Managing Virtual Links In A Network Service Instance
Chou; Joey ; et al.
U.S. patent application number 16/408448 was filed with the patent office on 2019-10-31 for managing virtual links in a network service instance. This patent application is currently assigned to Intel Corporation. The applicant listed for this patent is Intel Corporation. Invention is credited to Joey Chou, Yizhi Yao.
| Application Number | 20190334783 16/408448 |
| Document ID | / |
| Family ID | 67843574 |
| Filed Date | 2019-10-31 |








| United States Patent Application | 20190334783 |
| Kind Code | A1 |
| Chou; Joey ; et al. | October 31, 2019 |
MANAGING VIRTUAL LINKS IN A NETWORK SERVICE INSTANCE
Abstract
An apparatus of a Network Manager (NM) comprises one or more processors to send a Network Service (NS) update request to a Network Function Virtualization Orchestrator (NFVO) to add external connectivity to a Physical Network Function (PNF) instance or a Virtual Network Function (VNF) instance in an NS instance, to receive an operation result containing a lifecycle operation occurrence identifier from the NFVO, to receive a lifecycle change notification from the NFVO indicating a start of an NS update, and to receive an NS Lifecycle Change notification from the NFVO indicating a result of the NS update. A memory is to store the result of the NS update.
| Inventors: | Chou; Joey; (Scottsdale, AZ) ; Yao; Yizhi; (Chandler, AZ) | ||||||||||
| Applicant: |
|
||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|
| Assignee: | Intel Corporation Santa Clara CA |
||||||||||
| Family ID: | 67843574 | ||||||||||
| Appl. No.: | 16/408448 | ||||||||||
| Filed: | May 9, 2019 |
Related U.S. Patent Documents
| Application Number | Filing Date | Patent Number | ||
|---|---|---|---|---|
| 16357959 | Mar 19, 2019 | |||
| 16408448 | ||||
| 62648131 | Mar 26, 2018 | |||
| 62665924 | May 2, 2018 | |||
| Current U.S. Class: | 1/1 |
| Current CPC Class: | H04L 41/12 20130101; H04L 41/082 20130101; H04L 41/0806 20130101 |
| International Class: | H04L 12/24 20060101 H04L012/24 |
Claims
1. (canceled)
2. An apparatus of a network manager (NM), comprising: one or more processors to send a network service (NS) update request to a network functions virtualization orchestrator (NFVO) to add a virtual link to an NS instance, to receive from the NFVO an NM lifecycle operation occurrence identifier, and to receive from the NFVO an NM lifecycle change notification indicating a start of the operation; and a memory to store the NM lifecycle change notification.
3. The apparatus of claim 2, wherein the one or more processors are to receive from the NFVO another NM lifecycle change notification indicating a progress of the operation.
4. The apparatus of claim 2, wherein the one or more processors are to receive from the NFVO another NM lifecycle change notification indicating a result of the operation.
5. The apparatus of claim 4, wherein the virtual link is added to the NS instance as the result of the operation.
6. The apparatus of claim 2, wherein the NM is subscribed to receive NS lifecycle management (LCM) notifications.
7. An apparatus of a network functions virtualization orchestrator (NFVO), comprising: one or more processors to receive a request from a network manager (NM) to update a network service (NS) to add a virtual link to an NS instance, to send to the NM an NM lifecycle operation occurrence identifier, and to send to the NM an NM lifecycle change notification indicating a start the NS update; and a memory to store the request.
8. The apparatus of claim 7, wherein the one or more processors are to send to the NM another NM lifecycle change notification indicating a progress of the operation.
9. The apparatus of claim 7, wherein the one or more processors are to send to the NM another NM lifecycle change notification indicating a result of the operation.
10. The apparatus of claim 9, wherein the virtual link is added to the NS instance as the result of the operation.
11. The apparatus of claim 7, wherein the one or more processors are to receive an NS update request from the NM to remove the virtual link from the NS instance.
12. One or more non-transitory machine readable media having instructions stored thereon that, when executed by an apparatus of a network manager (NM), result in: sending a network service (NS) update request to a network functions virtualization orchestrator (NFVO) to add a virtual link to an NS instance; receiving from the NFVO an NM lifecycle operation occurrence identifier for; and receiving from the NFVO an NM lifecycle change notification indicating a start of the operation.
13. The one or more non-transitory machine readable media of claim 12, wherein the instructions, when executed, further result in receiving from the NFVO another NM lifecycle change notification indicating a progress of the operation.
14. The one or more non-transitory machine readable media of claim 12, wherein the instructions, when executed, further result in receiving from the NFVO another NM lifecycle change notification indicating a result of the operation.
15. The one or more non-transitory machine readable media of claim 14, wherein the virtual link is added to the NS instance as the result of the operation.
16. The one or more non-transitory machine readable media of claim 12, wherein the instructions, when executed, further result in sending an NS update request to the NFVO to remove the virtual link from the NS instance.
17. One or more non-transitory machine readable media having instructions stored thereon that, when executed by an apparatus of a network functions virtualization orchestrator (NFVO), result in: receiving a request from a network manager (NM) to update a network service (NS) to add a virtual link to an NS instance; sending to the NM an NM lifecycle operation occurrence identifier; and sending to the NM an NM lifecycle change notification indicating a start the NS update.
18. The one or more non-transitory machine readable media of claim 17, wherein the instructions, when executed, result in sending to the NM another NM lifecycle change notification indicating a progress of the operation.
19. The one or more non-transitory machine readable media of claim 17, wherein the instructions, when executed, result in sending to the NM another NM lifecycle change notification indicating a result of the operation.
20. The one or more non-transitory machine readable media of claim 19, wherein the virtual link is added to the NS instance as the result of the operation.
21. The one or more non-transitory machine readable media of claim 17, wherein it is assumed the NM is subscribed to receive NS lifecycle management (LCM) notifications.
Description
CROSS-REFERENCE TO RELATED APPLICATIONS
[0001] The preset application is a continuation of pending U.S. application Ser. No. 16/357,959 filed Mar. 19, 2019, entitled MANAGING VIRTUAL LINKS IN A NETWORK SERVICE INSTANCE, which in turn claims the benefit of U.S. Provisional Application No. 62/648,131 (AB0013-Z) filed Mar. 26, 2018 and U.S. Provisional Application No. 62/665,924 (AB1122-Z) filed May 5, 2018. Said application Ser. No. 16/357,959, said Application No. 62/648,131, and said Application No. 62/665,924 are hereby incorporated herein by reference in their entireties.
BACKGROUND
[0002] The architecture of Fifth Generation (5G) network architecture consists of 5G core Network Functions (NFs) such as User Plane Function (UPF), Session Management Function (SMF), Network Slice Select Function (NSSF), and Network Exposure Function (NEF). The architecture also consists of a Next Generation (NG) Radio Access Network (RAN) where the functional split feature splits a Next Generation NodeB (gNB) into a gNB Centralized Unit (gNB) that implements the upper layer gNB function and a gNB Distributed Unit (gNB-DU) that implements the lower layer gNB function. The gNB-CU can be implemented as a Virtualized Network Function (VNF), and the gNB-DU can be implemented as a Physical Network Function (PNF). A network operator can create a virtualized 5G network by using European Telecommunications Standards Institute (ETSI) Network Function Virtualization (NFV) lifecycle management function to instantiate a Network Service (NS) in the cloud that contains Virtual Network Functions (VFNs) such as 5G core NFs and the gNB-CU, and PNFs such as the gNB-DU.
DESCRIPTION OF THE DRAWING FIGURES
[0003] Claimed subject matter is particularly pointed out and distinctly claimed in the concluding portion of the specification. However, such subject matter may be understood by reference to the following detailed description when read with the accompanying drawings in which:
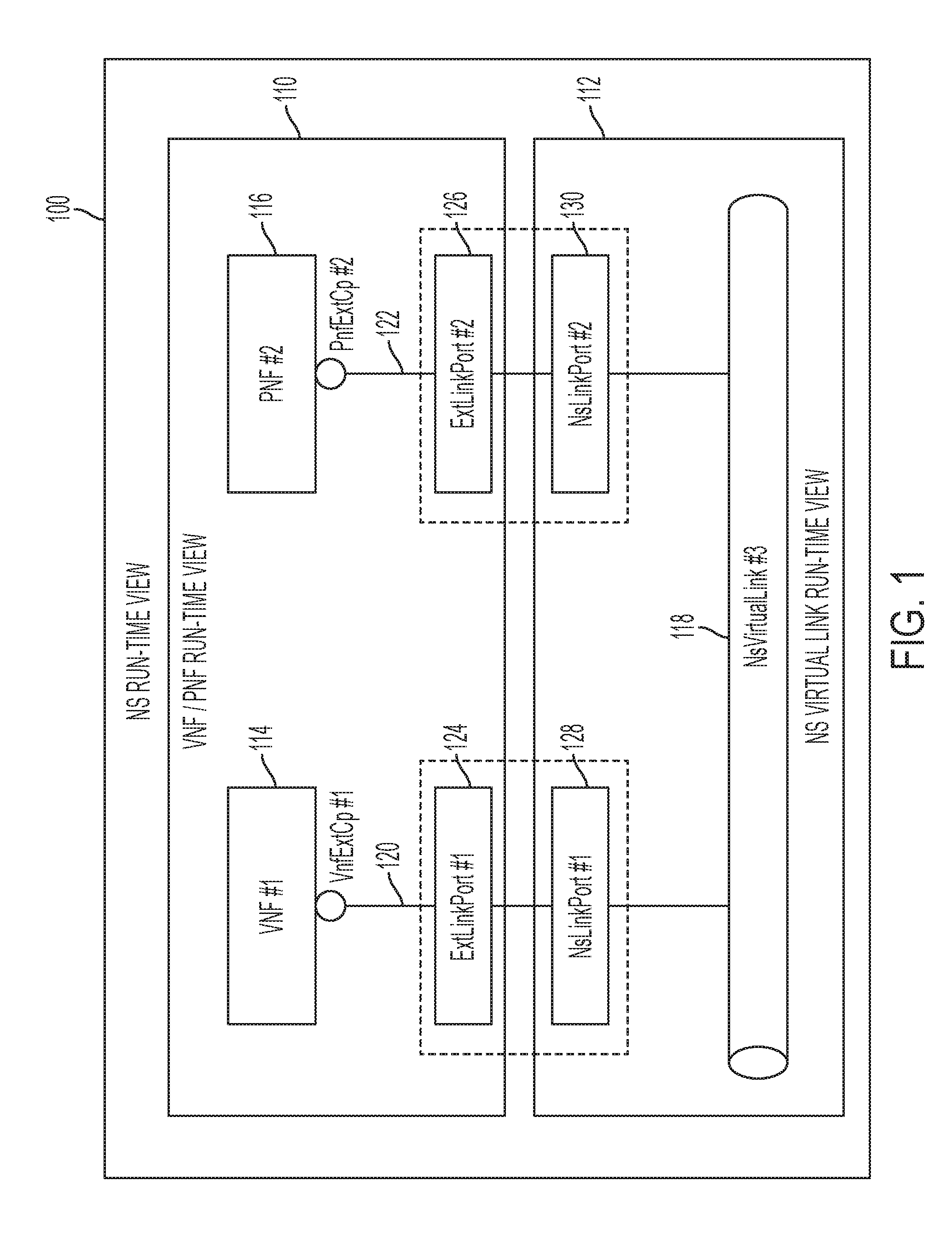
[0004] FIG. 1 is a diagram of a network service run-time view in accordance with one or more embodiments.
