Identity-based Message Integrity Protection And Verification For Wireless Communication
YANG; Xiangying ; et al.
U.S. patent application number 16/293521 was filed with the patent office on 2020-01-16 for identity-based message integrity protection and verification for wireless communication. The applicant listed for this patent is Apple Inc.. Invention is credited to Lanpeng CHEN, Yuqin CHEN, Hao DUO, Shu GUO, Haijing HU, Huarui LIANG, Qian SUN, Fangli XU, Xiangying YANG, Dawei ZHANG, Lijia ZHANG.
| Application Number | 20200021993 16/293521 |
| Document ID | / |
| Family ID | 69139889 |
| Filed Date | 2020-01-16 |
| United States Patent Application | 20200021993 |
| Kind Code | A1 |
| YANG; Xiangying ; et al. | January 16, 2020 |
IDENTITY-BASED MESSAGE INTEGRITY PROTECTION AND VERIFICATION FOR WIRELESS COMMUNICATION
Abstract
Techniques for identity-based message integrity protection and verification between a user equipment (UE) and a wireless network entity, include use of signatures derived from identity-based keys. To protect against attacks from rogue network entities before activation of a security context with a network entity, the UE verifies integrity of messages by checking a signature using an identity-based public key PK.sub.ID derived by the UE based on (i) an identity value (ID) of the network entity and (ii) a separate public key PK.sub.PKG of a private key generator (PKG) server. The network entity generates signatures for messages using an identity-based private key SK.sub.ID obtained from the PKG server, which generates the identity-based private key SK.sub.ID using (i) the ID value of the network entity and (ii) a private key SK.sub.PKG that is known only by the PKG server and corresponds to the public key PK.sub.PKG.
| Inventors: | YANG; Xiangying; (Cupertino, CA) ; GUO; Shu; (Beijing, CN) ; ZHANG; Lijia; (Beijing, CN) ; SUN; Qian; (Beijing, CN) ; LIANG; Huarui; (Beijing, CN) ; XU; Fangli; (Beijing, CN) ; CHEN; Yuqin; (Shenzen, CN) ; HU; Haijing; (Beijing, CN) ; ZHANG; Dawei; (Saratoga, CA) ; DUO; Hao; (Beijing, CN) ; CHEN; Lanpeng; (Beijing, CN) | ||||||||||
| Applicant: |
|
||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|
| Family ID: | 69139889 | ||||||||||
| Appl. No.: | 16/293521 | ||||||||||
| Filed: | March 5, 2019 |
| Current U.S. Class: | 1/1 |
| Current CPC Class: | H04L 9/083 20130101; H04W 12/0609 20190101; H04L 63/123 20130101; H04W 12/04033 20190101; H04W 12/1006 20190101; H04W 74/006 20130101; H04L 9/3247 20130101; H04W 72/042 20130101; H04L 9/3073 20130101; H04L 9/3268 20130101; H04L 9/3297 20130101; H04L 2209/80 20130101; H04W 12/0401 20190101 |
| International Class: | H04W 12/10 20060101 H04W012/10; H04W 72/04 20060101 H04W072/04; H04W 74/00 20060101 H04W074/00; H04W 12/04 20060101 H04W012/04; H04W 12/06 20060101 H04W012/06; H04L 9/32 20060101 H04L009/32 |
Foreign Application Data
| Date | Code | Application Number |
|---|---|---|
| Jul 10, 2018 | CN | PCT/CN2018/095137 |
Claims
1. A method for protecting message integrity, the method comprising: by a network entity: sending a request to a private key generator (PKG) server, the request including a first identity value (ID1) for the network entity; receiving from the PKG server a response that includes a first private key (SK.sub.ID1) that is based on ID1 and on a private key of the PKG server (SK.sub.PKG); and prior to establishing a security context with a user equipment (UE): generating a signature for a first message, the signature based on SK.sub.ID1; and sending the first message concatenated with the signature to the UE.
2. The method of claim 1, further comprising: by the network entity: providing ID1 to the UE before sending the first message, wherein the UE verifies the first message using a first public key (PK.sub.ID1) that corresponds to SK.sub.ID1.
3. The method of claim 2, wherein the UE generates PK.sub.ID1 using ID1 and a public key of the PKG server (PK.sub.PKG) that corresponds to SK.sub.PKG.
4. The method of claim 1, wherein: the network entity comprises a next generation NodeB (gNB) of a cellular wireless network; and the first message comprises an access stratum (AS) message.
5. The method of claim 4, wherein the first message comprises a radio resource control (RRC) signaling message.
6. The method of claim 4, wherein the first message comprises a random access response (RAR) message sent to the UE as part of a random access channel (RACH) procedure.
7. The method of claim 1, wherein: the network entity comprises an access and mobility management function (AMF) server of a cellular wireless network; and the first message comprises a non-access stratum (NAS) message.
8. The method of claim 1, wherein: ID1 comprises a concatenation of field values including a first time stamp value that indicates a first time period during which ID1 is valid.
9. The method of claim 8, further comprising: by the network entity and prior to expiration of the first time period: sending a second request to the PKG server, the second request including a second identity value (ID2) for the network entity that includes a second time stamp value that indicates a second time period during which ID2 is valid; and receiving from the PKG server a second response that includes a second private key (SK.sub.ID2) that is based on ID.sub.2 and on SK.sub.PKG.
10. The method of claim 1, wherein: ID1 and use of SK.sub.ID1 is valid for a first time period; and the network entity obtains from the PKG server a second private key (SK.sub.ID2) based on a second identity value (ID2) for use during a second time period that is non-overlapping with the first time period.
11. The method of claim 1, wherein: the network entity comprises a femto-cell; and ID1 comprises a concatenation of field values including a field value indicating the femto-cell operates for a closed subscriber group (CSG).
12. A method of verifying message integrity, the method comprising: by a user equipment (UE): obtaining a first identity value (ID1) for a network entity; generating a first public key (PK.sub.ID1) based on ID1 and on a public key of a private key generator (PKG) server (PK.sub.PKG); and prior to establishing a security context with the network entity: receiving from the network entity a first message concatenated with a signature based on a first private key (SK.sub.ID1) that is based on ID1 and on a private key of the PKG server (SK.sub.PKG) that corresponds to PK.sub.PKG; verifying integrity of the first message using the signature and PK.sub.ID1; and discarding the first message when integrity verification of the first message fails.
13. The method of claim 12, wherein obtaining ID1 for the network entity comprises extracting ID1 from a message transmitted by the network entity.
14. The method of claim 13, wherein the message comprises a system information block (SIB) message broadcast by the network entity.
15. The method of claim 12, wherein obtaining ID1 for the network entity comprises deriving ID1 based on information broadcast by the network entity.
16. The method of claim 12, wherein: the network entity comprises a next generation NodeB (gNB) of a cellular wireless network; and the first message comprises an access stratum (AS) message.
17. The method of claim 16, wherein the first message comprises a radio resource control (RRC) signaling message.
18. The method of claim 17, wherein the first message comprises a random access response (RAR) message received from the network entity as part of a random access channel (RACH) procedure.
19. The method of claim 12, wherein: the network entity comprises an access and mobility management function (AMF) server of a cellular wireless network; and the first message comprises a non-access stratum (NAS) message.
20. The method of claim 12, wherein: ID1 comprises a concatenation of field values including a first time stamp value that indicates a first time period during which ID1 is valid.
21. The method of claim 12, wherein: the network entity comprises a femto-cell; and ID1 comprises a concatenation of field values including a field value indicating the femto-cell operates for a closed subscriber group (CSG).
22. An apparatus configurable for operation in a user equipment (UE), the apparatus comprising a processor and a memory storing instructions that, when executed by the processor, cause the UE to perform steps that include: obtaining a first identity value (ID1) for a network entity; generating a first public key (PK.sub.ID1) based on ID1 and on a public key of a private key generator (PKG) server (PK.sub.PKG); and prior to establishing a security context with the network entity: receiving from the network entity a first message concatenated with a signature based on a first private key (SK.sub.ID1) that is based on ID1 and on a private key of the PKG server (SK.sub.PKG) that corresponds to PK.sub.PKG; verifying integrity of the first message using the signature and PK.sub.ID1; and discarding the first message when integrity verification of the first message fails.
Description
CROSS-REFERENCE TO RELATED APPLICATIONS
[0001] The present application claims the benefit of International Application No. PCT/CN2018/095137, entitled "IDENTITY-BASED MESSAGE INTEGRITY PROTECTION AND VERIFICATION FOR WIRELESS COMMUNICATION," filed Jul. 10, 2018, the content of which is incorporated by reference herein in its entirety for all purposes.
FIELD
[0002] The described embodiments set forth techniques for identity-based message integrity protection and verification when communicating messages between a wireless device and a wireless network entity, including use of signatures derived from identity-based keys for message integrity protection by a sending network entity and message integrity verification by the receiving wireless device.
BACKGROUND
[0003] Wireless communication, by nature of transmission through an open medium, is vulnerable to eavesdropping. In addition, rogue network entities, such as fake base stations, can impersonate genuine network entities in order to obtain private information from a wireless device or to misdirect the wireless to communicate with the rogue equipment. When associating with a cellular wireless network, a wireless device can perform an authentication and key agreement (AKA) procedure and subsequently activate a security context with the cellular wireless network, including establishing a set of keys for encryption and decryption as well as for integrity protection and verification of messages communicated between the wireless device and the cellular wireless network. Prior to security activation with the cellular wireless network, however, certain messages may be communicated in a clear, readable, unencrypted format that is open to snooping. Additionally, rogue network entities may send messages to the wireless device to redirect the wireless device improperly to a lower security wireless network or to cause the wireless device to reveal private information such as an unencrypted subscription permanent identifier (SUPI) of the wireless device. As the wireless device cannot verify integrity of messages received from network entities, whether genuine or rogue, before the security context is activated, the wireless device is vulnerable to security attacks.
SUMMARY
[0004] Representative embodiments set forth techniques for identity-based message integrity protection and verification when communicating messages between a wireless device, e.g., a user equipment (UE), and a wireless network entity, including use of signatures derived from identity-based keys for message integrity protection by a sending network entity and for message integrity verification by the receiving wireless device. To protect against attacks from rogue network entities, e.g., fake base stations, before activation of a security context with a network entity of a wireless network, the UE verifies integrity of messages received from the network entity by checking a signature of a received message using an identity-based public key PK.sub.ID derived by the UE. The public key PK.sub.ID is generated using (i) an identity value (ID) of the network entity that sent the message and (ii) a separate public key PK.sub.PKG of a public/private key pair maintained by a private key generator (PKG) server. The network entity generates signatures for messages using an identity-based private key SK.sub.ID that corresponds to the identity-based public key PK.sub.ID. The identity-based private key SK.sub.ID is obtained by the network entity from the PKG server, which generates the identity-based private key SK.sub.ID using (i) the ID value of the network entity and (ii) a private key SK.sub.PKG that is known only by the PKG server and corresponds to the public key PK.sub.PKG.
[0005] The UE obtains the ID value of the network entity based on one or more messages received from the network entity that include at least a portion of the ID value, such as a broadcast message that includes one or more of: a public land mobile network (PLMN) ID value, a next generation Node B (gNB) globally unique ID value, or a tracking area code (TAC) value. The ID value of the network entity can also include a time stamp that limits a time period during which the ID value is valid. Changes to the ID value of the network entity, such as an updated time stamp value, requires the network entity to obtain from the PKG server an updated private key SK.sub.ID based on the updated ID value. The UE also derives an updated public key PK.sub.ID based on the updated ID value. Signatures generated based on the private key SK.sub.ID are appended to one or more broadcast messages and/or to one or more unicast messages transmitted by the network entity to provide integrity protection for the messages. The UE verifies integrity of the received messages by checking the signature using the public key PK.sub.ID. Messages for which integrity cannot be verified can be ignored and/or discarded by the UE.
[0006] This Summary is provided merely for purposes of summarizing some example embodiments so as to provide a basic understanding of some aspects of the subject matter described herein. Accordingly, it will be appreciated that the above-described features are merely examples and should not be construed to narrow the scope or spirit of the subject matter described herein in any way. Other features, aspects, and advantages of the subject matter described herein will become apparent from the following Detailed Description, Figures, and Claims.
[0007] Other aspects and advantages of the embodiments described herein will become apparent from the following detailed description taken in conjunction with the accompanying drawings which illustrate, by way of example, the principles of the described embodiments.
BRIEF DESCRIPTION OF THE DRAWINGS
[0008] The included drawings are for illustrative purposes and serve only to provide examples of possible structures and arrangements for the disclosed inventive apparatuses and methods for providing wireless computing devices. These drawings in no way limit any changes in form and detail that may be made to the embodiments by one skilled in the art without departing from the spirit and scope of the embodiments. The embodiments will be readily understood by the following detailed description in conjunction with the accompanying drawings, wherein like reference numerals designate like structural elements.
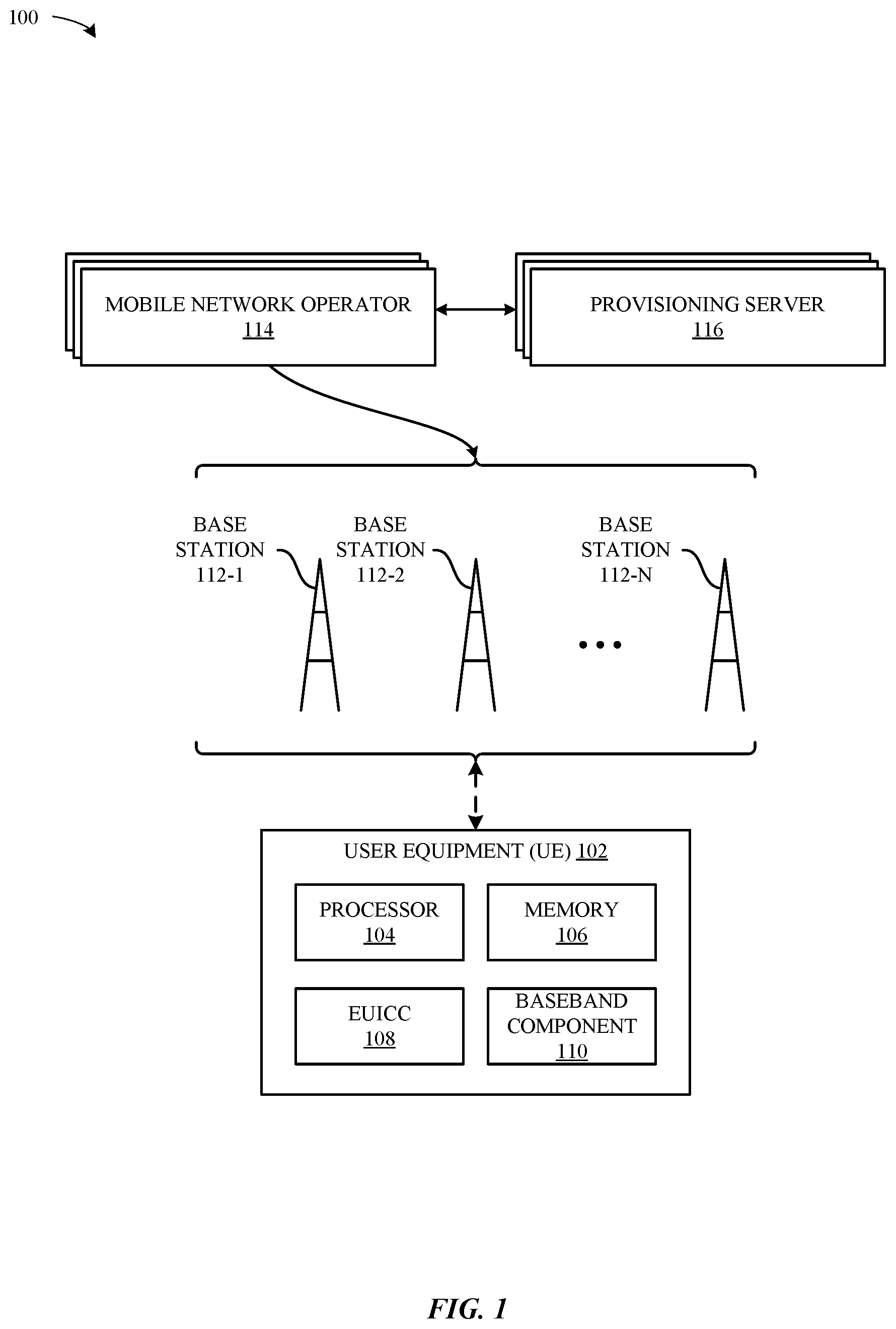
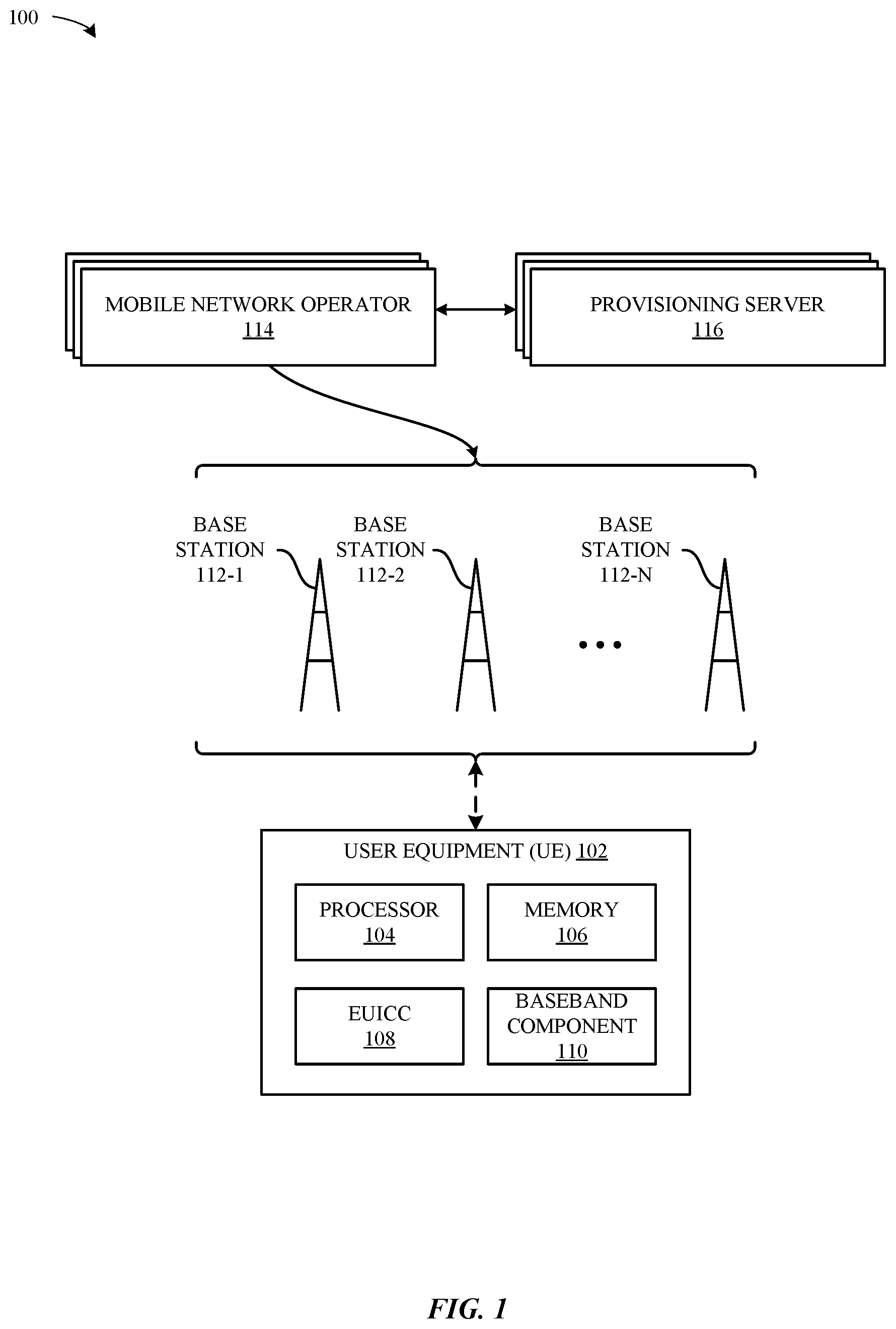
[0009] FIG. 1 illustrates a block diagram of different components of an exemplary system configured to implement the various techniques described herein, according to some embodiments.
