Method for generating and transmitting pilot sequence using non-CAZAC sequence in wireless communication system
Lee , et al.
U.S. patent number 10,277,373 [Application Number 15/323,670] was granted by the patent office on 2019-04-30 for method for generating and transmitting pilot sequence using non-cazac sequence in wireless communication system. This patent grant is currently assigned to LG ELECTRONICS INC.. The grantee listed for this patent is LG ELECTRONICS INC.. Invention is credited to Hangyu Cho, Jinsoo Choi, Jiwon Kang, Kilbom Lee, Wookbong Lee, Dongguk Lim, Eunsung Park.









View All Diagrams
| United States Patent | 10,277,373 |
| Lee , et al. | April 30, 2019 |
Method for generating and transmitting pilot sequence using non-CAZAC sequence in wireless communication system
Abstract
Disclosed is a method for transmitting a pilot sequence, the method comprising: generating a sequence set on the basis of a baseline sequence having non-CAZAC properties; and selecting any one pilot sequence form among sequence sets corresponding to different additional information, and transmitting same to a receiver.
| Inventors: | Lee; Kilbom (Seoul, KR), Kang; Jiwon (Seoul, KR), Lee; Wookbong (Seoul, KR), Choi; Jinsoo (Seoul, KR), Lim; Dongguk (Seoul, KR), Cho; Hangyu (Seoul, KR), Park; Eunsung (Seoul, KR) | ||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|
| Applicant: |
|
||||||||||
| Assignee: | LG ELECTRONICS INC. (Seoul,
KR) |
||||||||||
| Family ID: | 55351359 | ||||||||||
| Appl. No.: | 15/323,670 | ||||||||||
| Filed: | August 19, 2015 | ||||||||||
| PCT Filed: | August 19, 2015 | ||||||||||
| PCT No.: | PCT/KR2015/008659 | ||||||||||
| 371(c)(1),(2),(4) Date: | January 03, 2017 | ||||||||||
| PCT Pub. No.: | WO2016/028082 | ||||||||||
| PCT Pub. Date: | February 25, 2016 |
Prior Publication Data
| Document Identifier | Publication Date | |
|---|---|---|
| US 20170149540 A1 | May 25, 2017 | |
Related U.S. Patent Documents
| Application Number | Filing Date | Patent Number | Issue Date | ||
|---|---|---|---|---|---|
| 62038852 | Aug 19, 2014 | ||||
| Current U.S. Class: | 1/1 |
| Current CPC Class: | H04L 5/005 (20130101); H04L 27/18 (20130101); H04L 27/2613 (20130101); H04L 27/0008 (20130101); H04L 27/26 (20130101); H04L 5/0048 (20130101); H04L 5/0026 (20130101) |
| Current International Class: | H04L 5/00 (20060101); H04L 27/18 (20060101); H04L 27/00 (20060101); H04L 27/26 (20060101) |
References Cited [Referenced By]
U.S. Patent Documents
| 7848438 | December 2010 | Baum |
| 8036310 | October 2011 | Ban |
| 2007/0171995 | July 2007 | Muharemovic et al. |
| 2009/0168730 | July 2009 | Baum et al. |
| 2009/0303960 | December 2009 | Qu et al. |
| 2017/0195159 | July 2017 | Lee |
| 2017/0214506 | July 2017 | Lee |
| 2017/0279582 | September 2017 | Lee |
| 2018/0123758 | May 2018 | Lee |
| 101262687 | Sep 2008 | CN | |||
| 10-2009-0003185 | Jan 2009 | KR | |||
| 10-2009-0026019 | Mar 2009 | KR | |||
| 10-2011-0005748 | Jan 2011 | KR | |||
| WO 2007/084988 | Jul 2007 | WO | |||
Other References
|
Kang et al., "Optimal Pilot Sequence Design Based on Chu Sequences for Multi-cell Environments," The Journal of Korean Institute of Communications and Information Sciences, vol. 34, No. 11, Nov. 2009, pp. 1113-1121, with an English abstract. cited by applicant. |
Primary Examiner: Nguyen; Hanh N
Attorney, Agent or Firm: Birch, Stewart, Kolasch & Birch, LLP
Parent Case Text
CROSS REFERENCE TO RELATED APPLICATIONS
This application is the National Phase of PCT International Application No. PCT/KR2015/008659, filed on Aug. 19, 2015, which claims priority under 35 U.S.C. 119(e) to U.S. Provisional Application No. 62/038,852, filed on Aug. 19, 2014, all of which are hereby expressly incorporated by reference into the present application.
Claims
The invention claimed is:
1. A method of transmitting a signal by a transmitter to a receiver in a wireless communication system, the method comprising: generating a baseline sequence having non-Constant Amplitude Zero Auto Correlation (non-CAZAC) properties; generating a plurality of pilot sequences by shifting the baseline sequence in a time domain based on a shifting value; and transmitting a pilot sequence of a sequence set composed of the plurality of pilot sequences to the receiver, wherein each of the plurality of pilot sequences are related to different information, respectively, and wherein the shifting value is determined such that a correlation between two pilot sequences of the sequence set is minimized.
2. The method of claim 1, wherein a minimum value of the shifting value is determined based on at least one of a channel effective delay period and/or a timing offset.
3. The method of claim 1, wherein a minimum value of the shifting value is determined based on a channel effective delay period only or both the channel effective delay period and a timing offset, based on a capability of estimating the timing offset by the receiver.
4. The method of claim 1, wherein the plurality of pilot sequences are generated by using a quantized Chu sequence as the plurality of pilot sequences.
5. The method of claim 4, wherein the quantized Chu sequence is generated by approximating a phase of a Chu sequence to a phase of a predetermined constellation.
6. The method of claim 5, wherein the predetermined constellation is one of BPSK (Binary Phase Shift Keying), QPSK (Quadrature Phase Shift Keying), 8-PSK (Phase Shift Keying), 16-PSK and 32-PSK.
7. A transmission device for transmitting a signal to a reception device in a wireless communication system, the transmission device comprising: a transmitter; a receiver; and a processor connected to the transmitter and the receiver to operate, wherein the processor is configured to: generate a baseline sequence having non-Constant Amplitude Zero Auto Correlation (non-CAZAC) properties, generate a plurality of pilot sequences by shifting the baseline sequence in a time domain based on a shifting value, and control the transmitter to transmit a pilot sequence of a sequence set composed of the plurality of pilot sequences to the reception device, wherein each of the plurality of pilot sequences are related to different information, respectively, and wherein the shifting value is determined such that a correlation between two pilot sequences of the sequence set is minimized.
8. The transmission device of claim 7, wherein a minimum value of the shifting value is determined based on at least one of a channel effective delay period and/or a timing offset.
9. The transmission device of claim 7, wherein a minimum value of the shifting value is determined based on a channel effective delay period only or both the channel effective delay period and a timing offset, based on a capability of estimating the timing offset by the reception device.
10. The transmission device of claim 7, wherein the processor generates the plurality of pilot sequences using a quantized Chu sequence as the plurality of pilot sequences.
11. The transmission device of claim 10, wherein the quantized Chu sequence is generated by approximating a phase of a Chu sequence to a phase of a predetermined constellation.
12. The transmission device of claim 11, wherein the predetermined constellation is one of BPSK (Binary Phase Shift Keying), QPSK (Quadrature Phase Shift Keying), 8-PSK (Phase Shift Keying), 16-PSK and 32-PSK.
Description
TECHNICAL FIELD
The following description relates to a wireless communication system and, more specifically, to methods and devices for generating and transmitting a pilot sequence using a non-CAZAC sequence in a wireless LAN system.
BACKGROUND ART
Recently, with development of information communication technology, various wireless communication technologies have been developed. Among others, a wireless local area network (WLAN) enables wireless access to the Internet using a portable terminal such as a personal digital assistant (PDA), a laptop, a portable multimedia player (PMP) in a home, an enterprise or a specific service provision area based on radio frequency technology.
In order to overcome limitations in communication rate which have been pointed out as weakness of a WLAN, in recent technical standards, a system for increasing network speed and reliability and extending wireless network distance has been introduced. For example, in IEEE 802.11n, multiple input and multiple output (MIMO) technology using multiple antennas in a transmitter and a receiver has been introduced in order to support high throughput (HT) with a maximum data rate of 540 Mbps or more, to minimize transmission errors, and to optimize data rate.
As next-generation communication technology, machine-to-machine (M2M) communication technology has been discussed. Even in an IEEE 802.11 WLAN system, technical standards supporting M2M communication have been developed as IEEE 802.11ah. In M2M communication, a scenario in which a small amount of data is communicated at a low rate may be considered in an environment in which many apparatuses are present.
Communication in a WLAN system is performed in a medium shared between all apparatuses. As in M2M communication, if the number of apparatuses is increased, in order to reduce unnecessary power consumption and interference, a channel access mechanism needs to be more efficiently improved.
DISCLOSURE
Technical Problem
An object of the present invention devised to solve the problem lies in efficient information transmission through design of a pilot sequence.
Another object of the present invention is to maximize the performance of a receiver even when a non-CAZAC sequence is used.
The technical problems solved by the present invention are not limited to the above technical problems and other technical problems which are not described herein will become apparent to those skilled in the art from the following description.
Technical Solution
In an aspect of the present invention, a method of transmitting a pilot sequence by a transmitter to a receiver in a wireless communication system includes: generating a baseline sequence having non-CAZAC (non-Constant Amplitude Zero Auto Correlation) properties; generating a plurality of pilot sequences by shifting the baseline sequence in a time domain; and transmitting a pilot sequence selected from a sequence set composed of the plurality of pilot sequences to the receiver, wherein the shifting of the baseline sequence is performed in order that that a correlation between the pilot sequences is minimized, and wherein the pilot sequences included in the sequence set respectively correspond to different additional information to be transmitted to the receiver.
A minimum value of the shifting may be determined in consideration of at least one of a channel effective delay period and a timing offset.
When the receiver can estimate the timing offset, the minimum value of the shifting may be determined in consideration of only the channel effective delay period.
The generating of the plurality of pilot sequences may use a quantized Chu sequence as the plurality of pilot sequences.
The quantized Chu sequence may be generated by approximating the phase of a Chu sequence to a phase of a predetermined constellation.
The predetermined constellation may be one of BPSK (Binary Phase Shift Keying), QPSK (Quadrature Phase Shift Keying), 8-PSK (Phase Shift Keying), 16-PSK and 32-PSK.
In another aspect of the present invention, a transmitter for transmitting a pilot sequence to a receiver in a wireless communication system includes: a transmission unit; a reception unit; and a processor connected to the transmission unit and the reception unit to operate, wherein the processor is configured to: generate a baseline sequence having non-CAZAC properties; generate a plurality of pilot sequences by shifting the baseline sequence in a time domain; and transmit a pilot sequence selected from a sequence set composed of the plurality of pilot sequences to the receiver, wherein the shifting of the baseline sequence is performed in order that a correlation between the pilot sequences is minimized, and wherein the pilot sequences included in the sequence set respectively correspond to different pieces of additional information to be transmitted to the receiver.
Advantageous Effects
The embodiments of the present invention have the following effects.
First, identification performance of a receiver can be improved by defining a sequence set using a non-CAZAC sequence.
Second, the identification performance of the receiver can be secured by minimizing a correlation between pilot sequences during design of a sequence set.
Third, generation of problems with respect to an EVM can be restricted using a sequence set considering the hardware performance of a transmitter.
The effects of the present invention are not limited to the above-described effects and other effects which are not described herein may be derived by those skilled in the art from the following description of the embodiments of the present invention. That is, effects which are not intended by the present invention may be derived by those skilled in the art from the embodiments of the present invention.
DESCRIPTION OF DRAWINGS
The accompanying drawings, which are included to provide a further understanding of the invention, illustrate embodiments of the invention and together with the description serve to explain the principle of the invention. The technical features of the present invention are not limited to specific drawings and the features shown in the drawings are combined to construct a new embodiment. Reference numerals of the drawings mean structural elements.
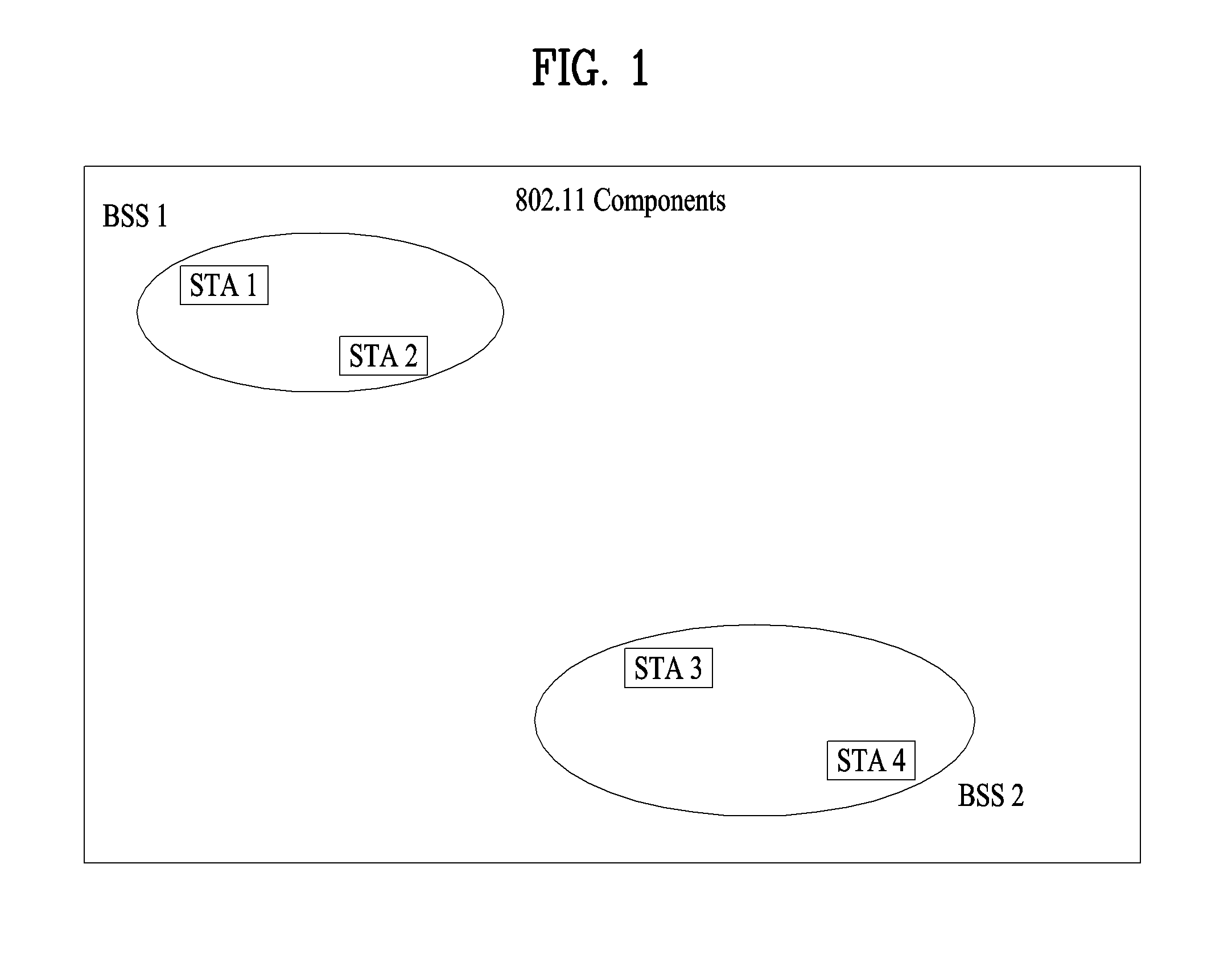
FIG. 1 is a diagram showing an exemplary structure of an IEEE 802.11 system to which the present invention is applicable.
FIG. 2 is a diagram showing another exemplary structure of an IEEE 802.11 system to which the present invention is applicable.
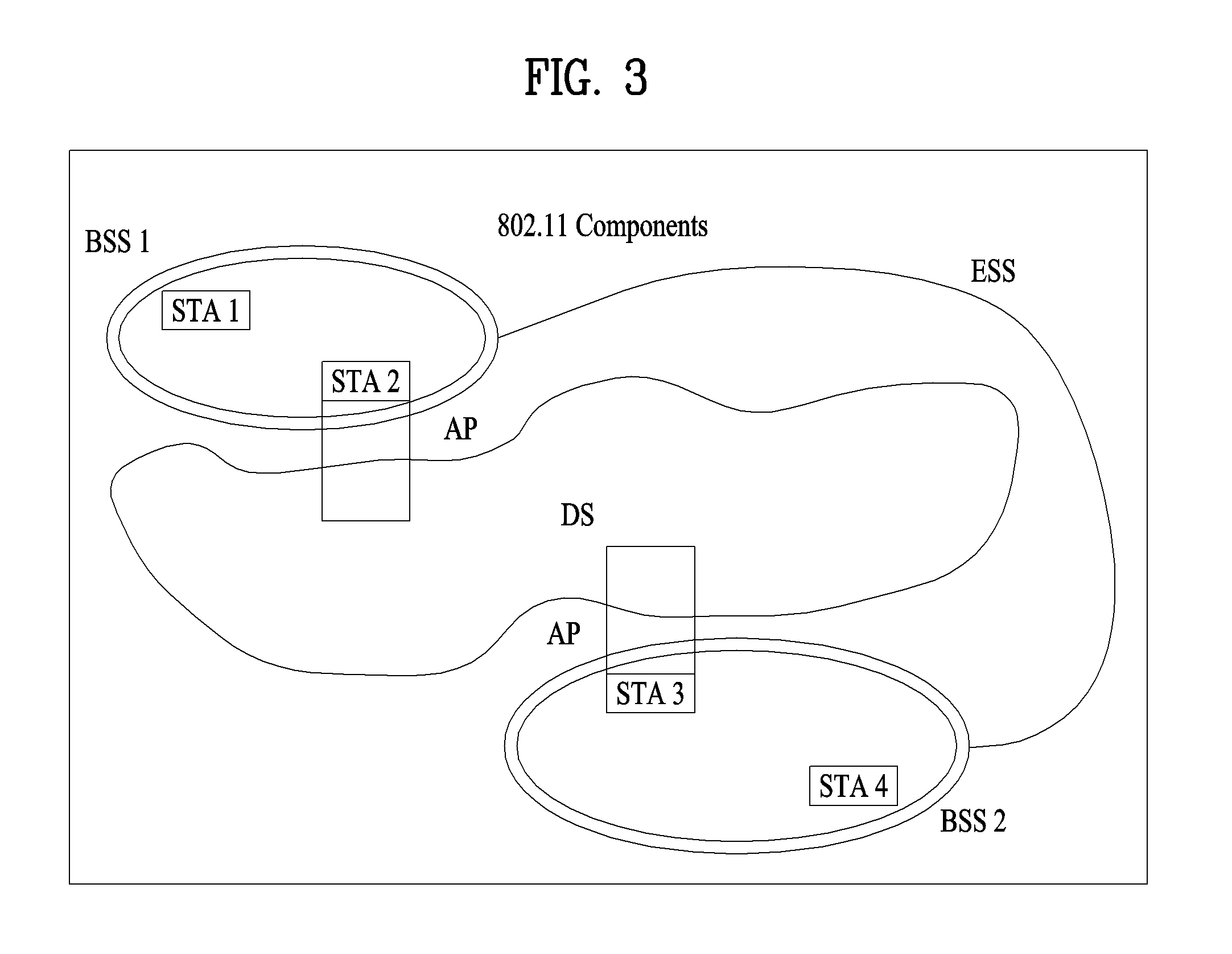
FIG. 3 is a diagram showing another exemplary structure of an IEEE 802.11 system to which the present invention is applicable.
FIG. 4 is a diagram showing an exemplary structure of a WLAN system.
FIG. 5 is a diagram illustrating a link setup process in a WLAN system.
FIG. 6 is a diagram illustrating a backoff process.
FIG. 7 is a diagram illustrating a hidden node and an exposed node.
FIG. 8 is a diagram illustrating request to send (RTS) and clear to send (CTS).
FIG. 9 is a diagram illustrating power management operation.
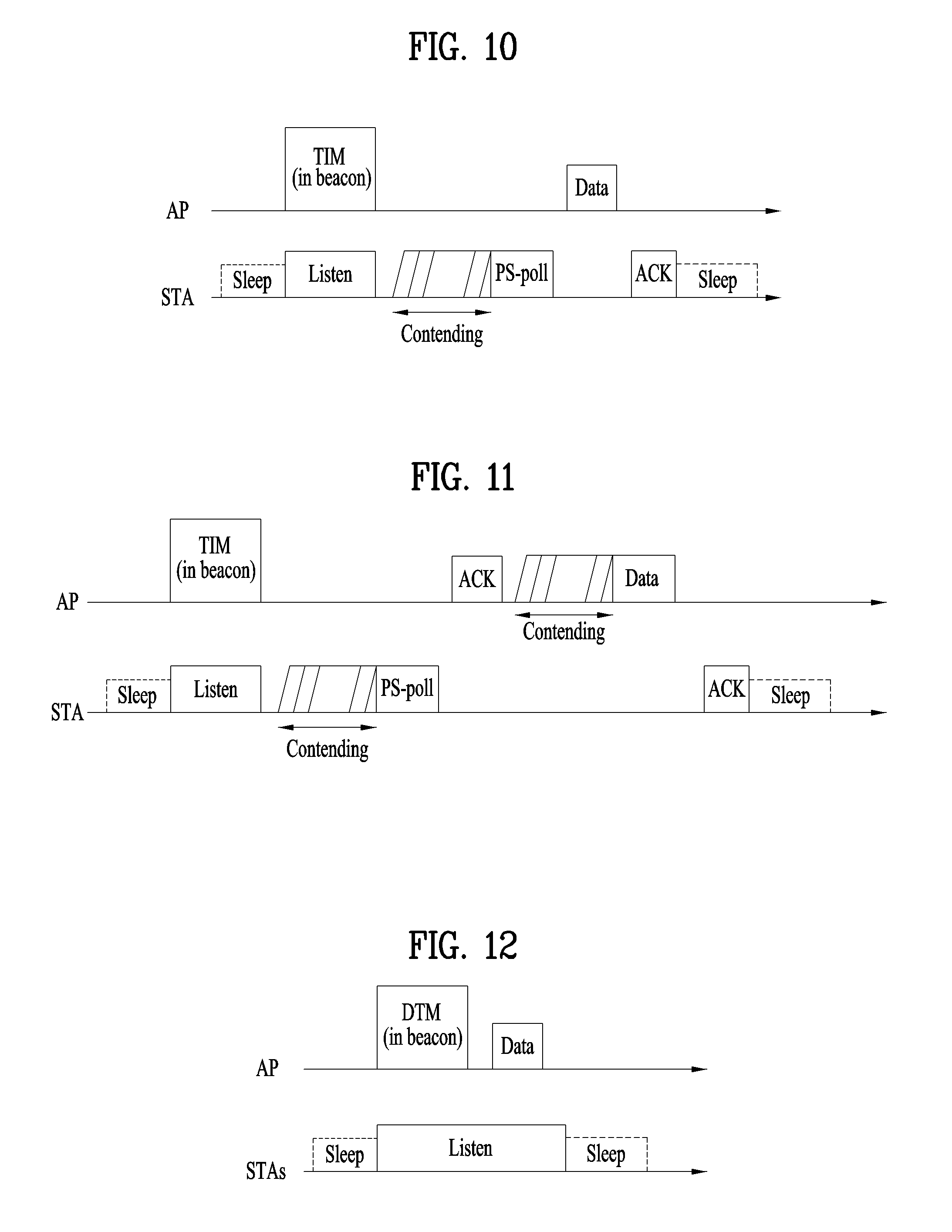
FIGS. 10 to 12 are diagrams illustrating operation of a station (STA) which receives a traffic indication map (TIM).
FIG. 13 is a diagram illustrating a group based association identifier (AID).
FIGS. 14 to 16 are diagrams showing examples of operation of an STA if a group channel access interval is set.
FIG. 17 is a diagram illustrating frame structures related to embodiments of the present invention.
FIG. 18 is a diagram illustrating a pilot sequence.
FIG. 19 is a diagram illustrating cyclic shifting of a pilot sequence.
FIG. 20 is a diagram illustrating a receiver structure for identification of a pilot sequence.
FIG. 21 is a diagram illustrating signals of a sequence set received by a receiver.
FIG. 22 is a diagram illustrating a sequence set composed of pilot sequences generated at a predetermined interval.
