Secure Data Processing
DING; Wenxiu ; et al.
U.S. patent application number 16/314196 was filed with the patent office on 2019-07-25 for secure data processing. The applicant listed for this patent is NOKIA TECHNOLOGIES OY. Invention is credited to Wenxiu DING, Zheng YAN.
| Application Number | 20190229887 16/314196 |
| Document ID | / |
| Family ID | 60785724 |
| Filed Date | 2019-07-25 |
View All Diagrams
| United States Patent Application | 20190229887 |
| Kind Code | A1 |
| DING; Wenxiu ; et al. | July 25, 2019 |
SECURE DATA PROCESSING
Abstract
According to an example aspect of the present invention, there is provided an apparatus comprising at least one processing core, at least one memory including computer program code, the at least one memory and the computer program code being configured to, with the at least one processing core, cause the apparatus at least to receive, from a data provider, a first ciphertext, perform a mathematical manipulation of the first ciphertext, the mathematical manipulation modifying plaintext of the first ciphertext without decrypting the first ciphertext, the mathematical manipulation being identified by a computation identifier, obtain a second ciphertext from the first ciphertext by performing a cryptographic re-encryption operation, and provide the second ciphertext to a first computation party.
| Inventors: | DING; Wenxiu; (Shaanxi, CN) ; YAN; Zheng; (Shaanxi, CN) | ||||||||||
| Applicant: |
|
||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|
| Family ID: | 60785724 | ||||||||||
| Appl. No.: | 16/314196 | ||||||||||
| Filed: | June 30, 2016 | ||||||||||
| PCT Filed: | June 30, 2016 | ||||||||||
| PCT NO: | PCT/CN2016/087876 | ||||||||||
| 371 Date: | December 28, 2018 |
| Current U.S. Class: | 1/1 |
| Current CPC Class: | H04L 9/0816 20130101; H04L 9/008 20130101; H04L 9/14 20130101 |
| International Class: | H04L 9/00 20060101 H04L009/00; H04L 9/14 20060101 H04L009/14; H04L 9/08 20060101 H04L009/08 |
Claims
1. An apparatus, comprising: at least one processor; and at least one memory including computer program code, the at least one memory and the computer program code being configured to, with the at least one processor, cause the apparatus at least to perform: receiving, from a data provider, a first ciphertext; performing a mathematical manipulation of the first ciphertext, the mathematical manipulation modifying plaintext of the first ciphertext without decrypting the first ciphertext, the mathematical manipulation being identified by a computation identifier; obtaining a second ciphertext from the first ciphertext by performing a cryptographic re-encryption operation; and providing the second ciphertext to a first computation party.
2. The apparatus according to claim 1, wherein the apparatus is configured to obtain the computation identifier from the first computation party.
3. The apparatus according to claim 1, wherein the apparatus is further configured to participate in negotiating a shared secret with the first computation party.
4. The apparatus according to claim 3, wherein the cryptographic re-encryption operation is performed in dependence of the computation identifier.
5. The apparatus according to claim 1, wherein the second ciphertext is not decryptable solely by a secret key of the first computation party.
6. The apparatus according to claim 1, wherein the apparatus is further configured to obtain a key pair comprising a public key of the apparatus and a secret key of the apparatus.
7. The apparatus according to claim 1, wherein the computation identifier identifies at least one of the following processes: addition, subtraction, multiplication, sign acquisition, comparison, equivalence test and variance.
8. The apparatus according to claim 1, wherein the apparatus is further configured to obtain a third ciphertext from the first ciphertext, to provide the third ciphertext to a second computation party, and to obtain a fourth ciphertext from responses received in the apparatus from the first computation party and the second computation party, and to obtain an encrypted result of a computation process identified by the computation identifier.
9. An apparatus, comprising: at least one processor, at least one memory including computer program code, the at least one memory and the computer program code being configured to, with the at least one processor, cause the apparatus at least to perform: determining, based on a message from a data requester, a computation identifier; transmitting a request to a data service provider, the request comprising the computation identifier; receiving, from the data service provider, a first ciphertext; obtaining a second ciphertext from the first ciphertext by performing a cryptographic re-encryption operation; and providing the second ciphertext to the data requester as a response to the message.
10. The apparatus according to claim 9, wherein the apparatus is further configured to check an access policy before providing the request to the data service provider.
11. The apparatus according to claim 9, wherein the apparatus is further configured to participate in negotiating a shared secret with the data service provider.
12. The apparatus according to claim 11, wherein the negotiating comprises a Diffie-Hellman negotiation.
13. The apparatus according to claim 9, wherein the apparatus is configured to perform the cryptographic re-encryption operation in dependence of the computation identifier.
14. The apparatus according to claim 9, wherein the computation identifier identifies one of the following computation processes: addition, subtraction, multiplication, sign acquisition, comparison, equivalence test and variance.
15-28. (canceled)
29. A system comprising an apparatus according to claim 1, an apparatus according to claim 9, a data requester and a data provider.
30. (canceled)
31. (canceled)
32. A computer program embodied on a non-transitory computer readable medium having stored thereon a set of computer readable instructions that, when executed by at least one processor, cause an apparatus to at least: receive, from a data provider, a first ciphertext; perform a mathematical manipulation of the first ciphertext, the mathematical manipulation modifying plaintext of the first ciphertext without decrypting the first ciphertext, the mathematical manipulation being identified by a computation identifier; obtain a second ciphertext from the first ciphertext by performing a cryptographic re-encryption operation; and provide the second ciphertext to a first computation party.
33. A computer program embodied on a non-transitory computer readable medium having stored thereon a set of computer readable instructions that, when executed by at least one processor, cause an apparatus to at least: obtain a key pair comprising a public key of an apparatus and a secret key of the apparatus; determine, based on a message from a data requester, a computation identifier; transmit a request to a data service provider, the request comprising the computation identifier and a public key of the data requester; receive, from the data service provider, a first ciphertext; obtain a second ciphertext from the first ciphertext by performing a cryptographic re-encryption operation; and provide the second ciphertext to the data requester as a response to the message.
34. (canceled)
Description
FIELD
[0001] The present invention relates to processing information in encrypted form, for example in a cloud service provision environment.
BACKGROUND
[0002] Cloud computing services provide off-site opportunities for individuals and corporations. For example, cloud storage service enables off-site storage of data sets in a flexible manner in a data centre, reducing the need for users of the cloud service to obtain their own storage hardware, for example for archiving purposes.
[0003] A further example of a cloud service is a cloud processing service, wherein a user is given access to processor resources at a computer or computing grid. This may be useful, for example where a user needs access to high-capacity computing intermittently, and obtaining actual high-capacity computing hardware would be wasteful as the hardware would mostly be unused, since the need is only intermittent.
[0004] Consumers may use cloud services to back up their data, for example during operating system updates of their devices, such as computers, smartphones and laptops. Some smart devices are configured to automatically upload images captured by users to a cloud storage service.
[0005] While useful, cloud services present high risk to users. Personal information may accidentally, or purposefully, be stored on a cloud storage service. Such personal information may become vulnerable to theft, unauthorised modification or eavesdropping either during transit to or from the cloud storage service, or while in the cloud storage service. The cloud service provider may be untrusted or only partially trusted. Furthermore, the cloud service may be distributed between several data centres, and customer data may be communicated between such data centres to balance load between the centres. Such communication presents additional risk of eavesdropping.
[0006] As it relates to cloud processing services, risks are also present. Where a user seeks to analyse medical patient data, for example, not only the data itself but also its processing is highly confidential by its intrinsic nature. Similar considerations apply to other confidential data that may be processed, such as corporate, personal or military data. For example, analysing stealth-defeating radar may comprise complex processing of plural radar signals and their combinations. Clearly, such signal processing is secret due to its nature.
SUMMARY OF THE INVENTION
[0007] The invention is defined by the features of the independent claims. Some specific embodiments are defined in the dependent claims.
[0008] According to a first aspect of the present invention, there is provided an apparatus comprising at least one processing core, at least one memory including computer program code, the at least one memory and the computer program code being configured to, with the at least one processing core, cause the apparatus at least to receive, from a data provider, a first ciphertext, perform a mathematical manipulation of the first ciphertext, the mathematical manipulation modifying plaintext of the first ciphertext without decrypting the first ciphertext, the mathematical manipulation being identified by a computation identifier, obtain a second ciphertext from the first ciphertext by performing a cryptographic re-encryption operation, and provide the second ciphertext to a first computation party.
[0009] Various embodiments of the first aspect may comprise at least one feature from the following bulleted list: [0010] the apparatus is configured to obtain the computation identifier from the first computation party [0011] the apparatus is further configured to participate in negotiating a shared secret with the first computation party [0012] the cryptographic re-encryption operation is performed in dependence of the computation identifier [0013] the second ciphertext is not decryptable solely by a secret key of the first computation party [0014] the apparatus is further configured to obtain a key pair comprising a public key of the apparatus and a secret key of the apparatus [0015] the computation identifier identifies at least one of the following processes: addition, subtraction, multiplication, sign acquisition, comparison, equivalence test and variance [0016] the apparatus is further configured to obtain a third ciphertext from the first ciphertext, to provide the third ciphertext to a second computation party, and to obtain a fourth ciphertext from responses received in the apparatus from the first computation party and the second computation party, and to obtain an encrypted result of a computation process identified by the computation identifier.
[0017] According to a second aspect of the present invention, there is provided an apparatus comprising at least one processing core, at least one memory including computer program code, the at least one memory and the computer program code being configured to, with the at least one processing core, cause the apparatus at least to determine, based on a message from a data requester, a computation identifier, transmit a request to a data service provider, the request comprising the computation identifier, receive, from the data service provider, a first ciphertext, obtain a second ciphertext from the first ciphertext by performing a cryptographic re-encryption operation, and provide the second ciphertext to the data requester as a response to the message.
[0018] Various embodiments of the second aspect may comprise at least one feature from the following bulleted list: [0019] the apparatus is further configured to check an access policy before providing the request to the data service provider [0020] the apparatus is further configured to participate in negotiating a shared secret with the data service provider [0021] the negotiating comprises a Diffie-Hellman negotiation [0022] the apparatus is configured to perform the cryptographic re-encryption operation in dependence of the computation identifier [0023] the computation identifier identifies one of the following computation processes: addition, subtraction, multiplication, sign acquisition, comparison, equivalence test and variance.
[0024] According to a third aspect of the present invention, there is provided a method comprising receiving, from a data provider, a first ciphertext, performing a mathematical manipulation of the first ciphertext, the mathematical manipulation modifying plaintext of the first ciphertext without decrypting the first ciphertext, the mathematical manipulation being identified by a computation identifier, obtaining a second ciphertext from the first ciphertext by performing a cryptographic re-encryption operation, and providing the second ciphertext to a first computation party.
[0025] Various embodiments of the third aspect may comprise at least one feature corresponding to a feature from the preceding bulleted list laid out in connection with the first aspect.
[0026] According to a fourth aspect of the present invention, there is provided a method comprising determining, based on a message from a data requester, a computation identifier, transmitting a request to a data service provider, the request comprising the computation identifier, receiving, from the data service provider, a first ciphertext, obtaining a second ciphertext from the first ciphertext by performing a cryptographic re-encryption operation, and providing the second ciphertext to the data requester as a response to the message.
[0027] Various embodiments of the fourth aspect may comprise at least one feature corresponding to a feature from the preceding bulleted list laid out in connection with the second aspect.
[0028] According to a fifth aspect of the present invention, there is provided a system comprising an apparatus according to the first aspect, an apparatus according to the second aspect, a data requester and a data provider.
[0029] According to a sixth aspect of the present invention, there is provided an apparatus comprising means for receiving, from a data provider, a first ciphertext, means for performing a mathematical manipulation of the first ciphertext, the mathematical manipulation modifying plaintext of the first ciphertext without decrypting the first ciphertext, the mathematical manipulation being identified by a computation identifier, means for obtaining a second ciphertext from the first ciphertext by performing a cryptographic re-encryption operation, and means for providing the second ciphertext to a first computation party.
[0030] According to a seventh aspect of the present invention, there is provided an apparatus comprising means for obtaining a key pair comprising a public key of an apparatus and a secret key of the apparatus, means for determining, based on a message from a data requester, a computation identifier, means for transmitting a request to a data service provider, the request comprising the computation identifier and a public key of the data requester, means for receiving, from the data service provider, a first ciphertext, means for obtaining a second ciphertext from the first ciphertext by performing a cryptographic re-encryption operation, and means for providing the second ciphertext to the data requester as a response to the message.
[0031] According to an eighth aspect of the present invention, there is provided a non-transitory computer readable medium having stored thereon a set of computer readable instructions that, when executed by at least one processor, cause an apparatus to at least receive, from a data provider, a first ciphertext, perform a mathematical manipulation of the first ciphertext, the mathematical manipulation modifying plaintext of the first ciphertext without decrypting the first ciphertext, the mathematical manipulation being identified by a computation identifier, obtain a second ciphertext from the first ciphertext by performing a cryptographic re-encryption operation, and provide the second ciphertext to a first computation party.
[0032] According to a ninth aspect of the present invention, there is provided a non-transitory computer readable medium having stored thereon a set of computer readable instructions that, when executed by at least one processor, cause an apparatus to at least obtain a key pair comprising a public key of an apparatus and a secret key of the apparatus, determine, based on a message from a data requester, a computation identifier, transmit a request to a data service provider, the request comprising the computation identifier and a public key of the data requester, receive, from the data service provider, a first ciphertext, obtain a second ciphertext from the first ciphertext by performing a cryptographic re-encryption operation, and provide the second ciphertext to the data requester as a response to the message.
[0033] According to a tenth aspect of the present invention, there is provided a computer program configured to cause a method in accordance with at least one of the third and fourth aspects to be performed.
