Remote Operational Management Of E-sim
Finger; Joshua ; et al.
U.S. patent application number 16/742697 was filed with the patent office on 2020-05-28 for remote operational management of e-sim. The applicant listed for this patent is T-Mobile USA, Inc.. Invention is credited to Joshua Finger, Ming Shan Kwok, Gina Tran.
| Application Number | 20200169869 16/742697 |
| Document ID | / |
| Family ID | 69528427 |
| Filed Date | 2020-05-28 |

| United States Patent Application | 20200169869 |
| Kind Code | A1 |
| Finger; Joshua ; et al. | May 28, 2020 |
REMOTE OPERATIONAL MANAGEMENT OF E-SIM
Abstract
Techniques are described herein for remotely managing profiles corresponding to various mobile network operators offering telecommunication services to target user equipment based on one or more policies. The techniques include loading at least one profile on an embedded UICC (eUICC) of a user equipment, the one of profiles including a prioritized profile. The techniques also include receiving a request that includes an embedded UICC identifier (EID) and an integrated circuit card identifier (ICCID) corresponding to the eUICC of the user equipment, wherein the request is for locking one or more functionalities of the user equipment. One or more policies are retrieved for locking the one or more functionalities from a policy database. Based at least on the one or more policies, locking instructions are sent to the user equipment. The instructions include instructions to enable the prioritized profile.
| Inventors: | Finger; Joshua; (Covington, WA) ; Tran; Gina; (Seattle, WA) ; Kwok; Ming Shan; (Seattle, WA) | ||||||||||
| Applicant: |
|
||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|
| Family ID: | 69528427 | ||||||||||
| Appl. No.: | 16/742697 | ||||||||||
| Filed: | January 14, 2020 |
Related U.S. Patent Documents
| Application Number | Filing Date | Patent Number | ||
|---|---|---|---|---|
| 16201175 | Nov 27, 2018 | 10567952 | ||
| 16742697 | ||||
| Current U.S. Class: | 1/1 |
| Current CPC Class: | H04L 9/006 20130101; H04W 8/205 20130101; H04W 12/0023 20190101; H04W 12/0609 20190101; H04L 9/0825 20130101; H04L 2209/80 20130101; H04W 8/183 20130101 |
| International Class: | H04W 8/18 20060101 H04W008/18; H04L 9/08 20060101 H04L009/08; H04W 12/06 20060101 H04W012/06 |
Claims
1. A computer-implemented method, comprising: loading at least one profile on an embedded UICC (eUICC) of a unique user equipment, one of the at least one profile comprising a prioritized profile; receiving a request comprising an embedded UICC identifier (EID) and an integrated circuit card identifier (ICCID) corresponding to the eUICC of the user equipment, the request for locking one or more functionalities of the user equipment; retrieving from a policy database, the policy database storing one or more policies for locking the one or more functionalities of the user equipment; determining, based at least on the one or more policies, whether to lock the one or more functionalities; and transmitting locking instructions to the user equipment in response to deciding to lock the one or more functionalities, the instructions comprising enabling the prioritized profile.
2. The computer-implemented method of claim 1, further comprising the steps of: validating the EID and the ICCID against a register of device identifiers.
3. The computer-implemented method of claim 1, wherein the prioritized profile is managed by a mobile network operator (MNO).
4. The computer-implemented method of claim 1, further comprising the steps of: receiving an additional request for deleting the prioritized profile in the eUICC; determining, based at least on the one or more policies, whether to delete the prioritized profile; and transmitting instructions to the user equipment to delete the prioritized profile in response to deciding to delete the prioritized profile.
5. The computer-implemented method of claim 4, wherein the determining comprises reviewing eligibility criteria in the one or more policies, the eligibility criteria based on a rate plan and account status associated with a customer account corresponding to the user equipment.
6. The computer-implemented method of claim 4, further comprising the steps of: receiving a new request for adding a new profile in the eUICC; determining whether the new profile has been loaded and available in a subscription manager in communication with the user equipment; and transmitting an error message to the user equipment in response to determining that the requested profile has not been loaded and available in the subscription manager.
7. The computer-implemented method of claim 1, wherein the determining comprises identifying delinquency in payment for a customer account corresponding to the user equipment.
8. A system, comprising: one or more nontransitory storage mediums configured to provide stored code segments, the one or more nontransitory storage mediums coupled to one or more processors, each configured to execute the code segments and causing the one or more processors to: load at least one profile on an embedded UICC (eUICC) of a unique user equipment, one of the at least one profile comprising a prioritized profile; receive a request comprising an embedded UICC identifier (EID) and an integrated circuit card identifier (ICCID) corresponding to the eUICC of the user equipment, the request for locking one or more functionalities of the user equipment; retrieve from a policy database, the policy database storing one or more policies for locking the one or more functionalities of the user equipment; determine, based at least on the one or more policies, whether to lock the one or more functionalities; and transmit locking instructions to the user equipment in response to deciding to lock the one or more functionalities, the instructions comprising enabling the prioritized profile.
9. The system of claim 8, wherein the one or more processor is further configured to: receive an additional request to replace the prioritized profile loaded on the eUICC with a new profile; determine, based at least on the one or more policies, whether to unlock the one or more functionalities; and in response to unlocking the one or more functionalities, serve the eUICC with a new profile.
10. The system of claim 9, wherein the one or more processor is further configured to: determine whether the new profile has been loaded and is available in a subscription manager in communication with the user equipment in response to deciding to unlock the one or more functionalities.
11. The system of claim 9, wherein the one or more processor is further configured to: transmitting instructions to the user equipment to replace the prioritized profile in response to deciding to unlock the one or more functionalities.
12. The system of claim 8, wherein the eUICC is stored in a data store, the data store comprising a home subscriber server (HSS) of a telecommunications network or a home location register (HLR) of the telecommunications network.
13. The system of claim 8, wherein the one or more processor is further configured to add, delete, and edit the one or more policies.
14. The system of claim 8, wherein the one or more functionalities are associated with the prioritized profile.
15. One or more nontransitory computer-readable media storing computer-executable instructions that upon execution cause one or more processors to perform acts comprising: loading at least one profile on an embedded UICC (eUICC) of a unique user equipment, one of the at least one profile comprising a prioritized profile; receiving a request comprising an embedded UICC identifier (EID) and an integrated circuit card identifier (ICCID) corresponding to the eUICC of the user equipment, the request for locking one or more functionalities of the user equipment; retrieving from a policy database, the policy database storing one or more policies for locking the one or more functionalities of the user equipment; determining, based at least on the one or more policies, whether to lock the one or more functionalities; and transmitting locking instructions to the user equipment in response to deciding to lock the one or more functionalities, the instructions comprising enabling the prioritized profile
16. The one or more nontransitory computer-readable media of claim 15, wherein the request includes credentials in accordance with a public key infrastructure (PKI)-based authentication protocol.
17. The one or more nontransitory computer-readable media of claim 15, wherein the request utilizes an identifier correlating with an account that is associated with a plurality of user equipment and a plurality of users.