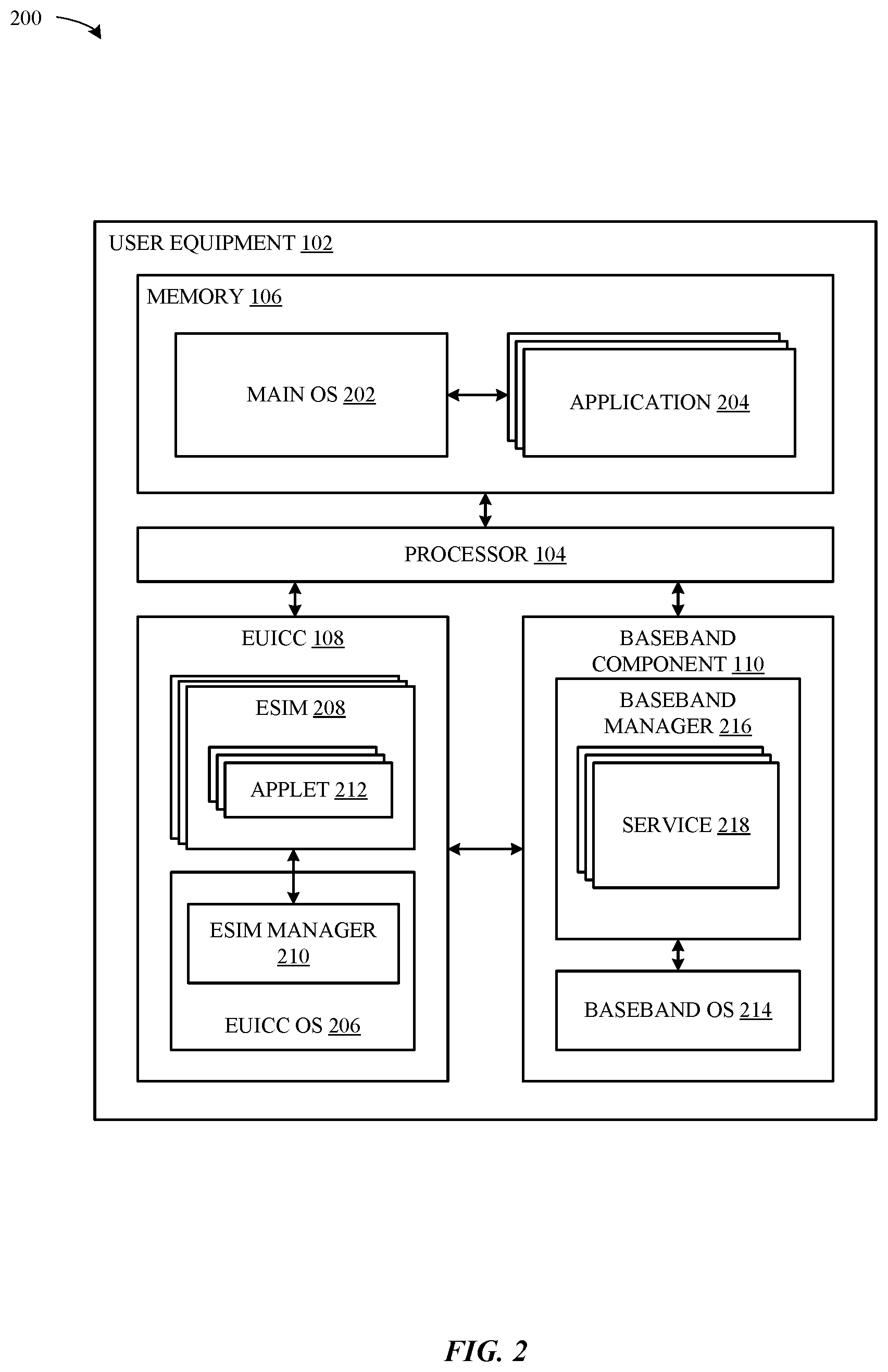
[0010] FIG. 2 illustrates a block diagram of a more detailed view of exemplary components of the system of FIG. 1, according to some embodiments.
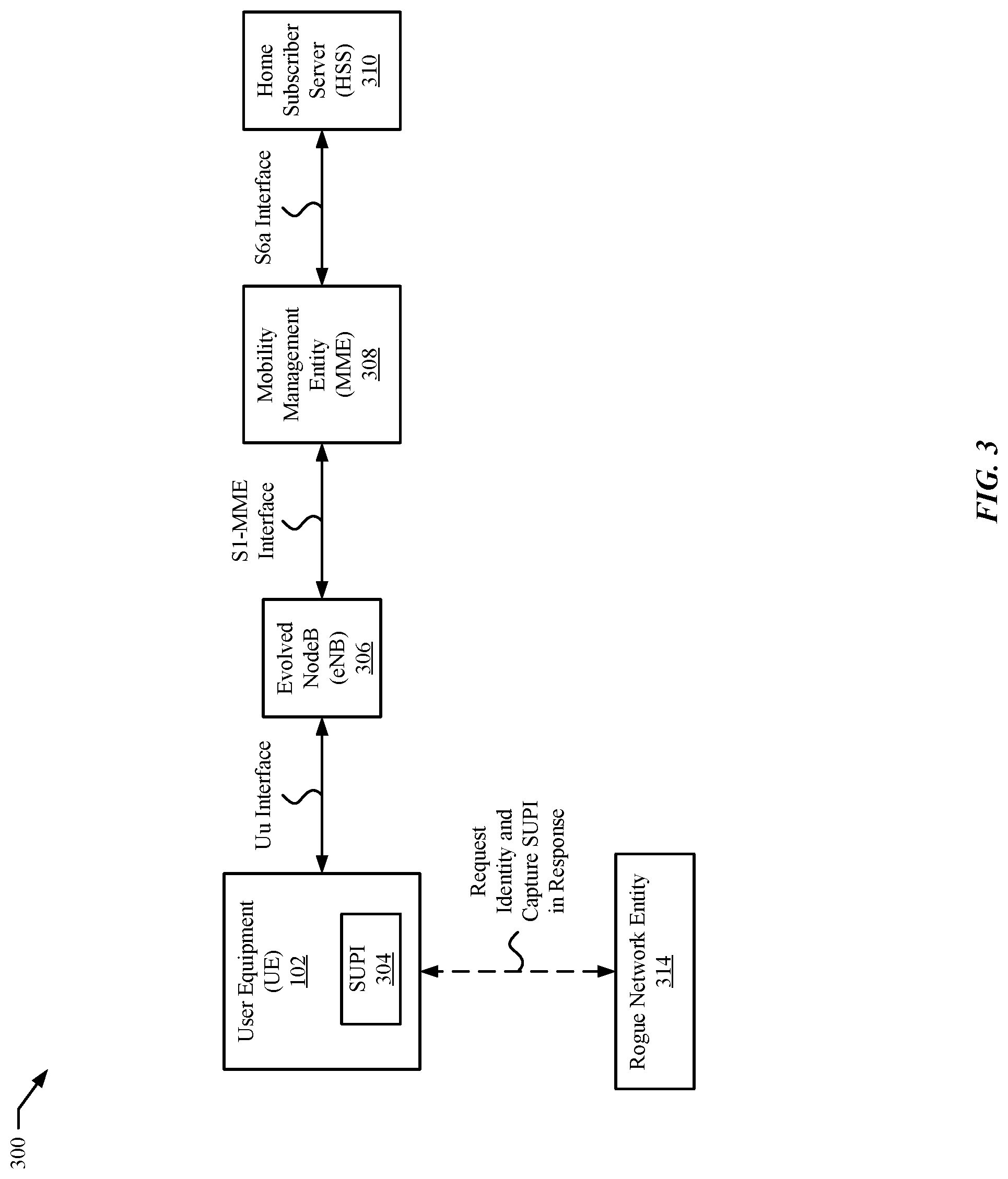
[0011] FIG. 3 illustrates a block diagram of an exemplary system subject to attach by a rogue network entity, according to some embodiments.
