Document security system that permits external users to gain access to secured files
Vainstein
U.S. patent number RE47,443 [Application Number 15/418,263] was granted by the patent office on 2019-06-18 for document security system that permits external users to gain access to secured files. This patent grant is currently assigned to Intellectual Ventures I LLC. The grantee listed for this patent is Intellectual Ventures I LLC. Invention is credited to Klimenty Vainstein.







| United States Patent | RE47,443 |
| Vainstein | June 18, 2019 |
Document security system that permits external users to gain access to secured files
Abstract
A system includes a server with an access manager configured to restrict access to files of an organization and maintain at least encryption keys for internal and external users and an external access server connected to the server and coupled between the server and a data network. The data network is configured to allow the external users use of the external access server. The external access server is also configured to permit file exchange between the internal users and the external users via the server.
| Inventors: | Vainstein; Klimenty (Cupertino, CA) | ||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|
| Applicant: |
|
||||||||||
| Assignee: | Intellectual Ventures I LLC
(Wilmington, DE) |
||||||||||
| Family ID: | 32030168 | ||||||||||
| Appl. No.: | 15/418,263 | ||||||||||
| Filed: | January 27, 2017 |
Related U.S. Patent Documents
| Application Number | Filing Date | Patent Number | Issue Date | ||
|---|---|---|---|---|---|
| 10262218 | May 8, 2012 | 8176334 | |||
| Reissue of: | 13439485 | Apr 4, 2012 | 8943316 | Jan 27, 2015 | |
| Current U.S. Class: | 1/1 |
| Current CPC Class: | G06F 21/6218 (20130101); G06F 21/6218 (20130101); G06F 21/6209 (20130101); G06F 21/6209 (20130101) |
| Current International Class: | G06F 21/00 (20130101); H04L 29/00 (20060101); H04N 7/16 (20110101); G06F 15/16 (20060101); G06F 7/04 (20060101); G06F 21/62 (20130101); H04L 29/06 (20060101) |
| Field of Search: | ;705/51,37 ;707/999.009 ;709/223,217 ;713/150,193 ;726/21 ;380/277,278,286 |
References Cited [Referenced By]
U.S. Patent Documents
| 4203166 | May 1980 | Ehrsam et al. |
| 4238854 | December 1980 | Ehrsam et al. |
| 4423387 | December 1983 | Sempel |
| 4734568 | March 1988 | Watanabe |
| 4757533 | July 1988 | Allen et al. |
| 4796220 | January 1989 | Wolfe |
| 4799258 | January 1989 | Davies |
| 4827508 | May 1989 | Shear |
| 4887204 | December 1989 | Johnson et al. |
| 4888800 | December 1989 | Marshall et al. |
| 4912552 | March 1990 | Allison, III et al. |
| 4972472 | November 1990 | Brown et al. |
| 5032979 | July 1991 | Hecht et al. |
| 5052040 | September 1991 | Preston et al. |
| 5058164 | October 1991 | Elmer et al. |
| 5144660 | September 1992 | Rose |
| 5204897 | April 1993 | Wyman |
| 5212788 | May 1993 | Lomet et al. |
| 5220657 | June 1993 | Bly et al. |
| 5235641 | August 1993 | Nozawa et al. |
| 5247575 | September 1993 | Sprague et al. |
| 5267313 | November 1993 | Hirata |
| 5276735 | January 1994 | Boebert et al. |
| 5301247 | April 1994 | Rasmussen et al. |
| 5319705 | June 1994 | Halter et al. |
| 5357375 | October 1994 | Harig et al. |
| 5369702 | November 1994 | Shanton |
| 5375169 | December 1994 | Seheidt et al. |
| 5404404 | April 1995 | Novorita |
| 5406628 | April 1995 | Beller et al. |
| 5414852 | May 1995 | Kramer et al. |
| 5434918 | July 1995 | Kung et al. |
| 5461710 | October 1995 | Bloomfield et al. |
| 5467342 | November 1995 | Logston et al. |
| 5495533 | February 1996 | Linehan et al. |
| 5497422 | March 1996 | Tysen et al. |
| 5499297 | March 1996 | Boebert |
| 5502766 | March 1996 | Boebert et al. |
| 5535375 | July 1996 | Eshel et al. |
| 5557765 | September 1996 | Lipner et al. |
| 5570108 | October 1996 | McLaughlin et al. |
| 5584023 | December 1996 | Hsu |
| 5600722 | February 1997 | Yamaguchi et al. |
| 5606663 | February 1997 | Kadooka |
| 5619576 | April 1997 | Shaw |
| 5638501 | June 1997 | Gough et al. |
| 5655119 | August 1997 | Davy |
| 5661668 | August 1997 | Yemini et al. |
| 5661806 | August 1997 | Nevoux et al. |
| 5671412 | September 1997 | Christiano |
| 5673316 | September 1997 | Auerbach et al. |
| 5677953 | October 1997 | Dolphin |
| 5680452 | October 1997 | Shanton |
| 5682537 | October 1997 | Davies et al. |
| 5684987 | November 1997 | Mamiya et al. |
| 5689688 | November 1997 | Strong et al. |
| 5689718 | November 1997 | Sakurai et al. |
| 5693652 | December 1997 | Takase et al. |
| 5699428 | December 1997 | McDonnal et al. |
| 5708709 | January 1998 | Rose |
| 5715403 | February 1998 | Stefik |
| 5717755 | February 1998 | Shanton |
| 5719941 | February 1998 | Swift et al. |
| 5720033 | February 1998 | Deo |
| 5721780 | February 1998 | Ensor et al. |
| 5729734 | March 1998 | Parker et al. |
| 5732265 | March 1998 | Dewitt et al. |
| 5745573 | April 1998 | Lipner et al. |
| 5745750 | April 1998 | Porcaro |
| 5748736 | May 1998 | Mittra |
| 5751287 | May 1998 | Hahn et al. |
| 5757920 | May 1998 | Misra et al. |
| 5765152 | June 1998 | Erickson |
| 5768381 | June 1998 | Hawthorne |
| 5778065 | July 1998 | Hauser et al. |
| 5778350 | July 1998 | Adams et al. |
| 5781711 | July 1998 | Austin et al. |
| 5787169 | July 1998 | Eldridge et al. |
| 5787173 | July 1998 | Seheidt et al. |
| 5787175 | July 1998 | Carter |
| 5790789 | August 1998 | Suarez |
| 5790790 | August 1998 | Smith et al. |
| 5813009 | September 1998 | Johnson et al. |
| 5821933 | October 1998 | Keller et al. |
| 5825876 | October 1998 | Peterson, Jr. |
| 5835592 | November 1998 | Chang et al. |
| 5835601 | November 1998 | Shimbo et al. |
| 5850443 | December 1998 | Van Oorschot et al. |
| 5857189 | January 1999 | Riddle |
| 5862325 | January 1999 | Reed et al. |
| 5864683 | January 1999 | Boebert et al. |
| 5870468 | February 1999 | Harrison |
| 5870477 | February 1999 | Sasaki et al. |
| 5881287 | March 1999 | Mast |
| 5892900 | April 1999 | Ginter et al. |
| 5893084 | April 1999 | Morgan et al. |
| 5898781 | April 1999 | Shanton |
| 5922073 | July 1999 | Shimada |
| 5923754 | July 1999 | Angelo et al. |
| 5933498 | August 1999 | Schneck et al. |
| 5940507 | August 1999 | Cane |
| 5944794 | August 1999 | Okamoto et al. |
| 5953419 | September 1999 | Lohstroh et al. |
| 5968177 | October 1999 | Batten-Carew et al. |
| 5970502 | October 1999 | Salkewicz et al. |
| 5978802 | November 1999 | Hurvig |
| 5987440 | November 1999 | O'Neil et al. |
| 5991879 | November 1999 | Still |
| 5999907 | December 1999 | Donner |
| 6011847 | January 2000 | Follendore, III |
| 6014730 | January 2000 | Ohtsu |
| 6023506 | February 2000 | Ote et al. |
| 6031584 | February 2000 | Gray |
| 6032216 | February 2000 | Schmuck et al. |
| 6035404 | March 2000 | Zhao |
| 6038322 | March 2000 | Harkins |
| 6044155 | March 2000 | Thomlinson et al. |
| 6055314 | April 2000 | Spies et al. |
| 6058424 | May 2000 | Dixon et al. |
| 6061790 | May 2000 | Bodnar |
| 6069057 | May 2000 | Wu |
| 6069957 | May 2000 | Richards |
| 6070244 | May 2000 | Orchier et al. |
| 6073242 | June 2000 | Hardy et al. |
| 6085323 | July 2000 | Shimizu et al. |
| 6088717 | July 2000 | Reed et al. |
| 6088805 | July 2000 | Davis et al. |
| 6098056 | August 2000 | Rusnak et al. |
| 6101507 | August 2000 | Cane et al. |
| 6105131 | August 2000 | Carroll |
| 6122630 | September 2000 | Strickler et al. |
| 6134327 | October 2000 | Van Oorschot |
| 6134658 | October 2000 | Multerer et al. |
| 6134660 | October 2000 | Boneh et al. |
| 6134664 | October 2000 | Walker |
| 6141754 | October 2000 | Choy |
| 6145084 | November 2000 | Zuili et al. |
| 6148338 | November 2000 | Lachelt et al. |
| 6158010 | December 2000 | Moriconi et al. |
| 6161139 | December 2000 | Win et al. |
| 6182142 | January 2001 | Win et al. |
| 6185684 | February 2001 | Pravetz et al. |
| 6192408 | February 2001 | Vahalia et al. |
| 6199070 | March 2001 | Polo-Wood et al. |
| 6205549 | March 2001 | Pravetz |
| 6212561 | April 2001 | Sitaraman et al. |
| 6223285 | April 2001 | Komuro et al. |
| 6226618 | May 2001 | Downs et al. |
| 6226745 | May 2001 | Wiederhold |
| 6240188 | May 2001 | Dondeti et al. |
| 6249755 | June 2001 | Yemini et al. |
| 6249873 | June 2001 | Richard et al. |
| 6253193 | June 2001 | Ginter et al. |
| 6260040 | July 2001 | Kauffman et al. |
| 6260141 | July 2001 | Park |
| 6263348 | July 2001 | Kathrow et al. |
| 6266420 | July 2001 | Langford et al. |
| 6272631 | August 2001 | Thomlinson et al. |
| 6272632 | August 2001 | Carman et al. |
| 6275941 | August 2001 | Saito et al. |
| 6282649 | August 2001 | Lambert et al. |
| 6289450 | September 2001 | Pensak et al. |
| 6289458 | September 2001 | Garg et al. |
| 6292895 | September 2001 | Baltzley |
| 6292899 | September 2001 | McBride |
| 6295361 | September 2001 | Kadansky et al. |
| 6298445 | October 2001 | Shostack et al. |
| 6299069 | October 2001 | Shona |
| 6301614 | October 2001 | Najork et al. |
| 6308256 | October 2001 | Folmsbee |
| 6308273 | October 2001 | Goertzel et al. |
| 6314408 | November 2001 | Salas et al. |
| 6314409 | November 2001 | Schneck et al. |
| 6317777 | November 2001 | Skarbo et al. |
| 6332025 | December 2001 | Takahashi et al. |
| 6334146 | December 2001 | Parasnis |
| 6336114 | January 2002 | Garrison |
| 6339423 | January 2002 | Sampson et al. |
| 6339825 | January 2002 | Pensak et al. |
| 6341164 | January 2002 | Dilkie et al. |
| 6343316 | January 2002 | Sakata |
| 6347374 | February 2002 | Drake et al. |
| 6349337 | February 2002 | Parsons, Jr. et al. |
| 6351813 | February 2002 | Mooney et al. |
| 6356903 | March 2002 | Baxter et al. |
| 6356941 | March 2002 | Cohen |
| 6357010 | March 2002 | Viets et al. |
| 6363480 | March 2002 | Perlman |
| 6366298 | April 2002 | Haitsuka et al. |
| 6370249 | April 2002 | Van Oorschot |
| 6381698 | April 2002 | Devanbu et al. |
| 6385644 | May 2002 | Devine et al. |
| 6389433 | May 2002 | Bolosky et al. |
| 6389538 | May 2002 | Gruse et al. |
| 6393420 | May 2002 | Peters |
| 6405315 | June 2002 | Burns et al. |
| 6405318 | June 2002 | Rowland |
| 6408404 | June 2002 | Ladwig |
| 6421714 | July 2002 | Rai et al. |
| 6442688 | August 2002 | Moses et al. |
| 6442695 | August 2002 | Dutcher et al. |
| 6446090 | September 2002 | Hart |
| 6449721 | September 2002 | Pensak et al. |
| 6453353 | September 2002 | Win et al. |
| 6453419 | September 2002 | Flint et al. |
| 6466476 | October 2002 | Wong et al. |
| 6466932 | October 2002 | Dennis et al. |
| 6476833 | November 2002 | Moshfeghi |
| 6477544 | November 2002 | Bolosky et al. |
| 6487662 | November 2002 | Kharon et al. |
| 6490680 | December 2002 | Scheidt et al. |
| 6505300 | January 2003 | Chan et al. |
| 6510349 | January 2003 | Schneck et al. |
| 6519700 | February 2003 | Ram et al. |
| 6529956 | March 2003 | Smith et al. |
| 6530020 | March 2003 | Aoki |
| 6530024 | March 2003 | Proctor |
| 6542608 | April 2003 | Scheidt et al. |
| 6549623 | April 2003 | Scheidt et al. |
| 6550011 | April 2003 | Sims, III |
| 6557039 | April 2003 | Leong et al. |
| 6567914 | May 2003 | Just et al. |
| 6571291 | May 2003 | Chow |
| 6574733 | June 2003 | Langford |
| 6584466 | June 2003 | Serbinis et al. |
| 6587878 | July 2003 | Merriam |
| 6587946 | July 2003 | Jakobsson |
| 6588673 | July 2003 | Chan et al. |
| 6591295 | July 2003 | Diamond et al. |
| 6594662 | July 2003 | Sieffert et al. |
| 6598161 | July 2003 | Kluttz et al. |
| 6601170 | July 2003 | Wallace, Jr. |
| 6603857 | August 2003 | Batten-Carew et al. |
| 6608636 | August 2003 | Roseman |
| 6609115 | August 2003 | Mehring et al. |
| 6611599 | August 2003 | Natarajan |
| 6611846 | August 2003 | Stoodley |
| 6615349 | September 2003 | Hair |