18. The one or more nontransitory computer-readable media of claim 17, wherein the determining is based on a rate plan and account status associated with the account.
19. The one or more nontransitory computer-readable media of claim 15, wherein the one or more nontransitory computer-readable media includes a firewall.
20. The one or more nontransitory computer-readable media of claim 15, wherein the one or more nontransitory computer-readable media comprises an on-premise server.
Description
CROSS-REFERENCE TO RELATED APPLICATIONS
[0001] This application is a divisional of U.S. patent application Ser. No. 16/201,175, filed Nov. 27, 2018, and entitled "ESIM SUBSIDY AND OPERATIONAL MANAGEMENT," which is incorporated herein by reference in its entirety.
BACKGROUND
[0002] Subscriber identity module (SIM) cards enable a telecommunication service subscriber to be identified on a corresponding service provider's network by storing a unique international mobile subscriber identifier (IMSI) that can be retrieved and subsequently authenticated over-the-air by a corresponding service provider each time a user equipment engages in communications (e.g., mobile voice calling, texting, data service) with its telecommunication service provider or mobile network operator (MNO). A SIM IMSI generally includes a mobile country code (MCC), a mobile network code (MNC), and a mobile subscriber identification number (MSIN). This information allows a user's provider-issued SIM card to be identified, registered, and authenticated with an issuing MNO.
[0003] The SIM circuit is a part of the function of a universal integrated circuit card (UICC), which can be physically inserted into the SIM socket of a user equipment. Because SIM cards are static and include IMSI data that cannot be modified after issuance, a customer may be issued a different SIM card each time the customer purchases a new user equipment and/or a new service plan offering from an MNO. Upon issuance of the new SIM card, the old SIM card is removed and the new SIM card is inserted into the SIM socket of the user equipment.
[0004] In contrast, remote management of embedded UICC (eUICC) or embedded SIM (eSIM) is distinguished from physical UICC or SIM in that eUICC allows an MNO to respond to requests to change subscription from one MNO to another MNO without having physical access to the eUICC in a user equipment or terminal. Generally, eUICCs can handle multiple profiles from multiple MNOs, but only one profile can be enabled at any time in operation.
[0005] Mechanisms for over-the-air remote provisioning and management of eUICC in user equipment entail downloading new profiles, updating subscription addresses, and enabling, disabling, or deleting profiles as defined in the GMSA Remote Provisioning Architecture for eUICC Technical Specification. Particularly, subscription managers (SMs) can generate and manage a profile on a eUICC. Additionally, an SM can manage service plans or subscription change. Each SM comprises one or more profiles and a subscription manager secure routing (SM-SR) can ensure the secure transport of both eUICC platform and eUICC profile management commands in order to load, enable, disable, and delete profiles on the eUICC. Subscription managers can further comprise a subscription manager data preparation (SM-DP) or subscription manager data preparation (enhanced) (SM-DP+) for securing packaging profiles to be provisioned on the eUICC. The SM-DP or SM-DP+ manages the installation of these profiles on the eUICC.
[0006] While remote provisioning and management of eUICC enable original equipment manufacturers (OEMs) to market user equipment with straightforward connectivity experience, offering a freedom of choice of mobile subscriptions can frustrate business and marketing objectives for MNOs because SMs may not account for the MNOs' eligibility criteria for loading, enabling, disabling, or deleting profiles. For instance, MNOs may desire to discourage customers to deviate from expected service usage within a lifecycle of cellular subscriptions by acquiring unaffiliated, generic/unlocked equipment to avoid purchasing services and products from an MNO. In order to better manage client privilege and increase accountability of end user contracts by allowing MNOs to oversee SMs' management of service plans or subscription change, a validated prioritized profile that is owned by an MNO should be loaded on a targeted user equipment and/or eUICC, and eligibility criteria for modifying, deleting, adding, or replacing the profile as set forth by an MNO and/or an SM must be determined.
BRIEF DESCRIPTION OF THE DRAWINGS
[0007] The detailed description is described with reference to the accompanying figures, in which the leftmost digit(s) of a reference number identifies the figure in which the reference number first appears. The use of the same reference numbers in different figures indicates similar or identical items.
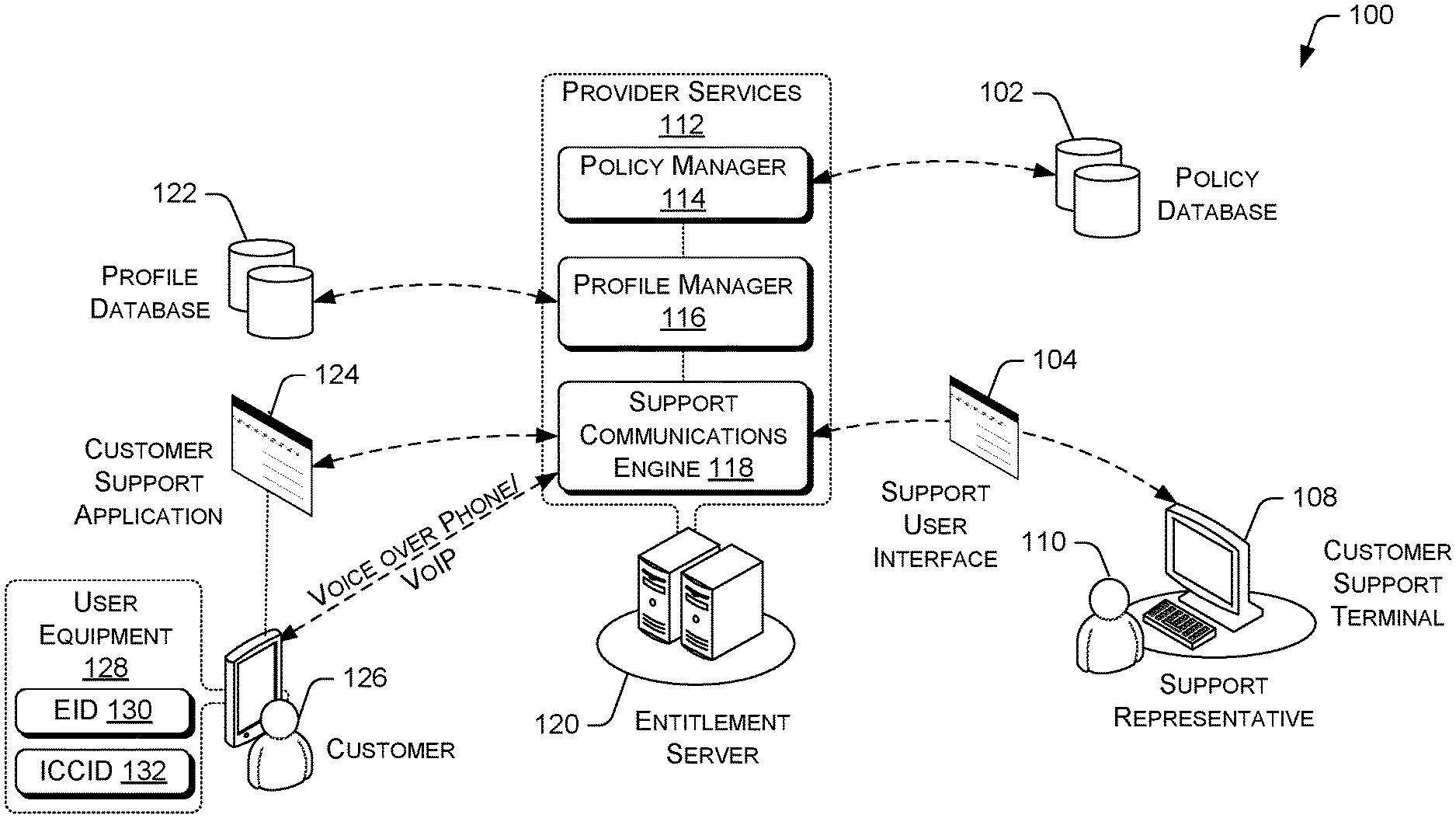
[0008] FIG. 1 illustrates example network architecture for managing subscription profiles within a eUICC for connectivity to one or more MNOs.