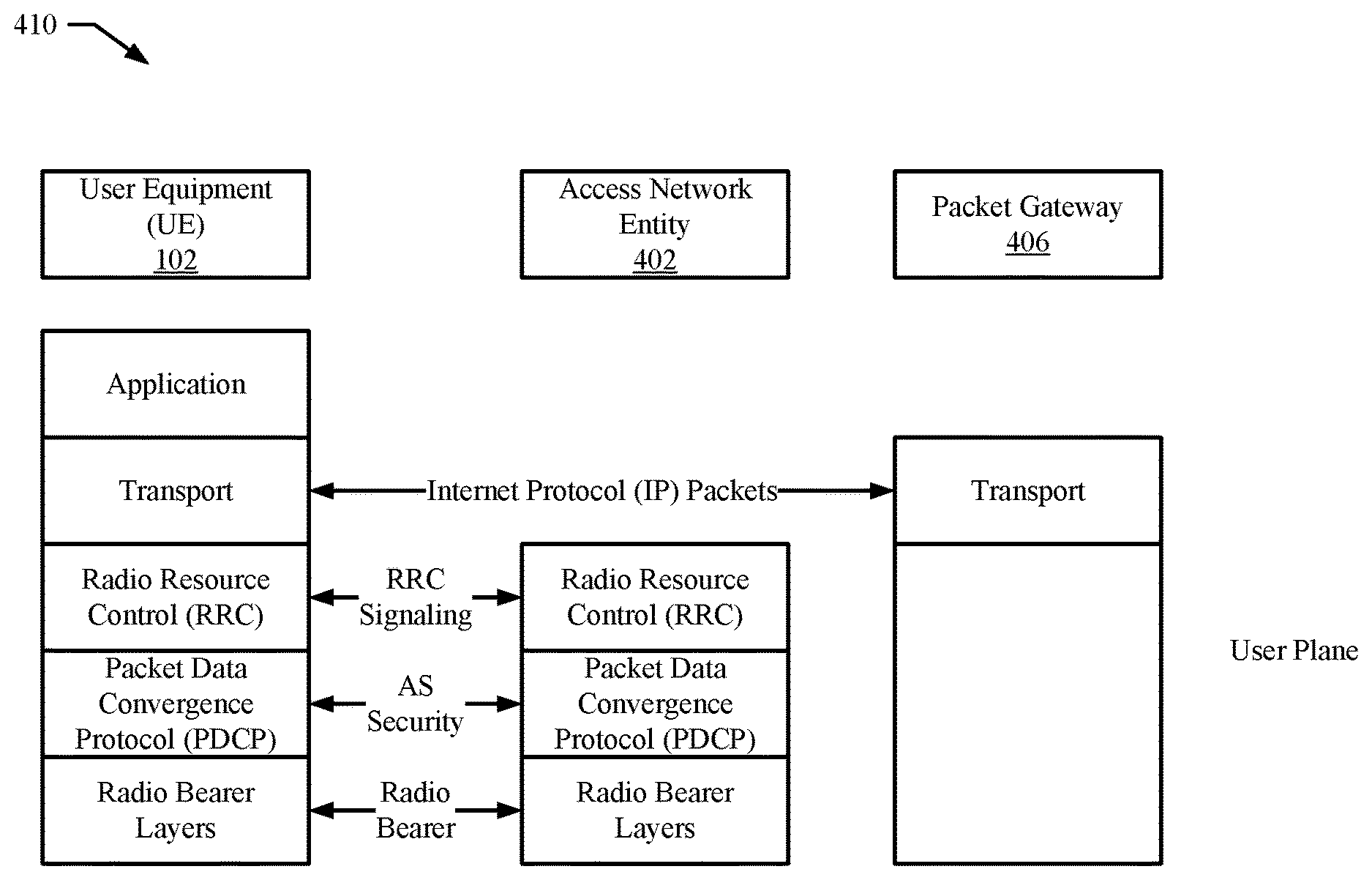
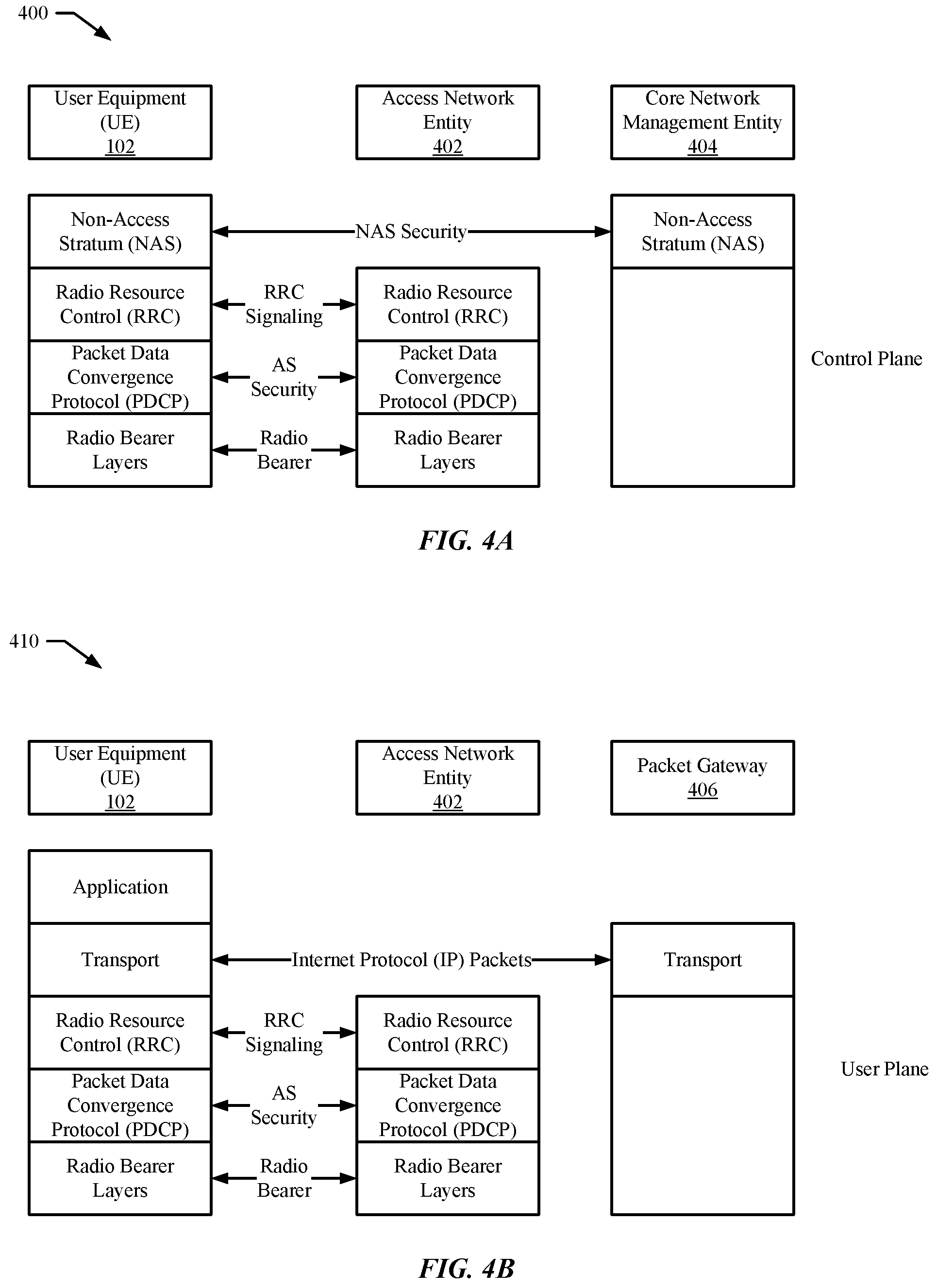
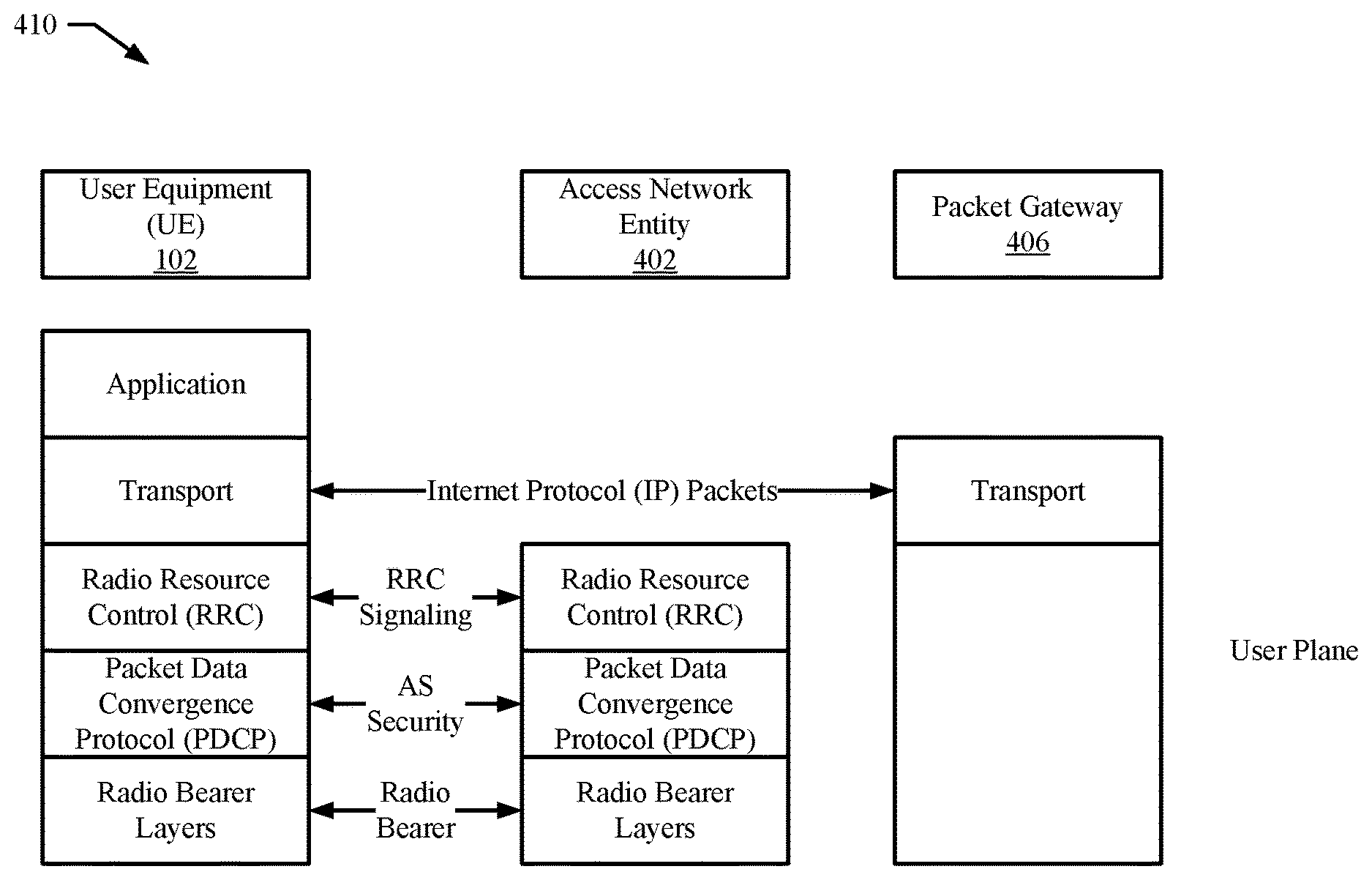
[0012] FIGS. 4A and 4B diagrams of communication protocol stacks that include message security for signaling messages and data packets after establishment of a security context between a wireless device and network entities of a wireless network, according to some embodiments.
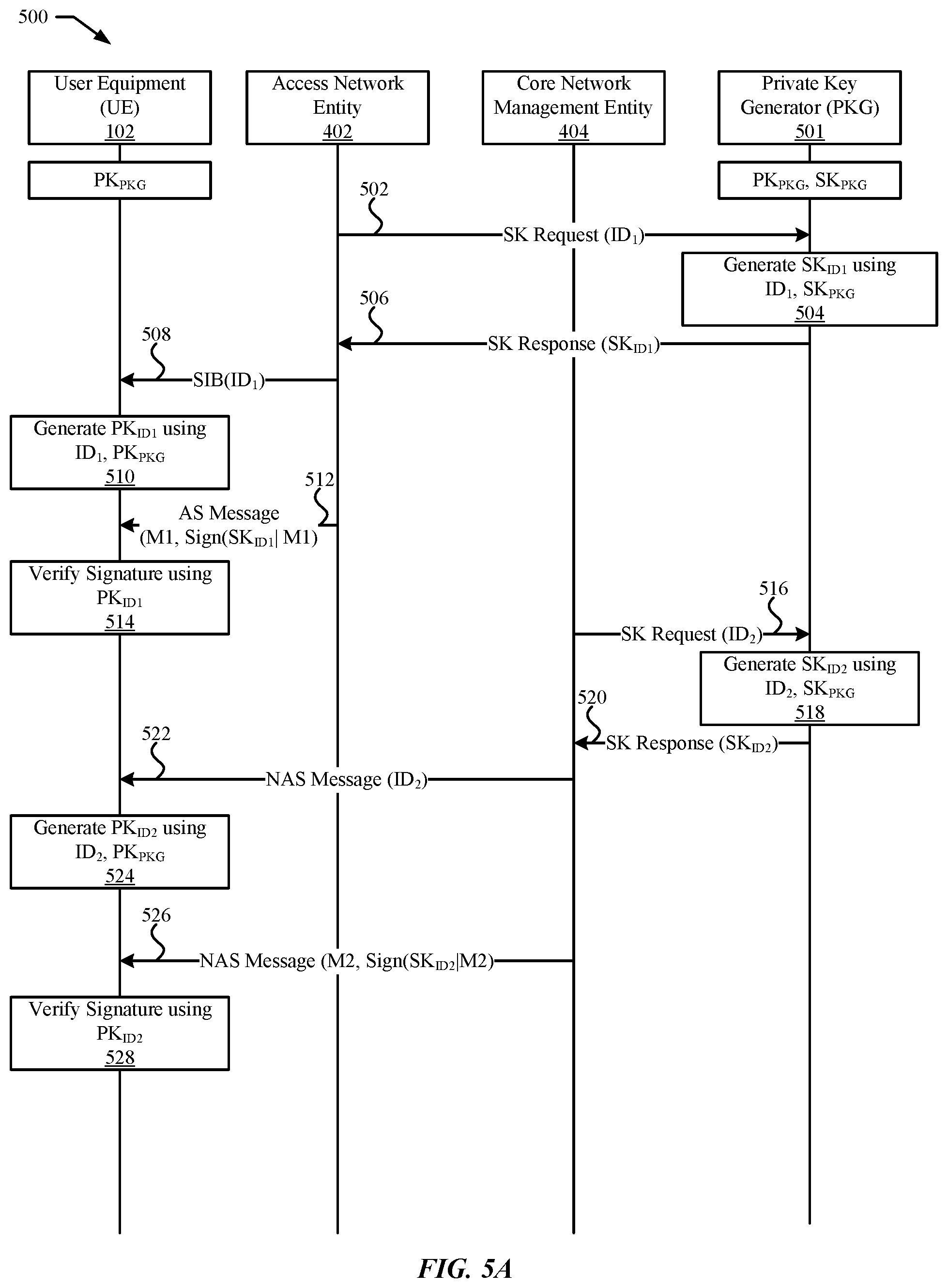
[0013] FIG. 5A illustrates an exemplary message exchange using identity-based message integrity protection and verification, according to some embodiments.
