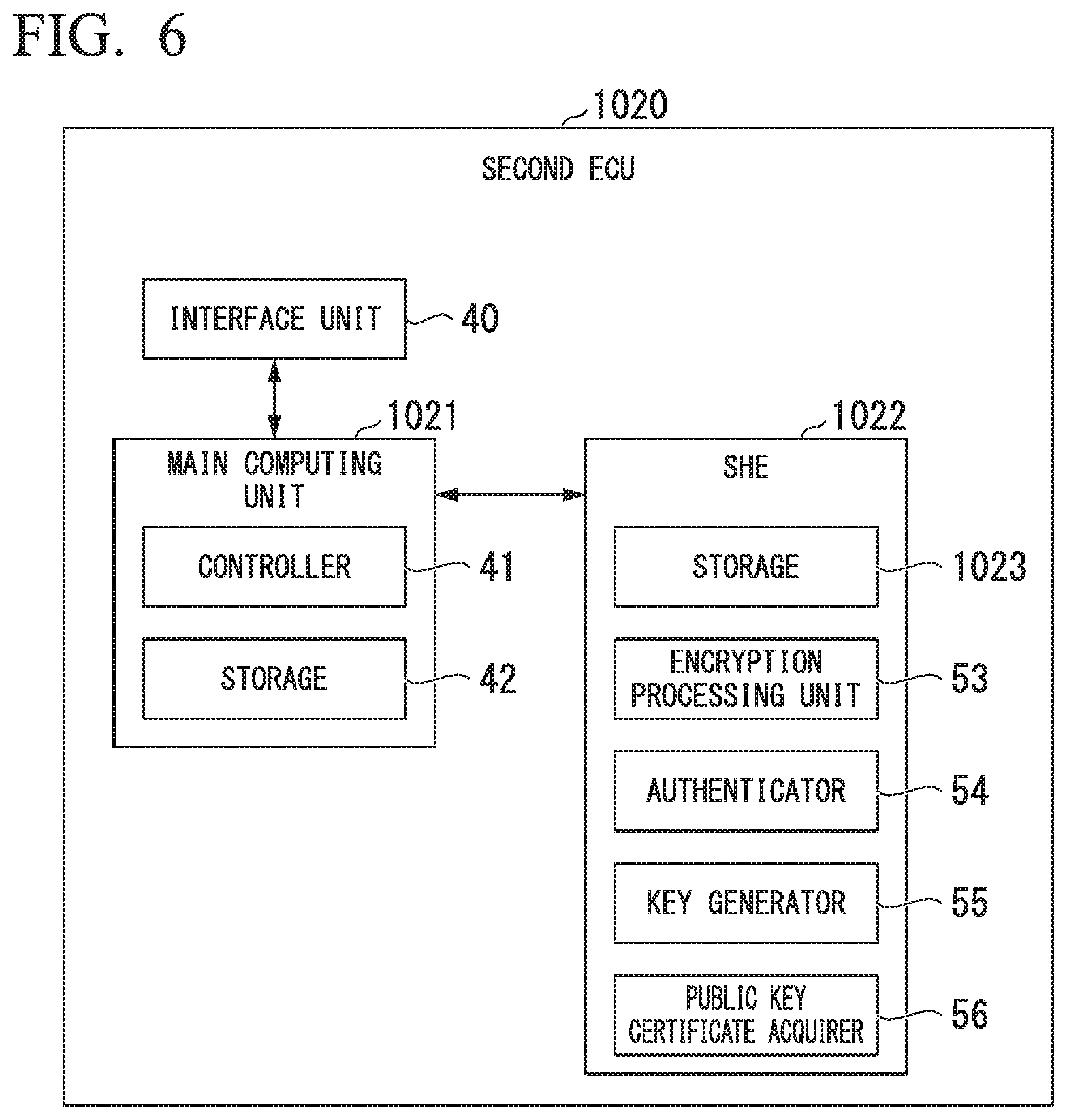
D00007
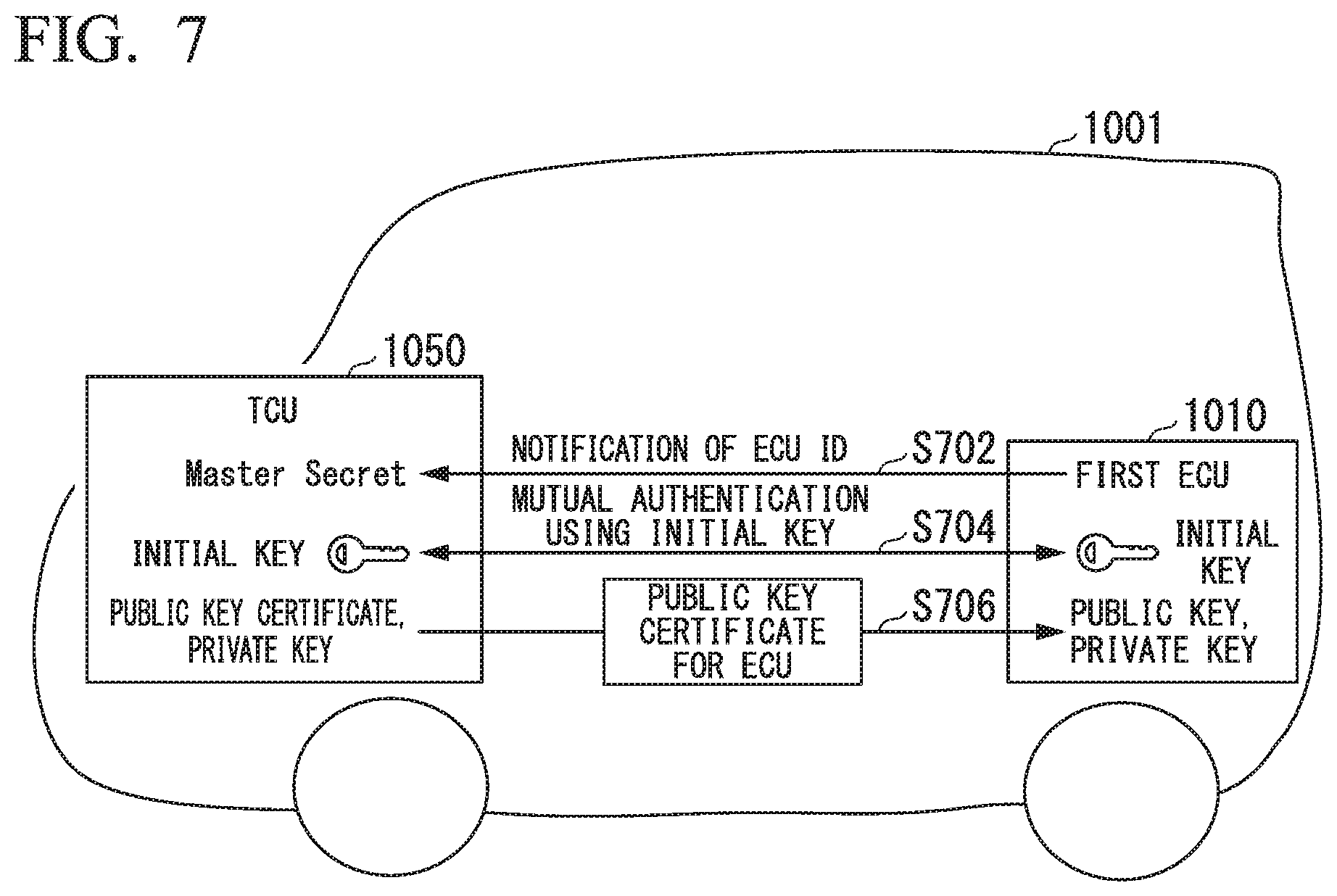
D00008
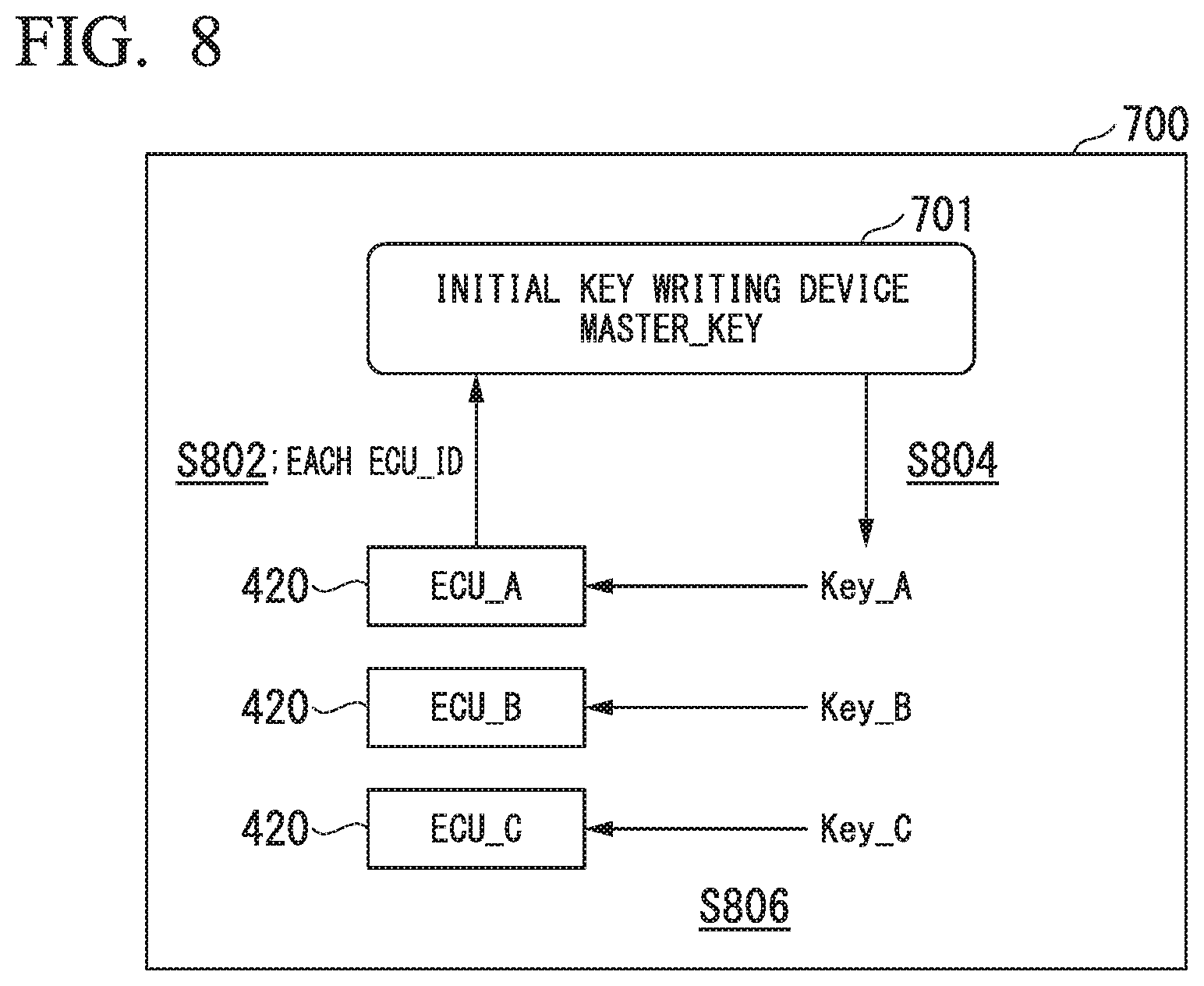
D00009
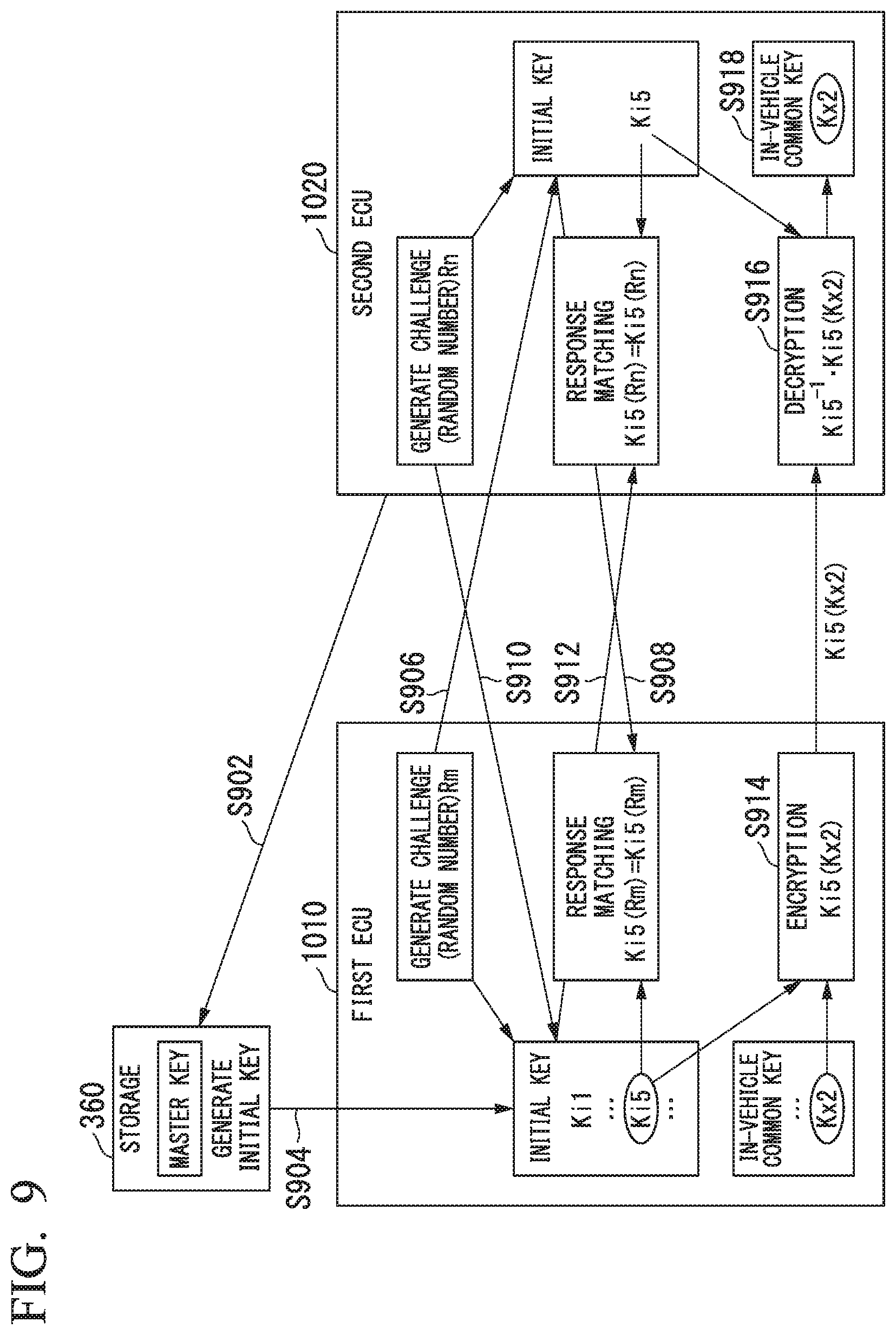
D00010