| 6615350 | September 2003 | Schell et al. |
| 6625650 | September 2003 | Stelliga |
| 6625734 | September 2003 | Marvit et al. |
| 6629140 | September 2003 | Fertell et al. |
| 6629243 | September 2003 | Kleinman et al. |
| 6633311 | October 2003 | Douvikas et al. |
| 6640307 | October 2003 | Viets et al. |
| 6646515 | November 2003 | Jun et al. |
| 6647388 | November 2003 | Numao et al. |
| 6678835 | January 2004 | Shah et al. |
| 6683954 | January 2004 | Searle |
| 6687822 | February 2004 | Jakobsson |
| 6693652 | February 2004 | Barrus et al. |
| 6698022 | February 2004 | Wu |
| 6711683 | March 2004 | Laczko, Sr. et al. |
| 6718361 | April 2004 | Basani et al. |
| 6735701 | May 2004 | Jacobson |
| 6738908 | May 2004 | Bonn et al. |
| 6751573 | June 2004 | Burch |
| 6754657 | June 2004 | Lomet |
| 6754665 | June 2004 | Kawamoto et al. |
| 6775779 | August 2004 | England et al. |
| 6779031 | August 2004 | Picher-Dempsey |
| 6782403 | August 2004 | Kino et al. |
| 6785810 | August 2004 | Lirov et al. |
| 6801999 | October 2004 | Venkatesan et al. |
| 6807534 | October 2004 | Erickson |
| 6807636 | October 2004 | Hartman et al. |
| 6810389 | October 2004 | Meyer |
| 6810479 | October 2004 | Barlow et al. |
| 6816871 | November 2004 | Lee |
| 6816969 | November 2004 | Miyazaki et al. |
| 6820204 | November 2004 | Desai et al. |
| 6826698 | November 2004 | Minkin et al. |
| 6834333 | December 2004 | Yoshino et al. |
| 6834341 | December 2004 | Bahl et al. |
| 6834351 | December 2004 | Kabenjian |
| 6842825 | January 2005 | Geiner et al. |
| 6845452 | January 2005 | Roddy et al. |
| 6851050 | February 2005 | Singhal et al. |
| 6862103 | March 2005 | Miura et al. |
| 6865555 | March 2005 | Novak |
| 6870920 | March 2005 | Henits |
| 6874139 | March 2005 | Krueger et al. |
| 6877010 | April 2005 | Smith-Semedo et al. |
| 6877136 | April 2005 | Bess et al. |
| 6882994 | April 2005 | Yoshimura et al. |
| 6889210 | May 2005 | Vainstein |
| 6891953 | May 2005 | DeMello et al. |
| 6892201 | May 2005 | Brown et al. |
| 6892306 | May 2005 | En-Seung et al. |
| 6898627 | May 2005 | Sekiguchi |
| 6907034 | June 2005 | Begis |
| 6909708 | June 2005 | Krishnaswamy et al. |
| 6915425 | July 2005 | Xu et al. |
| 6915434 | July 2005 | Kuroda et al. |
| 6915435 | July 2005 | Merriam |
| 6920558 | July 2005 | Sames et al. |
| 6922785 | July 2005 | Brewer et al. |
| 6924425 | August 2005 | Naples et al. |
| 6931450 | August 2005 | Howard et al. |
| 6931530 | August 2005 | Pham et al. |
| 6931597 | August 2005 | Prakash |
| 6938042 | August 2005 | Aboulhosn et al. |
| 6938156 | August 2005 | Wheeler et al. |
| 6941355 | September 2005 | Donaghey et al. |
| 6941456 | September 2005 | Wilson |
| 6941472 | September 2005 | Moriconi et al. |
| 6944183 | September 2005 | Iyer et al. |
| 6947556 | September 2005 | Matyas, Jr. et al. |
| 6950818 | September 2005 | Dennis et al. |
| 6950936 | September 2005 | Subramaniam et al. |
| 6950941 | September 2005 | Lee et al. |
| 6950943 | September 2005 | Bacha et al. |
| 6952780 | October 2005 | Olsen et al. |
| 6957261 | October 2005 | Lortz |
| 6959308 | October 2005 | Gramsamer et al. |
| 6961849 | November 2005 | Davis et al. |
| 6961855 | November 2005 | Rich et al. |
| 6968060 | November 2005 | Pinkas |
| 6968456 | November 2005 | Tripathi et al. |
| 6971018 | November 2005 | Witt et al. |
| 6976259 | December 2005 | Dutta et al. |
| 6978366 | December 2005 | Ignatchenko et al. |
| 6978376 | December 2005 | Giroux et al. |
| 6978377 | December 2005 | Asano et al. |
| 6987752 | January 2006 | Sarraf et al. |
| 6988133 | January 2006 | Zavalkovsky et al. |
| 6988199 | January 2006 | Toh et al. |
| 6990441 | January 2006 | Bolme et al. |
| 6993135 | January 2006 | Ishibashi |
| 6996718 | February 2006 | Henry et al. |
| 7000150 | February 2006 | Zunino et al. |
| 7003116 | February 2006 | Riedel et al. |
| 7003117 | February 2006 | Kacker et al. |
| 7003560 | February 2006 | Mullen et al. |
| 7003661 | February 2006 | Beattie et al. |
| 7010689 | March 2006 | Matyas, Jr. et al. |
| 7010809 | March 2006 | Hori et al. |
| 7013332 | March 2006 | Friedel et al. |
| 7013485 | March 2006 | Brown et al. |
| 7020645 | March 2006 | Bisbee et al. |
| 7024427 | April 2006 | Bobbitt et al. |
| 7035854 | April 2006 | Hsiao et al. |
| 7035910 | April 2006 | Dutta et al. |
| 7043637 | May 2006 | Bolosky et al. |
| 7046807 | May 2006 | Hirano et al. |
| 7047404 | May 2006 | Doonan et al. |
| 7051213 | May 2006 | Kobayashi et al. |
| 7058696 | June 2006 | Phillips et al. |
| 7058802 | June 2006 | Epstein et al. |
| 7058978 | June 2006 | Feuerstein et al. |
| 7062642 | June 2006 | Langrind et al. |
| 7073063 | July 2006 | Peinado |
| 7073073 | July 2006 | Nonaka et al. |
| 7076063 | July 2006 | Kuroiwa |
| 7076067 | July 2006 | Raike et al. |
| 7076312 | July 2006 | Law et al. |
| 7076469 | July 2006 | Schreiber et al. |
| 7076633 | July 2006 | Tormasov et al. |
| 7080077 | July 2006 | Ramamurthy et al. |
| 7095853 | August 2006 | Morishita |
| 7096266 | August 2006 | Lewin et al. |
| 7099926 | August 2006 | Ims et al. |
| 7103911 | September 2006 | Spies et al. |
| 7107185 | September 2006 | Yemini et al. |
| 7107269 | September 2006 | Arlein et al. |
| 7107416 | September 2006 | Stuart et al. |
| 7113594 | September 2006 | Boneh et al. |
| 7116785 | October 2006 | Okaue |
| 7117322 | October 2006 | Hochberg et al. |
| 7120635 | October 2006 | Bhide et al. |
| 7120757 | October 2006 | Tsuge |
| 7120935 | October 2006 | Serani et al. |
| 7124164 | October 2006 | Chemtob |
| 7126957 | October 2006 | Isukapalli et al. |
| 7130964 | October 2006 | Ims et al. |
| 7131071 | October 2006 | Gune et al. |
| 7134041 | November 2006 | Murray et al. |
| 7136903 | November 2006 | Phillips et al. |
| 7139399 | November 2006 | Zimmermann |
| 7140044 | November 2006 | Redlich et al. |
| 7145898 | December 2006 | Elliott |
| 7146388 | December 2006 | Stakutis et al. |
| 7146498 | December 2006 | Takechi et al. |
| 7149896 | December 2006 | Bahl et al. |
| 7159036 | January 2007 | Hinchliffe et al. |
| 7165179 | January 2007 | Maruyama et al. |
| 7168094 | January 2007 | Fredell |
| 7171557 | January 2007 | Kallahalla et al. |
| 7174563 | February 2007 | Brownlie et al. |
| 7177426 | February 2007 | Dube |
| 7177427 | February 2007 | Komuro et al. |
| 7177839 | February 2007 | Claxton et al. |
| 7178033 | February 2007 | Garcia |
| 7181017 | February 2007 | Nagel et al. |
| 7185192 | February 2007 | Kahn |
| 7185196 | February 2007 | Kuskin et al. |
| 7185199 | February 2007 | Balfanz et al. |
| 7185364 | February 2007 | Knouse et al. |
| 7187033 | March 2007 | Pendharkar |
| 7188181 | March 2007 | Squier et al. |
| 7194764 | March 2007 | Martherus et al. |
| 7197638 | March 2007 | Grawrock et al. |
| 7200747 | April 2007 | Riedel et al. |
| 7203317 | April 2007 | Kallahalla et al. |
| 7203968 | April 2007 | Asano et al. |
| 7216368 | May 2007 | Ishiguro |
| 7219230 | May 2007 | Riedel et al. |
| 7224795 | May 2007 | Takada et al. |
| 7225256 | May 2007 | Villavicencio |
| 7227953 | June 2007 | Shida |
| 7233948 | June 2007 | Shamoon et al. |
| 7234063 | June 2007 | Baugher et al. |
| 7237002 | June 2007 | Estrada et al. |
| 7249044 | July 2007 | Kumar et al. |
| 7249251 | July 2007 | Todd et al. |
| 7260555 | August 2007 | Rossmann et al. |
| 7265764 | September 2007 | Alben et al. |
| 7266684 | September 2007 | Jancula |
| 7280658 | October 2007 | Amini et al. |
| 7281272 | October 2007 | Rubin et al. |
| 7287055 | October 2007 | Cannata et al. |
| 7287058 | October 2007 | Loveland et al. |
| 7287620 | October 2007 | Thomas et al. |
| 7290148 | October 2007 | Tozawa et al. |
| 7308702 | December 2007 | Thomsen et al. |
| 7313824 | December 2007 | Bala et al. |
| 7319752 | January 2008 | Asano et al. |
| 7331058 | February 2008 | Gladney |
| 7340600 | March 2008 | Corella |
| 7343488 | March 2008 | Yadav |
| 7359517 | April 2008 | Rowe |
| 7362868 | April 2008 | Madoukh et al. |
| 7380120 | May 2008 | Garcia |
| 7383586 | June 2008 | Cross et al. |
| 7386529 | June 2008 | Kiessig et al. |
| 7386599 | June 2008 | Piersol et al. |
| 7401220 | July 2008 | Bolosky et al. |
| 7406596 | July 2008 | Tararukhina |
| 7415608 | August 2008 | Bolosky et al. |
| 7434048 | October 2008 | Shapiro et al. |
| 7454612 | November 2008 | Bolosky et al. |
| 7461157 | December 2008 | Ahlard et al. |
| 7461405 | December 2008 | Boudreault et al. |
| 7478243 | January 2009 | Bolosky et al. |
| 7478418 | January 2009 | Supramaniam et al. |
| 7484245 | January 2009 | Friedman et al. |
| 7496959 | February 2009 | Adelstein et al. |
| 7509492 | March 2009 | Boyen et al. |
| 7512810 | March 2009 | Ryan |
| 7539867 | May 2009 | Bolosky et al. |
| 7555558 | June 2009 | Kenrich et al. |
| 7562223 | July 2009 | Ragnet et al. |
| 7562232 | July 2009 | Zuili et al. |
| 7565683 | July 2009 | Huang et al. |
| 7577838 | August 2009 | Rossmann |
| 7580919 | August 2009 | Hannel et al. |
| 7594262 | September 2009 | Hanzlik et al. |
| 7614077 | November 2009 | Brew et al. |
| 7631184 | December 2009 | Ryan |
| 7681034 | March 2010 | Lee et al. |
| 7698230 | April 2010 | Brown et al. |
| 7702909 | April 2010 | Vainstein |
| 7703140 | April 2010 | Nath et al. |
| 7707427 | April 2010 | Kenrich et al. |
| 7729995 | June 2010 | Alain et al. |
| 7730543 | June 2010 | Nath et al. |
| 7748045 | June 2010 | Kenrich et al. |
| RE41546 | August 2010 | Vainstein |
| 7836310 | November 2010 | Gutnik |
| 7890990 | February 2011 | Vainstein et al. |
| 7913311 | March 2011 | Alain et al. |
| 7921284 | April 2011 | Kinghorn et al. |
| 7921288 | April 2011 | Hildebrand |
| 7921450 | April 2011 | Vainstein et al. |
| 7930756 | April 2011 | Crocker et al. |
| 7950066 | May 2011 | Zuili |
| 8006280 | August 2011 | Hildebrand et al. |
| 8065713 | November 2011 | Vainstein et al. |
| 8176334 | May 2012 | Vainstein |
| 8707034 | April 2014 | Ryan |
| 2001/0000265 | April 2001 | Schreiber et al. |
| 2001/0011254 | August 2001 | Clark |
| 2001/0018743 | August 2001 | Morishita |
| 2001/0021255 | September 2001 | Ishibashi |
| 2001/0021926 | September 2001 | Schneck et al. |
| 2001/0023421 | September 2001 | Numao et al. |
| 2001/0032181 | October 2001 | Jakstadt et al. |
| 2001/0033611 | October 2001 | Grimwood et al. |
| 2001/0034839 | October 2001 | Karjoth et al. |
| 2001/0037290 | November 2001 | Lai |
| 2001/0042110 | November 2001 | Furusawa et al. |
| 2001/0044903 | November 2001 | Yamamoto et al. |
| 2001/0056541 | December 2001 | Matsuzaki et al. |
| 2001/0056550 | December 2001 | Lee |
| 2002/0003886 | January 2002 | Hillegass et al. |
| 2002/0004902 | January 2002 | Toh et al. |
| 2002/0007335 | January 2002 | Millard et al. |
| 2002/0007340 | January 2002 | Isaf |
| 2002/0010679 | January 2002 | Felsher |
| 2002/0013772 | January 2002 | Peinado |
| 2002/0016910 | February 2002 | Wright |
| 2002/0016921 | February 2002 | Olsen et al. |
| 2002/0016922 | February 2002 | Richards et al. |
| 2002/0023208 | February 2002 | Jancula |
| 2002/0023213 | February 2002 | Walker et al. |
| 2002/0026321 | February 2002 | Faris et al. |
| 2002/0027886 | March 2002 | Fischer et al. |
| 2002/0029340 | March 2002 | Pensak et al. |
| 2002/0031230 | March 2002 | Sweet et al. |
| 2002/0035624 | March 2002 | Kim |
| 2002/0036984 | March 2002 | Chiussi et al. |
| 2002/0041391 | April 2002 | Bannai |
| 2002/0042756 | April 2002 | Kumar et al. |
| 2002/0046350 | April 2002 | Lordemann et al. |
| 2002/0049903 | April 2002 | Ussery et al. |
| 2002/0050098 | May 2002 | Chan |
| 2002/0052796 | May 2002 | Tadokoro et al. |
| 2002/0052981 | May 2002 | Yasuda |
| 2002/0056042 | May 2002 | Van Der Kaay et al. |
