Systems And Methods For Analyzing Snapshots
Ngo; David
U.S. patent application number 16/503411 was filed with the patent office on 2019-10-24 for systems and methods for analyzing snapshots. The applicant listed for this patent is Commvault Systems, Inc.. Invention is credited to David Ngo.
| Application Number | 20190324860 16/503411 |
| Document ID | / |
| Family ID | 44188688 |
| Filed Date | 2019-10-24 |









| United States Patent Application | 20190324860 |
| Kind Code | A1 |
| Ngo; David | October 24, 2019 |
SYSTEMS AND METHODS FOR ANALYZING SNAPSHOTS
Abstract
This application describes techniques for creating a second snapshot of a first snapshot of a set of data, modifying the first snapshot, and reverting the modifications to the first snapshot. For example, portions of one or more transaction logs may be played into a database to put the database in a particular state a particular point in time. The second snapshot may then be used to revert to a prior state of the database such that additional transaction logs may be played into the database. These techniques enable the ability to put the database into multiple states as the database existed at multiple points in time. Therefore, data can be recovered from the database as the data existed at different points in time. Moreover, individual data objects in the database can be accessed and analyzed as the individual data objects existed at different points in time.
| Inventors: | Ngo; David; (Shrewsbury, NJ) | ||||||||||
| Applicant: |
|
||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|
| Family ID: | 44188688 | ||||||||||
| Appl. No.: | 16/503411 | ||||||||||
| Filed: | July 3, 2019 |
Related U.S. Patent Documents
| Application Number | Filing Date | Patent Number | ||
|---|---|---|---|---|
| 15069228 | Mar 14, 2016 | 10379957 | ||
| 16503411 | ||||
| 13874323 | Apr 30, 2013 | 9298559 | ||
| 15069228 | ||||
| 12978984 | Dec 27, 2010 | 8433682 | ||
| 13874323 | ||||
| 61291805 | Dec 31, 2009 | |||
| Current U.S. Class: | 1/1 |
| Current CPC Class: | G06F 11/1461 20130101; G06F 11/1471 20130101; G06F 2201/84 20130101; G06F 11/1446 20130101; G06F 16/2477 20190101; G06F 2201/80 20130101; G06F 11/1448 20130101 |
| International Class: | G06F 11/14 20060101 G06F011/14; G06F 16/2458 20060101 G06F016/2458 |
Claims
1. At least one non-transitory, computer-readable medium carrying instructions, which when executed by at least one data processing device, executes operations for analyzing a snapshot of a set of data, the operations comprising: causing to be generated, by the least one data processing device, a first snapshot of a set of data at a first time, wherein the first snapshot captures a first state of the set of data at the first time, and wherein the set of data includes multiple data objects; causing to be generated a second snapshot at a second, later time, wherein the second snapshot captures a second state of the set of data at the second time; causing to be generated, before an accessing of the at least one of the multiple data objects, a snapshot of the second snapshot and at least one associated transaction log; and permitting to be accessed, via the first snapshot, at least one of the multiple data objects.
2. The tangible computer-readable medium of claim 1, further comprising causing a reversion to the second state of the set of data.
3. The tangible computer-readable medium of claim 1, wherein the second snapshot includes a copy of logical associations for the first snapshot.
4. The tangible computer-readable medium of claim 1, further comprising modifying the first snapshot after the second snapshot is generated.
5. The tangible computer-readable medium of claim 1, wherein causing the first snapshot of the set of data to be generated includes causing to be generated the first snapshot of the set of data at least partly with a software-based snapshot provider.
6. The tangible computer-readable medium of claim 1, wherein causing the first snapshot of the set of data to be generated includes causing to be generated the first snapshot of the set of data at least partly with a hardware-based snapshot provider.
7. The tangible computer-readable medium of claim 1, wherein the set of data includes a database and database logs, and the method further comprises modifying the first snapshot by playing one or more database logs into the database.
8. The tangible computer-readable medium of claim 1, further comprising reverting to the second state of the set of data by performing a revert operation utilizing the snapshot of the second snapshot.
9. The tangible computer-readable medium of claim 1, wherein the set of data is utilized by an application, and wherein the application includes either an email server, a Structured Query Language (SQL) server, a file server, or an application server.
10. The tangible computer-readable medium of claim 1, further comprising, modifying the first snapshot, and after reverting to the second state of the set of data, modifying the first snapshot again.
11. The tangible computer-readable medium of claim 1, further comprising causing at least one operation on the accessed one or more multiple data objects to be performed, wherein the at least one operation includes-- indexing the multiple data objects and adding information to an index, or associating the multiple data objects with one or more classifications and storing the one or more classifications in a metabase, or extracting the multiple data objects from the set of data and copying the multiple data objects to a storage device.
12. At least one non-transitory, computer-readable medium carrying instructions, which when executed by at least one computing device, performs operations for analyzing data, the operations comprising: receiving at least one replication log indicating at least one change to a first data set, wherein the first data set includes one or more individual data objects, wherein the least one replication log can be utilized to implement the at least one change to a second data set as the first data set existed at a first point in time, and wherein the least one replication log or data associated therewith includes at least one indication of a second point in time at which the first data set is consistent; utilizing, by the computing device, the least one replication log to cause the at least one change to the second data to be generated; causing to be created a snapshot of the second data at or near the second point in time; analyzing the snapshot of the second data changed according to the least one replication log; and accessing the one or more of the individual data objects as the data objects existed at the second point in time.
13. The at least one computer-readable medium of claim 12 wherein the second data includes a database and at least one database log, wherein the least one replication log includes modifications to the database and/or the at least one database log, and wherein utilizing the least one replication log to replicate the changes to the second data includes modifying the database using the at least one database log.
14. The at least one computer-readable medium of claim 12 wherein analyzing the snapshot of the second data includes performing at least one modification to the snapshot of the second data, and the method further comprises: after analyzing the snapshot of the second data, reverting the snapshot of the second data; and after reverting the snapshot of the second data, utilizing least one replication log to replicate additional changes to the second data.
15. The at least one computer-readable medium of claim 12 wherein the first data set includes a database, and wherein the method further comprises creating a first snapshot of both the database and transaction or replication logs associated with the database, playing portions of one or more of the logs to commit corresponding changes to the database, and creating a second snapshot of the first snapshot, wherein a user can analyze data in the database as the database existed as of a time that the logs were played into the database.
16. The at least one computer-readable medium of claim 12, wherein the method further comprises: causing an initial full second data to be created, thereafter causing a snapshot of the first data set to be created, and thereafter, causing incremental copies or snapshots of the first data set and the logs to be created.
17. The at least one computer-readable medium of claim 12, wherein the method further comprises performing at least one test of the first snapshot in order to validate or verify the snapshot and ensure that the first data set was correctly copied.
18. At least one non-transitory, computer-readable medium carrying instructions, which when executed by at least one computing device, performs operations for modifying data, the operations comprising: creating a second snapshot of a first snapshot of a set of data, wherein the set of data is for a database; modifying the first snapshot; and reverting the modifications to the first snapshot, wherein the reverting includes employ portions of one or more transaction logs to revert the set of data for the database to a first state corresponding to a first point in time for the first snapshot, and wherein the second snapshot is configured to revert the set of data for the database to a second state by employing portions of one or more additional transaction logs, so that the operations enable the set of data for the database to be put into multiple states corresponding to when the database existed at multiple points in time and allowing recovery of data from the database as the data existed at different points in time.
19. The at least one computer-readable medium of claim 18, wherein the first snapshot is a snapshot of both the set of data for the database and transaction logs associated with the database, wherein the portions of one or more transaction logs are usable to commit corresponding changes to the database.
20. The at least one computer-readable medium of claim 18, wherein the first snapshot is a snapshot of both the set of data for the database and transaction logs associated with the database, wherein the portions of one or more transaction logs are usable to commit corresponding changes to the database.
Description
CROSS-REFERENCE TO RELATED APPLICATIONS
[0001] This application is a continuation of U.S. patent application Ser. No. 15/069,228, filed Mar. 14, 2016, which is a continuation of U.S. patent application Ser. No. 13/874,323, entitled "SYSTEMS AND METHODS FOR ANALYZING SNAPSHOTS," filed Apr. 30, 2013, now U.S. Pat. No. 9,298,559, which is a continuation of U.S. patent application Ser. No. 12/978,984, entitled "SYSTEMS AND METHODS FOR ANALYZING SNAPSHOTS," filed Dec. 27, 2010, now U.S. Pat. No. 8,433,682, which claims priority to and the benefit of U.S. Patent Application No. 61/291,805, entitled "SYSTEMS AND METHODS FOR ANALYZING SNAPSHOTS," filed on Dec. 31, 2009, and is related to U.S. patent application Ser. No. 12/558,947, entitled "USING A SNAPSHOT AS A DATA SOURCE," filed on Sep. 14, 2009 and U.S. patent application Ser. No. 12/979,101 filed on Dec. 27, 2010, entitled "SYSTEMS AND METHODS FOR PERFORMING DATA MANAGEMENT OPERATIONS USING SNAPSHOTS," each of which is incorporated by reference in its entirety.