FIG. 23 is a diagram illustrating received signals of the sequence set illustrated in FIG. 22.
FIG. 24 is a diagram illustrating a timing offset.
FIG. 25 is a diagram illustrating received signals considering a timing offset.
FIG. 26 is a diagram illustrating a procedure of controlling the size of a zero correlation zone (ZCZ) in consideration of a timing offset.
FIG. 27 is a diagram illustrating a pilot sequence using a CAZAC sequence.
FIG. 28 is a diagram illustrating properties of a non-CAZAC sequence.
FIG. 29 is a diagram illustrating a procedure of receiving a pilot sequence using a non-CAZAC sequence.
FIG. 30 is a diagram illustrating a correlation between pilot sequences depending on shifting values.
FIG. 31 is a diagram illustrating an embodiment using a quantized Chu sequence.
FIG. 32 is a flowchart illustrating operation procedures of a transmitter and a receiver according to a proposed embodiment.
FIG. 33 is a diagram illustrating configurations of a UE and a base station related to an embodiment of the present invention.
BEST MODE
Although the terms used in the present invention are selected from generally known and used terms, terms used herein may be varied depending on operator's intention or customs in the art, appearance of new technology, or the like. In addition, some of the terms mentioned in the description of the present invention have been selected by the applicant at his or her discretion, the detailed meanings of which are described in relevant parts of the description herein. Furthermore, it is required that the present invention is understood, not simply by the actual terms used but by the meanings of each term lying within.
The following embodiments are proposed by combining constituent components and characteristics of the present invention according to a predetermined format. The individual constituent components or characteristics should be considered optional factors on the condition that there is no additional remark. If required, the individual constituent components or characteristics may not be combined with other components or characteristics. In addition, some constituent components and/or characteristics may be combined to implement the embodiments of the present invention. The order of operations to be disclosed in the embodiments of the present invention may be changed. Some components or characteristics of any embodiment may also be included in other embodiments, or may be replaced with those of the other embodiments as necessary.
In describing the present invention, if it is determined that the detailed description of a related known function or construction renders the scope of the present invention unnecessarily ambiguous, the detailed description thereof will be omitted.
In the entire specification, when a certain portion "comprises or includes" a certain component, this indicates that the other components are not excluded and may be further included unless specially described otherwise. The terms "unit", "-or/er" and "module" described in the specification indicate a unit for processing at least one function or operation, which may be implemented by hardware, software or a combination thereof. The words "a or an", "one", "the" and words related thereto may be used to include both a singular expression and a plural expression unless the context describing the present invention (particularly, the context of the following claims) clearly indicates otherwise.
In this document, the embodiments of the present invention have been described centering on a data transmission and reception relationship between a mobile station and a base station. The base station may mean a terminal node of a network which directly performs communication with a mobile station. In this document, a specific operation described as performed by the base station may be performed by an upper node of the base station.
Namely, it is apparent that, in a network comprised of a plurality of network nodes including a base station, various operations performed for communication with a mobile station may be performed by the base station, or network nodes other than the base station. The term base station may be replaced with the terms fixed station, Node B, eNode B (eNB), advanced base station (ABS), access point, etc.
The term mobile station (MS) may be replaced with user equipment (UE), subscriber station (SS), mobile subscriber station (MSS), mobile terminal, advanced mobile station (AMS), terminal, etc.
A transmitter refers to a fixed and/or mobile node for transmitting a data or voice service and a receiver refers to a fixed and/or mobile node for receiving a data or voice service. Accordingly, in uplink, a mobile station becomes a transmitter and a base station becomes a receiver. Similarly, in downlink transmission, a mobile station becomes a receiver and a base station becomes a transmitter.
Communication of a device with a "cell" may mean that the device transmit and receive a signal to and from a base station of the cell. That is, although a device substantially transmits and receives a signal to a specific base station, for convenience of description, an expression "transmission and reception of a signal to and from a cell formed by the specific base station" may be used. Similarly, the term "macro cell" and/or "small cell" may mean not only specific coverage but also a "macro base station supporting the macro cell" and/or a "small cell base station supporting the small cell".
The embodiments of the present invention can be supported by the standard documents disclosed in any one of wireless access systems, such as an IEEE 802.xx system, a 3rd Generation Partnership Project (3GPP) system, a 3GPP Long Term Evolution (LTE) system, and a 3GPP2 system. That is, the steps or portions, which are not described in order to make the technical spirit of the present invention clear, may be supported by the above documents.
In addition, all the terms disclosed in the present document may be described by the above standard documents. In particular, the embodiments of the present invention may be supported by at least one of P802.16-2004, P802.16e-2005, P802.16.1, P802.16p and P802.16.1b documents, which are the standard documents of the IEEE 802.16 system.
Hereinafter, the preferred embodiments of the present invention will be described with reference to the accompanying drawings. It is to be understood that the detailed description which will be disclosed along with the accompanying drawings is intended to describe the exemplary embodiments of the present invention, and is not intended to describe a unique embodiment which the present invention can be carried out.
It should be noted that specific terms disclosed in the present invention are proposed for convenience of description and better understanding of the present invention, and the use of these specific terms may be changed to another format within the technical scope or spirit of the present invention.
1. IEEE 802.11 System Overview
1.1 Structure of WLAN System
FIG. 1 is a diagram showing an exemplary structure of an IEEE 802.11 system to which the present invention is applicable.
An IEEE 802.11 structure may be composed of a plurality of components and a wireless local area network (WLAN) supporting station (STA) mobility transparent to a higher layer may be provided by interaction among the components. A basic service set (BSS) may correspond to a basic component block in an IEEE 802.11 LAN. In FIG. 1, two BSSs (BSS1 and BSS2) are present and each BSS includes two STAs (STA1 and STA2 are included in BSS1 and STA3 and STA4 are included in BSS2) as members. In FIG. 1, an ellipse indicating the BSS indicates a coverage area in which STAs included in the BSS maintains communication. This area may be referred to as a basic service area (BSA). If an STA moves out of a BSA, the STA cannot directly communicate with other STAs in the BSA.
In an IEEE 802.11 LAN, a BSS is basically an independent BSS (IBSS). For example, the IBSS may have only two STAs. In addition, the simplest BSS (BSS1 or BSS2) of FIG. 1, in which other components are omitted, may correspond to a representative example of the IBSS. Such a configuration is possible when STAs can directly perform communication. In addition, such a LAN is not configured in advance but may be configured if a LAN is necessary. This LAN may also be referred to as an ad-hoc network.
If an STA is turned on or off or if an STA enters or moves out of a BSS, the membership of the STA in the BSS may be dynamically changed. An STA may join a BSS using a synchronization process in order to become a member of the BSS. In order to access all services of a BSS based structure, an STA should be associated with the BSS. Such association may be dynamically set and may include use of a distribution system service (DSS).
FIG. 2 is a diagram showing another exemplary structure of an IEEE 802.11 system to which the present invention is applicable. In FIG. 2, a distribution system (DS), a distribution system medium (DSM) and an access point (AP) are added to the structure of FIG. 1.
In a LAN, a direct station-to-station distance may be restricted by PHY performance. Although such distance restriction may be possible, communication between stations located at a longer distance may be necessary. In order to support extended coverage, a DS may be configured.
The DS means a structure in which BSSs are mutually connected. More specifically, the BSSs are not independently present as shown in FIG. 1 but the BSS may be present as an extended component of a network including a plurality of BSSs.
The DS is a logical concept and may be specified by characteristics of the DSM. In IEEE 802.11 standards, a wireless medium (WM) and a DSM are logically distinguished. Logical media are used for different purposes and are used by different components. In IEEE 802.11 standards, such media are not restricted to the same or different media. Since plural media are logically different, an IEEE 802.11 LAN structure (a DS structure or another network structure) may be flexible. That is, the IEEE 802.11 LAN structure may be variously implemented and a LAN structure may be independently specified by physical properties of each implementation.
The DS provides seamless integration of a plurality of BSSs and provides logical services necessary to treat an address to a destination so as to support a mobile apparatus.
The AP means an entity which enables associated STAs to access the DS via the WM and has STA functionality. Data transfer between the BSS and the DS may be performed via the AP. For example, STA2 and STA3 shown in FIG. 2 have STA functionality and provide a function enabling associated STAs (STA1 and STA4) to access the DS. In addition, since all APs correspond to STAs, all APs may be addressable entities. An address used by the AP for communication on the WM and an address used by the AP for communication on the DSM may not be equal.
Data transmitted from one of STAs associated with the AP to the STA address of the AP may always be received by an uncontrolled port and processed by an IEEE 802.1X port access entity. In addition, if a controlled port is authenticated, transmission data (or frames) may be transmitted to the DS.
FIG. 3 is a diagram showing another exemplary structure of an IEEE 802.11 system to which the present invention is applicable. In FIG. 3, an extended service set (ESS) for providing wide coverage is added to the structure of FIG. 2.
A wireless network having an arbitrary size and complexity may be composed of a DS and BSSs. In an IEEE 802.11 system, such a network is referred to as an ESS network. The ESS may correspond to a set of BSSs connected to one DS. However, the ESS does not include the DS. The ESS network appears as an IBSS network at a logical link control (LLC) layer. STAs included in the ESS may communicate with each other and mobile STAs may move from one BSS to another BSS (within the same ESS) transparently to the LLC layer.
In IEEE 802.11, relative physical locations of the BSSs in FIG. 3 are not assumed and may be defined as follows. The BSSs may partially overlap in order to provide consecutive coverage. In addition, the BSSs may not be physically connected and a distance between BSSs is not logically restricted. In addition, the BSSs may be physically located at the same location in order to provide redundancy. In addition, one (or more) IBSS or ESS network may be physically present in the same space as one (or more) ESS network. This corresponds to an ESS network type such as a case in which an ad-hoc network operates at a location where the ESS network is present, a case in which IEEE 802.11 networks physically overlapped by different organizations are configured or a case in which two or more different access and security policies are necessary at the same location.
FIG. 4 is a diagram showing an exemplary structure of a WLAN system. FIG. 4 shows an example of an infrastructure BSS including a DS.
In the example of FIG. 4, BSS1 and BSS2 configure an ESS. In the WLAN system, an STA operates according to a MAC/PHY rule of IEEE 802.11. The STA includes an AP STA and a non-AP STA. The non-AP STA corresponds to an apparatus directly handled by a user, such as a laptop or a mobile phone. In the example of FIG. 4, STA1, STA3 and STA4 correspond to the non-AP STA and STA2 and STA5 correspond to the AP STA.
In the following description, the non-AP STA may be referred to as a terminal, a wireless transmit/receive unit (WTRU), a user equipment (UE), a mobile station (MS), a mobile terminal or a mobile subscriber station (MSS). In addition, the AP may correspond to a base station (BS), a Node-B, an evolved Node-B (eNB), a base transceiver system (BTS) or a femto BS.
1.2 Link Setup Process
FIG. 5 is a diagram illustrating a general link setup process.
In order to establish a link with respect to a network and perform data transmission and reception, an STA discovers the network, performs authentication, establishes association and performs an authentication process for security. The link setup process may be referred to as a session initiation process or a session setup process. In addition, discovery, authentication, association and security setup of the link setup process may be collectively referred to as an association process.
An exemplary link setup process will be described with reference to FIG. 5.
In step S510, the STA may perform a network discovery operation. The network discovery operation may include a scanning operation of the STA. That is, the STA discovers the network in order to access the network. The STA should identify a compatible network before participating in a wireless network and a process of identifying a network present in a specific area is referred to as scanning. The scanning method includes an active scanning method and a passive scanning method.