| 2002/0059144 | May 2002 | Meffert et al. |
| 2002/0062240 | May 2002 | Morinville |
| 2002/0062245 | May 2002 | Niu et al. |
| 2002/0062451 | May 2002 | Scheidt et al. |
| 2002/0069077 | June 2002 | Brophy et al. |
| 2002/0069272 | June 2002 | Kim et al. |
| 2002/0069363 | June 2002 | Winburn |
| 2002/0073320 | June 2002 | Rinkevich et al. |
| 2002/0077986 | June 2002 | Kobata et al. |
| 2002/0077988 | June 2002 | Sasaki et al. |
| 2002/0078239 | June 2002 | Howard et al. |
| 2002/0078361 | June 2002 | Giroux et al. |
| 2002/0087479 | July 2002 | Malcolm |
| 2002/0089602 | July 2002 | Sullivan |
| 2002/0091532 | July 2002 | Viets et al. |
| 2002/0091745 | July 2002 | Ramamurthy et al. |
| 2002/0091928 | July 2002 | Bouchard et al. |
| 2002/0093527 | July 2002 | Sherlock et al. |
| 2002/0099947 | July 2002 | Evans |
| 2002/0111885 | August 2002 | Geiger et al. |
| 2002/0112035 | August 2002 | Carey et al. |
| 2002/0112045 | August 2002 | Nirkhe et al. |
| 2002/0112048 | August 2002 | Gruyer et al. |
| 2002/0112168 | August 2002 | Filipi-Martin et al. |
| 2002/0116649 | August 2002 | Goshima |
| 2002/0120851 | August 2002 | Clarke |
| 2002/0124180 | September 2002 | Hagman |
| 2002/0129158 | September 2002 | Zhang et al. |
| 2002/0129235 | September 2002 | Okamoto et al. |
| 2002/0131601 | September 2002 | Ninomiya et al. |
| 2002/0133500 | September 2002 | Arlein et al. |
| 2002/0133699 | September 2002 | Pueschel |
| 2002/0138437 | September 2002 | Lewin et al. |
| 2002/0138571 | September 2002 | Trinon et al. |
| 2002/0138726 | September 2002 | Samson et al. |
| 2002/0138762 | September 2002 | Horne |
| 2002/0143710 | October 2002 | Liu |
| 2002/0143906 | October 2002 | Tormasov et al. |
| 2002/0150239 | October 2002 | Carny et al. |
| 2002/0152302 | October 2002 | Motoyama et al. |
| 2002/0154635 | October 2002 | Liu |
| 2002/0156726 | October 2002 | Kleckner et al. |
| 2002/0157016 | October 2002 | Russell et al. |
| 2002/0162104 | October 2002 | Raike et al. |
| 2002/0165870 | November 2002 | Chakraborty et al. |
| 2002/0165960 | November 2002 | Chan |
| 2002/0166053 | November 2002 | Wilson |
| 2002/0169866 | November 2002 | Lim |
| 2002/0169963 | November 2002 | Seder et al. |
| 2002/0169965 | November 2002 | Hale et al. |
| 2002/0172367 | November 2002 | Mulder et al. |
| 2002/0174030 | November 2002 | Praisner et al. |
| 2002/0174109 | November 2002 | Chandy et al. |
| 2002/0174415 | November 2002 | Hines |
| 2002/0176572 | November 2002 | Ananth |
| 2002/0178271 | November 2002 | Graham et al. |
| 2002/0184217 | December 2002 | Bisbee et al. |
| 2002/0184488 | December 2002 | Amini et al. |
| 2002/0194484 | December 2002 | Bolosky et al. |
| 2002/0198798 | December 2002 | Ludwig et al. |
| 2003/0005168 | January 2003 | Leerssen et al. |
| 2003/0009685 | January 2003 | Choo et al. |
| 2003/0014391 | January 2003 | Evans et al. |
| 2003/0018753 | January 2003 | Seki |
| 2003/0023559 | January 2003 | Choi et al. |
| 2003/0023677 | January 2003 | Morison Zuill et al. |
| 2003/0026431 | February 2003 | Hammersmith |
| 2003/0028610 | February 2003 | Pearson |
| 2003/0033528 | February 2003 | Ozog et al. |
| 2003/0037029 | February 2003 | Holenstein et al. |
| 2003/0037133 | February 2003 | Owens |
| 2003/0037237 | February 2003 | Abgrall et al. |
| 2003/0037253 | February 2003 | Blank et al. |
| 2003/0046176 | March 2003 | Hynes |
| 2003/0046238 | March 2003 | Nonaka et al. |
| 2003/0046270 | March 2003 | Leung et al. |
| 2003/0050919 | March 2003 | Brown et al. |
| 2003/0051039 | March 2003 | Brown et al. |
| 2003/0051148 | March 2003 | Garney |
| 2003/0056139 | March 2003 | Murray et al. |
| 2003/0061482 | March 2003 | Emmerichs |
| 2003/0061506 | March 2003 | Cooper |
| 2003/0074580 | April 2003 | Knouse et al. |
| 2003/0078959 | April 2003 | Yeung et al. |
| 2003/0079120 | April 2003 | Hearn et al. |
| 2003/0079175 | April 2003 | Limantsev |
| 2003/0081773 | May 2003 | Sugahara et al. |
| 2003/0081784 | May 2003 | Kallahalla et al. |
| 2003/0081785 | May 2003 | Boneh et al. |
| 2003/0081787 | May 2003 | Kallahalla et al. |
| 2003/0081790 | May 2003 | Kallahalla et al. |
| 2003/0088517 | May 2003 | Medoff |
| 2003/0088783 | May 2003 | DiPierro |
| 2003/0093250 | May 2003 | Goebel |
| 2003/0093457 | May 2003 | Goldick |
| 2003/0093467 | May 2003 | Anderson |
| 2003/0095552 | May 2003 | Bernhard et al. |
| 2003/0099248 | May 2003 | Speciner |
| 2003/0101072 | May 2003 | Dick et al. |
| 2003/0110169 | June 2003 | Zuili |
| 2003/0110266 | June 2003 | Rollias et al. |
| 2003/0110280 | June 2003 | Hinchliffe et al. |
| 2003/0110397 | June 2003 | Supramaniam et al. |
| 2003/0115146 | June 2003 | Lee et al. |
| 2003/0115218 | June 2003 | Bobbitt et al. |
| 2003/0115570 | June 2003 | Bisceglia |
| 2003/0120601 | June 2003 | Ouye et al. |
| 2003/0120684 | June 2003 | Zuili et al. |
| 2003/0126434 | July 2003 | Lim et al. |
| 2003/0132949 | July 2003 | Fallon et al. |
| 2003/0154296 | August 2003 | Noguchi et al. |
| 2003/0154381 | August 2003 | Ouye |
| 2003/0154396 | August 2003 | Godwin et al. |
| 2003/0154401 | August 2003 | Hartman et al. |
| 2003/0159048 | August 2003 | Matsumoto et al. |
| 2003/0159066 | August 2003 | Staw et al. |
| 2003/0163704 | August 2003 | Dick et al. |
| 2003/0165117 | September 2003 | Garcia-Luna-Aceves et al. |
| 2003/0172280 | September 2003 | Scheidt et al. |
| 2003/0177070 | September 2003 | Viswanath et al. |
| 2003/0177378 | September 2003 | Wittkotter |
| 2003/0182310 | September 2003 | Charnock et al. |
| 2003/0182579 | September 2003 | Leporini et al. |
| 2003/0182584 | September 2003 | Banes et al. |
| 2003/0185240 | October 2003 | Vuong |
| 2003/0191938 | October 2003 | Woods et al. |
| 2003/0196096 | October 2003 | Sutton |
| 2003/0197729 | October 2003 | Denoue et al. |
| 2003/0200202 | October 2003 | Hsiao et al. |
| 2003/0204692 | October 2003 | Tamer et al. |
| 2003/0208485 | November 2003 | Castellanos |
| 2003/0217264 | November 2003 | Martin et al. |
| 2003/0217266 | November 2003 | Epp et al. |
| 2003/0217281 | November 2003 | Ryan |
| 2003/0217282 | November 2003 | Henry |
| 2003/0217333 | November 2003 | Smith et al. |
| 2003/0220999 | November 2003 | Emerson |
| 2003/0222141 | December 2003 | Vogler et al. |
| 2003/0226013 | December 2003 | Dutertre |
| 2003/0229795 | December 2003 | Kunigkeit et al. |
| 2003/0233650 | December 2003 | Zaner et al. |
| 2004/0015723 | January 2004 | Pham et al. |
| 2004/0022390 | February 2004 | McDonald et al. |
| 2004/0025037 | February 2004 | Hair |
| 2004/0039781 | February 2004 | LaVallee et al. |
| 2004/0041845 | March 2004 | Alben et al. |
| 2004/0044908 | March 2004 | Markham et al. |
| 2004/0049702 | March 2004 | Subramaniam et al. |
| 2004/0064507 | April 2004 | Sakata et al. |
| 2004/0064710 | April 2004 | Vainstein |
| 2004/0068524 | April 2004 | Aboulhosn et al. |
| 2004/0068664 | April 2004 | Nachenberg et al. |
| 2004/0073660 | April 2004 | Toomey |
| 2004/0073718 | April 2004 | Johannessen et al. |
| 2004/0078423 | April 2004 | Satyavolu et al. |
| 2004/0088548 | May 2004 | Smetters et al. |
| 2004/0098580 | May 2004 | DeTreville |
| 2004/0103202 | May 2004 | Hildebrand et al. |
| 2004/0103280 | May 2004 | Balfanz et al. |
| 2004/0117371 | June 2004 | Bhide et al. |
| 2004/0131191 | July 2004 | Chen et al. |
| 2004/0133544 | July 2004 | Kiessig et al. |
| 2004/0158586 | August 2004 | Tsai |
| 2004/0186845 | September 2004 | Fukui |
| 2004/0193602 | September 2004 | Liu et al. |
| 2004/0193905 | September 2004 | Lirov et al. |
| 2004/0193912 | September 2004 | Li et al. |
| 2004/0199514 | October 2004 | Rosenblatt et al. |
| 2004/0205576 | October 2004 | Chikirivao et al. |
| 2004/0215956 | October 2004 | Venkatachary et al. |
| 2004/0215962 | October 2004 | Douceur et al. |
| 2004/0243853 | December 2004 | Swander et al. |
| 2004/0254884 | December 2004 | Haber et al. |
| 2005/0021467 | January 2005 | Franzdonk |
| 2005/0021629 | January 2005 | Cannata et al. |
| 2005/0028006 | February 2005 | Leser et al. |
| 2005/0039034 | February 2005 | Doyle et al. |
| 2005/0050098 | March 2005 | Barnett |
| 2005/0071275 | March 2005 | Vainstein et al. |
| 2005/0071657 | March 2005 | Ryan |
| 2005/0071658 | March 2005 | Nath et al. |
| 2005/0080720 | April 2005 | Betz et al. |
| 2005/0081029 | April 2005 | Thornton et al. |
| 2005/0086531 | April 2005 | Kenrich |
| 2005/0091289 | April 2005 | Shappell et al. |
| 2005/0091484 | April 2005 | Thornton et al. |
| 2005/0097061 | May 2005 | Shapiro et al. |
| 2005/0120199 | June 2005 | Carter |
| 2005/0138371 | June 2005 | Supramaniam |
| 2005/0138383 | June 2005 | Vainstein |
| 2005/0168766 | August 2005 | Troyansky et al. |
| 2005/0177716 | August 2005 | Ginter et al. |
| 2005/0177858 | August 2005 | Ueda |
| 2005/0198326 | September 2005 | Schlimmer et al. |
| 2005/0223242 | October 2005 | Nath |
| 2005/0223414 | October 2005 | Kenrich et al. |
| 2005/0235154 | October 2005 | Serret-Avila |
| 2005/0256909 | November 2005 | Aboulhosn et al. |
| 2005/0268033 | December 2005 | Ogasawara et al. |
| 2005/0273600 | December 2005 | Seeman |
| 2005/0283610 | December 2005 | Serret-Avila et al. |
| 2005/0288961 | December 2005 | Tabrizi |
| 2006/0005021 | January 2006 | Torrubia-Saez |
| 2006/0011400 | January 2006 | Thomas |
| 2006/0075258 | April 2006 | Adamson et al. |
| 2006/0075465 | April 2006 | Ramanathan et al. |
| 2006/0093150 | May 2006 | Reddy et al. |
| 2006/0101285 | May 2006 | Chen et al. |
| 2006/0149407 | July 2006 | Markham et al. |
| 2006/0168147 | July 2006 | Inoue et al. |
| 2006/0184637 | August 2006 | Hultgren et al. |
| 2006/0230437 | October 2006 | Boyer et al. |
| 2006/0277316 | December 2006 | Wang et al. |
| 2007/0006214 | January 2007 | Dubal et al. |
| 2007/0067837 | March 2007 | Schuster |
| 2007/0083575 | April 2007 | Leung et al. |
| 2007/0192478 | August 2007 | Louie et al. |
| 2007/0193397 | August 2007 | Hwan |
| 2007/0294368 | December 2007 | Bomgaars et al. |
| 2008/0075126 | March 2008 | Yang |
| 2009/0254843 | October 2009 | Van Wie et al. |
| 2010/0047757 | February 2010 | McCurry et al. |
| 2010/0199088 | August 2010 | Nath |
| 2017/0118214 | April 2017 | Vainstein et al. |
| 0 672 991 | Sep 1995 | EP | |||
| 0 674 253 | Sep 1995 | EP | |||
| 0 809 170 | Nov 1997 | EP | |||
| 0 913 966 | May 1999 | EP | |||
| 0 913 967 | May 1999 | EP | |||
| 0 950 941 | Oct 1999 | EP | |||
| 0 950 941 | Oct 1999 | EP | |||
| 1 107 504 | Jun 2001 | EP | |||
| 1 107 504 | Jun 2001 | EP | |||
| 1 130 492 | Sep 2001 | EP | |||
| 1 154 348 | Nov 2001 | EP | |||
| 1 324 565 | Jul 2003 | EP | |||
| 2 328 047 | Feb 1999 | GB | |||
| 2001-036517 | Feb 2001 | JP | |||
| 2006-244044 | Sep 2006 | JP | |||
| 2009-020720 | Jan 2009 | JP | |||
| WO 96/41288 | Dec 1996 | WO | |||
| WO 00/56028 | Sep 2000 | WO | |||
| WO 01/61438 | Aug 2001 | WO | |||
| WO 01/63387 | Aug 2001 | WO | |||
| WO 01/77783 | Oct 2001 | WO | |||
| WO 01/78285 | Oct 2001 | WO | |||
| WO 01/84271 | Nov 2001 | WO | |||
| WO 01/63387 | Aug 2007 | WO | |||
| WO 01/63387 | Aug 2007 | WO | |||
Other References
|