[0005] FIG. 2 is a diagram of a Third Generation Partnership Project (3GPP) management and a European Telecommunications Standards Institute (ETSI) Network Function Virtualization (NFV) Management and Orchestration (MANO) architecture in accordance with one or more embodiments.
[0006] FIG. 3 is a diagram of a network service with two Virtual Network Function Forwarding Graphs (VNFFGs) with different Network Forwarding Paths (NFPs) in accordance with one or more embodiments.
[0007] FIG. 4 is a diagram of a VNFFG update procedure to add, delete, or modify an NFP to a VNFFG instance in accordance with one or more embodiments.
[0008] FIG. 5 is a diagram of an NS update to add a VNFFG to an NS instance in accordance with one or more embodiments.
[0009] FIG. 6 illustrates an architecture of a system of a network in accordance with some embodiments.
[0010] FIG. 7 illustrates example components of a device in accordance with some embodiments.
[0011] FIG. 8 illustrates example interfaces of baseband circuitry in accordance with some embodiments.
[0012] It will be appreciated that for simplicity and/or clarity of illustration, elements illustrated in the figures have not necessarily been drawn to scale. For example, the dimensions of some of the elements may be exaggerated relative to other elements for clarity. Further, if considered appropriate, reference numerals have been repeated among the figures to indicate corresponding and/or analogous elements.
DETAILED DESCRIPTION
[0013] In the following detailed description, numerous specific details are set forth to provide a thorough understanding of claimed subject matter. It will, however, be understood by those skilled in the art that claimed subject matter may be practiced without these specific details. In other instances, well-known methods, procedures, components and/or circuits have not been described in detail.
[0014] In the following description and/or claims, the terms coupled and/or connected, along with their derivatives, may be used. In particular embodiments, connected may be used to indicate that two or more elements are in direct physical and/or electrical contact with each other. Coupled may mean that two or more elements are in direct physical and/or electrical contact. However, coupled may also mean that two or more elements may not be in direct contact with each other, but yet may still cooperate and/or interact with each other. For example, "coupled" may mean that two or more elements do not contact each other but are indirectly joined together via another element or intermediate elements. Finally, the terms "on," "overlying," and "over" may be used in the following description and claims. "On," "overlying," and "over" may be used to indicate that two or more elements are in direct physical contact with each other. It should be noted, however, that "over" may also mean that two or more elements are not in direct contact with each other. For example, "over" may mean that one element is above another element but not contact each other and may have another element or elements in between the two elements. Furthermore, the term "and/or" may mean "and", it may mean "or", it may mean "exclusive-or", it may mean "one", it may mean "some, but not all", it may mean "neither", and/or it may mean "both", although the scope of claimed subject matter is not limited in this respect. In the following description and/or claims, the terms "comprise" and "include," along with their derivatives, may be used and are intended as synonyms for each other.
[0015] FIG. 1 is a diagram of a network service run-time view in accordance with one or more embodiments. The core network functions of Fifth Generation (5G) networks and the 5G NodeB Centralized Unit (gNB-CU) can be implemented as Virtualized Network Functions (VNFs), and the gNB Distributed Unit (gNB-DU) can be implemented as a PNF (Physical Network Function). Network operators can create virtualized 5G networks by using European Telecommunications Standards Institute (ETSI) Network Function Virtualization (NFV) lifecycle management function to instantiate a NS (Network Service) in the cloud that contains Virtual Network Functions (VFNs) such as 5G core NFs and the gNB-CU, and PNFs such as the gNB-DU.
FIG. 1 shows the connectivity between VNF and PNF that is implemented by a Network Service (NS) virtual link. For example, NS run-time view 100 includes VNF/PNF run-time view 110 and NS Virtual Link run-time view 112. As shown in FIG. 1, virtual network function (VNF #1) 114 is connected to NS virtual link (NsVirtualLink #3) 118 via VNF external connection point (VnfExtCP #1) 120, and physical network function (PNF #2) 116 is connected to NS virtual link (NsVirtualLink #3) 118 via PNF external connection point (PnfExtCp #2). External link ports (ExtLinkPort #1) 124 and (ExtLinkPort #2) 126 of VNF/PNF run-time view 110 couple to NS link ports (NsLinkPort #1) 128 and (NsLinkPort #2) 130 of NS Virtual Link run-time view 112.
[0016] FIG. 2 is a diagram of a Third Generation Partnership Project (3GPP) management and a European Telecommunications Standards Institute (ETSI) Network Function Virtualization (NFV) Management and Orchestration (MANO) architecture in accordance with one or more embodiments. The 3GPP management system network management architecture 200 is based on Fourth Generation (4G) networks which may be subject to change in Fight Generation (5G) networks. As used herein, the term "Network Management Function (NM)" for 5G plays a similar role as the NM in 4G, and the scope of the claimed subject matter is not limited in this respect.
[0017] As shown in FIG. 2, network management architecture 200 can include an Operations Support System and/or Business Support System (OSS/BSS) 210, Network Manager (NM) 212, Domain Manager (DM) 214, and Element Manager (EM) 216. Where the NFV environment comprises a Third Generation Partnership Project (3GPP) network, the NM 212, DM 214, and EM 216 can comprise a 3GPP Management System 222. Such a 3GPP Management System can control one or more network elements (NEs) that operate as a Physical Network Function (PNF) (gNB-DU) 218, and further can control one or more Virtual Network Functions (VNFs), for example VNF (gNB-CU) 224 and/or VNF (5G NF) 226. An NFV Infrastructure (NFVI) 228 comprises hardware and/or software to realize the VNF blocks. In accordance with one or more embodiments, network architecture 200 can operate in compliance with a 3GPP standard, for example 3GPP Technical Standard 28.500 V14.1.0 (2017-03) or in compliance with European Telecommunications Standards Institute (ETSI) Group Specification (GS) NFV 002 V1.1.1 (2013-10), although the scope of the claimed subject matter is not limited in these respects.
[0018] In one or more embodiments, NFV Management and Orchestration (NFV-MANO) 230 comprises and architectural framework to manage and orchestrate the VNF blocks of NFV management architecture 200, for example to implement one or more VNF blocks as one or more virtual machines running on NFVI 228. The NFV-MANO 230 can include NFV Orchestrator (NFVO) 232, VNF Manager (VNFM) 234, and/or Virtualized Infrastructure Manager (VIM) 236. Furthermore, NVF-MANO 230 can include one or more interfaces to couple with OSS/BSS 210, EM 216, one or more VNF blocks, and NFVI 228.
[0019] In one or more embodiments, NM 212 can add external connectivity to a PNF 218 or VNF instance in a NS. Such external connectivity may be added when a VNF instance that has been instantiated or added in a NS may not have enough external connectivity, for example due the lack of an ExtVirtualLink 118 in the action of instantiating new VNF instances in the NS instance, when some NsVirtualLinkConnectivity is not ready for a VNFProfile in the NSD when instantiating the NS. Such external connectivity also can be added when some connectivity for a PNF instance in a NS may have not been established yet. In addition. When the NS is updated to have more PNF or VNF instances, new connectivity may be needed between the existing PNF or VNF instances and the new PNF or VNF instances. For instance, when some new eNBs are added to a NS, some new connectivity may be needed for Mobility Management Entity (MME) VNFs. The following use cases can be added to 3GPP TS 28.525 to enable operators to add external connectivity to a PNF or VNF instance, for example section 6.4.3.18 of 3GPP TS 28.525 V15.0.0 (2018-06).
TABLE-US-00001 TABLE 1 Use Cases for adding external connectivity to PNF or VNF instance Use Case Evolution/Specification Goal Add external connectivity to a PNF or VNF instance. Actors and NM Roles Telecom NFVO resources Assumptions NM is subscribed to receive the NS LCM notifications. Pre- A PNF or VNF instance has been added or instantiated in conditions an NS instance without the external connectivity, or a new external connectivity is needed due to PNF or VNF upgrade. Begins when NM determines (e.g. by operator's request) that it is necessary to add the external connectivity to an existing PNF or VNF instance. Step 1 (M) NM sends a request to the NFVO to update the NS instance by adding the external connectivity to an existing PNF or VNF instance. Step 2 (M) NFVO returns to the NM lifecycleOperationOccurrenceId and processes the request Step 3 (M) NFVO sends to NM Lifecycle Change Notification indicating start of the operation. Step 4 (M) NFVO sends to NM Lifecycle Change Notifications indicating progress of the operation. Step 5 (M) NFVO sends to NM Lifecycle Change Notification indicating result of the operation. Ends when All the steps identified above are successfully completed. Exceptions One of the steps identified above fails. Post- The external connectivity has been added to the PNF or conditions VNF instance according to the operator's needs. Traceability REQ-NFV_LCM_Os-Ma-nfvo-FUN-x
[0020] For REQ-NFV_LCM_Os-Ma-nfvo-FUN-x, the Os-Ma-nfvo reference point shall support a capability allowing NM to request the addition of the external connectivity to a PNF or VNF instance as part of NS update. The NM 212 can add a new virtual link instance to a NS instance, for example when no virtual link is available for use, or when a new virtual link is needed due to the update of NS. The NM 212 also can remove a virtual link from a NS instance when it is no longer needed.