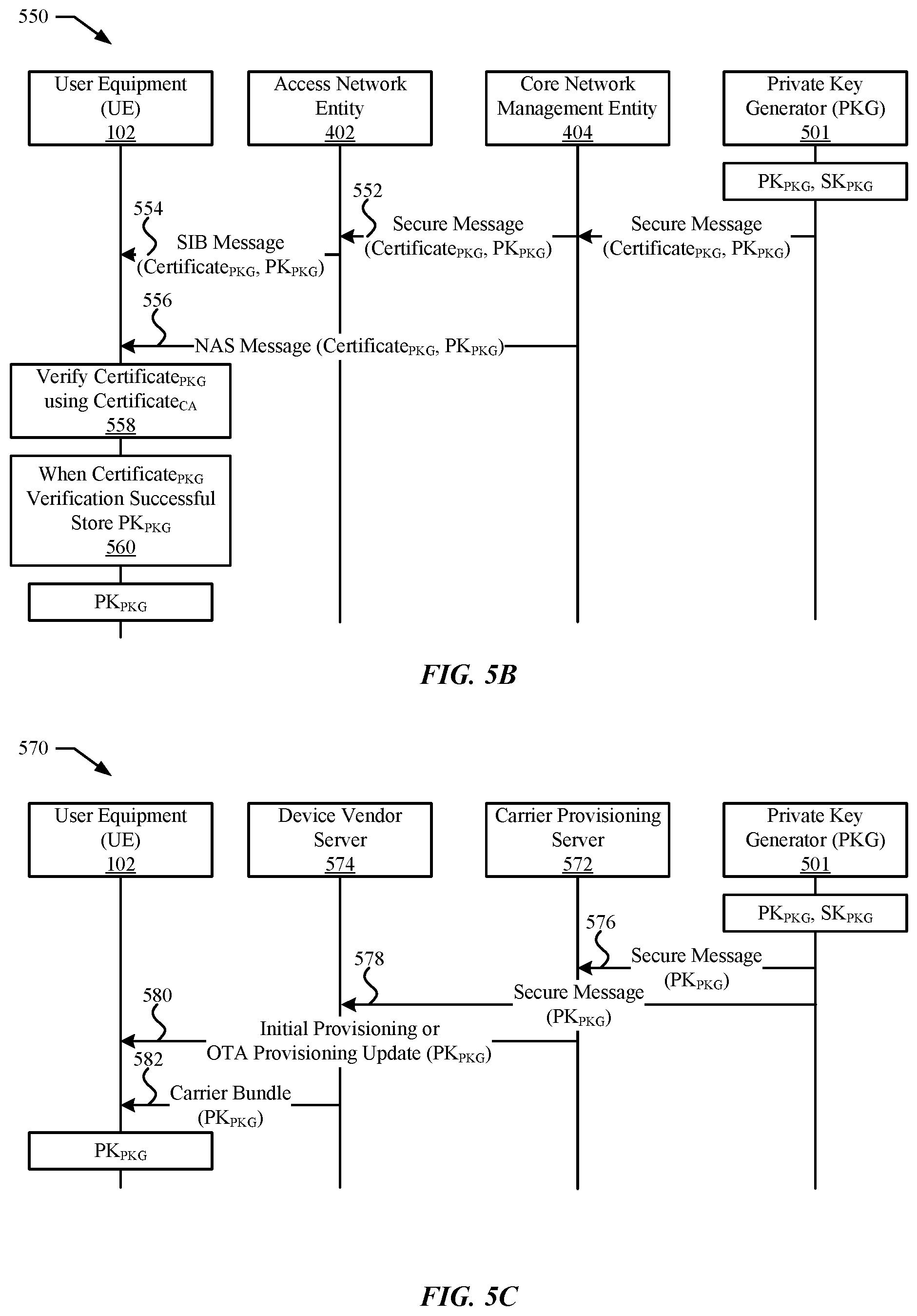
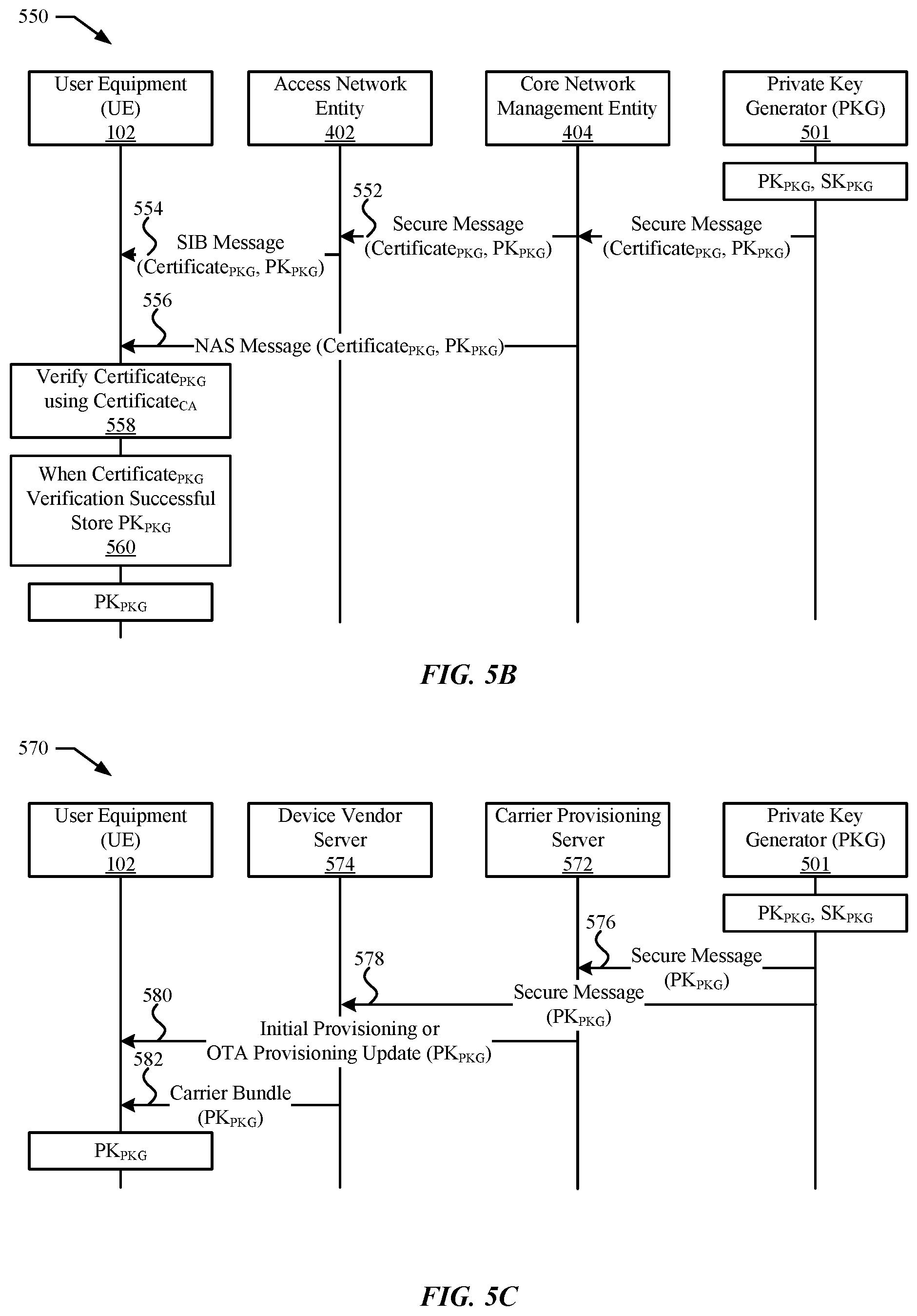
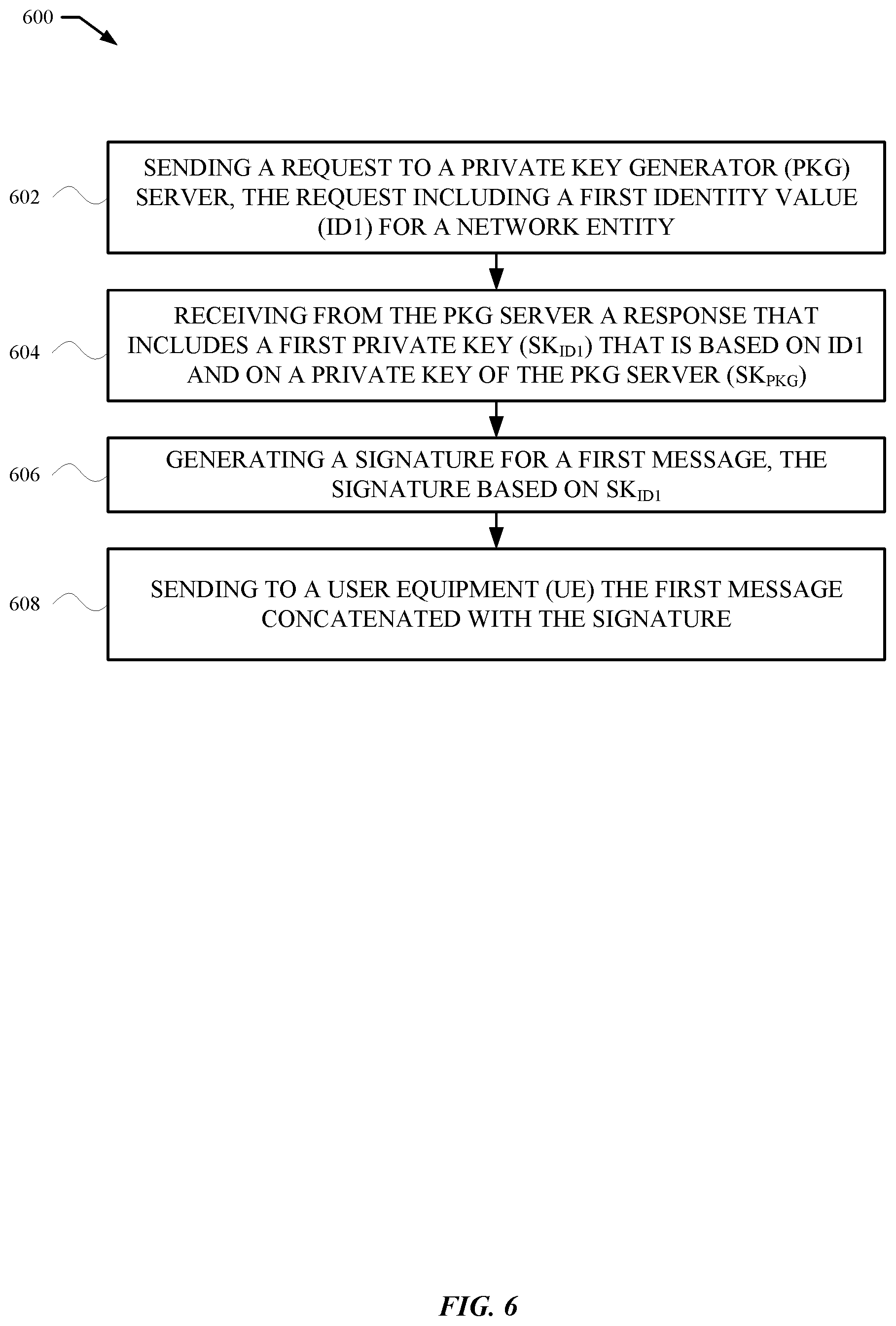
[0014] FIGS. 5B and 5C illustrate exemplary distribution mechanisms for providing a public key of the private key generator server to a wireless device, according to some embodiments.
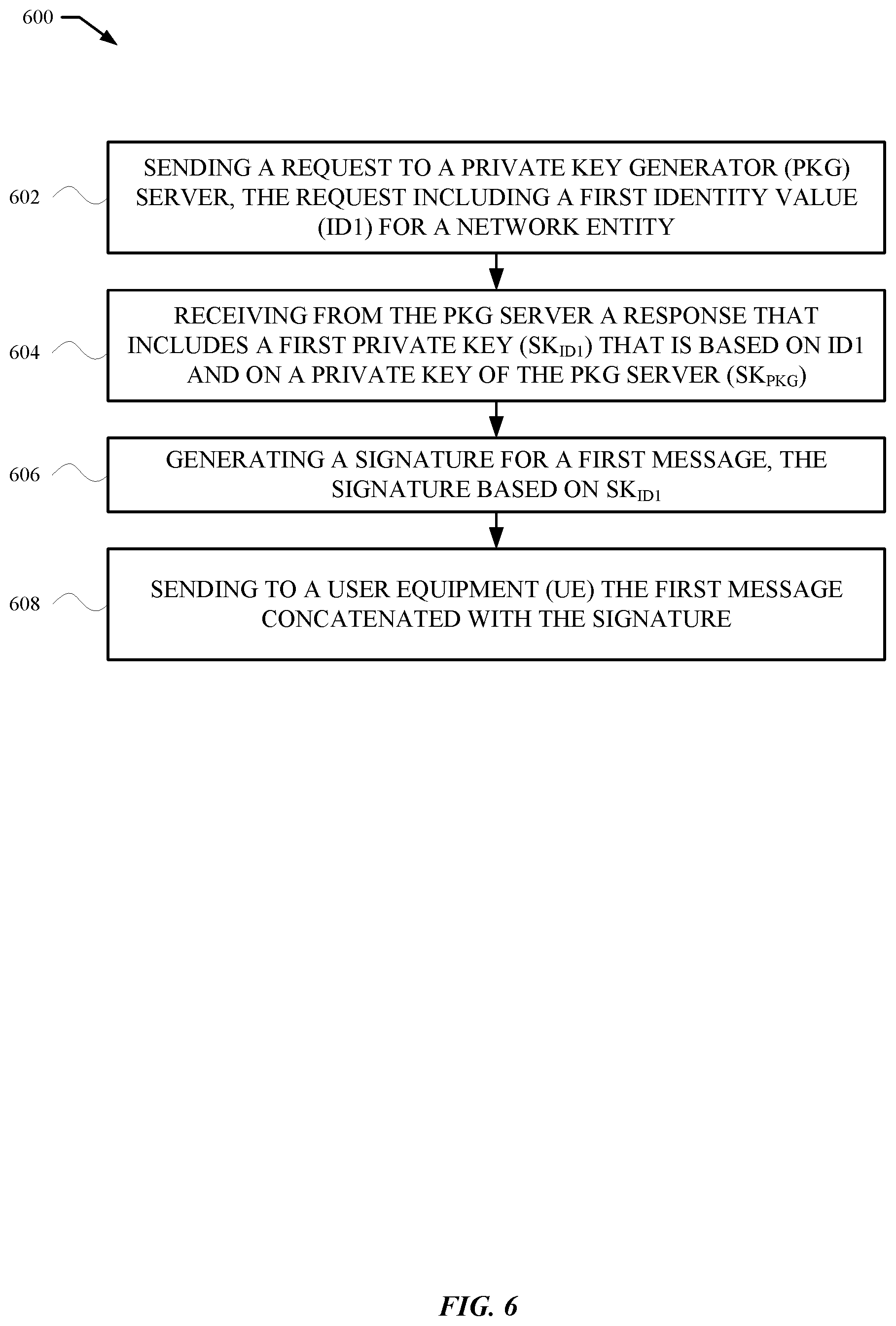
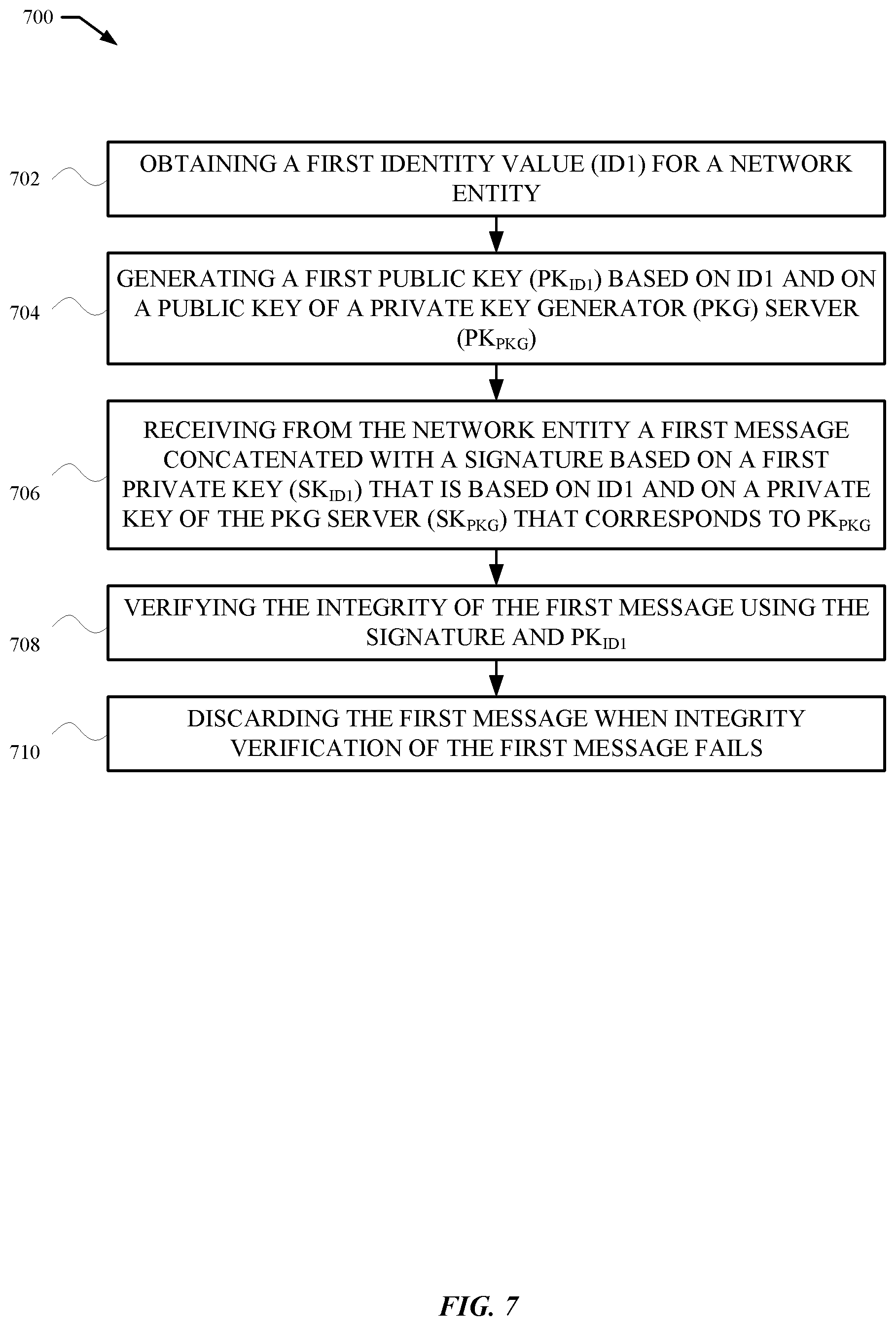
[0015] FIG. 6 illustrates a flow diagram of an exemplary sequence of actions by a network entity to protect the integrity of a message communicated to a wireless device, according to some embodiments.