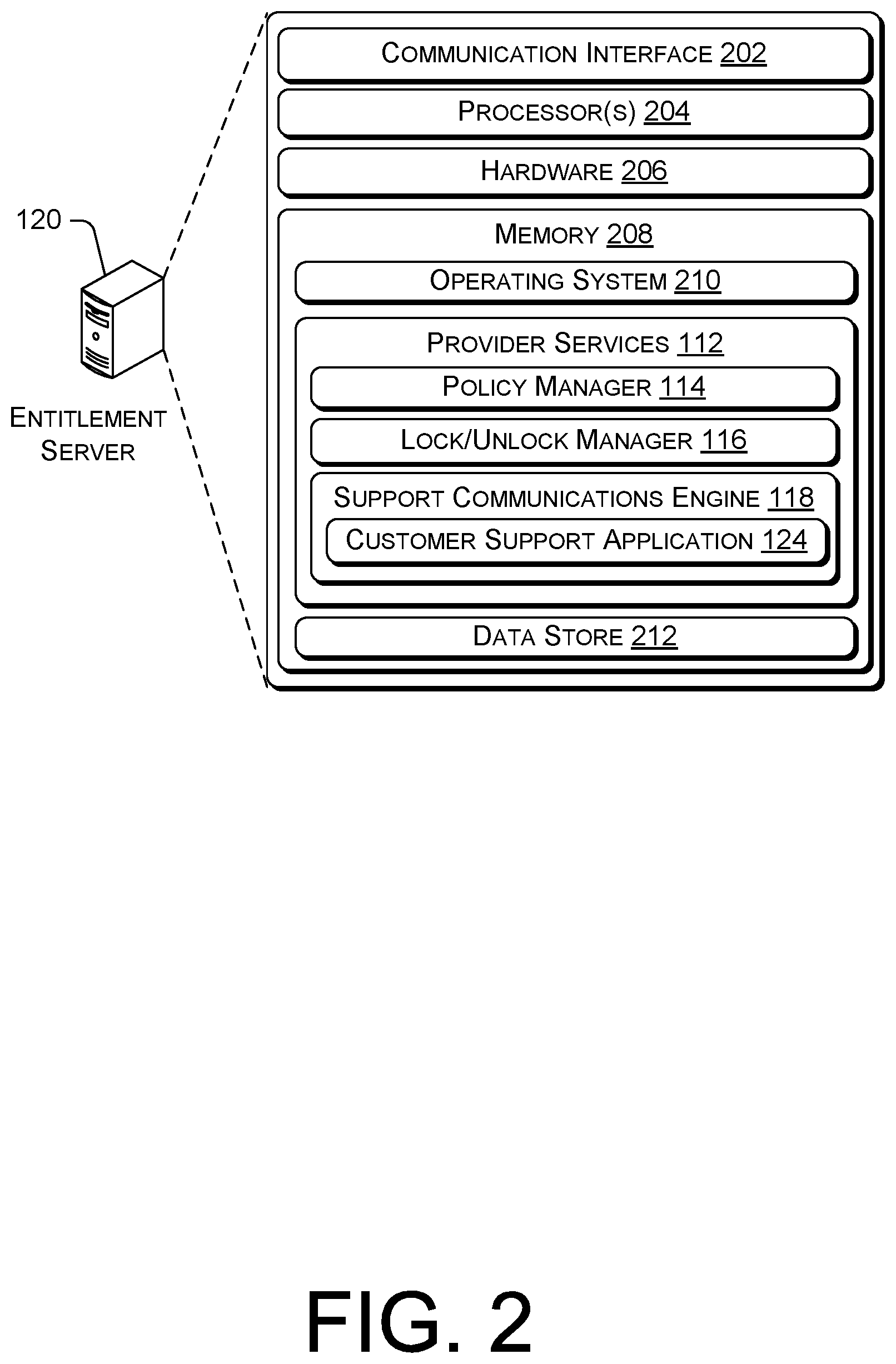
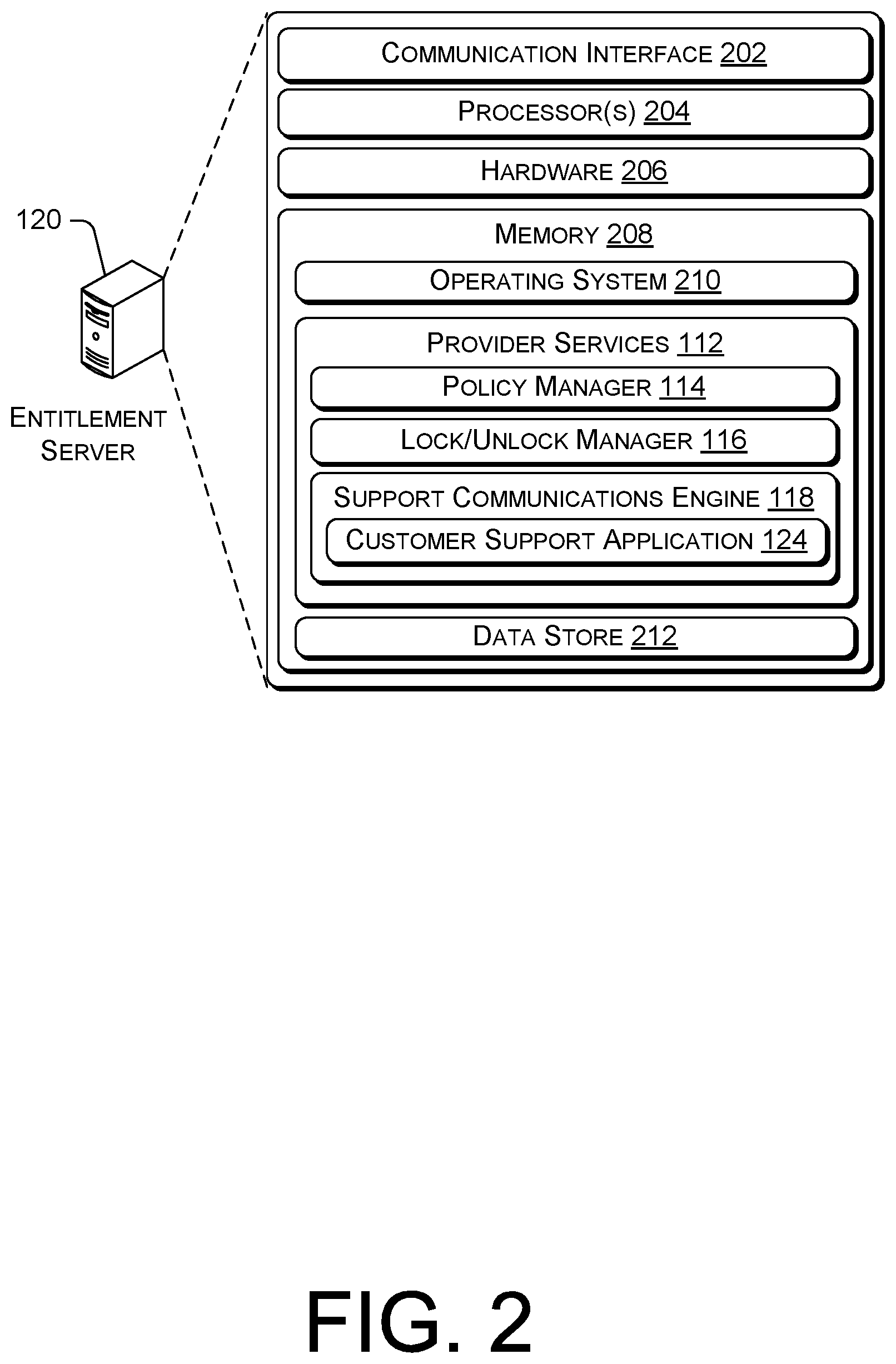
[0009] FIG. 2 is a block diagram showing various components of an illustrative computing device that implements provider services of an MNO.