[0021] The following lists use cases and requirements to be added to 3GPP TS 28.525 to enable operators to add a virtual link to a NS instance, and remove a virtual link from a NS instance.
TABLE-US-00002 TABLE 2 6.4.3.x Add a virtual link to a NS instance Use Case Evolution/Specification Goal Add a virtual link to a NS instance. Actors and NM Roles Telecom NFVO resources Assumptions NM is subscribed to receive the NS LCM notifications. Pre- The NS where the virtual link is to be added has been conditions instantiated. The virtual link descriptor and virtual link profile for the virtual link to be added are available in the NSD either on-boarded originally or updated. Begins when NM determines (e.g. by operator's request) that it is necessary to add a virtual link to an existing NS instance. Step 1 (M) NM sends a request to the NFVO to update the NS instance to add a virtual link. Step 2 (M) NFVO returns to the NM lifecycleOperationOccurrenceId and processes the request Step 3 (M) NFVO sends to NM Lifecycle Change Notification indicating start of the operation. Step 4 (M) NFVO sends to NM Lifecycle Change Notifications indicating progress of the operation. Step 5 (M) NFVO sends to NM Lifecycle Change Notification indicating result of the operation. Ends when All the steps identified above are successfully completed. Exceptions One of the steps identified above fails. Post- A virtual link has been added to the NS instance according conditions to the operator's needs. Traceability REQ-NFV_LCM_Os-Ma-nfvo-FUN-x
TABLE-US-00003 TABLE 3 6.4.3.y Remove a virtual link from a NS instance Use Case Evolution/Specification Goal Remove a virtual link from a NS instance. Actors and NM Roles Telecom NFVO resources Assumptions NM is subscribed to receive the NS LCM notifications. Pre- A virtual link in a NS instance is not used by conditions any PNF or VNF instance, and is no longer needed. Begins when NM determines (e.g. by operator's request) that it is necessary to remove the virtual link from an existing NS instance. Step 1 (M) NM sends a request to the NFVO to update the NS instance to remove a virtual link. Step 2 (M) NFVO returns to the NM lifecycleOperationOccurrenceId and processes the request Step 3 (M) NFVO sends to NM Lifecycle Change Notification indicating start of the operation. Step 4 (M) NFVO sends to NM Lifecycle Change Notifications indicating progress of the operation. Step 5 (M) NFVO sends to NM Lifecycle Change Notification indicating result of the operation. Ends when All the steps identified above are successfully completed. Exceptions One of the steps identified above fails. Post- The virtual link has been removed from the NS instance conditions according to the operator's needs. Traceability REQ-NFV_LCM_Os-Ma-nfvo-FUN-y
[0022] For REQ-NFV_LCM_Os-Ma-nfvo-FUN-x, the Os-Ma-nfvo reference point shall support a capability allowing NM 212 to request the addition of virtual link to a NS instance as part of NS update. For REQ-NFV_LCM_Os-Ma-nfvo-FUN-y, the Os-Ma-nfvo reference point shall support a capability allowing NM to request the removal of virtual link from a NS instance as part of NS update.
[0023] Referring now to FIG. 3, a diagram of a network service with two Virtual Network Function Forwarding Graphs (VNFFGs) with different Network Forwarding Paths (NFPs) in accordance with one or more embodiments will be discussed. FIG. 3 shows a Network Service (NS) 300 containing three Virtual Network Functions (VNFs), (VNF1) 310, (VNF2) 312, and (VNF3) 314 with two VNF Forwarding Graphs (VNFFGs), (VNFFG1) 316 and (VNFFG2) 318 where each VNFFG can contain one or more Network Forwarding Paths (NFPs).
[0024] The VNFFG is used to connect VNF instances in a NS via Service Access Point (SAP) such as Connection Points (CPs) such as (CP01) 320 and (CP02) 322 that are the entry point and exit point of a NS. In the example of FIG. 3, VNFFG2:NFP1 traverses through CP1, CP11, CP12, CP32, CP33, and CP02, VNFFG1:NFP1 traverses through CP1, CP11, CP13, CP21, CP32, CP33, and CP02, and VNFFG1:NFP2 traverses through CP1, CP11, CP13, CP32, CP33, and CP02.
[0025] The European Telecommunications Standards Institute (ETSI) Group Specification (GS) NFV-IFA 013 defines Update NS operation (see clause 7.3.5) to allow operators to create a VNFFG in a NS, or update a VNFFG instance in a NS. The following two actions, however in the Update NS operation are missing important information that prevents VNFFG addition and update from working. In one or more embodiments, the following information may be added to ETSI GS NFV-IFA 013. One embodiment is to add VNFFG action to add a VNFFG with NFP to a NS wherein the following parameters can be added. Added input parameters include NFP data information that characterizes the NFP, and added output parameters including NFP identifier indicating the NFP instance being added to a VNFFG, and VNFFG identifier indicating the VNFFG instance in which the NFP instance is contained. Another embodiment is to update VNFFG action to add an NFP to a given VNFFG wherein the following parameters can be added. Added output parameter--NFP identifier, indicating the NFP instance being added to the VNFFG.
[0026] The following shows the Update NS operation from ETSI GS NFV-IFA013, with selected actions being impacted. Furthermore, the subject matter discussed herein may added to 3GPP TS 28.525, for example section 6.4.3.19 of 3GPP TS 28.525 V. 15.0.0 (2018-06) and section 6.4.3.20 of 3GPP TS 28.525 V15.0.0 (2018-06).
7.3.5 Update NS Operation
7.3.5.1 Introduction
[0027] This operation updates an NS instance. This operation is also used to embed VNF LCM operations in support of fine grained NS LCM approach. See the informative message flows in annex C. Actions that can be performed with an update include:
[0028] Adding existing VNF instances to the NS instance.
[0029] Removing VNF instances from the NS instance.
[0030] Instantiating new VNF instances and adding them to the NS instance.
[0031] Changing the DF of VNF instances belonging to the NS instance.
[0032] Changing the operational state of a VNF instance belonging to the NS instance.
[0033] Modifying information data and/or the configurable properties of a VNF instance belonging to the NS instance.
[0034] Changing the external connectivity of a VNF instance belonging to the NS instance.
[0035] Adding SAPs to the NS instance.
[0036] Removing SAPs from the NS instance.
[0037] Adding existing NS instances to the NS instance.
[0038] Removing nested NS instances from the NS instance.
[0039] Associate a new NSD version to the NS instance.
[0040] Moving VNF instances from one NS instance to another NS instance.
[0041] Adding VNFFGs to the NS instance.
[0042] Removing VNFFGs from the NS instance.
[0043] Update VNFFGs of the NS instance.
[0044] Changing the DF of the NS instance.
[0045] Adding PNFs to the NS instance.
[0046] Modifying PNFs in the NS instance.
[0047] Removing PNFs from the NS instance.
[0048] In the above list, adding VNFFGs to the NS instance and updating VNFFGs of the NS instance are impacted. Only one type of update shall be allowed per operation.
[0049] Table 4 below comprises Table 7.3.5.1-1 from ETSI GS NFV-IFA013 which lists the information flow exchanged between the OSS/BSS 210 and the NFVO 232. It is possible, however, to request several updates of a given type in one Update NS operation as indicated in the cardinalities in table 7.3.5.2-1.
TABLE-US-00004 TABLE 4 Table 7.3.5.1-1: Update NS operation Message Requirement Direction UpdateNsRequest Mandatory OSS/BSS NFVO UpdateNsResponse Mandatory NFVO OSS/BSS
[0050] The input parameters (7.3.5.2 Input parameters) sent when invoking the operation shall follow the indications provided in Table 5 below, which comprises table 7.3.5.2-1 from ETSI GS NFV-IFA013.
