Process And System For Data Transmission
Danzeisen; Marc ; et al.
U.S. patent application number 16/154078 was filed with the patent office on 2019-02-14 for process and system for data transmission. The applicant listed for this patent is Swisscom AG. Invention is credited to Florian Baumgartner, Marc Danzeisen, Jan Linder, Simon Winiker.
| Application Number | 20190050857 16/154078 |
| Document ID | / |
| Family ID | 37603348 |
| Filed Date | 2019-02-14 |
| United States Patent Application | 20190050857 |
| Kind Code | A1 |
| Danzeisen; Marc ; et al. | February 14, 2019 |
PROCESS AND SYSTEM FOR DATA TRANSMISSION
Abstract
Methods and systems are provided for enhanced data transmissions. A central communications device may be configured for encrypting data into encrypted data, using an encryption parameter associated with a particular user; transmitting the encrypted data to a communications terminal associated with the particular user; and receiving in response to the transmitting of the encrypted data, user related data from the communications terminal. The communications device may be further configured for comparing the user related data received from the communications terminal with pre-set user related data associated with the encryption parameter, with the pre-set user related data is stored in the central communications device; and when the user related data received from the communications terminal matches the pre-set user related data, transmitting the encryption parameter to the communications terminal. The central communications device may activate a network interface of the communications terminal, for use in transmitting the encrypted data.
| Inventors: | Danzeisen; Marc; (Ittigen, CH) ; Linder; Jan; (Bern, CH) ; Winiker; Simon; (Bern, CH) ; Baumgartner; Florian; (Bern, CH) | ||||||||||
| Applicant: |
|
||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|
| Family ID: | 37603348 | ||||||||||
| Appl. No.: | 16/154078 | ||||||||||
| Filed: | October 8, 2018 |
Related U.S. Patent Documents
| Application Number | Filing Date | Patent Number | ||
|---|---|---|---|---|
| 13163374 | Jun 17, 2011 | 10096024 | ||
| 16154078 | ||||
| 11774674 | Jul 9, 2007 | 8527420 | ||
| 13163374 | ||||
| Current U.S. Class: | 1/1 |
| Current CPC Class: | H04L 63/08 20130101; H04L 63/0428 20130101; H04L 63/062 20130101; G06F 21/10 20130101; G06Q 20/3829 20130101 |
| International Class: | G06Q 20/38 20060101 G06Q020/38; H04L 29/06 20060101 H04L029/06; G06F 21/10 20060101 G06F021/10 |
Foreign Application Data
| Date | Code | Application Number |
|---|---|---|
| Jul 7, 2006 | EP | 06116828 |
Claims
1-15. (canceled)
16. A method comprising: in a central communications device: encrypting data into encrypted data, using an encryption parameter associated with a particular user; transmitting the encrypted data to a communications terminal associated with the particular user; receiving in response to the transmitting of the encrypted data, user related data from the communications terminal; comparing the user related data received from the communications terminal with pre-set user related data associated with the encryption parameter, wherein the pre-set user related data is stored in the central communications device; and when the user related data received from the communications terminal matches the pre-set user related data, transmitting the encryption parameter to the communications terminal.
17. The method in accordance with claim 16, comprising: selecting the encrypted data based on a user profile associated with the particular user; and transmitting the encrypted data to the communications terminal based on the user profile.
18. The method in accordance with claim 17, comprising storing at least a portion of the user profile in the central communications device.
19. The method in accordance with claim 17, comprising storing at least a portion of the user profile in the communications terminal.
20. The method in accordance with claim 16, comprising: activating by central communications device, a network interface of the communications terminal, when the encrypted data are ready for transmission; and transmitting the encrypted data to the communications terminal over the activated network interface.
21. The method in accordance with claim 16, comprising transmitting the encrypted data to a network device, wherein the network device is configured to store the encrypted data and asynchronously transmit the encrypted data to the communications terminal.
22. The method in accordance with claim 16, comprising debiting a user account with a monetary value upon transfer of at least part of the encryption parameter.
23. The method in accordance with claim 16, wherein the encrypted data comprises a program code that is configured for execution in the communications terminal, and checking validation criteria during the execution of the program code.
24. The method in accordance with claim 16, comprising assigning an identification parameter to the encrypted data.
25. The method in accordance with claim 16, comprising: determining availability of the communications terminal associated with the particular user, for communication with the central communications device; and transmitting the encrypted data to the communications terminal based on determination that the communications terminal is available.
26. A system comprising: an encryption circuit; a communication circuit; and a control circuit; wherein: the encryption circuit encrypts data into encrypted data, using an encryption parameter associated with a particular user; the communication circuit transmits the encrypted data to a communications terminal associated with the particular user; the communication circuit receives in response to the transmitting of the encrypted data, user related data from the communications terminal; the control circuit compares the user related data received from the communications terminal with pre-set user related data associated with the encryption parameter, wherein the pre-set user related data is stored in the system; and when the user related data received from the communications terminal matches the pre-set user related data, the communication circuit transmits the encryption parameter to the communications terminal.
27. The system in accordance with claim 26, wherein: the control circuit selects the encrypted data based on a user profile associated with the particular user; and the communication circuit transmits the encrypted data to the communications terminal based on the user profile.
28. The system in accordance with claim 27, the control circuit stores at least a portion of the user profile.
29. The system in accordance with claim 27, the communication circuit receives at least a portion of the user profile from the communications terminal.
30. The system in accordance with claim 26, wherein: the control circuit activates a network interface of the communications terminal, when the encrypted data are ready for transmission; and the communication circuit transmits the encrypted data to the communications terminal over the activated network interface.
31. The system in accordance with claim 26, wherein the communication circuit transmits the encrypted data to a network device, wherein the network device is configured to store the encrypted data and asynchronously transmit the encrypted data to the communications terminal.
32. The system in accordance with claim 26, wherein the control circuit debits a user account with a monetary value upon transfer of at least part of the encryption parameter.
33. The system in accordance with claim 26, wherein the encryption circuit incorporates into the encrypted data a program code that is configured for execution in the communications terminal, and checking validation criteria during the execution of the program code.
34. The system in accordance with claim 26, wherein the encryption circuit assigns an identification parameter to the encrypted data.
35. The system in accordance with claim 26, wherein: the control circuit determines availability of the communications terminal associated with the particular user, for communication with the central communications device; and the communication circuit transmits the encrypted data to the communications terminal based on determination that the communications terminal is available.