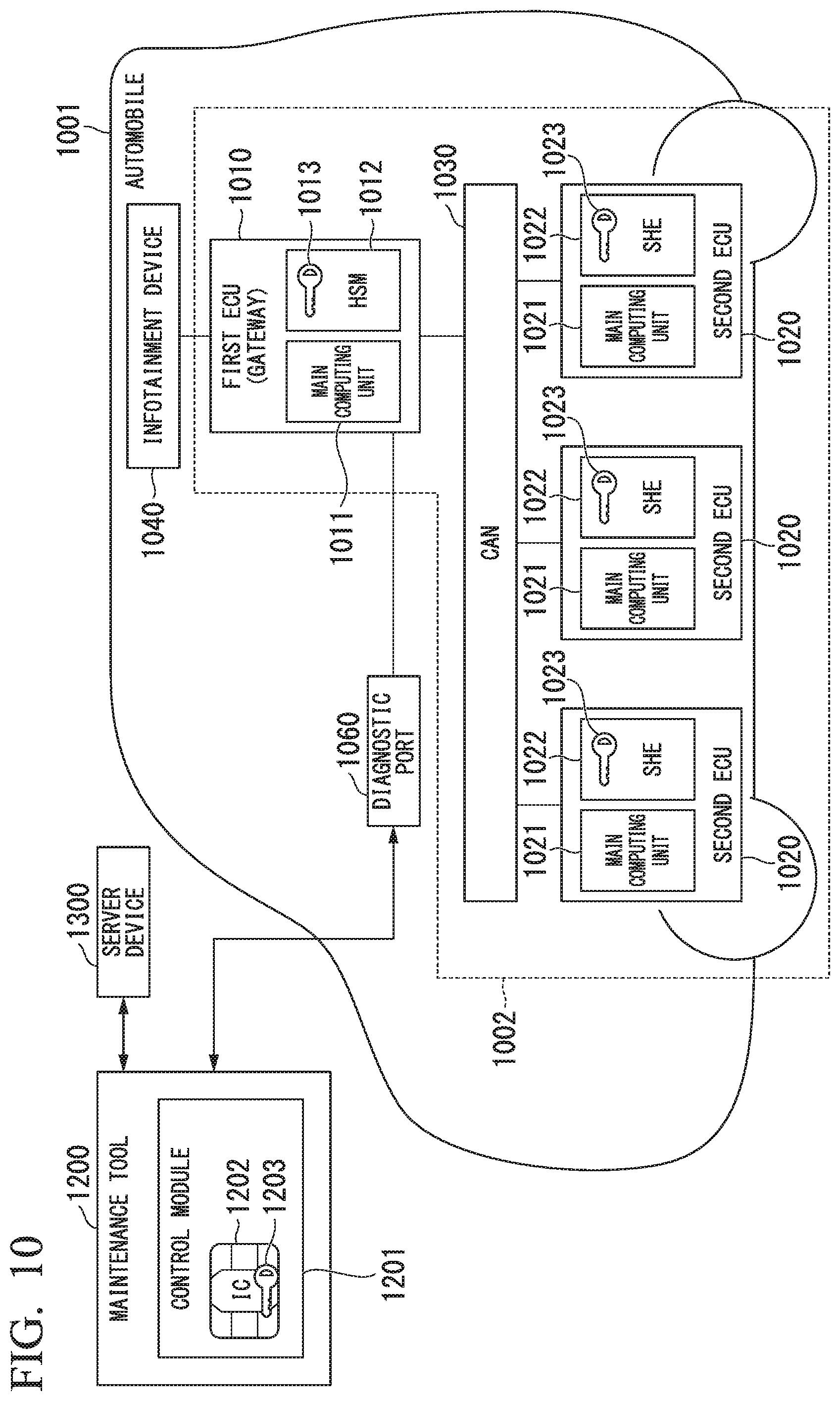
D00011
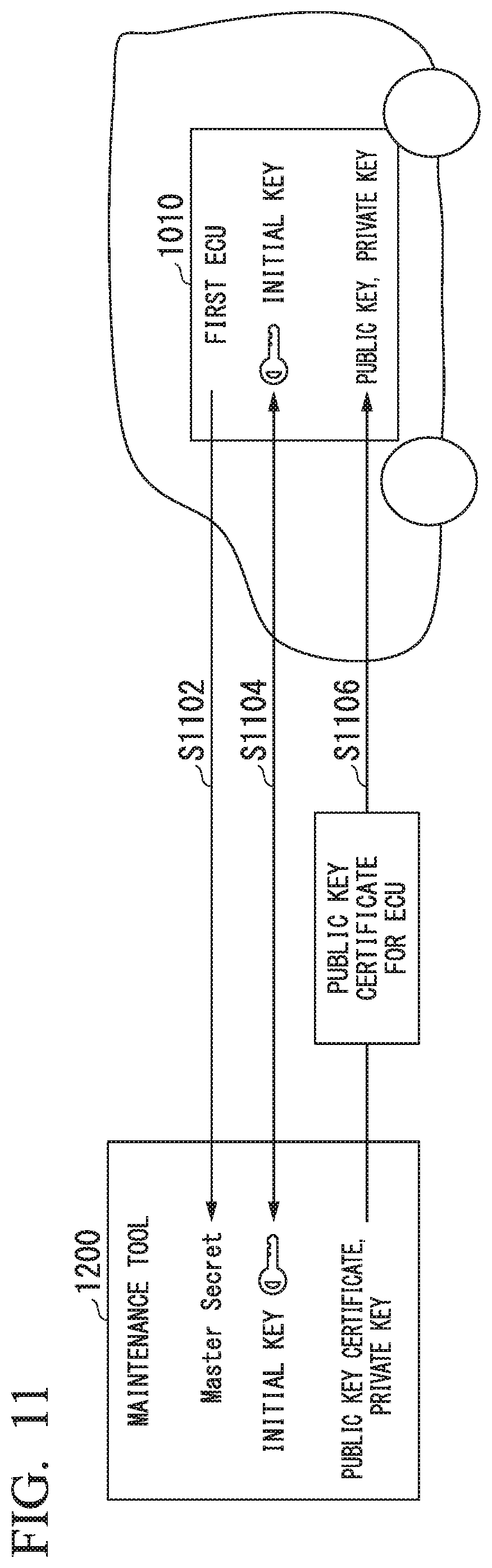
D00012
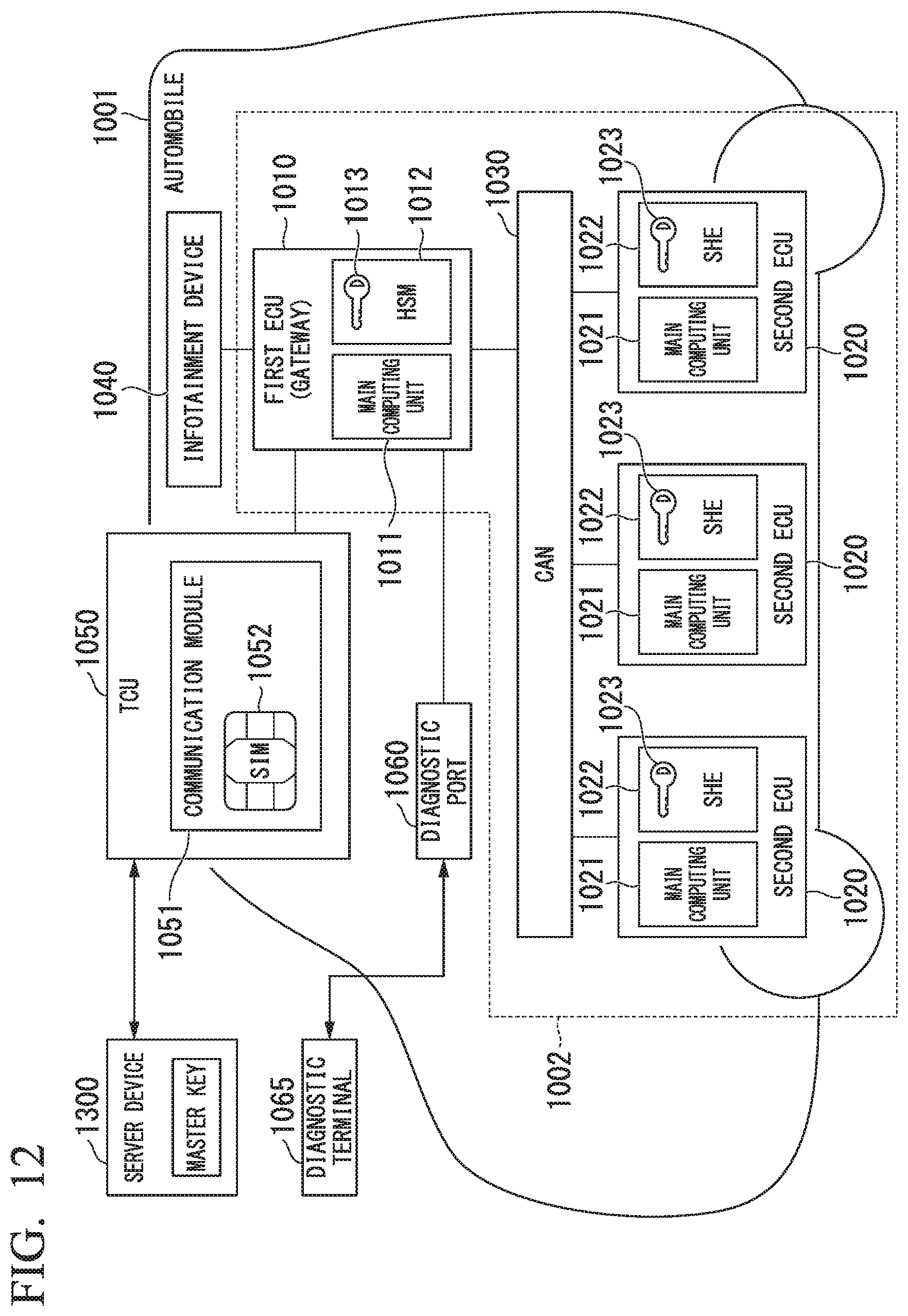
D00013
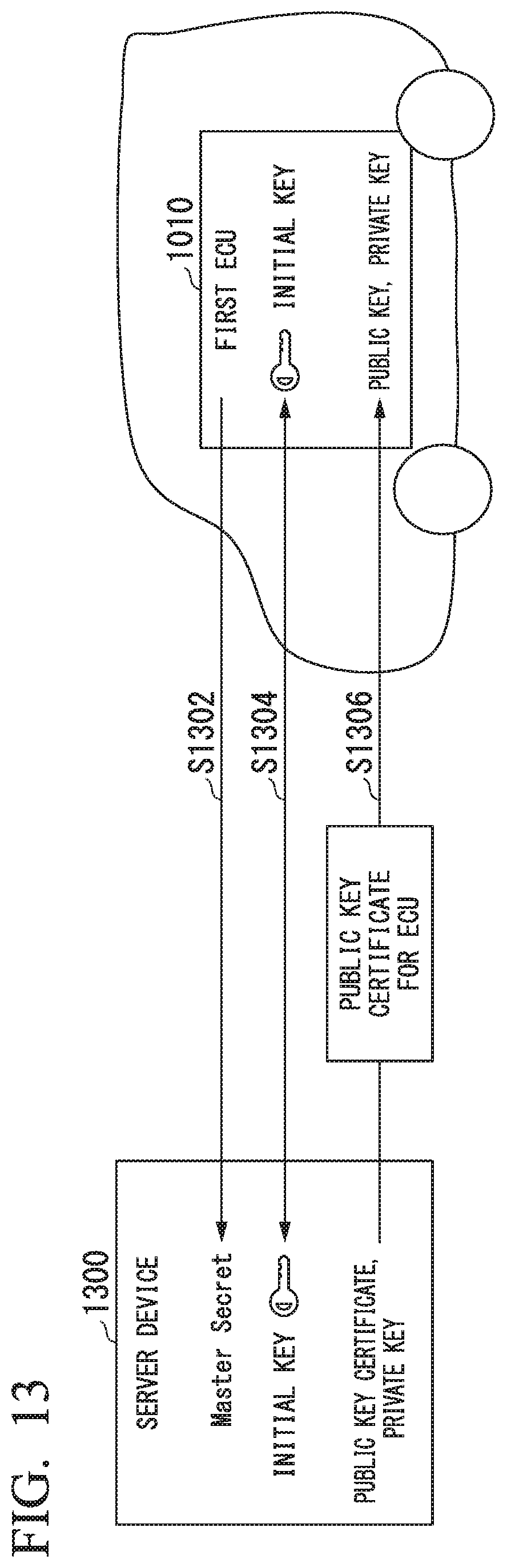