In FIG. 5, a network discovery operation including an active scanning process is shown. In active scanning, the STA which performs scanning transmits a probe request frame while moving between channels and waits for a response thereto, in order to detect which AP is present. A responder transmits a probe response frame to the STA, which transmitted the probe request frame, as a response to the probe request frame. The responder may be an STA which lastly transmitted a beacon frame in a BSS of a scanned channel. In the BSS, since the AP transmits the beacon frame, the AP is the responder. In the IBSS, since the STAs in the IBSS alternately transmit the beacon frame, the responder is not fixed. For example, the STA which transmits the probe request frame on a first channel and receives the probe response frame on the first channel stores BSS related information included in the received probe response frame, moves to a next channel (e.g., a second channel) and performs scanning (probe request/response transmission/reception on the second channel) using the same method.
Although not shown in FIG. 5, a scanning operation may be performed using a passive scanning method. In passive scanning, the STA which performs scanning waits for a beacon frame while moving between channels. The beacon frame is a management frame in IEEE 802.11 and is periodically transmitted in order to indicate presence of a wireless network and to enable the STA, which performs scanning, to discover and participate in the wireless network. In the BSS, the AP is responsible for periodically transmitting the beacon frame. In the IBSS, the STAs alternately transmit the beacon frame. The STA which performs scanning receives the beacon frame, stores information about the BSS included in the beacon frame, and records beacon frame information of each channel while moving to another channel. The STA which receives the beacon frame may store BSS related information included in the received beacon frame, move to a next channel and perform scanning on the next channel using the same method.
Active scanning has delay and power consumption less than those of passive scanning.
After the STA has discovered the network, an authentication process may be performed in step S520. Such an authentication process may be referred to as a first authentication process to be distinguished from a security setup operation of step S540.
The authentication process includes a process of, at the STA, transmitting an authentication request frame to the AP and, at the AP, transmitting an authentication response frame to the STA in response thereto. The authentication frame used for authentication request/response corresponds to a management frame.
The authentication frame may include information about an authentication algorithm number, an authentication transaction sequence number, a status code, a challenge text, a robust security network (RSN), a finite cyclic group, etc. The information may be examples of information included in the authentication request/response frame and may be replaced with other information. The information may further include additional information.
The STA may transmit the authentication request frame to the AP. The AP may determine whether authentication of the STA is allowed, based on the information included in the received authentication request frame. The AP may provide the STA with the authentication result via the authentication response frame.
After the STA is successfully authenticated, an association process may be performed in step S530. The association process includes a process of, at the STA, transmitting an association request frame to the AP and, at the AP, transmitting an association response frame to the STA in response thereto.
For example, the association request frame may include information about various capabilities, beacon listen interval, service set identifier (SSID), supported rates, RSN, mobility domain, supported operating classes, traffic indication map (TIM) broadcast request, interworking service capability, etc.
For example, the association response frame may include information about various capabilities, status code, association ID (AID), supported rates, enhanced distributed channel access (EDCA) parameter set, received channel power indicator (RCPI), received signal to noise indicator (RSNI), mobility domain, timeout interval (association comeback time), overlapping BSS scan parameter, TIM broadcast response, QoS map, etc.
This information is purely exemplary information included in the association request/response frame and may be replaced with other information. This information may further include additional information.
After the STA is successfully authenticated, a security setup process may be performed in step S540. The security setup process of step S540 may be referred to as an authentication process through a robust security network association (RSNA) request/response. The authentication process of step S520 may be referred to as the first authentication process and the security setup process of step S540 may be simply referred to as an authentication process.
The security setup process of step S540 may include a private key setup process through 4-way handshaking of an extensible authentication protocol over LAN (EAPOL) frame. In addition, the security setup process may be performed according to a security method which is not defined in the IEEE 802.11 standard.
2.1 Evolution of WLAN
As a technical standard recently established in order to overcome limitations in communication speed in a WLAN, IEEE 802.11n has been devised. IEEE 802.11n aims at increasing network speed and reliability and extending wireless network distance. More specifically, IEEE 802.11n is based on multiple input and multiple output (MIMO) technology using multiple antennas in a transmitter and a receiver in order to support high throughput (HT) with a maximum data rate of 540 Mbps or more, to minimize transmission errors, and to optimize data rate.
As WLANs have come into widespread use and applications using the same have been diversified, recently, there is a need for a new WLAN system supporting throughput higher than a data rate supported by IEEE 802.11n. A next-generation WLAN system supporting very high throughput (VHT) is a next version (e.g., IEEE 802.11ac) of the IEEE 802.11n WLAN system and is an IEEE 802.11 WLAN system newly proposed in order to support a data rate of 1 Gbps or more at a MAC service access point (SAP).
The next-generation WLAN system supports a multi-user MIMO (MU-MIMO) transmission scheme by which a plurality of STAs simultaneously accesses a channel in order to efficiently use a radio channel. According to the MU-MIMO transmission scheme, the AP may simultaneously transmit packets to one or more MIMO-paired STAs.
In addition, support of a WLAN system operation in a whitespace is being discussed. For example, introduction of a WLAN system in a TV whitespace (WS) such as a frequency band (e.g., 54 to 698 MHz) in an idle state due to digitalization of analog TVs is being discussed as the IEEE 802.11af standard. However, this is only exemplary and the whitespace may be incumbently used by a licensed user. The licensed user means a user who is allowed to use a licensed band and may be referred to as a licensed device, a primary user or an incumbent user.
For example, the AP and/or the STA which operate in the WS should provide a protection function to the licensed user. For example, if a licensed user such as a microphone already uses a specific WS channel which is a frequency band divided on regulation such that a WS band has a specific bandwidth, the AP and/or the STA cannot use the frequency band corresponding to the WS channel in order to protect the licensed user. In addition, the AP and/or the STA must stop use of the frequency band if the licensed user uses the frequency band used for transmission and/or reception of a current frame.
Accordingly, the AP and/or the STA should perform a procedure of determining whether a specific frequency band in a WS band is available, that is, whether a licensed user uses the frequency band. Determining whether a licensed user uses a specific frequency band is referred to as spectrum sensing. As a spectrum sensing mechanism, an energy detection method, a signature detection method, etc. may be used. It may be determined that the licensed user uses the frequency band if received signal strength is equal to or greater than a predetermined value or if a DTV preamble is detected.
In addition, as next-generation communication technology, machine-to-machine (M2M) communication technology is being discussed. Even in an IEEE 802.11 WLAN system, a technical standard supporting M2M communication has been developed as IEEE 802.11ah. M2M communication means a communication scheme including one or more machines and may be referred to as machine type communication (MTC). Here, a machine means an entity which does not require direct operation or intervention of a person. For example, a device including a mobile communication module, such as a meter or a vending machine, may include a user equipment such as a smart phone which is capable of automatically accessing a network without operation/intervention of a user to perform communication. M2M communication includes communication between devices (e.g., device-to-device (D2D) communication) and communication between a device and an application server. Examples of communication between a device and a server include communication between a vending machine and a server, communication between a point of sale (POS) device and a server and communication between an electric meter, a gas meter or a water meter and a server. An M2M communication based application may include security, transportation, health care, etc. If the characteristics of such examples are considered, in general, M2M communication should support transmission and reception of a small amount of data at a low rate in an environment in which very many apparatuses are present.
More specifically, M2M communication should support a larger number of STAs. In a currently defined WLAN system, it is assumed that a maximum of 2007 STAs is associated with one AP. However, in M2M communication, methods supporting the case in which a larger number of STAs (about 6000) are associated with one AP are being discussed. In addition, in M2M communication, it is estimated that there are many applications supporting/requiring a low transfer rate. In order to appropriately support the low transfer rate, for example, in a WLAN system, the STA may recognize presence of data to be transmitted thereto based on a traffic indication map (TIM) element and methods of reducing a bitmap size of the TIM are being discussed. In addition, in M2M communication, it is estimated that there is traffic having a very long transmission/reception interval. For example, in electricity/gas/water consumption, a very small amount of data is required to be exchanged at a long period (e.g., one month). In a WLAN system, although the number of STAs associated with one AP is increased, methods of efficiently supporting the case in which the number of STAs, in which a data frame to be received from the AP is present during one beacon period, is very small are being discussed.
WLAN technology has rapidly evolved. In addition to the above-described examples, technology for direct link setup, improvement of media streaming performance, support of fast and/or large-scale initial session setup, support of extended bandwidth and operating frequency, etc. is being developed.
2.2 Medium Access Mechanism
In a WLAN system according to IEEE 802.11, the basic access mechanism of medium access control (MAC) is a carrier sense multiple access with collision avoidance (CSMA/CA) mechanism. The CSMA/CA mechanism is also referred to as a distributed coordination function (DCF) of IEEE 802.11 MAC and employs a "listen before talk" access mechanism. According to such an access mechanism, the AP and/or the STA may perform clear channel assessment (CCA) for sensing a radio channel or medium during a predetermined time interval (for example, a DCF inter-frame space (DIFS)) before starting transmission. If it is determined that the medium is in an idle state as the sensed result, frame transmission starts via the medium. If it is determined that the medium is in an occupied state, the AP and/or the STA may set and wait for a delay period (e.g., a random backoff period) for medium access without starting transmission and then attempt to perform frame transmission. Since several STAs attempt to perform frame transmission after waiting for different times by applying the random backoff period, it is possible to minimize collision.
In addition, the IEEE 802.11 MAC protocol provides a hybrid coordination function (HCF). The HCF is based on the DCF and a point coordination function (PCF). The PCF refers to a periodic polling method for enabling all reception AP and/or STAs to receive data frames using a polling based synchronous access method. In addition, the HCF has enhanced distributed channel access (EDCA) and HCF controlled channel access (HCCA). The EDCA uses a contention access method for providing data frames to a plurality of users by a provider and the HCCA uses a contention-free channel access method using a polling mechanism. In addition, the HCF includes a medium access mechanism for improving quality of service (QoS) of a WLAN and may transmit QoS data both in a contention period (CP) and a contention free period (CFP).
FIG. 6 is a diagram illustrating a backoff process.
Operation based on a random backoff period will be described with reference to FIG. 6. If a medium is changed from an occupied or busy state to an idle state, several STAs may attempt data (or frame) transmission. At this time, a method of minimizing collision, the STAs may select respective random backoff counts, wait for slot times corresponding to the random backoff counts and attempt transmission. The random backoff count has a pseudo-random integer and may be set to one of values of 0 to CW. Here, the CW is a contention window parameter value. The CW parameter is set to CWmin as an initial value but may be set to twice CWmin if transmission fails (e.g., ACK for the transmission frame is not received). If the CW parameter value becomes CWmax, data transmission may be attempted while maintaining the CWmax value until data transmission is successful. If data transmission is successful, the CW parameter value is reset to CWmin. CW, CWmin and CWmax values are preferably set to 2n-1 (n=0, 1, 2, . . . ).
If the random backoff process starts, the STA continuously monitors the medium while the backoff slots are counted down according to the set backoff count value. If the medium is in the occupied state, countdown is stopped and, if the medium is in the idle state, countdown is resumed.
In the example of FIG. 6, if packets to be transmitted to the MAC of STA3 arrive, STA3 may confirm that the medium is in the idle state during the DIFS and immediately transmit a frame. Meanwhile, the remaining STAs monitor that the medium is in the busy state and wait. During a wait time, data to be transmitted may be generated in STA1, STA2 and STA5. The STAs may wait for the DIFS if the medium is in the idle state and then count down the backoff slots according to the respectively selected random backoff count values.