Description
CROSS-REFERENCE TO RELATED APPLICATIONS
[0001] This application is a continuation of and claims the benefit of priority from U.S. Ser. No. 11/774,674, filed Jul. 9, 2007, which claims the benefit of priority of European Patent Application No. 06116828.2, filed Jul. 7, 2006, the entire contents of each of which are incorporated herein by reference.
BACKGROUND OF THE INVENTION
Field Of The Invention
[0002] The present invention relates to a process and a system for data transmission.
DESCRIPTION OF THE RELATED ART
[0003] In the state of the art, a transmission of data between terminals and/or servers takes place in accordance with various processes. Such processes are often particularly adapted in order to transmit messages such as, for example, E-mail messages or current headlines, or in order to transmit multimedia data such as an audio or video file. In order to transmit data from a server to a terminal of a user; for example, it may be necessary first to check the entitlement of the user to access certain data. Such a check on entitlement may be made, for example, by a request for a user name and a password. Since a transmission of data often takes place over public networks, it is advantageous to carry out this transmission of data by means of a secured data connection, such as by means of a VPN connection (VPN: virtual private network). The transmission of data between a server and a terminal can thus be subdivided into a phase for the check on entitlement, or authentication phase, and a phase for the transfer of data. Because of the user interaction, the authentication phase often takes a relatively long time, though only little network bandwidth is required. The data transfer phase may on the other hand last only for a short while, depending on the volume of data, and use all of the available network bandwidth.
[0004] E-mail messages to a user are, for example, stored on an E-mail server. The user retrieves the E-mail messages stored on the E-mail server by means of an E-mail client. In the state of the art, protocols such as POP (POP: Post Office protocol) or IMAP (IMAP: Internet E-mail access protocol) are used for this purpose. By means of the E-mail client and such protocols, a connection is made between the E-mail client and the E-mail server, whereupon the E-mail client checks the E-mail server for available E-mail messages and, if necessary, downloads new E-mail messages to the E-mail client. The E-mail client is, of course, checked by authentication for its entitlement to access the E-mail messages. The authentication often takes much longer than the subsequent checking and downloading of the E-mail messages. The checking of E-mail messages can also be based on a VPN tunnel. In this case, however, a VPN tunnel is set up even if no new messages are available on the E-mail server. This leads to inefficiency, since a VPN tunnel is set up even if no data is ready for transmission.
[0005] In the state of the art, such a two-phase transmission of data suffers from many disadvantages, particularly for users of mobile terminals. It is admittedly the case that powerful WLAN or UWB networks (WLAN: wireless local area network; UWB: ultra wide band) are available to the user at railway stations, for example. But a user at a railway station often has no time to be authenticated for access to data and to download data to the mobile terminal. After the user has taken a seat on the train, however, the user often has enough time to be authenticated for access to data. At this time, however, the train has often already left the site of the station and frequently at this time the user only has much less powerful networks available, such as a GSM or UMTS network (GSM: global system for mobile communications; UMTS: universal mobile telecommunications system). Thus, the user cannot access large quantities of data at this time, such as an E-mail message with a video file as an attachment, since the transmission capacity of such a less powerful network would be inadequate. Thus, in summary, the authentication followed by data transmission used in the state of the art is, for one thing, inconvenient for the user, since the latter must undertake a user interaction. For another, this kind of user interaction prevents optimization of the capacity utilization of a network infrastructure.
[0006] A digital rights management architecture is disclosed in the document EP 1 372 055. A packager prepares data for a user and a licensor provides a license to the user. The packager and the licensor share a secret key and can calculate a content key for the prepared data. The prepared and encrypted data, as well as the content key, are transmitted to the user.
SUMMARY OF THE INVENTION
[0007] The present inventions include a new process and a new system for data transmission which overcome the disadvantages of the prior art.
[0008] According to an embodiment of the present invention, these objectives are achieved in particular by the elements of the independent claims. In addition, further advantageous embodiments emerge from the dependent claims and the description.
[0009] These objectives are achieved by the inventions in particular by the fact that authentication data and an electronic key are generated, whereby the electronic key is stored as assigned to the authentication data, that by means of an authentication module of a central module at least part of the electronic key is transmitted to a communications terminal, that by means of an encryption module and by means of at least part of the electronic key data are encrypted into encrypted data, that the encrypted data are transmitted between the central module and the communications terminal, and that by means of a decryption module of the communications terminal and by means of at least part of the electronic key the encrypted data are decrypted. Such a process has the particular advantage that the transmission of the authentication data or electronic key and the transmission of the encrypted data can take place completely asynchronously. Thus, for example, E-mail messages can be created on the communications terminal and be encrypted with the electronic key. At any time, for example as soon as the communications terminal is situated within the range of a wireless communications network, the encrypted data can be securely transmitted over the wireless communications network, be decrypted by the central module and be passed on to an E-mail server. Encrypted data can of course be transmitted both from the central module to the communications terminal and from the communications terminal to the central module.
[0010] In one embodiment of the present invention, data are encrypted into encrypted data by the central module, and the encrypted data are transmitted from the central module to the communications terminal. Such a process has the particular advantage that the authentication for access to data and the actual transmission of data to a communications terminal can take place at different points in time. Thus, the transmission of encrypted data can take place at a time when the user is situated in the vicinity of a powerful network, and the authentication for access to the electronic key and thus to the data can take place at a time when the user has enough time to carry out authentication.
[0011] In another embodiment of the present invention, data are encrypted by the communications terminal, and the encrypted data are transmitted from the communications terminal to a further communications device. Such a process has the particular advantage that, for example, data can be prepared for transmission on a mobile communications terminal, in that the data are encrypted into encrypted data. As soon as the mobile communications terminal is situated within the range of a powerful network, the encrypted data can be transmitted to a further communications device. Thus, the user can, for example, process a video file on the train, request a code for encrypting the video file while on the train, and encrypt the video file into an encrypted video file. As soon as the user's mobile communications terminal comes into the range of a powerful wireless network, when the user gets off the train at the railway station, the encrypted video file can be transmitted to a further communications device, to a file server, for example.
[0012] In one embodiment of the present invention, a user profile is stored in the central module or on the communications terminal, data being selected and encrypted in accordance with the user profile and transmitted to the communications terminal or to a further communications device. Such a process has the particular advantage that a user can enter into a user profile what data are to be encrypted and transmitted to the communications terminal or to the further communications device. So, for example, it can be entered into a user profile that all E-mail messages of a user are each encrypted and transmitted to the communications terminal of the user at a defined time, for example, in the morning around the time when the user is at the railway station in order to board a train.