Adobe Acrobat 5.0 Classroom in a Book, Adobe Press, Jun. 26, 2001, pp. 1-4. cited by applicant . Adobe Acrobat Security Settings, Acrobat 7.0, Nov. 15, 2004, pp. 1-4. cited by applicant . "Affect," The American Heritage Dictionary of the English Language, Fourth Edition, Houghton Mifflin Company, 2002. Retrieved May 4, 2006 from http://dictionary.reference.com/search?q=affect, 9 pages. cited by applicant . Boneh et al., "IBE Secure E-mail," Stanford University, Apr. 8, 2002, http://crypto.stanford.edu/ibe/, 3 pages. cited by applicant . Boneh, D., et al., "Identity-Based Encryption from the Weil Pairing", CRYPTO '01 Proceedings of the 21st Annual International Cryptology Conference on Advances in Cryptology, Springer-Verlag London, UK, Oct. 2001, 27 pages. cited by applicant . "Columns," Microsoft TechNet http://web.archive.org/web/20021014225142/www.microsoft.com/techneUcolumn- s/default.asp Oct. 14, 2002, Retrieved from web.archive.org on Dec. 3, 2009, 1 page. cited by applicant . "Column Archives," Microsoft TechNet, Professor Windows, technet.microsoft.com/menus/library/bb878075.aspx, retrieved on Dec. 3, 2009, 3 pages. cited by applicant . Curtis, et al., "Securing the Global, Remote, Mobile User," 1999 John Wiley & Sons, Ltd., Int. J. Network Mgmt. 9, pp. 9-21. cited by applicant . Definition of markup, in Foldoc (Free on Line Dictionary of Computing), 2010, 1 page. cited by applicant . "Encrypting File System," from MSDN Oct. 2001 version, exact publication date is unknown but believed prior to Dec. 12, 2001, 2 pages. cited by applicant . English language translation (unverified, machine-generated) of Japanese Patent Publication No. 2009-020720, Japanese Patent Office, Patent & Utility Model Gazette DB, 2009, 36 pages. cited by applicant . Examination Report, completion date Jun. 18, 2008, for European Patent Application No. EP 02 258 532.7-1244, 6 pgs. cited by applicant . "eXPeriencing Remote Assistance" Microsoft TechNet--Professor Windows Oct. 2002 Oct. 15, 2002 http://web.archive.org/web/20021015165237/www.microsoft.com/techneUcolumn- s/profwin/, Retrieved from web.archive.org on Dec. 3, 2009, 18 pages. cited by applicant . Expiration Mechanism for Chipcards, IBM Technical Disclosure Bulletin, Oct. 1, 2001, UK, 1 page. cited by applicant . "Features of EFS" from MSDN Oct. 2001 version, exact publication date is unknown but believed prior to Dec. 12, 2001, 2 pages. cited by applicant . "How EFS works," from MSDN Oct. 2001 version, exact publication date is unknown but believed prior to Dec. 12, 2001, 4 pages. cited by applicant . "Inside Encrypting file system," Part 1, from MSDN Oct. 2001 version, exact publication date is unknown but believed prior to Dec. 12, 2001, 6 pages. cited by applicant . "Inside Encrypting file system," Part 2, from MSDN Oct. 2001 version, exact publication date is unknown but believed prior to Dec. 12, 2001, 7 pages. cited by applicant . Juvva et al., "A Real-Time Push-Pull Communications Model for Distributed Real-Time and Multimedia Systems," CMU-CS-99-107, School of Computer Sciences, Carnegie Mellon University, Pittsburgh, PA, Jan. 1999, 25 pages. cited by applicant . McDaniel et al. "AntigonE: A Flexible Framework for Secure Group Communication," Proceedings of the 8th USENIX Security Symposium, Aug. 23, 1999, 15 pages. cited by applicant . Microsoft Press Computer Dictionary, 1997, Microsoft Press, Third Edition, 3 pages. cited by applicant . Microsoft Windows 2000 server. Windows 2000 Group Policy White Paper, 2000, 137 pages. cited by applicant . "Migrating Accounts From Windows NT 4.0 Domains to Windows 2000," Microsoft TechNet--Professor Windows Apr. 2002, http://web.archive.org/web/20020415004611/www. m icrosoft.com/tech netlcolumns/profwin/, Apr. 15, 2002, 4 pages. cited by applicant . Office Action, dated May 10, 2005, for European Patent Application No. 02258532.7, 6 pages. cited by applicant . Office Action, dated Dec. 5, 2006, for European Patent Application No. 02258532.7, European Patent Office, 5 pags. cited by applicant . "Scripting Your Windows 2000 Network, Part 1" Microsoft TechNet--Professor Windows Jun. 2002, http://web.archive.org/web/20020622055532/www.microsoft.com/techneUcolumn- s/profwin/Retrieved from web.archive.org on Dec. 3, 2009, 4 pages. cited by applicant . Search Report, completion date Apr. 14, 2005, for European Patent Application No. EP 02 25 8533, 2 pages. cited by applicant . Search Report, completion date Jul. 6, 2005, for European Patent Application No. EP 02 25 8529, 4 pages. cited by applicant . Search Report, completion date Mar. 16, 2005, for European Patent Application No. EP 02 25 8534, 2 pages. cited by applicant . Search Report, completion date Mar. 2, 2005, for European Patent Application No. EP 02 25 8535, 2 pages. cited by applicant . Search Report, completion date Mar. 3, 2005, for European Patent Application No. EP 02 25 8537, 2 pages. cited by applicant . Search Report, completion date May 12, 2005, for European Patent Application No. EP 02 25 8539, 2 pages. cited by applicant . Search Report, completion date May 8, 2003, for European Patent Application No. EP 02 25 8530, 2 pages. cited by applicant . Search Report, completion date May 8, 2003, for European Patent Application No. EP 02 25 8540, 2 pages. cited by applicant . Search Report, completion date Oct. 2, 2003, for European Patent Application No. EP 02 25 8531, 2 pages. cited by applicant . Search Report, completion date Oct. 8, 2003, for European Patent Application No. EP 02 25 8536, 2 pages. cited by applicant . "Secure Sockets Layer (SSL): How it Works," Verisign, http://www.verisign.com/ss/ssl-information-center/how-ssl-security-works, pp. 1-2. cited by applicant . "Security Options". Dec. 20, 2001. DC & Co. pp. 1-2. cited by applicant . "Security with Encrypting File System," from MSDN Oct. 2001 version, exact publication date is unknown but believed prior to Dec. 12, 2001, 2 pages. cited by applicant . Stallings, William, "Cryptography and Network Security: Principles and Practice," 1999, pp. 333-337, Second Edition, Prentice Hall, Upper Saddle River, New Jersey. cited by applicant . Symantec. Norton Antivirus Corporate Edition Implementation Guide, 1999, 42 pages. cited by applicant . "WayBack Machine" web.archive.org, http://web.archive.org/web/*/http://www.microsoft.com/technetlcolumns/pro- fwin/, Retrieved on Dec. 3, 2009, 1 page. cited by applicant . "Windows 2000 EFS" in the Apr. 1999 issue of Windows NT magazine, 1 page. cited by applicant . Boneh et al., "Hierarchical Identity Based Encryption with Constant Size Ciphertext," Advances in Cryptology--EUROCRYPT 2005, vol. 3493, Jun. 20, 2005, pp. 440-456. cited by applicant . English language abstract for Japanese Appl. Pub. No. 2006-244044, published Sep. 14, 2006, 1 pg. cited by applicant . English language abstract for Japanese Appl. Pub. No. 2009-020720, published Jan. 29, 2009, 1 pg. cited by applicant . English language translation (unverified, machine-generated) of Japanese Patent Publication No. JP 2006-244044, Japanese Patent Office, Patent & Utility Model Gazette DB, 2006, 15 pages. cited by applicant . Botha et al., "Access Control in Document-Centric Workflow Systems--An Agent--Based Approach," Computers & Security, vol. 20:6, Sep. 2001, pp. 525-532. cited by applicant . Botha et al., "Separation of Duties for Access Control Enforcement in Workflow Environments," IBM, 2001, 17 pages. cited by applicant . English language abstract for Japanese Appl. Pub. No. 2001-036517, filed Sep. 2, 2001, 1 pg. cited by applicant . U.S. Appl. No. 10/028,397, Zuili, "Method and System for restricting use of a clipboard application," filed Dec. 21, 2001, 48 pages. cited by applicant . U.S. Appl. No. 10/074,804, entitled "Secured Data Format for Access Control," Garcia, Feb. 12, 2002, 108 pgs. cited by applicant . U.S. Appl. No. 10/074,825, entitled "Method and Apparatus for Accessing Secured Electronic Data Off-line," Lee et al., Feb. 12, 2002, 108 pgs. cited by applicant . U.S. Appl. No. 10/074,996, entitled "Method and Apparatus for Securing Electronic Data," Lee et al., Feb. 12, 2002, 111 pgs. cited by applicant . U.S. Appl. No. 10/075,194, entitled "System and Method for Providing Multi-location Access Management to Secured Items," Vainstein et al., Feb. 12, 2002, 110 pgs. cited by applicant . U.S. Appl. No. 10/105,532, entitled "System and Method for Providing Different Levels of Key Security for Controlling Access to Secured Items," Hildebrand et al., Mar. 20, 2002, 86 pgs. cited by applicant . U.S. Appl. No 10/159,220, entitled "Method and system for protecting electronic data in enterprise environment," Kinghorn, May 31, 2002, 62 pages. cited by applicant . U.S. Appl. No. 10/186,203, entitled "Method and System for Implementing Changes to Security Policies in a Distributed Security System," Huang, Jun. 26, 2002, 65 pgs. cited by applicant . U.S. Appl. No. 10/201,756, entitled "Managing Secured Files in Designated Locations," Alain, Jul. 22, 2002, 121 pgs. cited by applicant . U.S. Appl. No. 10/206,737, entitled "Method and System for Updating Keys in a Distributed Security System" (now abandoned), Hildebrand, Jul. 26, 2002, 60 pgs. cited by applicant . U.S. Appl. No. 10/242,185, entitled "Method and system for fault-tolerant transfer of files across a network," Ryan, Sep. 11, 2002, 33 pgs. cited by applicant . U.S. Appl. No. 10/246,079, entitled "Security System for Generating Keys from Access rules in a Decentralized Manner and Methods Therefor," Hildebrand, Sep. 17, 2002, 78 pgs. (now U.S. Patent No. 8,006,280, issued Aug. 23, 2011). cited by applicant . U.S. Appl. No. 10/259,075, entitled "Effectuating Access Policy Changes to Designated Places for Secured Files," Crocker, Sep. 27, 2002, 60 pgs. cited by applicant . U.S. Appl. No. 10/286,524, entitled "Security system that uses indirect password-based encryption," Gutnik, Nov. 1, 2002, 38 pgs. cited by applicant . U.S. Appl. No. 10/286,575, entitled "Method and Archictecture for Providing Access to Secured Data from Non-Secured Clients," Vainstein, Nov. 1, 2002, 46 pgs. cited by applicant . U.S. Appl. No. 10/295,363, entitled "Security Using Indirect Key Generation from Access Rules and Methods Therefor," Vainstein, Nov. 15, 2002, 70 pgs. cited by applicant . U.S. Appl. No. 10/325,013, entitled "Hybrid systems for securing digital assets," Rossman, Dec. 20, 2002, 45 pages. cited by applicant . U.S. Appl. No. 10/325,102, entitled "Method and apparatus for securing/unsecuring files by file crawling," Prakash, Dec. 20, 2002, 76 pages. cited by applicant . U.S. Appl. No. 10/327,320, entitled "Security system with staging capabilities," Vainstein, Dec. 20, 2002, 39 pgs. cited by applicant . U.S. Appl. No. 10/368,277, Michael Michio Ouye, "Methods and Systems for Tracking User Actions on Files," filed Feb. 18, 2003, 35 pages. cited by applicant . U.S. Appl. No. 10/404,566, entitled "Multi-level cryptographic transformations for securing digital assets," Crocker et al., Mar. 31, 2003, 65 pages. cited by applicant . U.S. Appl. No. 10/405,587, entitled "Method and system for securing digital assets using content type designations," Nath, Apr. 1, 2003, 49 pages. cited by applicant . U.S. Appl. No. 10/448,806, entitled "Method and System for Using Remote Headers to Secure Electronic Files," Ryan, May 30, 2003, 35 pgs. cited by applicant . U.S. Appl. No. 10/610,832, entitled "Method and system for enabling users of a group shared across mulitple file security systems to access secured files," Ryan, Jun. 30, 2003, 33 pgs. cited by applicant . U.S. Appl. No. 10/642,041, entitled "Method and system for fault-tolerant transfer of files across a network," Kenrich, Aug. 15, 2003, 32 pgs. cited by applicant . U.S. Appl. No. 10/889,685, entitled "Method and Apparatus for Controlling the Speed Ranges of a Machine," Thomas, Jul. 31, 2004, 18 pgs. cited by applicant . U.S. Appl. No. 10/894,493, entitled "Multi-Level File Digest," Kenrich, Jul. 19, 2004. cited by applicant . U.S. Appl. No. 11/797,367, entitled "Method and System for Managing Security Tiers," Vainstein, May 2, 2007, 11 pgs. cited by applicant . U.S. Appl. No. 11/889,310, entitled "Methods and Systems for Providing Access Control to Electronic Data," Rossmann et al., Aug. 10, 2007, 90 pgs. cited by applicant. |
Primary Examiner: Lee; Christopher E.