BACKGROUND
[0002] A transactional database application, such as Microsoft SQL Server or Microsoft Exchange Server, typically writes transactions to transaction logs prior to committing the transactions to the database. The database application then commits the transactions in the transaction logs to the database as permitted.
[0003] An administrator typically protects the data of the transactional database application by directing data protection software to periodically perform a full backup (or other data protection operation) of the database and the transaction logs, as well as additional incremental backups (or other data protection operations) to capture changed data. For example, the administrator may direct the software to perform a full snapshot copy of the database and the transaction logs. The administrator may then direct the software to perform additional snapshots of the database and the transaction logs to capture data that has changed, such as additional transaction logs, since the full snapshot copy was performed.
[0004] In order to recover the transactional database application as it existed at a specific point in time, the administrator typically directs the software to recover the database and then "play" the necessary transaction logs. Playing (alternatively referred to as replaying or applying) transaction logs refers to committing transactions in the transaction logs to the database. This brings the transactional database application to the state it was in at the specific point in time. However, once the administrator has recovered the transactional database application, the administrator is typically not able to play additional transaction logs to bring the transactional database application to a state at a later point in time. Stated another way, once a database is put into a state corresponding to a particular point in time in order to recover data from the database as the data existed at that particular point in time, the administrator cannot put the database into another state corresponding to another point in time in order to recover data from the database as the data existed at the other point in time.
[0005] The need exists for a system that overcomes the above problems, as well as one that provides additional benefits. Overall, the examples herein of some prior or related systems and their associated limitations are intended to be illustrative and not exclusive. Other limitations of existing or prior systems will become apparent to those of skill in the art upon reading the following Detailed Description.
BRIEF DESCRIPTION OF THE DRAWINGS
[0006] FIG. 1 is a block diagram illustrating an example of a data storage enterprise that may employ aspects of the invention.
[0007] FIG. 2 is a block diagram illustrating in more detail certain components of a data storage system according to some examples.
[0008] FIG. 3 is a flow diagram of a process for analyzing a snapshot.
[0009] FIGS. 4A-4E are diagrams illustrating aspects of the process of FIG. 3.
[0010] FIG. 5 is a flow diagram of another process for analyzing a snapshot.
DETAILED DESCRIPTION
[0011] The headings provided herein are for convenience only and do not necessarily affect the scope or meaning of the claimed invention.
Overview
[0012] This application describes, among other things, techniques for creating a second snapshot of a first snapshot of a set of data, modifying the first snapshot, and reverting the modifications to the first snapshot. For example, the described techniques may be used to play portions of one or more transaction logs into a database to put the database in a particular state that corresponds to a particular point in time. The second snapshot may then be used to revert the database to a prior state such that additional transaction logs may be played into the database. These techniques enable the database to be put into multiple states that correspond to when the database existed at multiple points in time. Therefore, data can be recovered from the database as the data existed at different points in time. Moreover, individual data objects in the database can be accessed and analyzed as the individual data objects existed at different points in time.
[0013] In some examples, these techniques described herein involve creating a first snapshot of both a database and transaction logs associated with the database. Portions of one or more transaction logs may be played to commit corresponding changes to the database. A second snapshot is then taken of the first snapshot. The database can then be analyzed as it existed as of the time that the transaction logs were played into the database. Using the example of a Microsoft Exchange database, the database can be analyzed to read data from individual mailboxes, emails, attachments, etc. The second snapshot is then used to revert the database to the state it existed in as of the time the second snapshot was taken. Any number of transaction logs can then be played in order to put the database in a state that the database existed in at multiple points in time.
[0014] In some examples, the techniques described herein involve utilizing replication logs to take snapshots of a replication copy of data. The replication logs indicate changes to a first set of data, and can be used to replicate the changes to a second set of data that is a copy of the first set of data as the first set of data existed at a first point in time. The replication logs include at least one marker indicating a second point in time at which the first set of data is consistent. At least some of the replication logs are utilized to replicate at least some of the changes to the second set of data. Upon reaching the marker in the replication logs, a snapshot of the second set of data is created. The snapshot of the second set of data is analyzed, which may include accessing individual data objects within the second set of data.
[0015] Various examples of the invention will now be described. The following description provides specific details for a thorough understanding and enabling description of these examples. One skilled in the relevant art will understand, however, that the invention may be practiced without many of these details. Likewise, one skilled in the relevant art will also understand that the invention may include many other obvious features not described in detail herein. Additionally, some well-known structures or functions may not be shown or described in detail below, so as to avoid unnecessarily obscuring the relevant description.
[0016] The terminology used below is to be interpreted in its broadest reasonable manner, even though it is being used in conjunction with a detailed description of certain specific examples of the invention. Indeed, certain terms may even be emphasized below; however, any terminology intended to be interpreted in any restricted manner will be overtly and specifically defined as such in this Detailed Description section.
[0017] FIGS. 1 and 2 and the discussion herein provide a brief, general description of suitable specialized environments in which aspects of the invention can be implemented. Those skilled in the relevant art will appreciate that aspects of the invention can be practiced with other communications, data processing, or computer system configurations, including: Internet appliances, hand-held devices (including personal digital assistants (PDAs)), wearable computers, all manner of cellular phones, mobile phones, and/or mobile devices, multi-processor systems, microprocessor-based or programmable consumer electronics, set-top boxes, network PCs, mini-computers, mainframe computers, and the like. The terms "computer," "server," "host," "host system," "client," and the like are generally used interchangeably herein, and refer to any of the above devices and systems, as well as any data processor.
[0018] While aspects of the invention, such as certain functions, are described as being performed exclusively on a single device, the invention can also be practiced in distributed environments where functions or modules are shared among disparate processing devices, which are linked through a communications network, such as a Local Area Network (LAN), Wide Area Network (WAN), and/or the Internet. In a distributed computing environment, program modules may be located in both local and remote memory storage devices.
[0019] Aspects of the invention may be stored or distributed on computer-readable media, including tangible computer-readable storage media such as magnetically or optically readable computer discs, hard-wired or preprogrammed chips (e.g., EEPROM semiconductor chips), nanotechnology memory, biological memory, or other data storage media. Alternatively, computer implemented instructions, data structures, screen displays, and other data under aspects of the invention may be distributed over the Internet or over other networks (including wireless networks), on a propagated signal on a propagation medium (e.g., an electromagnetic wave(s), a sound wave, etc.) over a period of time, or they may be provided on any analog or digital network (packet switched, circuit switched, or other scheme).
[0020] Aspects of the invention will now be described in detail with respect to FIGS. 1 through 4. FIG. 1 illustrates an example of a data storage system that may employ aspects of the invention. FIG. 2 illustrates in more detail certain components of the example data storage system of FIG. 1. FIG. 3 illustrates a process for creating a second snapshot of a first snapshot of a set of data, such as a database and associated logs. FIGS. 4A-4E illustrate aspects of the process of FIG. 3 in more detail. FIG. 5 illustrates a process for utilizing consistency points to take snapshots of a set of data, such as a database and associated logs, in a data replication process.
Suitable Data Storage System
[0021] FIG. 1 illustrates an example of one arrangement of resources in a computing network, comprising a data storage system 150. The resources in the data storage system 150 may employ the processes and techniques described herein. The system 150 includes a storage manager 105, one or more data agents 195, one or more secondary storage computing devices 165, one or more storage devices 115, one or more computing devices 130 (called clients 130), one or more data or information stores 160 and 162, and a single instancing database 123. The storage manager 105 includes an index 111, a jobs agent 120, an interface agent 125, and a management agent 131. The system 150 may represent a modular storage system such as the CommVault QiNetix system, and also the CommVault GALAXY backup system, available from CommVault Systems, Inc. of Oceanport, N.J., aspects of which are further described in the commonly-assigned U.S. patent application Ser. No. 09/610,738, now U.S. Pat. No. 7,035,880, the entirety of which is incorporated by reference herein. The system 150 may also represent a modular storage system such as the CommVault Simpana system, also available from CommVault Systems, Inc.
[0022] The system 150 may generally include combinations of hardware and software components associated with performing storage operations on electronic data. Storage operations include copying, backing up, creating, storing, retrieving, and/or migrating primary storage data (e.g., data stores 160 and/or 162) and secondary storage data (which may include, for example, snapshot copies, backup copies, hierarchical storage management (HSM) copies, archive copies, and other types of copies of electronic data stored on storage devices 115). The system 150 may provide one or more integrated management consoles for users or system processes to interface with in order to perform certain storage operations on electronic data as further described herein. Such integrated management consoles may be displayed at a central control facility or several similar consoles distributed throughout multiple network locations to provide global or geographically specific network data storage information.