[0013] In accordance with the inventions, the availability of the communications terminal or of a further communications device is checked by means of an availability module of the central module or of the communications terminal and, if the communications terminal or the further communications device is available, the encrypted data are transmitted to the communications terminal or to the further communications device. Such a process has the particular advantage that the encrypted data can be transmitted to the communications terminal or to the further communications device at the earliest possible time.
[0014] In a further embodiment of the present invention, a network interface of the communications terminal is activated by means of an activation module of the central module, and the encrypted data are transmitted to the communications terminal over the activated network interface. Thus, for example, a first network interface of the communications terminal, such as a GSM network interface, can be permanently switched on and a second network interface of the communications terminal, such as a WLAN network interface, can be activated over this first network interface. Such a process has the particular advantage that network interfaces are only switched on by the central module if encrypted data are ready for transmission, whereby in particular the power consumption on the communications terminal can be minimized.
[0015] In another embodiment of the present invention, the encrypted data are transmitted to a network device of a network infrastructure, whereby the encrypted data are stored on the network device, and are transmitted asynchronously from the network device to the communications terminal. The network device mentioned can, for example, refer to a network device of a WLAN hot spot, whereby the encrypted data are transmitted to the network device at a first time, for example, in the early morning at a time of low network load, and are transmitted, by this network device to the communications terminal of the user at a second time, for example, at a time when the user is waiting for a train at the railway station. Such a process has the particular advantage that the capacity utilization of a network infrastructure can be optimized. Before the encryption of the data, the data can of course be matched to a communications terminal. If, for example, the communications terminal of the user is a mobile computer with an XGA screen resolution of 1024.times.768 pixels, it makes no sense to encrypt directly a video file with very high resolution. It is much more sensible in this case first to match the video file by transformation of its resolution to the screen resolution of the user and only then to carry out an encryption of the video file. Such a transformation of the data can in particular be carried out if, for example, appropriate information is stored in a user profile.