In the example of FIG. 6, STA2 selects a smallest backoff count value and STA1 selects a largest backoff count value. That is, the residual backoff time of STA5 is less than the residual backoff time of STA1 when STA2 completes backoff count and starts frame transmission. STA1 and STA5 stop countdown and wait while STA2 occupies the medium. If occupancy of the medium by STA2 ends and the medium enters the idle state again, STA1 and STA5 wait for the DIFS and then resume countdown. That is, after the residual backoff slots corresponding to the residual backoff time are counted down, frame transmission may start. Since the residual backoff time of STA5 is less than of STA1, STA5 starts frame transmission.
If STA2 occupies the medium, data to be transmitted may be generated in the STA4. At this time, STA4 may wait for the DIFS if the medium enters the idle state, perform countdown according to a random backoff count value selected thereby, and start frame transmission. In the example of FIG. 6, the residual backoff time of STA5 accidentally matches the random backoff time of STA4. In this case, collision may occur between STA4 and STA5. If collision occurs, both STA4 and STA5 do not receive ACK and data transmission fails. In this case, STA4 and STA5 may double the CW value, select the respective random backoff count values and then perform countdown. STA1 may wait while the medium is busy due to transmission of STA4 and STA5, wait for the DIFS if the medium enters the idle state, and start frame transmission if the residual backoff time has elapsed.
2.3 Sensing Operation of STA
As described above, the CSMA/CA mechanism includes not only physical carrier sensing for directly sensing a medium by an AP and/or an STA but also virtual carrier sensing. Virtual carrier sensing solves a problem which may occur in medium access, such as a hidden node problem. For virtual carrier sensing, MAC of a WLAN may use a network allocation vector (NAV). The NAV refers to a value of a time until a medium becomes available, which is indicated to another AP and/or STA by an AP and/or an STA, which is currently utilizing the medium or has rights to utilize the medium. Accordingly, the NAV value corresponds to a period of time when the medium will be used by the AP and/or the STA for transmitting the frame, and medium access of the STA which receives the NAV value is prohibited during that period of time. The NAV may be set according to the value of the "duration" field of a MAC header of a frame.
A robust collision detection mechanism for reducing collision has been introduced, which will be described with reference to FIGS. 7 and 8. Although a transmission range may not be equal to an actual carrier sensing range, for convenience, assume that the transmission range may be equal to the actual carrier sensing range.
FIG. 7 is a diagram illustrating a hidden node and an exposed node.
FIG. 7(a) shows a hidden node, and, in this case, an STA A and an STA B are performing communication and an STA C has information to be transmitted. More specifically, although the STA A transmits information to the STA B, the STA C may determine that the medium is in the idle state, when carrier sensing is performed before transmitting data to the STA B. This is because the STA C may not sense transmission of the STA A (that is, the medium is busy). In this case, since the STA B simultaneously receives information of the STA A and the STA C, collision occurs. At this time, the STA A may be the hidden node of the STA C.
FIG. 7(b) shows an exposed node and, in this case, the STA B transmits data to the STA A and the STA C has information to be transmitted to the STA D. In this case, if the STA C performs carrier sensing, it may be determined that the medium is busy due to transmission of the STA B. If the STA C has information to be transmitted to the STA D, since it is sensed that the medium is busy, the STA C waits until the medium enters the idle state. However, since the STA A is actually outside the transmission range of the STA C, transmission from the STA C and transmission from the STA B may not collide from the viewpoint of the STA A. Therefore, the STA C unnecessarily waits until transmission of the STA B is stopped. At this time, the STA C may be the exposed node of the STA B.
FIG. 8 is a diagram illustrating request to send (RTS) and clear to send (CTS).
In the example of FIG. 7, in order to efficiently use a collision avoidance mechanism, short signaling packet such as RTS and CTS may be used. RST/CTS between two STAs may be enabled to be overheard by peripheral STAs such that the peripheral STAs confirm information transmission between the two STAs. For example, if a transmission STA transmits an RTS frame to a reception STA, the reception STA transmits a CTS frame to peripheral UEs to inform the peripheral UEs that the reception STA receives data.
FIG. 8(a) shows a method of solving a hidden node problem. Assume that both the STA A and the STA C attempt to transmit data to the STA B. If the STA A transmits the RTS to the STA B, the STA B transmits the CTS to the peripheral STA A and C. As a result, the STA C waits until data transmission of the STA A and the STA B is finished, thereby avoiding collision.
FIG. 8(b) shows a method of solving an exposed node problem. The STA C may overhear RTS/CTS transmission between the STA A and the STA B and determine that collision does not occur even when the STA C transmits data to another STA (e.g., the STA D). That is, the STA B transmits the RTS to all peripheral UEs and transmits the CTS only to the STA A having data to be actually transmitted. Since the STA C receives the RTS but does not receive the CTS of the STA A, it can be confirmed that the STA A is outside carrier sensing of the STA C.
2.4 Power Management
As described above, in a WLAN system, channel sensing should be performed before an STA performs transmission and reception. When the channel is always sensed, continuous power consumption of the STA is caused. Power consumption in a reception state is not substantially different from power consumption in a transmission state and continuously maintaining the reception state imposes a burden on an STA with limited power (that is, operated by a battery). Accordingly, if a reception standby state is maintained such that the STA continuously senses the channel, power is inefficiently consumed without any special advantage in terms of WLAN throughput. In order to solve such a problem, in a WLAN system, a power management (PM) mode of the STA is supported.
The PM mode of the STA is divided into an active mode and a power save (PS) mode. The STA fundamentally operates in an active mode. The STA which operates in the active mode is maintained in an awake state. The awake state refers to a state in which normal operation such as frame transmission and reception or channel scanning is possible. The STA which operates in the PS mode operates while switching between a sleep state or an awake state. The STA which operates in the sleep state operates with minimum power and does not perform frame transmission and reception or channel scanning.
Since power consumption is reduced as the sleep state of the STA is increased, the operation period of the STA is increased. However, since frame transmission and reception is impossible in the sleep state, the STA may not unconditionally operate in the sleep state. If a frame to be transmitted from the STA, which operates in the sleep state, to the AP is present, the STA may be switched to the awake state to transmit the frame. If a frame to be transmitted from the AP to the STA is present, the STA in the sleep state may not receive the frame and may not confirm that the frame to be received is present. Accordingly, the STA needs to perform an operation for switching to the awake state according to a specific period in order to confirm presence of the frame to be transmitted thereto (to receive the frame if the frame to be transmitted is present).
FIG. 9 is a diagram illustrating power management operation.
Referring to FIG. 9, an AP 210 transmits beacon frames to STAs within a BSS at a predetermined period (S211, S212, S213, S214, S215 and S216). The beacon frame includes a traffic indication map (TIM) information element. The TIM information element includes information indicating that buffered traffic for STAs associated with the AP 210 is present and the AP 210 will transmit a frame. The TIM element includes a TIM used to indicate a unicast frame or a delivery traffic indication map (DTIM) used to indicate a multicast or broadcast frame.
The AP 210 may transmit the DTIM once whenever the beacon frame is transmitted three times. An STA1 220 and an STA2 222 operate in the PS mode. The STA1 220 and the STA2 222 may be switched from the sleep state to the awake state at a predetermined wakeup interval to receive a TIM element transmitted by the AP 210. Each STA may compute a time to switch to the awake state based on a local clock thereof. In the example of FIG. 9, assume that the clock of the STA matches the clock of the AP.
For example, the predetermined awake interval may be set such that the STA1 220 is switched to the awake state every beacon interval to receive a TIM element. Accordingly, the STA1 220 may be switched to the awake state (S211) when the AP 210 first transmits the beacon frame (S211). The STA1 220 may receive the beacon frame and acquire the TIM element. If the acquired TIM element indicates that a frame to be transmitted to the STA1 220 is present, the STA1 220 may transmit, to the AP 210, a power save-Poll (PS-Poll) frame for requesting frame transmission from the AP 210 (S221a). The AP 210 may transmit the frame to the STA1 220 in correspondence with the PS-Poll frame (S231). The STA1 220 which completes frame reception is switched to the sleep state.
When the AP 210 secondly transmits the beacon frame, since another device access the medium and thus the medium is busy, the AP 210 may not transmit the beacon frame at an accurate beacon interval and may transmit the beacon frame at a delayed time (S212). In this case, the operation mode of the STA1 220 is switched to the awake state according to the beacon interval but the delayed beacon frame is not received. Therefore, the operation mode of the STA1 220 is switched to the sleep state again (S222).
When the AP 210 thirdly transmits the beacon frame, the beacon frame may include a TIM element set to a DTIM. Since the medium is busy, the AP 210 transmits the beacon frame at a delayed time (S213). The STA1 220 is switched to the awake state according to the beacon interval and may acquire the DTIM via the beacon frame transmitted by the AP 210. Assume that the DTIM acquired by the STA1 220 indicates that a frame to be transmitted to the STA1 220 is not present and a frame for another STA is present. In this case, the STA1 220 may confirm that a frame transmitted thereby is not present and may be switched to the sleep state again. The AP 210 transmits the beacon frame and then transmits the frame to the STA (S232).
The AP 210 fourthly transmits the beacon frame (S214). Since the STA1 220 cannot acquire information indicating that buffered traffic therefor is present via reception of the TIM element twice, the wakeup interval for receiving the TIM element may be controlled. Alternatively, if signaling information for controlling the wakeup interval of the STA1 220 is included in the beacon frame transmitted by the AP 210, the wakeup interval value of the STA1 220 may be controlled. In the present example, the STA1 220 may change switching of the operation state for receiving the TIM element every beacon interval to switching of the operation state every three beacon intervals. Accordingly, since the STA1 220 is maintained in the sleep state when the AP 210 transmits the fourth beacon frame (S214) and transmits the fifth beacon frame (S215), the TIM element cannot be acquired.
When the AP 210 sixthly transmits the beacon frame (S216), the STA1 220 may be switched to the awake state to acquire the TIM element included in the beacon frame (S224). Since the TIM element is a DTIM indicating that a broadcast frame is present, the STA1 220 may not transmit the PS-Poll frame to the AP 210 but may receive a broadcast frame transmitted by the AP 210 (S234). The wakeup interval set in the STA2 230 may be set to be greater than that of the STA1 220. Accordingly, the STA2 230 may be switched to the awake state to receive the TIM element (S241), when the AP 210 fifthly transmits the beacon frame (S215). The STA2 230 may confirm that a frame to be transmitted thereto is present via the TIM element and transmits the PS-Poll frame to the AP 210 (S241a) in order to request frame transmission. The AP 210 may transmit the frame to the STA2 230 in correspondence with the PS-Poll frame (S233).
For PM management shown in FIG. 9, a TIM element includes a TIM indicating whether a frame to be transmitted to an STA is present and a DTIM indicating whether a broadcast/multicast frame is present. The DTIM may be implemented by setting a field of the TIM element.
FIGS. 10 to 12 are diagrams illustrating operation of a station (STA) which receives a traffic indication map (TIM).
Referring to FIG. 10, an STA may be switched from a sleep state to an awake state in order to receive a beacon frame including a TIM from an AP and interpret the received TIM element to confirm that buffered traffic to be transmitted thereto is present. The STA may contend with other STAs for medium access for transmitting a PS-Poll frame and then transmit the PS-Poll frame in order to request data frame transmission from the AP. The AP which receives the PS-Poll frame transmitted by the STA may transmit the frame to the STA. The STA may receive the data frame and transmit an ACK frame to the AP. Thereafter, the STA may be switched to the sleep state again.
As shown in FIG. 10, the AP may receive the PS-Poll frame from the STA and then operate according to an immediate response method for transmitting a data frame after a predetermined time (e.g., a short inter-frame space (SIFS)). If the AP does not prepare a data frame to be transmitted to the STA during the SIFS after receiving the PS-Poll frame, the AP may operate according to a deferred response method, which will be described with reference to FIG. 11.
In the example of FIG. 11, operation for switching the STA from the sleep state to the awake state, receiving a TIM from the AP, contending and transmitting a PS-Poll frame to the AP is equal to that of FIG. 10. If the data frame is not prepared during the SIFS even when the AP receives the PS-Poll frame, the data frame is not transmitted but an ACK frame may be transmitted to the STA. If the data frame is prepared after transmitting the ACK frame, the AP may contend and transmit the data frame to the STA. The STA may transmit the ACK frame indicating that the data frame has been successfully received to the AP and may be switched to the sleep state.
FIG. 12 shows an example in which the AP transmits the DTIM. The STAs may be switched from the sleep state to the awake state in order to receive the beacon frame including the DTIM element from the AP. The STA may confirm that a multicast/broadcast frame will be transmitted via the received DTIM. The AP may immediately transmit data (that is, a multicast/broadcast frame) without PS-Poll frame transmission and reception after transmitting the beacon frame including the DTIM. The STAs may receive data in the awake state after receiving the beacon frame including the DTIM and may be switched to the sleep state again after completing data reception.
2.5 TIM Structure