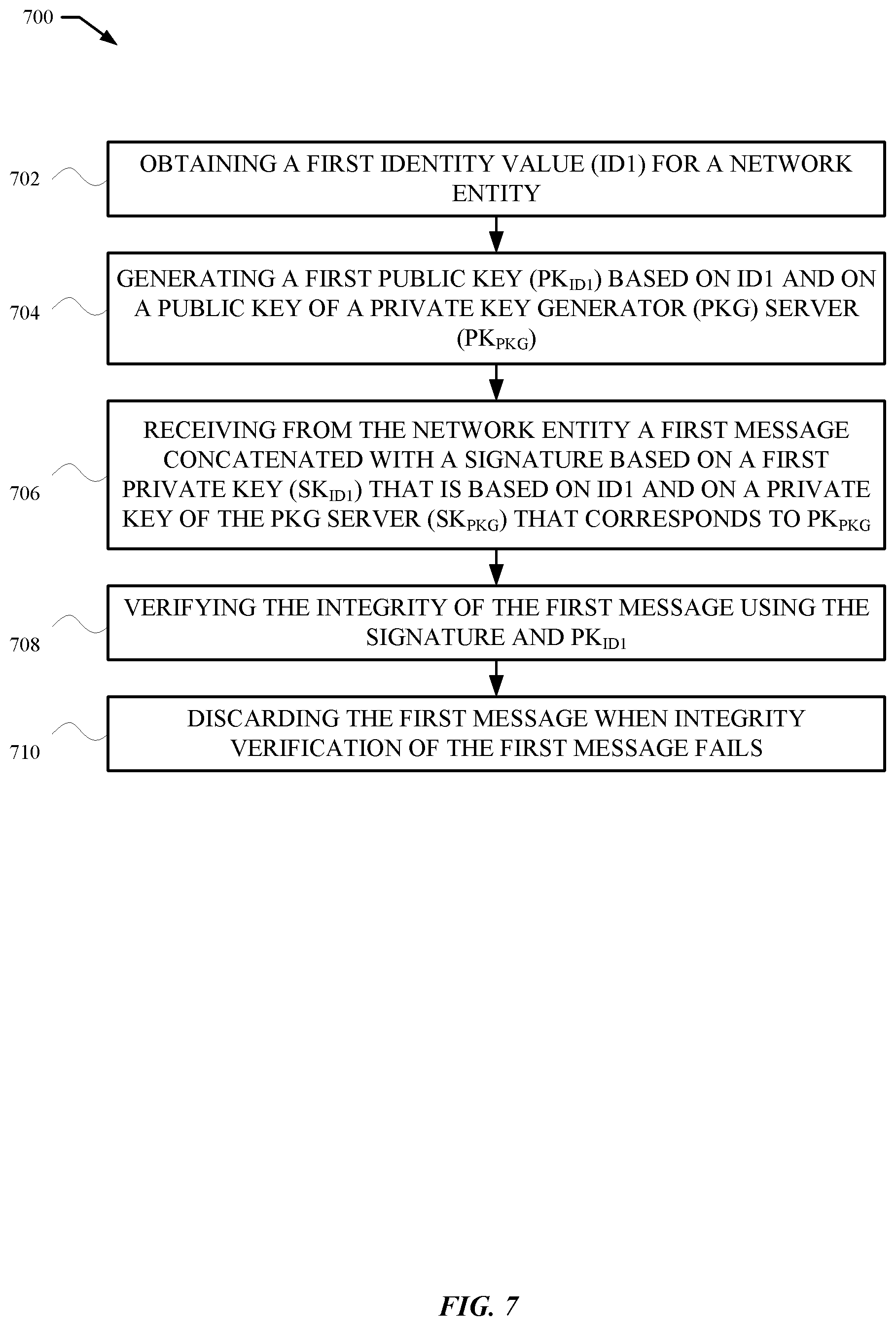
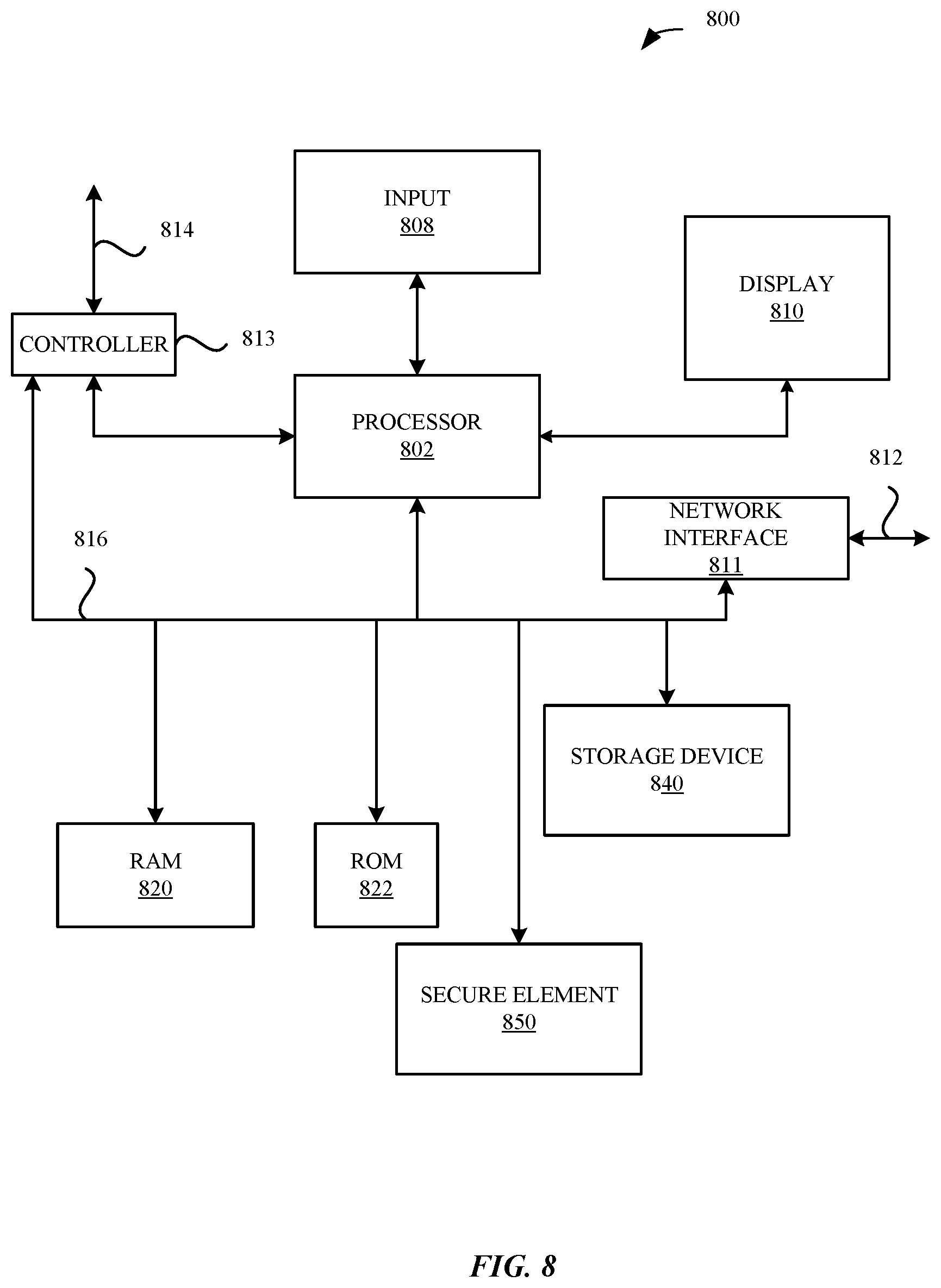
[0016] FIG. 7 illustrates a flow diagram of an exemplary sequence of actions by a wireless device to verify integrity of a message received from a network entity, according to some embodiments.
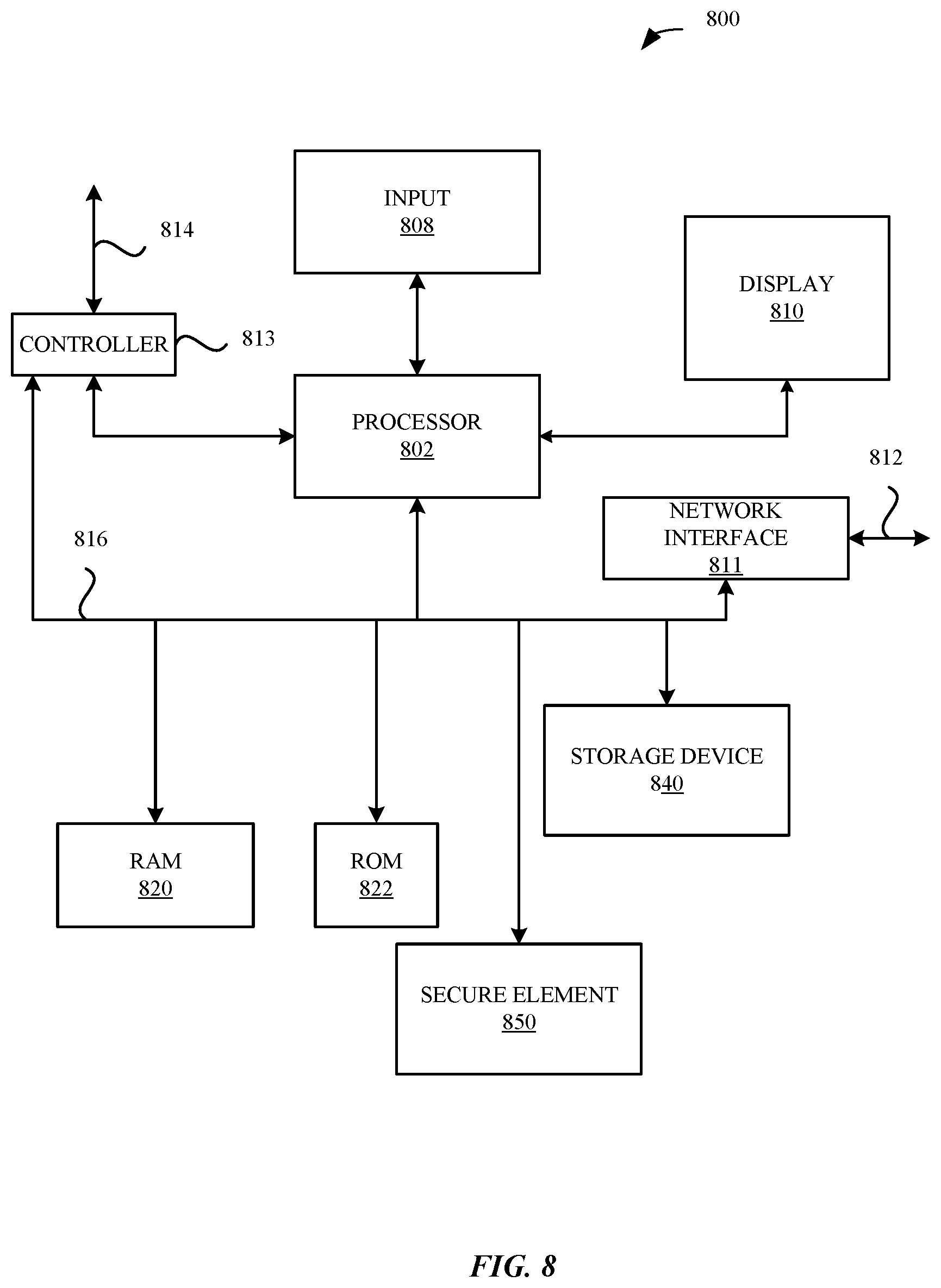
[0017] FIG. 8 illustrates a detailed view of a representative computing device that can be used to implement various methods described herein, according to some embodiments.
DETAILED DESCRIPTION
[0018] Representative applications of apparatuses and methods according to the presently described embodiments are provided in this section. These examples are being provided solely to add context and aid in the understanding of the described embodiments. It will thus be apparent to one skilled in the art that the presently described embodiments can be practiced without some or all of these specific details. In other instances, well known process steps have not been described in detail in order to avoid unnecessarily obscuring the presently described embodiments. Other applications are possible, such that the following examples should not be taken as limiting.
[0019] Representative embodiments described herein set forth techniques for identity-based message integrity protection and verification when communicating messages between a wireless device, e.g., a user equipment (UE), and a wireless network entity, including use of signatures derived from identity-based keys for message integrity protection by a sending network entity and for message integrity verification by the receiving wireless device. Identity-based signatures are included with at least some messages provided by an access network entity, e.g., a NodeB (NB), evolved NodeB (eNB), next generation NodeB (gNB), or femto-cell home equivalents, to a wireless device before establishment of a security context between the access network entity and the wireless device. The security context at the access stratum (AS) level includes a set of ciphering keys used for encryption and decryption of message content and a set of message integrity keys for the protection and verification of messages from an AS level network entity. Similarly, the security context at the non-access stratum (NAS) level includes an additional set of ciphering keys used for encryption and decryption of signaling message content and an additional set of message integrity keys for the protection and verification of the signaling messages from a NAS level network entity. Separate ciphering keys can be used for signaling messages in the control plane and for data messages in the user plane, while keys for message integrity can be used for signaling messages in the control plane. Before these keys are established, signaling messages from an access network entity and/or from a core network entity can be sent unencrypted and/or without integrity verification signatures and thus be vulnerable to manipulation by a rogue network entity.
[0020] To protect against attacks from rogue network entities, e.g., fake base stations, before activation of the security context with a network entity of a wireless network, the UE verifies integrity of at least some messages received from the network entity by checking a signature of a received message using an identity-based public key PK.sub.ID derived by the UE. The public key PK.sub.ID is generated using (i) an identity value (ID) of the network entity that sent the message and (ii) a separate public key PK.sub.PKG of a public/private key pair maintained by a trusted third-party entity, namely a private key generator (PKG) server. All or a portion of the ID value of the network entity can be provided in a message to the UE, such as in a message broadcast by the network entity. In some embodiments, a portion of the ID value of the network entity may be obtained by the UE from storage in the UE and/or from a network accessible storage. In some embodiments, a portion of the ID value of the network entity may also be assembled by the UE, such as a time-based value. The public key PK.sub.PKG of the PKG server can be provided to the UE before the UE attempts to camp on and/or connect the wireless network of the network entity, such as during subscriber identity module (SIM) provisioning from a mobile network operator (MNO) server, during carrier bundle provisioning from a third-party server, during device manufacture, during device sales distribution, and/or by querying the PKG server directly for the public key PK.sub.PKG. The public key PK.sub.PKG of the PKG server can also be broadcast to the UE by network entities in various access stratum (AS) system information block (SIB) messages and/or in various non-access stratum (NAS) messages. The messages can include the PK.sub.PKG along with a certificate that the UE can verify based on a certificate authority (CA) certificate that the UE and the PKG server have in common. Representative network entities that can communicate the PK.sub.PKG to the UE include those that provide the PKG server function and/or interface therewith. as those that provide the PKG server function or interface therewith. The UE can derive the identity-based public key PK.sub.ID by combining the PKG server's public key PK.sub.PKG and the identity value ID of the network entity using an algorithm known by the UE. The network entity generates signatures for one or more messages using an identity-based private key SK.sub.ID that corresponds to the identity-based public key PK.sub.ID. The identity-based private key SK.sub.ID is obtained by the network entity from the PKG server, which generates the identity-based private key SK.sub.ID using (i) the ID value of the network entity and (ii) a private key SK.sub.PKG that is known only by the PKG server and corresponds to the public key PK.sub.PKG. The private key SK.sub.PKG used to generate the identity-based private key SK.sub.ID is kept secret by the PKG server. An updated identity-based private key SK.sub.ID can be obtained by the network entity by subsequently providing an updated identity value ID to the PKG server and receiving an updated SK.sub.ID in return. Communication between the network entity and the PKG server can be through a secure connection.
[0021] The UE obtains the ID value of the network entity based on one or more messages received from the network entity that include at least a portion of the ID value, such as a broadcast message that includes one or more of: a public land mobile network (PLMN) ID value, a next generation Node B (gNB) globally unique ID value, or a tracking area code (TAC) value. The ID value of the network entity can also include a time stamp that limits a time period during which the ID value is valid. Changes to the ID value of the network entity, such as an updated time stamp value, requires the network entity to obtain from the PKG server an updated private key SK.sub.ID based on the updated ID value. The UE also derives updated public key PK.sub.ID values based on updated ID values as required. Signatures generated by the network entity and based on the private key SK.sub.ID are appended to one or more messages transmitted by the network entity to provide integrity protection for the messages. Representative message can include broadcast messages, multicast messages, and/or unicast messages. The UE verifies integrity of messages received from the network entity by checking the signature included with the message using the applicable public key PK.sub.ID for the network entity. Messages from a network entity for which message integrity cannot be verified using the public key PK.sub.ID derived from the identity value ID of the network entity can be ignored and/or discarded by the UE. In some embodiments, the signature is a full signature generated by the network entity using the private key SK.sub.ID as a signing key. In some embodiments, the signature is a partial, e.g., truncated, signature derived from the full signature. In some embodiments, the signature is a message authentication code (MAC) value that is calculated using a symmetric MAC key derived using a key derivation function (KDF) based on the private key SK.sub.ID.
[0022] The UE can determine whether a network entity of a wireless network uses ID-based signature protection and verification of one or more messages based on an indication of network properties, such as a key or flag, that is included with a SIM profile provided during SIM provisioning by an MNO server and/or in a carrier configuration bundle provided by a third party server. In some embodiments, one or more system information block (SIB) messages can be integrity protected by including a signature signed by the network entity that broadcasts the SIB messages. In some embodiments, one or more public warning system (PWS) messages, such as an earthquake and tsunami warning system (ETWS) message, can be integrity protected by including a signature signed by the network entity that broadcasts the PWS message. In some embodiments, one or more unicast messages sent during a random access channel (RACH) procedure, such as a random access response (RAR) message, can be integrity protected by including a signature signed by the network entity that transmits the unicast message to the UE. In some embodiments, one or more radio resource control (RRC) signaling messages sent to the UE before activation of a security context between the UE and the network entity can be integrity protected by including a signature signed by the network entity that transmits the RRC signaling message to the UE. Representative RRC signaling messages that can be integrity protected include RRC configuration messages and RRC redirection messages, such as those messages used for a circuit-switched fallback (CSFB) procedure. In some embodiments, one or more NAS level messages communicated by a core network entity to the UE can be message integrity protected by including a signature signed by the network entity that generates the NAS level message. Representative core network entities include an access and mobility management function (AMF), a mobility management entity (MME), an authentication server function (AUSF), or home subscriber server (HSS). Message integrity protection can provide additional certainty to a UE for critical messages that request private information from a UE or redirect a UE. Representative messages generated upon failure of retrieval of a UE context can include such messages as identity request messages or attach reject messages. Representative identity request messages include those that request the UE provide an unencrypted identifier, e.g., an international mobile subscriber identity (IMSI) or a subscription permanent identifier (SUPI). As NAS messages are embedded within RRC messages, in various embodiments, the embedded NAS message may include a signature, the encompassing RRC message may include a signature, or both the NAS and RRC messages may each include a signature.
[0023] To protect against fraudulent misuse of a network entity that may be vulnerable to hacking, the private key SK.sub.ID provided to the network entity can be restricted to be used only during a finite time period that is specified in the ID value used to generate the private key SK.sub.ID. The network entity can obtain a new private key SK.sub.ID for each finite time period. In some embodiments, the ID value includes a field that specifies a time period for which the ID value and the resulting private key SK.sub.ID are valid. For example, the ID value can include a field having a string value such as "YYYY|MM|WW" to indicate a specific year, month, and week during which the ID value and private key SK.sub.ID are valid. In some embodiments, the PKG server can determine whether to provide an updated private key SK.sub.ID to a network entity based on the ID value submitted to the PKG server. In some embodiments, the PKG server can deny providing an updated private key SK.sub.ID to a network entity, such as responsive to a report that the network entity has been compromised. In some embodiments, the ID value can include a field that indicates a particular type of operation for the network entity, e.g., a field having a string value that contains "CSG" as an indication that the network entity is intended for connections with a closed subscriber group (CSG). As such, the network entity that includes a CSG value cannot be changed to operate as a public cell, rather than as a private femto-cell as intended by the MNO with which the femto-cell is associated. A UE can recognize a network entity as a private femto-cell based on the presence of the CSG value in the network entity's ID and can avoid communicating private information or following redirection commands that may indicate the network entity is masquerading as a public cell. Redirection commands can include directing a UE to move to a circuit-switched network as part of a CSFB procedure. Requests for private information, such as for an IMSI/SUPI, can occur during error handling procedures when a core network entity fails to retrieve a UE context.