[0023] In one example, storage operations may be performed according to various storage preferences, for example, as expressed by a user preference, a storage policy, a schedule policy, and/or a retention policy. A "storage policy" is generally a data structure or other information source that includes a set of preferences and other storage criteria associated with performing a storage operation. The preferences and storage criteria may include, but are not limited to, a storage location, relationships between system components, network pathways to utilize in a storage operation, data characteristics, compression or encryption requirements, preferred system components to utilize in a storage operation, a single instancing or variable instancing policy to apply to the data, and/or other criteria relating to a storage operation. For example, a storage policy may indicate that certain data is to be stored in the storage device 115, retained for a specified period of time before being aged to another tier of secondary storage, copied to the storage device 115 using a specified number of data streams, etc.
[0024] A "schedule policy" may specify a frequency with which to perform storage operations and a window of time within which to perform them. For example, a schedule policy may specify that a storage operation is to be performed every Saturday morning from 2:00 a.m. to 4:00 a.m. A "retention policy" may specify how long data is to be retained at specific tiers of storage or what criteria must be met before data may be pruned or moved from one tier of storage to another tier of storage. In some cases, the storage policy includes information generally specified by the schedule policy and/or the retention policy. (Put another way, the storage policy includes the schedule policy and/or the retention policy.) Storage policies, schedule policies and/or retention policies may be stored in a database of the storage manager 105, to archive media as metadata for use in restore operations or other storage operations, or to other locations or components of the system 150.
[0025] The system 150 may comprise a storage operation cell that is one of multiple storage operation cells arranged in a hierarchy or other organization. Storage operation cells may be related to backup cells and provide some or all of the functionality of backup cells as described in the assignee's U.S. patent application Ser. No. 09/354,058, now U.S. Pat. No. 7,395,282, which is incorporated herein by reference in its entirety. However, storage operation cells may also perform additional types of storage operations and other types of storage management functions that are not generally offered by backup cells.
[0026] Storage operation cells may contain not only physical devices, but also may represent logical concepts, organizations, and hierarchies. For example, a first storage operation cell may be configured to perform a first type of storage operations such as HSM operations, which may include backup or other types of data migration, and may include a variety of physical components including a storage manager 105 (or management agent 131), a secondary storage computing device 165, a client 130, and other components as described herein. A second storage operation cell may contain the same or similar physical components; however, it may be configured to perform a second type of storage operations, such as storage resource management (SRM) operations, and may include monitoring a primary data copy or performing other known SRM operations.
[0027] Thus, as can be seen from the above, although the first and second storage operation cells are logically distinct entities configured to perform different management functions (i.e., HSM and SRM, respectively), each storage operation cell may contain the same or similar physical devices. Alternatively, different storage operation cells may contain some of the same physical devices and not others. For example, a storage operation cell configured to perform SRM tasks may contain a secondary storage computing device 165, client 130, or other network device connected to a primary storage volume, while a storage operation cell configured to perform HSM tasks may instead include a secondary storage computing device 165, client 130, or other network device connected to a secondary storage volume and not contain the elements or components associated with and including the primary storage volume. (The term "connected" as used herein does not necessarily require a physical connection; rather, it could refer to two devices that are operably coupled to each other, communicably coupled to each other, in communication with each other, or more generally, refer to the capability of two devices to communicate with each other.) These two storage operation cells, however, may each include a different storage manager 105 that coordinates storage operations via the same secondary storage computing devices 165 and storage devices 115. This "overlapping" configuration allows storage resources to be accessed by more than one storage manager 105, such that multiple paths exist to each storage device 115 facilitating failover, load balancing, and promoting robust data access via alternative routes.
[0028] Alternatively or additionally, the same storage manager 105 may control two or more storage operation cells (whether or not each storage operation cell has its own dedicated storage manager 105). Moreover, in certain embodiments, the extent or type of overlap may be user-defined (through a control console) or may be automatically configured to optimize data storage and/or retrieval.
[0029] The clients 130 typically include application software for performing various operations. Clients 130 typically also include an operating system on which the application software runs. A file system can be provided to facilitate and control file access by the operating system and application software. File systems can facilitate access to local and remote storage devices for file or data access and storage. Clients 130 can also include local storage such as a media module media drive with fixed or removable media.
[0030] In some examples, the clients 130 include storage mechanisms for allowing computer programs or other instructions or data to be loaded into memory for execution. Such storage mechanisms might include, for example, a fixed or removable storage unit and an interface. Examples of such storage units and interfaces can include a program cartridge and cartridge interface, a removable memory (for example, a flash memory or other removable memory module) and memory slot, a PCMCIA slot and card, and other fixed or removable storage units and interfaces that allow software and data to be transferred from the storage unit to memory.
[0031] Data agent 195 may be a software module or part of a software module that is generally responsible for performing storage operations on the data of the client 130 stored in data store 160/162 or other memory location. Each client 130 may have at least one data agent 195 and the system 150 can support multiple clients 130. Data agent 195 may be distributed between client 130 and storage manager 105 (and any other intermediate components), or it may be deployed from a remote location or its functions approximated by a remote process that performs some or all of the functions of data agent 195.
[0032] As used herein, the term module might describe a given unit of functionality that can be performed in accordance with one or more embodiments of the present invention. As used herein, a module might be implemented utilizing any form of hardware, software, firmware, or a combination thereof. For example, one or more processors, controllers, ASICs, PLAs, logical components, software routines or other mechanisms might be implemented to make up a module. In implementation, the various modules described herein might be implemented as discrete modules or the functions and features described can be shared in part or in total among one or more modules. In other words, as would be apparent to one of ordinary skill in the art after reading this description, the various features and functionality described herein may be implemented in any given application and can be implemented in one or more separate or shared modules in various combinations and permutations. Even though various features or elements of functionality may be individually described or claimed as separate modules, one of ordinary skill in the art will understand that these features and functionality can be shared among one or more common software and hardware elements, and such description shall not require or imply that separate hardware or software components are used to implement such features or functionality.
[0033] The overall system 150 may employ multiple data agents 195, each of which may perform storage operations on data associated with a different application. For example, different individual data agents 195 may be designed to handle Microsoft Exchange data, Lotus Notes data, Microsoft Windows file system data, Microsoft Active Directory Objects data, Microsoft SQL Server data, Microsoft Sharepoint Server data, and other types of data known in the art. Other embodiments may employ one or more generic data agents 195 that can handle and process multiple data types rather than using the specialized data agents described above.
[0034] If a client 130 has two or more types of data, one data agent 195 may be required for each data type to perform storage operations on the data of the client 130. For example, to back up, migrate, and restore all the data on a Microsoft Exchange server, the client 130 may use one Microsoft Exchange Mailbox data agent 195 to back up the Exchange mailboxes, one Microsoft Exchange Database data agent 195 to back up the Exchange databases, one Microsoft Exchange Public Folder data agent 195 to back up the Exchange Public Folders, and one Microsoft Windows File System data agent 195 to back up the file system of the client 130. These data agents 195 would be treated as four separate data agents 195 by the system even though they reside on the same client 130.
[0035] Alternatively, the overall system 150 may use one or more generic data agents 195, each of which may be capable of handling two or more data types. For example, one generic data agent 195 may be used to back up, migrate and restore Microsoft Exchange Mailbox data and Microsoft Exchange Database data while another generic data agent 195 may handle Microsoft Exchange Public Folder data and Microsoft Windows File System data, etc.
[0036] Data agents 195 may be responsible for arranging or packing data to be copied or migrated into a certain format such as an archive file. Nonetheless, it will be understood that this represents only one example, and any suitable packing or containerization technique or transfer methodology may be used if desired. Such an archive file may include metadata, a list of files or data objects copied, the file, and data objects themselves. Moreover, any data moved by the data agents may be tracked within the system by updating indexes associated with appropriate storage managers 105 or secondary storage computing devices 165. As used herein, a file or a data object refers to any collection or grouping of bytes of data that can be viewed as one or more logical units.
[0037] Generally speaking, storage manager 105 may be a software module or other application that coordinates and controls storage operations performed by the system 150. Storage manager 105 may communicate with some or all elements of the system 150, including clients 130, data agents 195, secondary storage computing devices 165, and storage devices 115, to initiate and manage storage operations (e.g., backups, migrations, data recovery operations, etc.).