In the PM mode management method based on the TIM (or DTIM) protocol described with reference to FIGS. 9 to 12, the STAs may confirm whether a data frame to be transmitted thereto is present via STA identification included in the TIM element. The STA identification may be related to an association identifier (AID) assigned to the STA upon association with the AP.
The AID is used as a unique identifier for each STA within one BSS. For example, in a current WLAN system, the AID may be one of values of 1 to 2007. In a currently defined WLAN system, 14 bits are assigned to the AID in a frame transmitted by the AP and/or the STA. Although up to 16383 may be assigned as the AID value, 2008 to 16383 may be reserved.
The TIM element according to an existing definition is not appropriately applied to an M2M application in which a large number (e.g., more than 2007) of STAs is associated with one AP. If the existing TIM structure extends without change, the size of the TIM bitmap is too large to be supported in an existing frame format and to be suitable for M2M communication considering an application with a low transfer rate. In addition, in M2M communication, it is predicted that the number of STAs, in which a reception data frame is present during one beacon period, is very small. Accordingly, in M2M communication, since the size of the TIM bitmap is increased but most bits have a value of 0, there is a need for technology for efficiently compressing the bitmap.
As an existing bitmap compression technology, a method of omitting 0 which continuously appears at a front part of a bitmap and defining an offset (or a start point) is provided. However, if the number of STAs in which a buffered frame is present is small but a difference between the AID values of the STAs is large, compression efficiency is bad. For example, if only frames to be transmitted to only two STAs respectively having AID values of 10 and 2000 are buffered, the length of the compressed bitmap is 1990 but all bits other than both ends have a value of 0. If the number of STAs which may be associated with one AP is small, bitmap compression inefficiency is not problematic but, if the number of STAs is increased, bitmap compression inefficiency deteriorates overall system performance.
As a method of solving this problem, AIDs may be divided into several groups to more efficiently perform data transmission. A specific group ID (GID) is assigned to each group. AIDs assigned based on the group will be described with reference to FIG. 13.
FIG. 13(a) shows an example of AIDs assigned based on a group. In the example of FIG. 13(a), several bits of a front part of the AID bitmap may be used to indicate the GID. For example, four DIDs may be expressed by the first two bits of the AID of the AID bitmap. If the total length of the AID bitmap is N bits, the first two bits (B1 and B2) indicate the GID of the AID.
FIG. 13(a) shows another example of AIDs assigned based on a group. In the example of FIG. 13(b), the GID may be assigned according to the location of the AID. At this time, the AIDs using the same GID may be expressed by an offset and a length value. For example, if GID 1 is expressed by an offset A and a length B, this means that AIDs of A to A+B-1 on the bitmap have GID 1. For example, in the example of FIG. 13(b), assume that all AIDs of 1 to N4 are divided into four groups. In this case, AIDs belonging to GID 1 are 1 to N1 and may be expressed by an offset 1 and a length N1. AIDs belonging to GID2 may be expressed by an offset N1+1 and a length N2-N1+1, AIDs belonging to GID 3 may be expressed by an offset N2+1 and a length N3-N2+1, and AIDs belonging to GID 4 may be expressed by an offset N3+1 and a length N4-N3+1.
If the AIDs assigned based on the group are introduced, channel access is allowed at a time interval which is changed according to the GID to solve lack of TIM elements for a large number of STAs and to efficiently perform data transmission and reception. For example, only channel access of STA(s) corresponding to a specific group may be granted during a specific time interval and channel access of the remaining STA(s) may be restricted. A predetermined time interval at which only access of specific STA(s) is granted may also be referred to as a restricted access window (RAW).
Channel access according to GID will be described with reference to FIG. 13(c). FIG. 13(c) shows a channel access mechanism according to a beacon interval if the AIDs are divided into three groups. At a first beacon interval (or a first RAW), channel access of STAs belonging to GID 1 is granted but channel access of STAs belonging to other GIDs is not granted. For such implementation, the first beacon includes a TIM element for AIDs corresponding to GID 1. A second beacon frame includes a TIM element for AIDs corresponding to GID 2 and thus only channel access of the STAs corresponding to the AIDs belonging to GID 2 is granted during the second beacon interval (or the second RAW). A third beacon frame includes a TIM element for AIDs corresponding to GID 3 and thus only channel access of the STAs corresponding to the AIDs belonging to GID 3 is granted during the third beacon interval (or the third RAW). A fourth beacon frame includes a TIM element for AIDs corresponding to GID 1 and thus only channel access of the STAs corresponding to the AIDs belonging to GID 1 is granted during the fourth beacon interval (or the fourth RAW). Only channel access of the STAs corresponding to a specific group indicated by the TIM included in the beacon frame may be granted even in fifth and subsequent beacon intervals (or fifth and subsequent RAWs).
Although the order of GIDs allowed according to the beacon interval is cyclic or periodic in FIG. 13(c), the present invention is not limited thereto. That is, by including only AID(s) belonging to specific GID(s) in the TIM elements, only channel access of STA(s) corresponding to the specific AID(s) may be granted during a specific time interval (e.g., a specific RAW) and channel access of the remaining STA(s) may not be granted.
The above-described group based AID assignment method may also be referred to as a hierarchical structure of a TIM. That is, an entire AID space may be divided into a plurality of blocks and only channel access of STA(s) corresponding to a specific block having a non-zero value (that is, STAs of a specific group) may be granted. A TIM having a large size is divided into small blocks/groups such that the STA easily maintains TIM information and easily manages blocks/groups according to class, QoS or usage of the STA. Although a 2-level layer is shown in the example of FIG. 13, a TIM of a hierarchical structure having two or more levels may be constructed. For example, the entire AID space may be divided into a plurality of page groups, each page group may be divided into a plurality of blocks, and each block may be divided into a plurality of sub-blocks. In this case, as an extension of the example of FIG. 13(a), the first N1 bits of the AID bitmap indicate a paging ID (that is, a PID), the next N2 bits indicate a block ID, the next N3 bits indicate a sub-block ID, and the remaining bits indicate the STA bit location in the sub-block.
In the following examples of the present invention, various methods of dividing and managing STAs (or AIDs assigned to the STAs) on a predetermined hierarchical group basis are applied and the group based AID assignment method is not limited to the above examples.
2.6 Improved Channel Access Method
If AIDs are assigned/managed based on a group, STAs belonging to a specific group may use a channel only at a "group channel access interval (or RAW)" assigned to the group. If an STA supports an M2M application, traffic for the STA may have a property which may be generated at a long period (e.g., several tens of minutes or several hours). Since such an STA does not need to be in the awake state frequently, the STA may be in the sleep mode for g a long period of time and be occasionally switched to the awake state (that is, the awake interval of the STA may be set to be long). An STA having a long wakeup interval may be referred to as an STA which operates in a "long-sleeper" or "long-sleep" mode. The case in which the wakeup interval is set to be long is not limited to M2M communication and the wakeup interval may be set to be long according to the state of the STA or surroundings of the STA even in normal WLAN operation.
If the wakeup interval is set, the STA may determine whether a local clock thereof exceeds the wakeup interval. However, since the local clock of the STA generally uses a cheap oscillator, an error probability is high. In addition, if the STA operates in long-sleep mode, the error may be increased with time. Accordingly, time synchronization of the STA which occasionally wakes up may not match time synchronization of the AP. For example, although the STA computes when the STA may receive the beacon frame to be switched to the awake state, the STA may not actually receive the beacon frame from the AP at that timing. That is, due to clock drift, the STA may miss the beacon frame and such a problem may frequently occur if the STA operates in the long sleep mode.
FIGS. 14 to 16 are diagrams showing examples of operation of an STA if a group channel access interval is set.
In the example of FIG. 14, STA3 may belong to group 3 (that is, GID=3), wake up at a channel access interval assigned to group 1 and perform PS-Poll for requesting frame transmission from the AP. The AP which receives PS-Poll from the STA transmits an ACK frame to STA3. If buffered data to be transmitted to STA3 is present, the AP may provide information indicating that data to be transmitted is present via the ACK frame. For example, the value of a "More Data" field (or an MD field) having a size of 1 bit included in the ACK frame may be set to 1 (that is, MD=1) to indicate the above information.
Since a time when STA3 transmits PS-Poll belongs to the channel access interval for group 1, even if data to be transmitted to STA3 is present, the AP does not immediately transmit data after transmitting the ACK frame but transmits data to STA3 at a channel access interval (GID 3 channel access of FIG. 14) assigned to group 3 to which STA3 belongs.
Since STA3 receives the ACK frame set to MD=1 from the AP, STA3 continuously waits for transmission of data from the AP. That is, in the example of FIG. 14, since STA3 cannot receive the beacon frame immediately after waking up, STA3 transmits PS-Poll to the AP on the assumption that a time when STA3 wakes up corresponds to the channel access interval assigned to the group, to which STA3 belongs, according to computation based on the local clock thereof and data to be transmitted thereto is present. Alternatively, since STA3 operates in the long-sleep mode, on the assumption that time synchronization is not performed, if the data to be transmitted thereto is present, STA3 may transmit PS-Poll to the AP in order to receive the data. Since the ACK frame received by STA3 from the AP indicates that data to be transmitted to STA3 is present, STA3 continuously waits for data reception under the assumption of the interval in which channel access thereof is granted. STA3 unnecessarily consumes power even when data reception is not allowed, until time synchronization is appropriately performed from information included in a next beacon frame.
In particular, if STA3 operates in the long-sleep mode, the beacon frame may frequently not be received, CCA may be performed even at the channel access interval, to which STA2 does not belong, thereby causing unnecessary power consumption.
Next, in the example of FIG. 15, the beacon frame is missed when the STA having GID 1 (that is, belonging to group 1) wakes up. That is, the STA which does not receive the beacon frame including the GID (or PID) assigned thereto is continuously in the awake state until the beacon frame including the GID (or PID) thereof is received. That is, although the STA wakes up at channel access interval assigned thereto, the STA cannot confirm whether the GID (or PID) thereof is included in the TIM transmitted via the beacon frame and thus cannot confirm whether the timing corresponds to the channel access interval assigned to the group thereof.
In the example of FIG. 15, the STA which is switched from the sleep state to the awake state is continuously in the awake state until the fourth beacon frame including the GID (that is, GID 1) thereof is received after the first beacon frame has been missed, thereby causing unnecessary power consumption. As a result, after unnecessary power consumption, the STA may receive the beacon frame including GID 1 and then may perform RTS transmission, CTS reception, data frame transmission and ACK reception.
FIG. 16 shows the case in which an STA wakes up at a channel access interval for another group. For example, the STA having GID 3 may wake up at the channel access interval for GID 1. That is, the STA having GID 3 unnecessarily consumes power until the beacon frame having the GID thereof is received after waking up. If a TIM indicating GID 3 is received via a third beacon frame, the STA may recognize the channel access interval for the group thereof and perform data transmission and ACK reception after CCA through RTS and CTS.
3. Proposed Pilot Sequence Transmission and Reception Methods
As interest in future Wi-Fi and demand for improvement of yield and QoE (quality of experience) after 802.11ac increase, it is necessary to define a new frame format for future WLAN systems. The most important part in a new frame format is a preamble part because design of a preamble used for synchronization, channel tracking, channel estimation, adaptive gain control (AGC) and the like may directly affect system performance.
In the future Wi-Fi system in which a large number of APs and STAs simultaneously access and attempt data transmission and reception, system performance may be limited when legacy preamble design is employed. That is, if each preamble block (e.g., a short training field (STF) in charge of AGC, CFO estimation/compensation, timing control and the like or a long training field (LTF) in charge of channel estimation/compensation, residual CFO compensation and the like) executes only the function thereof defined in the legacy preamble structure, frame length increases, causing overhead. Accordingly, if a specific preamble block can support various functions in addition to the function designated therefor, an efficient frame structure can be designed.
Furthermore, since the future Wi-Fi system considers data transmission in outdoor environments as well as indoor environments, the preamble structure may need to be designed differently depending on environments. Although design of a unified preamble format independent of environment variation can aid in system implementation and operation, of course, it is desirable that preamble design be adapted to system environment.
Preamble design for efficiently supporting various functions is described hereinafter. For convenience, a new WLAN system is referred to as an HE (High Efficiency) system and a frame and a PPDU (PLCP (Physical Layer Convergence Procedure) Protocol Data Unit) of the HE system are respectively referred to as an HE frame and an HE PPDU. However, it is obvious to those skilled in the art that the proposed preamble is applicable to other WLAN systems and cellular systems in addition to the HE system.