BRIEF DESCRIPTION OF THE DRAWINGS
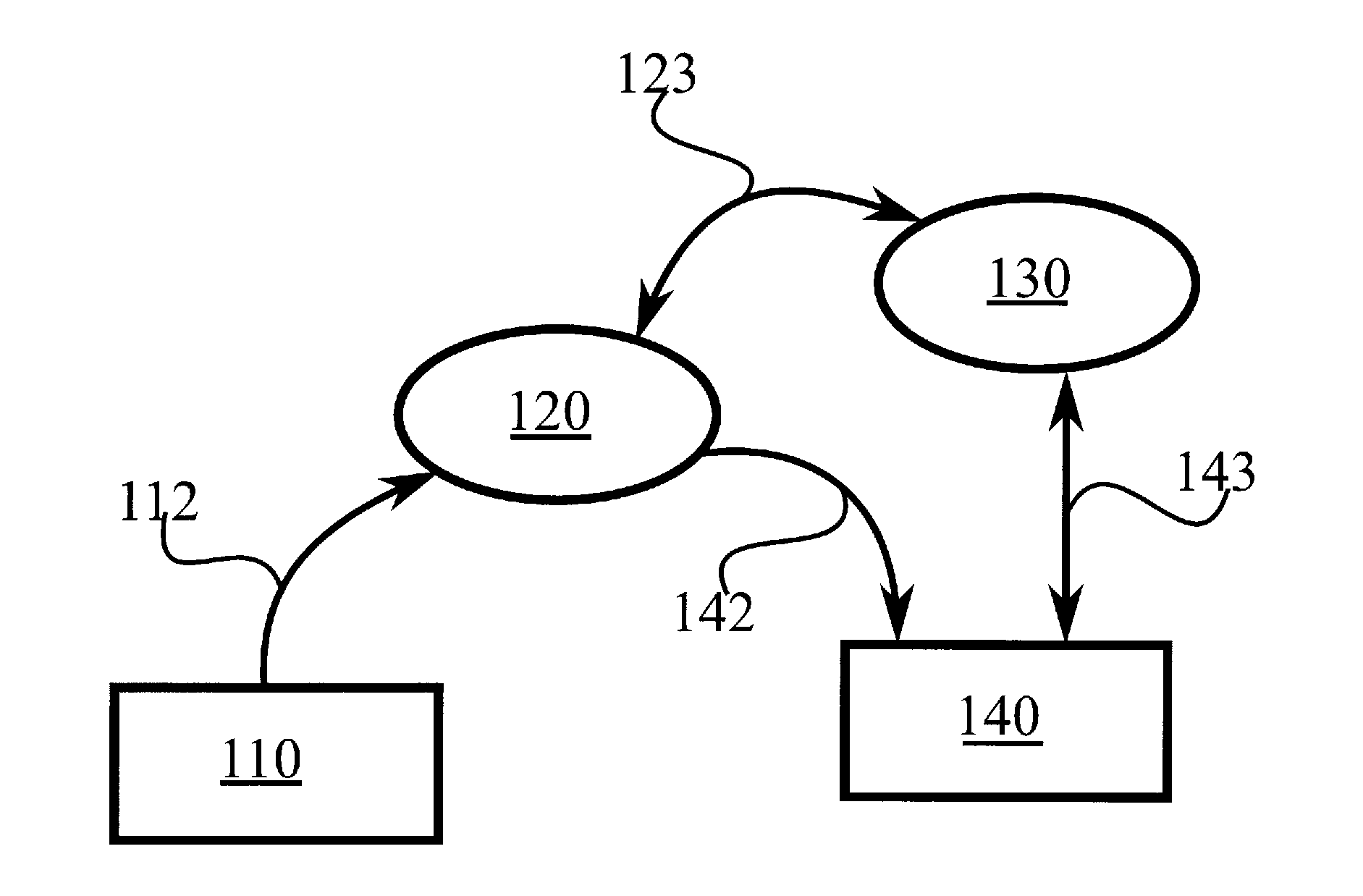
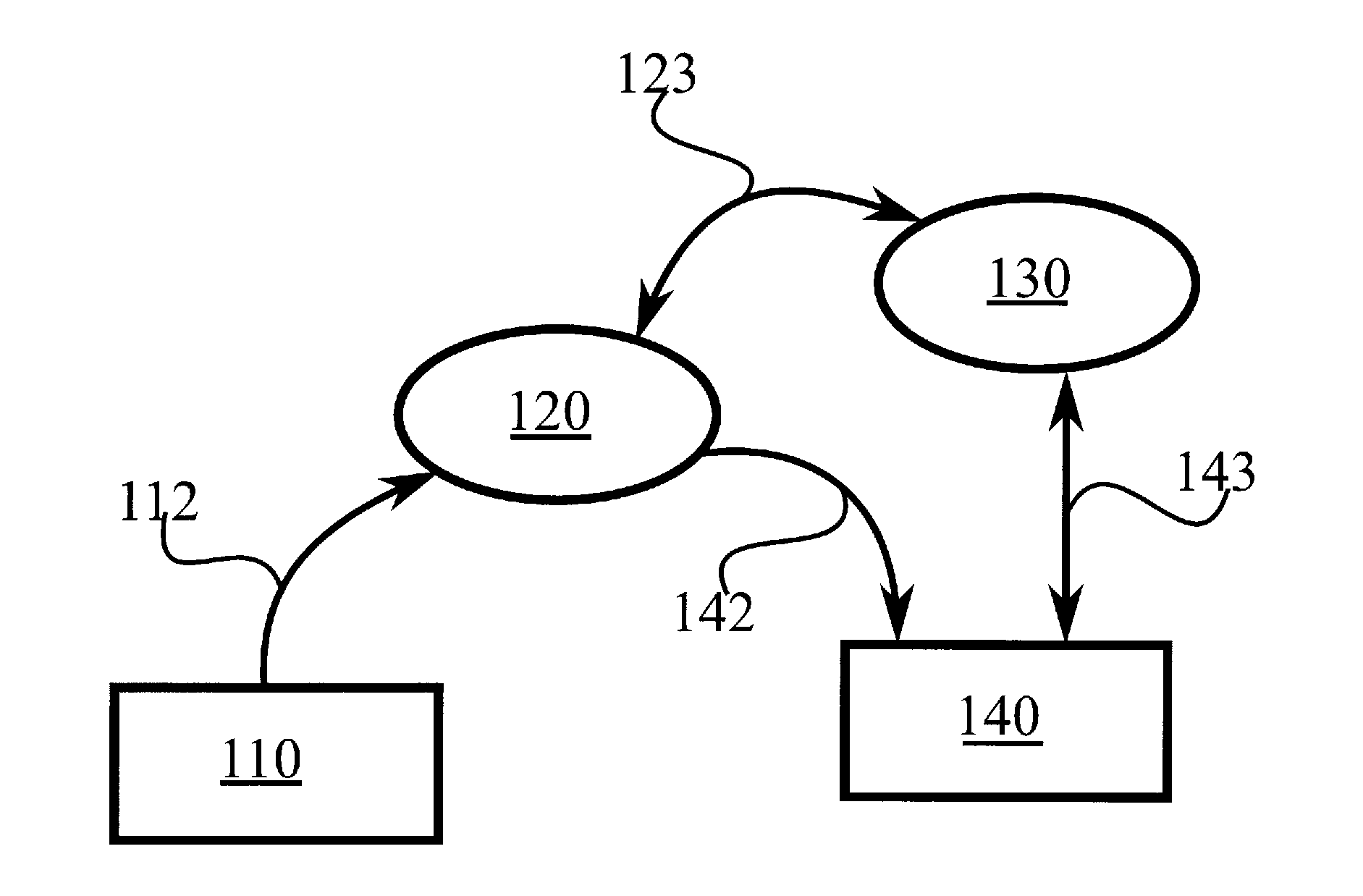
[0034] FIG. 1 illustrates an example system in accordance with at least some embodiments of the present invention;
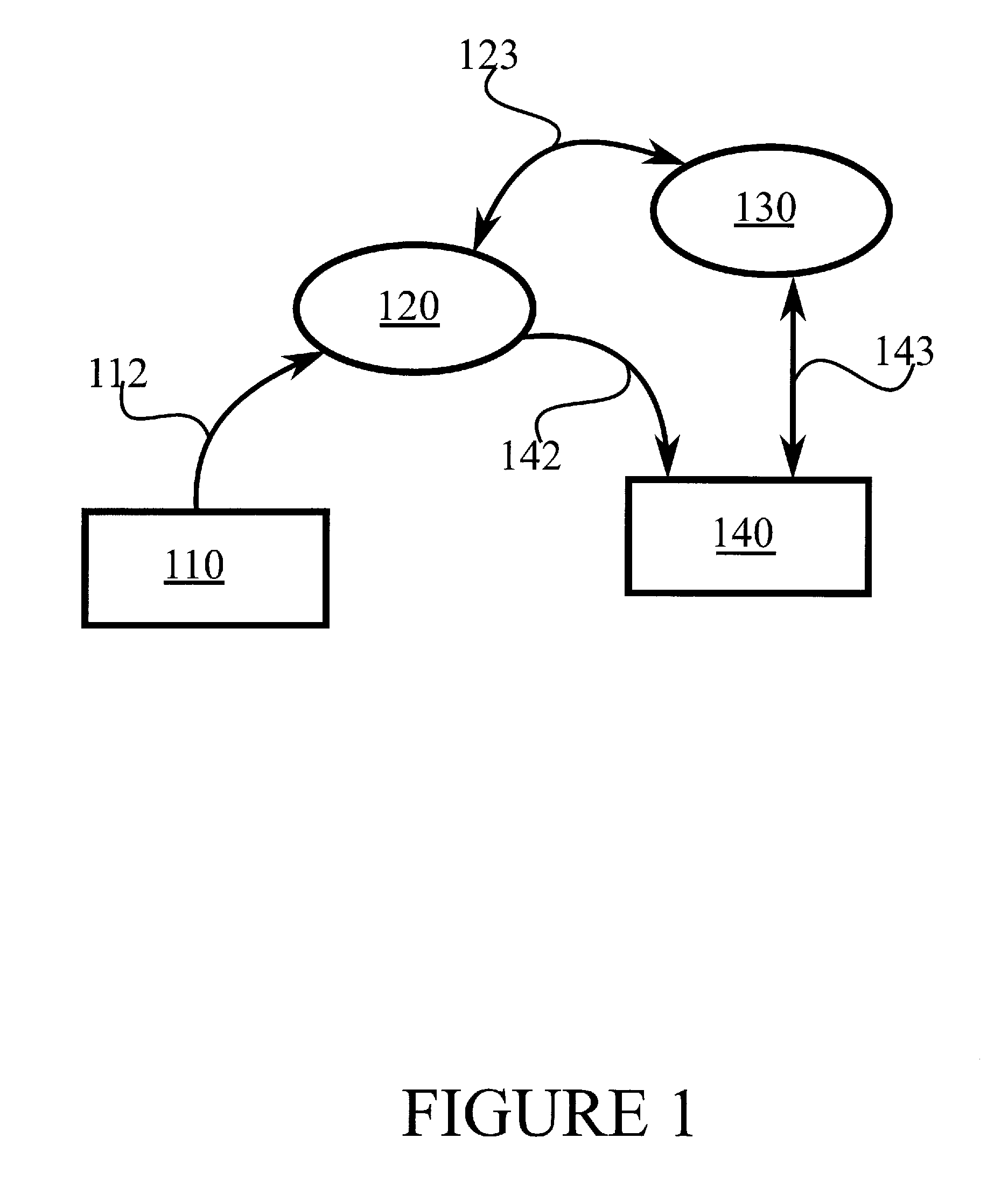
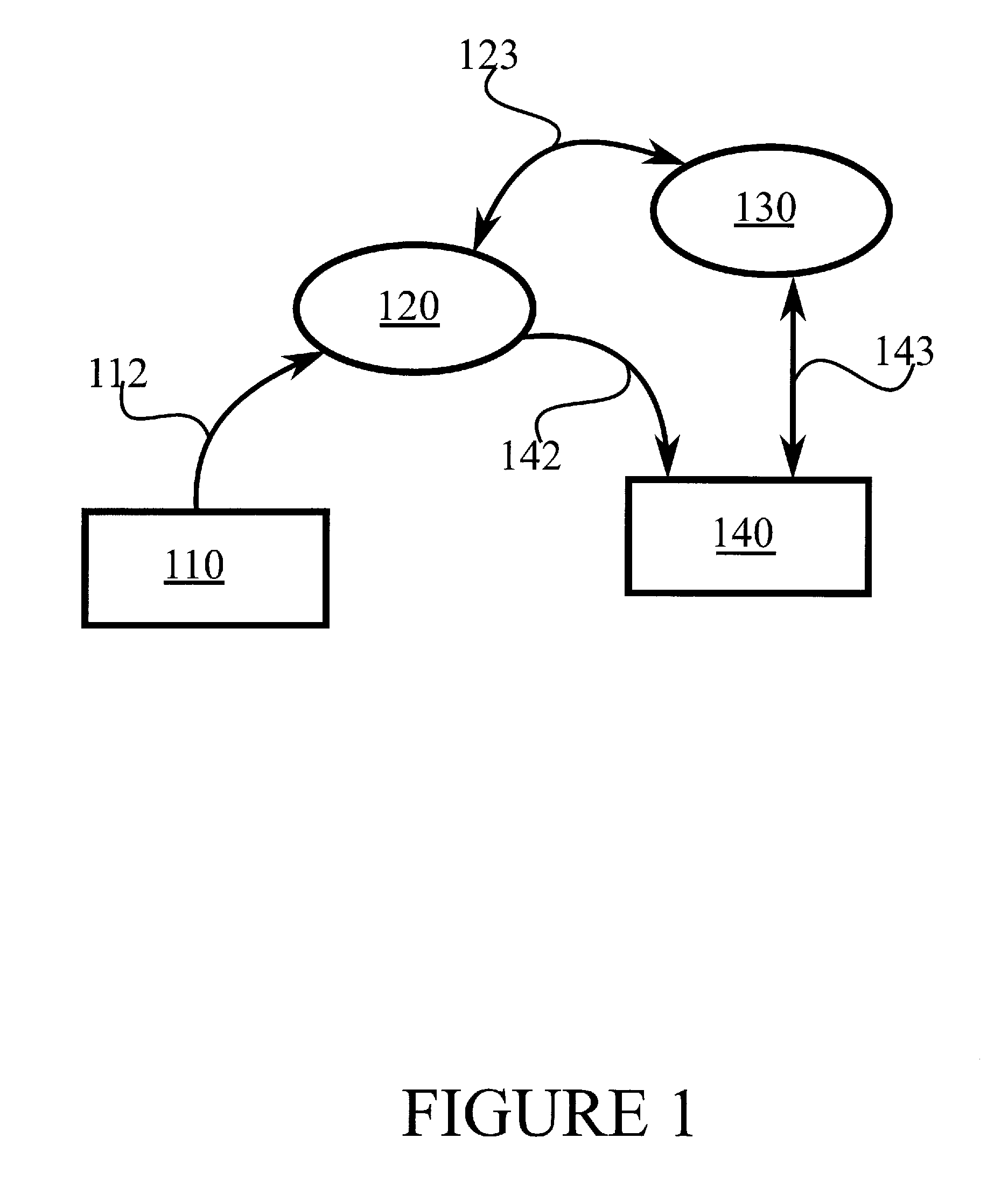
[0035] FIG. 2 illustrates an example system in accordance with at least some embodiments of the present invention.