Attorney, Agent or Firm: Sterne, Kessler, Goldstein & Fox P.L.L.C.
Parent Case Text
CROSS-REFERENCE TO RELATED APPLICATION
This is a Division of U.S. application Ser. No. 10/262,218, filed Sep. 30, 2002, now allowed, which is hereby incorporated by reference in its entirety for all purposes.
U.S. application Ser. No. 10/262,218 is related to U.S. patent application Ser. No. 10/075,194, filed Feb. 12, 2002, now U.S. Pat. No. 8,065,713 issued on Nov. 22, 2011 and entitled "SYSTEM AND METHOD FOR PROVIDING MULTI-LOCATION ACCESS MANAGEMENT TO SECURED ITEMS," which is hereby incorporated by reference in its entirety for all purposes.
Claims
What is claimed is:
1. A system comprising: a server .Iadd.comprising .Iaddend.an access manager configured to.Iadd.:.Iaddend. restrict access to a file of an organization having an internal user responsive to a request for the file, the file comprising a header portion including an access rule that restricts access to the file.[.,.]. and a content portion encrypted by a file key; .Iadd.and determine whether a partner relationship exists between the organization and an external partner;.Iaddend. a database coupled to the server and configured to store an encryption key for use between the internal user and .[.an.]. .Iadd.the .Iaddend.external partner comprising an external user, wherein the access manager is further configured to encrypt the file key, located within security information of the header portion of the file, with the encryption key in response to .[.a.]. .Iadd.determining that the .Iaddend.partner relationship .[.existing.]. .Iadd.exists .Iaddend.between the organization and the external partner and deny the request in response to .Iadd.determining that .Iaddend.the partner relationship .Iadd.does .Iaddend.not .[.existing.]. .Iadd.exist.Iaddend.; and an external access server operatively connected to the server and coupled between the server and a data network, the data network configured to allow the external user use of the external access server, wherein the external access server is configured to permit file exchange between the internal user and the external user via the server.
2. The system of claim 1, wherein file exchange .[.by.]. .Iadd.between .Iaddend.the internal and external users is permitted in response to the internal and external users being members of a common group.
3. The system of claim 1, wherein the encryption key comprises a public-private key pair, and wherein the access manager is configured to encrypt the security information with the public key.
4. The system of claim 1, wherein the server further comprises: a central server; and a local server operatively connected to the central server.
5. The system of claim 1, wherein the data network includes at least a part of an Internet.
6. The system of claim 1, wherein the external user is unaffiliated with the .Iadd.organization comprising the .Iaddend.internal user.
7. The system of claim 1, wherein: the external user and the internal user are members of a common group; and the external user is unable to change group membership and is unable to query group membership to determine members of the common group.
8. A method comprising: maintaining, in a database, an encryption key for use between an organization comprising an internal user and an external partner comprising an external user; receiving, by a server coupled to the database, a request to access a file, the file comprising a header portion including an access rule that restricts access to the filer and a content portion encrypted by a file key; .Iadd.determining whether a partner relationship exists between the organization and the external partner;.Iaddend. encrypting the file key, located within security information of the header portion, with the encryption key in response to .[.a.]. .Iadd.determining that the .Iaddend.partner relationship .[.existing.]. .Iadd.exists .Iaddend.between the organization and the external partner; and denying the request in response to .Iadd.determining that .Iaddend.the partner relationship .Iadd.does .Iaddend.not .[.existing.]. .Iadd.exist.Iaddend..
9. The method of claim 8, further comprising permitting file exchange between the internal user and the external user through an external access server in response to the internal user and the external user being members of a common group.
10. The method of claim 8, further comprising using a public-private key pair as the encryption key.
11. The method of claim 10, further comprising: encrypting the .[.security information.]. .Iadd.file key .Iaddend.with the public key.
12. The method of claim 8, further comprising: communicating, in response to the .[.security information.]. .Iadd.file key .Iaddend.being encrypted, the requested file via a data network.
13. The method of claim 8, wherein the external user is unaffiliated with the organization comprising the internal user.
14. The method of claim 13, further comprising: blocking the external user from changing group membership and querying group membership to determine members of a common group, the common group comprising the internal user and the external user.
15. A computer-readable storage device having instructions stored thereon, execution of which, by a computing device associated with an organization, causes the computing device to perform operations comprising: maintaining an encryption key for use between the organization comprising an internal user and an external partner comprising an external user; receiving a request to access a file at the computing device, the file comprising a header portion including an access rule that restricts access to the file and a content portion encrypted by a file key; .Iadd.determining whether a partner relationship exists between the organization and the external partner;.Iaddend. encrypting the file key, located within security information of the header portion, with the encryption key in response to .[.a.]. .Iadd.determining that the .Iaddend.partner relationship .[.existing.]. .Iadd.exists .Iaddend.between the organization and the external partner; and denying the request in response to .Iadd.determining that .Iaddend.the partner relationship .Iadd.does .Iaddend.not .[.existing.]. .Iadd.exist.Iaddend..
16. The computer-readable storage device of claim 15, the operations further comprising permitting file exchange between the internal user and the external user through an external access server in response to the internal user and the external user being members of a common group.
17. The computer-readable storage device of claim 15, further comprising using a public-private key pair as the encryption key.
18. The computer-readable storage device of claim 17, the operations further comprising: encrypting the .[.security information.]. .Iadd.file key .Iaddend.with the public key.
19. The computer-readable storage device of claim 15, the operations further comprising: communicating, in response to the .[.security information.]. .Iadd.file key .Iaddend.being encrypted, the requested file via a data network.
20. The computer-readable storage device of claim 15, wherein the external user is unaffiliated with the organization comprising the internal user.
.Iadd.21. A system comprising: a server comprising an access manager configured to restrict access to a file of an organization responsive to a request for the file, the file comprising a header portion including an access rule that restricts access to the file, and a content portion encrypted by a file key; a database coupled to the server and configured to store an encryption key associated with an external user, wherein the access manager is further configured to encrypt the file key, located within security information of the header portion of the file, with the encryption key in response to determining that the encryption key associated with the external user is available and deny the request in response to the encryption key not existing; and an external access server operatively connected to the server and coupled between the server and a data network, the data network configured to allow the external user use of the external access server, wherein the external access server is configured to transmit the file to the external user via the data network..Iaddend.
.Iadd.22. The system of claim 21, wherein the encryption key comprises a public-private key pair, and wherein the access manager is configured to encrypt the security information with the public key..Iaddend.
.Iadd.23. The system of claim 21, wherein the server further comprises: a central server; and a local server operatively connected to the central server..Iaddend.
.Iadd.24. The system of claim 21, wherein the data network includes at least a part of an Internet..Iaddend.
.Iadd.25. The system of claim 21, wherein the external user is unaffiliated with the organization..Iaddend.
.Iadd.26. The system of claim 21, wherein the external user is in a partner relationship with an internal user of the organization..Iaddend.
.Iadd.27. The system of claim 21, wherein the access manager is further configured to: decrypt the header portion of the file using the encryption key associated with the external user; and evaluate the access rule against an access privilege of the external user to determine whether to permit access to the file..Iaddend.
Description
BACKGROUND OF THE INVENTION
1. Field of the Invention
The present invention relates to security systems for data and, more particularly, to security systems that protect data in an inter/intra enterprise environment.
2. Description of Related Art
The Internet is the fastest growing telecommunications medium in history. This growth and the easy access it affords have significantly enhanced the opportunity to use advanced information technology for both the public and private sectors. It provides unprecedented opportunities for interaction and data sharing among businesses and individuals. However, the advantages provided by the Internet come with a significantly greater element of risk to the confidentiality and integrity of information. The Internet is an open, public and international network of interconnected computers and electronic devices. Without proper security measures, an unauthorized person or machine may intercept any information traveling across the Internet, and may even get access to proprietary information stored in computers that interconnect to the Internet, but are otherwise generally inaccessible by the public.
As organizations become more dependent on networks for business transactions, data sharing, and everyday communications, their networks have to be increasingly accessible to customers, employees, suppliers, partners, contractors and telecommuters. Unfortunately, as the accessibility increases, so does the exposure of critical data that is stored on the network. Hackers can threaten all kinds of valuable corporate information resources including intellectual property (e.g., trade secrets, software code, and prerelease competitive data), sensitive employee information (e.g., payroll figures and HR records), and classified information (e.g., passwords, databases, customer records, product information, and financial data). Thus data security is becoming increasingly mission-critical.
There are many efforts in progress aimed at protecting proprietary information traveling across the Internet and controlling access to computers carrying the proprietary information. Every day hundreds of thousands of people interact electronically, whether it is through e-mail, e-commerce (business conducted over the Internet), ATM machines or cellular phones. The perpetual increase of information transmitted electronically has led to an increased reliance on cryptography.
In protecting the proprietary information traveling across the Internet, one or more cryptographic techniques are often used to secure a private communication session between two communicating computers on the Internet. Cryptographic techniques provide a way to transmit information across an unsecure communication channel without disclosing the contents of the information to anyone eavesdropping on the communication channel. An encryption process is a cryptographic technique whereby one party can protect the contents of data in transit from access by an unauthorized third party, yet the intended party can read the data using a corresponding decryption process.
Many organizations have deployed firewalls, Virtual Private Networks (VPNs), and Intrusion Detection Systems (IDS) to provide protection. Unfortunately, these various security means have been proven insufficient to reliably protect proprietary information residing on their internal networks. For example, depending on passwords to access sensitive documents from within often causes security breaches when the password of a few characters long is leaked or detected.
Enterprise security solutions secure data within an enterprise premise (e.g., internal networks). Some enterprise security solutions prohibit external users (clients) to have any access to secure data. Unfortunately, such enterprise security solutions are not suitable for use in a collaborative environment in which both regular internal users (e.g., employees) and external users (e.g., consultants) need to access some secured data of the enterprise.
Thus, there is a need for improved approaches to enable file security systems to permit external users to access secured data without compromising the integrity of an enterprise security system.
SUMMARY OF THE INVENTION
The invention relates to an improved system and approaches for exchanging secured files (e.g., documents) between internal users of an organization and external users. A file security system of the organization operates to protect the files of the organization and thus prevents or limits external users from accessing internal documents. Although the external users are unaffiliated with the organization (i.e., not employees or contractors), the external users often have working relationships with internal users. These working relationships (also referred to herein as partner relationships) often present the need for file (document) exchange. According to one aspect of the invention, external users having working relationships with internal users are able to be given limited user privileges within the file security system, such that restricted file (document) exchange is permitted between such internal and external users.
The invention can be implemented in numerous ways, including as a method, system, device, and computer readable medium. Several embodiments of the invention are discussed below.
An embodiment of the present invention provides a system that includes a server including an access manager configured to restrict access to files of an organization and maintain at least encryption keys for internal and external users and an external access server operatively connected to the server and coupled between the server and a data network. The data network is configured to allow the external users use of the external access server. In addition, the external access server is configured to permit file exchange between the internal users and the external users via the server.
Another embodiment of the present invention provides a method that includes restricting access to files in a server including an access manager that restricts access to files of an organization and maintains at least encryption keys for internal and external users, permitting file exchange between the internal users and the external users through an external access server operatively connected to the server and coupled between the server and a data network and using the data network to allow the external users to interact with the external access server.
A further embodiment of the present invention provides a computer-readable storage device having instructions stored thereon, execution of which, by a computing device, causes the computing device to perform operations including restricting access to files in a server, including an access manager that restricts access to files of an organization and maintains at least encryption keys for internal and external users, permitting file exchange between the internal users and the external users through an external access server operatively connected to the server and coupled between the server and a data network and using the data network to allow the external users to interact with the external access server.
Other objects, features, and advantages of the present invention will become apparent upon examining the following detailed description of an embodiment thereof, taken in conjunction with the attached drawings.
BRIEF DESCRIPTION OF THE DRAWINGS
The present invention will be readily understood by the following detailed description in conjunction with the accompanying drawings, wherein like reference numerals designate like structural elements, and in which:
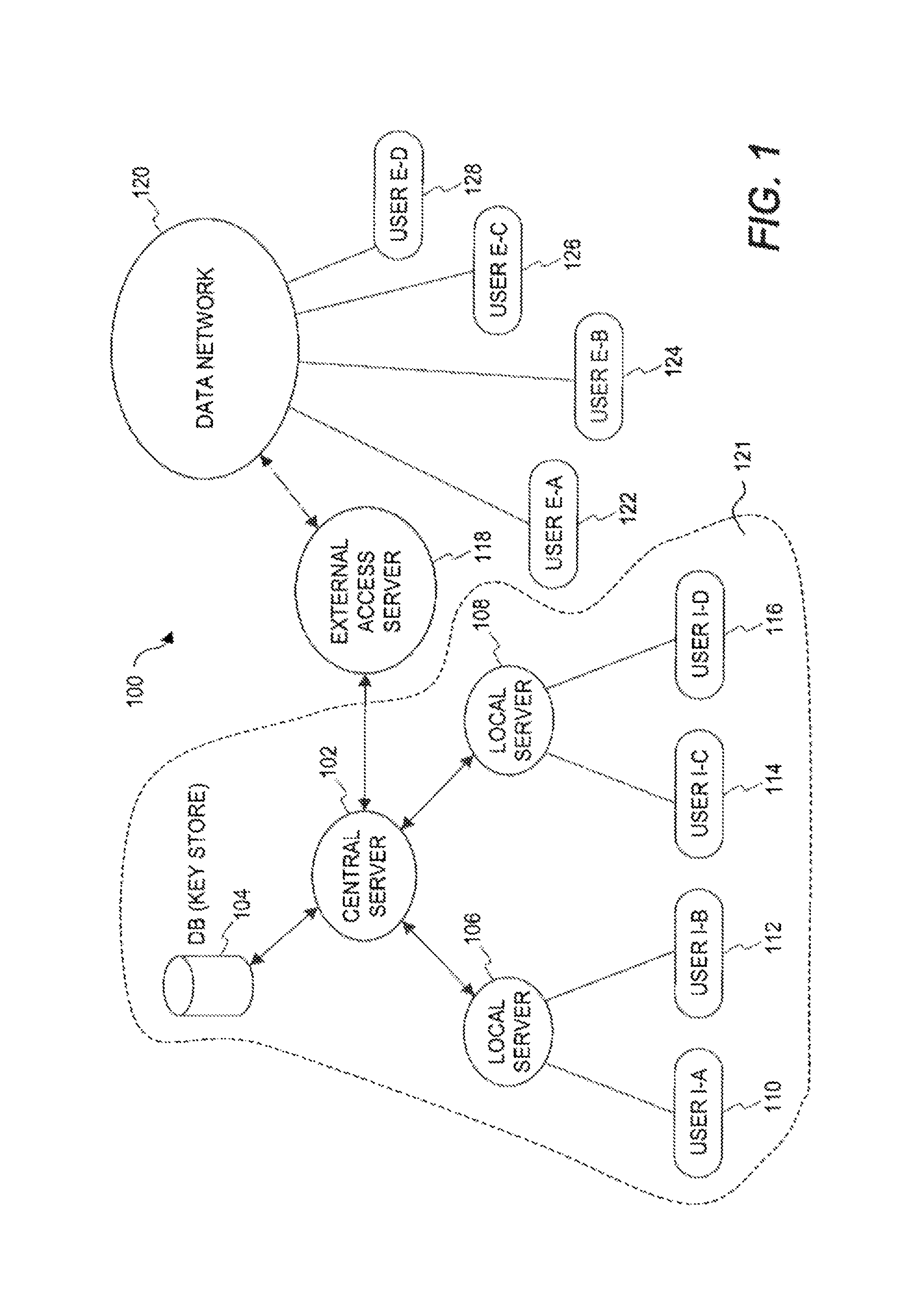
FIG. 1 is a block diagram of a document security system according to one embodiment of the invention.