The following table 1 shows OFDM numerology which is a premise of a pilot sequence transmission method described below. Table 1 shows an example of new OFDM numerology proposed in the HE system and numerals and items shown in Table 1 are merely examples and other values may be applied. Table 1 is based on the assumption that FFT having a size four times the legacy one is applied to a given BW and 3 DCs are used per BW.
TABLE-US-00001 TABLE 1 Parameter CBW20 CBW40 CBW80 CBW80 + 80 CBW160 Description N.sub.FFT 256 512 1024 1024 2048 FFT size N.sub.SD 238 492 1002 1002 2004 Number of complex data numbers per frequency segment N.sub.SP 4 6 8 8 16 Number of pilot values per frequency segment N.sub.ST 242 498 1010 1010 2020 Total number of subcarriers per frequency segment. See NOTE. N.sub.SR 122 250 506 506 1018 Highest data subcarrier index per frequency segment N.sub.Seg 1 1 1 2 1 Number of frequency segments .DELTA..sub.F 312.5 kHz Subcarrier frequency Spacing for non-HE portion .DELTA..sub.F HE 78.125 kHz Subcarrier frequency Spacing for HE portion T.sub.DFT 3.2 .mu.s IDFT/DFT period for non-HE portion T.sub.DFT_HE 12.8 .mu.s IDFT/DFT period for HE portion T.sub.GI 0.8 .mu.s = T.sub.DFT/4 Guard interval duration for non- HE portion T.sub.GI_HE 3.2 .mu.s = T.sub.DFT_HE/4 Guard interval duration for HE portion T.sub.GI2 1.6 .mu.s Double guard interval for non-HE portion T.sub.GIS HE 0.8 .mu.s = T.sub.DFT_HE/16 Short guard interval [Alternative: 0.4 .mu.s (1/32 CP)] Duration (used only for HE data) T.sub.SYML 4 .mu.s = T.sub.DFT + T.sub.GI Long GI symbol interval for non-HE portion T.sub.SYML_HE 16 .mu.s = T.sub.DFT_HE + T.sub.GI_HE Long GI symbol interval for HE portion T.sub.SYMS_HE 13.6 .mu.s = T.sub.DFT_HE + T.sub.GIS_HE Short GI symbol [Alternative: 13.2 .mu.s (with 1/32 CP)] interval (used only for HE data) T.sub.SYM T.sub.SYML or T.sub.SYMS depending on the GI used Symbol interval for non-HE portion T.sub.SYM HE T.sub.SYML_HE or T.sub.SYMS_HE depending on the GI used Symbol interval for HE portion T.sub.L-STF 8 .mu.s = 10 * T.sub.DFT/4 Non-HE Short Training field duration T.sub.L-LTF 8 .mu.s = 2 .times. T.sub.DFT + T.sub.GI2 Non-HE Long Training field duration T.sub.L-SIG 4 .mu.s = T.sub.SYML Non-HE SIGNAL field duration T.sub.HE-SIGA 12.8 .mu.s = 2(T.sub.SYML + 3T.sub.GI) in HE- HE Signal A field PPDU format-1 or T.sub.SYML_HE in HE- duration PPDU format-2 and HE-PPDU format-3 T.sub.HE-STF T.sub.SYML_HE HE Short Training field duration T.sub.HE-LTF T.sub.SYML_HE Duration of each HE LTF symbol T.sub.HE-SIGB T.sub.SYML_HE HE Signal B field duration N.sub.service 16 Number of bits in the SERVICE field N.sub.tail 6 Number of tail bits per BCC encoder NOTE N.sub.ST = N.sub.SD + N.sub.SP
FIG. 17 is a diagram illustrating frame structures related to an embodiment of the present invention. As illustrated in FIGS. 17(a), 17(b) and 17(c), various frame structures can be configured, and a proposed pilot sequence transmission method is related to an HE-STF (High Efficiency Short Training Field) in a preamble in a frame structure.
FIG. 18 is a diagram illustrating a pilot sequence related to an embodiment of the present invention. The HE-STF illustrated in FIG. 17 is a part of a preamble and carries pilot signals for channel estimation, CFO (Carrier Frequency Offset) estimation, symbol timing estimation and the like. Sequentially transmitted pilot signals are called a pilot sequence. FIG. 18 illustrates general design of a pilot sequence in the HE-STF. In FIG. 18, the upper graph shows a pilot sequence in the frequency domain and the lower graph shows a pilot sequence in the time domain.
The pilot sequence in the frequency domain is defined by a guard interval, a pilot distance and a pilot signal magnitude. In the example shown in FIG. 18, small arrows in the pilot sequence in the frequency domain indicate pilot signals having a magnitude of 0 and a distance between neighboring pilot signals is 2 (i.e., pilot distance=2). When the guard interval is a multiple of the pilot distance (a multiple of 2), if pilot signals in the frequency domain are transformed into the time domain, pilot signals in the time domain have a repeated pattern as shown in the lower part of FIG. 18. When signals in a first period are referred to as first signals and signals in a second period are referred to as second signals, the first signals and the second signals have the same pattern.
If the pilot distance of the pilot signals in the frequency domain is 4 and the guard interval is a multiple of 4, the pilot signals in the time domain are defined as 4 repeated patterns and first/second/third/fourth signals have the same pattern. Such definition of signals in a repeated pattern in the time domain is meaningful because it enables accurate symbol timing and CFO estimation without channel information.
FIG. 19 is a diagram illustrating cyclic shifting of a pilot sequence. FIG. 19 illustrates first signals in the time domain, shown in FIG. 18, and signals shifting from the first signals. A plurality of pilot sequences generated through shifting of a specific pilot sequence is called a sequence set, and a transmitter selects a pilot sequence from a sequence set and transmits the selected pilot sequence to a receiver. Shifting of a pilot signal in the time domain can be understood as a process of changing the phase of the pilot signal, whereas shifting of a pilot signal in the frequency domain can be understood as cyclic shifting.
In FIG. 19, a transmitter selects a pilot sequence (or simply a sequence) from a sequence set composed of 4 pilot sequences (shifting=0, 1, 2 and 3) generated through shifting and transmits the selected pilot sequence to a receiver. The receiver can identify the received pilot sequence from among the 4 pilot sequences. This procedure can be performed through a process of calculating correlation with respect to received signal by the receiver. The receiver can detect the received pilot sequence by comparing results of correlation between previously stored pilot sequences and received signals.
As the receiver can discriminate the 4 pilot sequences, the transmitter can transmit 2 bits of additional information to the receiver. That is, upon determining that a case of transmitting a pilot sequence of shifting=0 and a case of transmitting a pilot sequence of shifting=1 indicate different pieces of information between the transmitter and the receiver, the receiver can acquire the additional information corresponding to 2 bits depending on which pilot sequence in the sequence set is received. This additional information is called a "signature".
In FIG. 19, four different pilot sequences can be transmitted to the receiver and the receiver can discriminate the four pilot sequences. Transmitted pilot sequences in the sequence set respectively correspond to four different pieces of information, and thus the receiver can acquire additional information (i.e., a signature) corresponding to 2 bits. Specifically, the receiver can recognize that 2 bits information corresponding to "00" is received when the pilot sequence of shifting=0 is received, recognize that 2 bits information corresponding to "01" is received when the pilot sequence of shifting=1 is received, recognize that 2 bits information corresponding to "10" is received when the pilot sequence of shifting=2 is received and recognize that 2 bits of information corresponding to "11" is received when the pilot sequence of shifting=3 is received.
FIG. 20 is a diagram illustrating a receiver structure for identification of a pilot sequence and FIG. 21 is a diagram illustrating signals of a sequence set received by the receiver. A description will be given of FIGS. 20 and 21.
A receiver structure for identifying a received pilot sequence may be implemented as shown in FIG. 20. In FIG. 20, N is the length of a first signal, r is a received vector in the time domain, t.sup.(i) is the vector of an i-th shifting pilot sequence and y.sub.i=|r.sup.it.sup.(i)|.
An environment having no AWGN (Additive White Gaussian Noise) channel and noise is assumed. When the transmitter transmits the first sequence from among the pilot sequences shown in FIG. 19, the receiver calculates {y0, y1, y2, y3} as shown in FIG. 21. Then, the receiver can identify the sequence transmitted by the transmitter from the sequence set by detecting yi having the highest magnitude from among {y0, y1, y2, y3}.
FIG. 22 is a diagram illustrating a sequence set composed of pilot sequences generated at a predetermined interval.
Meanwhile, the aforementioned communication method of the transmitter and the receiver has a disadvantage of performance deterioration in multipath environments. To overcome this disadvantage, pilot sequences of a sequence set are generated at a predetermined interval and used, as illustrated in FIG. 22.
Compared to the pilot sequences of FIG. 19, the pilot sequences shown in FIG. 22 are generated at a shifting interval of 4. The shifting interval is determined by a channel effective delay period L. When the transmitter transmits a sequence with shifting-0 in a noise-free environment, the receiver having the structure shown in FIG. 20 can calculate a received signal yi as illustrated in FIG. 23.
FIG. 23 is a diagram illustrating received signals of the sequence set illustrated in FIG. 22. In FIG. 23, the size W of a zero correlation zone (ZCZ) is determined as a maximum shifting value L of the sequence (W=L). The receiver selects the highest signal yi in each ZCZ and compares highest signals yi selected in respective ZCZs to select a ZCZ having the highest value. Referring to FIG. 23, the first ZCZ has {y0, y1, y2, y3} higher than other ZCZs, which is caused by delay spread of transmitted signals due to reception through multiple paths. The receiver can identify a sequence transmitted by the transmitter without error by setting a ZCZ larger than the effective channel delay period.
When the sequence set shown in FIG. 19 instead of the sequence set shown in FIG. 22 is used, the size of the ZCZ is 1 (W=1). In this case, it is necessary to identify a sequence by comparing all results {y.sub.0, y.sub.1, . . . , y.sub.N-1} of processing of received signals because y.sub.0, y.sub.1, . . . , y.sub.N-1 are representative values of respective ZCZs. If the transmitter transmits a sequence with shifting=0, one of {y1, y2, y3} may have a value greater than y.sub.0, abruptly decreasing the identification performance of the receiver.
As the sequence interval decreases, the number of signatures that can be generated increases. For example, when the sequence interval is set to 1 in FIG. 22, a total of 16 signatures can be defined. That is, as the interval of pilot sequences forming a sequence set decreases, the number of generated signatures can increase to transmit more information. In this case, however, tradeoff of deterioration of the identification performance of the receiver is generated.
FIG. 24 is a diagram illustrating a timing offset. FIG. 24 shows a process of receiving one OFDM symbol through two paths. It can be confirmed that a signal received through the second path is delayed from a signal transmitted through the first path. In general, a receiver estimates the start point of an OFDM symbol as a point between the guard interval (GI) start point of the first path and the GI end point of the second path. With respect to the estimated start point (ESP), a timing offset NTO is represented by the following mathematical expression 1. That is, the timing offset is represented as a difference between the ESP and the start point (SP) of the first symbol. N.sub.TO=ESP-1st SP [Expression 1]
If the receiver determines the ESP within an inter-symbol-interference-free (ISI) period, ISI can be avoided. That is, orthogonality between subcarriers can be maintained in an OFDM symbol.
FIG. 25 is a diagram illustrating received signals considering a timing offset. The timing offset described above affects the signature identification performance of the receiver. For example, when the timing offset N.sub.TO is 4, FIG. 23 is modified into FIG. 25.
Distinguished from FIG. 23, all values yi are shifted by 4 in FIG. 25. If the receiver knows the timing offset, the receiver can correctly identify the received sequence by shifting a window by the timing offset. If the receiver does not know the timing offset, the receiver misrecognizes the shifting value of the received sequence and thus determines that an incorrect sequence has been received.
FIG. 26 is a diagram illustrating a procedure of controlling the size of the ZCZ in consideration of a timing offset. FIG. 26 illustrates a method for solving the aforementioned problem.
In FIG. 26, a maximum timing offset that can be generated is defined as N.sub.TO and a minimum shifting value between sequences forming a sequence set in a process of generating the sequence set is defined as L+N.sub.TO. In addition, the receiver defines the size of the ZCZ as L+N.sub.TO corresponding to the sum of the effective channel delay period and TO. Distinguished from FIG. 25, an error caused by the timing offset is not generated because the window is sufficiently large in FIG. 26. On the other hands, the large window causes tradeoff that the number of signatures that can be identified between the transmitter and the receiver is reduced from 4 to 2.
FIG. 27 is a diagram illustrating a pilot sequence using a CAZAC (Constant Amplitude Zero Auto Correlation) sequence.
FIG. 27 illustrates an embodiment in which a Chu sequence having a length of N.sub.s is used as pilot signals in the frequency domain. In FIG. 27, it is assumed that OFMD symbol length N.sub.o satisfies N.sub.o=.alpha.N.sub.s (.alpha. is a positive number greater than 0). Here, first signals and second signals have properties of the CAZAC sequence.
All pilot sequences of the time domain have a constant amplitude. In addition, the sequences have zero auto-correlation except themselves. That is, first signals and second signals have CAZAC properties.
When the CAZAC sequence is used in the time domain as described above, various advantages can be obtained. All pilot sequences have a magnitude of 1 and thus PAPR (Peak to Average Power Ratio) becomes 1. The PAPR is defined as the ratio of peak power to average power and has a minimum value of 1. The peak power means highest power from among powers of time domain elements and the average power means average power of the time domain elements.
When a transmitter amplifies OFDM symbols, a maximum number of OFDM symbols that can be amplified is determined by an element having a maximum magnitude from among the time domain elements. This is because all time elements of OFDM symbols should not exceed peak power when the OFDM symbols are amplified by an amplifier. Accordingly, when all symbols have a magnitude of 1, sequences can be amplified to peak power of the amplifier and transmitted. That is, OFDM symbols can be amplified to peak power of the amplifier and transmitted, increasing SNR.