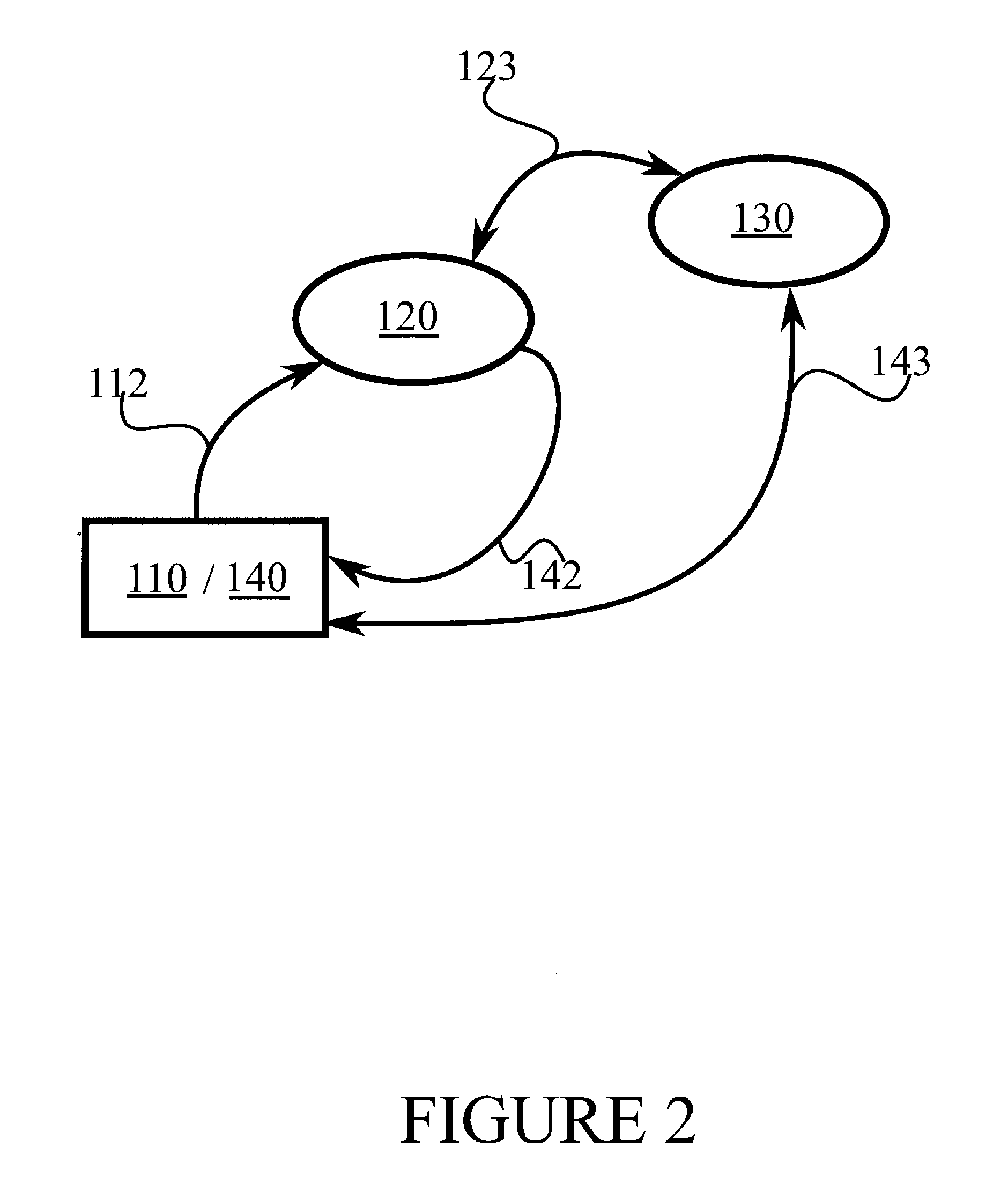
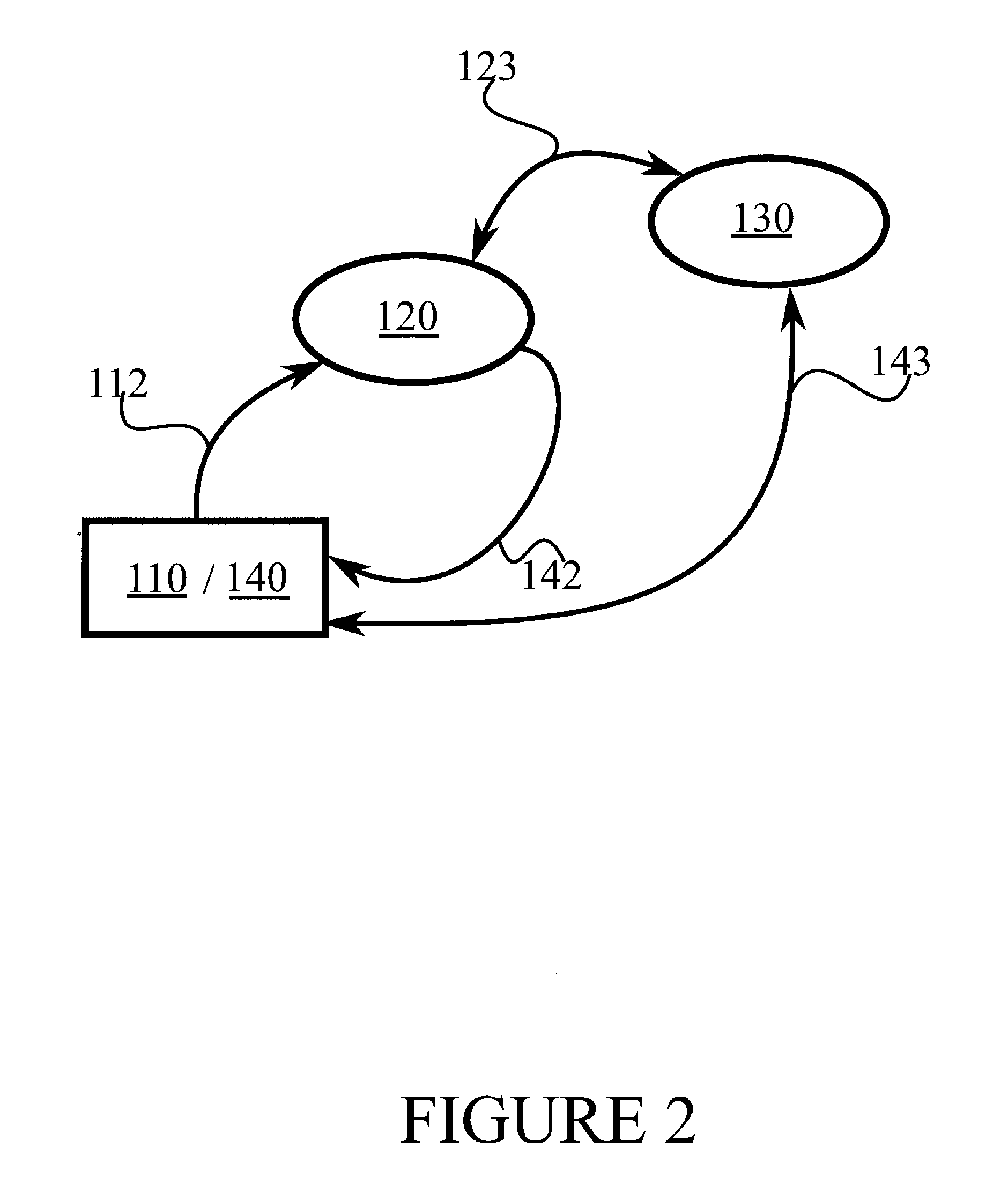
[0036] FIG. 3 illustrates an example apparatus capable of supporting at least some embodiments of the present invention;
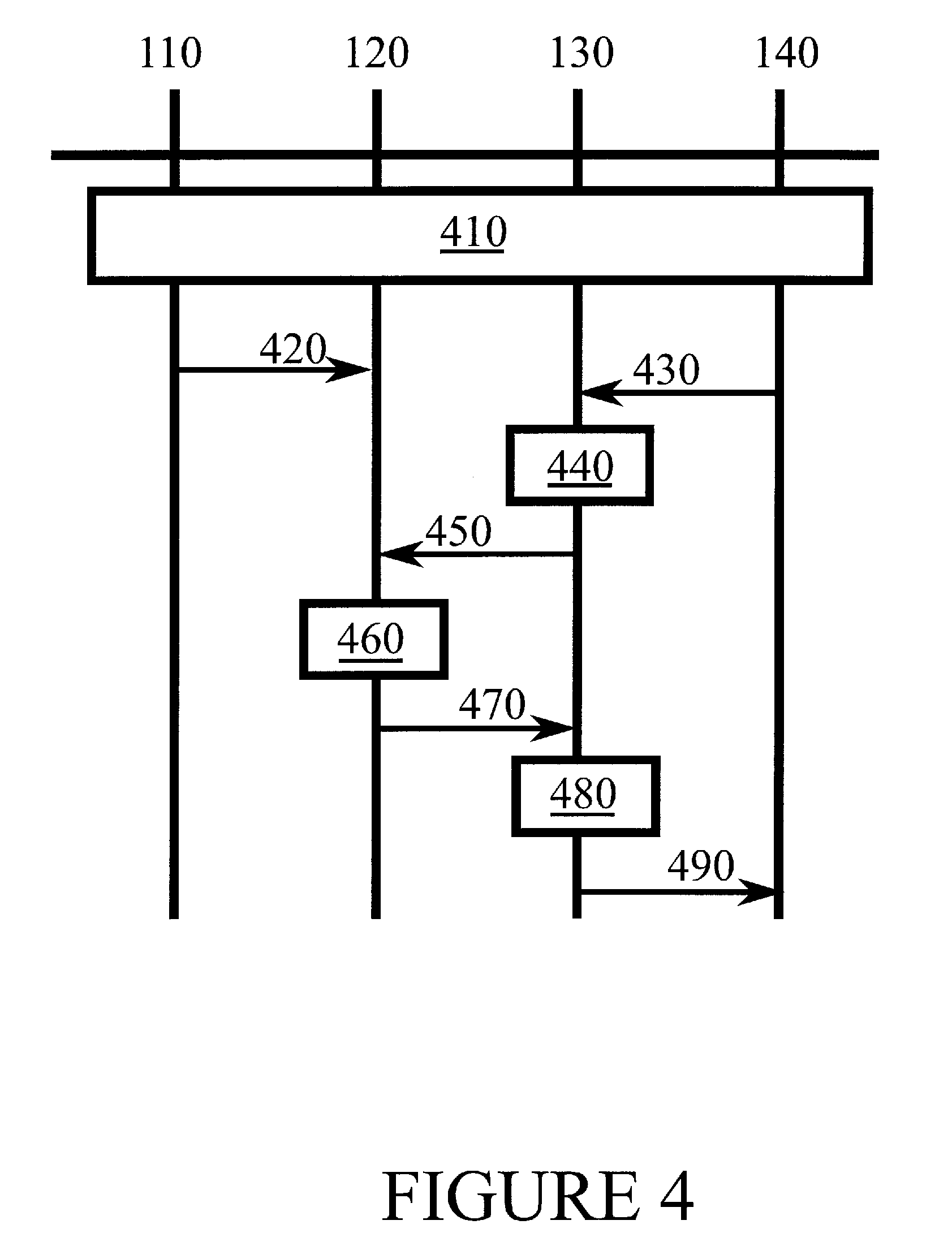
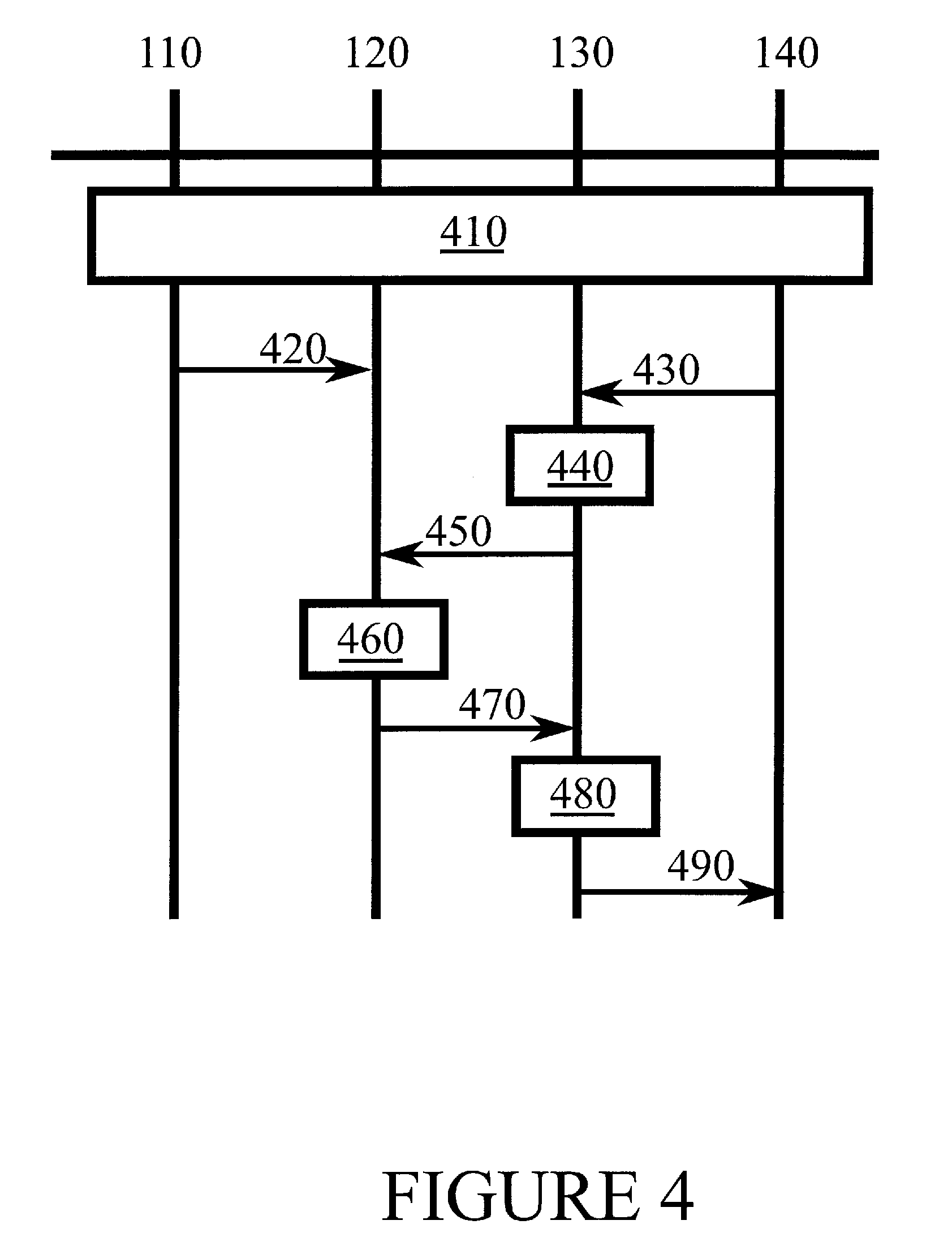
[0037] FIG. 4 illustrates signalling in accordance with at least some embodiments of the present invention;
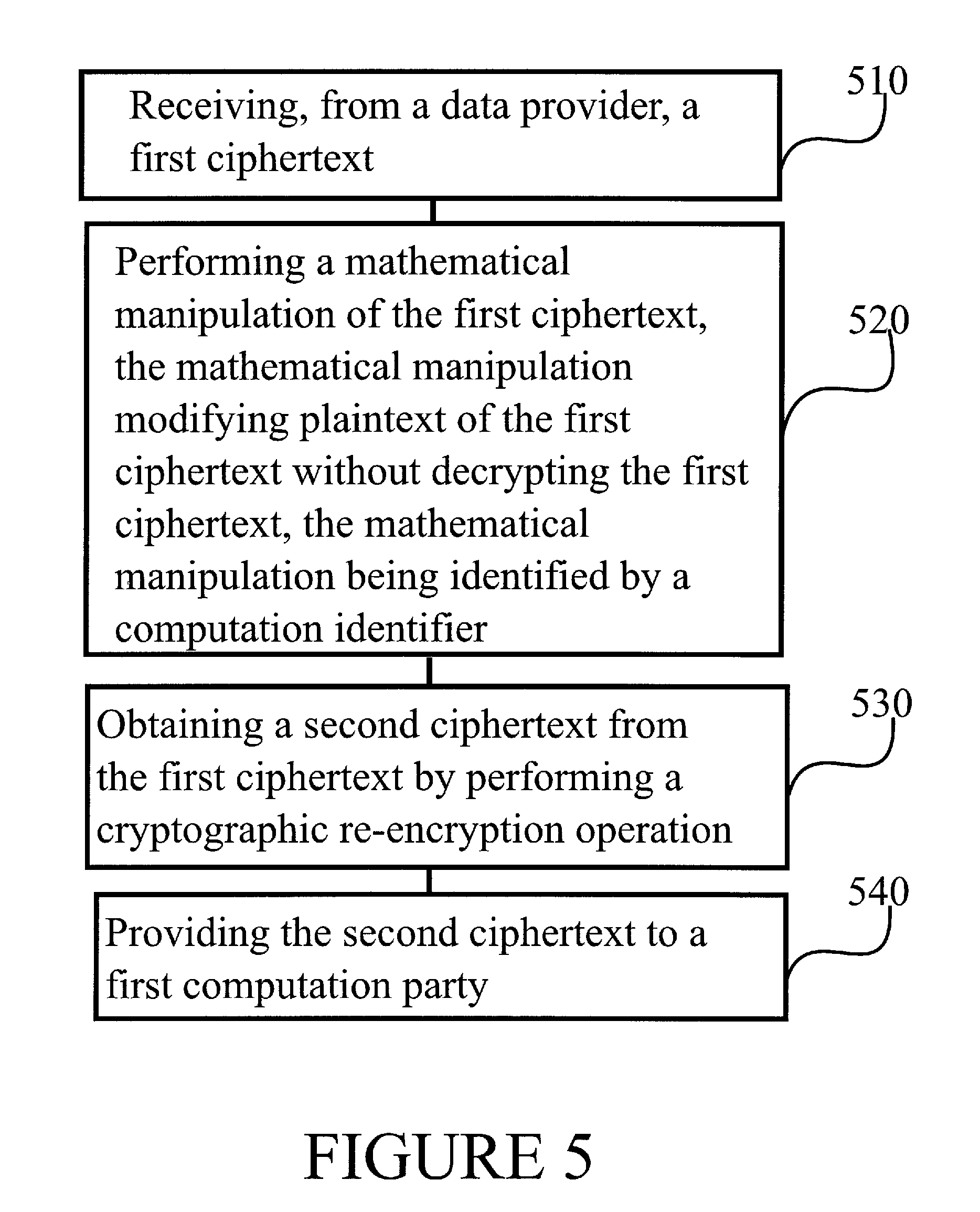
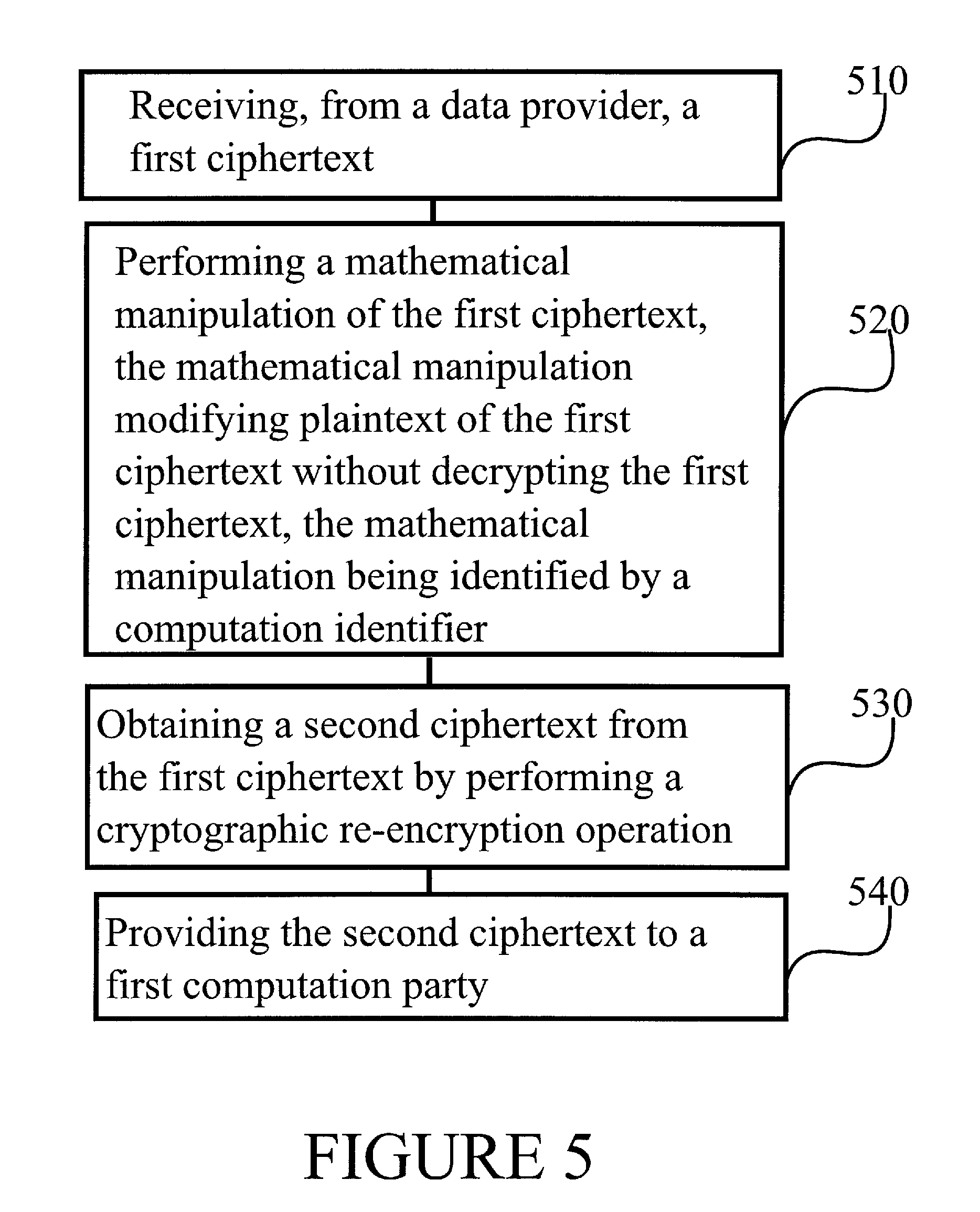
[0038] FIG. 5 is a flow graph of a method in accordance with at least some embodiments of the present invention, and
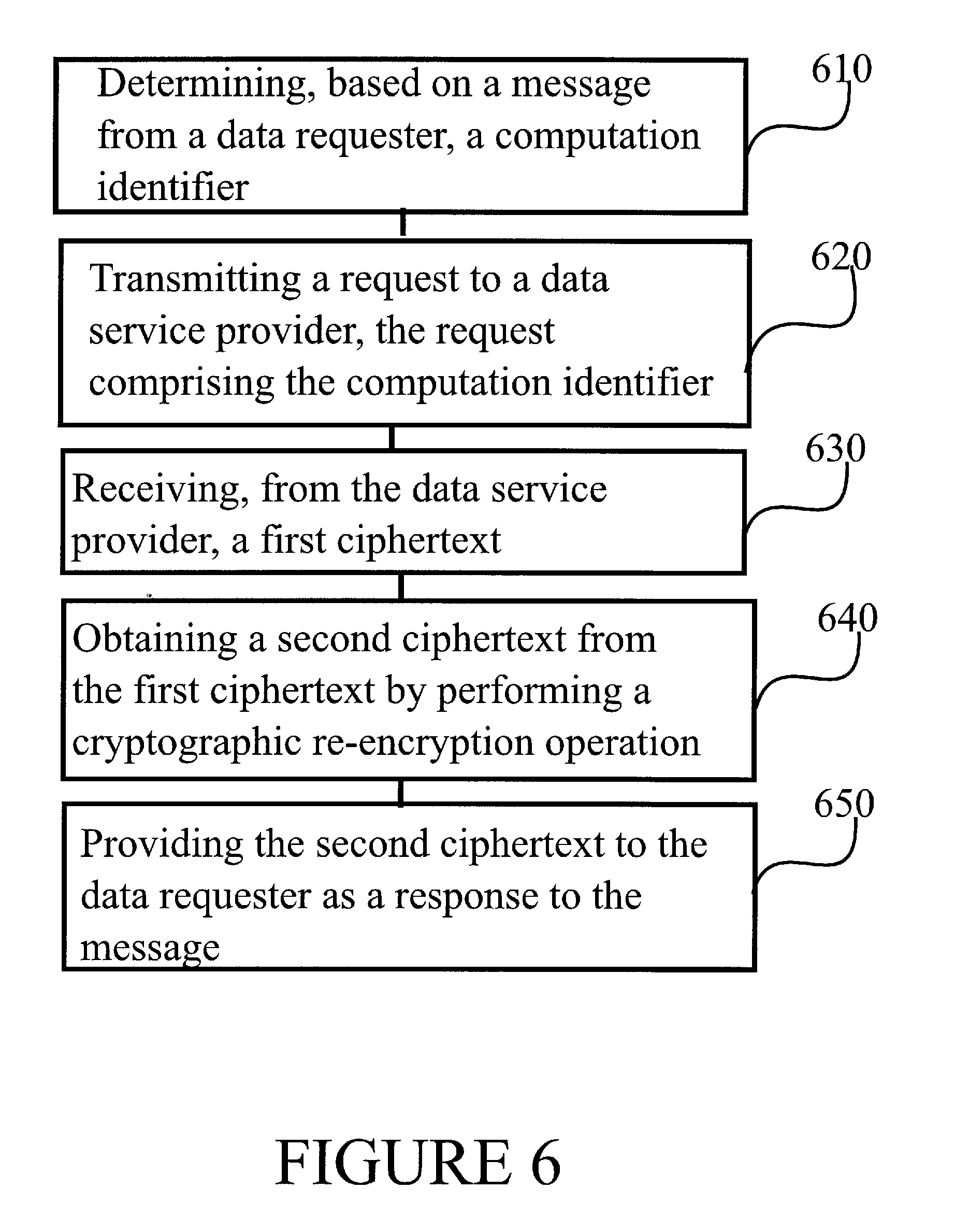
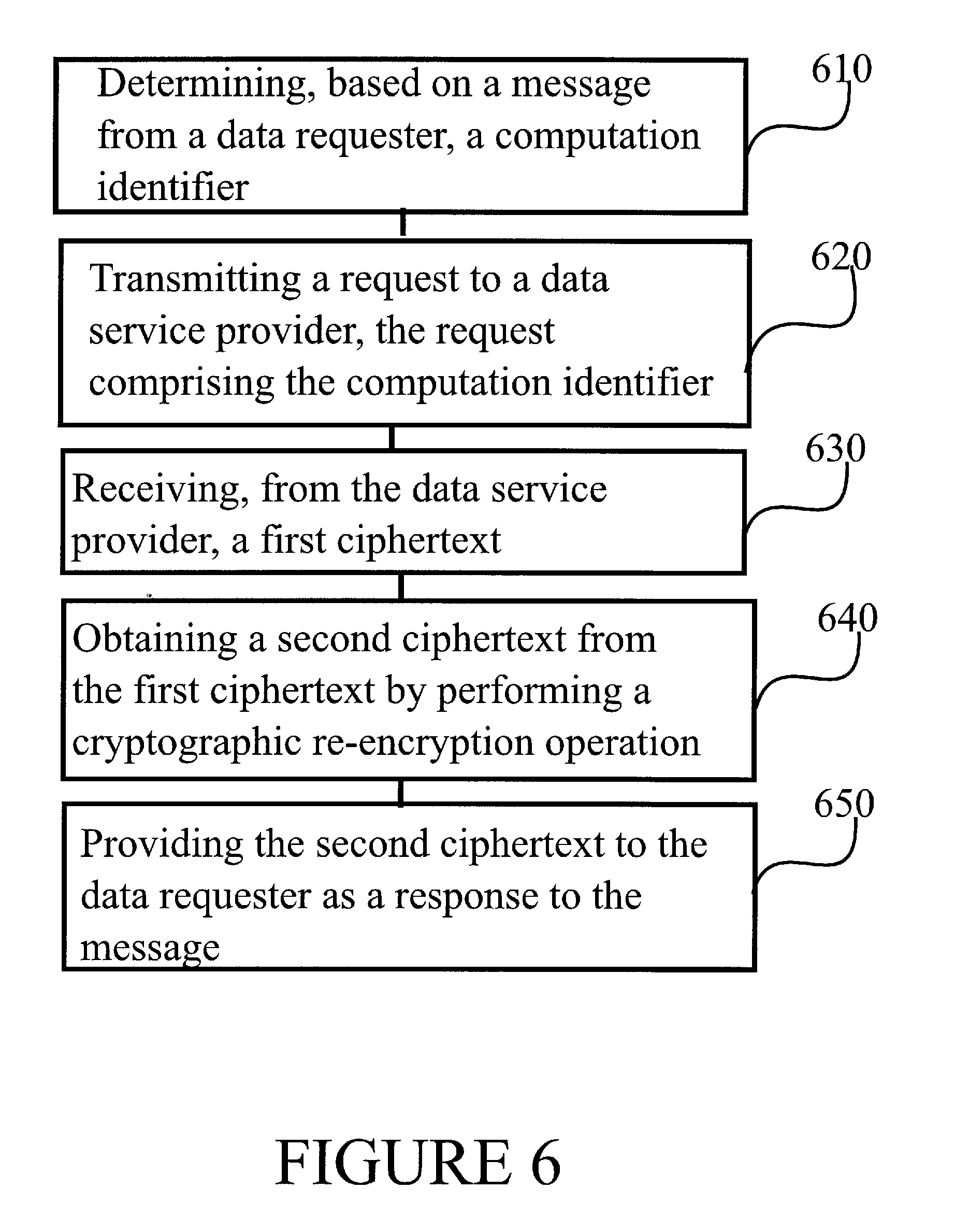
[0039] FIG. 6 is a flow graph of a method in accordance with at least some embodiments of the present invention.
EMBODIMENTS
[0040] Confidential processing of data in a cloud service may be obtained by dividing processing into parts, the processing being conducted on encrypted data, which is known as ciphertext. A two-level decryption process is used with two service provision entities, a data service provider and a computation party, which co-operate to jointly perform secure processing of data and deliver processed data in encrypted form to a data requesting party. The data requesting party may be a same party as the one that provided the data, that it, a data provider. At least some embodiments of the invention operate using homomorphic re-encryption.
[0041] The data service provider may receive a computation identifier and perform a mathematical manipulation of a first ciphertext, to thereby modify a plaintext underlying the first ciphertext. In other words, the data service provider may perform a computation on plaintext of the first ciphertext, without decrypting the first ciphertext, by mathematically manipulating the first ciphertext. The manipulation, and/or corresponding modification of the plaintext, is identified by the computation identifier. Subsequently, the data service provider may re-encrypt the manipulated first ciphertext to obtain a second ciphertext. The re-encrypting may comprise use of a secret key of the data service provider and a public key of a data requester, for example. The re-encrypting may be performed in dependence of the computation identifier. Re-encrypting may comprise at least partial decryption followed by encryption.