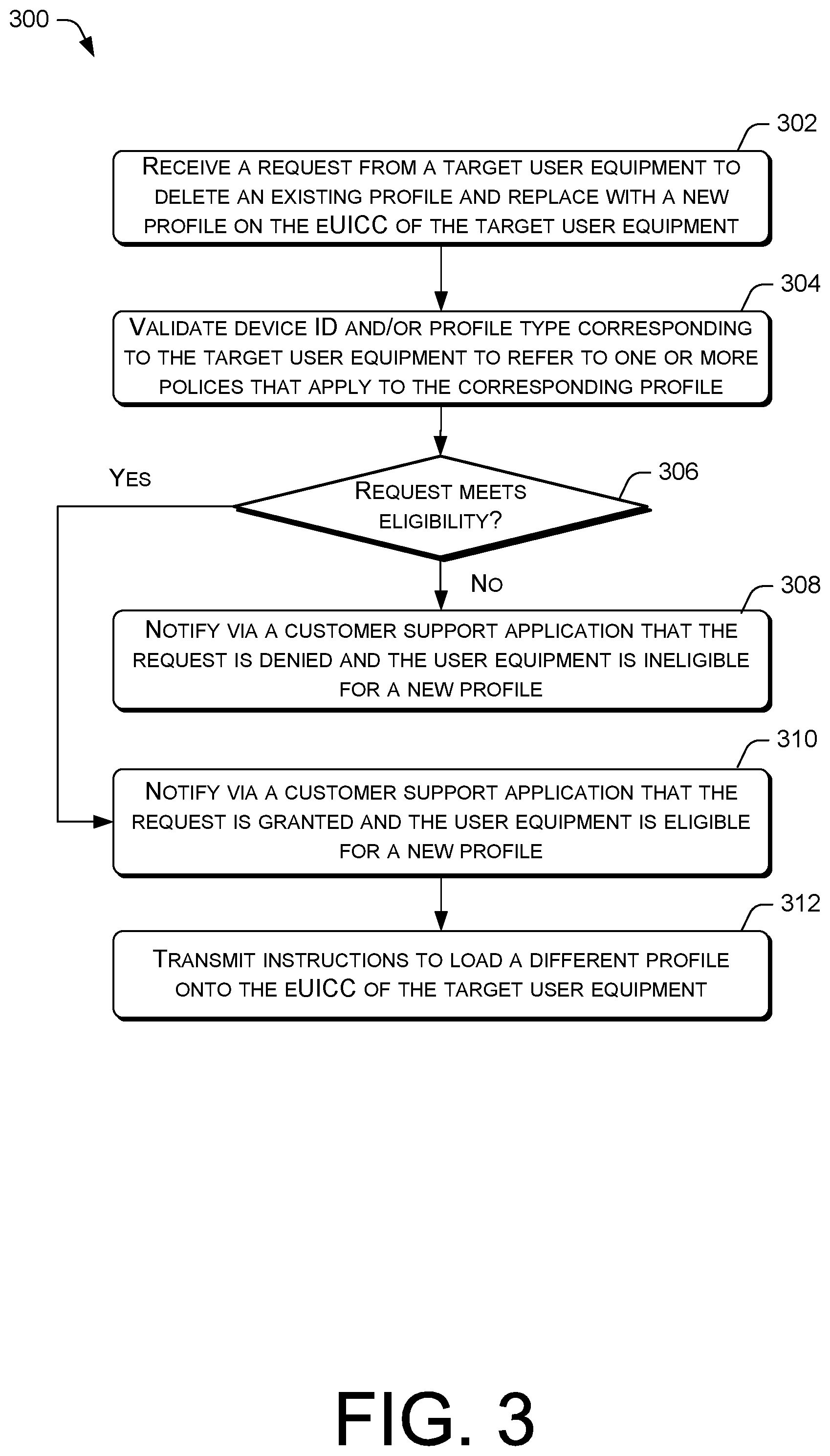
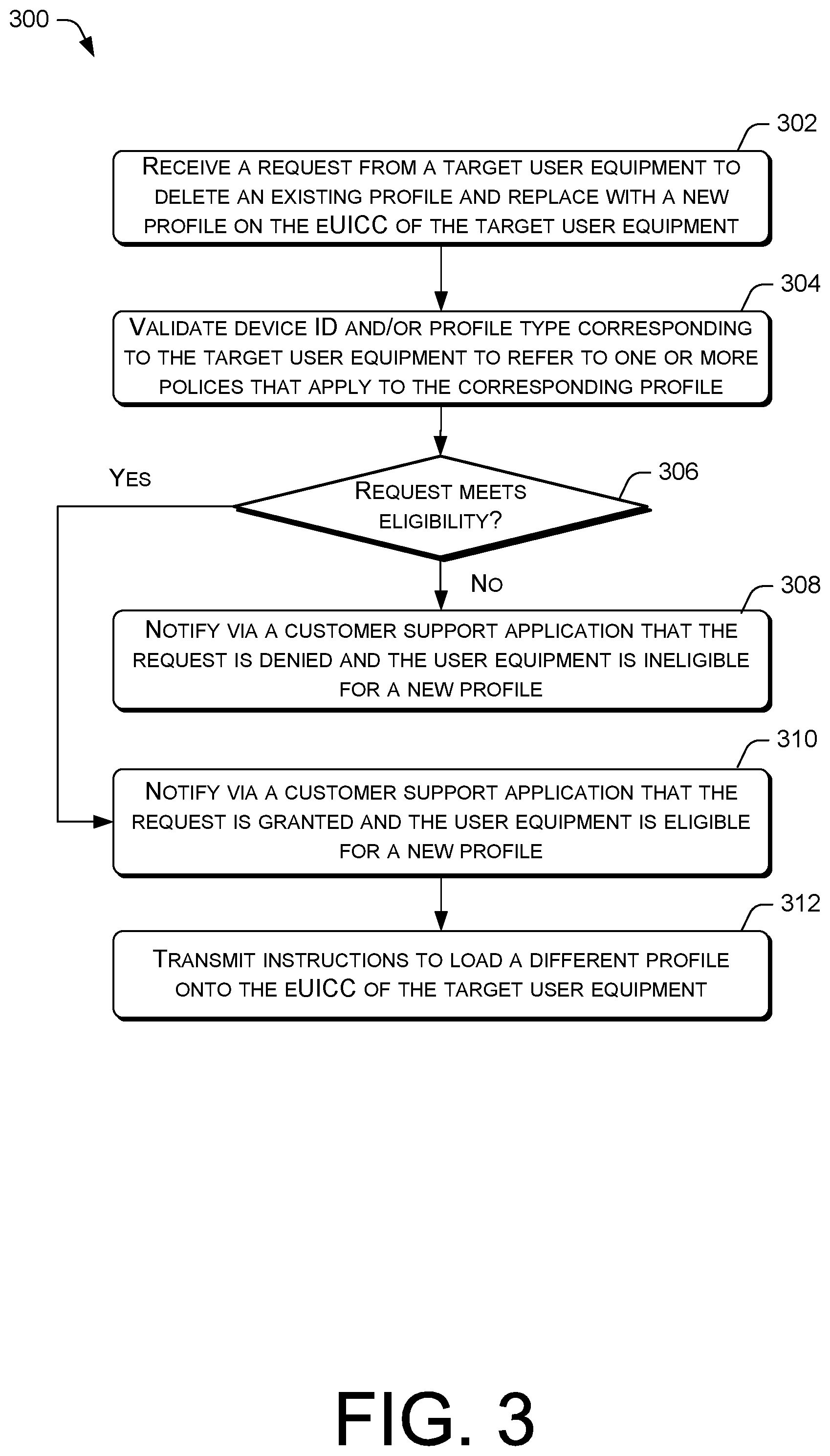
[0010] FIG. 3 is a flow diagram of an example process for determining eligibility for loading a new profile to a eUICC to manage the functionality of user equipment corresponding to the eUICC.
DETAILED DESCRIPTION
[0011] This disclosure is directed to techniques for determining eligibility for receiving and loading new profiles on a target user equipment and/or eUICC in a machine-to-machine (M2M) environment or a consumer device environment. In various embodiments, a customer's user equipment can have profiles loaded from eUICC manufacturers (EUMs), the profiles corresponding to data preparation (DP), enhanced DP (DP+), and/or secure routing (SR) in the SM, wherein at least one of the profiles comprises a prioritized profile owned by an MNO for connectivity to the MNO. The prioritized profile is a preferred profile that can be loaded onto the eUICC before other profiles that may also reside on the user equipment. The prioritized profile can be prepared during end-user contract finalization, depending upon embodiments. The profiles can be managed via a profile manager that is operated via an entitlement server that can be controlled via the MNO. MNOs can source profiles from multiple EUMs in order to simplify profile ordering.
[0012] To delete the prioritized profile and request a new profile in order to, for example, unlock the functionality of the user equipment, a customer associated with the user equipment can contact an MNO in any of a number of ways. For example, the MNO can enable customers to submit a request for a new profile via a website that is operated by the MNO. Additionally, or alternatively, a customer support representative of the MNO can interface with various customer support systems to enable the customer to call or engage in an online chat with a customer support representative. The customer support system can include a support communications engine that can be operated via the entitlement server.
[0013] The customer can be asked for a device identifier corresponding to the customer's user equipment, such as ICCID, EID, IMEI, and/or so forth, which the MNO can validate against a register of device identifiers, such as an equipment identification register (EIR) or another database. If the device identifier is valid, the MNO can identify a profile that corresponds to the device identifier and the request is provided to a policy manager to refer to one or more policies of the MNO that apply to the customer's profile. The policy manager can be operated via the entitlement server to manage the policies of the MNO, wherein the policies can reflect business priorities, plans, and decisions of the MNO.