When a sequence satisfying zero auto-correlation (ZAC) is used in the time domain, y.sub.1, y.sub.2 and y.sub.3 become 0 in FIG. 23. This property improves identification performance of the receiver. If a sequence having no ZAC property is used, all y.sub.1, y.sub.2 and y.sub.3 are non-zero, decreasing identification performance of the receiver. In other words, identification performance of the receiver is reduced when sequences have a correlation therebetween.
A description will be given of a proposed pilot sequence transmission method with reference to FIGS. 28 to 32.
A transmitter generates a baseline sequence and then shifts the baseline sequence in the time domain to generate a plurality of pilot sequences. The generated pilot sequences form a sequence set and are mapped to different pieces of additional information (i.e., a signature) as described above.
While the CAZAC sequence has been described above, a guard interval (or a guard band) is present before pilot signals in the frequency domain, similarly to the structure shown in FIG. 18, in an actually implemented system. Accordingly, a pilot sequence does not have the CAZAC properties as in FIG. 27, resulting in N.sub.o.noteq..alpha.N.sub.s. For example, FIG. 28 illustrates the magnitude and auto-correlation of first signals when N.sub.o=256 and N.sub.s=122. Referring to FIG. 28, samples have different magnitudes (non-constant amplitude) and non-zero auto-correlation at non-zero shifting values can be confirmed. A sequence having such properties is called a non-CAZAC sequence hereinafter.
In the case of non-CAZAC sequence, sequences have a non-zero correlation therebetween and {y.sub.1, y.sub.2, y.sub.3} illustrated in FIG. 21 have values greater than 0. FIG. 29 shows that all elements yi have non-zero values when the non-CAZAC sequence is used. This means that non-zero values are generated in zones other than a ZCZ with respect to a pilot sequence transmitted by the transmitter, and thus performance of the receiver is deteriorated compared to cases using the CAZAC sequence. A degree of performance deterioration is determined by a largest value from among values generated in ZCZs to which a received pilot sequence does not belong. For example, y.sub.13 determines identification performance of the receiver in FIG. 29.
In view of this, the transmitter can configure a sequence set in consideration of a correlation between sequences in a procedure of designing the sequence set based on a non-CAZAC sequence. Specifically, in a procedure of shifting the baseline sequence to generate pilot sequences, the transmitter according to an embodiment determines a shifting value such that a correlation between pilot sequences is minimized.
FIG. 30 illustrates variations in a correlation between sequences depending on shifting value differences. For example, when a correlation corresponding to a shifting value of 0 is defined as 1, it can be seen from FIG. 30 that correlations are -13 dB and -30-dB when the shifting value is 1 and 21, respectively. Accordingly, the transmitter can generate a sequence set in consideration of correlation variations depending on shifting value differences. This will be described below in detail.
In the following, t.sup.(0) denotes a baseline sequence and t.sup.(i) denotes a pilot sequence shifted from the baseline sequence by i. Two sequence sets as represented by the following mathematical expression 2 can be considered with reference to FIG. 30. Set A: {t.sup.(0),t.sup.(1),t.sup.(2),t.sup.(3), . . . ,t.sup.(127)} Set B: {t.sup.(11),t.sup.(21),t.sup.(42),t.sup.(63)} [Expression 2]
In the case of sequence set A, a sequence distance (i.e., shifting value) is 1 and a largest correlation difference is -13 dB. In the case of sequence set B, a sequence distance is 21 and a largest correlation difference is -29 dB. Since properties of sequences become closer to CAZAC properties to improve receiver performance as a correlation between the sequences decreases, sequence set B provides better receiver identification performance than sequence set A. However, when sequence set A is used, a larger number of signatures than sequence set B can be defined and transmitted to the receiver.
As described above, the transmitter can determine a shifting value such that a correlation between pilot sequences is minimized to configure a sequence set. According to another embodiment, a minimum shifting value can be determined in consideration of a channel effective delay period L and a timing offset N.sub.TO in the procedure of generating a sequence set.
The channel effective delay period L can be defined to be shorter than delay spread length of an actual channel. The influence of delay spread on receiver performance has been described with reference to FIG. 23 and the influence of a timing offset on receiver performance has been described with reference to FIG. 25. In addition, performance deterioration due to a correlation between sequences when the non-CAZAC sequence is used has been described with reference to FIG. 29.
Accordingly, in determination of a shifting value of pilot sequences, a minimum shifting value can be determined on the basis of the channel effective delay period L and the timing offset N.sub.TO and then a shifting value capable of minimizing a correlation between sequences can be finally determined on the basis of the determined minimum shifting value.
For example, the transmitter determines a minimum shifting value as L+N.sub.TO as illustrated in FIG. 26. Then, the transmitter determines a shifting value capable of minimizing a correlation between pilot sequences using auto-correlation values described with reference to FIG. 30. A sequence set generated through this procedure secures receiver performance robust against delay spread and timing offset. This causes tradeoff that a maximum number of signatures that can be defined by the generated sequence set is limited to mathematical expression 3.
.function..times..times. ##EQU00001##
If the receiver can estimate the timing offset, the receiver can shift a window by the timing offset to correctly identify a received pilot sequence, as illustrated in FIG. 25. In this case, the transmitter may not consider the timing offset in the procedure of generating the sequence set and may determine the minimum shifting value as L without considering the timing offset. In this embodiment, a maximum number of defined signatures is represented by mathematical expression 4.
.times..times. ##EQU00002##
A description will be given of an embodiment using a quantized Chu sequence with reference to FIG. 31.
The procedure of generating first signals and second signals using a Chu sequence as a pilot sequence has been described with reference to FIG. 27. Values of samples of the Chu sequence are defined through subdivided phase differences, and hardware of the transmitter needs to discriminate and control such phases in order to support the Chu sequence. If not, an error vector magnitude (EVM) may be generated. The EVM refers to a problem that a transmitter transmits signals out of points on a constellation which are originally intended to be transmitted due to imperfect hardware. For example, although the transmitter intends to transmit QPSK signals denoted by a square in FIG. 31, the transmitter transmits a signal denoted by a triangle when EVM is generated.
To solve this problem, the transmitter can quantize a Chu sequence and then use the quantize Chu sequence as pilot signals. Then, the transmitter generates a baseline sequence in the time domain through IFFT (Inverse Fast Fourier Transform). In this manner, the transmitter can generate a baseline sequence and a sequence set in consideration of accuracy of phase control supportable by hardware.
A sequence set based on the quantized Chu sequence has an increasing PAPR compared to a sequence set generated based on the Chu sequence. The following table 2 shows root indices and PAPRs of a pilot sequence according to constellations when N.sub.o=256 and N.sub.s=122.
TABLE-US-00002 TABLE 2 Root index 1 15 BPSK 4.2039 4.5864 QPSK 2.5323 3.5769 8-PSK 1.9833 2.9272 16-PSK 1.8554 3.545 32-PSK 1.8295 2.8135 Chu 1.7826 2.9513
As can be seen from Table 2, PAPR decreases as constellation increases when the same root index is used. In Table 2, "Chu" represents a non-quantized case and has a PAPR gain of 0.46 dB compared to the 8-PSK (Phase Shift Keying) case. Accordingly, a sufficiently low PAPR can be provided through the quantized Chu sequence even when 8-PSK is used.
In FIG. 31, points denoted by a circle represent the phase of the Chu sequence before quantization and points denoted by a square represent the phase of QPSK (Quadrature Phase Shift Keying). Quantization of the Chu sequence through QPSK refers to a procedure of approximating the points denoted by a circle to closest square points.
As described above, the transmitter can generate a sequence set such that a correlation between pilot sequences is minimized when a non-CAZAC sequence is used. Accordingly, the transmitter can secure performance of the receiver while transmitting a signature.
FIG. 32 is a flowchart illustrating operation processes of a transmitter and a receiver according to a proposed embodiment. FIG. 32 illustrates a time series flow based on the aforementioned embodiments and the above description can be equally or similarly applied to the flow even if the flow is not described in detail.
The transmitter generates a sequence set such that a correlation between pilot sequences is minimized (S3210). This process can be performed through a procedure of controlling a shifting value during shifting of a baseline sequence. For example, the transmitter can determine a minimum shifting value in consideration of a channel effective delay period or a timing offset. The transmitter can finally determine a shifting value that minimizes a correlation between pilot sequences in consideration of a correlation between pilot sequences depending on a shifting value. Alternatively, the transmitter may configure a sequence set using a quantized Chu sequence.
Subsequently, the transmitter transmits a pilot sequence selected from the generated sequence set (S3220). Pilot sequences included in the sequence set are mapped to additional information (a signature) represented by different bits. Accordingly, the receiver receives the pilot sequence (S3230) and obtains additional information transmitted by the transmitter by identifying the received pilot sequence (S3240). That is, the receiver can recognize the additional information intended to be transmitted by the transmitter by identifying the shifting value of the received pilot sequence.
4. Apparatus Configuration
FIG. 33 is a block diagram showing the configuration of a reception module and a transmission module according to one embodiment of the present invention. In FIG. 33, a reception module 100 and the transmission module 150 may include radio frequency (RF) units 110 and 160, processors 120 and 170 and memories 130 and 180, respectively. Although a 1:1 communication environment between the reception module 100 and the transmission module 150 is shown in FIG. 33, a communication environment may be established between a plurality of reception module and the transmission module. In addition, the transmission module 150 shown in FIG. 33 is applicable to a macro cell base station and a small cell base station.
The RF units 110 and 160 may include transmitters 112 and 162 and receivers 114 and 164, respectively. The transmitter 112 and the receiver 114 of the reception module 100 are configured to transmit and receive signals to and from the transmission module 150 and other reception modules and the processor 120 is functionally connected to the transmitter 112 and the receiver 114 to control a process of, at the transmitter 112 and the receiver 114, transmitting and receiving signals to and from other apparatuses. The processor 120 processes a signal to be transmitted, sends the processed signal to the transmitter 112 and processes a signal received by the receiver 114.
If necessary, the processor 120 may store information included in an exchanged message in the memory 130. By this structure, the reception module 100 may perform the methods of the various embodiments of the present invention.
The transmitter 162 and the receiver 164 of the transmission module 150 are configured to transmit and receive signals to and from another transmission module and reception modules and the processor 170 are functionally connected to the transmitter 162 and the receiver 164 to control a process of, at the transmitter 162 and the receiver 164, transmitting and receiving signals to and from other apparatuses. The processor 170 processes a signal to be transmitted, sends the processed signal to the transmitter 162 and processes a signal received by the receiver 164. If necessary, the processor 170 may store information included in an exchanged message in the memory 180. By this structure, the transmission module 150 may perform the methods of the various embodiments of the present invention.
The processors 120 and 170 of the reception module 100 and the transmission module 150 instruct (for example, control, adjust, or manage) the operations of the reception module 100 and the transmission module 150, respectively. The processors 120 and 170 may be connected to the memories 130 and 180 for storing program code and data, respectively. The memories 130 and 180 are respectively connected to the processors 120 and 170 so as to store operating systems, applications and general files.
The processors 120 and 170 of the present invention may be called controllers, microcontrollers, microprocessors, microcomputers, etc. The processors 120 and 170 may be implemented by hardware, firmware, software, or a combination thereof.
If the embodiments of the present invention are implemented by hardware, Application Specific Integrated Circuits (ASICs), Digital Signal Processors (DSPs), Digital Signal Processing Devices (DSPDs), Programmable Logic Devices (PLDs), Field Programmable Gate Arrays (FPGAs), etc. may be included in the processors 120 and 170.
The present invention can also be embodied as computer-readable code on a computer-readable recording medium. The computer-readable recording medium includes all data storage devices that can store data which can be thereafter read by a computer system. Examples of the computer-readable recording medium include read-only memory (ROM), random-access memory (RAM), CD-ROMs, magnetic tapes, floppy disks and optical data storage devices. The computer-readable recording medium can also be distributed over network coupled computer systems so that the computer readable code is stored and executed in a distributed fashion.
It will be apparent to those skilled in the art that various modifications and variations can be made in the present invention without departing from the spirit or scope of the inventions. Thus, it is intended that the present invention covers the modifications and variations of this invention provided they come within the scope of the appended claims and their equivalents.
INDUSTRIAL APPLICABILITY
While the methods of generating and transmitting a pilot sequence have been described on the basis of examples applied to the IEEE 802.11 system and HEW system, the methods can be applied to various wireless communication systems in addition to the IEEE 802.11 system and HEW system.
* * * * *
D00000