[0016] In another embodiment of the present invention, a user account is debited with a monetary value upon the transfer of at least part of the electronic key. Such a process has the particular advantage that chargeable services, such as the provision of audio or video files, can be offered to the user by means of the transmission of encrypted data. The service, of course, is only considered to have been provided if both the encrypted data and the associated key have been transmitted to the communications terminal of the user.
[0017] In a further embodiment of the present invention, the encrypted data include program code that must be executed in order to decrypt the encrypted data, while validation criteria are checked during the execution of the program code. Thus, the program code can, for example, be of such form that the validity of the key is checked with reference to a time measurement on a central server with which the validity of codes is monitored, or in accordance with any other process. Such a process has the particular advantage that, for example, a time can be defined after which the encrypted data are no longer available. Such a process moreover guarantees compatibility with processes known from DRM (DRM: digital rights management).
[0018] In another embodiment of the present invention, an identification is assigned to the data and/or to the encrypted data, and the authentication data are stored as assigned to the identification. Such an identification can, for example, be formed as the result of a hash function on the encrypted data. Such a process has the particular advantage that authentication for access to the encrypted data can also be of different forms with reference to the encrypted data.
BRIEF DESCRIPTION OF THE DRAWINGS
[0019] A more complete appreciation of the invention and many of the attendant advantages thereof will be readily obtained as the same becomes better understood by reference to the following detailed description when considered in connection with the accompanying drawings, wherein:
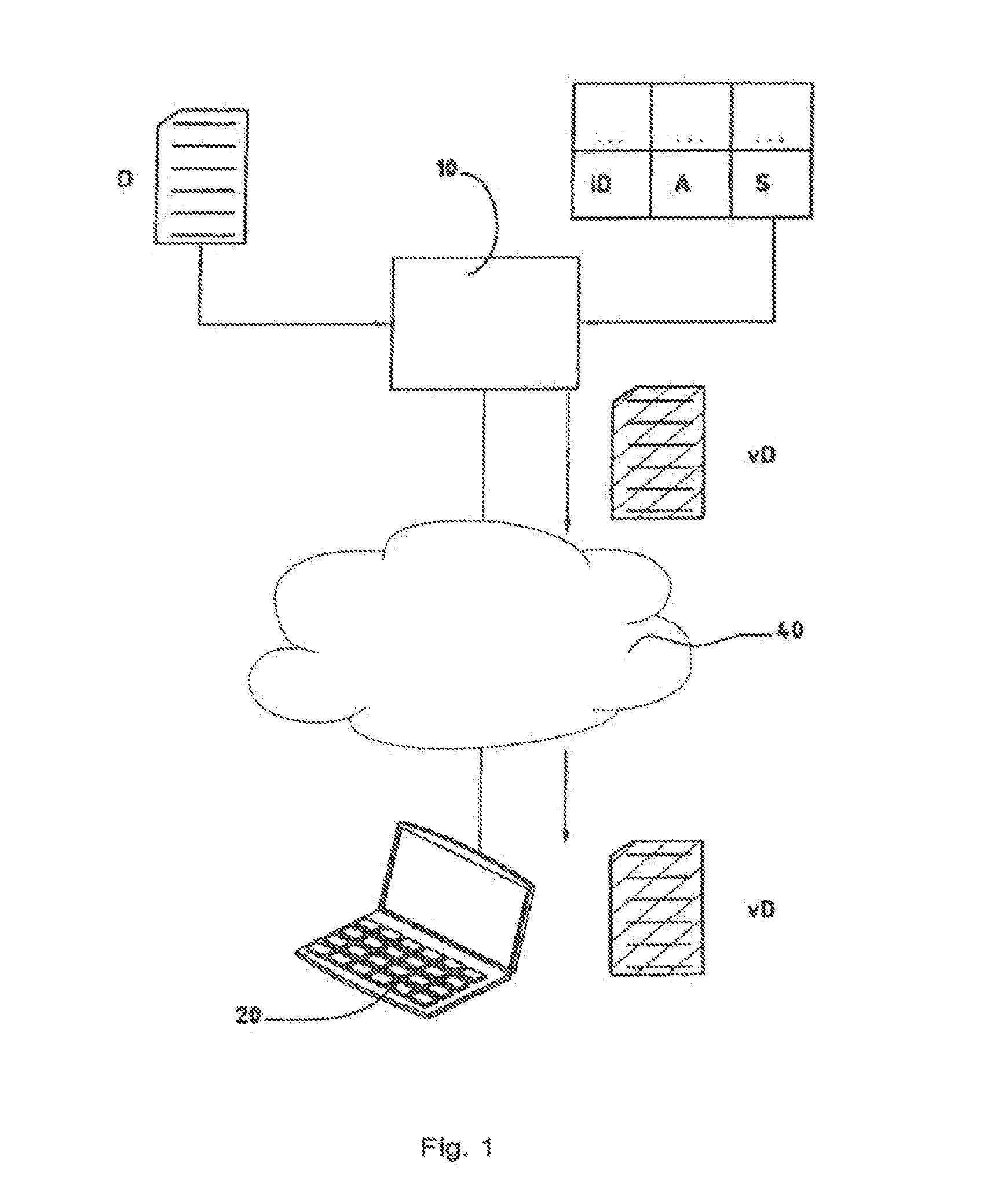
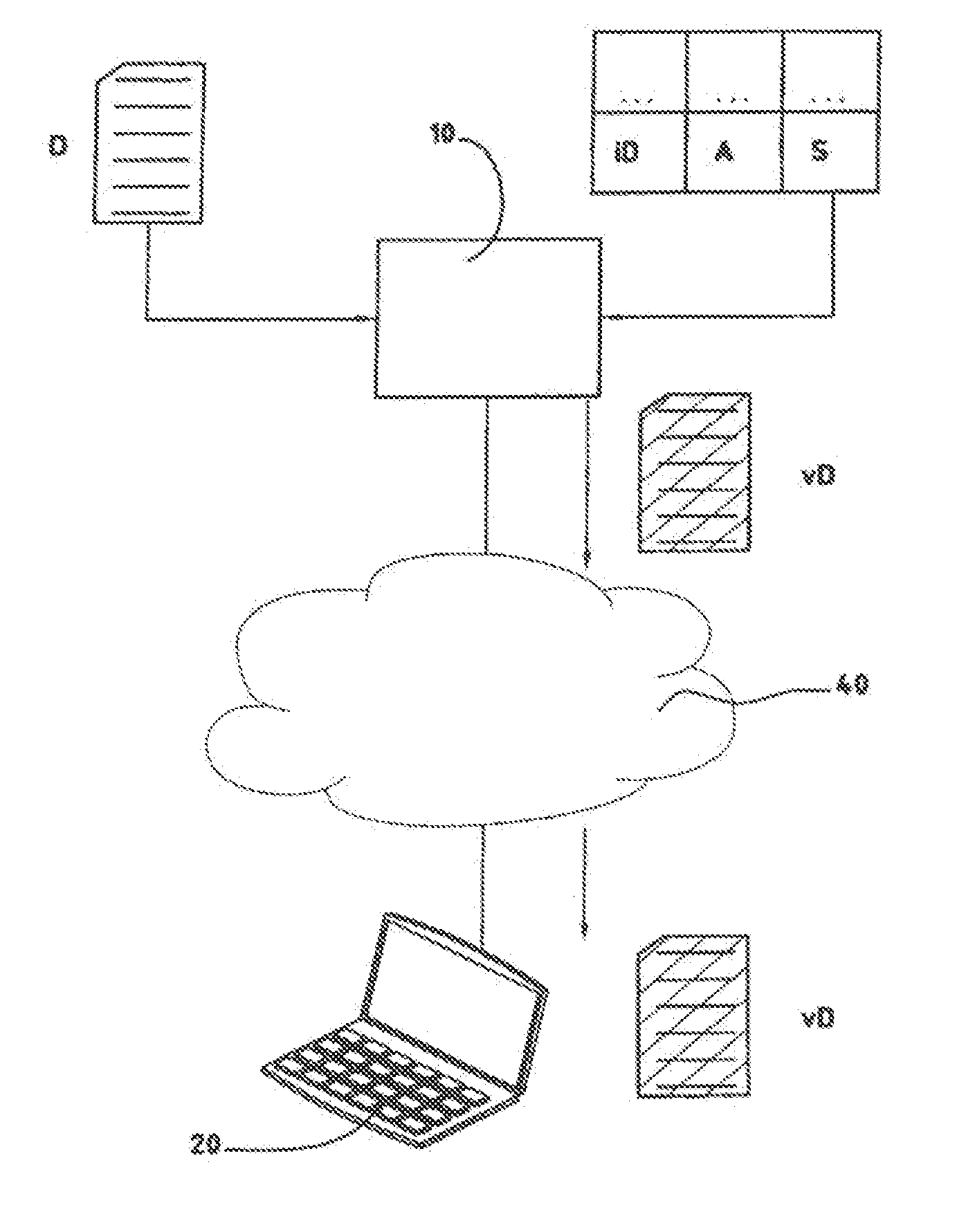
[0020] FIG. 1 shows a block diagram with the individual components for the encryption of data and for the transfer of the encrypted data.