TABLE-US-00005 TABLE 5 Table 7.3.5.2-1: Update NS operation input parameters Parameter Qualifier Cardinality Content Description nsInstanceId M 1 Identifier Identifier of the NS instance being updated. updateType M 1 Enum Specifies the type of update. This parameter determines also which one of the following parameter is present in the operation. Possible values are: AddVnf (adding existing VNF instance(s)), RemoveVnf (removing VNF instance(s)), InstantiateVnf (instantiating new VNF(s)), ChangeVnfDf (Changing VNF DF), OperateVnf (changing VNF state), ModifyVnfInformation (modifying VNF information and/or the configurable properties of VNF instance(s)), ChangeExtVnfConnectivity (changing the external connectivity of VNF instance(s)), AddSap (adding SAP(s)), RemoveSap (removing SAP(s)), AddNestedNs (adding existing NS instance(s) as nested NS(s)), RemoveNestedNs (removing existing nested NS instance(s)), AssocNewNsdVersion (associating a new NSD version to the NS instance), MoveVnf (moving VNF instance(s) from one origin NS instance to a another target NS instance), AddVnffg (adding VNFFG(s)), RemoveVnffg (removing VNFFG(s)), UpdateVnffg (updating VNFFG(s)), ChangeNsDf (changing NS DF), AddPnf (adding PNF), ModifyPnf(modify PNF), RemovePnf (removing PNF). addVnfInstance M 0 . . . N VnfInstanceData Specify an existing VNF instance to be added to the NS instance. This parameter shall be present only if updateType = AddVnf. removeVnfInstanceId M 0 . . . N Identifier Specify an existing VNF instance to be removed from the NS instance. The parameter contains the identifier(s) of the VNF instances to be removed. This parameter shall be present only if updateType = RemoveVnf. See note 1. instantiateVnfData M 0 . . . N InstantiateVnfData Specify the new VNF to be instantiated. This parameter can be used e.g. for the bottom-up NS creation. This parameter shall be present only if updateType = InstantiateVnf. changeVnfFlavourData M 0 . . . N ChangeVnfFlavourData Specify the new DF of the VNF instance to be changed to. This parameter shall be present only if updateType = ChangeVnfDf. operateVnfData M 0 . . . N OperateVnfData Specify the state of the VNF instance to be changed. This parameter shall be present only if updateType = OperateVnf. modifyVnfInfoData M 0 . . . N ModifyVnfInfoData Specify the VNF Information parameters and/or the configurable properties of VNF instance to be modified. This parameter shall be present only if updateType = ModifyVnfInformation. changeExtVnfConnectivityData M 0 . . . N ChangeExtVnfConnectivityData Specify the new external connectivity data of the VNF instance to be changed. This parameter shall be present only if updateType = ChangeExtVnfConnectivity. addSap M 0 . . . N SapData Specify a new SAP to be added to the NS instance. This parameter shall be present only if updateType = AddSap. removeSapId M 0 . . . N Identifier Specify an existing SAP to be removed from the NS instance. The parameter shall be present only if updateType = RemoveSap. addNestedNsId M 0 . . . N Identifier Specify an existing nested NS instance to be added to (nested within) the NS instance. This parameter shall be present only if updateType = AddNestedNs. removeNestedNsId M 0 . . . N Identifier Specify an existing nested NS instance to be removed from the NS instance. The parameter shall be present only if updateType = RemoveVnfNestedNs. assocNewNsdVersionData M 0 . . . 1 AssocNewNsdVersionData Specify the new NSD to be used for the NS instance. This parameter shall be present only if updateType = AssocNewNsdVersion. moveVnfInstanceData M 0 . . . N MoveVnfInstanceData Specify existing VNF instance to be moved from one NS instance to another NS instance. This parameter shall be present only if updateType = MoveVnf. addVnffg M 0 . . . N AddVnffgData Specify the new VNFFG to be created to the NS Instance. This parameter shall be present only if updateType = AddVnffg. removeVnffgId M 0 . . . N Identifier Identifier of an existing VNFFG to be removed from the NS Instance. This parameter shall be present only if updateType = RemoveVnffg. updateVnffg M 0 . . . N UpdateVnffgData Specify the new VNFFG Information data to be updated for a VNFFG of the NS Instance. This parameter shall be present only if updateType = UpdateVnffg. changeNsFlavourData M 0 . . . 1 ChangeNsFlavourData Specifies the new DF to be applied to the NS instance. It shall be present only if updateType = ChangeNsDf. updateTime M 0 . . . 1 DateTime Timestamp indicating the update time of the NS, i.e. the NS will be updated at this timestamp. Cardinality "0" indicates the NS update takes place immediately. addPnfData M 0 . . . N AddPnfData Information of the PNF(s) that are being added into the NS instance. This parameter shall be present only if updateType = AddPnf. modifyPnfData M 0 . . . N ModifyPnfData Information on the PNF(s) that are being modified in this NS instance. This parameter shall be present only if updateType = ModifyPnf. See note 2 removePnfId M 0 . . . N Identifier Identifier of the PNF(s) that are part of this NS instance and that should be deleted from it. This parameter shall be present only if updateType = RemovePnf. NOTE 1: If a VNF instance is removed from an NS and this NS was the last one for which this VNF instance was a part, the VNF instance is terminated by the NFVO. NOTE 2: New CP addresses should be contained in the element, if PNF CPs need to be changed.
[0051] The following shows the text being added to both input and output parameters to support the Add VNFFG action.
8.3.4.21 AddVnffgData Information Element
8.3.4.21.1 Description
[0052] This information element specifies the parameters that are needed for the creation of a new VNFFG instance.
8.3.4.21.2 Attributes
[0053] The attributes of the AddVnffgData information element shall follow the indications provided in Table 6 which comprises Table 8.3.4.21.2 from ETSI GS NFV-IFA0131.
TABLE-US-00006 TABLE 6 Table 8.3.4.21.2-1: Attributes of the AddVnffgData information element Attribute Qualifier Cardinality Content Description vnffgdId M 1 Identifier(Reference Identifier of the VNFFGD to Vnffgd) which defines the VNFFG to be added. vnffgName M 1 String Human readable name for the VNFFG. description M 1 String Human readable description for the VNFFG. nfp N 0 . . . N NfpData Indicate the desired new NFP(s) for a given VNFFG after the operations of addition/removal of NS components (e.g. VNFs, VLs, etc.) have been completed, or indicate the NFP classification and selection rule for the new NFP to be added to the VNFFG instance.
7.3.5 Update NS Operation
7.3.5.3 Output Parameters
[0054] The output parameter returned by the operation shall follow the indications provided in Table 7 comprising Table 7.3.5.3-1 from ETSI GS NFV-IFA0131.
TABLE-US-00007 TABLE 7 Table 7.3.5.3-1: Update NS operation output parameters Parameter Qualifier Cardinality Content Description vnfInstanceId M 0 . . . N Identifier Identifier of the instance of the instantiated VNF. This information shall be retuned as the result of the operation if successful. pnfId M 0 . . . N Identifier Identifier of the PNF assigned by OSS. It shall be present only if updateType = AddPnf. This information shall be returned as the result of the operation if successful. addedVnffgInfo M 0 . . . N AddedVnffgInfo Information of the instance of the created VNFFG. It shall be present only if updateType = AddVnffg. This information shall be returned as the result of the operation if successful. sapId M 0 . . . N Identifier Identifier of the instance of the created SAP. It shall be present only if updateType = addSap. This information shall be returned as the result of the operation if successful. lifecycleOperationOccurrenceId M 1 Identifier The identifier of the NS lifecycle operation occurrence. This information shall be returned immediately before any notification, message or operation is done
8.3.4.x AddedVnffgInfo Information Element
8.3.4.x.1 Description
[0055] This information element specifies the VNFFG instance being added to a NS instance.
8.3.4.x.2 Attributes
[0056] The attributes of the AddedVnffgInfo information element shall follow the indications provided in Table 8 comprising Table 8.3.4.x.2-1 1 from ETSI GS NFV-IFA0131.
TABLE-US-00008 TABLE 8 Table 8.3.4.x.2-1: Attributes of the AddVnffgInfo information element Attribute Qualifier Cardinality Content Description vnffgId M 0 . . . 1 Identifier Identifier of the instance of the created VNFFG. nfpId M 0 . . . N Identifier Identifier(s) of the (Reference NFP to be added to a to Nfp)) given VNFFG.
[0057] The following shows the text being added to the output parameters to support the Update VNFFG action.
7.3.5 Update NS Operation
7.3.5.3 Output Parameters
[0058] The output parameter returned by the operation shall follow the indications provided in Table 9 comprising table 7.3.5.3-1 from ETSI GS NFV-IFA0131.
TABLE-US-00009 TABLE 9 Table 7.3.5.3-1: Update NS operation output parameters Parameter Qualifier Cardinality Content Description vnfInstanceId M 0 . . . N Identifier Identifier of the instance of the instantiated VNF. This information shall be retuned as the result of the operation if successful. pnfId M 0 . . . N Identifier Identifier of the PNF assigned by OSS. It shall be present only if updateType = AddPnf. This information shall be returned as the result of the operation if successful. vnffgId M 0 . . . N Identifier Identifier of the instance of the created VNFFG. It shall be present only if updateType = AddVnffg. This information shall be returned as the result of the operation if successful. sapId M 0 . . . N Identifier Identifier of the instance of the created SAP. It shall be present only if updateType = addSap. This information shall be returned as the result of the operation if successful. lifecycleOperationOccurrenceId M 1 Identifier The identifier of the NS lifecycle operation occurrence. This information shall be returned immediately before any notification, message or operation is done nfpId M 0 . . . N Identifier Identifier(s) of the NFP being deleted to a given VNFFG. It shall be present only if updateType = UpdateVnffg. This information shall be returned as the result of the operation if successful.
[0059] The following use cases, requirements, and procedures are added to TS 28.525 to describe how NM 212 or 3GPP operators can use Add VNFFG and Update VNFFG actions in the NS update operation to add VNFFG with NFP to a NS instance.
TABLE-US-00010 TABLE 10 6.4.3.x Add VNF forwarding graph to a NS instance Use Case Evolution/Specification Goal Add VNF forwarding graph to a NS instance. Actors and NM Roles Telecom NFVO resources Assumptions NM is subscribed to receive the NS LCM notifications. Pre- An NS instance, containing the VNF instances and all conditions necessary components (e.g. VLs, CPs, SAPs, . . .) to form a VNFFG, has been instantiated, VNFFGD for the VNFFG to be added already exists. Begins when NM determines (e.g. by operator's request) that it is necessary to add a VNFFG to a NS instance. Step 1 (M) NM sends a request to the NFVO to update the NS instance (see clause 7.3.5 in [6]) by adding a VNFFG to a NS instance. Step 2 (M) NFVO returns to the NM lifecycleOperationOccurrenceId and processes the request Step 3 (M) NFVO sends to NM Lifecycle Change Notification indicating start of the operation. Step 4 (M) NFVO sends to NM Lifecycle Change Notifications indicating progress of the operation. Step 5 (M) NFVO sends to NM Lifecycle Change Notification indicating result of the operation. Ends when All the steps identified above are successfully completed. Exceptions One of the steps identified above fails. Post- The VNFFG has been added to the NS instance according conditions to the operator's needs. Traceability REQ-NFV_LCM_Os-Ma-nfvo-FUN-x
TABLE-US-00011 TABLE 11 6.4.3.x Update VNF forwarding graph in a NS instance Use Case Evolution/Specification Goal Update VNF forwarding graph in a NS instance. Actors and NM Roles Telecom NFVO resources Assumptions NM is subscribed to receive the NS LCM notifications. Pre- An NS instance with VNFFG already exists, conditions VNFFGD for the VNFFG to be updated already exists. Begins when NM determines (e.g. by operator's request) that it is necessary to update the VNFFG in a NS instance. Step 1 (M) NM sends a request to the NFVO to update the VNFFG (e.g. addition, deletion, and modification of NFP) in a NS instance via the NS update operation (see clause 7.3.5 in [6]). Step 2 (M) NFVO returns to the NM lifecycleOperationOccurrenceId, and the identifier of new NFP if the update is to add a NFP to the existing VNFFG, and processes the request. Step 3 (M) NFVO sends to NM Lifecycle Change Notification indicating start of the operation. Step 4 (M) NFVO sends to NM Lifecycle Change Notifications indicating progress of the operation. Step 5 (M) NFVO sends to NM Lifecycle Change Notification indicating result of the operation. Ends when All the steps identified above are successfully completed. Exceptions One of the steps identified above fails. Post- The VNFFG has been updated to the NS instance according conditions to the operator's needs. Traceability REQ-NFV_LCM_Os-Ma-nfvo-FUN-x
[0060] For REQ-NFV_LCM_Os-Ma-nfvo-FUN-x, the Os-Ma-nfvo reference point shall support a capability allowing NM 212 to request the addition of the VNFFG as part of NS update (covered by requirement Os-Ma-nfvo.NsLcm.027 in ETSI GS NFV-IFA 013 [6]).