[0014] Based on the one or more policies, the profile manager can determine whether the customer is eligible for a new profile. For example, the profile manager can determine that the customer is not eligible for a new profile in response to the user equipment being reported lost or stolen, in response to delinquency in payment for an account associated with the user equipment, or in response to expiration of a service plan associated with the user equipment. In various embodiments, the profile manager can determine whether the customer is eligible for a new profile on a case-by-case basis and request for policy overrides from the MNO as deemed necessary. If the customer is eligible for a new profile other than the prioritized profile, the functionality of user equipment can be unlocked and the MNO can notify the customer that the request for a new profile has been granted. Additionally, the MNO transmit instructions to the user equipment, via the website that is operated by the MNO or a customer support interface, to install the new profile on the eUICC. Profile status for deleted and/or new profiles can be managed via the profile manager.
[0015] The functionality of user equipment can be unlocked for any of a number of reasons. For example, an unlocked user equipment can be purchased outright without a service contract obligation that is tied to the user equipment. In another example, a user equipment can be unlocked after a customer's cellular subscription has lapsed and/or the terms of the customer's contract obligation have been fulfilled. The techniques described herein may be implemented in a number of ways. Example implementations are provided below with reference to the following figures.
Example Network Architecture
[0016] FIG. 1 illustrates example architecture for management of subscription profiles over the air based on eligibility criteria for customers. The architecture may include an entitlement server 120 of an MNO in communication with one or more network base stations via portions of a network backhaul and/or via other distributed portions of a network 100. The backhaul can employ any common wireline communication technology, such as optical fiber, coaxial cable, twisted pair cable, Ethernet cable, and powerline cable, along with any common wireless communication technology.
[0017] The network 100 can be a cellular network that implements 2G, 3G, 4G, and long-term evolution (LTE), LTE advanced, high-speed data packet access (HSDPA), evolved high-speed packet access (HSPA+), universal mobile telecommunication system (UMTS), code-division multiple access (CDMA), global system for mobile communications (GSM), WiMax, and WiFi access technologies. The entitlement server 120 is in communication with one or more user equipment 128 that is associated with a customer 126, wherein the user equipment 128 comprises smartphones, mobile devices, personal digital assistants (PDAs) or other electronic devices having a wireless communication function that are capable of receiving inputs, processing the inputs, and generating output data. The user equipment 128 is connected to a telecommunication network utilizing one or more wireless base stations or any other common wireless or wireline network access technologies. The user equipment 128 comprises a eUICC comprising a corresponding embedded UICC identifier (EID) 130 and integrated circuit card identifier (ICCID) 132. Thus, a eUICC can be identified by its EID 130 and ICCID 132. The eUICC can comprise a plurality of profiles, wherein one of the plurality of profiles comprises a prioritized profile that can be generated and owned by the MNO.