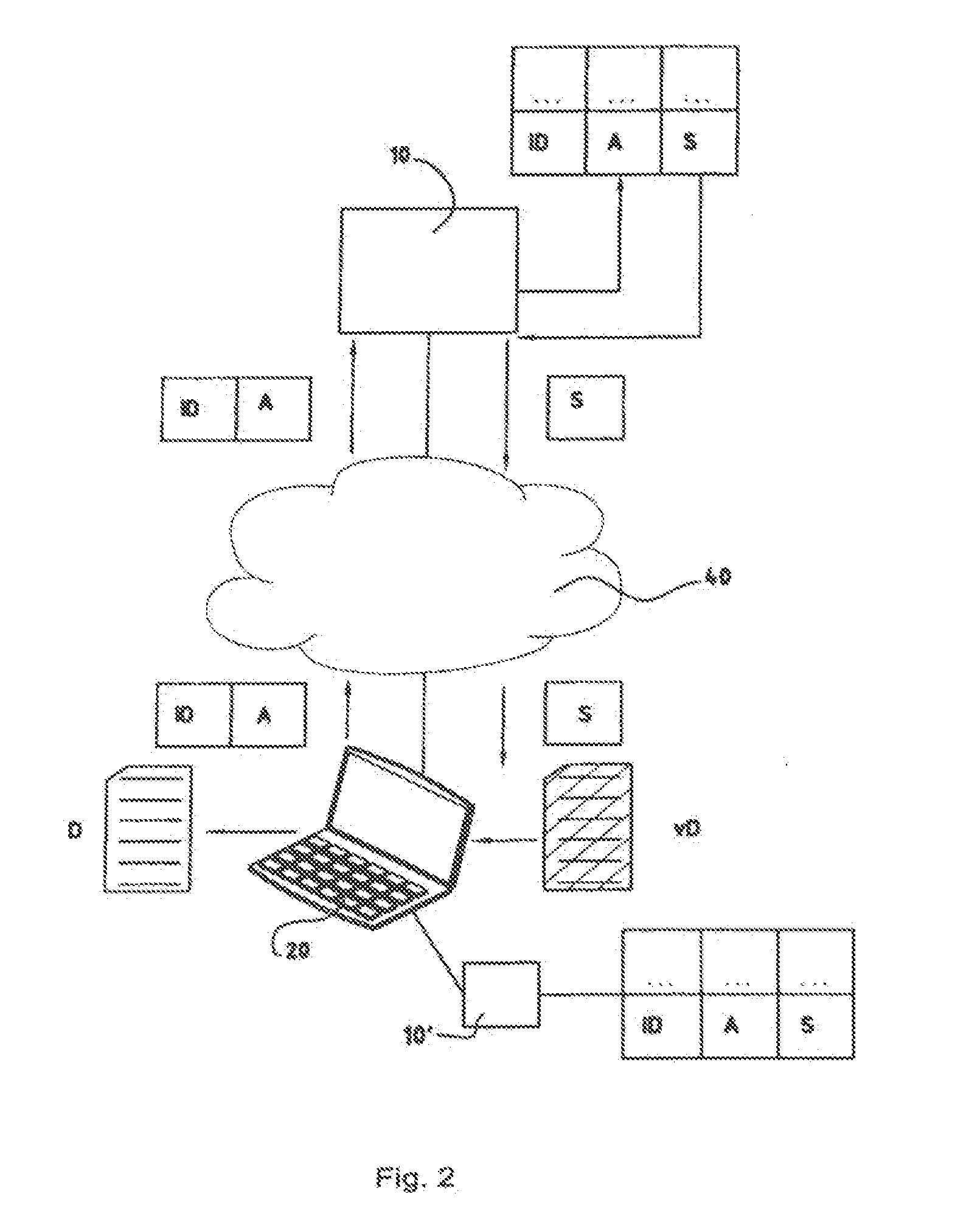
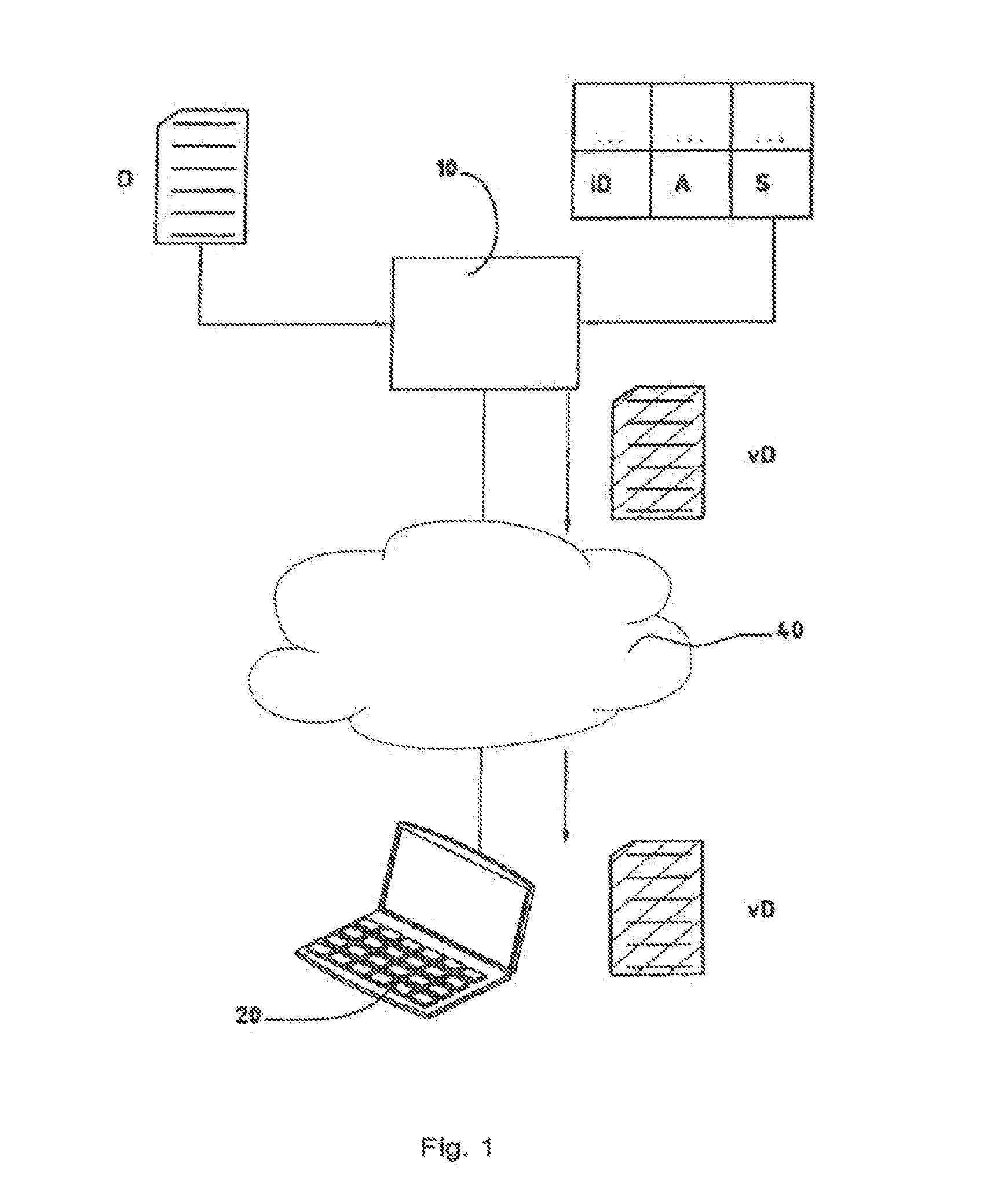
[0021] FIG. 2 shows a block diagram with the individual components for the authentication and decryption of the encrypted data.