[0042] FIG. 1 illustrates an example system in accordance with at least some embodiments of the present invention. The system comprises data service provider 120, which may comprise a cloud data storage data centre or cloud data centre system, for example. Data service provider 120 may also be a cloud processing service provider. A cloud data centre system may comprise a plurality of data centres, with load balancing arranged in a suitable manner between individual data centres comprised in the plurality. In general, data service provider 120 may be configured to store data and provide some computation services.
[0043] The system of FIG. 1 further comprises at least one computation party 130. Computation party 130 may comprise a processing-enabled computing entity, such as, for example, a data centre, data centre system, server, server farm or indeed an individual networked computer such as a desktop or a laptop. In general, computation party 130 may be configured to provide data computation services and/or data access control for its users. In the model described herein, there may exist several computation parties, CP, 130 that are operated by different entities, such as medical institutions, schools, and/or banks. Different CPs may deal with different kinds of data, for example health-related data, student records and financial information. Hence, a user may freely choose a CP he trusts for service consumption. This may enhance user security.
[0044] The system of FIG. 1 further comprises at least one data provider 110. Data provider 110 may comprise a data owner, such as, for example, a consumer, corporation or government entity, for example. For example, data provider 110 may generate the data. Data may be provided by an X-ray device or body scanner where data provider 110 is a medical entity, such as a clinic or hospital. Data may be generated in an industrial process or a design tool where data provider 110 is a corporate entity, such as a manufacturer or engineering company. Data may be generated in a radar or flight control facility where data provider 110 is a government entity, such as a military or aviation authority. Data provider 110 may be configured to provide data in encrypted form to data service provider 120.
[0045] The system of FIG. 1 further comprises data requester 140. Data requester 140 may comprise an entity authorised by data provider 110 to access, at least partly, data owned and/or generated by data provider 110. Data requester 140 may need the data of data provider 110 in a processed form. Data requester 140 may be the same entity as data provider 110.
[0046] Overall, data provider 110, data service provider 120, computation party 130 and data requester 140 may be seen as roles or functions that may be assumed and performed by different kinds of entities. As indicated above, data provider 110 and data requester 140 may be one and the same. On the other hand, data service provider 120 and computation party 130 are not physically the same entity. In detail, data service provider 120 need not be trusted by data provider 110, while computation party 130 may be trusted by data provider 110.
[0047] Networked connections interconnect the entities described above to each other. In detail, connection 112 enables data provider 110 to transmit ciphertext to data service provider 120. Connection 142 enables communication between data requester 140 and data service provider 120. Connection 123 enables communication between computation party 130 and data service provider 120. Finally, connection 143 enables communication between data requester 140 and computation party 130. The connections may be wired or, at least partly, wireless, connections, where applicable.
[0048] FIG. 2 illustrates an example system in accordance with at least some embodiments of the present invention. Like numbering denotes like structure as in FIG. 1. FIG. 2 corresponds to the case, where data requester 140 is the same entity as data provider 110. For example, this is the case where a data owner requests a cloud data processing result of his own data.
[0049] In the systems illustrated in FIG. 1 and FIG. 2, all entities are assumed to be curious but honest. That is, they are curious about others' data but act honestly by following the design of system protocols. In addition, the DSP 120 and the CPs 130 would be unlikely to collude with each other due to interest conflicts. Moreover, any collusion would decrease user trust in the CP 130, which leads to the loss of its users.
[0050] Three challenges are addressed by various embodiments of the present invention.
[0051] Firstly, existing ciphertext processing schemes cannot flexibly support multiparty access. Many schemes are designed based on a specified aggregator, wherein only this aggregator can access the aggregated result. Such schemes cannot support genuine multiparty access. The data provided by users cannot be used for data analysis by other authorized requesters. In some situations, data should be observed and collected all the time for potential use without knowing a concrete data access requester. For example, medical and clinical research can benefit greatly from statistics of patients. More than one party could be interested in requesting encrypted processing results after data collection and process. Hence, such an application scenario calls for a privacy-preserving data processing scheme for multiple unspecified requesters. However, existing work cannot support this demand in a flexibly and efficient way.
[0052] Secondly, it is desired that ciphertext processing results should be only accessed by authorized requesters. A data processing party, such as a cloud service provider, should not be able to access the results if it cannot be fully trusted by the data owner. The problem of privacy-preserving data aggregation with a distrusted aggregator has been studied, but such studies only describe systems that allow the aggregator to access the final aggregated results. Such schemes cannot satisfy the practical security requirement.
[0053] Thirdly, most existing research focuses on encrypted data aggregation and multiplication, which cannot support various computation operations over the same encrypted outsourced data. Aggregation and multiplication of encrypted data are not sufficient to satisfy emerging demands on data analytics in our daily life. Fully homomorphic encryption could support various computations of encrypted data, but it cannot flexibly control multiparty access on the processed data in an encrypted form because the finally processed data can only be decrypted with a corresponding secret key.
[0054] To solve the above-described three problems, a re-encryption scheme is proposed, which can flexibly support access control on encrypted-data computation results with two-level decryption. Furthermore, the proposed re-encryption scheme is applied to realize a number of operations over ciphertexts including addition, subtraction, multiplication, sign acquisition, comparison, equivalent test, and variance, which may support various applications that request processing of encrypted data and/or analytics thereof.
[0055] We consider a scenario with two types of independent service providers that do not collude with each other. One is data service provider, DSP, 120 that is responsible for data storage and partial computations. The other is computation party, CP, 130 that is in charge of data access control and additional computations. DSP 120 collects and stores the data in an encrypted form from a number of data providers, DP, 110. When a data requester, DR, 140, requires a data processing result, CP 130 may first check an access right of DR 140. If DR 140 is eligible to access the data, CP 130 contacts DSP 120 to further process the ciphertext with a re-encryption process for the DR 140, and then CP 130 may provide the re-encryption result to the authorized DR 140 for decryption. In addition, the described scheme supports multiple CPs 130 served by different companies for distributed data processing and access control. In general, DSP 120 and CP 130 together produce the ciphertext, with contents of the ciphertext processed as requested by DR 140, such that DSP 120 does not obtain access to the contents of the ciphertext despite DSP 120 participating in performing the requested processing.
[0056] Specifically, the contributions of this invention can be summarized as the following three elements:
[0057] Firstly, a new cryptographic primitive is described, which uses two service providers, DSP 120 and CP 130, to manage encrypted data and realizes re-encryption over homomorphic encryption. The primitive enables processing and analysis of ciphertext. Only authorized users can access the encrypted data processing result in a secure way.
[0058] Secondly, seven basic operations on encrypted data based on the primitive are described: addition, subtraction, multiplication, sign acquisition, comparison, equivalent test, and variance, which can satisfy many data processing demands.
[0059] Thirdly, to enhance the flexibility and security of the proposed schemes, we apply multiple CPs to take in charge of the data from their own customers and design computing operations over ciphertexts belonging to multiple CPs.
[0060] Paillier's cryptosystem, as described in Paillier: "Public key cryptosystems based on composite degree residuosity classes" (Advances in cryptology, EUROCRYPT 1999, pp. 223-238) is one of the most important additive homomorphic encryption systems. Suppose we have N encrypted data under same key pk, which can be presented as [m.sub.i].sub.pk (i=1, 2, . . . , N). The additive homomorphic encryption satisfies the following equation:
D.sub.sk(.PI..sub.i=1.sup.N[m.sub.i].sub.pk)=.SIGMA..sub.i=1.sup.Nm.sub.- i
[0061] where D.sub.sk( ) is the corresponding homomorphic decryption algorithm with secret key sk. Reference is made to Paillier (see above), EIGamal "A public key cryptosystem and a signature scheme based on discrete algorithms" (Advances in cryptology, Springer, 1985, pp 10-18.) and Bresson et al. "A simple public-key cryptosystem with a double trapdoor decryption mechanism and its applications", (Advances in cryptology, ASIACRYPT 2003, Springer, pp. 37-54).
[0062] For easy presentation, we use the acronym EDD to present the mechanism proposed by E. Bresson, D. Catalano and D. Pointcheval: "A simple public-key cryptosystem with a double trapdoor decryption mechanism and its applications" (Advances in Cryptology, ASIACRYPT, 2003, pp. 37-54, Springer, 2003), which is a variant of Cramper-Shoup "Universal hash proofs and a paradigm for adaptive chosen ciphertext secure public-key encryption" (Advances in cryptology, EUROCRYPT 2002, pp. 45-64).
[0063] Let g and h be two elements of maximal order in . Note that, if h is computed as g.sup.x, where x.di-elect cons..sub.R [1, .lamda.(n.sup.2)], then x is coprime with ord() with high probability, and thus h is of maximal order.
[0064] Key Generation: The public parameters are n, g and h=g.sup.x by randomly choosing a value x.di-elect cons.[1, ord()] (where g is generated by first choosing a random element .alpha..di-elect cons..sub.n.sub.2*, and then setting g=.alpha..sup.2 mod n.sup.2).
[0065] Encrypt: Given a message m.di-elect cons..sub.n, random number r is chosen uniformly in .sub.n.sub.2*. The ciphertext is computed as (T, T')={h.sup.r(1+m*n) (mod n.sup.2), g.sup.r(mod n.sup.2)}.
[0066] Decryption: Knowing x, one can obtain m as follows:
m=L(T/(T').sup.x mod n.sup.2), where L(u)=(u-1)/n.
[0067] Note: if the factorization of n=p*q (.lamda.(n)=(p-1)(q-1)/2) is given, one can directly decrypt the ciphertext by computing m=L((T).sup..lamda.(n))[.lamda.(n))].sup.-1 mod n.
[0068] In this section, we briefly introduce the original attempt of proxy re-encryption, PRE, in Ateniese et al. "Improved proxy re-encryption schemes with applications to secure distributed storage" (ACM Transactions on Information and System Security (TISSEC), vol. 9, no. 1, pp. 1-30, 2006), which lays the foundation of our proposed schemes. Generally, the ciphertext that can be only decrypted by Entity A can be converted into the one that can be decrypted by Entity B through the re-encryption of a proxy.
[0069] The PRE is based on Cramper-Shoup and EDD. It has the same operation of key generation as EDD. Thus, we skip it and focus on re-encryption operation.
[0070] Data Encryption: to encrypt a message m.di-elect cons..sub.n, select a random r.di-elect cons.[1, n/4] and compute: (T, T')={h.sup.r(1+m*n)(mod n.sup.2), g.sup.r}.
[0071] Decryption with x: m=L(T/(T').sup.x mod n.sup.2), where L(u)=(u-1)/n, for all u.di-elect cons.{u<n.sup.2|u=1 mod n}.
[0072] Proxy Re-encryption: the secret key x is divided into two shares x.sub.1 and x.sub.2, such that x=x.sub.1+x.sub.2. The share x.sub.1 is given to the proxy, while x.sub.2 is kept by Entity B.
[0073] Re-encryption (done by the proxy): ({tilde over (T)}, )=(T/(T').sup.x.sup.1, T')=(h.sup.r(1+m*n)(mod n.sup.2)/(g.sup.r).sup.x.sup.1, g.sup.r);
[0074] Decryption (done by Entity B): m=L({tilde over (T)}/().sup.x.sup.2 mod n.sup.2).
[0075] This is a proxy-invisible scheme, which means that it is unable to distinguish the original ciphertext from the re-encrypted ciphertext. In our proposed scheme, two servers play as an invisible proxy to transfer the encrypted data to the ciphertext under the key of an authorized requester. Moreover, the non-colluding servers help ensure the correct transformation of ciphertext.
[0076] The following table summarizes notation used herein:
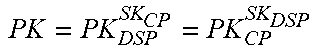
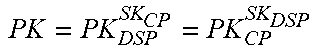
TABLE-US-00001 Symbols Description g The system generator that is public; n The system parameter; (SK.sub.DSP, PK.sub.DSP) The key pair of DSP; (SK.sub.CP, PK.sub.CP) The key pair of CP PK = PK DSP SK CP = PK CP SK DSP ##EQU00001## The public parameter based on keys of DSP and CP; (sk.sub.j, pk.sub.j) The key pair of DR j; (sk.sub.i, pk.sub.i) The key pair of DP i; m.sub.i The raw data provided by DP i; [m] The ciphertext of m under PK; [m].sup.+ The re-encryption result of m by DSP; [m].sub.pk.sub.i The ciphertext of m under pk.sub.i; r The random number; r.sub.* The random number chosen for encryption; CID The public computation identifier, which is related to the operation type; N The number of data providers; (*) The bit length of input data; H( ) The hash function; The set of data providers related to CID; | | The number of providers in .
[0077] In order to support privacy-preserving data processing, we adapt the EDD to encrypt personal data with the Diffie-Hellman key of two servers, i.e., PK=PK.sub.DSP.sup.SK.sup.CP=PK.sub.CP.sup.SK.sup.DSP. We design the primitive, HRES, which can realize proxy-invisible re-encryption and secure data processing. The HRES consists of the following algorithms:
[0078] KeyGen: Let k be a security parameter and p, q be two large primes, where (p)=(q)=k(( ) returns the bit length of input data). Due to the property of safe primes, there exist two primes p' and q' which satisfy that p=2p'+1, q=2q'+1. We compute n=p*q and choose a generator g with order .lamda.=2p'q', which can be chosen by selecting a random number z.di-elect cons..sub.n.sub.2* and computing g=-z.sup.2n. The value .lamda. can be used to decrypt the encrypted data, but we choose to conceal it and protect it from all involved parties. In the HRES, we only use key pair (sk, g.sup.sk) for data encryption and decryption. The DSP 120 and the CP 130 generate their key pairs: (SK.sub.DSP=a, PK.sub.DSP=g.sup.a) and (SK.sub.CP=b, PK.sub.CP=g.sup.b), and then negotiate their Diffie-Hellman key PK=PK.sub.DSP.sup.SK.sup.CP=PK.sub.CP.sup.SK.sup.DSP=g.sup.a*b. To support encrypted data processing, PK is public to all involved parties. Cloud user i generates its key pair (sk.sub.i, pk.sub.i)=(k.sub.i, g.sup.k.sup.i). The public system parameters include {g, n, PK}.
[0079] First, the Original Encryption scheme is directly obtained from EDD.
[0080] Encryption (Enc): For a personal purpose, a user can outsource private data with its own key pair, which can ensure the unavailability of data to other entities. It can also be used to send data to a specified target. User encrypts their data with the public key of user i and a random r.OR right.[1, n/4] as follows:
[m].sub.pk.sub.i=((1+m*n)pk.sub.i.sup.r, g.sup.r)(mod n.sup.2).