[0061] FIG. 4 is a diagram of a VNFFG update procedure to add, delete, or modify an NFP to a VNFFG instance in accordance with one or more embodiments as discussed below. As shown in FIG. 4, in VNFFG update procedure 400, NM 212 sends an UpdateNsRequest--UpdateVnffg message to NFVO 212 at operation 410. NFVO 232 responds to NM 212 with an UpdateNsResponse message at operation 412. NFVO 232 sends Notify--NsLifecycleChangeNotification (start) message to NM 212 at operation 414. NFVO 232 then sends Notify--NsIndentifierChangeNotification (result) message to NM 212 at operation. Details of VNFFG update procedure 400 to add an NFP, to delete an NFP, and to modify an NFP are presented below.
4.4.5 NS Instance Updating
4.4.5,x VNFFG Update to Add a NFP
[0062] Figure 4.4.5.x-1 depicts the procedure of VNFFG update to add a NFP (Network Forwarding Path) to a VNFFG instance (see clause 7.3.5 [5]). [0063] 1. NM sends to NFVO an UpdateNsRequest (see clause 7.3.5 of [5]) with the following parameters (see clause 7.3.5.2 of [5]) to on-board the NSD: [0064] nsInstanceId: the identifier of the NS instance being updated. [0065] updateType="UpdateVnffg" to indicate the type of update operation. [0066] UpdateVnffgData: the information of VNFFG to be updated (see clause 8.3.4.22.2 of [5]): [0067] vnffgId: Identifier of an existing VNFFG information element to be updated for the NS instance; [0068] nfp: Indicate the desired new NFP(s) for a given VNFFG; [0069] nfpName: Human readable name for the NFP; [0070] description: Human readable description for the NFP; [0071] cp: Identifier(s) of the CPs and SAPs which the NFP passes by; [0072] nfpRule: NFP classification and selection rule. [0073] 2. NFVO sends to NM an UpdateNsResponse (see clause 7.3.5 of [5]) with the attributes: [0074] lifecycleOperationOccurrenceId: the identifier of the NS lifecycle operation occurrence; [0075] nfpId that is the identifier of NFP being added to the given VNFFG; [0076] Note: the nfpId: is currently not defined in clause 7.3.5.3 in [5]. [0077] 3. NFVO sends to NM a Notify (see clause 7.4.3 [5]) carrying an NsLifecycleChangeNotification information element with attributes nsInstanceId, lifecycleOperationOccurrenceId, operation="NsUpdate", and notificationType="start" to indicate the start of the NS instantiation (see clause 8.3.2.2 [5]). [0078] 4. NFVO sends to NM a Notify (see clause 7.4.3 [5]) carrying an NsLifecycleChangeNotification information element with attributes nsInstanceId, lifecycleOperationOccurrenceId, operation="NsUpdate", and notificationType="result" to indicate the end result of the NS instantiation (see clause 8.3.2.2 [5]).
4.4.5,x VNFFG Update to Delete a NFP
[0079] Figure 4.4.5.x-1 depicts the procedure of VNFFG update to delete a NFP from a VNFFG instance (see clause 7.3.5 [5]). [0080] 1. NM sends to NFVO an UpdateNsRequest (see clause 7.3.5 of [5]) with the following parameters (see clause 7.3.5.2 of [5]) to on-board the NSD: [0081] nsInstanceId: the identifier of the NS instance being updated. [0082] updateType="UpdateVnffg" to indicate the type of update operation. [0083] UpdateVnffgData: the information of the external connectivity (see clause 8.3.4.22.2 of [5]): [0084] vnffgId: Identifier of an existing VNFFG information element to be updated for the NS instance; [0085] nfpId: Identifier(s) of the NFP to be deleted from a given VNFFG. [0086] 2. NFVO sends to NM an UpdateNsResponse (see clause 7.3.5 of [5]) with the attribute nsInstanceId identifier of the lifecycleOperationOccurrenceId that is the identifier of the NS lifecycle operation occurrence, [0087] 3. NFVO sends to NM a Notify (see clause 7.4.3 [5]) carrying an NsLifecycleChangeNotification information element with attributes nsInstanceId, lifecycleOperationOccurrenceId, operation="NsUpdate", and notificationType="start" to indicate the start of the NS instantiation (see clause 8.3.2.2 [5]). [0088] 4. NFVO sends to NM a Notify (see clause 7.4.3 [5]) carrying an NsLifecycleChangeNotification information element with attributes nsInstanceId, lifecycleOperationOccurrenceId, operation="NsUpdate", and notificationType="result" to indicate the end result of the NS instantiation (see clause 8.3.2.2 [5]).
4.4.5,x VNFFG Update to Modify a NFP
[0089] Figure 4.4.5.x-1 depicts the procedure of VNFFG update to modify a NFP (Network Forwarding Path) of a VNFFG instance (see clause 7.3.5 [5]). [0090] 1. NM sends to NFVO an UpdateNsRequest (see clause 7.3.5 of [5]) with the following parameters (see clause 7.3.5.2 of [5]) to on-board the NSD: [0091] nsInstanceId: the identifier of the NS instance being updated. [0092] updateType="UpdateVnffg" to indicate the type of update operation. [0093] UpdateVnffgData: the information of the external connectivity (see clause 8.3.4.22.2 of [5]): [0094] vnffgId: Identifier of an existing VNFFG information element to be updated for the NS instance; [0095] nfp: Indicate the desired new NFP(s) for a given VNFFG, and may contain one or more of the following attributes: [0096] nfpName: Human readable name for the NFP; [0097] description: Human readable description for the NFP; [0098] cp: Identifier(s) of the CPs and SAPs which the NFP passes by; [0099] nfpRule: NFP classification and selection rule. [0100] nfpId: Indicate the identifier of the NFP to be modified. [0101] 2. NFVO sends to NM an UpdateNsResponse (see clause 7.3.5 of [5]) with the attribute lifecycleOperationOccurrenceId that is the identifier of the NS lifecycle operation occurrence. [0102] 3. NFVO sends to NM a Notify (see clause 7.4.3 [5]) carrying an NsLifecycleChangeNotification information element with attributes nsInstanceId, lifecycleOperationOccurrenceId, operation="NsUpdate", and notificationType="start" to indicate the start of the NS instantiation (see clause 8.3.2.2 [5]). [0103] 4. NFVO sends to NM a Notify (see clause 7.4.3 [5]) carrying an NsLifecycleChangeNotification information element with attributes nsInstanceId, lifecycleOperationOccurrenceId, operation="NsUpdate", and notificationType="result" to indicate the end result of the NS instantiation (see clause 8.3.2.2 [5]).
[0104] FIG. 5 is a diagram of an NS update to add a VNFFG to an NS instance in accordance with one or more embodiments. As shown in FIG. 5, in NS update procedure 500, NM 212 sends an UpdateNsRequest--AddVnffg message to NFVO 232 at operation 510. NFVO 232 sends an UpdateNsResponse message to NM 212 at operation 512. NFVO 232 then sends a Notify--NsLifecycleChangeNotification (start) message to NM 212 at operation 514. NFVO 232 then sends a Notify--NsIdentifierChangeNotification (result) message to NM 212 at operation 516. Details of NS update procedure 500 to add a VNFFG are described below.
4.4.5,x NS Update to Add a VNFFG
[0105] Figure 4.4.5.x-1 depicts the procedure of NS update to add a VNFFG to a NS instance (see clause 7.3.5 [5]). [0106] 1. NM sends to NFVO an UpdateNsRequest (see clause 7.3.5 of [5]) with the following parameters (see clause 7.3.5.2 of [5]) to on-board the NSD: [0107] nsInstanceId: the identifier of the NS instance being updated. [0108] updateType="AddVnffg" to indicate the type of update operation. [0109] AddVnffgData: the information of the VNFFG to be added (see clause 8.3.4.21.2 of [5]): [0110] vnffgdId: Identifier of the VNFFGD which defines the VNFFG to be added; [0111] vnffgName: Human readable name for the VNFFG. [0112] description: Human readable description for the VNFFG. [0113] nfp: indicate the NFP classification and selection rule for the new NFP to be added to the VNFFG instance. [0114] Note: > nfp is currently not defined in clause 5.3.4.22.2 in [5]. [0115] 2. NFVO sends to NM an UpdateNsResponse (see clause 7.3.5 of [5]) with the attribute: [0116] nsInstanceId: the identifier of the NS instance lifecycleOperationOccurrenceId that is the identifier of the NS lifecycle operation occurrence; [0117] addedVnffgInfo: Information of the of the created VNFFG instance. [0118] vnffgId: Identifier of the VNFFG instance in which the NFP instances are contained; [0119] nfpId: Identifier(s) of the NFP to be added to a given VNFFG. [0120] Note: addedVnffgInfo is currently not defined in clause 7.3.5.3 in [5]. [0121] 3. NFVO sends to NM a Notify (see clause 7.4.3 [5]) carrying an NsLifecycleChangeNotification information element with attributes nsInstanceId, lifecycleOperationOccurrenceId, operation="NsUpdate", and notificationType="start" to indicate the start of the NS instantiation (see clause 8.3.2.2 [5]). [0122] 4. NFVO sends to NM a Notify (see clause 7.4.3 [5]) carrying an NsLifecycleChangeNotification information element with attributes nsInstanceId, lifecycleOperationOccurrenceId, operation="NsUpdate", and notificationType="result" to indicate the end result of the NS instantiation (see clause 8.3.2.2 [5]).