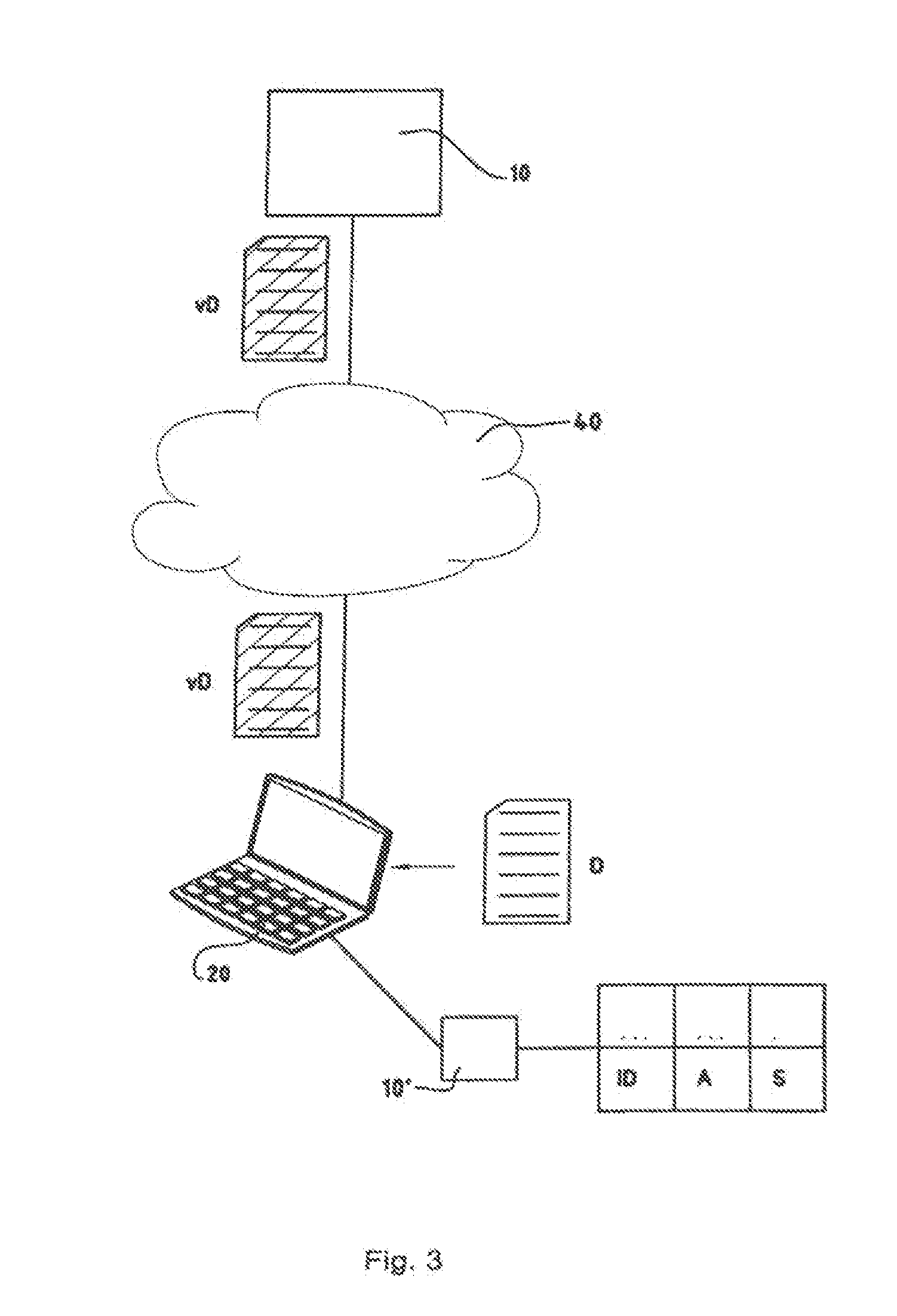
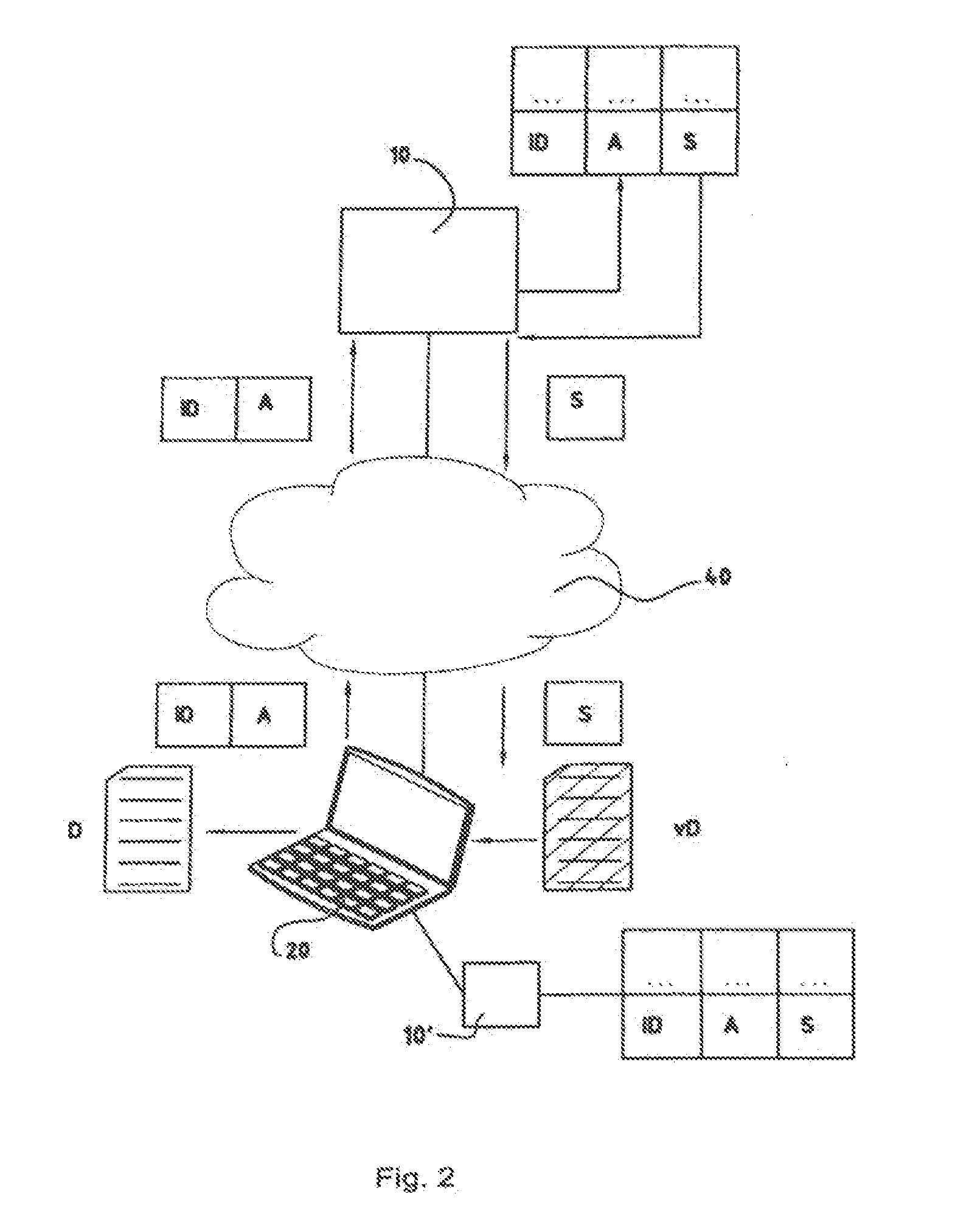
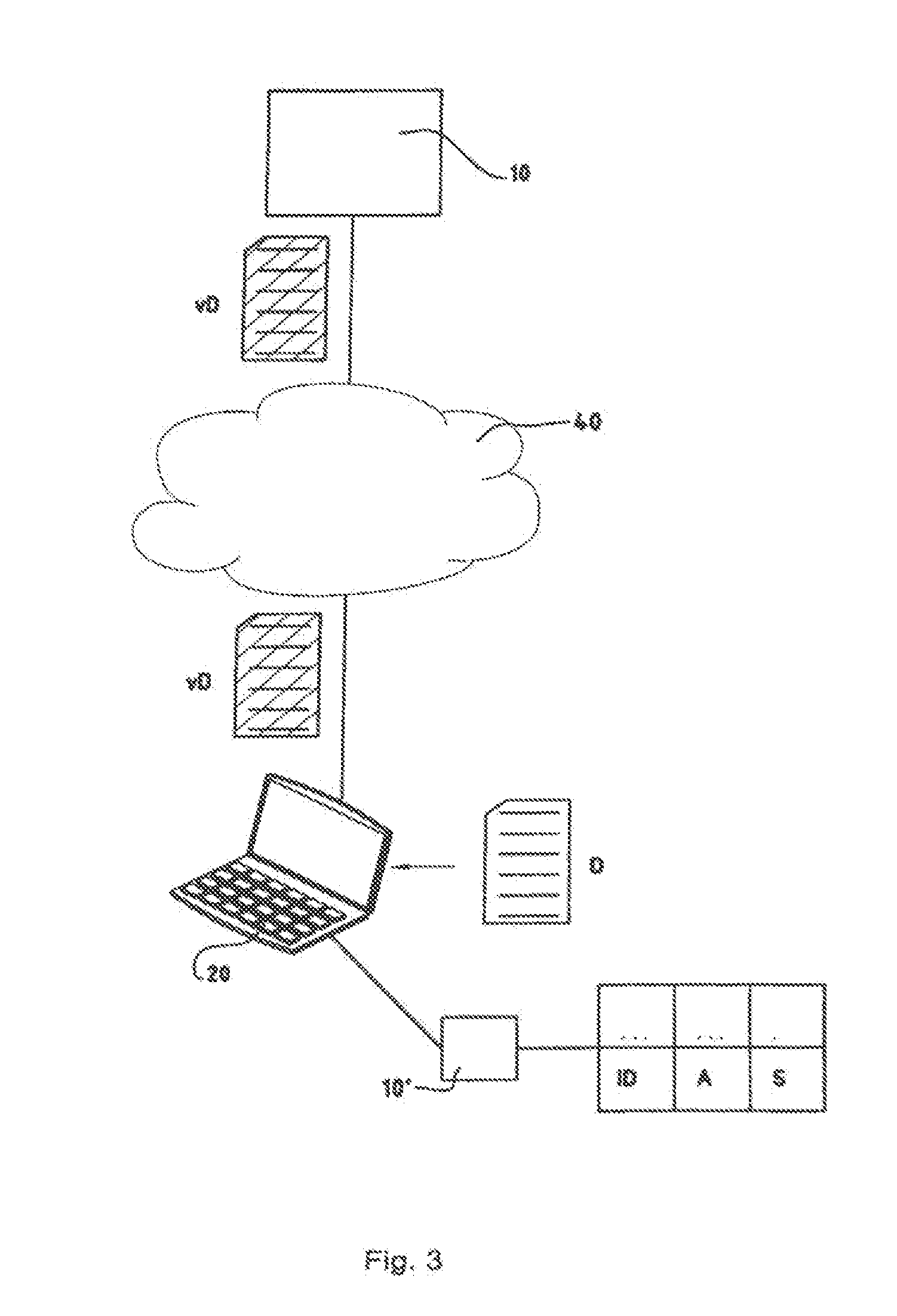
[0022] FIG. 3 shows a block diagram with the individual components for the encryption and sending of encrypted data.
DETAILED DESCRIPTION OF THE PREFERRED EMBODIMENTS
[0023] Referring now to the drawings, wherein like reference numerals designate identical or corresponding parts throughout the several views.
[0024] In FIG. 1, the reference mark 10 refers to a central module. The central module 10 can, for example, be formed as a software module of a network server. The central module 10 can also, of course, be formed completely as a hardware module with appropriate electronic circuits. In FIG. 1, the reference mark D refers to electronic data. The data D can be electronic data of any kind, for example E-mail messages, texts, animations, audio files, video files, or electronic data of any other kind. In FIG. 1, the reference mark A refers to authentication data and the reference mark S refers to an electronic key. The authentication data A can, for example, include a user name and a password or pass phrase. The electronic key S can, for example, consist of a symmetrical electronic key with a secret key or an asymmetrical electronic key with a public key and a private key. The authentication data A are stored as assigned to the electronic key S while, for example, with the central module 10 including a corresponding table. In FIG. 1, the reference mark 40 refers to a communications network. The communications network can, for example, refer to the Internet and can be constructed from various networks of differing technologies. Thus, the communications network can include GSM networks, UMTS networks, WLAN networks, Ethernet networks, UWB networks, or networks of any other kind. As shown in FIG. 1, the central module 10 can in particular be connected to the communications network 40. Data D can be encrypted by means of the electronic key S and an encryption module of the central module 10. Such encryption can refer to any encryption algorithm, for example a DES algorithm (DES: data encryption standard), a PGP algorithm (PGP: pretty good privacy), an IDEA algorithm (IDEA: international data encryption standard), or any other encryption algorithm. Encrypted data vD are generated by the encryption of the data D. The authentication data A and the electronic key S can moreover be stored as assigned to an identification iD of the data, so that the authentication data A and the electronic key S are valid only with reference to data that can be identified by the identification iD of the data. Corresponding tables can of course also be provided for in the central module 10 with reference to the identification iD of the data.