D00001
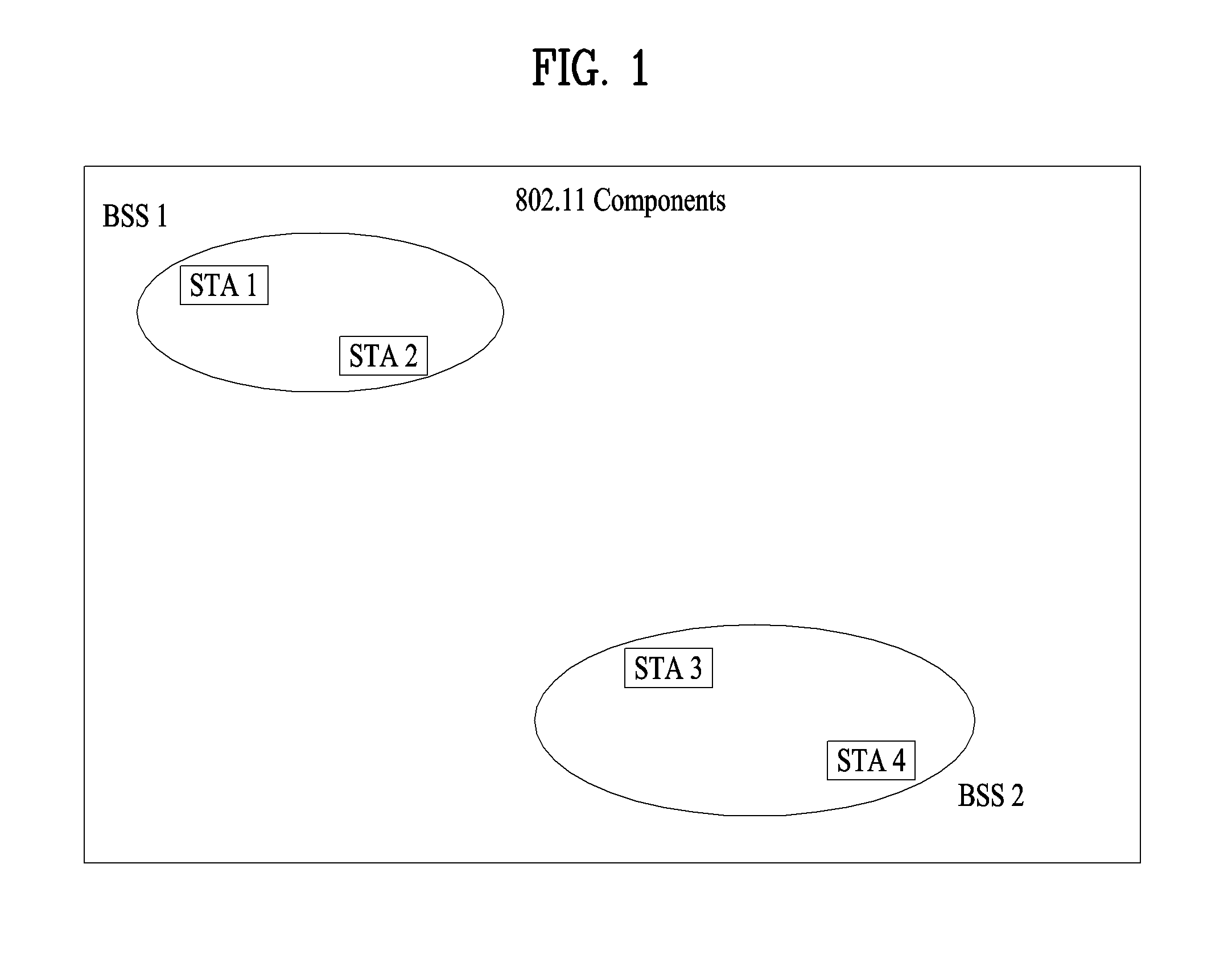
D00002

D00003
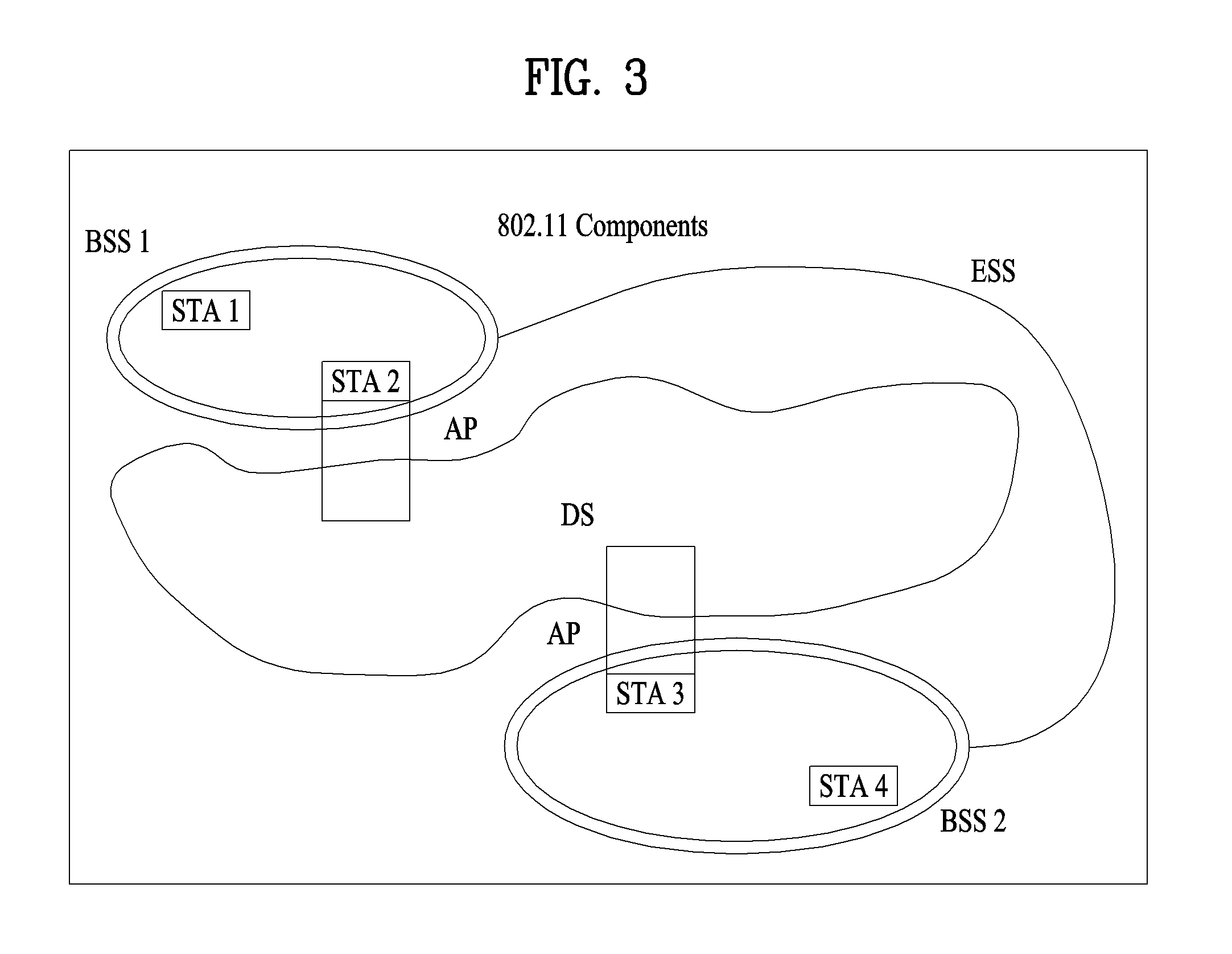
D00004

D00005

D00006

D00007

D00008

D00009

D00010
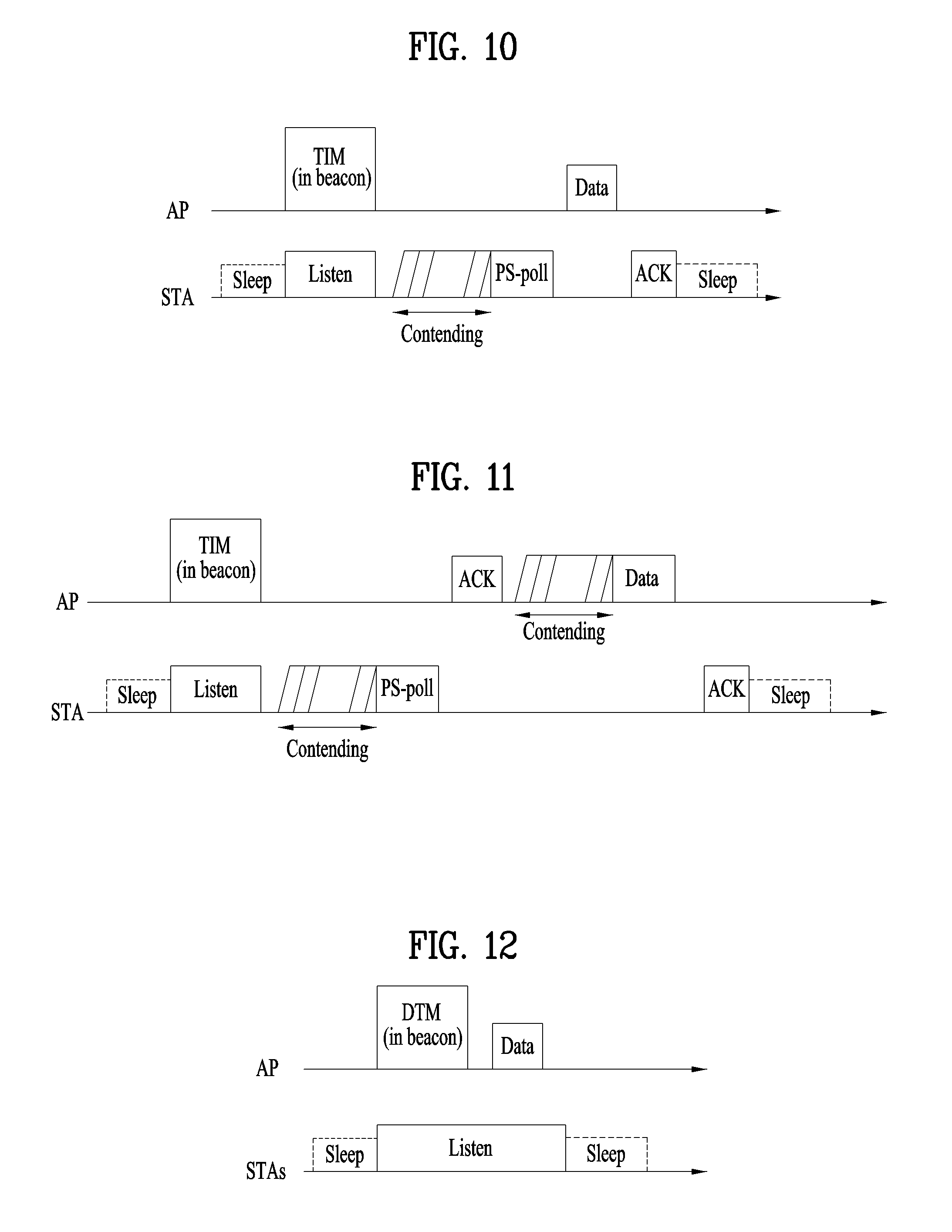
D00011

D00012

D00013

D00014

D00015

D00016

D00017

D00018

D00019

D00020

D00021

D00022

D00023

D00024
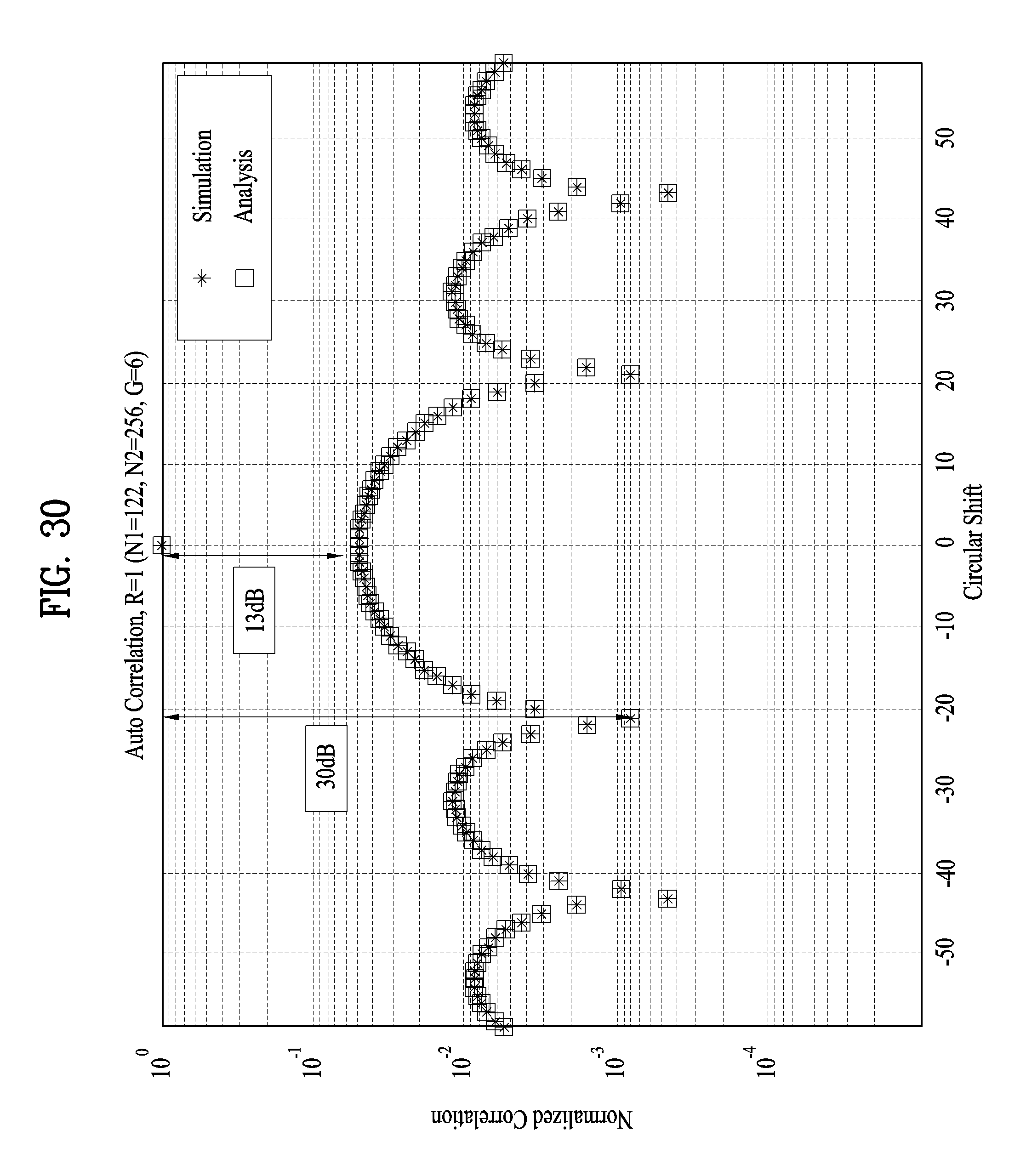
D00025
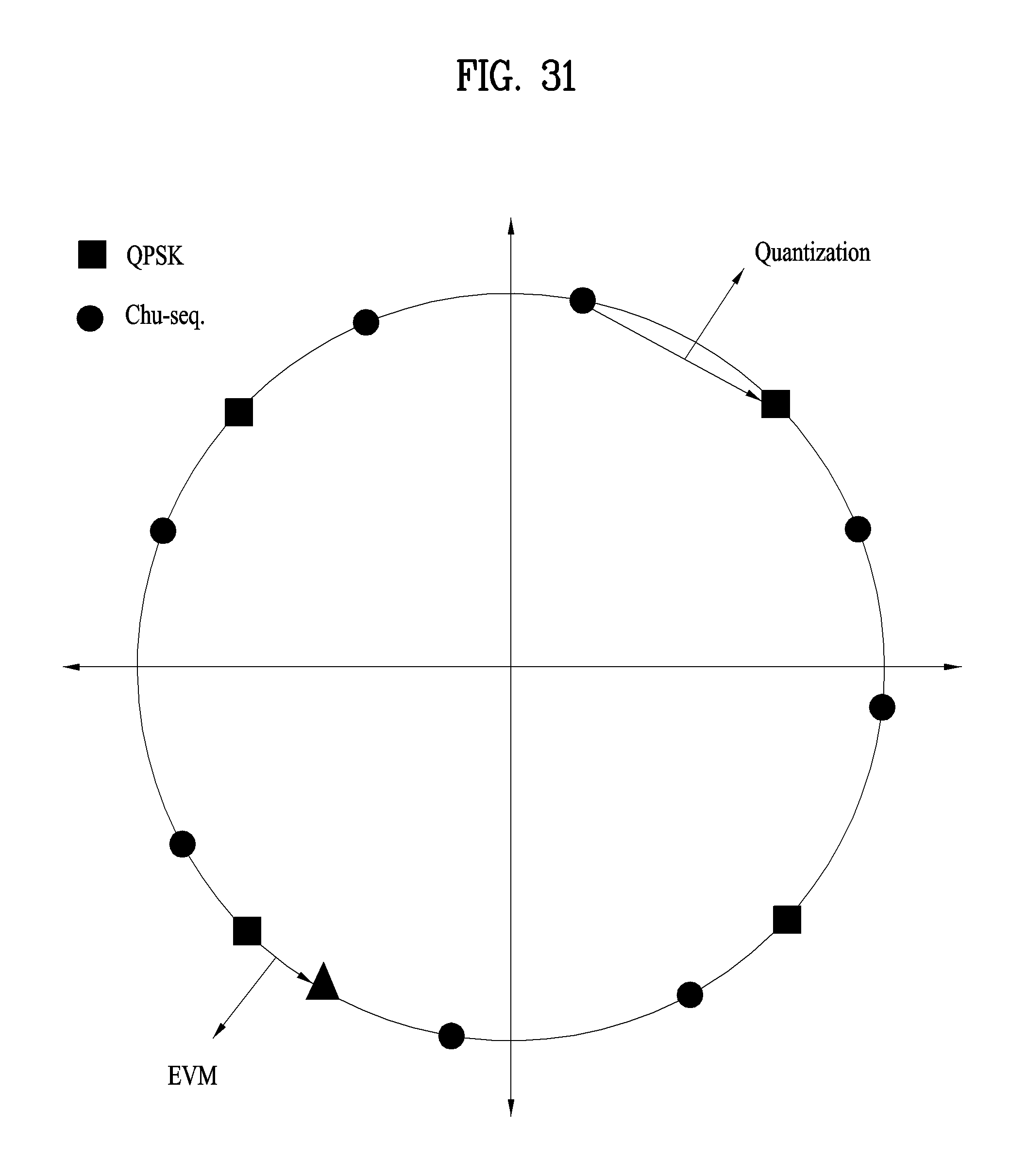
D00026

D00027

M00001

M00002

XML
uspto.report is an independent third-party trademark research tool that is not affiliated, endorsed, or sponsored by the United States Patent and Trademark Office (USPTO) or any other governmental organization. The information provided by uspto.report is based on publicly available data at the time of writing and is intended for informational purposes only.
While we strive to provide accurate and up-to-date information, we do not guarantee the accuracy, completeness, reliability, or suitability of the information displayed on this site. The use of this site is at your own risk. Any reliance you place on such information is therefore strictly at your own risk.
All official trademark data, including owner information, should be verified by visiting the official USPTO website at www.uspto.gov. This site is not intended to replace professional legal advice and should not be used as a substitute for consulting with a legal professional who is knowledgeable about trademark law.