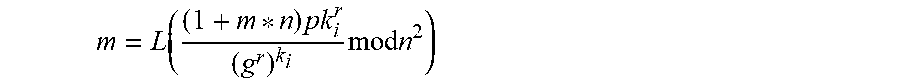
[0081] Decryption (Dec): Upon receiving the encrypted data under its own public key, user i can directly decrypt it to obtain the original data:
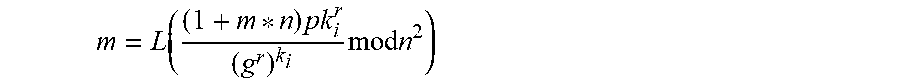
m = L ( ( 1 + m * n ) pk i r ( g r ) k i mod n 2 ) ##EQU00002##
[0082] Second, the following encryption is a Two-Level Decryption scheme that can support outsourced data processing flexibly.
[0083] Encryption with Two Keys (EncTK): To support ciphertext process flexibly, we propose to encrypt original data under the keys of two servers. Given a message m.sub.i.di-elect cons..sub.n provided by user i, we first select a random number r.di-elect cons.[1, n/4] and then encrypt it with PK. The ciphertext is generated as [m.sub.i]={T.sub.i, T.sub.i'}, where T.sub.i'=g.sup.r mod n.sup.2, T.sub.i=(1+m.sub.i*n)*PK.sup.r mod n.sup.2.
[0084] Note: [m.sub.i] denotes the ciphertext of m.sub.i encrypted with PK, which can only be decrypted under the cooperation of the DSP and the CP. [m.sub.i].sub.pk.sub.i denotes the data that is encrypted with pk.sub.i, which can be decrypted by user i.
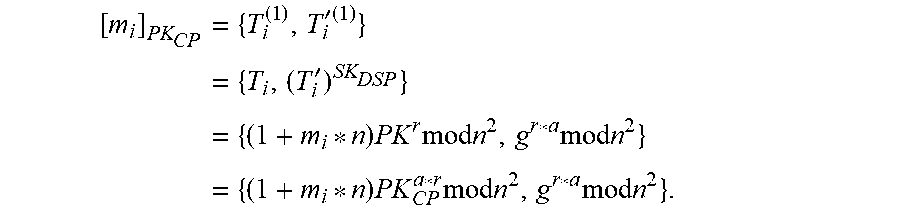
[0085] Partial Decryption with SK.sub.DSP (PDec1): Once [m.sub.i] is received by the DSP, algorithm PDec1( ) will be run to transfer it into another ciphertext which can be decrypted by the CP as follows:
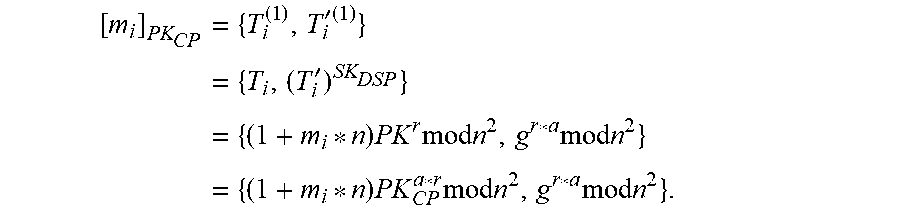
[ m i ] PK CP = { T i ( 1 ) , T i ' ( 1 ) } = { T i , ( T i ' ) SK DSP } = { ( 1 + m i * n ) PK r mod n 2 , g r * a mod n 2 } = { ( 1 + m i * n ) PK CP a * r mod n 2 , g r * a mod n 2 } . ##EQU00003##
[0086] Partial Decryption with SK.sub.CP (PDec2): Once the message [m.sub.i].sub.PK.sub.CP is received, the CP can directly decrypt it with its own secret key as follows:
[0087] 1) Select the public computation identifier CID, which specifies the operation type.
[0088] 2) h.sub.1=H ((pk.sub.j).sup.SK.sup.DSP.parallel.CID);
[0089] 3) [m.sub.i].sup.+={{tilde over (T)}, }={T.sub.i, (T.sub.i').sup.SK.sup.DSP*g.sup.h.sup.1}.
[0090] To achieve the proxy-invisible re-encryption, we further propose a Somewhat Re-Encryption scheme, wherein differently from the scheme described above, it aims to transfer the encrypted data to the ciphertext under the public key of an authorized requester. Here, we assume DR j with key pair (sk.sub.j, pk.sub.j)=(t, g.sup.t) requires to obtain m.sub.i through outsourced data [m.sub.i]. In our scheme, the transformation needs the cooperation and recognition of both the DSP and the CP. They together play the role of a proxy.
[0091] First Phase of Re-Encryption (FPRE): In order to prevent the decryption PDec2( ) by the CP, the DSP initiates algorithm FPRE( ) as follows:
[0092] 1) Select the public computation identifier CID, which specifies the operation type.
[0093] 2) h.sub.1=H ((pk.sub.j).sup.SK.sup.DSP.parallel.CID);
[0094] 3) [m.sub.i].sup.+={{tilde over (T)}, }={T.sub.i, (T.sub.i').sup.SK.sup.DSP*g.sup.h.sup.1}. Notes: [m.sub.i].sup.+ denotes the encrypted data that can only be decrypted by an authorized data requester with the support of the CP 130.
[0095] Second Phase of Re-Encryption (SPRE): Upon receiving the data packet [m.sub.i].sup.+, the CP launches re-encryption algorithm SPRE( ) as below:
[0096] 1) h.sub.2=H ((pk.sub.j).sup.SK.sup.CP.parallel.CID;
[0097] 2) [m.sub.i].sub.pk.sub.j={T, T'}={{circumflex over (T)}, ().sup.SK.sup.CP*g.sup.h.sup.2}. Note: If data outsourced by a user are extremely private and not allowed to be processed or analyzed, the cloud user can choose to use Enc( ) to encrypt its personal data with its own public key and then store them at the DSP. If the data can be analyzed in a privacy-preserving way by authorized parties, the user need to store encrypted data by calling the encryption algorithm EncTK( ).
[0098] FIG. 3 illustrates an example apparatus capable of supporting at least some embodiments of the present invention. Illustrated is device 300, which may comprise, for example, a DP 110, DSP 120, CP 130 or DR 140 of FIG. 1 or FIG. 2. Comprised in device 300 is processor 310, which may comprise, for example, a single- or multi-core processor wherein a single-core processor comprises one processing core and a multi-core processor comprises more than one processing core. Processor 310 may comprise more than one processor. A processing core may comprise, for example, a Cortex-A8 processing core manufactured by ARM Holdings or a Steamroller processing core produced by Advanced Micro Devices Corporation. Processor 310 may comprise at least one Qualcomm Snapdragon and/or Intel Atom processor. Processor 310 may comprise at least one application-specific integrated circuit, ASIC. Processor 310 may comprise at least one field-programmable gate array, FPGA. Processor 310 may be means for performing method steps in device 300. Processor 310 may be configured, at least in part by computer instructions, to perform actions.
[0099] Device 300 may comprise memory 320. Memory 320 may comprise random-access memory and/or permanent memory. Memory 320 may comprise at least one RAM chip. Memory 320 may comprise solid-state, magnetic, optical and/or holographic memory, for example. Memory 320 may be at least in part accessible to processor 310. Memory 320 may be at least in part comprised in processor 310. Memory 320 may be means for storing information. Memory 320 may comprise computer instructions that processor 310 is configured to execute. When computer instructions configured to cause processor 310 to perform certain actions are stored in memory 320, and device 300 overall is configured to run under the direction of processor 310 using computer instructions from memory 320, processor 310 and/or its at least one processing core may be considered to be configured to perform said certain actions. Memory 320 may be at least in part comprised in processor 310. Memory 320 may be at least in part external to device 300 but accessible to device 300.
[0100] Device 300 may comprise a transmitter 330. Device 300 may comprise a receiver 340. Transmitter 330 and receiver 340 may be configured to transmit and receive, respectively, information in accordance with at least one cellular or non-cellular standard. Transmitter 330 may comprise more than one transmitter. Receiver 340 may comprise more than one receiver. Transmitter 330 and/or receiver 340 may be configured to operate in accordance with global system for mobile communication, GSM, wideband code division multiple access, WCDMA, long term evolution, LTE, IS-95, wireless local area network, WLAN, Ethernet and/or worldwide interoperability for microwave access, WiMAX, standards, for example.
[0101] Device 300 may comprise a near-field communication, NFC, transceiver 350. NFC transceiver 350 may support at least one NFC technology, such as NFC, Bluetooth, Wibree or similar technologies.
[0102] Device 300 may comprise user interface, UI, 360. UI 360 may comprise at least one of a display, a keyboard, a touchscreen, a vibrator arranged to signal to a user by causing device 300 to vibrate, a speaker and a microphone. A user may be able to operate device 300 via UI 360, for example to manage ciphertext-form data.
[0103] Device 300 may comprise or be arranged to accept a user identity module 370. User identity module 370 may comprise, for example, a subscriber identity module, SIM, card installable in device 300. A user identity module 370 may comprise information identifying a subscription of a user of device 300. A user identity module 370 may comprise cryptographic information usable to verify the identity of a user of device 300 and/or to facilitate encryption of communicated information and billing of the user of device 300 for communication effected via device 300.
[0104] Processor 310 may be furnished with a transmitter arranged to output information from processor 310, via electrical leads internal to device 300, to other devices comprised in device 300. Such a transmitter may comprise a serial bus transmitter arranged to, for example, output information via at least one electrical lead to memory 320 for storage therein. Alternatively to a serial bus, the transmitter may comprise a parallel bus transmitter. Likewise processor 310 may comprise a receiver arranged to receive information in processor 310, via electrical leads internal to device 300, from other devices comprised in device 300. Such a receiver may comprise a serial bus receiver arranged to, for example, receive information via at least one electrical lead from receiver 340 for processing in processor 310. Alternatively to a serial bus, the receiver may comprise a parallel bus receiver.
[0105] Device 300 may comprise further devices not illustrated in FIG. 3. For example, where device 300 comprises a smartphone, it may comprise at least one digital camera. Some devices 300 may comprise a back-facing camera and a front-facing camera, wherein the back-facing camera may be intended for digital photography and the front-facing camera for video telephony. Device 300 may comprise a fingerprint sensor arranged to authenticate, at least in part, a user of device 300. In some embodiments, device 300 lacks at least one device described above. For example, some devices 300 may lack a NFC transceiver 350 and/or user identity module 370.
[0106] Processor 310, memory 320, transmitter 330, receiver 340, NFC transceiver 350, UI 360 and/or user identity module 370 may be interconnected by electrical leads internal to device 300 in a multitude of different ways. For example, each of the aforementioned devices may be separately connected to a master bus internal to device 300, to allow for the devices to exchange information. However, as the skilled person will appreciate, this is only one example and depending on the embodiment various ways of interconnecting at least two of the aforementioned devices may be selected without departing from the scope of the present invention.
[0107] FIG. 4 illustrates signalling in accordance with at least some embodiments of the present invention. On the vertical axes are disposed, from the left to the right, DP 110, DSP 120, CP 130 and DR 140. Time advances from the top toward the bottom.
[0108] Phase 410, which takes place in all the four entities, comprises a system setup phase. DSP 120 and CP 130 get their own key pairs respectively (SK.sub.DSP, PK.sub.DSP)=(a, g.sup.a) and (SK.sub.CP, PK.sub.CP)=(b, g.sup.b), and then negotiate PK=PK.sub.CP.sup.SK.sup.DSP=PK.sub.DSP.sup.SK.sup.CP=g.sup.a*b. The corresponding secret key of PK is a*b. DP 110, that is, user i, generates its own key pair (sk.sub.i, pk.sub.i)=(k.sub.i, g.sup.k.sup.i) by randomly choosing k.sub.i.di-elect cons.[1, n/4], and then registers at the CP. The public parameters are (n, g, PK, (n)) and the public keys of all involved entities. DR 140 j performs similarly to generate its key pair (sk.sub.j, pk.sub.j)=(k.sub.j, g.sup.k.sup.j)=(t, g.sup.t). If multiple CPs 130 are employed in the system, each CP 130 may negotiate a Diffie-Hellman key with the DSP 120 and publish this key to its customers. For simplifying presentation, we only present the detailed operations in the case that there is only one CP 130 interacting with the DSP 120 as below.
[0109] Phase 420 comprises a data upload from DP 110 to DSP 120. DPs 110 encrypt their data before uploading it to the DSP 120. DP i 110 calls EncTK( ) to encrypt data m.sub.i:
[m.sub.i]=(T.sub.i, T.sub.i')={(1+m.sub.i*n)*PK.sup.r.sup.i mod n.sup.2, g.sup.r.sup.i mod n.sup.2}.
[0110] For correctly supporting various computations, the length of the data may be restricted (m.sub.i)<(n)/4. Then DP i 110 uploads and stores [m.sub.i] at the DSP 120.
[0111] Phase 430 comprises DR 140 requesting the data uploaded in phase 420, by signalling to CP 130. The request of phase 430 may comprise a computation identifier, CID. The request may comprise a request to obtain the data in processed and encrypted form. The request may comprise a public key of DR 140.
[0112] Phase 440 may comprise CP 130 assessing, whether DR 140 is authorized to access the data. In case no, processing may stop here. In case DR 140 is authorized, CP 130 may forward the request to DSP 120, the forwarding being illustrated in FIG. 4 as phase 450. The forwarded request may likewise comprise the CID, and/or a public key of DR 140.
[0113] Phase 460 comprises DSP 120 pre-processing the requested data, upon receiving the request from DR 140 authorized by CP 130, according to the computation identifier CID by calling the algorithm FPRE( ), which is described above, to prepare data packet DPacket for CP 130. Phase 470 comprises DSP 120 providing the processed data, DPacket, to CP 130. Phase 460 may further comprise DSP 120 performing a mathematical manipulation of the data in encrypted form, in dependence of the CID.
[0114] Phase 480 comprises CP 130 further processing DPacket, received from DSP 120, by calling the algorithm SPRE( ) to obtain DPacket'. Algorithm SPRE( ) is described above. Alternatively, phase 480 may comprise CP 130 transferring DPacket under DR 140's public key using a different method, such as by first using PDec2( ) and then Enc( ).
[0115] These algorithms are described above. Finally, in phase 490, DPacket' is provided to DR 140 as a response to the request of phase 430. Once DR 140 has DPacket', it may decrypt it, for example by calling algorithm DPRE( ) to obtain the data. DPRE( ) is described above.
[0116] In the following, processing of encrypted data will be described with respect to the computations listed above, namely The HRES primitive may support seven basic operations, indicated by different CID: 1) addition; 2) subtraction; 3) multiplication; 4) sign acquisition; 5) comparison; 6) equivalent Test; and 7) variance.
[0117] System setup and data collection have no difference from that in FIG. 4. Hence, we ignore the process of data upload and mainly focus on phases 460, 480 and 490 in the following presentation. DP i 110 offers personal data as [m.sub.i] and DR j 140 holds the key pair (sk.sub.j, pk.sub.j)=(k.sub.j, g.sup.k.sup.j)=(t, g.sup.t).
[0118] Addition: this scheme aims to obtain the sum of all raw data (m=m.sub.i) where represents the set of data providers related to CID in the request.
[0119] Phase 460 (Data Preparation at DSP): Due to the additive homomorphism, the DSP can directly multiply encrypted data one by one as following:
[m]=(T, T')=(T.sub.i, T.sub.i').