FIG. 2 is a flow diagram of relationship setup processing according to one embodiment of the invention.
FIG. 3 is a flow diagram of document delivery processing according to one embodiment of the invention.
FIG. 4 is a flow diagram of document access processing according to one embodiment of the invention.
FIG. 5 is a flow diagram of access control processing according to one embodiment of the invention.
FIG. 6 is a flow diagram of client-side document delivery processing according to one embodiment of the invention.
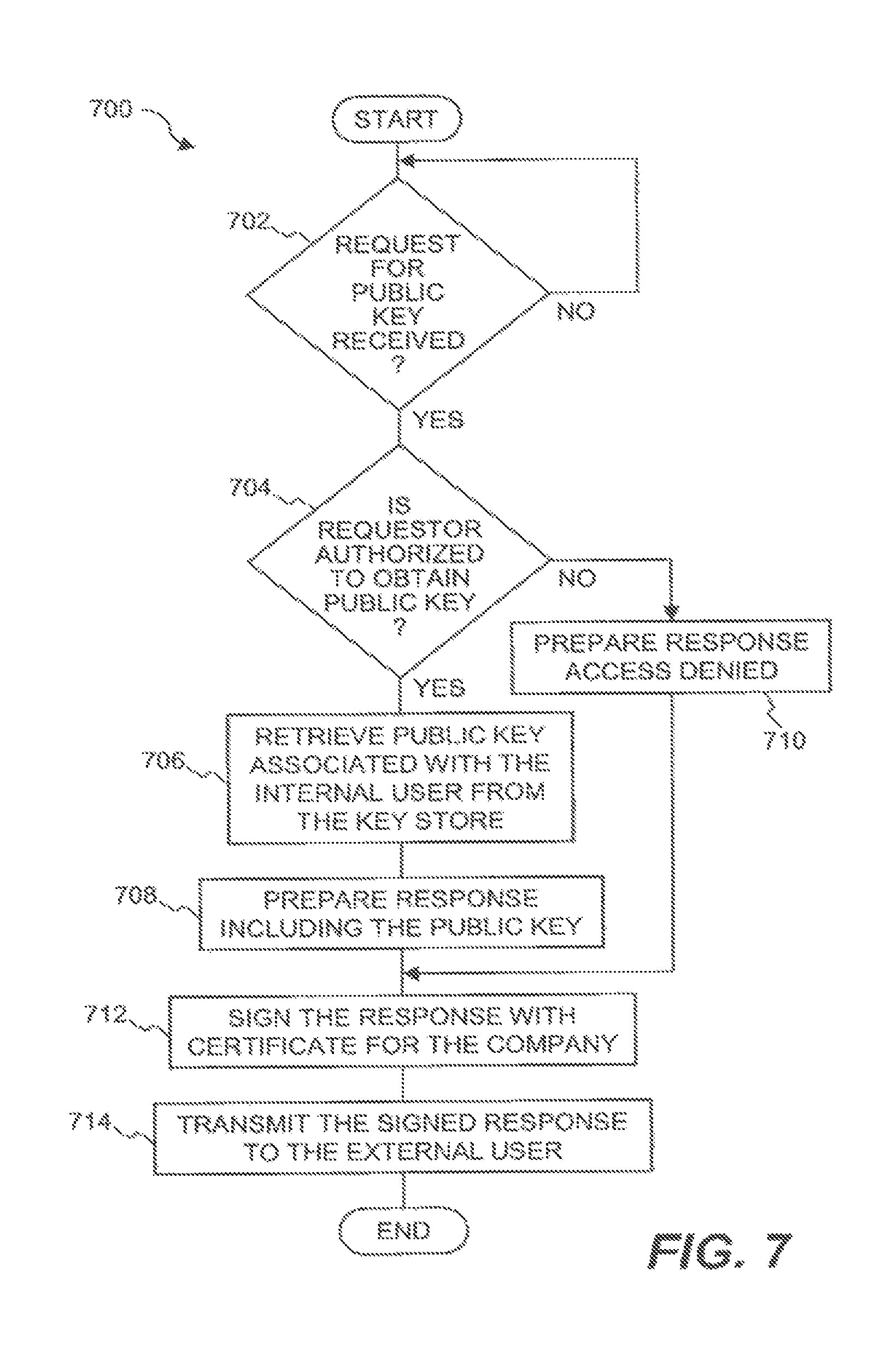
FIG. 7 is a flow diagram of server-side document delivery processing according to one embodiment of the invention.
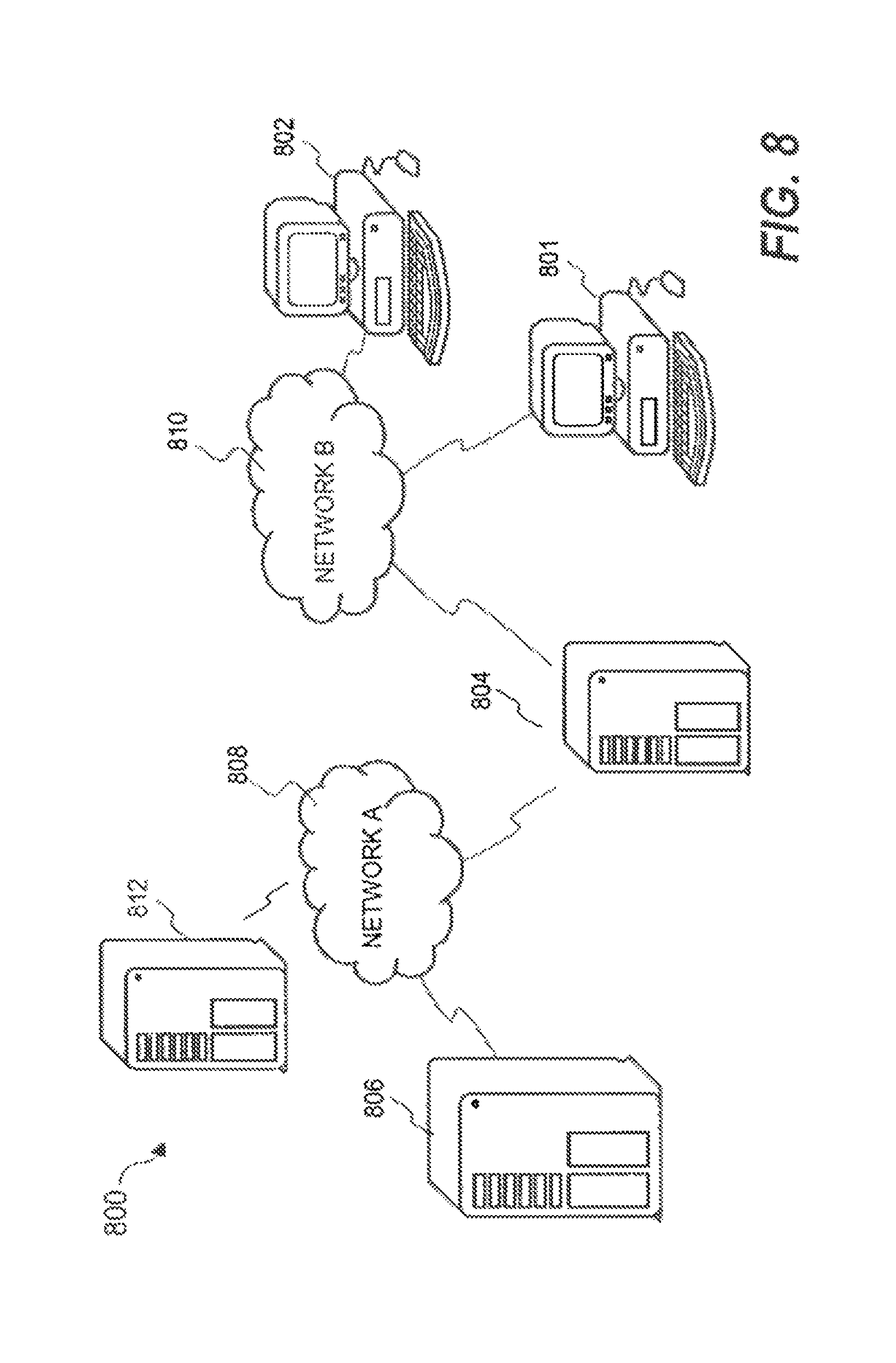
FIG. 8 shows a basic security system in which the invention may be practiced in accordance with one embodiment thereof.
FIG. 9 shows an exemplary data structure of a secured file that may be used in one embodiment of the invention.
DETAILED DESCRIPTION OF THE INVENTION
The invention relates to an improved system and approaches for exchanging secured files (e.g., documents) between internal users of an organization and external users. A file security system of the organization operates to protect the files of the organization and thus prevents or limits external users from accessing internal documents. Although the external users are unaffiliated with the organization (i.e., not employees or contractors), the external users often have working relationships with internal users. These working relationships (also referred to herein as partner relationships) often present the need for file (document) exchange. According to one aspect of the invention, external users having working relationships with internal users are able to be given limited user privileges within the file security system, such that restricted file (document) exchange is permitted between such internal and external users. The invention is suitable for use in an enterprise file security system.
A file security system (or document security system) serves to limit access to files (documents) to authorized users. Often, an organization, such as a company, would use a file security system to limit access to its files (documents). For example, users of a group might be able to access files (documents) pertaining to the group, whereas other users not within the group would not be able to access such files (documents). Such access, when permitted, would allow a user of the group to retrieve a copy of the file (document) via a data network.
As used herein, a user may mean a human user, a software agent, a group of users, member of a group of users, a device and/or application. Besides a human user who needs to access a secured document, a software application or agent sometimes needs to access secured files in order to proceed. Accordingly, unless specifically stated, the "user" as used herein does not necessarily pertain to a human being.
Secured files are files that require one or more keys, passwords, access privileges, etc. to gain access to their content. According to one aspect of the invention, the security is provided through encryption and access rules. The files, for example, can pertain to documents, multimedia files, data, executable code, images and text. In general, a secured file can only be accessed by authenticated users with appropriate access rights or privileges. In one embodiment, each secured file is provided with a header portion and a data portion, where the header portion contains or points to security information. The security information is used to determine whether access to associated data portions of secured files is permitted.
In the following description, numerous specific details are set forth in order to provide a thorough understanding of the present invention. However, it will become obvious to those skilled in the art that the invention may be practiced without these specific details. The description and representation herein are the common meanings used by those experienced or skilled in the art to most effectively convey the substance of their work to others skilled in the art. In other instances, well-known methods, procedures, components, and circuitry have not been described in detail to avoid unnecessarily obscuring aspects of the present invention.
Reference herein to "one embodiment" or "an embodiment" means that a particular feature, structure, or characteristic described in connection with the embodiment can be included in at least one embodiment of the invention. The appearances of the phrase "in one embodiment" in various places in the specification are not necessarily all referring to the same embodiment, nor are separate or alternative embodiments mutually exclusive of other embodiments. Further, the order of blocks in process flowcharts or diagrams representing one or more embodiments of the invention do not inherently indicate any particular order nor imply any limitations in the invention.
Embodiments of the present invention are discussed herein with reference to FIGS. 1-9. However, those skilled in the art will readily appreciate that the detailed description given herein with respect to these figures is for explanatory purposes as the invention extends beyond these limited embodiments.
FIG. 1 is a block diagram of a document security system 100 according to one embodiment of the invention. The document security system 100 is responsible for providing protection of electronic data in an organization and includes a central server 102 that controls the overall operation of the document security system 100. The central server 102 imposes restrictions on the access to secured documents that are stored centrally or locally.
The central server 102 is assisted by a key store 104. Among other things, the key store 104 can store key pairs (public and private keys). In one embodiment, the key store 104 can be implemented in a database that stores key pairs (among other things). The central server 102 is also assisted by local servers 106 and 108 that can provide distributed access control. Various internal users to an organization that are utilizing the document security system 100 interact with the central server 102 and/or one of the local servers 106 and 108. These internal users are represented by users 110-116. As illustrated in the embodiment shown in FIG. 1, user I-A 110 and user I-B 112 are affiliated with the local server 106, and user I-C 114 and user I-D 116 are affiliated with the local server 108. It should be understood, however, that various other arrangements or configurations of local servers and users can be utilized.
The document security system 100 also facilitates access by external users to secured documents that are maintained by the document security system 100. In this regard, the document security system 100 includes an external access server 118. The external access server 118 allows external users to be granted access to some of the secured documents. More particularly, the external access server 118 is coupled between a private network 121 in the document security system 100 and a (public) data network 120 and thus facilitates the access from external users 122-128 to some of the secured files without compromising the security integrity of the document security system 100. The data network 120 is, for example, a global computer network, a wide area network or a local area network. However, since the external users 122-128 are not directly affiliated with the organization, the external users are therefore often given limited access rights to some of the secured documents from machines coupled to the data network 120. Although the document security system 100 shown in FIG. 1 illustrates multiple local servers 106 and 108, multiple internal users 110-116, multiple external users 122-128, it should be recognized that the document security system 100 can, more generally, utilize zero or more local servers, one or more internal users, and one or more external users.