[0038] Storage manager 105 may include a jobs agent 120 that monitors the status of some or all storage operations previously performed, currently being performed, or scheduled to be performed by the system 150. (One or more storage operations are alternatively referred to herein as a "job" or "jobs.") Jobs agent 120 may be communicatively coupled to an interface agent 125 (e.g., a software module or application). Interface agent 125 may include information processing and display software, such as a graphical user interface ("GUI"), an application programming interface ("API"), or other interactive interface through which users and system processes can retrieve information about the status of storage operations. For example, in an arrangement of multiple storage operations cell, through interface agent 125, users may optionally issue instructions to various storage operation cells regarding performance of the storage operations as described and contemplated herein. For example, a user may modify a schedule concerning the number of pending snapshot copies or other types of copies scheduled as needed to suit particular needs or requirements. As another example, a user may employ the GUI to view the status of pending storage operations in some or all of the storage operation cells in a given network or to monitor the status of certain components in a particular storage operation cell (e.g., the amount of storage capacity left in a particular storage device 115).
[0039] Storage manager 105 may also include a management agent 131 that is typically implemented as a software module or application program. In general, management agent 131 provides an interface that allows various management agents 131 in other storage operation cells to communicate with one another. For example, assume a certain network configuration includes multiple storage operation cells hierarchically arranged or otherwise logically related in a WAN or LAN configuration. With this arrangement, each storage operation cell may be connected to the other through each respective interface agent 125. This allows each storage operation cell to send and receive certain pertinent information from other storage operation cells, including status information, routing information, information regarding capacity and utilization, etc. These communications paths may also be used to convey information and instructions regarding storage operations.
[0040] For example, a management agent 131 in a first storage operation cell may communicate with a management agent 131 in a second storage operation cell regarding the status of storage operations in the second storage operation cell. Another illustrative example includes the case where a management agent 131 in a first storage operation cell communicates with a management agent 131 in a second storage operation cell to control storage manager 105 (and other components) of the second storage operation cell via management agent 131 contained in storage manager 105.
[0041] Another illustrative example is the case where management agent 131 in a first storage operation cell communicates directly with and controls the components in a second storage operation cell and bypasses the storage manager 105 in the second storage operation cell. If desired, storage operation cells can also be organized hierarchically such that hierarchically superior cells control or pass information to hierarchically subordinate cells or vice versa.
[0042] Storage manager 105 may also maintain an index, a database, or other data structure 111. The data stored in database 111 may be used to indicate logical associations between components of the system, user preferences, management tasks, media containerization and data storage information or other useful data. For example, the storage manager 105 may use data from database 111 to track logical associations between secondary storage computing device 165 and storage devices 115 (or movement of data as containerized from primary to secondary storage).
[0043] Generally speaking, the secondary storage computing device 165, which may also be referred to as a media agent, may be implemented as a software module that conveys data, as directed by storage manager 105, between a client 130 and one or more storage devices 115 such as a tape library, a magnetic media storage device, an optical media storage device, or any other suitable storage device. In one embodiment, secondary storage computing device 165 may be communicatively coupled to and control a storage device 115. A secondary storage computing device 165 may be considered to be associated with a particular storage device 115 if that secondary storage computing device 165 is capable of routing and storing data to that particular storage device 115.
[0044] In operation, a secondary storage computing device 165 associated with a particular storage device 115 may instruct the storage device to use a robotic arm or other retrieval means to load or eject a certain storage media, and to subsequently archive, migrate, or restore data to or from that media. Secondary storage computing device 165 may communicate with a storage device 115 via a suitable communications path such as a SCSI or Fibre Channel communications link. In some embodiments, the storage device 115 may be communicatively coupled to the storage manager 105 via a SAN.
[0045] Each secondary storage computing device 165 may maintain an index, a database, or other data structure 161 that may store index data generated during storage operations for secondary storage (SS) as described herein, including creating a metabase (MB). For example, performing storage operations on Microsoft Exchange data may generate index data. Such index data provides a secondary storage computing device 165 or other external device with a fast and efficient mechanism for locating data stored or backed up. Thus, a secondary storage computing device index 161, or a database 111 of a storage manager 105, may store data associating a client 130 with a particular secondary storage computing device 165 or storage device 115, for example, as specified in a storage policy, while a database or other data structure in secondary storage computing device 165 may indicate where specifically the data of the client 130 is stored in storage device 115, what specific files were stored, and other information associated with storage of the data of the client 130. In some embodiments, such index data may be stored along with the data backed up in a storage device 115, with an additional copy of the index data written to index cache in a secondary storage device. Thus the data is readily available for use in storage operations and other activities without having to be first retrieved from the storage device 115.
[0046] Generally speaking, information stored in cache is typically recent information that reflects certain particulars about operations that have recently occurred. After a certain period of time, this information is sent to secondary storage and tracked. This information may need to be retrieved and uploaded back into a cache or other memory in a secondary computing device before data can be retrieved from storage device 115. In some embodiments, the cached information may include information regarding format or containerization of archives or other files stored on storage device 115.
[0047] One or more of the secondary storage computing devices 165 may also maintain one or more single instance databases 123. Single instancing (alternatively called data deduplication) generally refers to storing in secondary storage only a single instance of each data object (or data block) in a set of data (e.g., primary data). More details as to single instancing may be found in one or more of the following commonly-assigned U.S. patent applications: 1) U.S. patent application Ser. No. 11/269,512 (entitled SYSTEM AND METHOD TO SUPPORT SINGLE INSTANCE STORAGE OPERATIONS, Attorney Docket No. 60692-8023.US00); 2) U.S. patent application Ser. No. 12/145,347 (entitled APPLICATION-AWARE AND REMOTE SINGLE INSTANCE DATA MANAGEMENT, Attorney Docket No. 60692-8056.US00); or 3) U.S. patent application Ser. No. 12/145,342 (entitled APPLICATION-AWARE AND REMOTE SINGLE INSTANCE DATA MANAGEMENT, Attorney Docket No. 60692-8057.US00), 4) U.S. patent application Ser. No. 11/963,623 (entitled SYSTEM AND METHOD FOR STORING REDUNDANT INFORMATION, Attorney Docket No. 60692-8036.US02); 5) U.S. patent application Ser. No. 11/950,376 (entitled SYSTEMS AND METHODS FOR CREATING COPIES OF DATA SUCH AS ARCHIVE COPIES, Attorney Docket No. 60692-8037.US01); 6) U.S. patent application Ser. No. 12/565,576 (entitled SYSTEMS AND METHODS FOR MANAGING SINGLE INSTANCING DATA, Attorney Docket No. 60692-8067.US01); or 7) U.S. patent application Ser. No. 12/647,906 (entitled BLOCK-LEVEL SINGLE INSTANCING, Attorney Docket No. 60692-8073.US01), each of which is incorporated by reference herein in its entirety.
[0048] In some examples, the secondary storage computing devices 165 maintain one or more variable instance databases. Variable instancing generally refers to storing in secondary storage one or more instances, but fewer than the total number of instances, of each data block (or data object) in a set of data (e.g., primary data). More details as to variable instancing may be found in the commonly-assigned U.S. patent application Ser. No. 12/649,454 (entitled STORING A VARIABLE NUMBER OF INSTANCES OF DATA OBJECTS, Attorney Docket No. 60692-8068.US01).
[0049] In some embodiments, certain components may reside and execute on the same computer. For example, in some embodiments, a client 130 such as a data agent 195, or a storage manager 105, coordinates and directs local archiving, migration, and retrieval application functions as further described in the previously-referenced U.S. patent application Ser. No. 09/610,738. This client 130 can function independently or together with other similar clients 130.
[0050] As shown in FIG. 1, each secondary storage computing device 165 has its own associated metabase 161. Each client 130 may also have its own associated metabase 170. However in some embodiments, each "tier" of storage, such as primary storage, secondary storage, tertiary storage, etc., may have multiple metabases or a centralized metabase, as described herein. For example, rather than a separate metabase or index associated with each client 130 in FIG. 1, the metabases on this storage tier may be centralized. Similarly, second and other tiers of storage may have either centralized or distributed metabases. Moreover, mixed architecture systems may be used if desired, that may include a first tier centralized metabase system coupled to a second tier storage system having distributed metabases and vice versa, etc.
[0051] Moreover, in operation, a storage manager 105 or other management module may keep track of certain information that allows the storage manager 105 to select, designate, or otherwise identify metabases to be searched in response to certain queries as further described herein. Movement of data between primary and secondary storage may also involve movement of associated metadata and other tracking information as further described herein.
[0052] In some examples, primary data may be organized into one or more sub-clients. A sub-client is a portion of the data of one or more clients 130, and can contain either all of the data of the clients 130 or a designated subset thereof. As depicted in FIG. 1, the data store 162 includes two sub-clients. For example, an administrator (or other user with the appropriate permissions; the term administrator is used herein for brevity) may find it preferable to separate email data from financial data using two different sub-clients having different storage preferences, retention criteria, etc.