[0123] FIG. 6 illustrates an architecture of a system 600 of a network in accordance with some embodiments. The system 600 is shown to include a user equipment (UE) 601 and a UE 602. The UEs 601 and 602 are illustrated as smartphones (e.g., handheld touchscreen mobile computing devices connectable to one or more cellular networks) but may also comprise any mobile or non-mobile computing device, such as Personal Data Assistants (PDAs), pagers, laptop computers, desktop computers, wireless handsets, or any computing device including a wireless communications interface.
[0124] In some embodiments, any of the UEs 601 and 602 can comprise an Internet of Things (IoT) UE, which can comprise a network access layer designed for low-power IoT applications utilizing short-lived UE connections. An IoT UE can utilize technologies such as machine-to-machine (M2M) or machine-type communications (MTC) for exchanging data with an MTC server or device via a public land mobile network (PLMN), Proximity-Based Service (ProSe) or device-to-device (D2D) communication, sensor networks, or IoT networks. The M2M or MTC exchange of data may be a machine-initiated exchange of data. An IoT network describes interconnecting IoT UEs, which may include uniquely identifiable embedded computing devices (within the Internet infrastructure), with short-lived connections. The IoT UEs may execute background applications (e.g., keep-alive messages, status updates, etc.) to facilitate the connections of the IoT network.
[0125] The UEs 601 and 602 may be configured to connect, e.g., communicatively couple, with a radio access network (RAN) 610--the RAN 610 may be, for example, an Evolved Universal Mobile Telecommunications System (UMTS) Terrestrial Radio Access Network (E-UTRAN), a NextGen RAN (NG RAN), or some other type of RAN. The UEs 601 and 602 utilize connections 603 and 604, respectively, each of which comprises a physical communications interface or layer (discussed in further detail below); in this example, the connections 603 and 604 are illustrated as an air interface to enable communicative coupling, and can be consistent with cellular communications protocols, such as a Global System for Mobile Communications (GSM) protocol, a code-division multiple access (CDMA) network protocol, a Push-to-Talk (PTT) protocol, a PTT over Cellular (POC) protocol, a Universal Mobile Telecommunications System (UMTS) protocol, a 3GPP Long Term Evolution (LTE) protocol, a fifth generation (5G) protocol, a New Radio (NR) protocol, and the like.
[0126] In this embodiment, the UEs 601 and 602 may further directly exchange communication data via a ProSe interface 605. The ProSe interface 605 may alternatively be referred to as a sidelink interface comprising one or more logical channels, including but not limited to a Physical Sidelink Control Channel (PSCCH), a Physical Sidelink Shared Channel (PSSCH), a Physical Sidelink Discovery Channel (PSDCH), and a Physical Sidelink Broadcast Channel (PSBCH).
[0127] The UE 602 is shown to be configured to access an access point (AP) 606 via connection 607. The connection 607 can comprise a local wireless connection, such as a connection consistent with any IEEE 802.11 protocol, wherein the AP 606 would comprise a wireless fidelity (WiFi.RTM.) router. In this example, the AP 606 is shown to be connected to the Internet without connecting to the core network of the wireless system (described in further detail below).
[0128] The RAN 610 can include one or more access nodes that enable the connections 603 and 604. These access nodes (ANs) can be referred to as base stations (BSs), NodeBs, evolved NodeBs (eNBs), next Generation NodeBs (gNB), RAN nodes, and so forth, and can comprise ground stations (e.g., terrestrial access points) or satellite stations providing coverage within a geographic area (e.g., a cell). The RAN 610 may include one or more RAN nodes for providing macrocells, e.g., macro RAN node 611, and one or more RAN nodes for providing femtocells or picocells (e.g., cells having smaller coverage areas, smaller user capacity, or higher bandwidth compared to macrocells), e.g., low power (LP) RAN node 612.
[0129] Any of the RAN nodes 611 and 612 can terminate the air interface protocol and can be the first point of contact for the UEs 601 and 602. In some embodiments, any of the RAN nodes 611 and 612 can fulfill various logical functions for the RAN 610 including, but not limited to, radio network controller (RNC) functions such as radio bearer management, uplink and downlink dynamic radio resource management and data packet scheduling, and mobility management.
[0130] In accordance with some embodiments, the UEs 601 and 602 can be configured to communicate using Orthogonal Frequency-Division Multiplexing (OFDM) communication signals with each other or with any of the RAN nodes 611 and 612 over a multicarrier communication channel in accordance various communication techniques, such as, but not limited to, an Orthogonal Frequency-Division Multiple Access (OFDMA) communication technique (e.g., for downlink communications) or a Single Carrier Frequency Division Multiple Access (SC-FDMA) communication technique (e.g., for uplink and ProSe or sidelink communications), although the scope of the embodiments is not limited in this respect. The OFDM signals can comprise a plurality of orthogonal subcarriers.
[0131] In some embodiments, a downlink resource grid can be used for downlink transmissions from any of the RAN nodes 611 and 612 to the UEs 601 and 602, while uplink transmissions can utilize similar techniques. The grid can be a time-frequency grid, called a resource grid or time-frequency resource grid, which is the physical resource in the downlink in each slot. Such a time-frequency plane representation is a common practice for OFDM systems, which makes it intuitive for radio resource allocation. Each column and each row of the resource grid corresponds to one OFDM symbol and one OFDM subcarrier, respectively. The duration of the resource grid in the time domain corresponds to one slot in a radio frame. The smallest time-frequency unit in a resource grid is denoted as a resource element. Each resource grid comprises a number of resource blocks, which describe the mapping of certain physical channels to resource elements. Each resource block comprises a collection of resource elements; in the frequency domain, this may represent the smallest quantity of resources that currently can be allocated. There are several different physical downlink channels that are conveyed using such resource blocks.
[0132] The physical downlink shared channel (PDSCH) may carry user data and higher-layer signaling to the UEs 601 and 602. The physical downlink control channel (PDCCH) may carry information about the transport format and resource allocations related to the PDSCH channel, among other things. It may also inform the UEs 601 and 602 about the transport format, resource allocation, and H-ARQ (Hybrid Automatic Repeat Request) information related to the uplink shared channel. Typically, downlink scheduling (assigning control and shared channel resource blocks to the UE 102 within a cell) may be performed at any of the RAN nodes 611 and 612 based on channel quality information fed back from any of the UEs 601 and 602. The downlink resource assignment information may be sent on the PDCCH used for (e.g., assigned to) each of the UEs 601 and 602.
[0133] The PDCCH may use control channel elements (CCEs) to convey the control information. Before being mapped to resource elements, the PDCCH complex-valued symbols may first be organized into quadruplets, which may then be permuted using a sub-block interleaver for rate matching. Each PDCCH may be transmitted using one or more of these CCEs, where each CCE may correspond to nine sets of four physical resource elements known as resource element groups (REGs). Four Quadrature Phase Shift Keying (QPSK) symbols may be mapped to each REG. The PDCCH can be transmitted using one or more CCEs, depending on the size of the downlink control information (DCI) and the channel condition. There can be four or more different PDCCH formats defined in LTE with different numbers of CCEs (e.g., aggregation level, L=1, 2, 4, or 8).
[0134] Some embodiments may use concepts for resource allocation for control channel information that are an extension of the above-described concepts. For example, some embodiments may utilize an enhanced physical downlink control channel (EPDCCH) that uses PDSCH resources for control information transmission. The EPDCCH may be transmitted using one or more enhanced the control channel elements (ECCEs). Similar to above, each ECCE may correspond to nine sets of four physical resource elements known as an enhanced resource element groups (EREGs). An ECCE may have other numbers of EREGs in some situations.
[0135] The RAN 610 is shown to be communicatively coupled to a core network (CN) 620--via an S1 interface 613. In embodiments, the CN 620 may be an evolved packet core (EPC) network, a NextGen Packet Core (NPC) network, or some other type of CN. In this embodiment the S1 interface 613 is split into two parts: the S1-U interface 614, which carries traffic data between the RAN nodes 611 and 612 and the serving gateway (S-GW) 622, and the S1-mobility management entity (MME) interface 615, which is a signaling interface between the RAN nodes 611 and 612 and MMEs 621.
[0136] In this embodiment, the CN 620 comprises the MMEs 621, the S-GW 622, the Packet Data Network (PDN) Gateway (P-GW) 623, and a home subscriber server (HSS) 624. The MMEs 621 may be similar in function to the control plane of legacy Serving General Packet Radio Service (GPRS) Support Nodes (SGSN). The MMEs 621 may manage mobility aspects in access such as gateway selection and tracking area list management. The HSS 624 may comprise a database for network users, including subscription-related information to support the network entities' handling of communication sessions. The CN 620 may comprise one or several HSSs 624, depending on the number of mobile subscribers, on the capacity of the equipment, on the organization of the network, etc. For example, the HSS 624 can provide support for routing/roaming, authentication, authorization, naming/addressing resolution, location dependencies, etc.
[0137] The S-GW 622 may terminate the S1 interface 613 towards the RAN 610, and routes data packets between the RAN 610 and the CN 620. In addition, the S-GW 622 may be a local mobility anchor point for inter-RAN node handovers and also may provide an anchor for inter-3GPP mobility. Other responsibilities may include lawful intercept, charging, and some policy enforcement.
[0138] The P-GW 623 may terminate an SGi interface toward a PDN. The P-GW 623 may route data packets between the EPC network 623 and external networks such as a network including the application server 630 (alternatively referred to as application function (AF)) via an Internet Protocol (IP) interface 625. Generally, the application server 630 may be an element offering applications that use IP bearer resources with the core network (e.g., UMTS Packet Services (PS) domain, LTE PS data services, etc.). In this embodiment, the P-GW 623 is shown to be communicatively coupled to an application server 630 via an IP communications interface 625. The application server 630 can also be configured to support one or more communication services (e.g., Voice-over-Internet Protocol (VoIP) sessions, PTT sessions, group communication sessions, social networking services, etc.) for the UEs 601 and 602 via the CN 620.