According to one embodiment of the invention, external users are permitted to be members of user groups maintained by the central server 102. As such, the external users are able to exchange certain secured documents with internal users. In one embodiment, the exchange of the secured documents between internal and external users is limited to exchanges between members of a common user group. Despite document exchange capabilities, the external users are unable to perform various operations with respect to user groups that internal users would be able to perform. For example, external users would be unable to change group membership or to query group membership to determine who are the members of the user group. Typically, an external user would be added to a particular user group when a relationship between the organization and the external user is arranged. The exchange of documents between internal users and external users is secured using public key encryption. The document security system 100 manages the storage and accessibility of public and private keys for the internal and external users. The document security system 100 can advantageously minimize the client software needed at the machines utilized by the external users.
The invention facilitates exchange of files (e.g., documents) between internal users of an organization and external users. Although the external users are unaffiliated with the organization (i.e., not employees or contractors), the external users often have working relationships with internal users. These working relationships (also referred to herein as partner relationships) often present the need for file (document) exchange. A file security system (e.g., document security system 100) of the organization operates to protect the files of the organization and thus prevents or limits external users from accessing internal documents. According to the invention, external users having working relationships with internal users are able to be given limited user privileges within a file security system such that restricted file (document) exchange is permitted between such internal and external users.
FIG. 2 is a flow diagram of relationship setup processing 200 according to one embodiment of the invention. The relationship setup processing 200 operates to arrange or set up a partner relationship between a partner and an organization (e.g., company). The organization is typically represented by an internal user or a group of users, and the partner is typically represented by one or more external users.
The relationship setup processing 200 initially establishes 202 a partner relationship between a partner and an organization. In this context, the organization is deemed to protect various documents of the organization and its various internal users. In one embodiment, the organization uses a file (document) security system to protect the various documents. The partner is deemed external to the organization. However, the partner is desirous of exchanging documents with the organization. The partner relationship between the partner and the organization (or between respective members thereof) is such that document exchange is permitted so that mutual business objectives can be efficiently achieved. After the partner relationship has been established 202, key pairs are created 204. The key pairs are used in document exchanges between the partner and the organization (e.g., between respective individuals thereof). For example, each of the partner and the organization would have a public key for encryption, as well as a private key for decryption. For example, to release a document from the organization to the partner, the organization would secure (e.g., encrypt) the document using the public key of the partner and then, upon acquiring the secured document, the partner would unsecure (e.g., decrypt) the secured document using its private key. Similarly, when the partner releases a document to the organization, the partner can secure (e.g., encrypt) the document using the public key of the organization and then, upon acquiring the secured document, the organization can unsecure (e.g., decrypt) the document using its private key. After the key pairs are created 204, the key pairs can be stored 206 to a key store. In one embodiment, the key store is within the file security system. System rights for the partner can then be configured 208. The system rights can be configured to permit limited access privileges to the partner. For example, the partner can be configured to include one or more of its employees within a user group maintained for the organization. After the system rights have been configured 208, the relationship setup processing 200 ends.
According to one embodiment, a partner relationship between an organization and a partner can confer on the partner: (i) query rights, and (ii) rights to get public keys of the organization. For example query right might include the right to get members of a group used by the file security system. However, having the right to get public keys of the organization does not give access to secured documents of the organization.
FIG. 3 is a flow diagram of document delivery processing 300 according to one embodiment of the invention. The document delivery processing 300 serves to deliver a secured document from an internal user to an external user. The internal user is associated with an organization, and the external user is associated with the partner.
The document delivery processing 300 begins with a decision 302 that determines whether a request to release a document to an external user has been received. In one embodiment, the request to release a document to an external user is initiated by an internal user. When the decision 302 determines that a request to release a document to an external user has not yet been received, the document delivery processing 300 awaits such a request. In other words, the document delivery processing 300 can be considered to be invoked when a request to release a document to an external user is received.
After a request to release a document to an external user has been received, a public key associated with the external user is retrieved 304 from a key store. In general, the key store serves to store a plurality of keys utilized by a document security system of the organization. In one embodiment, the key store can be the key store 104 illustrated in FIG. 1. Next, a decision 306 determines whether a public key associated with the external user was available from the key store. In one embodiment, the availability of the public key is controlled by the partner relationship. When the decision 306 determines that the key store does not have a public key associated with the external user, then the document is not permitted to be delivered to the external user and thus the request is denied 308. Here, the particular external user is deemed not authorized to exchange documents with either the organization in general, or an internal user in particular.
On the other hand, when the decision 306 determines that a public key associated with the external user is available from the key store, then at least a portion of security information for the secured document is encrypted 310 using the public key. In one embodiment, the secured document that is to be delivered to the external user has a security information portion (also known as a header portion) and a data portion. The security information portion includes the security information providing restrictive access to the secured document. The security information may include access control components, such as keys or access rules that are utilized to control access to the data portion of the secured document. When the decision 306 determines that a public key is available, then at least a part of the security information portion for the secured document is encrypted 310 using the public key. Then, access control restrictions can be imposed 312 on the external user. The access control restrictions can limit the type, character or extent of access that the external user is granted with respect to the secured document. For example, the access control restrictions can be imposed by providing access rules within the security information portion of the secured document. After the access control restrictions are imposed 312 and encryption 310 with the public key, the secured document is released 314 to the external user. In one embodiment, the secured document is released 314 by being transmitted. Typically, the transmission of the secured document to the external user is performed through one or more networks (e.g., data networks). After the secured document has been released 314 to the external user (or after operation 308 when the request to deliver the secured document to the external user is denied), the document delivery processing 300 is complete and ends.
FIG. 4 is a flow diagram of document access processing 400 according to one embodiment of the invention. The document access processing 400 involves an external user accessing a secured document that has been made available to the external user by an internal user.
The document access processing 400 begins with the external user acting to login 402 to an external access server. The external access server is associated with the document security system and utilized to permit limited external access to the document security system. As an example, the external access server can be the external access server 118 illustrated in FIG. 1.
A decision 404 then determines whether the login 402 has been successful. When the decision 404 determines that login has not been successful, then access is denied 406 to the external access server and no secured documents are made available to external users. Following the operation 406, the document access processing 400 is complete and ends as the external user was unable to successfully log into the external access server.
On the other hand, when the decision 404 determines that the external user has successfully logged into the external access server, then a private key associated with the external user is retrieved 408. In one embodiment, the private key is downloaded from the document security system via the external access server. In another embodiment, the private key is recovered locally.
Next, a decision 410 determines whether an access request for an encrypted document has been received. When the decision 410 determines that an access request for the secured document has not yet been received, a decision 412 determines whether the document access processing 400 should end. When the decision 412 determines that the document access processing 400 should not end, then the document access processing 400 returns to repeat the decision 410 and subsequent operations. On the other hand, when the decision 412 determines that the document access processing 400 should end, then the document access processing 400 is complete and ends.
Alternatively, when the decision 410 determines that an access request for the secured document has been received, then at least a portion of the security information for the secured document is decrypted 414 using the private key. Next, document level security is evaluated 416 to permit or deny access to the document contents. Following the operation 416, the document access processing 400 is complete and ends.
FIG. 5 is a flow diagram of access control processing 500 according to one embodiment of the invention. The access control processing 500 is, for example, suitable for use as the operations carried out by the operation 416 illustrated in FIG. 4.
The access control processing 500 initially obtains 502 access rules associated with the secured document. In one embodiment, the access rules are provided within the security information portion of the secured document. The access rules are then evaluated 504 against the access privilege of the user attempting to access the secured document. A decision 506 then determines whether the access rules are satisfied. When the decision 506 determines that the access rules are not satisfied, then access to the secured document is denied. Alternatively, when the decision 506 determines that the access rules are satisfied, then a file key associated with the secured document is obtained 510. In one embodiment, the file key is provided within the security information portion of the secured document. The file key can be encrypted or in a clear format. In the case in which the file key is itself encrypted, the file key is first decrypted. Next, the secured document is decrypted 512 using the file key. Following the operation 512, the access control processing 500 is complete and ends.
FIGS. 6 and 7 pertain to document delivery processing in which an external user provides a secured document to an internal user. FIG. 6 is a flow diagram of client-side document delivery processing 600 according to one embodiment of the invention. The client-side document delivery processing 600 is referred to as client-side because a client machine associated with the external user is performing or initiating the operations.
The client-side document delivery processing 600 begins with a decision 602 that determines whether a request (from an external user) to release a document to an internal user has been received. When the decision 602 determines that a request to release a document to an internal user has not yet been received, the client-side document delivery processing 600 awaits such a request. Once the decision 602 determines that a request to release a document to an internal user has been received, the client-side document delivery processing 600 continues. In other words, the client-side document delivery processing 600 can be considered to be invoked when the decision 602 determines that a request to release a document to an internal user has been received. The external user can interact with the client machine to initiate or make such a request.
After the decision 602 determines that a request to release a document to an internal user has been received, a public key associated with the internal user is requested 604. Here, according to one embodiment, the public key associated with the internal user is requested 604 from the document security system. A decision 606 then determines whether a response has been received. When the decision 606 determines that a response has not yet been received, the client-side document delivery processing 600 awaits such a response. When the decision 606 determines that a response has been received, a decision 608 first determines whether the request is from an external user who is what they claim to be. According to one embodiment, certificates are used prevent someone from impersonating someone else. Depending on implementation, a certification of the external user may be issued by a third party (e.g., Certificate Authority) or the document security system itself. When the decision 608 determines that the external user is not who they claim to be, then the request is denied 610 because the response received was presumably from an unauthorized user or system.
On the other hand, when the decision 608 determines that the external user is who they claim to be (i.e., an authorized user), a decision 612 determines whether a public key is available. Here, the response received is examined to determine whether the response includes the public key associated with the internal user. Hence, when the public key is available, it is provided with the response being received. In one embodiment, the availability of the public key is controlled by the partner relationship.
When the decision 612 determines that the public key is not available, then the request is denied 610 because the client machine does not have access to the public key associated with the internal user. On the other hand, when the decision 612 determines that the public key is available, then at least a portion of the security information for the secured document is encrypted 614 using the public key. In one embodiment, a file key within the security information for the secured document is encrypted using the public key. Thereafter, the secured document is released 616 to the internal user. In one embodiment, the secured document is released 616 by being transmitted. Following the operations 610 or 616, the client-side document delivery processing 600 is complete and ends.
FIG. 7 is a flow diagram of server-side document delivery processing 700 according to one embodiment of the invention. The server-side document delivery processing 700 is, for example, performed by the document security system, such as the document security system 100 illustrated in FIG. 1. The server-side document delivery processing 700 is responsive to a public key request from the client-side document delivery processing 600.
The server-side document delivery processing 700 begins with a decision 702 that determines whether a request for a public key from an external user has been received. In one embodiment, the request is provided by the operation 604 of the client-side document delivery processing 600 illustrated in FIG. 6. When the decision 702 determines that a request for a public key has not yet been received, then the server-side document delivery processing 700 awaits such a request. When the decision 702 determines that a request for a public key has been received, then a decision 704 determines whether the external user (requestor) is authorized to obtain the public key. Here, the authorization can be determined based on whether a partner relationship has been previously established between the external user and an organization. When the decision 704 determines that the external user is not authorized to receive the public key, then a response is prepared 710 indicating that access has been denied.
On the other hand, when the decision 704 determines that the external user is authorized to obtain the public key, then the public key associated with the internal user is retrieved 706 from a key store. The key store can, for example, be implemented as a database provided within the document security system. After the public key associated with the internal user has been retrieved 706, a response including the public key can be prepared 708. After the response has been prepared in operations 708 or 710, the response is signed 712 with a certificate for the organization. In one embodiment, the certificate would have been previously embedded a priori in the machine (e.g., client machine) of the external user. The signed response is then transmitted 714 to the external user. Typically, the transmission of the signed response is sent to the external user over a secured channel through a network (data network, e.g., the Internet). Following the operation 714, the server-side document delivery processing 700 is complete and ends.
FIG. 8 shows a basic security system 800 in which the invention may be practiced in accordance with one embodiment thereof. The security system 800 may be employed in an enterprise or inter-enterprise environment. It includes a first server 808 (also referred to as a central server) providing centralized access management for the enterprise. The first server 808 can control restrictive access to files secured by the security system 800. To provide dependability, reliability and scalability of the system, one or more second servers 804 (also referred to as local servers, of which one is shown) may be employed to provide backup or distributed access management for users or client machines serviced locally. For illustration purposes, there are two client machines 801 and 802 being serviced by a local server 804. Alternatively, one of the client machines 801 and 802 may be considered as a networked storage device.
Secured files may be stored in either one of the devices 801, 802, 804, 806 and 812. When a user of the client machine 801 attempts to exchange a secured file with a remote destination 812 being used by an external user, one or more of the processing 200, 300, 400, 500, 600 and 700 discussed above are activated to ensure that the requested secured file is delivered without compromising the security imposed on the secured file.
FIG. 9 shows an exemplary data structure 920 of a secured file that may be used in one embodiment of the invention. The data structure 920 includes two portions: a header (or header portion) 922 and encrypted data (or an encrypted data portion) 924. The header 922 can be generated in accordance with a security template associated with the store and thus provides restrictive access to the data portion 924 which is an encrypted version of a plain file. Optionally, the data structure 920 may also include an error-checking portion 925 that stores one or more error-checking codes, for example, a separate error-checking code for each block of encrypted data 924. These error-checking codes may also be associated with a Cyclical Redundancy Check (CRC) for the header 922 and/or the encrypted data 924. The header 922 includes a flag bit or signature 927 and security information 926 that is in accordance with the security template for the store. According to one embodiment, the security information 926 is encrypted and can be decrypted with a user key associated with an authenticated user (or requestor).
The security information 926 can vary depending upon implementation. However, as shown in FIG. 9, the security information 926 includes a user identifier (ID) 928, access policy (access rules) 929, a file key 930 and other information 931. Although multiple user identifiers may be used, a user identifier 928 is used to identify a user or a group that is permitted to access the secured file. The access rules 929 provide restrictive access to the encrypted data portion 924. The file key 930 is a cipher key that, once obtained, can be used to decrypt the encrypted data portion 924 and thus, in general, is protected. In one implementation of the data structure 920, the file key 930 is encrypted in conjunction with the access rules 929. In another implementation of the data structure 920, the file key 930 is double encrypted with a protection key and further protected by the access rules 929. The other information 931 is an additional space for other information to be stored within the security information 926. For example, the other information 931 may be used to include other information facilitating secure access to the secured file, such as version number or author identifier.