Suitable System for Creating Snapshots
[0053] FIG. 2 is a block diagram illustrating in more detail certain components 200 of the data storage system 150 of FIG. 1. FIG. 2 depicts one of the clients 130, secondary storage computing device 165, secondary storage computing device index 161, and storage device 115.
[0054] In addition to the data agent 195, the client 130 includes a snapshot component 205, an application 210, and data 215. The application 210 may be any application executing on the client 130, such as a database server application (for example, Microsoft SQL server, Microsoft Active Directory Server, Oracle, etc.), an email server application (for example, Microsoft Exchange Server, Apache, etc.), or other types of servers (for example, application servers such as Microsoft SharePoint servers or web servers, virtual machine servers such as Microsoft Virtual Server, file servers, etc.). The application 210 has associated data 215, which includes a database 220 and logs 225, shown as logs one through n. The application 210 may write data to the database 220 using transactional techniques. That is, the application 210 may write changes to the logs 225 before committing the changes to the database 220.
[0055] For example, consider an application 210 that is an email server application 210, such as Microsoft Exchange. The email server application 210 has an associated database 220 to which it writes its data in a transactional manner. The data 215 of the application also includes logs 225. For example, logs one and two may exist as of day one. A full copy of the database 220 and its logs 225 that occurs on day one may result in copying the database 220 and logs one and two. On day two, the email server application 210 creates logs three and four, and an incremental copy of the database 220 and its logs 225 on day two would only copy logs three and four. On day three, logs five and six are created, and an incremental copy of the database 220 and its logs 225 on day three would copy over logs five and six. Accordingly, the state of the data 215 of the email server application 210 can be recovered to multiple points in time over days one through three, by playing portions of the appropriate logs 225 into the database 220. Further incremental copies of additional logs 220 can be made at later points in time. Although this example describes that the email server application 210 creates two logs 225 each day, those of skill in the art will understand that any number of logs (i.e., zero logs, one log, or greater than two logs) may be created each day.
[0056] The snapshot component 205 creates snapshots of the data 215 of the client 130. The snapshot component 205 includes software components and may also include hardware and/or firmware components. The snapshot component 205 may be provided in its entirety by a single entity (for example, a single vendor), or the snapshot component 205 may include sub-components that are provided by different entities (such as multiple vendors).
[0057] In some examples, the snapshot component includes a Microsoft Volume Shadow Copy Service (VSS) sub-component and a software-based VSS provider sub-component that is provided by the assignee of the present application, CommVault Systems, Inc. In these examples, the data agent 195 interacts with the Microsoft VSS sub-component to create snapshots. The Microsoft VSS sub-component notifies the application 210 to prepare the data 215 for creating a snapshot. The application 210 prepares the data 215 in an appropriate manner (such as completing open transactions, flushing application caches, etc.). The Microsoft VSS sub-component initiates a commit phase and notifies the application 210 that the application 210 should be quiesced and to freeze writes to the data 215. The Microsoft VSS sub-component may also flush a file system buffer and freeze the file system to ensure that file system metadata is written and that the data 215 is written in a consistent order. The Microsoft VSS sub-component notifies the VSS provider sub-component to create the snapshot, and the VSS provider sub-component creates the snapshot. The Microsoft VSS sub-component then "thaws" or resumes file system operations and notifies the application 210 that the application 210 can unquiesce and complete any writes to the data 215.
[0058] In other examples, in addition to or as an alternative to the software-based VSS provider sub-component, the snapshot component 205 includes other software-based VSS provider sub-components, such as a Microsoft system software provider, a Microsoft Data Protection Manager provider sub-component or a NetApp SnapManager provider sub-component. These other software-based VSS provider sub-components may create snapshots in manners similar to the manner described in the preceding paragraph, or may use other techniques to create snapshots.
[0059] In other examples, in addition to the Microsoft VSS sub-component, the snapshot component 205 includes one or more hardware-based VSS provider sub-components, such as those provided by vendors such as Hewlett-Packard, EMC, NetApp, IBM, and other vendors. These hardware-based VSS provider sub-components may create snapshots in manners similar to the manner described above, or may use other techniques to create snapshots. Those of skill in the art will understand that the snapshot component 205 may include various software-based and/or hardware-based sub-components and interact with other components in various ways in order to create snapshots of the data 215.
[0060] The snapshot component 205 may create snapshots using various techniques, such as copy-on-write, redirect-on-write, split mirror, copy-on-write with background copy, log structure file architecture techniques, continuous data protection techniques, and/or other techniques. The snapshot component 205 may store the created snapshots on a particular volume of the client 130.
[0061] The secondary storage computing device 165 includes a copy component 240 that copies snapshots from the client 130 to another storage device, such as storage device 115. The secondary storage computing device 165 also stores certain snapshot information and/or snapshot metadata in various data structures as described herein. The secondary storage computing device 165 may store snapshot information and/or snapshot metadata in secondary storage computing device index 161.
[0062] The secondary storage computing device 165 also includes an interface component 242. The interface component 242 provides access to the copied snapshot data. The interface component 242 can be used to access data objects created in other types of secondary copies, such as backup copies, archive copies, and other types of copies. The interface component 242 can also be used to display to a user available snapshots or point in time copies of the data 215 that can be used for recovery or other purposes. The secondary storage computing device 165 also includes a snapshot component 244. The snapshot component 244 may function similarly to the snapshot component 205.
[0063] The secondary storage computing device 165 also includes applications 245 that perform various functions using copied snapshot data. The applications 245 include an indexing component 250, a search component 255, an e-discovery component 260, and an information management component 265. As described in more detail herein, the applications 245 access copied snapshot data stored on storage device 115 and data structures stored in secondary storage computing device index 161 in order to perform various functions.
Analyzing Snapshots
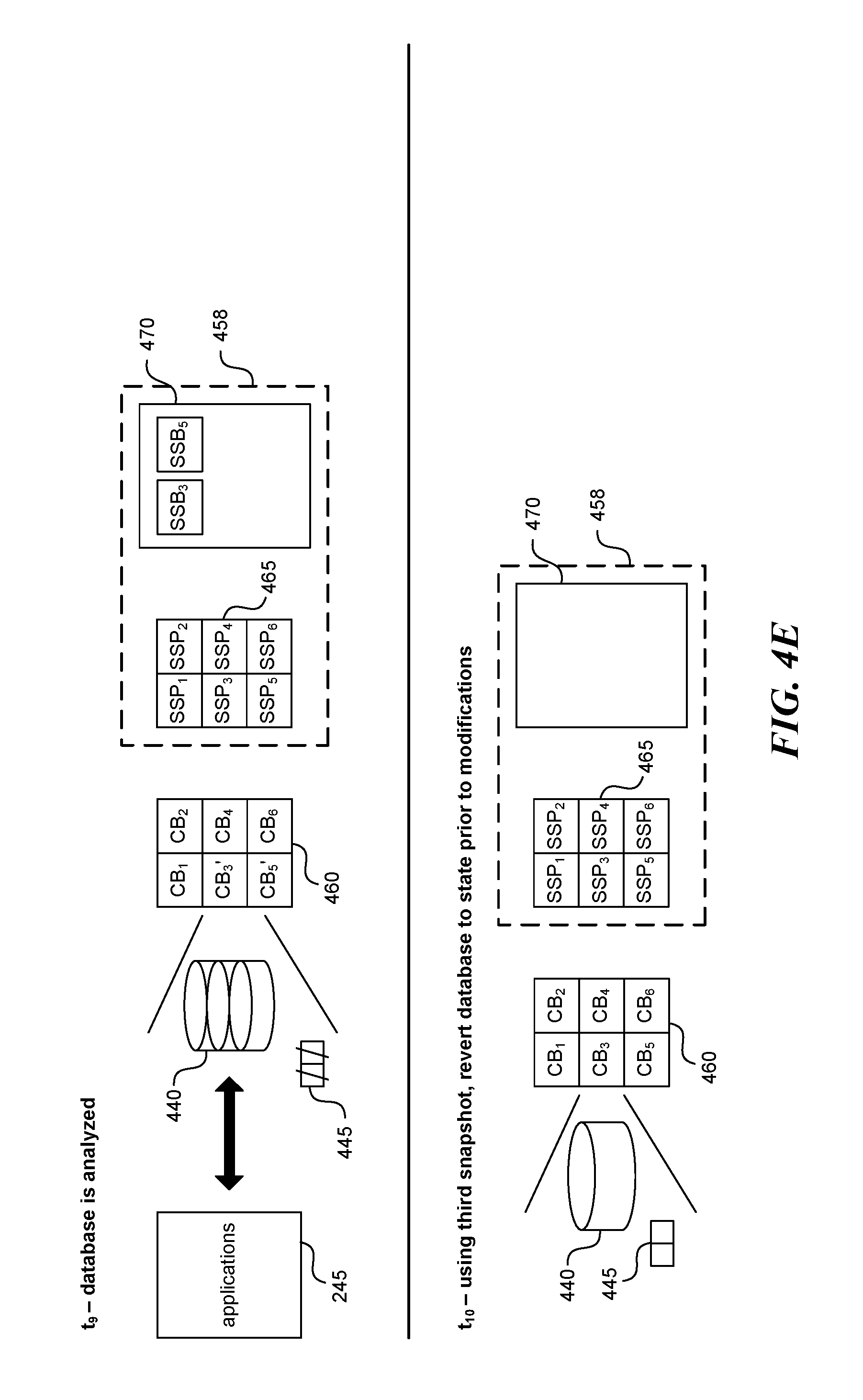
[0064] FIG. 3 is a flow diagram of a process 300 for analyzing a snapshot (alternatively referred to as mining a snapshot), and FIGS. 4A-4E illustrate aspects of the process 300 in more detail. The process 300 is described using the example of a transactional application 210 having associated data 215, which includes a database 220 and logs 225. As can be seen in FIGS. 4A-4E, the database 220 and associated logs 225 are stored as blocks B.sub.1 through B.sub.6 405 on a storage device associated with the client 130.