[0018] The entitlement server 120 may include general-purpose computers, such as desktop computers, tablet computers, laptop computers, servers (e.g., on-premise servers), or other electronic devices that are capable of receiving inputs, processing the inputs, and generating output data. The entitlement server 120 may be operated by the MNO or a third-party entity that is working with the MNO. The entitlement server 120 may store data in a distributed storage system, in which data may be stored for long periods of time and replicated to guarantee reliability.
[0019] Accordingly, the entitlement server 120 may provide data and processing redundancy, in which data processing and data storage may be scaled in response to demand. Further, in a networked deployment, new entitlement servers 120 may be added. Thus, the entitlement server 120 can include a plurality of physical machines that may be grouped together and presented as a single computing system. Each physical machine of the plurality of physical machines may comprise a node in a cluster. The entitlement server 120 may also be in the form of virtual machines, such as virtual engines (VE) and virtual private servers (VPS).
[0020] The entitlement server 120 is configured to execute provider services 112 to grant or deny consumer initiated requests for loading a non-prioritized profile when a prioritized profile is currently loaded on the user equipment 128. In an example embodiment, the provider services 112 include a policy manager 114, a profile manager 116, and a support communications engine 118. Without limitation, the provider services can also provide a framework for additional functionalities such as customized reporting, analytics, inventory management, access control, and/or so forth, depending upon embodiments. The policy manager 114 is configured to add, delete, and edit policies for the MNO. The policy manager 114 can communicate with policy manager tools of the MNO or a third party entity that is responsible for setting or entering policies on behalf of the MNO. The policies can reflect business priorities, plans, and decisions relating to the telecommunication services provided by the MNO.
[0021] The policy manager 114 is in communication with a policy database 102, which stores and maintains MNO policies within a resident or distributed MNO data store, to enable customer accounts and affiliated user equipment to be managed by a corresponding MNO using the entitlement server. In various embodiments, the policy database 102 can also maintain customer account information (e.g., service plan information, billing information). The policy manager 114 can enforce the policies in the policy database 102 for facilitating profile management and profile loading schemes described herein. The policy manager 114 can add, delete, and edit policies stored in the policy database 102 on a predetermined scheduled basis. In this regard, the policy manager 114 can include a scheduling mechanism to periodically check and maintain available data in the policy database 102.
[0022] The profile manager 116 can determine, based on at least one or more policies from the policy database 102, whether to grant or deny a request to apply a new profile within the eUICC of the user equipment 128. For example, one or more policies can relate to customers' account status. The profile manager 116 can take into account a rate plan or account status associated with the user equipment 128, such as an account status retrieved from an equipment identity payment (EIP) server. If an account status shows delinquency in payment, the profile manager 116 can determine that the user equipment 128 associated with that account is not eligible to receive a new profile. If user equipment 128 is not eligible to receive a new profile within its eUICC, the profile manager 116 can cause a message (e.g., a SMS message, an IP message, etc.), to be delivered to the user equipment 128 informing the customer 126 of the user equipment 128 that the request for a new profile has been denied.
[0023] Conversely, if the customer 126 is eligible for a new profile within the eUICC of the user equipment 128, the profile manager 116 causes a message to be sent to the user equipment 128 informing the customer 126 of the user equipment 128 that the request has been granted. If the profile manager 116 cannot determine whether the user equipment 128 is eligible to receive a new profile within its eUICC (i.e., based on the one or more policies of the MNO), the profile manager 116 can cause a message to be delivered to the user equipment 128 informing the customer 126 of the user equipment 128 to contact the MNO. Additionally or alternatively, the profile manager 116 can cause a message to be delivered to a support representative 110 to contact the customer 126 of the user equipment 128 to resolve the customer's 126 request for a new profile.
[0024] The profile manager 116 is in communication with a profile database 122. In various embodiments, the profiles stored within the profile database 122 can comprise a provisioning profile, an operational profile, and/or a user profile. The provisioning profile includes information needed to establish a connection to an MNO. The operational profile includes MNO network access information for receiving telecommunication services. If there is no provisioning profile, the operational profile can act as the provisioning file, depending upon embodiments. The user profile can include user information, including user account information and user equipment information. The user profile may be included in an operational profile, depending upon embodiments.
[0025] Additionally, each profile can include information related to a corresponding SM and information for establishing a connection or for allowing communication with the SM, and an authentication credential and key information for performing an authentication (e.g., key exchanges). The authentication credential can comprise an Authentication and Key Agreement (AKA) scheme, public key infrastructure (PKI), and/or other authentication protocol such as multi-factor authentication and SAS certification. The profiles enable SMs to communicate with a respective user equipment or terminals that comprise eUICC having matching or corresponding profiles. More specifically, a user equipment can access an SM by using a profile selected from one of the profiles stored in the SM. In this way, the user equipment can communicate with an MNO using the SM. The eUICC automatically performs a user authentication with respect to a mobile communication network, to which the customer 126 has subscribed, by using the information stored in the eUICC, so that the customer 126 may conveniently receive telecommunication services through the user equipment 128.
[0026] The support communications engine 118 is configured to facilitate communication between the customer 126 at the user equipment 128 and a support representative 110 at a customer support terminal 108. In various embodiments, the support communications engine 118 provides a support user interface 104, which is accessible at the customer support terminal 108.
[0027] The user equipment 128 can include a trusted execution environment (TEE) connected by a trusted layer connector (TLC) and is configured to run any known operating system (e.g., Microsoft Windows.RTM., Google Android.RTM., Apple iOS.RTM., Linux.RTM., etc.). The operating system is configured to execute a customer support application 124 that at least partially resides on the user equipment 128. In a scenario where a customer wants to apply a new profile, the customer can contact its MNO via the customer support application 124. For example, the customer can call in via the customer support application 124 and speak directly with a support representative 110 at a customer support terminal 108 using voice over phone or voice over IP (VoIP).
[0028] In another example, the customer support application 124 can comprise a messaging feature that enables the customer 126 to send messages to the support representative 110 to engage in a chat or an online conversation. The customer support application 124 and/or the support communications engine 118 at the entitlement server 120 can automatically generate session notes upon completion of a customer support session. The session notes can be associated with the customer's account and stored in a data store such as a customer database and/or a policy database 102.