[0024] In accordance with various embodiments described herein, the terms "wireless communication device," "wireless device," "mobile device," "mobile station," and "user equipment" (UE) may be used interchangeably herein to describe one or more common consumer electronic devices that may be capable of performing procedures associated with various embodiments of the disclosure. In accordance with various implementations, any one of these consumer electronic devices may relate to: a cellular phone or a smart phone, a tablet computer, a laptop computer, a notebook computer, a personal computer, a netbook computer, a media player device, an electronic book device, a MiFi.RTM. device, a wearable computing device, as well as any other type of electronic computing device having wireless communication capability that can include communication via one or more wireless communication protocols such as used for communication on: a wireless wide area network (WWAN), a wireless metro area network (WMAN) a wireless local area network (WLAN), a wireless personal area network (WPAN), a near field communication (NFC), a cellular wireless network, a fourth generation (4G) Long Term Evolution (LTE), LTE Advanced (LTE-A), and/or fifth generation (5G) or other present or future developed advanced cellular wireless networks.
[0025] The wireless communication device, in some embodiments, can also operate as part of a wireless communication system, which can include a set of client devices, which can also be referred to as stations, client wireless devices, or client wireless communication devices, interconnected to an access point (AP), e.g., as part of a WLAN, and/or to each other, e.g., as part of a WPAN and/or an "ad hoc" wireless network. In some embodiments, the client device can be any wireless communication device that is capable of communicating via a WLAN technology, e.g., in accordance with a wireless local area network communication protocol. In some embodiments, the WLAN technology can include a Wi-Fi (or more generically a WLAN) wireless communication subsystem or radio, the Wi-Fi radio can implement an Institute of Electrical and Electronics Engineers (IEEE) 802.11 technology, such as one or more of: IEEE 802.11a; IEEE 802.11b; IEEE 802.11g; IEEE 802.11-2007; IEEE 802.11n; IEEE 802.11-2012; IEEE 802.11ac; or other present or future developed IEEE 802.11 technologies.
[0026] Additionally, it should be understood that some UEs described herein may be configured as multi-mode wireless communication devices that are also capable of communicating via different third generation (3G) and/or second generation (2G) RATs. In these scenarios, a multi-mode user equipment (UE) can be configured to prefer attachment to LTE networks offering faster data rate throughput, as compared to other 3G legacy networks offering lower data rate throughputs. For instance, in some implementations, a multi-mode UE may be configured to fall back to a 3G legacy network, e.g., an Evolved High Speed Packet Access (HSPA+) network or a Code Division Multiple Access (CDMA) 2000 Evolution-Data Only (EV-DO) network, when LTE and LTE-A networks are otherwise unavailable.
[0027] These and other embodiments are discussed below with reference to FIGS. 1 through 8; however, those skilled in the art will readily appreciate that the detailed description given herein with respect to these figures is for explanatory purposes only and should not be construed as limiting.
[0028] FIG. 1 illustrates a block diagram of different components of a system 100 that is configured to implement the various techniques described herein, according to some embodiments. More specifically, FIG. 1 illustrates a high-level overview of the system 100, which, as shown, includes a user equipment (UE) 102, a group of base stations 112-1 to 112-n that are managed by different Mobile Network Operators (MNOs) 114, and a set of provisioning servers 116 that are in communication with the MNOs 114. The UE 102 can represent a mobile computing device (e.g., an iPhone.RTM. or an iPad.RTM. by Apple.RTM.), the base stations 112-1 to 112-n can represent cellular wireless network entities including evolved NodeBs (eNBs) and/or next generation NodeBs (gNBs or gNB) that are configured to communicate with the UE 102, and the MNOs 114 can represent different wireless service providers that provide specific services (e.g., voice and data) to which the UE 102 can be subscribed.
[0029] As shown in FIG. 1, the UE 102 can include processing circuitry, which can include a processor 104 and a memory 106, an embedded Universal Integrated Circuit Card (eUICC) 108, and a baseband component 110. In some embodiments, the UE 102 includes one or more physical Subscriber Identity Module (SIM) cards (not shown) in addition to or substituting for the eUICC. The components of the UE 102 work in conjunction to enable the UE 102 to provide useful features to a user of the UE 102, such as localized computing, location-based services, and Internet connectivity. The eUICC 108 can be configured to store multiple electronic SIMs (eSIMs) for accessing different MNOs 114 through the base stations 112-1 to 112-n. For example, the eUICC 108 can be configured to store and manage one or more eSIMs for one or more MNOs 114 for different subscriptions to which the UE 102 is associated. To be able to access services provided by the MNOs, an eSIM can be provisioned to the eUICC 108. In some embodiments, the eUICC 108 obtains one or more eSIMs (or updates for one or more eSIMs) from one or more associated provisioning servers 116. It is noted that provisioning servers 116 can be maintained by a manufacturer of the UE 102, the MNOs 114, third party entities, and the like. Communication of eSIM data between a provisioning server 116 and the eUICC 108 (or between the provisioning server 116 and processing circuitry of the UE 102 external to the eUICC 108, e.g., the processor 104) can use a secure communication channel.
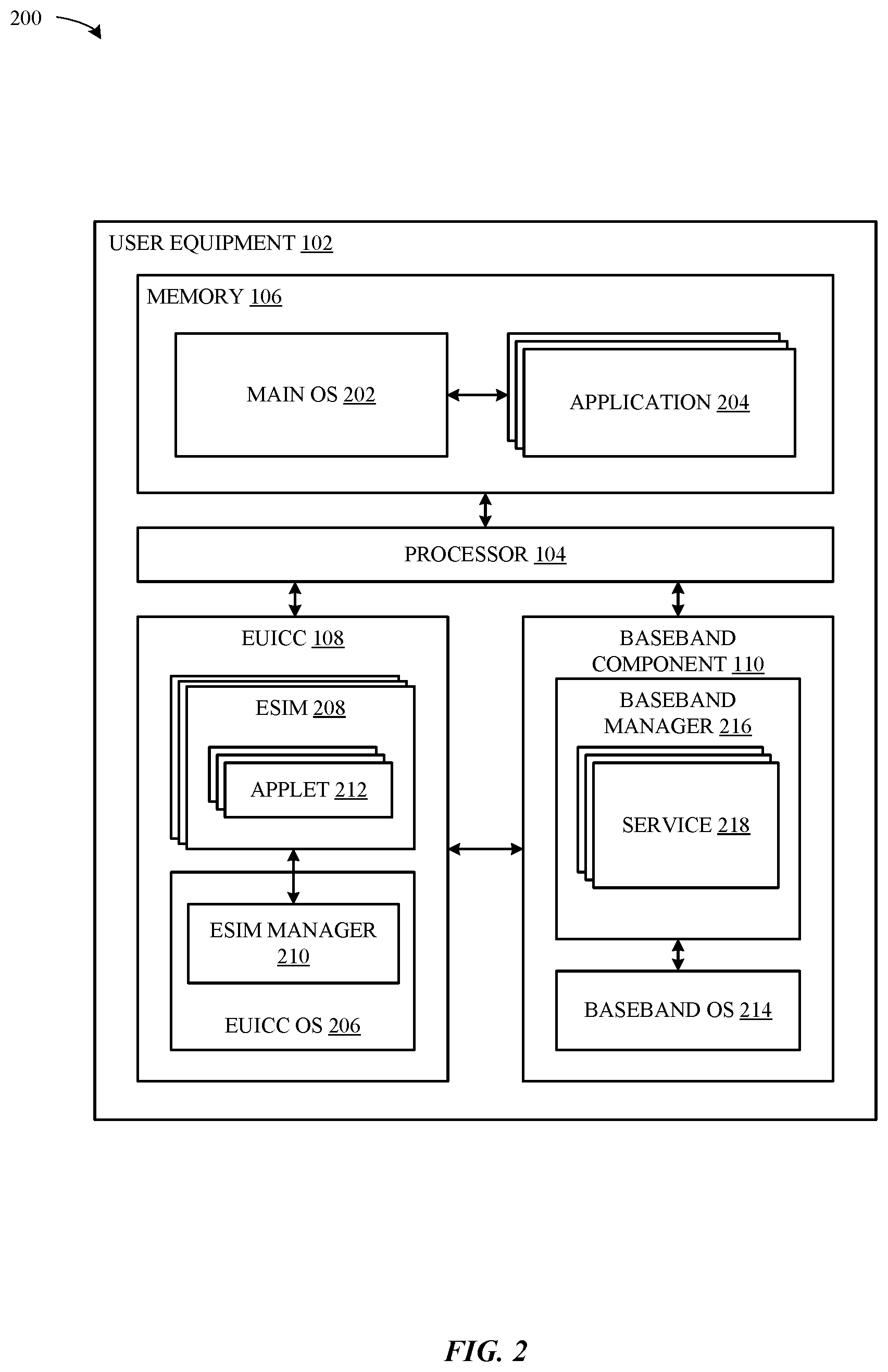
[0030] FIG. 2 illustrates a block diagram of a more detailed view 200 of particular components of the UE 102 of FIG. 1, according to some embodiments. As shown in FIG. 2, the processor 104, in conjunction with the memory 106, can implement a main operating system (OS) 202 that is configured to execute applications 204 (e.g., native OS applications and user applications). As also shown in FIG. 2, the eUICC 108 can be configured to implement an eUICC OS 206 that is configured to manage the hardware resources of the eUICC 108 (e.g., a processor and a memory embedded in the eUICC 108). The eUICC OS 206 can also be configured to manage eSIMs 208 that are stored by the eUICC 108, e.g., by enabling, disabling, modifying, or otherwise performing management of the eSIMs 208 within the eUICC 108 and providing the baseband component 110 with access to the eSIMs 208 to provide access to wireless services for the UE 102. The eUICC 108 OS can include an eSIM manager 210, which can perform management functions for various eSIMs. According to the illustration shown in FIG. 2, each eSIM 208 can include a number of applets 212 that define the manner in which the eSIM 208 operates. For example, one or more of the applets 212, when implemented by the baseband component 110 and the eUICC 108, can be configured to enable the UE 102 to communicate with an MNO 114 and provide useful features (e.g., phone calls and internet) to a user of the UE 102.
[0031] As also shown in FIG. 2, the baseband component 110 of the UE 102 can include a baseband OS 214 that is configured to manage hardware resources of the baseband component 110 (e.g., a processor, a memory, different radio components, etc.). According to some embodiments, the baseband component 110 can implement a baseband manager 216 that is configured to interface with the eUICC 108 to establish a secure channel with a provisioning server 116 and obtaining information (such as eSIM data) from the provisioning server 116 for purposes of managing eSIMs 208. The baseband manager 216 can be configured to implement services 218, which represents a collection of software modules that are instantiated by way of the various applets 212 of enabled eSIMs 208 that are included in the eUICC 108. For example, services 218 can be configured to manage different connections between the UE 102 and MNOs 114 according to the different eSIMs 208 that are enabled within the eUICC 108.
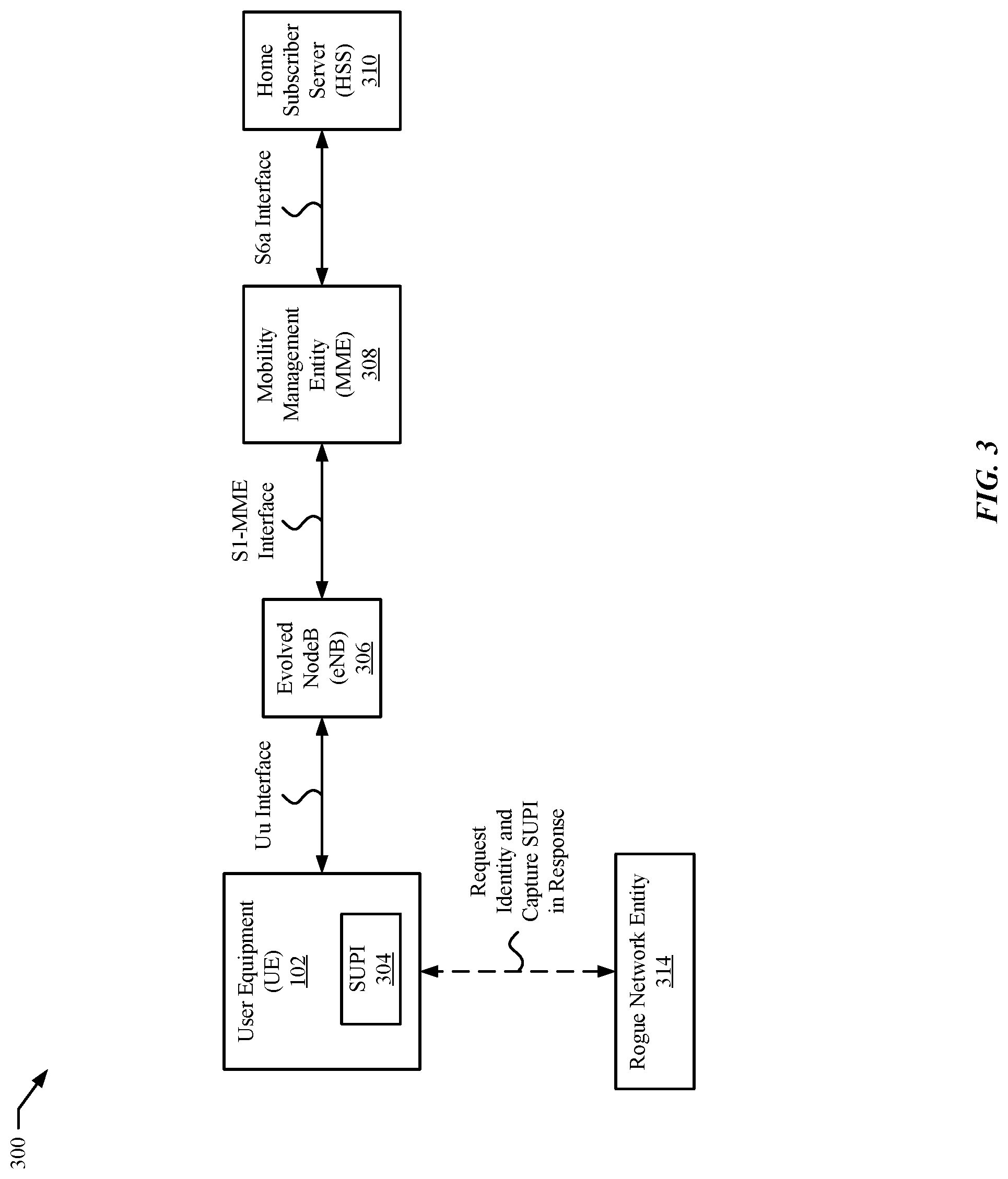
[0032] FIG. 3 illustrates a block diagram 300 of an exemplary system subject to attack by a rogue network entity. The system includes a UE 102, which includes private information, such as an unencrypted subscription permanent identifier (SUPI) 304 by which a subscription for a user of the UE 102 can be uniquely identified, in communication with an exemplary genuine cellular wireless network entity, namely an evolved NodeB (eNB) 306. An example of a SUPI 304 includes an international mobile subscriber identity (IMSI). The UE 102 and the eNB 306 can communicate via a Uu interface, which for some messages or for certain periods of time, such as prior to establishment of a secure connection between the UE 102 and the eNB 306, can be subject to eavesdropping by a third party, such as by the rogue network entity 314. While the eNB 306 connects to a Mobility Management Entity (MME) 308 of the core network via a secure S1-MME interface, and the MME 308 connects to a Home Subscriber Server (HSS) 310 via a secure S6a interface, the eNB 306 can send some messages to and receive some messages from the UE 102 "in the clear". The rogue network entity 314 can mimic communication from a genuine wireless network entity, such as from the eNB 306 and/or from the MME 308, and can request that the UE 102 provide information that should only be sent to a genuine wireless network entity. For example, the rogue network entity 314 can send a Request Identity message to the UE 102, which can unknowingly respond to the rogue network entity 314 with an Identity Response message that includes the unencrypted SUPI 304 of the UE 102.