D00014
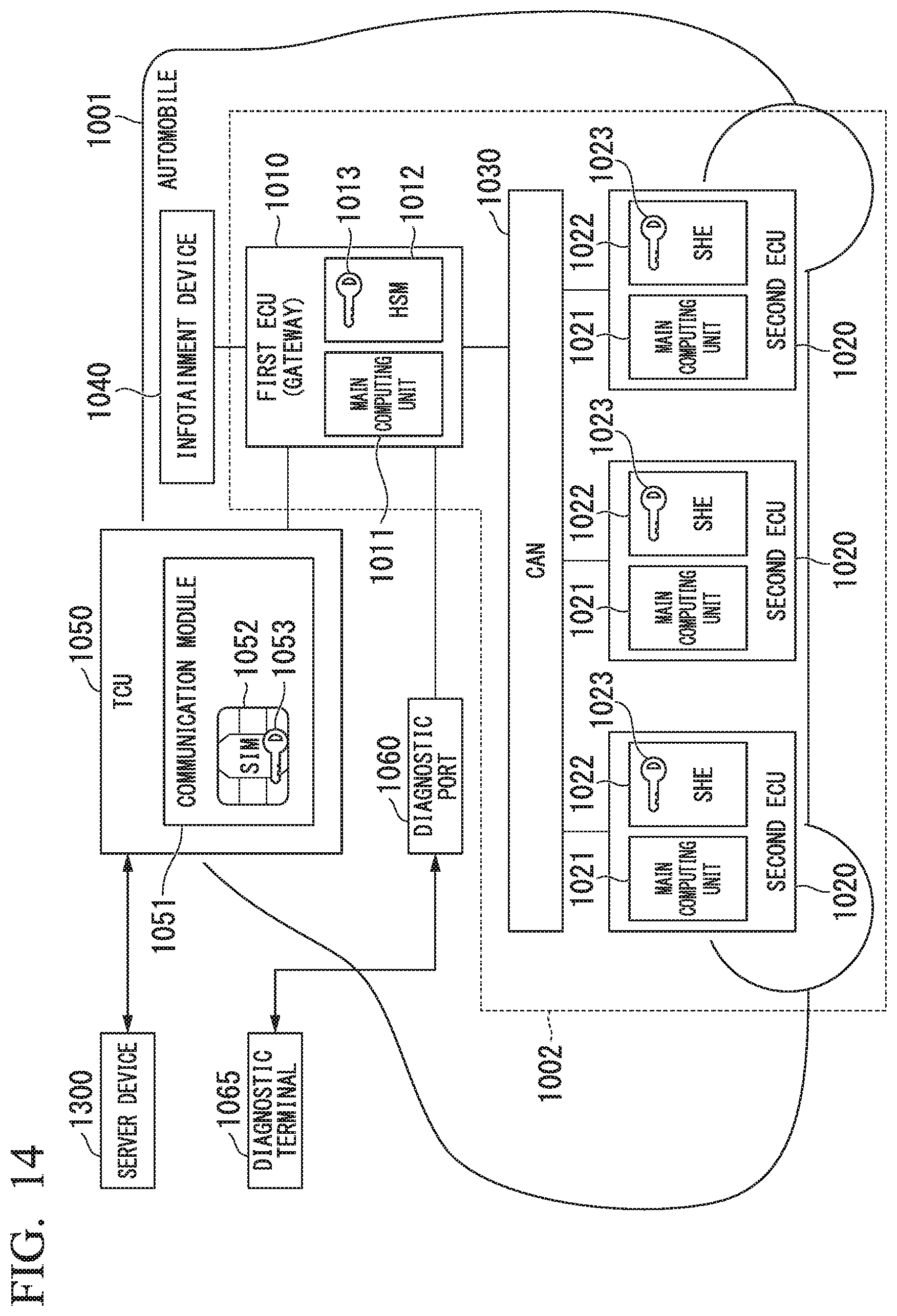
D00015

D00016
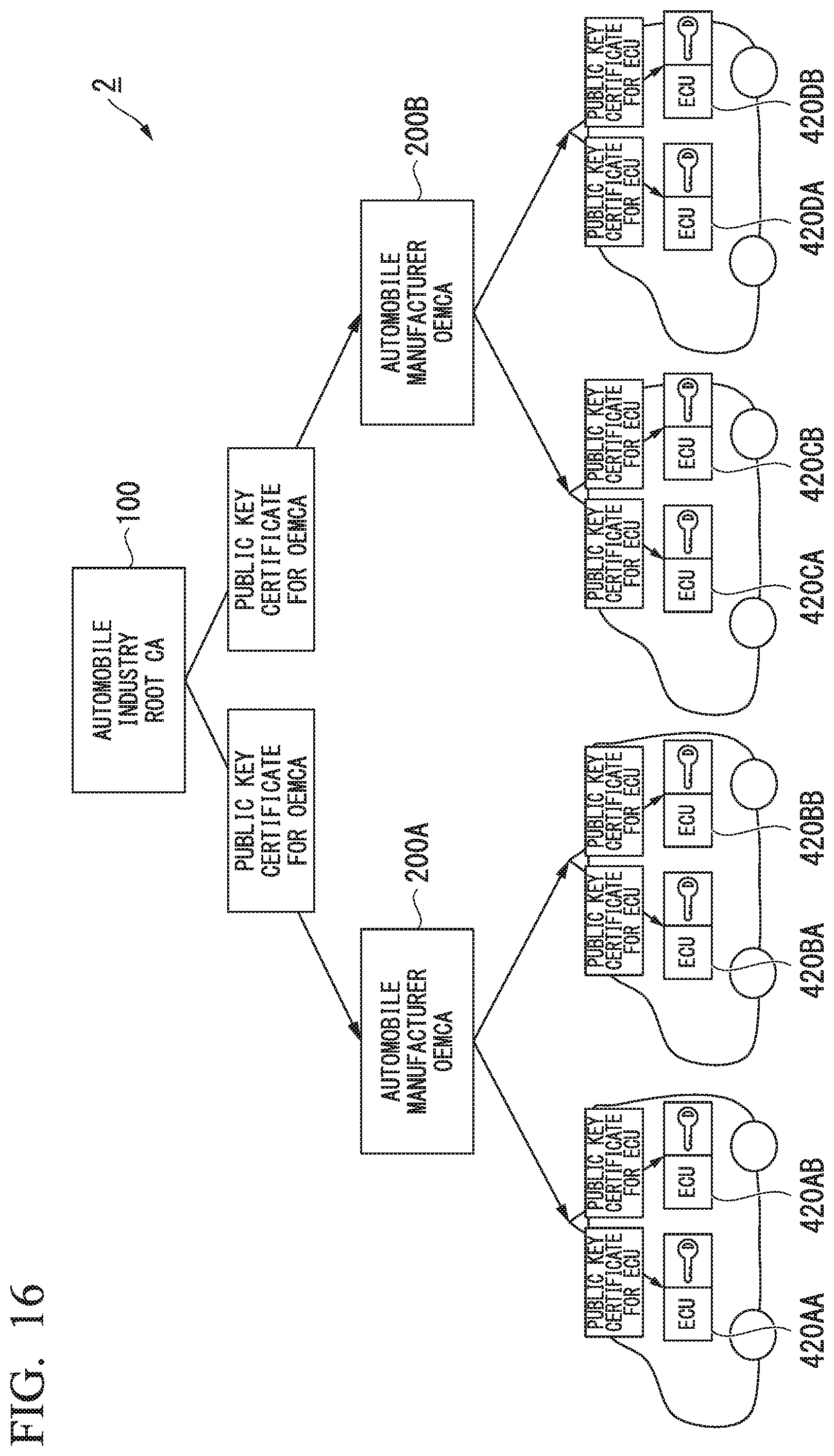
D00017
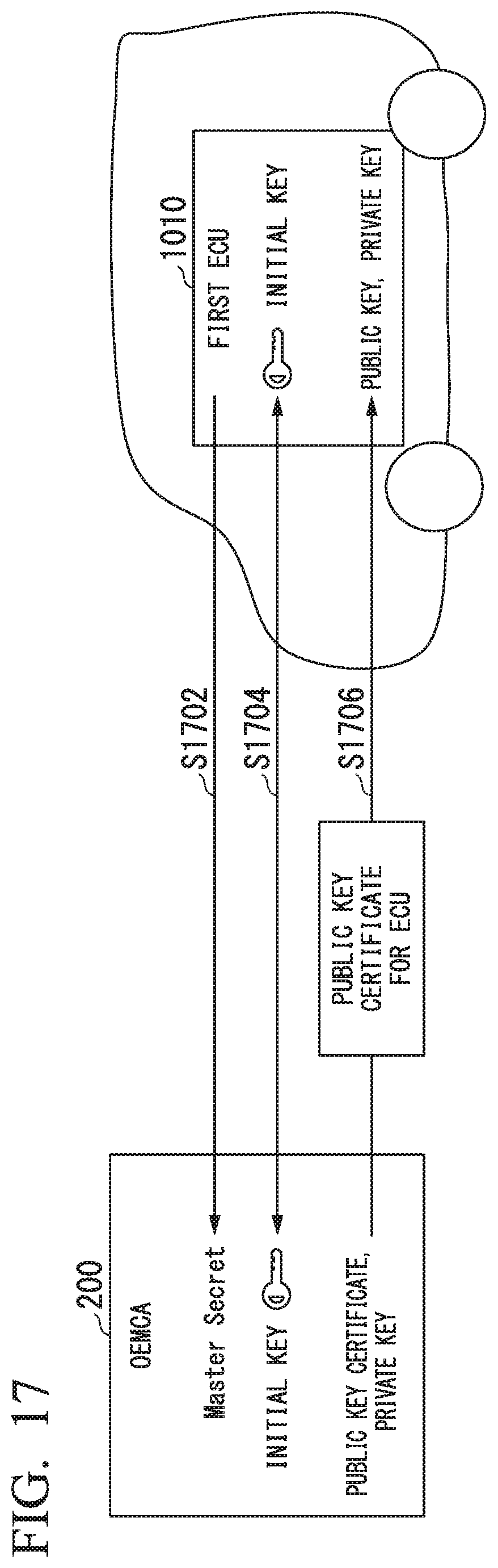
XML
uspto.report is an independent third-party trademark research tool that is not affiliated, endorsed, or sponsored by the United States Patent and Trademark Office (USPTO) or any other governmental organization. The information provided by uspto.report is based on publicly available data at the time of writing and is intended for informational purposes only.
While we strive to provide accurate and up-to-date information, we do not guarantee the accuracy, completeness, reliability, or suitability of the information displayed on this site. The use of this site is at your own risk. Any reliance you place on such information is therefore strictly at your own risk.
All official trademark data, including owner information, should be verified by visiting the official USPTO website at www.uspto.gov. This site is not intended to replace professional legal advice and should not be used as a substitute for consulting with a legal professional who is knowledgeable about trademark law.