[0120] To transfer it into the ciphertext under DR j's public key, the DSP further calls the algorithm FPRE( ) to process the data with its own secret key and DR j's public key pk.sub.j:
[m].sup.+=({tilde over (T)}, )={T, (T').sup.a*g.sup.H((pk.sup.j.sup.).sup.a.sup..parallel.CID)}.
[0121] The DSP finally prepares a data packet ([m].sup.+, CID) and sends it to the CP.
[0122] Phase 480 (Data Process at CP): The CP calls the second re-encryption algorithm SPRE( ) to finally transfer the encrypted data to the ciphertext under DR j's public key:
[m].sub.pk.sub.j=(T, T')={{circumflex over (T)}, ().sup.b*g.sup.H((pk.sup.j.sup.).sup.b.sup..parallel.CID)}.
[0123] Then the CP sends ([m].sub.pk.sub.j, CID) to the DR.
[0124] Phase 490 (Data Access at DR): The DR can obtain the aggregated result by calling the algorithm DPRE( ):
m=L(T*PK.sub.CP.sup.H((PK.sup.DSP.sup.).sup.sk.sup.j.sup..parallel.CID)*- g.sup.H((PK.sup.CP.sup.).sup.sk.sup.j.sup..parallel.CID)/T' mod n.sup.2).
[0125] Subtraction: this function aims to obtain the subtraction of some data (for example, m=m.sub.1-m.sub.2) with encrypted data [m.sub.1] and [m.sub.2]. The HRES has an additional property as follows:
[m.sub.i].sup.n-1={{(1+m.sub.i*n)PK.sup.r.sup.i}.sup.(n-1), (g.sup.r.sup.i).sup.(n-1)}={(1+m.sub.i(n-1)*n)PK.sup.r.sup.i.sup.(n-1), g.sup.r.sup.i.sup.(n-1)}={(1-m.sub.i*n)PK.sup.r.sup.i.sup.(n-1), g.sup.r.sup.i.sup.(n-1)}mod n.sup.2=[-m.sub.i]
[0126] Phase 460 (Data Preparation at DSP): The DSP first computes [-m.sub.2]=[m.sub.2].sup.n-1, and then multiplies it with [m.sub.1] to obtain [m]=[m.sub.1-m.sub.2].
[0127] Then the subsequent process is the same as that in Addition. For length and simplicity reasons, we skip its details.
[0128] Multiplication: This function aims to obtain the product of all raw data (m=m.sub.i). For ease of presentation, we describe the details with two pieces of data ([m.sub.1], [m.sub.2]). The DR wants to get the multiplication result m=m.sub.1*m.sub.2.
[0129] Note that the available number of the data in multiplication influences the length of raw data. If we need to get the product of f pieces of data, it must be guaranteed that the length of each raw data (m.sub.i)<(n)/(2f).
[0130] Phase 460 (Data Preparation at DSP): First, the DSP chooses two random numbers c.sub.1, c.sub.2 (the number of random numbers is equal to that of provided data) and sets another one c.sub.3=(c.sub.1*c.sub.2).sup.-1 mod n.
[0131] To conceal each raw data from the CP, the DSP does one exponentiation and one decryption with its own secret key by calling PDec1( ). Then the DSP encrypts c.sub.3 with Enc( ) using the public key pk.sub.j of the requesting DR:
[c.sub.1*m.sub.1]={T.sub.1, (T.sub.1').sup.c.sup.1}
[c.sub.1*m.sub.1].sub.PK.sub.CP=(T.sub.1.sup.(1), T.sub.1'.sup.(1))={T.sub.1.sup.c.sup.1, (T.sub.1').sup.c.sup.1.sup.*a}={(1+c.sub.1*m.sub.1*n)*PK.sup.r.sup.1.sup.- *c.sup.1, g.sup.r.sup.1.sup.*a*c.sup.1}
[c.sub.2*m.sub.2]={T.sub.2, (T.sub.2').sup.c.sup.2}
[c.sub.2*m.sub.2].sub.PK.sub.CP=(T.sub.2.sup.(1), T.sub.2'.sup.(1))={T.sub.2.sup.c.sup.2, (T.sub.2').sup.c.sup.2.sup.*a}={(1+c.sub.2*m.sub.2*n)*PK.sup.r.sup.2.sup.- *c.sup.2, g.sup.r.sup.2.sup.*a*c.sup.2}
[c.sub.3].sub.pk.sub.j=(T.sub.j, T.sub.j')={(1+c.sub.3*n)*pk.sub.j.sup.r.sup.3, g.sup.r.sup.3}
[0132] The data packet sent to the CP 130 is {[c.sub.1*m.sub.1].sub.PK.sub.CP, [c.sub.2*m.sub.2].sub.PK.sub.CP, [c.sub.3].sub.pk.sub.j}.
[0133] Phase 480 (Data Process at CP): Upon receiving the data packet from the CSP, the CP uses the algorithm PDec2( ) to decrypt the data:
c.sub.1*m.sub.1=T.sub.1.sup.(1)/(T.sub.1'.sup.(1)).sup.b,
c.sub.2*m.sub.2=T.sub.2.sup.(1)/(T.sub.2'.sup.(1)).sup.b,
[0134] It further multiplies the two values and then calls Enc( ) to encrypt it as (T, T')=[c.sub.1*c.sub.2*m.sub.1*m.sub.2].sub.pk.sub.j. Finally, the CP 130 forwards (T, T') and [c.sub.3].sub.pk.sub.j to the DR 140.
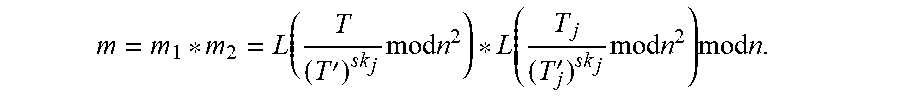
[0135] Phase 490 (Data Access at DR): the DR 140 can obtain the product by calling Dec( ) to decrypt the two ciphertexts with its secret key:
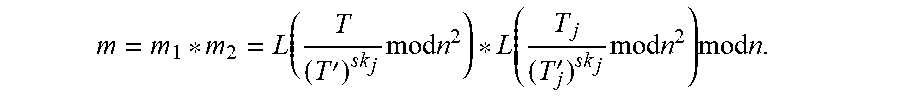
m = m 1 * m 2 = L ( T ( T ' ) sk j mod n 2 ) * L ( T j ( T j ' ) sk j mod n 2 ) mod n . ##EQU00004##
[0136] Sign Acquisition: As (m)<(n)/4, we assume that BIG is the largest raw data of m. Then the raw data is in the scope [-BIG, BIG]. DR j wants to know the sign of raw data m.sub.1 from [m.sub.1].
[0137] Phase 460 (Data Preparation at DSP): The DSP chooses a random number c.sub.1 where (c.sub.1)<(n)/4. It first computes
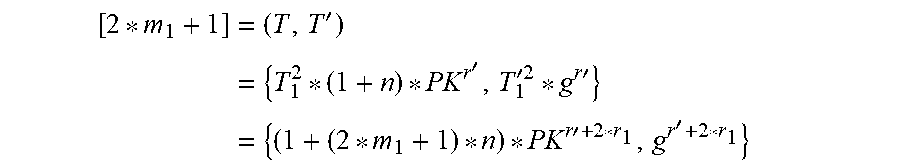
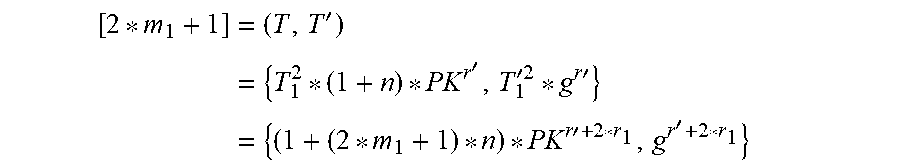
[ 2 * m 1 + 1 ] = ( T , T ' ) = { T 1 2 * ( 1 + n ) * PK r ' , T 1 '2 * g r ' } = { ( 1 + ( 2 * m 1 + 1 ) * n ) * PK r ' + 2 * r 1 , g r ' + 2 * r 1 } ##EQU00005##
[0138] Then it flips a coins s. If s=0; it computes as follows: (T.sub.1.sup.(1), T.sub.1'.sup.(1))={T.sup.n-c.sup.1, (T').sup.a*(n-c.sup.1.sup.)}=[-c.sub.1*(2*m.sub.1+1)]. Otherwise, it calls PDec1( ) and computes: (T.sub.1.sup.(1), T.sub.1'.sup.(1))={T.sup.c.sup.1, T'.sup.a*c.sup.1}=[c.sub.1*(2*m.sub.1+1)].
[0139] The DSP also encrypts s with pk.sub.j through Enc( ): [s].sub.pk.sub.j=(T.sub.s, T.sub.s')={(1+s*n)*pk.sub.j.sup.r.sup.s, g.sup.r.sup.s}. The data packet sent to the CP is {(T.sub.1.sup.(1), T.sub.1'.sup.(1)), [s].sub.pk.sub.j}.
[0140] Phase 480 (Data Process at CP): Upon receiving the data packet from the DSP 120, the CP 130 decrypts (T.sub.1.sup.(1), T.sub.1'.sup.(1)) with PDec2( ) to obtain raw data m'=(-1).sup.s+1*c.sub.1*(2*m.sub.1+1) mod n.sup.2. The CP compares (m') with (n)/2. If (m')<(n)/2, it calls Enc( ) to encrypt u=1 with pk.sub.j; otherwise, it encrypts u=0 with pk.sub.j;
[u].sub.pk.sub.j=(T.sub.u, T.sub.u')={(1+u*n)*pk.sub.j.sup.r.sup.u, g.sup.r.sup.u}
[0141] It further multiplies the two ciphertexts.
[0142] [s+u].sub.pk.sub.j=(T, T')={T.sub.s*T.sub.u, T.sub.u'*T.sub.s'}. Finally, the CP forwards (T, T') to DR j.
[0143] Phase 490 (Data Access at DR): DR j can call Dec( ) to obtain the final result: u+s=L(T/(T').sup.sk.sup.j mod n.sup.2). Then DR j needs to check it and determine the sign of raw data: if u+s=1, the original data is negative (i.e., m.sub.1<0); otherwise, it is positive or zero (i.e., m.sub.1.gtoreq.0). Note: if (s=1, u=0) or (u=1, s=0), m.sub.1<0; if (s=1, u=1) or (u=0, s=0), m.sub.1.gtoreq.0.
[0144] Comparison: Similar to the schemes above, DR j wants to compare the raw data (m.sub.1, m.sub.2) based on their encrypted data. For ease of presentation, m.sub.1-m.sub.2 is denoted as m.sub.1-2.
[m.sub.1]=(T.sub.1, T.sub.1')={(1+m.sub.1*n)*PK.sup.r.sup.1, g.sup.r.sup.1}
[m.sub.2]=(T.sub.2, T.sub.2')={(1+m.sub.2*n)*PK.sup.r.sup.2, g.sup.r.sup.2}
[0145] Phase 460 (Data Preparation at DSP): DSP first computes to get the subtraction of encrypted data:
(T, T')={T.sub.1*(T.sub.2).sup.n-1, T.sub.1'*(T.sub.2').sup.n-1}=[(m.sub.1-m.sub.2)].
[0146] The following steps are the same to that in Sign Acquisition, which is skipped for the reason of length limitation. Through the cooperation of the DSP 120 and the CP 130, the DR 140 finally gets the sign of m.sub.1-2=m.sub.1-m.sub.2. In the end, the DR can obtain the comparison result. If m.sub.1-2.gtoreq.0, m.sub.1.gtoreq.m.sub.2; otherwise, m.sub.1<m.sub.2.
[0147] Equivalent test: If DR j 140 wants to know if m.sub.1 is equal to m.sub.2 with encrypted data ([m.sub.1], [m.sub.2]). The DSP 120 and the CP 130 directly interact with each other in two parallel computations of Comparison.
[0148] They compare m.sub.1 and m.sub.2 in two forms: 1) m.sub.1-2=m.sub.1-m.sub.2; 2) m.sub.2-1=m.sub.2-m.sub.1. Through the operations in Comparison, DSP can get two computation results [s.sub.1+u.sub.1].sub.pk.sub.j and [s.sub.2+u.sub.2].sub.pk.sub.j respectively.
[0149] To conceal the comparing result of m.sub.1 and m.sub.2, [s.sub.1+u.sub.1].sub.pk.sub.j and [s.sub.2+u.sub.2].sub.pk.sub.j are sent to the DR in a random order. If both testing result are ".gtoreq.", we can know m.sub.1=m.sub.2.
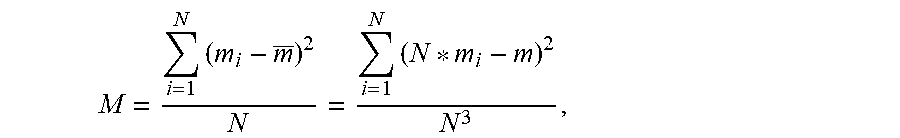
[0150] Variance: In some scenarios, DR j 140 may want to get the variance of some data according to provided encrypted data. In this presentation, we set N be the number of provided data and m=.SIGMA..sub.i=1.sup.N m.sub.i. Variance function can be presented as
M = i = 1 N ( m i - m _ ) 2 N = i = 1 N ( N * m i - m ) 2 N 3 , ##EQU00006##
where m is the average of m.sub.i (i=1, . . . , N). For ease of presentation, we assume there are three pieces of encrypted data (i.e., N=3): [m.sub.1], [m.sub.2] and [m.sub.3].
[0151] Phase 460 (Data Preparation at DSP): First, the DSP 120 obtains [N*m.sub.i-.SIGMA..sub.i=1.sup.N m.sub.i] through following steps:
[0152] [m]=(T ,T')=[m.sub.1]*[m.sub.2]*[m.sub.3],
[0153] [-m]=(T.sup.n-1, (T').sup.n-1);
[0154] [N*m.sub.i]=[m.sub.i].sup.N for i=1,2,3;
[0155] [N*m.sub.i-m]=[m.sub.i].sup.N*[-m] for i=1,2,3;
[0156] Then the DSP 120 partially decrypts the data with its secret key by calling PDec1( ) to obtain: [N*m.sub.i-m].sub.PK.sub.CP for i=1,2,3. The DSP 120 chooses three random numbers c.sub.1, c.sub.2, c.sub.3, and computes to obtain:
[c.sub.i(N*m.sub.i-m)].sub.PK.sub.CP=([N*m.sub.i-m].sub.PK.sub.CP).sup.c- .sup.i for i=1,2,3
[0157] Then the DSP 120 send the three ciphertexts to the CP 130. In addition, DSP 120 needs to store c.sub.1.sup.2, c.sub.2.sup.2, c.sub.3.sup.2.