[0033] The Uu interface between the UE 102 and the eNB 306 is also vulnerable to attacks in which the rogue network entity 314 seeks to extract information from the UE 102 and/or to misdirect the UE 102 to lower its security. Exemplary attacks include the rogue network entity 314 sending a radio resource control (RRC) redirection command as part of a CSFB procedure to cause the UE 102 to move to a fake base station (not shown) that imitates a wireless network that does not have advanced security measures, e.g., from a 4G/5G network e/gNB to a 2G/3G network. The rogue network entity 314 can also manipulate the UE 102 to obtain private information by re-appropriating error handling mechanisms, e.g., by requesting that the UE send its SUPI/IMSI as a result of a fictitious UE context retrieval failure. Until a security context is established for access stratum (AS) communication between the UE 102 and the eNB 306 (or equivalently gNB) and for non-access stratum (NAS) communication, messages received by the UE 102 may be suspect and subject to misuse without a mechanism to verify message integrity. While FIG. 3 illustrates the UE 102 connected to the eNB 306 of an LTE network, a similar architecture for a fifth generation (5G) in which the UE 102 communicates through a next generation NodeB (gNB) is also subject to eavesdropping before a security context is established between the UE 102 and network entities of the wireless network.
[0034] The techniques presented herein can apply to any messages communicated between the UE 102 and a cellular wireless network entity, including over insecure connections susceptible to eavesdropping. Examples of a wireless network entity include a radio access network entity, such as the eNB 306 or a next generation NodeB (also referred to as a gNodeB or gNB), or a core network entity, such as the MME 308, the HSS 310, an authentication server function (AUSF), or an access and mobility management function (AMF). As described further herein, the UE 102 can verify one or more messages that include identity-based signatures received from a network entity, including an access network entity such as an eNB 306 or gNB.
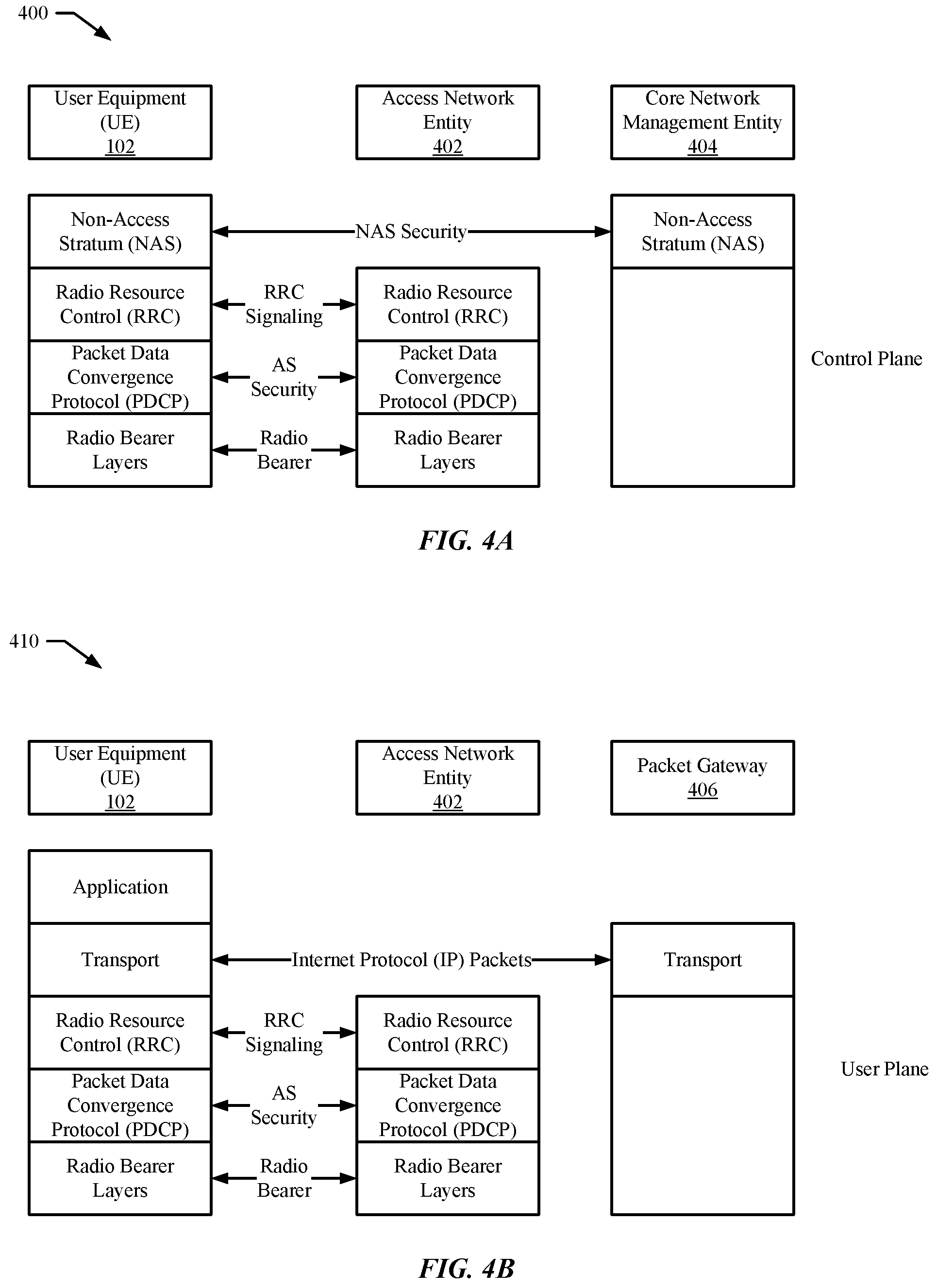
[0035] FIGS. 4A and 4B illustrate diagrams 400/410 of communication protocol stacks that include message security for signaling messages and data packets after establishment of a security context between a wireless device and network entities of a wireless network. During an authentication and key agreement (AKA) procedure, the UE 102 can establish a security key, e.g., an encryption/decryption key, for communication between the UE 102 and a core network management entity 404, e.g., the mobility management entity (MME) 308 of an LTE network or an equivalent AMF of a 5G network. Using a key derivation function (KDF) for an identified encryption algorithm, the UE 102 can derive from the security key obtained as part of the AKA procedure a NAS encryption/decryption key to use for encrypting and decrypting NAS messages communicated between the core network management entity 404 and the UE 102 in the control plane. Similarly, using the KDF for an identified integrity algorithm, the UE 102 can derive a NAS integrity key to use for verifying the integrity of messages received from the core network management entity 404 via the control plane. The NAS encryption/decryption key and NAS integrity key are used to protect NAS level messages. Additionally, using the KDF for another identified encryption algorithm, the UE 102 can derive an AS encryption/decryption key to use for encrypting and decrypting AS signaling messages communicated between an access network entity 402 and the UE 102. Furthermore, the UE 102 can derive an AS integrity key to use for verifying the integrity of signaling messages received from the access network entity 402. RRC signaling messages can be encrypted and decrypted and integrity protected and verified at a packet data convergence protocol (PDCP) layer before being provided to and after being received from radio bearer layers that transport the RRC signaling messages via radio bearers. The AS encryption/decryption key and AS integrity key are used to protect AS level signaling messages in the control plane. Data messages communicated via the user plane can also be encrypted and decrypted using an additional AS encryption/decryption key to protect Internet Protocol (IP) packets communicated via the transport layer between the UE 102 and an applicable data gateway, e.g., a packet gateway 406. The combination of NAS keys and AS keys provide a complete security context for communication between the UE 102 and network entities of the wireless network. Prior to establishment of these NAS and AS keys, one or more signaling messages may be subject to eavesdropping and/or misuse by a rogue network entity. Protecting at least some of such signaling messages can be accomplished as described further herein using ID-based signatures that accompany the signaling messages, where the ID-based signatures are generated using a private key obtained by the network entity from a trusted private key generator (PKG) server over a secure connection. The rogue network entity will not have access to the private key of a genuine network entity. The private key is based on an ID of the network entity and also based on a private key of the PKG server that remains secret and is not shared by the PKG server with the network entity. The UE 102 can verify integrity of a message by checking an accompanying signature using a public key that corresponds to the private key of the network entity. The UE 102 can derive the public key of the network entity using the ID of the network entity and a public key of the PKG server that corresponds to the secret, unshared, private key of the PKG server. Signaling messages, once verified, can be trusted by the UE 102, and signaling messages that cannot be verified, can be treated as suspect and ignored and/or discarded by the UE 102.
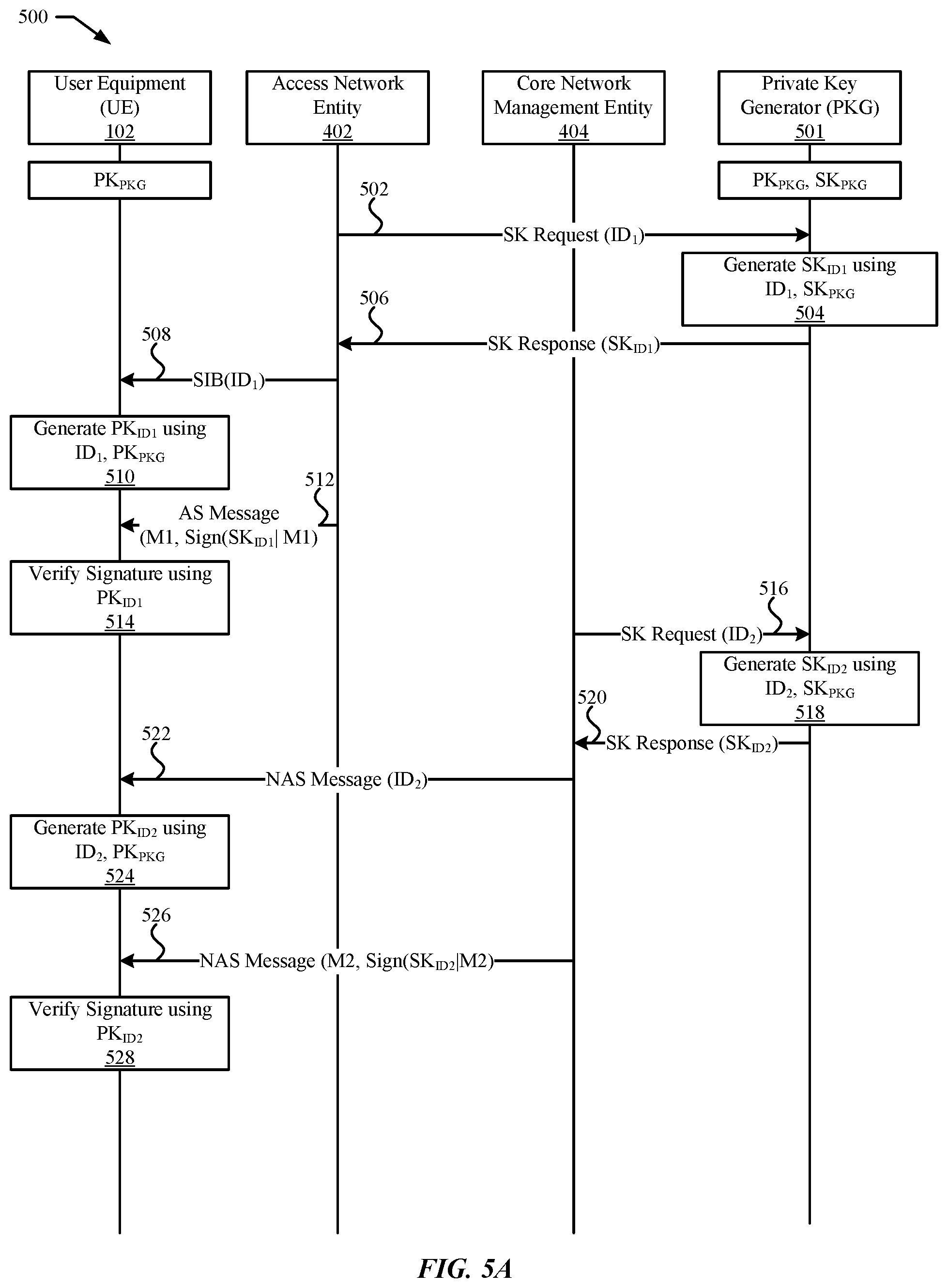
[0036] FIG. 5A illustrates a diagram 500 of an exemplary message exchange using identity-based message integrity protection and verification. Any network entity in the access network or in the core network of a cellular wireless network can apply identity-based message integrity protection for communication to the UE 102 to verify by obtaining a private key that corresponds to their identity from a private key generator (PKG) server. Initially, the UE 102 can be configured with a public key PK.sub.PKG of the PKG server 501, while the PKG server 502 can be configured with the public key PK.sub.PKG and a corresponding private key SK.sub.PKG. In order to provide message integrity protection for access stratum (AS) level signaling messages communicated by the access network entity 402 to the UE 102, the access network entity 402 interact with the PKG server 501 to obtain a ID-based private key with which to generate signatures to accompany the messages. At 502, the access network entity 402 can send to the PKG server 501 a request for a private key, e.g., SK Request(ID.sub.1) based on an ID value, e.g., ID.sub.1, of the access network entity 402. At 504, the PKG server 501 generates the private key SK.sub.ID1 using the received identity value ID1 of the access network entity 402 and also using a private key of the PKG server 501, namely SK.sub.PKG. At 506, the PKG server 501 sends to the access network entity 402 a response that includes the private key, e.g., SK Response(SK.sub.ID1). At 508, the access network entity 402 provides its ID value ID1 to the UE 102, e.g., broadcast in a system information block (SIB) message. At 510, the UE 102 generates a public key PK.sub.ID1 for the access network entity 402 using the ID value ID1 and the public key PK.sub.PKG of the PKG server 501. At 512, the access network entity 402 sends an access stratum (AS) signaling message to the UE 102 that includes message content M1 and a signature Sign(SK.sub.ID1|M1) that is generated for the message content M1 using the private key SK.sub.ID1. At 514, the UE 102 verifies the signature of the AS signaling message using the public key PK.sub.ID1. When the signature is verified, the UE 102 can determine that the AS signaling message can be trusted. When the signature does not verify, the UE 102 can treat the AS signaling message as suspect and act accordingly, e.g., ignore and/or discard the AS signaling message. The access network entity 402 can include an NB, eNB, gNB, or femto-cell (home-based) equivalent.
[0037] A core network management entity 404 can use the same mechanism to obtain a message integrity protection key from the PKG server 501 to use for protecting non-access stratum (NAS) level signaling messages as done by the access network entity 402 to protect AS level signaling messages. At 516, the core network management entity 404 can send to the PKG server 501 a request for a private key, e.g., SK Request(ID.sub.2) based on an ID value, e.g., ID.sub.2, of the core network management entity 404. At 518, the PKG server 501 generates the private key SK.sub.ID2 using the received identity value ID.sub.2 of the core network management entity 404 and also using the private key SK.sub.PKG of the PKG server 501. At 520, the PKG server 501 sends to the core network management entity 404 a response that includes the private key, e.g., SK Response(SK.sub.ID2). At 522, the core network management entity 404 provides its ID value ID.sub.2 to the UE 102, e.g., unicast to the UE 102 in a NAS level signaling message. At 524, the UE 102 generates a public key PK.sub.ID2 for the core network management entity 404 using the ID value ID.sub.2 and the public key PK.sub.PKG of the PKG server 501. At 526, the core network management entity 404 sends a NAS signaling message to the UE 102 that includes message content M2 and a signature Sign(SK.sub.ID2|M2) that is generated for the message content M2 using the private key SK.sub.ID2. At 528, the UE 102 verifies the signature of the NAS signaling message using the public key PK.sub.ID2. When the signature is verified, the UE 102 can determine that the NAS signaling message can be trusted. When the signature does not verify, the UE 102 can treat the NAS signaling message as suspect and act accordingly, e.g., ignore and/or discard the NAS signaling message. The core network management entity 404 can include an MME, AMF, AUSF, HSS, or another core network management function server. As NAS messages from the core network management entity 404 are communicated through the access network entity 402 and embedded within RRC messages provided by access network entity 402 to the UE 102, in various embodiments, the embedded NAS message may include a NAS signature, while the encompassing RRC message may include an AS signature.