[0029] The customer support application 124 can comprise an application user interface, including a graphical user interface (GUI) for displaying information and notifications to the customer. For example, the customer support application 124 can include a customer web interface that allows the customer 126 of the user equipment 128 to utilize a dedicated customer account webpage of a corresponding MNO website, to perform various user-driven account management functions. For instance, the user-driven account management functions can include enabling the customer 126 to receive and view invoices and pay monthly service fees online using a secure online payment system of the MNO's website. Additionally, the customer 126 can view his or her account activities and user equipment associated with the customer's 126 account. In another example, a user-driven account management function of a customer's account webpage can facilitate the customer 126 requesting a new profile over the Internet. In this regard, the user equipment 128 may be locked based on a prioritized profile that is enabled, wherein the prioritized profile can be managed by the MNO or an SM, depending upon embodiments.
[0030] When initiating a request to apply a new profile on the eUICC of the user equipment 128, the customer 126 may be asked for a device identifier, such as an IMEI, EID 130, ICCID 132, which may be validated. More specifically, the provider services 112 at the entitlement server 120 can validate the device identifier against a register of device identifiers, such as an equipment identification register (EIR) or another database (not shown). If the device identifier validates (e.g., EID 130, ICCID 132), the request is provided to a policy manager 114 to refer to the policy database 102.
[0031] Based on the policies from the policy database 102, the profile manager 116 performs client privilege responsibility. For instance, the profile manager 116 can check if the customer 126 is allowed to modify one or more profiles (i.e., a prioritized profile) on the eUICC of the target user equipment 128. If the customer 126 is allowed to delete the prioritized profile and load a new profile on the eUICC of the user equipment 128, the profile manager 116 can transmit a message to the user equipment 128 to inform the customer 126 that the customer's 126 request was granted. Thus, a customer initiated request for replacing or deleting the prioritized profile must be reviewed for approval via the profile manager 116 of the entitlement server 120. Additionally, the profile manager 116 can check if a requested profile has been loaded and is available in one or more SMs before making a request for ordering profiles or EID. If the requested profile has not been loaded, the profile manager 116 can provide an error message in response to the customer's request for loading the requested profile.
[0032] Upon determining eligibility for loading a new profile, the customer support application 124 can provide instructions to a trustlet through the TLC and the trustlet may affect the locking or unlocking of the functionalities of the user equipment 128. The trustlet or another component of the TEE can provide a secure connection to an identification module such as a eUICC of the user equipment 128.
[0033] In some embodiments, the provider services 112 are operatively connected to at least one data store, wherein the data store can comprise a policy database 102, a profile database 122, and/or other data sources such as enterprise entities that can maintain, without limitation, EID, ICCID, subscription manager secure routing identifier (SMSR-ID), and/or so forth. The data store can comprise a home subscriber server (HSS) of a telecommunications network or a home location register (HLR) of the telecommunications network. The data store may store information relating to MNOs, SMs, customers 126, and/or so forth. In various embodiments, the data store can store a tree having a root node for security and that is configured to implement a protocol to coordinate with a third-party entity.
Example Computing Device Components
[0034] FIG. 2 is a block diagram showing various components of an illustrative computing device, wherein the computing device can comprise an entitlement server 120. It is noted that the entitlement server 120 as described herein can operate with more or fewer of the components shown herein. Additionally, the entitlement server 120 as shown herein or portions thereof can serve as a representation of one or more of the computing devices of the present system. The entitlement server 120 may include a communication interface 202, one or more processors 204, hardware 206, and memory 208. The communication interface 202 may include wireless and/or wired communication components that enable the entitlement server 120 to transmit data to and receive data from other networked devices. In at least one example, the one or more processor(s) 204 may be a central processing unit(s) (CPU), graphics processing unit(s) (GPU), a both a CPU and GPU, or any other sort of processing unit(s). Each of the one or more processor(s) 204 may have numerous arithmetic logic units (ALUs) that perform arithmetic and logical operations as well as one or more control units (CUs) that extract instructions and stored content from processor cache memory, and then execute these instructions by calling on the ALUs, as necessary during program execution. The one or more processor(s) 204 may also be responsible for executing all computer applications stored in the memory, which can be associated with common types of volatile (RAM) and/or nonvolatile (ROM) memory. The hardware 206 may include additional user interface, data communication, or data storage hardware. For example, the user interfaces may include a data output device (e.g., visual display, audio speakers), and one or more data input devices. The data input devices may include but are not limited to, combinations of one or more of keypads, keyboards, mouse devices, touch screens that accept gestures, microphones, voice or speech recognition devices, and any other suitable devices.
[0035] The memory 208 may be implemented using computer-readable media, such as computer storage media. Computer-readable media includes, at least, two types of computer-readable media, namely computer storage media and communications media. Computer storage media includes volatile and nonvolatile, removable and non-removable media implemented in any method or technology for storage of information such as computer-readable instructions, data structures, program modules, or other data. Computer storage media includes, but is not limited to, RAM, ROM, EEPROM, flash memory or other memory technology, CD-ROM, digital versatile disks (DVD), high-definition multimedia/data storage disks, or other optical storage, magnetic cassettes, magnetic tape, magnetic disk storage or other magnetic storage devices, or any other non-transmission medium that can be used to store information for access by a computing device. In contrast, communication media may embody computer-readable instructions, data structures, program modules, or other data in a modulated data signal, such as a carrier wave, or other transmission mechanisms. The memory 208 may also include a firewall. In some embodiments, the firewall may be implemented as hardware 206 in the entitlement server 120.
[0036] The processors 204 and the memory 208 of the entitlement server 120 may implement an operating system 210, the provider services 112, and a data store 212. The data store 212 can comprise a data management layer that includes software utilities for facilitating the acquisition, processing, storing, reporting, and analysis of data from multiple data sources such as a policy database, a profile database, and/or so forth. In various embodiments, the data store 212 can interface with an API for providing data access.
[0037] The operating system 210 may include components that enable the entitlement server 120 to receive and transmit data via various interfaces (e.g., user controls, communication interface, and/or memory input/output devices), as well as process data using the processors 204 to generate output. The operating system 210 may include a presentation component that presents the output (e.g., display the data on an electronic display, store the data in memory, transmit the data to another electronic device, etc.). Additionally, the operating system 210 may include other components that perform various additional functions generally associated with an operating system.
[0038] The provider services 112 include a policy manager 114, a profile manager 116, and a support communications engine 118 that comprises a customer support application 124. These components of the provider services 112 may include routines, program instructions, objects, and/or data structures that perform particular tasks or implement particular abstract data types.
[0039] The policy manager 114 is operatively connected to a policy database 102 in order to add, delete, update, and/or replace MNO policies. In this regard, the policy manager 114 can be in communication with an entity for creating and/or amending policies, wherein the entity can be a third party entity or an entity that is operated and/or controlled by the MNO (collectively, "policy-making entities"). The policy manager 114 can implement a scheduling mechanism to periodically check and retrieve newly available data from the policy-making entities. The policy manager 114 can handle the extraction and the handling of the policy data based on various configurations. For example, the configurations can include frequency of data retrieval, data retention period, and data disposal following an expiration of the data retention period.
[0040] The policy manager 114 is configured to identify one or more policies that apply to a customer operating a target user equipment, and therefore the customer's account. In this regard, a first set of policies can apply to a first customer operating a first target equipment, and a second set of policies can apply to a second customer operating a second target equipment, wherein the first set of policies and the second set of policies differ, although one or more of the policies within the first set of policies and the second set of policies can be the same such that the first set of policies and the second set of policies can at least partially overlap.