The invention is preferably implemented by software or a combination of hardware and software, but can also be implemented in hardware. The invention can also be embodied as computer readable code on a computer readable medium. The computer readable medium is any data storage device that can store data which can thereafter be read by a computer system. Examples of the computer readable medium include read-only memory, random-access memory, CD-ROMs, DVDs, magnetic tape, optical data storage devices, and carrier waves. The computer readable medium can also be distributed over network-coupled computer systems so that the computer readable code is stored and executed in a distributed fashion.
The various embodiments, implementations and features of the invention noted above can be combined in various ways or used separately. Those skilled in the art will understand from the description that the invention can be equally applied to or used in other various different settings with respect to various combinations, embodiments, implementations or features provided in the description herein.
The advantages of the invention are numerous. Different embodiments or implementations may yield one or more of the following advantages. One advantage of the invention is that file security systems are able to protect secured files (e.g., documents) even when external users are provided limited access to secured files. Another advantage of the invention is that a file security system can permit external users to access certain secured files (e.g., secured documents) without compromising integrity of the file security system. For example, external users having working relationships with internal users are able to be given limited user privileges within the file security system such that restricted file (document) exchange is permitted between such internal and external users. Still another advantage of the invention is that that amount of specialized software required at machines utilized by external users is minimal.
The foregoing description of embodiments is illustrative of various aspects/embodiments of the present invention. Various modifications to the present invention can be made to the preferred embodiments by those skilled in the art without departing from the true spirit and scope of the invention as defined by the appended claims. Accordingly, the scope of the present invention is defined by the appended claims rather than the foregoing description of embodiments.
* * * * *
References
-
dictionary.reference.com/search?q=affect
-
crypto.stanford.edu/ibe
-
microsoft.com/techneUcolumns/default.aspOct
-
microsoft.com/techneUcolumns/profwin
-
microsoft.com/techneUcolumns/profwin/Retrievedfromweb.archive.org
-
verisign.com/ss/ssl-information-center/how-ssl-security-works
-
microsoft.com/technetlcolumns/profwin
D00000

D00001
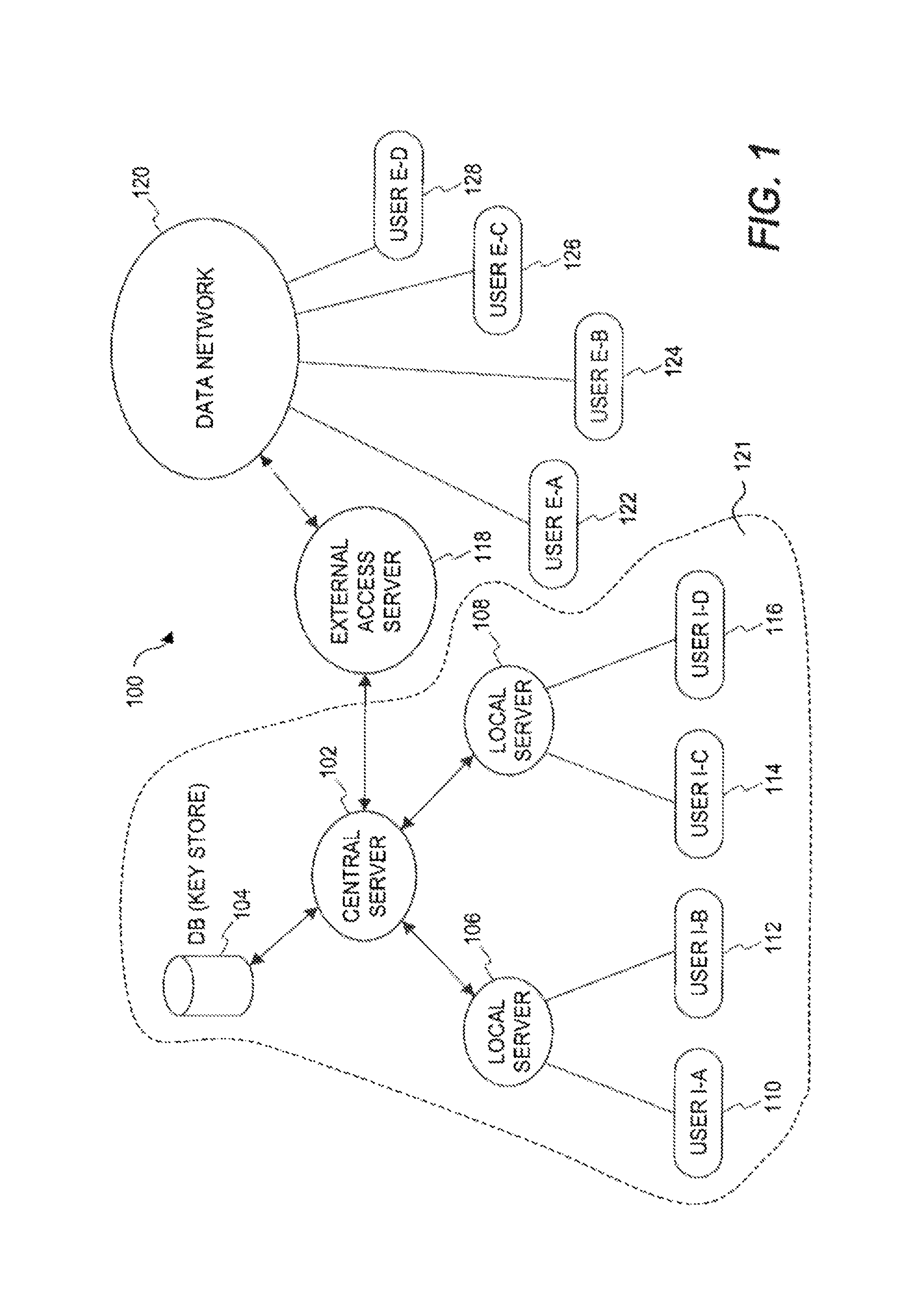
D00002

D00003

D00004

D00005

D00006

D00007
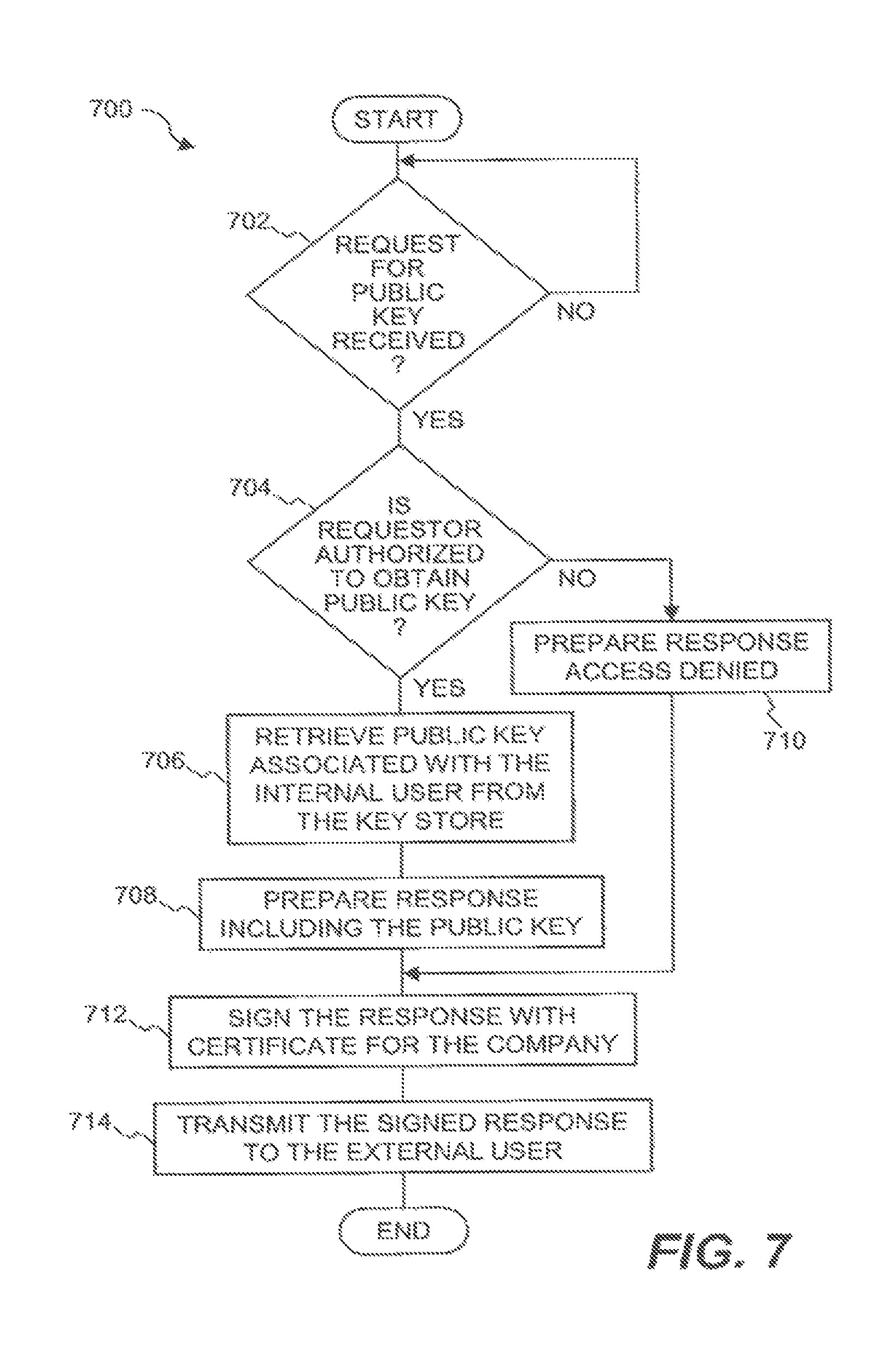
D00008
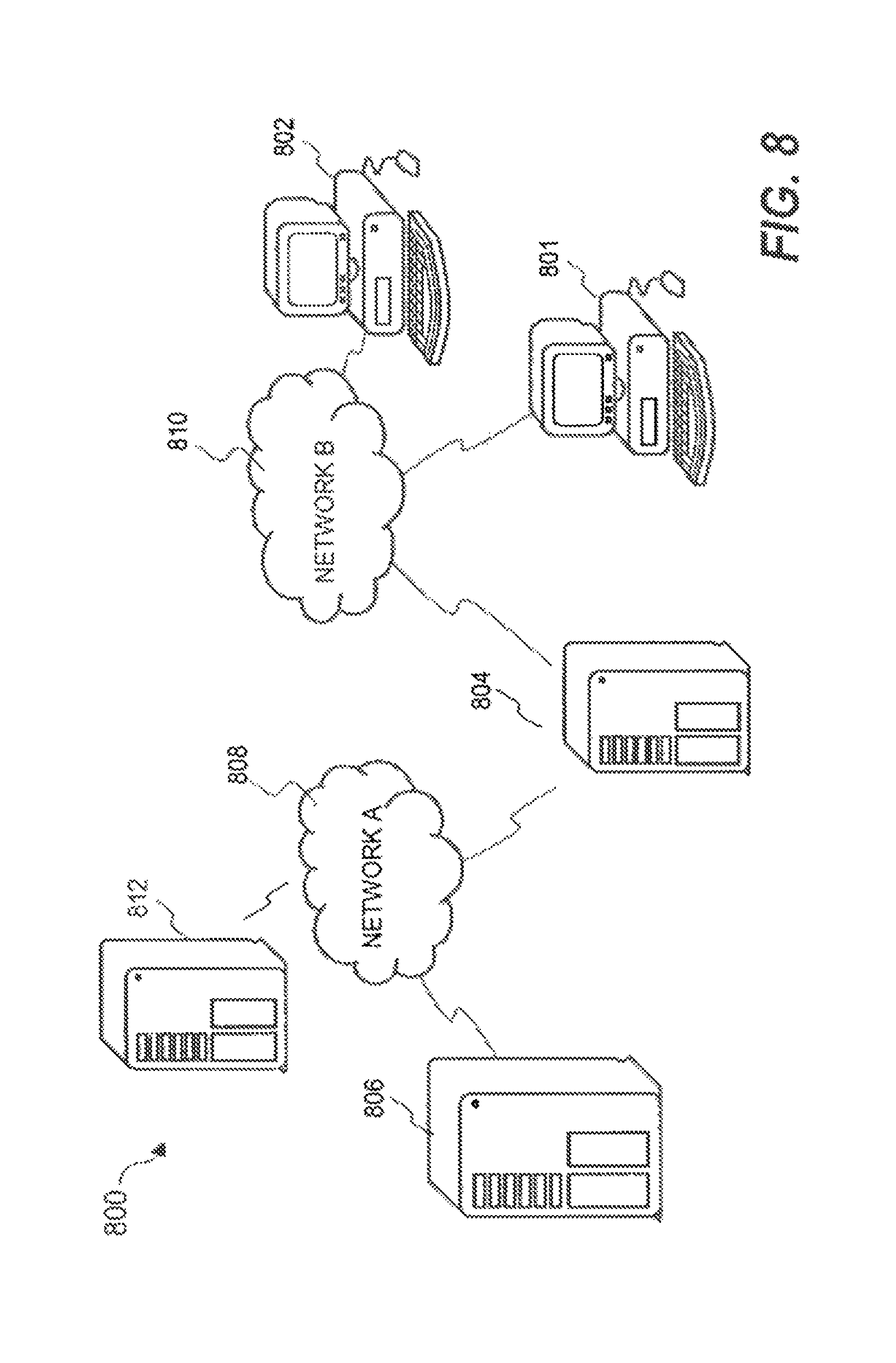
D00009

XML
uspto.report is an independent third-party trademark research tool that is not affiliated, endorsed, or sponsored by the United States Patent and Trademark Office (USPTO) or any other governmental organization. The information provided by uspto.report is based on publicly available data at the time of writing and is intended for informational purposes only.
While we strive to provide accurate and up-to-date information, we do not guarantee the accuracy, completeness, reliability, or suitability of the information displayed on this site. The use of this site is at your own risk. Any reliance you place on such information is therefore strictly at your own risk.
All official trademark data, including owner information, should be verified by visiting the official USPTO website at www.uspto.gov. This site is not intended to replace professional legal advice and should not be used as a substitute for consulting with a legal professional who is knowledgeable about trademark law.