[0065] The process 300 begins at step 305 (time to), where the snapshot component 205 accesses the database 220 and associated logs 225 and creates a first snapshot 408a of the database 220 and associated logs 225. See FIG. 4A. For example, the snapshot component 205 may use a copy-on-write technique to create the first snapshot, and the process 300 is described using this example (although other techniques for creating snapshots may be used). The first snapshot 408a includes a set of pointers P.sub.1 through P.sub.6 410 (that point to blocks B.sub.1 through B.sub.6, 405, respectively) and storage location 415 for blocks.
[0066] At step 310 (time t.sub.1), the application 210 modifies the database 220 and logs 225. For example, the application 210 may commit changes in certain logs 225 to the database 220 and/or create new logs 225. These changes may result to modifications to blocks B.sub.1 and B.sub.4 (which become blocks B.sub.1' and B.sub.4', respectively). Prior to their modification, the snapshot component 205 copies blocks B.sub.1 and B.sub.4 to storage location 415. Pointers Pi and P.sub.4 may now point to blocks B.sub.1 and B.sub.4 in storage location 415, rather than B.sub.1 and B.sub.4 in storage location 405.
[0067] At step 315 (time t2), the copy component 240 copies the first snapshot 408a to another location, such as the storage device 115, thereby creating a copy 428a of the first snapshot 408a. See FIG. 4B. For example, the copy component 240 may copy the first snapshot 408a as part of a backup process. The copy component 240 creates a copy set of blocks (blocks CBI through CB.sub.6, 425) and a copy set of pointers that point to the copy set of blocks (CPI through CP.sub.6 420). Additionally or alternatively, the first snapshot 408a may be transferred to the other location as part of a background copy process or using other techniques as known to those of skill in the art.
[0068] At step 320, the snapshot component 205 determines whether to take additional snapshots of the database 220 and logs 225. For example, the snapshot component 205 may be programmed to create snapshots periodically, such as once a day at, for example, 2:00 a.m. As another example, an administrator may request that the snapshot component 205 create additional snapshots of the database 220 and logs 225, such as on an ad-hoc basis. If the snapshot component 205 is to take additional snapshots, the process 300 returns to step 305, and additional snapshots are created (e.g., snapshot 408b), the database 220 and logs 225 may be modified, and the additional snapshots (e.g., snapshot 408b) are copied to the other location (e.g., creating snapshot copy 428b). As shown in FIGS. 4B-4C, these additional steps occur at times t.sub.3 through t.sub.5, where blocks B.sub.2 and B.sub.5 are now changed and copied out (before being changed) to storage location 425.
[0069] If the snapshot component 205 is not to take additional snapshots at this time, the process 300 continues at step 325, where the secondary storage computing device 165 receives an indication to analyze a copy of a snapshot copied to the other location (e.g., snapshot copy 428a or snapshot copy 428b). For example, the secondary storage computing device 165 may receive a request to obtain a data object (for example, an email message, a mailbox, a message store, etc.) stored in the database 220 and logs 225.
[0070] At step 330 (time t.sub.6), the snapshot component 244 mounts the snapshot copy 428a at the other location. Mounting the snapshot copy 428a creates a read-write copy of the database 440 and logs 445. See FIG. 4C.
[0071] At step 335 (time t.sub.7), the snapshot component 244 creates a snapshot 458 of the database 440 and logs 445. This creates a set of pointers (SSP.sub.1 through SSP.sub.6 465) and a storage location 470. See FIG. 4D.
[0072] At step 340 (time t.sub.8), the snapshot component 244 plays the logs 445 into the database 440. For example, if the snapshot 458 is created by a hardware-based sub-component, the snapshot 458 may be read/write, and the snapshot component 244 can modify the snapshot 458 any time after creating the snapshot 458. As another example, if the snapshot 458 is created by a software-based sub-component, the snapshot component 244 may have a window of time immediately following the creation during which the snapshot component 244 can modify the snapshot 458. The snapshot component 244 may play all or portions of one or more logs 445 into the database 440. Playing the logs 445 into the database 440 modifies certain blocks (as shown, blocks CB.sub.3 and CB.sub.5, which become blocks CB.sub.3' and CB.sub.5', respectively). (If the logs and snapshots include insufficient detail to make certain changes to the database, the system may also create and maintain an index of changes that map changes recorded by the snapshots with files or data objects changed, so that the system can identify specific blocks that may need to be restored before analysis is performed.) Before the blocks are modified, the snapshot component 244 copies the blocks (blocks CB.sub.3 and CB.sub.5) to storage location 470. See FIG. 4D.
[0073] After the snapshot component 244 plays logs 445 into the database 440, the database 440 may be in a state in which additional logs 445 cannot be played into the database 440. For example, a bit or flag may be set in the database 440 indicating that further logs 445 cannot be played into the database 445. In some examples, the snapshot component 244 creates the snapshot 458 of the database 440 and logs 445 after playing the logs 445 into the database 440.
[0074] At step 345 (time t.sub.9), the applications 245 analyze the database 445 and logs 445. See FIG. 4E. For example, the applications 245 may analyze the database 445 and logs 445 in order to, for example, analyze individual data objects within the database 445 and logs 445. The applications 245 may analyze the database 445 and logs 445 to perform various functions on individual data objects. For example, the applications 245 may index individual data objects, classify individual data objects, extract individual data objects from the set of data in order to or copy restore individual data objects to other locations, deduplicate individual data objects, and/or perform other functions. More details as to functions that may be performed on the database 445 and logs 445 are described in the previously-referenced U.S. patent application Ser. No. 12/979,101, now U.S. Pat. No. 8,595,191 (Attorney Docket No. 60692-8074.US01), entitled "SYSTEMS AND METHODS FOR PERFORMING DATA MANAGEMENT OPERATIONS USING SNAPSHOTS."
[0075] At step 350 (time tic)), the snapshot component 244 reverts the mounted database 445 and logs 440 to the state they were at the time the snapshot 458 was created (time t.sub.7). For example, the snapshot component 244 may revert the mounted database 445 and logs 440 by performing a VSS revert operation using the snapshot 458. Additionally or alternatively, the snapshot component 244 may use revert operations other than VSS revert operations and/or other techniques to revert the mounted database 445 and logs 440. See FIG. 4E. The process may then loop back to block 305 and take additional snapshots, or end.
[0076] Performing a revert operation reverts the mounted database 445 and logs 440 to the state they were in at the time the snapshot 458 was created (time t.sub.7). For example, if the snapshot 458 was created before the mounted database 445 and logs 440 were modified by playing logs 445 into the database 440, performing a revert operation on the mounted database 440 and logs 445 will revert mounted database 445 and logs 440 to the state it was in before playing the logs 445 into the database 440. This puts the database 440 into a state such that additional logs 445 can be played into it. For example, if the snapshot component 244 had previously created the snapshot 458 of the mounted database 445 and logs 440 and then played logs one and two into the database 440, the snapshot component 244 can then play additional logs 445 (for example, logs three to n) into the database 440.
[0077] As another example, if the snapshot of the mounted database 445 and logs 440 was taken after the mounted database 445 and logs 440 were modified, performing a revert operation will revert the mounted database 445 and logs 440 to the state they were in after being modified (for example, after logs 445 were played into the database 440). This also offers the opportunity to play additional logs 445 (such as those from later snapshots) into the database 440 in order to put the database 440 into the state it existed in at multiple points in time.
[0078] Accordingly, using snapshots in this way preserves the integrity of the database 440 in such a way that it can be used for both analyzing the data in the database 440 and the logs 445, as well as using the database 440 and the logs 445 to perform a full recovery of the database 440 and logs 445, or to perform restores of individual data objects within the database 440 and logs 445.