[0041] Upon identifying one or more policies that apply to the customer operating the target user equipment, the applicable policies can be passed to the profile manager 116 to enable the profile manager 116 to decide whether to grant the customer's request for applying a new profile onto the eUICC of the customer's user equipment and/or replace a prioritized profile that is enabled in the eUICC. In this way, the profile manager 116 provides accountability measurements to prevent SMs and/or consumers from readily loading different profiles on the eUICC, thereby preventing changes to service plans or subscriptions without receiving approval from the MNO while still allowing remote management. The profile manager 116 can communicate with the policy manager 114 in order to determine, based on at least one policy, whether the target user equipment is eligible for a new profile in various scenarios. If the target user equipment is eligible to receive a new profile, the profile manager 116 can instruct the user equipment to receive a new profile (e.g., from a new subscription manager).
[0042] In various embodiments, the profile manager 116 can implement a validation mechanism to ensure that the identifier (e.g., ICCID, EID) received from the target equipment matches user account information and the existing profile. For example, the profile manager 116 can validate the profile status to ensure that the profile is currently active and not already deleted. Further, the profile manager 116 can receive authentication parameters for remote provisioning from an SM and receive security credentials therefrom upon verification of authentication parameters. In some embodiments, the profile manager 116 can implement key exchanges and/or generate a secure digital identifier based on the security credentials.
[0043] The support communication engine 118, via the customer support application 124, may enable the MNO to communicate with customers that operate one or more user equipment of the present system. For example, the customer support application 124 may provide an interface for displaying a customer's account information and account activities for the customer's account. More specifically, the customer's account information can include information pertaining to all of the user equipment and each of the individual customers associated with the customer's account if the customer's account includes a primary account holder and one or more additional customers (i.e., secondary account holders). In this regard, the customer can add, delete, or replace products and/or services as well as other customers to the account. Additionally, the customer support application 124 can provide a secure payment portal for receiving payments (e.g., via a credit card) for a telecommunication service subscription. Moreover, the customer support application can provide access to the customer's service contract, which includes the service contract obligation associated with the customer's service plan.
[0044] The customer support application 124 is configured to enable the customer to contact a support representative at a customer support terminal. In various embodiments, the customer can call the support representative using a chat application, voice over phone, or voice over Internet protocol. In this way, the customer can request to remove a prioritized profile that is managed by the MNO or an SM and apply a new profile to the eUICC of the customer's user equipment. The customer support application 124 can save session notes generated from the customer's interactions with the support representative. The session notes can be archived to a user account database or the data store 212.
Example Processes
[0045] FIG. 3 presents an illustrative process 300 for remotely managing profiles. The process 300 is illustrated as a collection of blocks in a logical flow chart, which represents a sequence of operations that can be implemented in hardware, software, or a combination thereof. In the context of software, the blocks represent computer-executable instructions that, when executed by one or more processors, perform the recited operations. Generally, computer-executable instructions may include routines, programs, objects, components, data structures, and the like that perform particular functions or implement particular abstract data types. The order in which the operations are described is not intended to be construed as a limitation, and any number of the described blocks can be combined in any order and/or in parallel to implement the process. For discussion purposes, the process 300 is described with reference to the network 100 of FIG. 1.
[0046] FIG. 3 is a flow diagram of an example process 300 for determining, by an entitlement server, whether to apply a new profile and/or replace a prioritized profile on a eUICC of a target device based on policies and in response to a customer request, in accordance with embodiments of the disclosure. At block 302, an entitlement server receives and processes a request from a customer operating a target user equipment for deleting a prioritized profile and loading a new profile on a eUICC of the target user equipment. In various embodiments, the request can comprise deleting an existing profile and loading a prioritized profile on the eUICC of the user target equipment. The request includes a device identifier such as EID or ICCID that corresponds to the target user equipment. The eUICC that corresponds to the EID comprises a plurality of profiles loaded thereon. One of the profiles comprises a prioritized profile that can be managed by an MNO or an SM, depending upon embodiments.
[0047] The request can also include credentials in accordance with PKI-based authentication protocol and/or utilizes multi-factor authentication. The request can also include one or more SAS certificates. In various embodiments, the request utilizes an identifier correlating with an account that is associated with a plurality of user equipment and a plurality of users (e.g., a user identifier associated with a wireless service provider, a wireless carrier, a cellular company, a mobile network carrier, etc.). Preferably, the request is submitted to the MNO via a customer support application that can reside in whole or in part on the user equipment.
[0048] At block 304, the entitlement server validates a profile type that is enabled on the eUICC of the target user equipment to determine whether the enabled profile is a prioritized profile. Additionally, or alternatively, the entitlement server validates the device identifier corresponding to the target user equipment. In this case, the entitlement server can validate the device identifier against a register of device identifiers, such as an EIR or another database. If a profile type has not been provided, the profile manager identifies a profile type associated with the device identifier or other metadata attributes. If the device identifier is valid, the MNO can confirm that the device identifier is correctly associated with the one or more profiles that is loaded on the eUICC. Thereafter, the request is provided to a policy manager to refer to one or more policies of the MNO that apply to the customer's profile.
[0049] At decision block 306, a profile manager determines whether the request meets the eligibility criteria as specified in the one or more policies. If the request does not meet the eligibility criteria ("no" response from the decision block 306), a support communications engine transmits a message to the customer denying the request via, for example, the customer support application, as indicated in block 308. If the request meets the eligibility criteria, ("yes" response from the decision block 308), the support communications engine transmits a message to the customer approving the request, as indicated in block 310. At block 312, the support communications engine can also transmit instructions to the target user equipment for loading a new profile. In various embodiments, the profile manager can retrieve a requested profile from a profile database and/or order an SM or the MNO to serve the eUICC of the target user equipment with the requested profile. In this regard, MNOs can provide metadata attributes (e.g., ICCID, profile type) associated with profile orders.
CONCLUSION
[0050] Although the subject matter has been described in language specific to structural features and/or methodological acts, it is to be understood that the subject matter defined in the appended claims is not necessarily limited to the specific features or acts described. Rather, the specific features and acts are disclosed as exemplary forms of implementing the claims.
* * * * *
D00000
D00001

D00002
D00003
XML
uspto.report is an independent third-party trademark research tool that is not affiliated, endorsed, or sponsored by the United States Patent and Trademark Office (USPTO) or any other governmental organization. The information provided by uspto.report is based on publicly available data at the time of writing and is intended for informational purposes only.
While we strive to provide accurate and up-to-date information, we do not guarantee the accuracy, completeness, reliability, or suitability of the information displayed on this site. The use of this site is at your own risk. Any reliance you place on such information is therefore strictly at your own risk.
All official trademark data, including owner information, should be verified by visiting the official USPTO website at www.uspto.gov. This site is not intended to replace professional legal advice and should not be used as a substitute for consulting with a legal professional who is knowledgeable about trademark law.