[0139] The P-GW 623 may further be a node for policy enforcement and charging data collection. Policy and Charging Enforcement Function (PCRF) 626 is the policy and charging control element of the CN 620. In a non-roaming scenario, there may be a single PCRF in the Home Public Land Mobile Network (HPLMN) associated with a UE's Internet Protocol Connectivity Access Network (IP-CAN) session. In a roaming scenario with local breakout of traffic, there may be two PCRFs associated with a UE's IP-CAN session: a Home PCRF (H-PCRF) within a HPLMN and a Visited PCRF (V-PCRF) within a Visited Public Land Mobile Network (VPLMN). The PCRF 626 may be communicatively coupled to the application server 630 via the P-GW 623. The application server 630 may signal the PCRF 626 to indicate a new service flow and select the appropriate Quality of Service (QoS) and charging parameters. The PCRF 626 may provision this rule into a Policy and Charging Enforcement Function (PCEF) (not shown) with the appropriate traffic flow template (TFT) and QoS class of identifier (QCI), which commences the QoS and charging as specified by the application server 630.
[0140] FIG. 7 illustrates example components of a device 700 in accordance with some embodiments. In some embodiments, the device 700 may include application circuitry 702, baseband circuitry 704, Radio Frequency (RF) circuitry 706, front-end module (FEM) circuitry 708, one or more antennas 710, and power management circuitry (PMC) 712 coupled together at least as shown. The components of the illustrated device 700 may be included in a UE or a RAN node. In some embodiments, the device 700 may include less elements (e.g., a RAN node may not utilize application circuitry 702, and instead include a processor/controller to process IP data received from an EPC). In some embodiments, the device 700 may include additional elements such as, for example, memory/storage, display, camera, sensor, or input/output (I/O) interface. In other embodiments, the components described below may be included in more than one device (e.g., said circuitries may be separately included in more than one device for Cloud-RAN (C-RAN) implementations).
[0141] The application circuitry 702 may include one or more application processors. For example, the application circuitry 702 may include circuitry such as, but not limited to, one or more single-core or multi-core processors. The processor(s) may include any combination of general-purpose processors and dedicated processors (e.g., graphics processors, application processors, etc.). The processors may be coupled with or may include memory/storage and may be configured to execute instructions stored in the memory/storage to enable various applications or operating systems to run on the device 700. In some embodiments, processors of application circuitry 702 may process IP data packets received from an EPC.
[0142] The baseband circuitry 704 may include circuitry such as, but not limited to, one or more single-core or multi-core processors. The baseband circuitry 704 may include one or more baseband processors or control logic to process baseband signals received from a receive signal path of the RF circuitry 706 and to generate baseband signals for a transmit signal path of the RF circuitry 706. Baseband processing circuitry 704 may interface with the application circuitry 702 for generation and processing of the baseband signals and for controlling operations of the RF circuitry 706. For example, in some embodiments, the baseband circuitry 704 may include a third generation (3G) baseband processor 704A, a fourth generation (4G) baseband processor 704B, a fifth generation (5G) baseband processor 704C, or other baseband processor(s) 704D for other existing generations, generations in development or to be developed in the future (e.g., second generation (2G), sixth generation (6G), etc.). The baseband circuitry 704 (e.g., one or more of baseband processors 704A-D) may handle various radio control functions that enable communication with one or more radio networks via the RF circuitry 706. In other embodiments, some or all of the functionality of baseband processors 704A-D may be included in modules stored in the memory 704G and executed via a Central Processing Unit (CPU) 704E. The radio control functions may include, but are not limited to, signal modulation/demodulation, encoding/decoding, radio frequency shifting, etc. In some embodiments, modulation/demodulation circuitry of the baseband circuitry 704 may include Fast-Fourier Transform (FFT), precoding, or constellation mapping/demapping functionality. In some embodiments, encoding/decoding circuitry of the baseband circuitry 704 may include convolution, tail-biting convolution, turbo, Viterbi, or Low Density Parity Check (LDPC) encoder/decoder functionality. Embodiments of modulation/demodulation and encoder/decoder functionality are not limited to these examples and may include other suitable functionality in other embodiments.
[0143] In some embodiments, the baseband circuitry 704 may include one or more audio digital signal processor(s) (DSP) 704F. The audio DSP(s) 704F may be include elements for compression/decompression and echo cancellation and may include other suitable processing elements in other embodiments. Components of the baseband circuitry may be suitably combined in a single chip, a single chipset, or disposed on a same circuit board in some embodiments. In some embodiments, some or all of the constituent components of the baseband circuitry 704 and the application circuitry 702 may be implemented together such as, for example, on a system on a chip (SOC).
[0144] In some embodiments, the baseband circuitry 704 may provide for communication compatible with one or more radio technologies. For example, in some embodiments, the baseband circuitry 704 may support communication with an evolved universal terrestrial radio access network (EUTRAN) or other wireless metropolitan area networks (WMAN), a wireless local area network (WLAN), a wireless personal area network (WPAN). Embodiments in which the baseband circuitry 704 is configured to support radio communications of more than one wireless protocol may be referred to as multi-mode baseband circuitry.
[0145] RF circuitry 706 may enable communication with wireless networks using modulated electromagnetic radiation through a non-solid medium. In various embodiments, the RF circuitry 706 may include switches, filters, amplifiers, etc. to facilitate the communication with the wireless network. RF circuitry 706 may include a receive signal path which may include circuitry to down-convert RF signals received from the FEM circuitry 708 and provide baseband signals to the baseband circuitry 704. RF circuitry 706 may also include a transmit signal path which may include circuitry to up-convert baseband signals provided by the baseband circuitry 704 and provide RF output signals to the FEM circuitry 708 for transmission.
[0146] In some embodiments, the receive signal path of the RF circuitry 706 may include mixer circuitry 706a, amplifier circuitry 706b and filter circuitry 706c. In some embodiments, the transmit signal path of the RF circuitry 706 may include filter circuitry 706c and mixer circuitry 706a. RF circuitry 706 may also include synthesizer circuitry 706d for synthesizing a frequency for use by the mixer circuitry 706a of the receive signal path and the transmit signal path. In some embodiments, the mixer circuitry 706a of the receive signal path may be configured to down-convert RF signals received from the FEM circuitry 708 based on the synthesized frequency provided by synthesizer circuitry 706d. The amplifier circuitry 706b may be configured to amplify the down-converted signals and the filter circuitry 706c may be a low-pass filter (LPF) or band-pass filter (BPF) configured to remove unwanted signals from the down-converted signals to generate output baseband signals. Output baseband signals may be provided to the baseband circuitry 704 for further processing. In some embodiments, the output baseband signals may be zero-frequency baseband signals, although this is not a requirement. In some embodiments, mixer circuitry 706a of the receive signal path may comprise passive mixers, although the scope of the embodiments is not limited in this respect.
[0147] In some embodiments, the mixer circuitry 706a of the transmit signal path may be configured to up-convert input baseband signals based on the synthesized frequency provided by the synthesizer circuitry 706d to generate RF output signals for the FEM circuitry 708. The baseband signals may be provided by the baseband circuitry 704 and may be filtered by filter circuitry 706c.
[0148] In some embodiments, the mixer circuitry 706a of the receive signal path and the mixer circuitry 706a of the transmit signal path may include two or more mixers and may be arranged for quadrature downconversion and upconversion, respectively. In some embodiments, the mixer circuitry 706a of the receive signal path and the mixer circuitry 706a of the transmit signal path may include two or more mixers and may be arranged for image rejection (e.g., Hartley image rejection). In some embodiments, the mixer circuitry 706a of the receive signal path and the mixer circuitry 706a may be arranged for direct downconversion and direct upconversion, respectively. In some embodiments, the mixer circuitry 706a of the receive signal path and the mixer circuitry 706a of the transmit signal path may be configured for super-heterodyne operation.
[0149] In some embodiments, the output baseband signals and the input baseband signals may be analog baseband signals, although the scope of the embodiments is not limited in this respect. In some alternate embodiments, the output baseband signals and the input baseband signals may be digital baseband signals. In these alternate embodiments, the RF circuitry 706 may include analog-to-digital converter (ADC) and digital-to-analog converter (DAC) circuitry and the baseband circuitry 704 may include a digital baseband interface to communicate with the RF circuitry 706. In some dual-mode embodiments, a separate radio IC circuitry may be provided for processing signals for each spectrum, although the scope of the embodiments is not limited in this respect.
[0150] In some embodiments, the synthesizer circuitry 706d may be a fractional-N synthesizer or a fractional N/N+1 synthesizer, although the scope of the embodiments is not limited in this respect as other types of frequency synthesizers may be suitable. For example, synthesizer circuitry 706d may be a delta-sigma synthesizer, a frequency multiplier, or a synthesizer comprising a phase-locked loop with a frequency divider. The synthesizer circuitry 706d may be configured to synthesize an output frequency for use by the mixer circuitry 706a of the RF circuitry 706 based on a frequency input and a divider control input. In some embodiments, the synthesizer circuitry 706d may be a fractional N/N+1 synthesizer.
[0151] In some embodiments, frequency input may be provided by a voltage-controlled oscillator (VCO), although that is not a requirement. Divider control input may be provided by either the baseband circuitry 704 or the applications processor 702 depending on the desired output frequency. In some embodiments, a divider control input (e.g., N) may be determined from a look-up table based on a channel indicated by the applications processor 702.
[0152] Synthesizer circuitry 706d of the RF circuitry 706 may include a divider, a delay-locked loop (DLL), a multiplexer and a phase accumulator. In some embodiments, the divider may be a dual modulus divider (DMD) and the phase accumulator may be a digital phase accumulator (DPA). In some embodiments, the DMD may be configured to divide the input signal by either N or N+1 (e.g., based on a carry out) to provide a fractional division ratio. In some example embodiments, the DLL may include a set of cascaded, tunable, delay elements, a phase detector, a charge pump and a D-type flip-flop. In these embodiments, the delay elements may be configured to break a VCO period up into Nd equal packets of phase, where Nd is the number of delay elements in the delay line. In this way, the DLL provides negative feedback to help ensure that the total delay through the delay line is one VCO cycle.
[0153] In some embodiments, synthesizer circuitry 706d may be configured to generate a carrier frequency as the output frequency, while in other embodiments, the output frequency may be a multiple of the carrier frequency (e.g., twice the carrier frequency, four times the carrier frequency) and used in conjunction with quadrature generator and divider circuitry to generate multiple signals at the carrier frequency with multiple different phases with respect to each other. In some embodiments, the output frequency may be a LO frequency (fLO). In some embodiments, the RF circuitry 706 may include an IQ/polar converter.