[0025] In FIG. 1, reference mark 20 refers to a communications terminal. The communications terminal 20 can be any terminal of a user, for example a mobile computer such as a notebook or a PDA (PDA: personal digital assistant), a mobile telephone, a games console, a permanently installed computer, or any other communications terminal. As shown in FIG. 1, the communications terminal 20 can be connected to the communications network 40. Such a connection can refer to a wireless connection, such as a WLAN connection, a GSM connection, or any other wireless connection, or to a wire-based connection, such as a twisted-pair Ethernet connection, or any other wire-based connection.
[0026] The encrypted data vD can thus be transmitted over the communications network 40 to the communications terminal 20 and be stored there. There is the widest variety of options in order thus to store data D as encrypted data vD on the communications terminal 20. E-mail messages, texts, animations, audio files, video files or data of any other kind can be stored on the communications terminal 20 as encrypted E-mail messages, encrypted texts, encrypted animations, encrypted audio files, or encrypted video files. It is, however, the case that the encrypted data vD may still be useless, since for the time being the key to decrypt the encrypted data is stored only on the central module 10.
[0027] The transmission of the encrypted data vD to the communications terminal 20 can take place at any convenient time. A convenient time can refer to the arrival of new E-mail messages, the availability of texts, or the publication of a new audio file. A convenient time, however, can also refer to the availability of a communications link between the communications network 40 and the communications terminal 20, the capacity utilization of the communications network 40, the capacity utilization of parts of the communications network 40, a time that occurs due to an input from the user on one of the communications terminals, or any other time.
[0028] The transmission of the encrypted data vD can also take place in accordance with various scenarios. One scenario can be that the encrypted data vD are transmitted to the communications terminal 20 at any time during the night over a broadband communications link, such as an Ethernet connection. Such a scenario may be selected, for example, in order to transmit a very large encrypted video file, of an order of magnitude of 5 Gbyte, for example, to the communications terminal 20. Or, in another scenario, encrypted data may be transmitted to the communications terminal 20 as soon as the user carrying this communications terminal 20 comes into the range of a wireless communications network, such as a WLAN network or UWB network at a railway station or on the site of an airport. Such a scenario may be selected, for example, in order to transmit encrypted E-mail messages or encrypted texts to the communications terminal 20 of a user before he boards a train. It may be remarked here that encrypted texts may refer for example to the current electronic issue of a daily newspaper.
[0029] In FIG. 2, the reference marks introduced in FIG. 1 are retained. As shown in FIG. 2, authentication data A are transmitted from the communications terminal 20 to the central module 10. Entitlement is thus authenticated with the electronic key S. At least parts of the electronic key S are then transmitted from the central module 10 to the communications terminal 20. By means of the electronic key S, the encrypted data vD stored on the communications terminal can be decrypted and stored as data D on the communications terminal, so that the user can access these data D.
[0030] An authentication of entitlement with the electronic key S can take place in accordance with known processes. Such processes can take place on the basis of a password or pass phrases, by means of a SecureID card (SecureID: authentication process of the firm RSA Security), on the basis of the acquisition of biometric characteristics, or on any other basis that provides proof of entitlement.
[0031] As indicated by the dotted areas in FIGS. 1 to 3, the identification iD, the authentication data A, and the key S can be stored in a table containing tuples of such data. A particular tuple may be provided with an identification iD, with authentication data A, and with a key S for a defined purpose. Thus, a first tuple may include an identification iD that refers to video data. A second tuple may include an identification iD that refers to audio data. Thus, video data and audio data, for example, can be encrypted with different keys, with a key for video data, for example, that causes particularly high efficiency in the encryption of the video data and with a key for audio data, for example, that causes particularly high security.
[0032] In FIG. 2, the reference mark 10' refers to a local copy of the central module 10 placed on the communications terminal 20. The local copy 10' of the central module 10 may include the same functions as the central module 10. Thus, local copies of the tuples with an identification iD, with authentication data A, and with a key S, can also be stored on the communications terminal 20. The local copy 10' of the central module and the local copies of the tuples mentioned can be protected, for example, by the use of a secret key, such as a PIN (PIN: personal identification number). Thus, it can be provided for that access to the local copy of these functions and data is only enabled for a user who knows the secret key. For example, the functions and data of this local copy can of course track incrementally the corresponding functions and data of the central module 10, or only specific functions and data may be stored in the local copy.
[0033] As shown in FIG. 3, data D can be encrypted into encrypted data vD on the communications terminal 20 and be transmitted to a further communications device. Thus, a local copy 10' of the central module 10 with functionality for the encryption of data and with a corresponding key S can be stored on the communications terminal 20. The user of the communications terminal 20 may, for example, record a new video file. As soon as the video file has been completed, the video file can be encrypted into an encrypted video file by means of the functions provided by the local copy 10' of the central module 10. Of course the user can also, by making an appropriate request, obtain a key S from the central module 10 for encrypting the video file. The video file can be encrypted into an encrypted video file and the encrypted video file can be stored on the communications terminal 20. As soon as the communications terminal 20 comes within the range of a powerful network, a WLAN network, for example, the encrypted video file can be transmitted to a further communications device. The further communications device can refer, for example, to the central module 10, a file server, a communications terminal of another user, or any other further communications device.
[0034] The previously described process may be encoded in software on a computer readable medium including a compact disk, memory device, flash memory or any other computer readable physical medium. The software is configured to cause a processor-based device to carry out one or more of the steps described above. Computer operations are described in "How Computers Work, Millennium Edition," by Ron White, Que Publications, 1999, the entire contents of which being incorporated herein by reference.
[0035] Obviously, numerous modifications and variations of the present invention are possible in light of the above teachings. It is therefore to be understood that within the scope of the appended claims, the invention may be practiced otherwise than as specifically described herein.
* * * * *
D00000
D00001
D00002
D00003
XML
uspto.report is an independent third-party trademark research tool that is not affiliated, endorsed, or sponsored by the United States Patent and Trademark Office (USPTO) or any other governmental organization. The information provided by uspto.report is based on publicly available data at the time of writing and is intended for informational purposes only.
While we strive to provide accurate and up-to-date information, we do not guarantee the accuracy, completeness, reliability, or suitability of the information displayed on this site. The use of this site is at your own risk. Any reliance you place on such information is therefore strictly at your own risk.
All official trademark data, including owner information, should be verified by visiting the official USPTO website at www.uspto.gov. This site is not intended to replace professional legal advice and should not be used as a substitute for consulting with a legal professional who is knowledgeable about trademark law.