[0038] To protect against fraudulent misuse of a network entity that may be vulnerable to hacking, the private keys SK.sub.ID1 and SK.sub.ID2 provided to the access network entity 402 and to the core network management entity 404 can be restricted to be used only during finite time periods specified in their respective ID values used to generate the private keys SK.sub.ID1 and SK.sub.ID2. The access network entity 402 can obtain a new private key SK.sub.ID1 for each finite time period. Similarly, the core network management entity 404 can obtain a new private key SK.sub.ID2. The time periods used for each network entity can vary. In some embodiments, an ID value includes a field that specifies a time period for which the ID value and the resulting private key SK.sub.ID are valid. For example, the ID value can include a field having a string value such as "YYYY|MM|WW" to indicate a specific year, month, and week during which the ID value and private key SK.sub.ID are valid.
[0039] In some embodiments, the PKG server 501 can determine whether to provide an updated private key SK.sub.ID to a network entity based on the ID value submitted to the PKG server 501. In some embodiments, the PKG server can deny providing an updated private key SK.sub.ID to a network entity, such as responsive to a report that the network entity has been compromised. In some embodiments, the ID value can include a field that indicates a particular type of operation for a network entity, e.g., a field having a string value that contains "CSG" as an indication that an access network entity is intended for connections with a closed subscriber group (CSG). As such, the access network entity that includes a CSG value cannot be changed to operate as a public cell, rather than as a private femto-cell as intended by the MNO with which the femto-cell is associated. The UE 102 can recognize an access network entity as a private femto-cell based on the presence of the CSG value in the access network entity's ID and can avoid communicating private information or following redirection commands that may indicate the access network entity is masquerading as a public cell. Representative redirection commands include directing a UE to move to a circuit-switched network as part of a CSFB procedure. Representative requests for private information, such as for an IMSI/SUPI, can include commands that occur during error handling procedures when a core network entity fails to retrieve a UE context.
[0040] FIGS. 5B and 5C illustrate diagrams 550 and 570 of exemplary distribution mechanisms for providing a public key of the private key generator server 501, e.g., PK.sub.PKG, to a wireless device, e.g., UE 102. The public key PK.sub.PKG of the PKG server 501 can be provided to the UE 102 before the UE 102 attempts to camp on and/or connect to the wireless network of the network entity, such as during subscriber identity module (SIM) provisioning from a mobile network operator (MNO) server, during carrier bundle provisioning from a third-party server, during device manufacture, during device sales distribution, and/or by querying the PKG server 501 directly for the public key PK.sub.PKG. The public key PK.sub.PKG of the PKG server 501 can also be broadcast to the UE 102 by network entities, e.g., access network entity 402 and/or core network management entity 404, in various access stratum (AS) system information block (SIB) messages and/or in various non-access stratum (NAS) messages. The messages can include the PK.sub.PKG along with a certificate that the UE 102 can use to verify the sender of the message based on a certificate authority (CA) certificate that the UE 102 and the PKG server 501 have in common. Representative network entities that can communicate the PK.sub.PKG to the UE 102 include those that provide the PKG server 501 function and/or interface therewith.
[0041] As illustrated is diagram 550, the PKG server 501 can generate (or have previously generated) a public key PK.sub.PKG and private key SK.sub.PKG pair. As previously described, the PKG server 501 uses the private key SK.sub.PKG to generate private keys for a network entity based on an identifier of the network entity. The corresponding public key PK.sub.PKG is used by the UE 102 to generate a corresponding public key for the network entity in order to verify message signatures provided by the network entity, the message signatures generated using the network entity's private key. At 552, the PKG server 501 can communicate to a core network management entity 404 the public key PK.sub.PKG of the PKG server 501 in a secure message. At 552, the PKG server 501 can also communicate to the access network entity 402 directly (not shown) or via the core network management entity 404 the public key PK.sub.PKG of the PKG server 501 in a secure message. The secure message can include a copy of the public key PK.sub.PKG and a certificate of the PKG server 501, indicated as Certificate.sub.PKG. The core network management entity 404, in some embodiments, can verify the certificate of the PKG server using a certificate of a certificate authority (CA) that both the core network management entity 404 and the PKG server 501 have in common in order to trust the secure message that includes the public key PK.sub.PKG of the PKG server 501 communicated to the core network management entity 404. In some embodiments, the core network management entity 404 need not verify the certificate of the PKG server 501 in order to trust the secure message's contents received from the PKG server 501, as the secure message can be delivered via a secure connection to the core network management entity 404. Similarly, the access network entity 402, in some embodiments, can verify the certificate of the PKG server using a certificate of a certificate authority (CA) that both the access network entity 402 and the PKG server 501 have in common in order to trust the secure message that includes the public key PK.sub.PKG of the PKG server 501 communicated to the access network entity 402. In some embodiments, the access network entity 402 need not verify the certificate of the PKG server 501 in order to trust the secure message's contents received from the PKG server 501, as the secure message can be delivered via a secure connection to the access network entity 402. The PKG server 501 can communicate the public key PK.sub.PKG at regular intervals and/or on demand. The PKG server 501 can communicate updated values for the public key PK.sub.PKG when new versions of the PK.sub.PKG and SK.sub.PKG pair are created.
[0042] The access network entity 402 can communicate the certificate Certificate.sub.PKG and the public key PK.sub.PKG to the UE 102 in one or more system information block (SIB) messages as indicated at 554. To accommodate the size of the certificate Certificate.sub.PKG and the public key PK.sub.PKG, the SIB message can include sufficient space in the data payload. Multiple independent SIB messages can include the certificate Certificate.sub.PKG and the public key PK.sub.PKG, and the UE 102 can receive the certificate Certificate.sub.PKG and the public key PK.sub.PKG in any one of the multiple SIB messages used by the access network entity 402 to broadcast them. The core network management entity 404 can also communicate the certificate Certificate.sub.PKG and the public key PK.sub.PKG to the UE 102 in one or more different NAS messages as indicated at 556. The NAS messages can be communicated before and/or after establishment of a security context at the NAS level between the UE 102 and the core network management entity 404. The UE 102, at 558, can verify the certificate Certificate.sub.PKG using a certificate of a CA that is common between the UE 102 and the PKG server 501. In some embodiments, the CA can be a root CA, while in some embodiments the CA can be a subordinate CA of the root CA. As the UE 102 can be used for different network operators and in different geographic regions, the UE 102 can include certificates for multiple root CAs and/or multiple subordinate CAs, and when at least one of these certificates is common with the certificate of the PKG server 501, the UE 102 can verify the certificate Certificate.sub.PKG received from the access network entity 402 and/or from the core network management entity 404. When the certificate Certificate.sub.PKG verification is successful, at 560, the UE 102 can trust the message and accept the included public key PK.sub.PKG of the PKG server 501 as genuine and store the public key PK.sub.PKG for use when verifying messages from network entities as described herein.
[0043] Diagram 570 illustrates another mechanism by which the public key PK.sub.PKG of the PKG server 501 can be provided to the UE 102. At 576, the PKG server 501 can communicate the public key PK.sub.PKG to a carrier provisioning server 572 in a secure message using a secure communication link between the PKG server 501 and the carrier provisioning server 572. Alternatively, and/or additionally, the PKG server 501 can communicate, at 578, the public key PK.sub.PKG to a device vendor server 574 in a secure message via a separate secure communication link. At 580, the carrier provisioning server 572 can download to the UE 102 the public key PK.sub.PKG, during an initial provisioning session and/or during an over-the-air (OTA) provisioning update sessions. Provisioning sessions use secure communication links, and entities within the UE 102, e.g., a secure element, such as eUICC 108 and/or a removable universal SIM card, can receive the public key PK.sub.PKG securely during the provisioning session or provisioning update. The secure element, e.g., eUICC 108, can share the public key PK.sub.PKG with external processing circuitry of the UE 102, e.g., processor 104 and/or baseband component 110 to use for verification of messages from network entities as described herein. For roaming scenarios, a network entity of a visited public land mobile network (VPLMN) can provide the public key PK.sub.PKG to the UE 102 in one or more AS SIB messages and/or in one or more NAS messages. In some embodiments, the VPLMN obtains the public key PK.sub.PKG from a network entity of a home PLMN (HPLMN) to communicate to the UE 102. In some embodiments, the VPLMN communicates the PK.sub.PKG applicable for network entities of its own PKG server 501. At 582, the device vendor server 574 can also provide the public key PK.sub.PKG to the UE 102, such as in an initial carrier bundle upload to the UE 102 and/or during a carrier bundle update to the UE 102. Each of the mechanisms illustrated in FIGS. 5B and 5C can be used individually or together, e.g., one mechanism used for initial loading of a PK.sub.PKG and another mechanism used for subsequent updating of a PK.sub.PKG.
[0044] FIG. 6 illustrates a flow diagram 600 of an exemplary sequence of actions by a network entity to protect the integrity of a message communicated to a wireless device. At 602, a network entity, e.g., access network entity 402 or core network management entity 404, sends a request to the PKG server 502, the request including a first identity value ID1 for the network entity. At 604, the network entity receives from the PKG server 501 a response that includes a first private key SK.sub.ID1 that is based on the first identity value ID1 for the network entity and on a private key of the PKG server SK.sub.PKG. At 606, the network entity generates a signature for a first message, the signature based on the private key SK.sub.ID1 of the network entity. At 608, the network entity sends to the UE 102 the first message concatenated with the signature.
[0045] In some embodiments, the network entity provides the identity value ID1 of the network entity to the UE 102 before sending the first message. In some embodiments, the UE 102 verifies the first message using a first public key PK.sub.ID1 that corresponds to the first private key SK.sub.ID1. In some embodiments, the UE 102 generates the first public key PK.sub.ID1 using the identity value ID1 of the network entity and using a public key of the PKG server PK.sub.PKG that corresponds to the private key SK.sub.PKG of the PKG server. In some embodiments, the network entity is a NodeB (NB), an evolved NodeB (eNB), a next generation NodeB (gNB) of a cellular wireless network, or a femto-cell home-based equivalent network entity to the NB, eNB, or gNB, and the first message is an access stratum (AS) message. In some embodiments, the first message is a radio resource control (RRC) signaling message. In some embodiments, the first message is a random access response (RAR) message sent to the UE 102 as part of a random access channel (RACH) procedure. In some embodiments, the network entity is a mobility management entity (MME), access and mobility management function (AMF) server, a home subscriber server (HSS), an authentication server function (AUSF), or another core network entity, and the first message is a non-access stratum (NAS) message. In some embodiments, the identity value ID1 of the network entity is a concatenation of field values that include a first time stamp value that indicates a first time period during which the identity value ID1 is valid. In some embodiments, before expiration of the first time period, the network entity sends a second request to the PKG server 501, the second request including a second identity value ID.sub.2 for the network entity and including a second time stamp value that indicates a second time period during which ID.sub.2 is valid. Subsequently, the network entity receives from the PKG server 501 a second response that includes a second private key (SK.sub.ID2) that is based on the second ID value ID.sub.2 and also on the private key SK.sub.PKG of the PKG server 501. In some embodiments, the network entity provides to the PKG server 501 one or more identity values for different time periods and obtains corresponding private keys based on each of the one or more identity values. In some embodiments, only one private key used for ID-based message integrity protection may be valid during any single time period. In some embodiments, different private keys based on different ID values can be used for different, non-overlapping time periods. In some embodiments, the ID value ID1 includes a concatenation of field values that include a particular field value indicating the network entity is a femto-cell an operates for a closed subscriber group (CSG).
[0046] FIG. 7 illustrates a flow diagram 700 of an exemplary sequence of actions by a wireless device to verify integrity of a message received from a network entity. At 702, the wireless device, e.g., UE 102, obtains a first identity value ID1 for a network entity, e.g., access network entity 402 or core network management entity 404. At 704, the UE 102 generates a first public key PK.sub.ID1 based on the first identity value ID1 for the network entity and on a public key PK.sub.PKG of the PKG server 501. At 706, the UE 102 receives from the network entity a first message concatenated with a signature based on a first private key SK.sub.ID1 that is based on the first identity value ID1 and on the private key SK.sub.PKG of the PKG server 501 that corresponds to the public key PK.sub.PKG of the PKG server 501. At 708, the UE 102 verifies the integrity of the first message using the signature and the public key PK.sub.ID1 of the network entity. At 710, the UE 102 ignores or discards the first message when integrity verification of the first message fails.
[0047] In some embodiments, the UE 102 obtains the first identity value ID1 for the network entity by extracting the first identity value ID1 from a message transmitted by the network entity. In some embodiments, the message includes a system information block (SIB) message broadcast by the network entity. In some embodiments, the UE 102 obtains the first identity value ID1 for the network entity by deriving ID1 based on information broadcast by the network entity. In some embodiments, the network entity is an NB, eNB, gNB, or a femto-cell home-based equivalent network entity to the NB, eNB, or gNB of a cellular wireless network, and the first message is an access stratum (AS) message. In some embodiments, the first message is a radio resource control (RRC) signaling message. In some embodiments, the first message is a random access response (RAR) message received from the network entity as part of a random access channel (RACH) procedure. In some embodiments, the network entity is a mobility management entity (MME), access and mobility management function (AMF) server, a home subscriber server (HSS), an authentication server function (AUSF), or another core network entity, and the first message is a non-access stratum (NAS) message. In some embodiments, the identity value ID1 of the network entity is a concatenation of field values that include a first time stamp value that indicates a first time period during which the identity value ID1 is valid. In some embodiments, the ID value ID1 includes a concatenation of field values that include a particular field value indicating the network entity is a femto-cell an operates for a closed subscriber group (CSG).
[0048] FIG. 8 illustrates a detailed view of a representative computing device 800 that can be used to implement various methods described herein, according to some embodiments. In particular, the detailed view illustrates various components that can be included in the UE 102 illustrated in FIG. 1. As shown in FIG. 8, the computing device 800 can include a processor 802 that represents a microprocessor or controller for controlling the overall operation of computing device 800. The computing device 800 can also include a user input device 808 that allows a user of the computing device 800 to interact with the computing device 800. For example, the user input device 808 can take a variety of forms, such as a button, keypad, dial, touch screen, audio input interface, visual/image capture input interface, input in the form of sensor data, etc. Still further, the computing device 800 can include a display 810 that can be controlled by the processor 802 to display information to the user. A data bus 816 can facilitate data transfer between at least a storage device 840, the processor 802, and a controller 813. The controller 813 can be used to interface with and control different equipment through and equipment control bus 814. The computing device 800 can also include a network/bus interface 811 that couples to a data link 812. In the case of a wireless connection, the network/bus interface 811 can include a wireless transceiver.
[0049] The computing device 800 also includes a storage device 840, which can comprise a single disk or a plurality of disks (e.g., hard drives), and includes a storage management module that manages one or more partitions within the storage device 840. In some embodiments, storage device 840 can include flash memory, semiconductor (solid state) memory or the like. The computing device 800 can also include a Random Access Memory (RAM) 820 and a Read-Only Memory (ROM) 822. The ROM 822 can store programs, utilities or processes to be executed in a non-volatile manner. The RAM 820 can provide volatile data storage, and stores instructions related to the operation of the computing device 800. The computing device 800 can further include a secure element (SE) 850, which can represent an eUICC 108 of the UE 102.
[0050] The various aspects, embodiments, implementations or features of the described embodiments can be used separately or in any combination. Software, hardware, or a combination of hardware and software can implement various aspects of the described embodiments. The described embodiments can also be embodied as computer readable code on a non-transitory computer readable medium. The non-transitory computer readable medium is any data storage device that can store data, which can thereafter be read by a computer system. Examples of the non-transitory computer readable medium include read-only memory, random-access memory, CD-ROMs, DVDs, magnetic tape, hard disk drives, solid state drives, and optical data storage devices.
[0051] The foregoing description, for purposes of explanation, used specific nomenclature to provide a thorough understanding of the described embodiments. However, it will be apparent to one skilled in the art that the specific details are not required in order to practice the described embodiments. Thus, the foregoing descriptions of specific embodiments are presented for purposes of illustration and description. They are not intended to be exhaustive or to limit the described embodiments to the precise forms disclosed. It will be apparent to one of ordinary skill in the art that many modifications and variations are possible in view of the above teachings.
* * * * *
D00000
D00001
D00002
D00003
D00004
D00005
D00006
D00007
D00008
D00009
XML
uspto.report is an independent third-party trademark research tool that is not affiliated, endorsed, or sponsored by the United States Patent and Trademark Office (USPTO) or any other governmental organization. The information provided by uspto.report is based on publicly available data at the time of writing and is intended for informational purposes only.
While we strive to provide accurate and up-to-date information, we do not guarantee the accuracy, completeness, reliability, or suitability of the information displayed on this site. The use of this site is at your own risk. Any reliance you place on such information is therefore strictly at your own risk.
All official trademark data, including owner information, should be verified by visiting the official USPTO website at www.uspto.gov. This site is not intended to replace professional legal advice and should not be used as a substitute for consulting with a legal professional who is knowledgeable about trademark law.