[0154] FEM circuitry 708 may include a receive signal path which may include circuitry configured to operate on RF signals received from one or more antennas 710, amplify the received signals and provide the amplified versions of the received signals to the RF circuitry 706 for further processing. FEM circuitry 708 may also include a transmit signal path which may include circuitry configured to amplify signals for transmission provided by the RF circuitry 706 for transmission by one or more of the one or more antennas 710. In various embodiments, the amplification through the transmit or receive signal paths may be done solely in the RF circuitry 706, solely in the FEM 708, or in both the RF circuitry 706 and the FEM 708.
[0155] In some embodiments, the FEM circuitry 708 may include a TX/RX switch to switch between transmit mode and receive mode operation. The FEM circuitry may include a receive signal path and a transmit signal path. The receive signal path of the FEM circuitry may include an LNA to amplify received RF signals and provide the amplified received RF signals as an output (e.g., to the RF circuitry 706). The transmit signal path of the FEM circuitry 708 may include a power amplifier (PA) to amplify input RF signals (e.g., provided by RF circuitry 706), and one or more filters to generate RF signals for subsequent transmission (e.g., by one or more of the one or more antennas 710).
[0156] In some embodiments, the PMC 712 may manage power provided to the baseband circuitry 704. In particular, the PMC 712 may control power-source selection, voltage scaling, battery charging, or DC-to-DC conversion. The PMC 712 may often be included when the device 700 is capable of being powered by a battery, for example, when the device is included in a UE. The PMC 712 may increase the power conversion efficiency while providing desirable implementation size and heat dissipation characteristics.
[0157] While FIG. 7 shows the PMC 712 coupled only with the baseband circuitry 704. In other embodiments, however, the PMC 712 may be additionally or alternatively coupled with, and perform similar power management operations for, other components such as, but not limited to, application circuitry 702, RF circuitry 706, or FEM 708.
[0158] In some embodiments, the PMC 712 may control, or otherwise be part of, various power saving mechanisms of the device 700. For example, if the device 700 is in an RRC_Connected state, where it is still connected to the RAN node as it expects to receive traffic shortly, then it may enter a state known as Discontinuous Reception Mode (DRX) after a period of inactivity. During this state, the device 700 may power down for brief intervals of time and thus save power.
[0159] If there is no data traffic activity for an extended period of time, then the device 700 may transition off to an RRC_Idle state, where it disconnects from the network and does not perform operations such as channel quality feedback, handover, etc. The device 700 goes into a very low power state and it performs paging where again it periodically wakes up to listen to the network and then powers down again. The device 700 may not receive data in this state, in order to receive data, it must transition back to RRC_Connected state.
[0160] An additional power saving mode may allow a device to be unavailable to the network for periods longer than a paging interval (ranging from seconds to a few hours). During this time, the device is totally unreachable to the network and may power down completely. Any data sent during this time incurs a large delay and it is assumed the delay is acceptable.
[0161] Processors of the application circuitry 702 and processors of the baseband circuitry 704 may be used to execute elements of one or more instances of a protocol stack. For example, processors of the baseband circuitry 704, alone or in combination, may be used execute Layer 3, Layer 2, or Layer 1 functionality, while processors of the application circuitry 704 may utilize data (e.g., packet data) received from these layers and further execute Layer 4 functionality (e.g., transmission communication protocol (TCP) and user datagram protocol (UDP) layers). As referred to herein, Layer 3 may comprise a radio resource control (RRC) layer, described in further detail below. As referred to herein, Layer 2 may comprise a medium access control (MAC) layer, a radio link control (RLC) layer, and a packet data convergence protocol (PDCP) layer, described in further detail below. As referred to herein, Layer 1 may comprise a physical (PHY) layer of a UE/RAN node, described in further detail below.
[0162] FIG. 8 illustrates example interfaces of baseband circuitry in accordance with some embodiments. As discussed above, the baseband circuitry 704 of FIG. 7 may comprise processors 704A-704E and a memory 704G utilized by said processors. Each of the processors 704A-704E may include a memory interface, 804A-804E, respectively, to send/receive data to/from the memory 704G.
[0163] The baseband circuitry 704 may further include one or more interfaces to communicatively couple to other circuitries/devices, such as a memory interface 812 (e.g., an interface to send/receive data to/from memory external to the baseband circuitry 704), an application circuitry interface 814 (e.g., an interface to send/receive data to/from the application circuitry 702 of FIG. 7), an RF circuitry interface 816 (e.g., an interface to send/receive data to/from RF circuitry 706 of FIG. 7), a wireless hardware connectivity interface 818 (e.g., an interface to send/receive data to/from Near Field Communication (NFC) components, Bluetooth.RTM. components (e.g., Bluetooth.RTM. Low Energy), Wi-Fi.RTM. components, and other communication components), and a power management interface 820 (e.g., an interface to send/receive power or control signals to/from the PMC 712.
[0164] Although the claimed subject matter has been described with a certain degree of particularity, it should be recognized that elements thereof may be altered by persons skilled in the art without departing from the spirit and/or scope of claimed subject matter. It is believed that the subject matter pertaining to managing virtual links in a network service instance and many of its attendant utilities will be understood by the forgoing description, and it will be apparent that various changes may be made in the form, construction and/or arrangement of the components thereof without departing from the scope and/or spirit of the claimed subject matter or without sacrificing all of its material advantages, the form herein before described being merely an explanatory embodiment thereof, and/or further without providing substantial change thereto. It is the intention of the claims to encompass and/or include such changes.
* * * * *
D00000

D00001
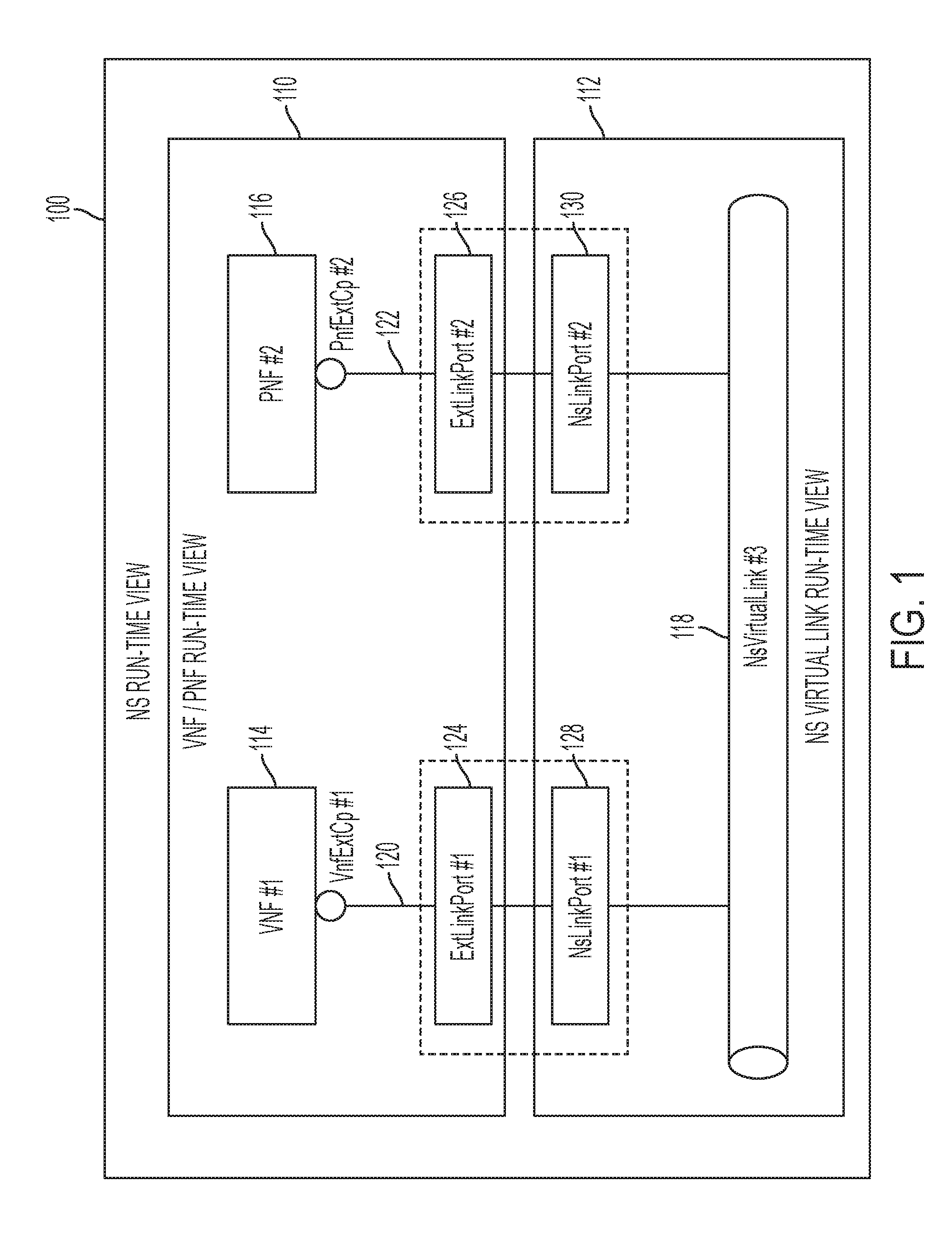
D00002

D00003

D00004

D00005

D00006

D00007

D00008

XML
uspto.report is an independent third-party trademark research tool that is not affiliated, endorsed, or sponsored by the United States Patent and Trademark Office (USPTO) or any other governmental organization. The information provided by uspto.report is based on publicly available data at the time of writing and is intended for informational purposes only.
While we strive to provide accurate and up-to-date information, we do not guarantee the accuracy, completeness, reliability, or suitability of the information displayed on this site. The use of this site is at your own risk. Any reliance you place on such information is therefore strictly at your own risk.
All official trademark data, including owner information, should be verified by visiting the official USPTO website at www.uspto.gov. This site is not intended to replace professional legal advice and should not be used as a substitute for consulting with a legal professional who is knowledgeable about trademark law.