[0079] In order to analyze the data in the database 440 and logs 445, certain logs 445 may need to be played into the database 440. For example, to analyze the state of the data 215 as it existed at the end of day one, logs one and two would need to be played into the database 440. However, playing such logs 445 into the database 440 may preclude the possibility of playing additional logs 445 into the database 440. Taking a snapshot of the mounted database 440 and logs 445 solves this problem by enabling the ability to revert the data 215 to the state it existed in prior to or immediately after the playing of certain logs 445 into the database 440. The techniques described herein facilitate putting the data 215 into a state at a specific point in time, analyzing the data 215 as it existed at that specific point in time, and then performing a revert operation upon a snapshot of the data 215 in order to revert the data to a state in which additional logs 445 may be played into the database 440, or in which all or portions of the data 215 can be recovered.
[0080] Accordingly, the data 215 can be analyzed (for example, individual data objects may be indexed, searched, extracted, recovered, etc.), and then such individual data objects can be also analyzed at a later point in time in order to pick up any later changes to the individual data objects. For example, an email message in an email server application database 220 and logs 225 may have a first state at a first point in time. Using the techniques described herein, the snapshot component 205 can put the database 220 into the first state at the first point in time and extract the email message from the database 220. The snapshot component 205 can then revert the database 220 to a prior state, and then play additional logs 225 into the database 220, to recover the email message as it existed at a second, later point in time. After step 415, the process 400 concludes.
[0081] In some examples, the techniques described herein may be used on copies of data created other than by snapshot operations. For example, the secondary storage computing device 165 may create copies of the database 220 and logs 225 by performing backup operations on the database 220 and logs 225. The secondary storage computing device 165 may create a full backup of the database 220 and logs one and two on day one. On day two, the email server application 210 creates logs three and four, and an incremental backup of the database 220 and logs 225 on day two would only backup logs three and four. On day three, logs five and six are created, and an incremental backup of the database 220 and logs 225 on day three would backup logs five and six. The following table illustrates this example:
TABLE-US-00001 Day/Time Type of backup Data Day 1/11:00 p.m. Full Database, logs one and two Day 2/11:00 p.m. Incremental Logs three and four Day 3/11:00 p.m. Incremental Logs five and six
Utilizing Consistent Recovery Points to Create Snapshots that can be Analyzed
[0082] In some examples, the techniques described herein may be used on copies of data created by replication operations such as CDR (Continuous Data Replication), DDR (Discrete Data Replication), and other replication operations. For example, for data protected by a replication operation, multiple Consistent Recovery Points (CRPs, alternatively referred to as markers) can be established, and snapshots can be taken at such CRPs. To create a CRP, the system suspends writes to the data, and inserts the CRP into the CDR logs that indicate changes to the data. The system then copies the first CDR logs to another location. The system can play the CDR logs to replicate the changes to a copy of the data at another location (the replication data copy). When the system arrives at or reaches the CRP, the system can take a snapshot of the replicated data copy. The system can then modify the snapshot of the replicated data copy (for example, by playing application logs into an application database) so that the snapshot of the replicated data copy can be analyzed.
[0083] FIG. 5 is a flow diagram of a process 500 for analyzing a snapshot (alternatively referred to as mining a snapshot). The process 500 is described using the example of a transactional application 210 having associated data 215, which includes a database 220 and logs 225. The transactional application 210 executes on a source computing system (e.g., the client 130). A copy of the data 215 as the data 215 existed at a first point in time is stored on a destination computing system (e.g., the secondary storage computing device 165). The copy of the data 215 is referred to as the replication data copy. As changes to the data 215 are made, such changes are tracked in CDR logs on the source computing system.
[0084] The process 500 begins at step 505, where the snapshot component 205 quiesces the application 210. Quiescing the application 210 puts the data 215 into a state in which the data 215 is consistent or stable. The snapshot component 205 can quiesce the application 210 using the VSS sub-component. The VSS sub-component can then notify the VSS provider sub-component to create the snapshot. However, the VSS provider sub-component does not create a snapshot. Instead, at step 510, which occurs at a second point in time after the first point in time, the snapshot component 205 inserts a CRP into the CDR logs. The CRP may be places at predetermined periodic intervals, such as every hour or every midnight, or sporadically upon user command. At step 512 the snapshot component (e.g., the VSS sub-component) unquiesces the application 210.
[0085] At step 515, the data agent 195 copies the CDR logs from the source computing system to the destination computing system. The copying can be done periodically, as the CDR logs are created, using other techniques. At step 520, the destination computing system plays the CDR logs to replicate changes to the data 215 to the replication data copy stored at the destination computing system. At step 525, the destination computing system arrives at or reaches the CRP in the CDR logs and takes a snapshot of the replication data copy with the logs replayed (i.e. changes to the data populated based on the changes indicated in the logs).
[0086] At step 530, the destination computing system puts the snapshot of the replication data copy into a state at which the application data can be analyzed (e.g., a clean shutdown state). To do so, the destination computing system can play the logs 225 into the database 220 of the snapshot of the replication data copy, as described herein. At step 535 the destination computing system analyzes the database 220, as described herein. The destination computing system can access one or more individual data objects in the database 220 (e.g., emails, files, etc.) At step 540, the destination computing system continues playing CDR logs to replicate additional or other changes to the replication data copy at the destination computing system. The process 500 then concludes.
[0087] Additionally or alternatively, instead of analyzing the snapshot of the replication data copy, the destination computing system can analyze the replication data copy. To do so, the destination computing system plays the logs 225 into the database 220 of the replication data copy. Such modifications prevent the destination computing system from playing the CDR logs to replicate changes to the replication data copy. After analyzing the replication data copy, the destination computing system can then utilize the revert functionality of the snapshot to revert the replication data copy to the state it was in prior to the playing of the logs 225 into the database 220. Such reversion allows the destination computing system to play the CDR logs into the replication data copy.
[0088] The process 500 provides several advantages. One advantage is that control over when the data 215 on the source computing system is to be snapshotted is located on the source computing system, while the actual snapshotting occurs on the destination computing system. Such division between an instruction to take a snapshot and the creation of the snapshot according to the instruction can save resources on the source computing system. Another advantage is that the snapshot taken on the destination computing system, although not application-aware (because the application is not executing on the destination computing system), can be considered as application-aware, because the snapshot is taken at a time when the replication data copy is consistent. Other advantages will be apparent to those of skill in the art.
Additional Examples
[0089] In some examples, both snapshot operations and non-snapshot operations may be used. For example, an initial full copy and snapshot may be taken of the database 220 and logs 225. Subsequent to the initial snapshot, incremental copies or snapshots of the database 220 and logs 225 may be made. Those of skill in the art will understand that various techniques may be used to protect the database 220 and logs 225.
Other Uses of Data Copies
[0090] Copies of data created using the techniques described herein may be utilized in other fashions. For example, a first snapshot of a database 220 and logs 225 could be mounted for use by a client 130 other than the original client 130 (for example, for use as a standby server). Prior to being mounted, a second snapshot could be made of the first snapshot in order to be able to back out or undo any changes to the first snapshot by the mounting and subsequent use.
[0091] As another example, after the first snapshot of the database 220 and logs 225 is mounted by the other client 130, tests could be run on the first snapshot in order to validate or verify the first snapshot (e.g., to ensure that the database 220 and logs 225 was correctly copied, such as by reading individual data objects in the database 220 and logs 225). For example, data could be read out of the database 220 and logs 225 and compared to data read out of the copy of the database 220 and logs 225 to ensure that the data is valid (e.g., by creating checksums of the data and comparing the checksums). This could obviate the need to validate or verify the first snapshot by restoring the first snapshot to its original location, which could be a lengthy process. Tests could also be run on the first snapshot to check the integrity of the original database 220 and logs 225.
[0092] Snapshots may be taken of copies of data created by non-snapshot operations in order to perform these and other functions described herein.
CONCLUSION
[0093] From the foregoing, it will be appreciated that specific examples of data storage systems have been described herein for purposes of illustration, but that various modifications may be made without deviating from the spirit and scope of the invention. For example, although snapshot operations may have been described, the systems may be used to perform many types of storage operations (e.g., backup operations, restore operations, archival operations, copy operations, Continuous Data Replication (CDR) operations, recovery operations, migration operations, HSM operations, etc.). Accordingly, the invention is not limited except as by the appended claims.
[0094] Terms and phrases used in this document, and variations thereof, unless otherwise expressly stated, should be construed as open ended as opposed to limiting. As examples of the foregoing: the term "including" should be read as meaning "including, without limitation" or the like; the term "example" is used to provide suitable instances of the item in discussion, not an exhaustive or limiting list thereof; the terms "a" or "an" should be read as meaning "at least one," "one or more" or the like; and adjectives such as "conventional," "traditional," "normal," "standard," "known" and terms of similar meaning should not be construed as limiting the item described to a given time period or to an item available as of a given time, but instead should be read to encompass conventional, traditional, normal, or standard technologies that may be available or known now or at any time in the future. Likewise, where this document refers to technologies that would be apparent or known to one of ordinary skill in the art, such technologies encompass those apparent or known to the skilled artisan now or at any time in the future.