[0158] Phase 480 (Data Process at CP): Upon receiving the data from the DSP, the CP directly decrypts to obtain raw data and then processes the data for DR j as follows:
[0159] Decrypt to obtain: C.sub.i=c.sub.i(N*m.sub.i-m) for i=1,2,3;
[0160] Encrypt processed data with the public key pk.sub.j of DR j 140:
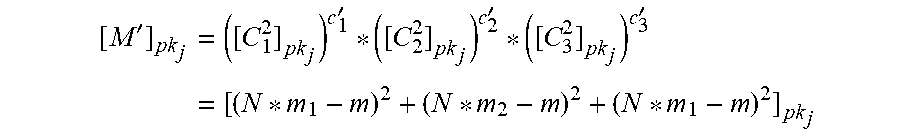
[0161] [C.sub.i.sup.2].sub.pk.sub.j=[c.sub.i.sup.2(N*m.sub.i-m).sup.2].sub- .pk.sub.j for i=1,2,3. Then CP 130 sends them back to DSP 120. Additional Operation at DSP: The DSP first computes the reverse of c.sub.1.sup.2, c.sub.2.sup.2, c.sub.3.sup.2 respectively: c.sub.i'=(c.sub.i.sup.2).sup.-1 mod n.sup.2 for i=1,2,3. Then DSP 120 can prepare the final result for DR j:
[ M ' ] pk j = ( [ C 1 2 ] pk j ) c 1 ' * ( [ C 2 2 ] pk j ) c 2 ' * ( [ C 3 2 ] pk j ) c 3 ' = [ ( N * m 1 - m ) 2 + ( N * m 2 - m ) 2 + ( N * m 1 - m ) 2 ] pk j ##EQU00007##
[0162] Finally, [M'].sub.pk.sub.j can be sent to DR j.
[0163] Phase 490 (Data Access at DR): DR j can obtain M' by calling Dec( ) and then get the variance:
M'=(N*m.sub.1-m).sup.2+(N*m.sub.2-m).sup.2+(N*m.sub.1-m).sup.2;
M=M'/N.sup.3.
[0164] In the following, processing involving multiple CPs 130 will be described. Due to length limitations, we will only present such basic operations as addition, subtraction, multiplication, and comparison across the CPs 130 in this section. We set an example of two encrypted data belonging to two CPs: CP B and CP V. Besides the settings above, we further set the key pair of B and V as (SK.sub.b, PK.sub.b)=(b, g.sup.b mod n.sup.2) and (SK.sub.v, PK.sub.v)=(v, h.sup.v). Hence, we have PK=PK.sub.b.sup.a=PK.sub.a.sup.b and PK'=PK.sub.v.sup.a=PK.sub.a.sup.v. Two messages are encrypted as:
[m.sub.1].sub.PK={T.sub.1=(1+m.sub.1*n)PK.sup.r.sup.1 mod n.sup.2, T.sub.1'=g.sup.r.sup.1 mod n.sup.2}.
[m.sub.2].sub.PK'={T.sub.2=(1+m.sub.1*n)PK'.sup.r.sup.2 mod n.sup.2, T.sub.2'=g.sup.r.sup.2 mod n.sup.2}.
[0165] That is to say, the data provider of m.sub.1 trusts CP B; while the data provider of m.sub.2 trusts CP V. Hence, they encrypt their data with the corresponding Diffie-Hellman key (PK or PK').
[0166] DR j with key pair (sk.sub.j, pk.sub.j)=(k.sub.j, g.sup.k.sup.j mod n.sup.2) wants to obtain a data processing result across CPs. We assume DR j is a customer of CP B. The detailed procedure is introduced as follows.
[0167] Addition across CPs 130: This computation wants to obtain the sum of data over two servers.
[0168] Data Preparation at DSP: DSP selects a random number w and then operates as follows: 1) Encrypt w and -w: [w].sub.PK and [-w].sub.PK'; and 2) Compute [m.sub.1+w].sub.PK and [m.sub.2-w].sub.PK'; then 3) call PDec1( ) to re-encrypt the two data to obtain [m.sub.1+w].sub.PK.sub.B and [m.sub.2-w].sub.PK.sub.V.
[0169] Data Process at CPs: Upon receiving [m.sub.1+w].sub.PK.sub.B CP B first checks its CID and determines if the requester is allowed to access the data; if positive, CP B calls PDec2( ) to obtain the fused raw data m.sub.1+w and then encrypt it with DR j's public key [m.sub.1+w].sub.pk.sub.j. Similar to the operations of CP B, CP V also obtains [m.sub.2-w].sub.pk.sub.j.
[0170] Additional Operation at DSP: DSP 120 multiplies the two ciphertexts to obtain [m.sub.1+m.sub.2].sub.pk.sub.j and then forwards it to DR. Finally DR j can directly get the sum of data (m.sub.1+m.sub.2) by calling Dec( ).
[0171] Subtraction across CPs 130: the operation is similar to addition, but it needs to do one more operation to obtain the negative of subtractor by doing exponentiation with the power of (n-1).
[0172] Multiplication across CPs 130: Different from Multiplication described earlier with reference to a single CP 130, multiple CPs are involved in the computation and leads to a slightly higher computation on the CPs.
[0173] Data Preparation at DSP: The DSP selects two random numbers (c.sub.1, c.sub.2) to conceal the raw data, and set c.sub.3=(c.sub.2*c2).sup.-1 mod n. Then the DSP does the same operations about Multiplication as those described above and obtains:
[c.sub.1*m.sub.1].sub.PK.sub.B=(, )={T.sub.1.sup.c.sup.1, (T.sub.1').sup.a*c.sup.1}={(1+c.sub.1*m.sub.1*n)*PK.sup.r.sup.1.sup.*c.su- p.1, g.sup.r.sup.1.sup.*a*c.sup.1}
[c.sub.2m.sub.2].sub.PK.sub.V=(, )={T.sub.2.sup.c.sup.2, (T.sub.2').sup.a*c.sup.2}={(1+c.sub.2*m.sub.2*n)*PK'.sup.(r.sup.2.sup.*c.- sup.2.sup.), g.sup.r.sup.2.sup.*a*c.sup.2}
[c.sub.3].sub.pk.sub.j=(T.sub.j, T.sub.j')={(1+c.sub.3*n)*pk.sub.j.sup.r.sup.3, g.sup.r.sup.3}
[0174] The data packet sent to CP B is {[c.sub.1*m.sub.1].sub.PK.sub.B, [c.sub.3].sub.pk.sub.j}; while the data [c.sub.2*m.sub.2].sub.PK.sub.V is sent to CP V.
[0175] Data Process at CPs: Upon receiving the data package, the CP first checks the legality and its access policy, and then calls PDec2( ) if it is positive. Concretely, the CP V obtains the value of c.sub.2*m.sub.2, encrypts it with PK.sub.B and then sends [c.sub.2*m.sub.2].sub.PK.sub.B to the CP B. The CP B obtains the two plaintext and multiplies them to get c.sub.1*c.sub.2*m.sub.1*m.sub.2.
[0176] Finally, the CP B encrypts c.sub.1*c.sub.2*m.sub.1*m.sub.2 with the DR j's public key and sends it together with [c.sub.3].sub.pk.sub.j to DR j.
[0177] Data Access at DR: Upon obtaining the data form the CP B, the DR can directly calls Dec( ) to get the data of c.sub.1*c.sub.2*m.sub.1*m.sub.2 and c.sub.3. Finally, it can get:
m=m.sub.1*m.sub.2=c.sub.1*c.sub.2*m.sub.1*m.sub.2*c.sub.3 mod n.
[0178] Comparison across CPs 130: Different from the Comparison over one CP, the initial operation is executed by the CPs 130 rather than the DSP 120.
[0179] First, the DSP directly sends the data [m.sub.1].sub.PK and [m.sub.2].sub.PK, to the CP B and the CP V respectively.
[0180] Data Preparation at CPs: The CP V calls PDec1( ) to obtain [m.sub.2].sub.PK.sub.a and then sends it to the CP B through a secure way. The CP B first decrypts to obtain [m.sub.1].sub.PK.sub.a and computes as follows:
[m.sub.1-2].sub.PK.sub.a=[m.sub.1].sub.PK.sub.a*([m.sub.2].sub.PK.sub.a)- .sup.n-1;
{T, T'}=[2*m.sub.1-2+1].sub.PK.sub.a={[m.sub.1-2].sub.PK.sub.a}.sup.2*[1- ].sub.PK.sub.a;
[0181] Then it flips a coins. If s=0; it computes as follows:
(, )={T.sup.n-c.sup.1, (T').sup.a*(n-c.sup.1.sup.)}
[0182] Otherwise, it computes (, )={T.sup.c.sup.1, T'.sup.a*c.sup.1}
[0183] The CP B also encrypts s with the public key of DR: [s].sub.pk.sub.j=(T.sub.s, T.sub.s'), and then sends (, ) and [s].sub.pk.sub.j to the DSP.
[0184] Data Process at DSP: The DSP decrypts (, ) to obtain raw data m'=(-1).sup.s+1*c.sub.1*[2*(m.sub.1-m.sub.2)+1] mod n.sup.2. The DSP compares its length with (n)/2. If (m')<(n)/2, it encrypts u=1 with pk.sub.j; otherwise, it encrypts u=0 with pk.sub.j;
[u].sub.pk.sub.j=(T.sub.u, T.sub.u')={(1+u*n)*pk.sub.j.sup.r.sup.u, g.sup.r.sup.u}
[0185] It further multiplies the two ciphertexts.
[s+u].sub.pk.sub.j=(T, T')={T.sub.s*T.sub.u, T.sub.s'*T.sub.u'}
[0186] Data Access at DR: DR j can call Dec( ) to obtain the final result: u+s=T/T').sup.k.sup.j. Then DR j determines the sign of m.sub.1-2. If u+s=1, the original data is negative (i.e., m.sub.1<m.sub.2); otherwise, it is positive or zero (i.e., m.sub.1.gtoreq.m.sub.2). Comparing with the schemes described herein above, we can observe that the cross-CP computation does not introduce too much overhead. For example, in Addition, the DSP needs to do some encryptions on random numbers, but it calls PDec1( ) rather than SPRE( ), which is more efficient. The CP also only needs to do one more PDec2( ) and one more Enc( ). The computation cost of DR is low due to the high efficiency of Dec( ).
[0187] FIG. 5 is a flow graph of a method in accordance with at least some embodiments of the present invention. The phases of the illustrated method may be performed in DSP 120, or in a control device configured to control the functioning thereof, when implanted therein.
[0188] Phase 510 comprises receiving, from a data provider, a first ciphertext. Phase 520 comprises performing a mathematical manipulation of the first ciphertext, the mathematical manipulation modifying plaintext of the first ciphertext without decrypting the first ciphertext, the mathematical manipulation being identified by a computation identifier. Phase 530 comprises obtaining a second ciphertext from the first ciphertext by performing a cryptographic re-encryption operation. Finally, phase 540 comprises providing the second ciphertext to a first computation party
[0189] FIG. 6 is a flow graph of a method in accordance with at least some embodiments of the present invention. The phases of the illustrated method may be performed in CP 130, or in a control device configured to control the functioning thereof, when implanted therein.
[0190] Phase 610 comprises determining, based on a message from a data requester, a computation identifier. Phase 620 comprises transmitting a request to a data service provider, the request comprising the computation identifier. Phase 630 comprises receiving, from the data service provider, a first ciphertext. Phase 640 comprises obtaining a second ciphertext from the first ciphertext by performing a cryptographic re-encryption operation. Finally, phase 650 comprises providing the second ciphertext to the data requester as a response to the message.
[0191] It is to be understood that the embodiments of the invention disclosed are not limited to the particular structures, process steps, or materials disclosed herein, but are extended to equivalents thereof as would be recognized by those ordinarily skilled in the relevant arts. It should also be understood that terminology employed herein is used for the purpose of describing particular embodiments only and is not intended to be limiting.
[0192] Reference throughout this specification to one embodiment or an embodiment means that a particular feature, structure, or characteristic described in connection with the embodiment is included in at least one embodiment of the present invention. Thus, appearances of the phrases "in one embodiment" or "in an embodiment" in various places throughout this specification are not necessarily all referring to the same embodiment. Where reference is made to a numerical value using a term such as, for example, about or substantially, the exact numerical value is also disclosed.
[0193] As used herein, a plurality of items, structural elements, compositional elements, and/or materials may be presented in a common list for convenience. However, these lists should be construed as though each member of the list is individually identified as a separate and unique member. Thus, no individual member of such list should be construed as a de facto equivalent of any other member of the same list solely based on their presentation in a common group without indications to the contrary. In addition, various embodiments and example of the present invention may be referred to herein along with alternatives for the various components thereof. It is understood that such embodiments, examples, and alternatives are not to be construed as de facto equivalents of one another, but are to be considered as separate and autonomous representations of the present invention.
[0194] Furthermore, the described features, structures, or characteristics may be combined in any suitable manner in one or more embodiments. In the preceding description, numerous specific details are provided, such as examples of lengths, widths, shapes, etc., to provide a thorough understanding of embodiments of the invention. One skilled in the relevant art will recognize, however, that the invention can be practiced without one or more of the specific details, or with other methods, components, materials, etc. In other instances, well-known structures, materials, or operations are not shown or described in detail to avoid obscuring aspects of the invention.
[0195] While the forgoing examples are illustrative of the principles of the present invention in one or more particular applications, it will be apparent to those of ordinary skill in the art that numerous modifications in form, usage and details of implementation can be made without the exercise of inventive faculty, and without departing from the principles and concepts of the invention. Accordingly, it is not intended that the invention be limited, except as by the claims set forth below.
[0196] The verbs "to comprise" and "to include" are used in this document as open limitations that neither exclude nor require the existence of also un-recited features. The features recited in depending claims are mutually freely combinable unless otherwise explicitly stated. Furthermore, it is to be understood that the use of "a" or "an", that is, a singular form, throughout this document does not exclude a plurality.
INDUSTRIAL APPLICABILITY
[0197] At least some embodiments of the present invention find industrial application in secure data processing.
ACRONYMS LIST
[0198] ABC Definition [0199] CID computation identifier [0200] CP computation party [0201] EDD Emmanuel, Dario and David mechanism [0202] DP data provider [0203] DSP data service provider [0204] HRES homomorphic re-encryption scheme [0205] PRE proxy re-encryption [0206] DR data requester
TABLE-US-00002 [0206] REFERENCE SIGNS LIST 110 data provider 120 data service provider 130 computation party 140 data requester 300-370 structure of the device of FIG. 3 410-490 phases of the method of FIG. 4 510-540 phases of the method of FIG. 5 610-650 phases of the method of FIG. 6
* * * * *
D00000
D00001
D00002
D00003
D00004
D00005
D00006
P00001

P00002

P00003

P00004

P00005

P00006

P00007

P00008

P00009

P00010

P00011

P00012

P00013

P00014

XML
uspto.report is an independent third-party trademark research tool that is not affiliated, endorsed, or sponsored by the United States Patent and Trademark Office (USPTO) or any other governmental organization. The information provided by uspto.report is based on publicly available data at the time of writing and is intended for informational purposes only.
While we strive to provide accurate and up-to-date information, we do not guarantee the accuracy, completeness, reliability, or suitability of the information displayed on this site. The use of this site is at your own risk. Any reliance you place on such information is therefore strictly at your own risk.
All official trademark data, including owner information, should be verified by visiting the official USPTO website at www.uspto.gov. This site is not intended to replace professional legal advice and should not be used as a substitute for consulting with a legal professional who is knowledgeable about trademark law.