[0095] The presence of broadening words and phrases such as "one or more," "at least," "but not limited to" or other like phrases in some instances shall not be read to mean that the narrower case is intended or required in instances where such broadening phrases may be absent. The use of the term "module" does not imply that the components or functionality described or claimed as part of the module are all configured in a common package. Indeed, any or all of the various components of a module, whether control logic or other components, can be combined in a single package or separately maintained and can further be distributed in multiple groupings or packages or across multiple locations.
[0096] Unless the context clearly requires otherwise, throughout the description and the claims, the words "comprise," "comprising," and the like are to be construed in an inclusive sense, as opposed to an exclusive or exhaustive sense; that is to say, in the sense of "including, but not limited to." The word "coupled," as generally used herein, refers to two or more elements that may be either directly connected, or connected by way of one or more intermediate elements. Additionally, the words "herein," "above," "below," and words of similar import, when used in this application, shall refer to this application as a whole and not to any particular portions of this application. Where the context permits, words in the above Detailed Description using the singular or plural number may also include the plural or singular number respectively. The word "or" in reference to a list of two or more items, that word covers all of the following interpretations of the word: any of the items in the list, all of the items in the list, and any combination of the items in the list.
[0097] The above detailed description of embodiments of the invention is not intended to be exhaustive or to limit the invention to the precise form disclosed above. While specific embodiments of, and examples for, the invention are described above for illustrative purposes, various equivalent modifications are possible within the scope of the invention, as those skilled in the relevant art will recognize. For example, while processes or blocks are presented in a given order, alternative embodiments may perform routines having steps, or employ systems having blocks, in a different order, and some processes or blocks may be deleted, moved, added, subdivided, combined, and/or modified. Each of these processes or blocks may be implemented in a variety of different ways. Also, while processes or blocks are at times shown as being performed in series, these processes or blocks may instead be performed in parallel, or may be performed at different times.
[0098] The teachings of the invention provided herein can be applied to other systems, not necessarily the system described above. The elements and acts of the various embodiments described above can be combined to provide further embodiments.
[0099] Any patents and applications and other references noted above, including any that may be listed in accompanying filing papers, are incorporated herein by reference. Aspects of the invention can be modified, if necessary, to employ the systems, functions, and concepts of the various references described above to provide yet further implementations of the invention.
[0100] These and other changes can be made to the invention in light of the above Detailed Description. While the above description details certain embodiments of the invention and describes the best mode contemplated, no matter how detailed the above appears in text, the invention can be practiced in many ways. Details of the system may vary considerably in implementation details, while still being encompassed by the invention disclosed herein. As noted above, particular terminology used when describing certain features or aspects of the invention should not be taken to imply that the terminology is being redefined herein to be restricted to any specific characteristics, features, or aspects of the invention with which that terminology is associated. In general, the terms used in the following claims should not be construed to limit the invention to the specific embodiments disclosed in the specification, unless the above Detailed Description section explicitly defines such terms. Accordingly, the actual scope of the invention encompasses not only the disclosed embodiments, but also all equivalent ways of practicing or implementing the invention under the claims.
[0101] While certain aspects of the invention are presented below in certain claim forms, the inventors contemplate the various aspects of the invention in any number of claim forms. For example, while only one aspect of the invention is recited as embodied in a computer-readable medium, other aspects may likewise be embodied in a computer-readable medium. As another example, while only one aspect of the invention is recited as a means-plus-function claim under 35 U.S.C. .sctn. 112, sixth paragraph, other aspects may likewise be embodied as a means-plus-function claim, or in other forms, such as being embodied in a computer-readable medium. (Any claims intended to be treated under 35 U.S.C. .sctn. 112, 6 will begin with the words "means for.") Accordingly, the inventors reserve the right to add additional claims after filing the application to pursue such additional claim forms for other aspects of the invention.
* * * * *
D00000

D00001

D00002

D00003

D00004

D00005

D00006

D00007

D00008
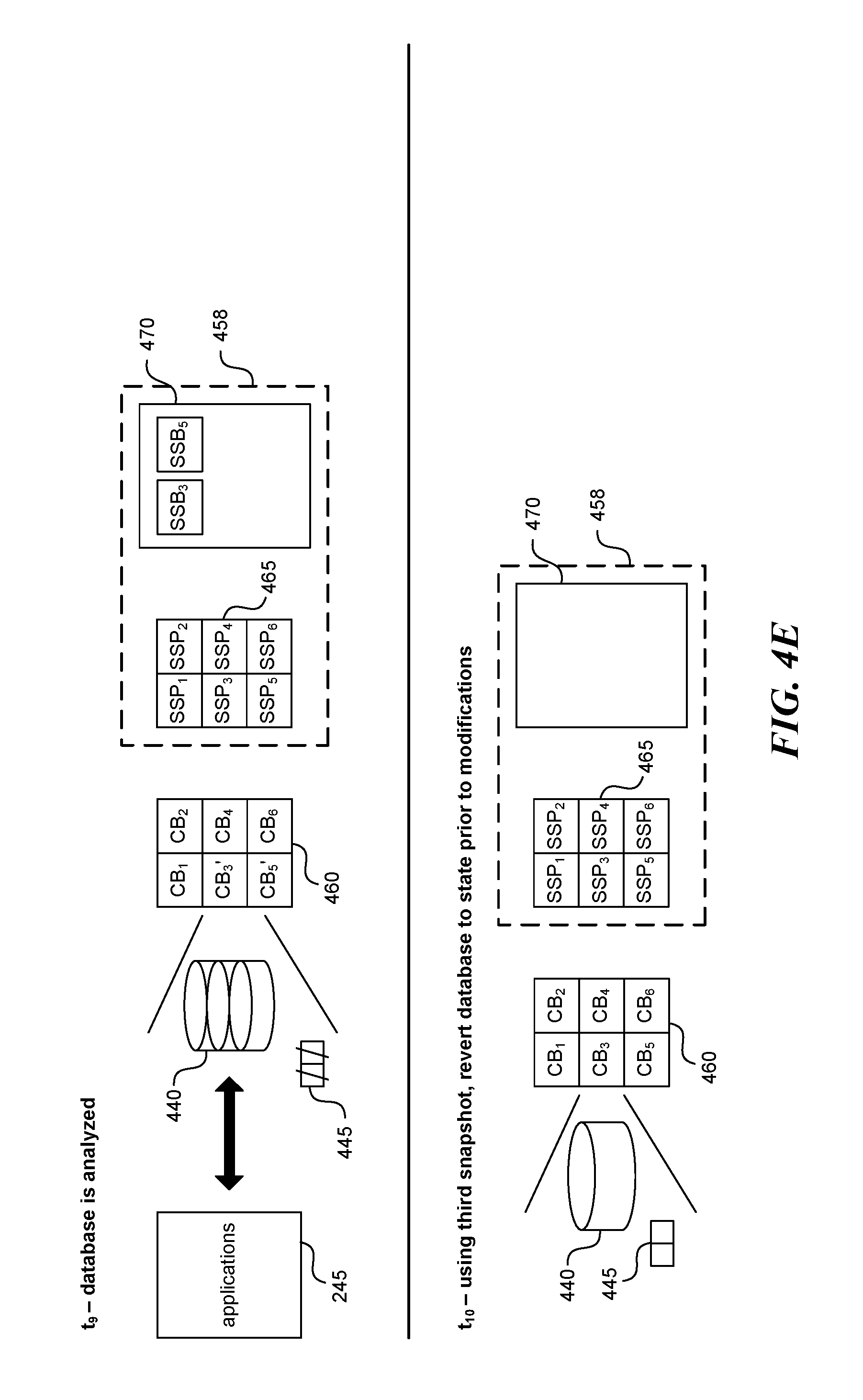
D00009

XML
uspto.report is an independent third-party trademark research tool that is not affiliated, endorsed, or sponsored by the United States Patent and Trademark Office (USPTO) or any other governmental organization. The information provided by uspto.report is based on publicly available data at the time of writing and is intended for informational purposes only.
While we strive to provide accurate and up-to-date information, we do not guarantee the accuracy, completeness, reliability, or suitability of the information displayed on this site. The use of this site is at your own risk. Any reliance you place on such information is therefore strictly at your own risk.
All official trademark data, including owner information, should be verified by visiting the official USPTO website at www.uspto.gov. This site is not intended to replace professional legal advice and should not be used as a substitute for consulting with a legal professional who is knowledgeable about trademark law.